QuickCash: Secure Transfer Payment Systems
Abstract
:1. Introduction
- They enable individuals who do not have a bank account to use and benefit from ATMs without opening a bank account.
- They provide a fast and secure method to transfer money and access cash in just a few seconds.
- They help minimize the need for sharing a bankcard or sensitive information with family members or friends.
- They provide direct access to cash in cases of emergency such as losing or forgetting bankcards.
- They grant more access to banking, and makes use of limited banking infrastructures in developing countries.
- They promote the growth of transactions carried out through ATMs, thus improving their utilization.
2. Current P2P Payment Systems and Related Work
2.1. Cash
2.2. Check
2.3. PayPal
2.4. ClearXchange
2.5. Visa Direct
2.6. Related Work
3. QuickCash Online
3.1. QuickCash Online Description
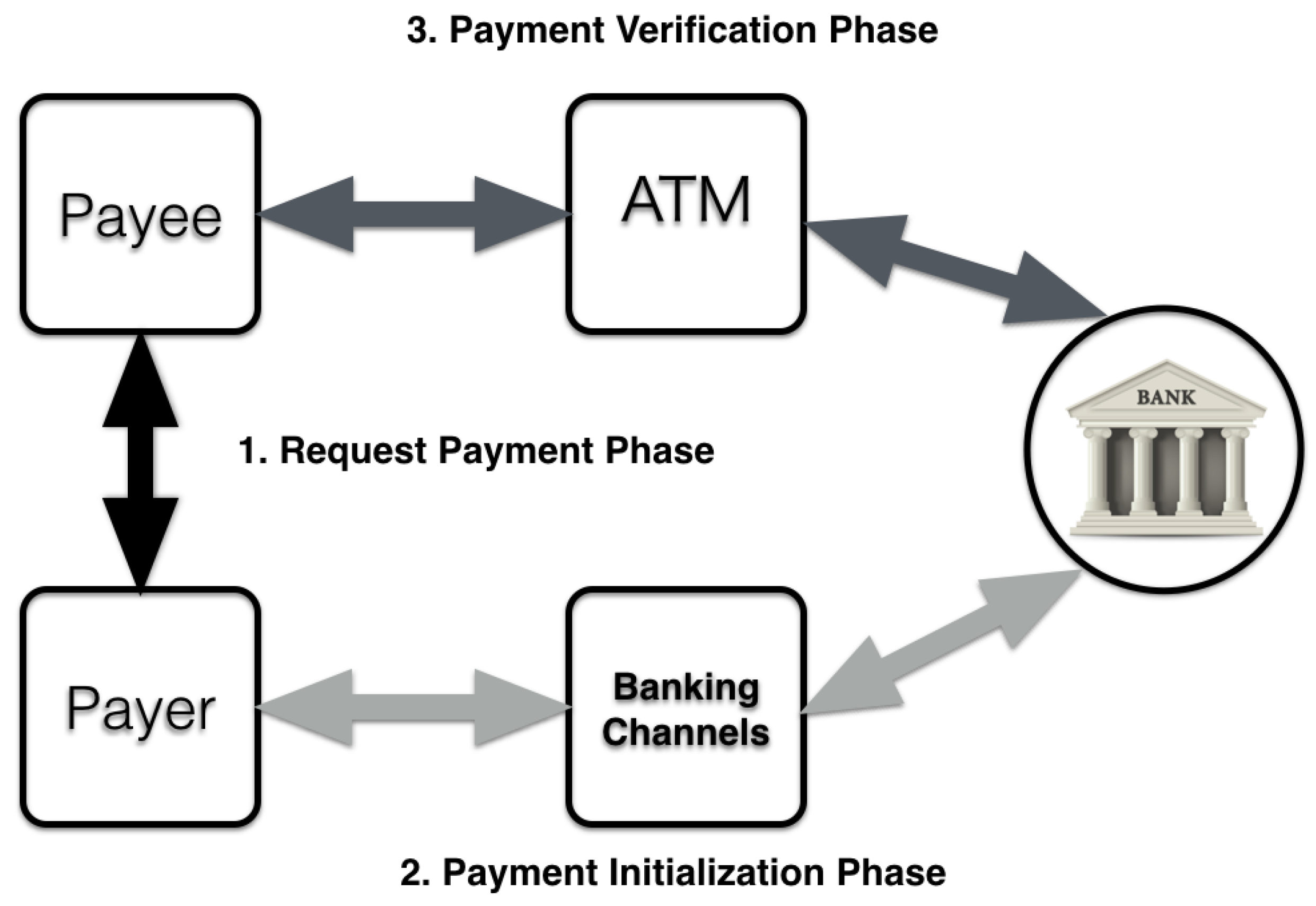
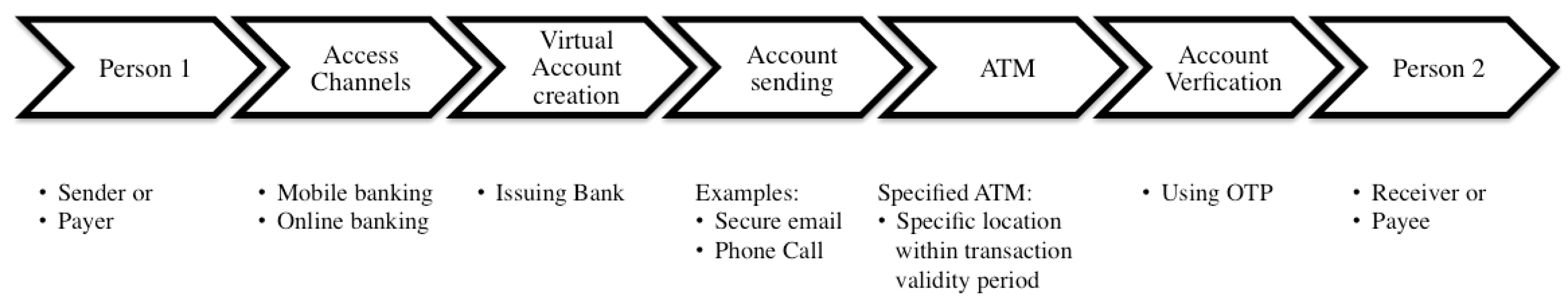
3.1.1. First Phase of QuickCash Online: Request Payment
- Automatic Teller Machine’s Location (ATML) as a location factor.
- Transaction Validity Period as a time factor (TVP).
- Mobile Number m as a possession factor.
3.1.2. Second Phase of QuickCash Online: Payment Initialization
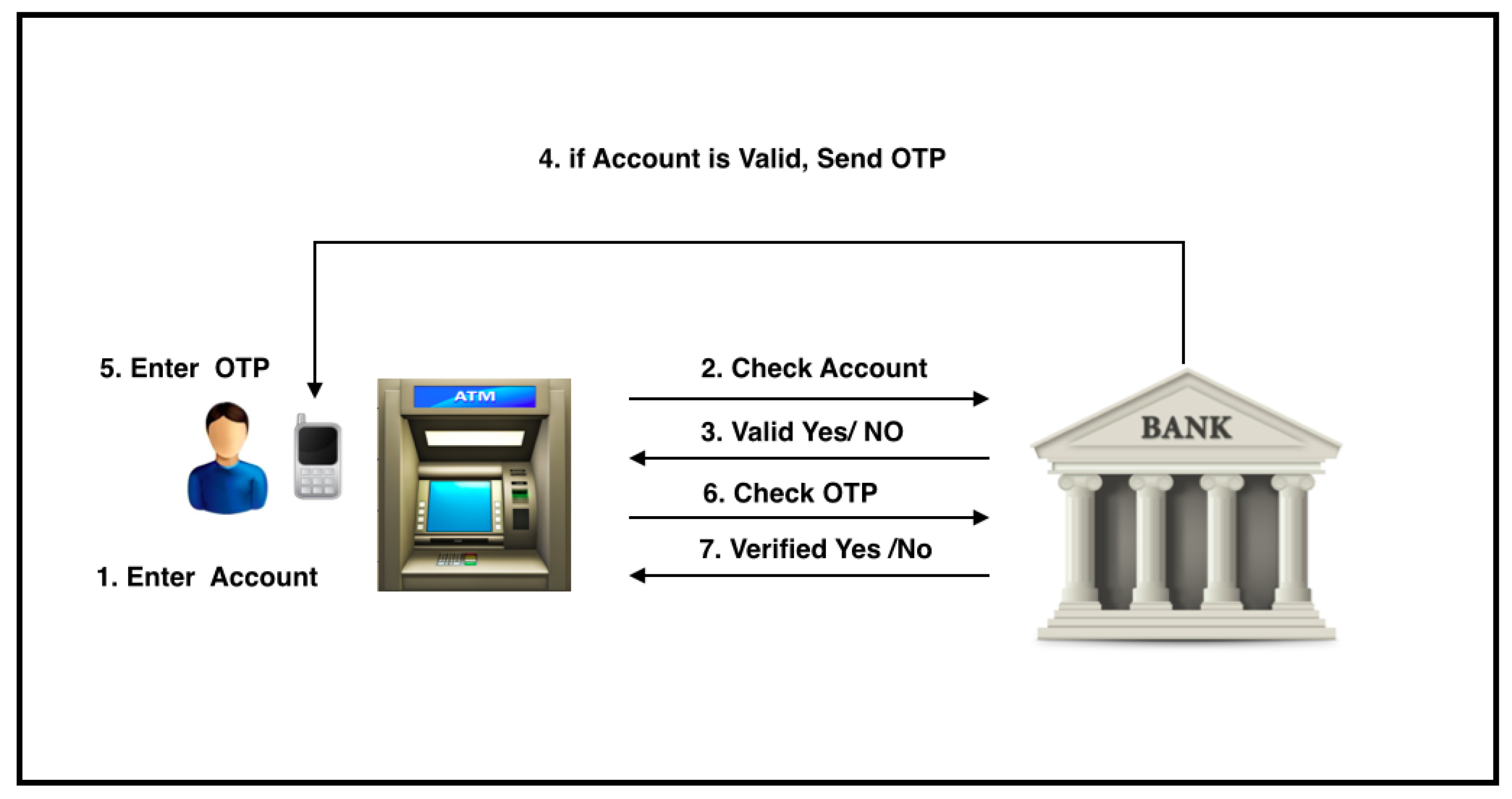
3.1.3. Third Phase of QuickCash Online: Withdrawal Process
- The payee should enter the received virtual account number VA at the specified ATM within the transaction validity period.
- After entering the virtual account number, the ATM sends an identification request containing the VA and its location to the bank host through the banking network.
- The bank host identifies the request and checks the validity of the transaction, verifies the transaction location, and checks whether the number of verification attempts has reached MaxAttempts. In QuickCash Online, we allow MaxAttempts to prevent brute force attacks before the transaction is revoked.
- The bank host sends the result of the identification to the ATM. If identified; the bank host sends OTP to the user for virtual account holder verification; otherwise, the bank host instructs the ATM to show an error message.
- The ATM instructs the payee to input the OTP.
- The ATM sends the entered OTP to the bank host for PIN verificationIf verified (Entered_OTP = Sent_OTP), then the bank host sends a Verified message to the ATM. Otherwise, the bank host sends a Not Verified message. Algorithm 1 shows a high-level description of QuickCash Online verification using the three verification factors ATML, TVP, and OTP.
- If a Verified message is sent, the bank posts debit to the payer’s account.
- In addition, the bank sends an email or text message to the payer S informing her that the payee has cashed the payment.
| Algorithm 1: QuickCash Online Verification. |
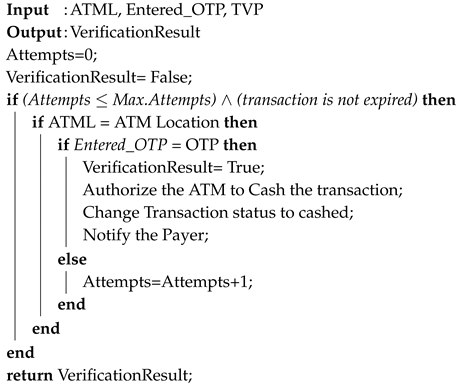 |
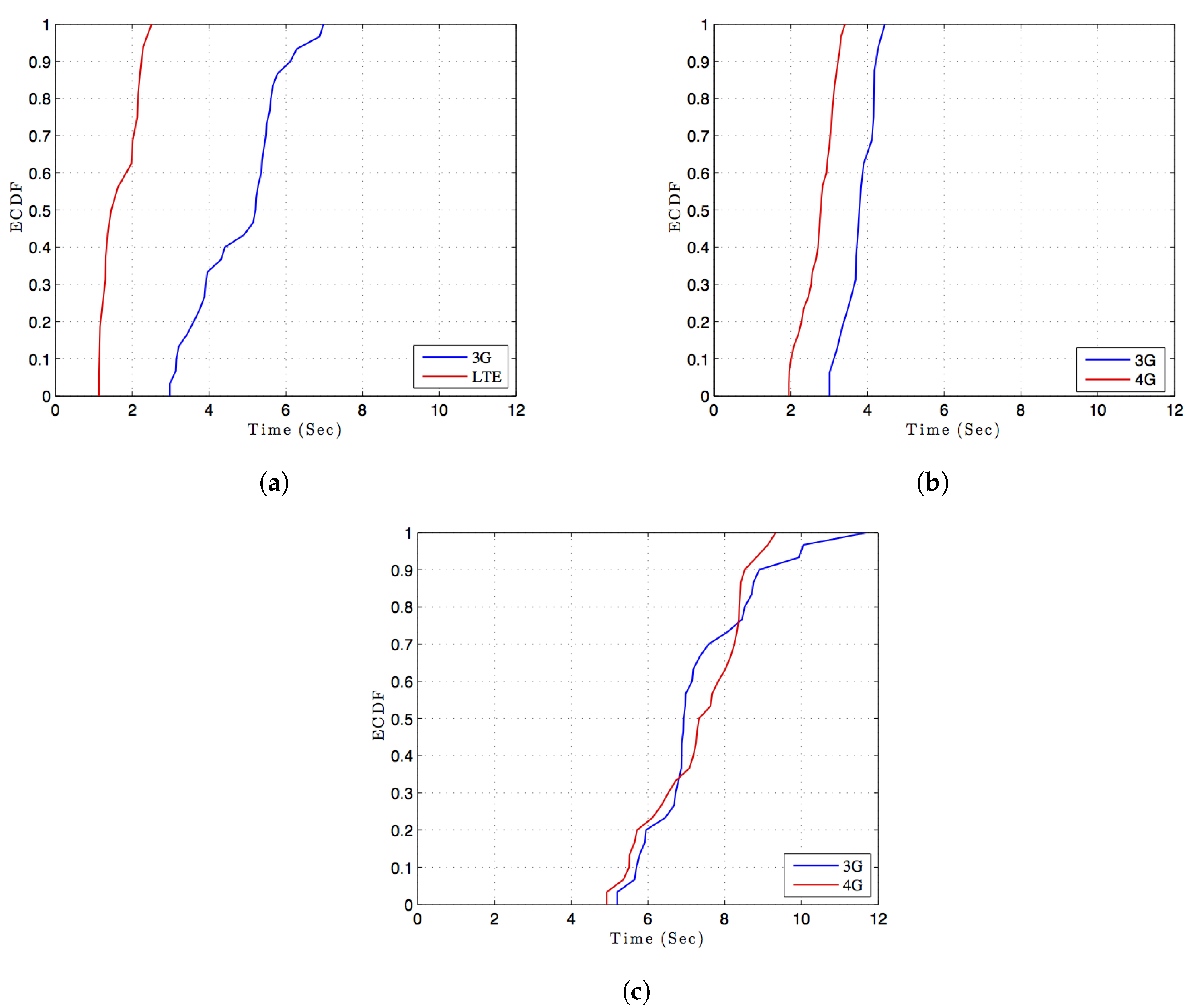
3.2. Experiment Details and Results
4. QuickCash Offline
4.1. Cryptographic Primitives
4.2. QR Codes
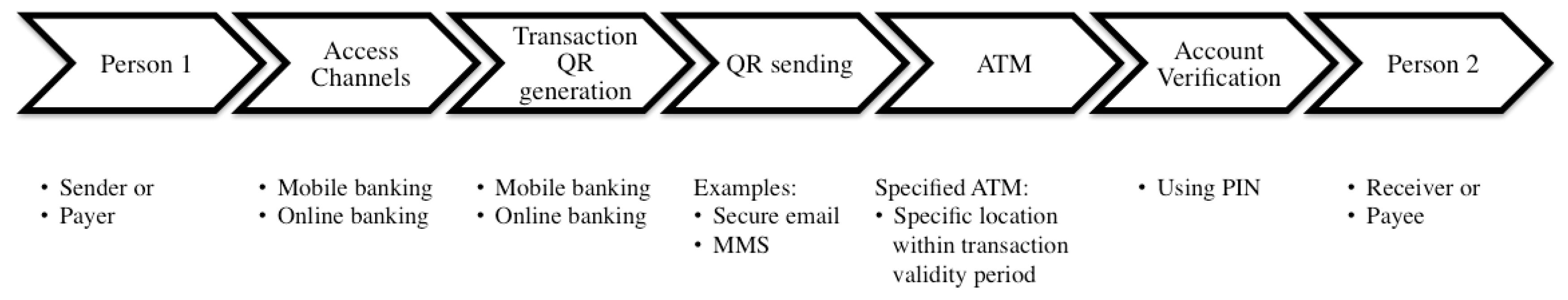
4.3. QuickCash Offline Description
4.3.1. Second Phase of QuickCash Offline: Payment Initialization
- The payer creates a transaction that contains the following information:
- Virtual account number VA.
- Amount of the transaction.
- ATM Location ATML.
- Transaction Validity Period TVP.
- PIN.
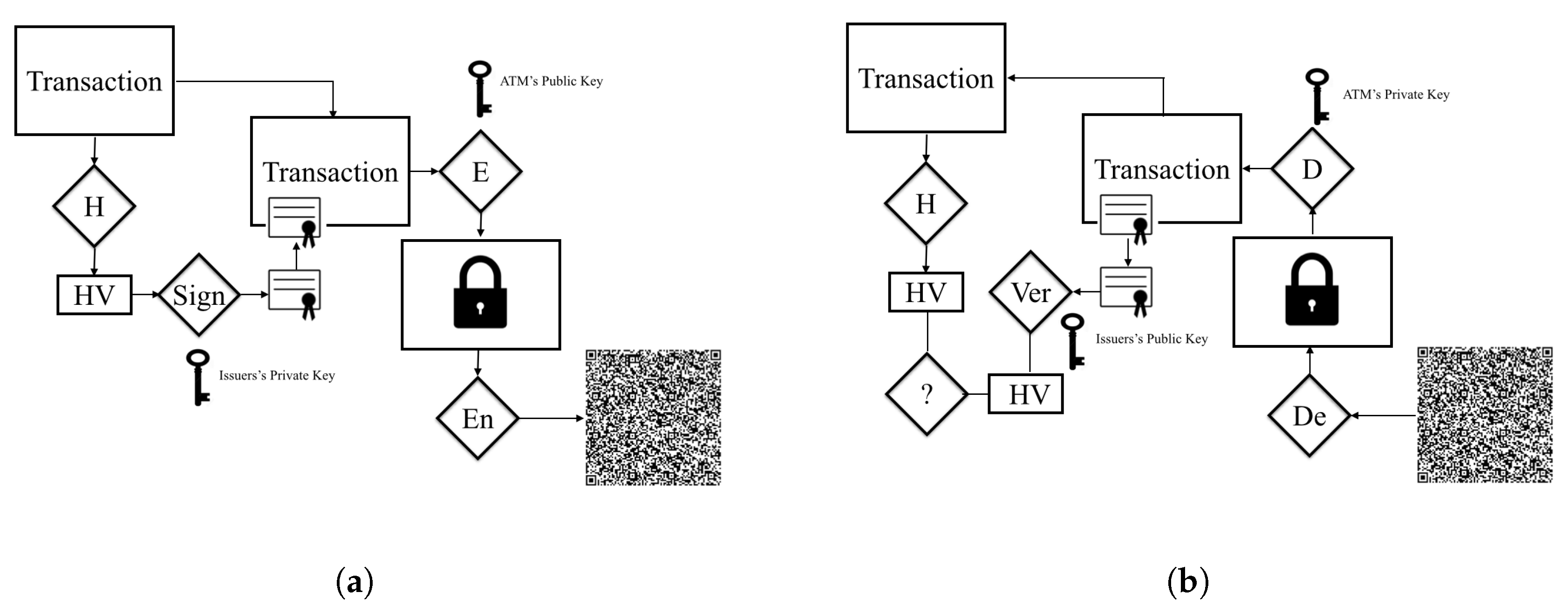
- The whole transaction is hashed using one way hashing function , and the hash digest is signed by the bank using the bank’s private key.
- The transaction along with the digital signature is encrypted by the bank using the ATM’s public key.
- The QR code of the whole encrypted transaction is generated by the bank using a QR encoder algorithm.
- The payer securely sends the QR code along with the PIN to the payee.
4.3.2. Third Phase of QuickCash Offline: Withdrawal Process
- The payee should have the QR ready to be scanned at the designated ATM within the transaction validity period.
- The scanned QR code is decoded and converted to the message E.
- The ATM decrypts the encrypted message E using the ATM’s private key. The message contains two parts: the transaction details, and the digital signature.
- The ATM identifies the transaction and checks the transaction validity via signature verification.
- If the transaction is identified and valid, and number of verification attempts is less than or equal to the maximum allowable attempts, then the ATM prompts the user to enter the PIN.
- If the user is verified (entered PIN = PIN), then the ATM allows the payee to access the cash, and then sends a cashed transaction message to the bank. Algorithm 2 illustrates a high-level description of QuickCash Offline verification.
- The bank posts debit to the payer account and sends an email or text message to the payer informing her that the payee has cashed the payment.
| Algorithm 2: Offline QuickCash Verification. |
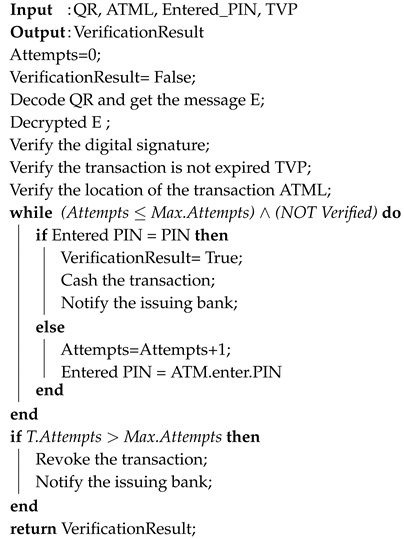 |
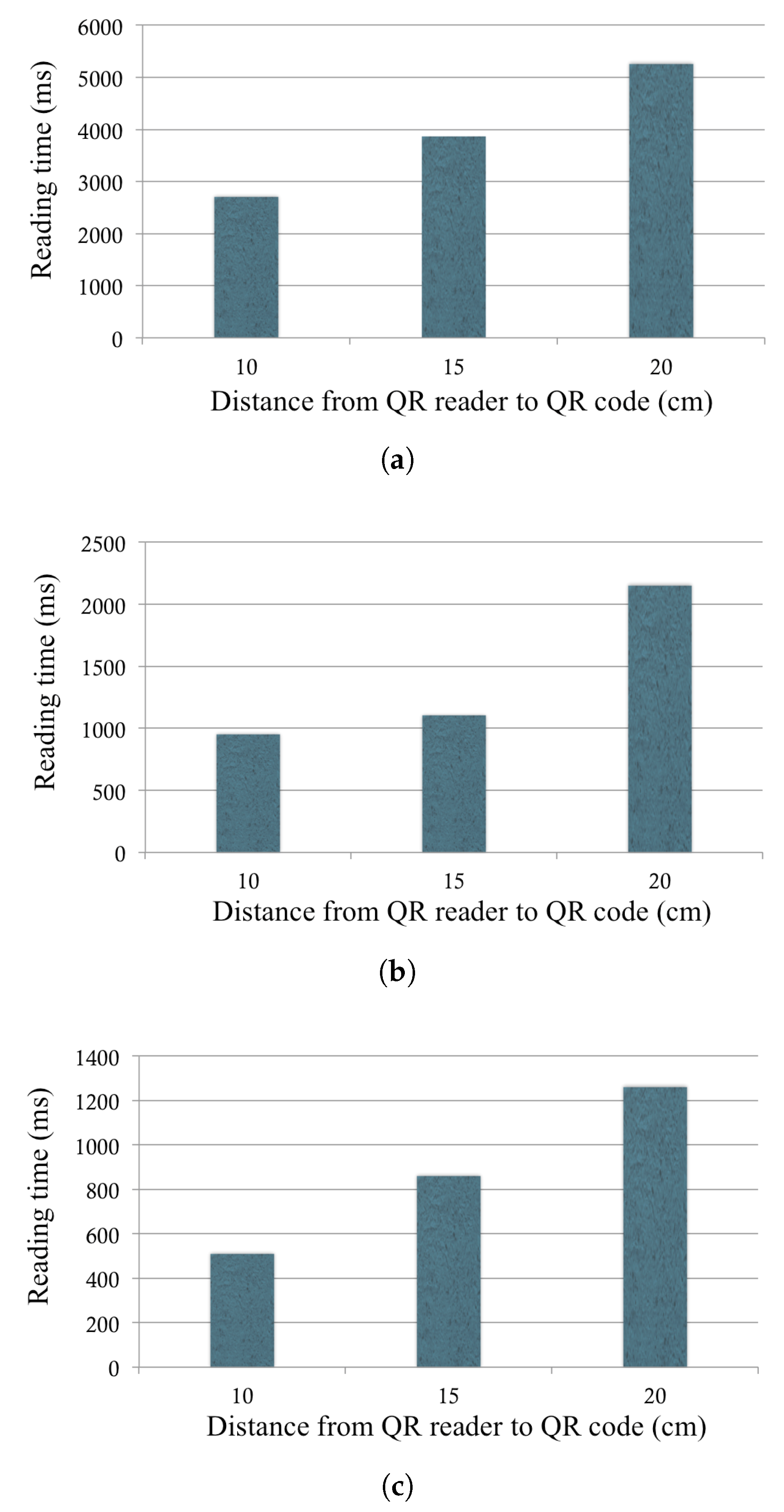
4.4. Experiment Details and Results
5. Security Analysis
5.1. Privacy
5.2. Brute-Force Attacks
5.3. Verification
5.4. Integrity
5.5. Theft of the Virtual Account or QR Code
5.6. Double Spending
6. QuickCash and IoT
7. Discussion and Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Bonneau, J.; Preibusch, S.; Anderson, R. A birthday present every eleven wallets? The security of customer-chosen banking PINs. In Financial Cryptography and Data Security; Springer: Berlin, Heidelberg, 2012; pp. 25–40. [Google Scholar]
- Anderson, R.; Murdoch, S.J. EMV: Why payment systems fail. Commun. ACM 2014, 57, 24–28. [Google Scholar] [CrossRef]
- Banking in the Developing World: The Poor are Different. 2012. Available online: http://www.economist.com/blogs/feastandfamine/2012/04/banking-developing-world (accessed on 20 April 2012).
- The World, Bank. Information and Communications for Development 2012: Maximizing Mobile. 2012. Available online: https://siteresources.worldbank.org/EXTINFORMATIONANDCOMMUNICATIONANDTECHNOLOGIES/Resources/IC4D-2012-Report.pdf (accessed on 12 June 2017).
- Bradford, T.; Keeton, W.R. New person-to-person payment methods: Have checks met their match? In Federal Reserve Bank of Kansas City Economic Review; Federal Reserve Bank of Kansas City: Kansas City, MI, USA, 2012. [Google Scholar]
- Bennett, B.; Conover, D.; O’Brien, S.; Advincula, R. Cash Continues to Play a Key Role in Consumer Spending: Evidence from the Diary of Consumer Payment Choice; Federal Reserve Bank of San Francisco: San Francisco, CA, USA, 2014. [Google Scholar]
- Gerdes, G.R.; McKee, J.M.; Liu, M.X.; Dake, S.; Berkenpas, J.P.; Dyer, P.; Chen, M.C.; Brangaccio, D.; Hayward, M.C.; Donahue, N.; et al. The 2013 Federal Reserve Payments Study; Federal Reserve System: Washington, DC, USA, 2014. [Google Scholar]
- Paypal. Available online: https://www.paypal.com/ (accessed on 22 May 2014).
- Statista. Available online: http://www.statista.com/ (accessed on 28 May 2014).
- Chase Goes Live On clearXchange. Available online: http://www.pymnts.com/news/2015/chase-goes-live-on-clearxchange-p2p-network/#.VXYAVVyqqko (accessed on 24 May 2014).
- Valentine, L. Payment Innovations: Are You in? the Payments Space Is Alive with New Options like P2P. Here’s a Look at the Hottest, and Possible Bank Impacts. ABA Bank. J. 2012, 104, 26. [Google Scholar]
- Visa Direct. Available online: https://developer.visa.com/vpp/ (accessed on 26 May 2014).
- Send Money Transfers Anywhere in the World with EasyWeb. Available online: https://www.tdcanadatrust.com/products-services/banking/electronic-banking/ways-to-send-money/visa-direct.jsp (accessed on 24 May 2014).
- Gomzin, S. Hacking Point of Sale: Payment Application Secrets, Threats, and Solutions; Wiley: Indianapolis, IN, USA, 2014. [Google Scholar]
- Nakajima, M. Payment System Technologies and Function Innovations and Developments; IGI Globale: Hershey, PA, USA, 2011. [Google Scholar]
- Gao, J.; Edunuru, K.; Cai, J.; Shim, S. P2P-Paid: A peer-to-peer wireless payment system. In Proceedings of the Second IEEE International Workshop on Mobile Commerce and Services (WMCS’05), Munich, Germany, 19 July 2005; pp. 102–111. [Google Scholar]
- Monteiro, D.M.; Rodrigues, J.J.; Lloret, J.; Sendra, S. A hybrid NFC—Bluetooth secure protocol for Credit Transfer among mobile phones. Secur. Commun. Netw. 2014, 7, 325–337. [Google Scholar] [CrossRef]
- Carminati, B.; Ferrari, E.; Tran, N.H. Enforcing trust preferences in mobile person-to-person payments. In Proceedings of the 2013 IEEE International Conference on Social Computing (SocialCom), Alexandria, VA, USA, 8–14 September 2013; pp. 429–434. [Google Scholar]
- Balan, R.K.; Ramasubbu, N.; Prakobphol, K.; Christin, N.; Hong, J. mFerio: The design and evaluation of a peer-to-peer mobile payment system. In Proceedings of the 7th International Conference on Mobile Systems, Applications, and Services (ACM), Krakòw, Poland, 22–25 June 2009; pp. 291–304. [Google Scholar]
- Hiltgen, A.; Kramp, T.; Weigold, T. Secure Internet banking authentication. IEEE Secur. Priv. 2006, 4, 21–29. [Google Scholar] [CrossRef]
- Alhothaily, A.; Alrawais, A.; Cheng, X.; Bie, R. Towards More Secure Cardholder Verification in Payment Systems. In Proceedings of the 9th International Conference on Wireless Algorithms, Systems, and Applications (WASA 2014), Harbin, China, 23–25 June 2014. [Google Scholar]
- Alhothaily, A.; Alrawais, A.M.; Cheng, X.; Bie, R. A novel verification method for payment card systems. In Personal and Ubiquitous Computing; Springer: London, UK, 2015; Volume 19, pp. 1145–1156. [Google Scholar]
- Marforio, C.; Karapanos, N.; Soriente, C.; Kostiainen, K.; Capkun, S. Smartphones as practical and secure location verification tokens for payments. In Proceedings of the Network and Distributed System Security Symposium (NDSS), San Diego, CA, USA, 23–26 February 2014. [Google Scholar]
- Park, F.S.; Gangakhedkar, C.; Traynor, P. Leveraging cellular infrastructure to improve fraud prevention. In Proceedings of the 2009 IEEE Annual Computer Security Applications Conference (ACSAC’09), Honolulu, HI, USA, 7–11 December 2009; pp. 350–359. [Google Scholar]
- Twilio. Available online: https://www.twilio.com/docs/api (accessed on 24 May 2014).
- Rivest, R.L.; Shamir, A.; Adleman, L. A method for obtaining digital signatures and public-key cryptosystems. Commun. ACM 1978, 21, 120–126. [Google Scholar] [CrossRef]
- Stallings, W. Cryptography and Network Security: Principles and Practice; Pearson: Boston, MA, USA, 2014. [Google Scholar]
- Winter, M. Scan Me: Everybody’s Guide to the Magical World of QR Codes— Barcodes, Mobile Devices and Hyperlinking the Real to the Virtual; Westsong Pub.: Napa, CA, USA, 2011. [Google Scholar]
- International Organization for Standardization (ISO). Information Technology— Automatic Identification and Data Capture Techniques—QR Code Bar Code Symbology Specification; ISO ISO/IEC 18004:2015; International Organization for Standardization: Geneva, Switzerland, 2015. [Google Scholar]
- Payment Card Industry (PCI) Data Security Standard. Available online: https://www.pcisecuritystandards.org/documents/pci_dss_v2.pdf (accessed on 26 May 2014).
- Singh, S. Secure shared passwords: the social and cultural centered design of banking. J. Financ. Transform. 2008, 23, 110–114. [Google Scholar]
- Singh, S.; Cabraal, A.; Demosthenous, C.; Astbrink, G.; Furlong, M. Password sharing: implications for security design based on social practice. In Proceedings of the SIGCHI Conference on Human Factors in Computing Systems (ACM), San Jose, CA, USA, 30 April–3 May 2007; pp. 895–904. [Google Scholar]
- Alhothaily, A.; Hu, C.; Alrawais, A.; Song, T.; Cheng, X.; Chen, D. A Secure and Practical Authentication Scheme Using Personal Devices. IEEE Access 2017. submitted. [Google Scholar]
- Alrawais, A.; Alhothaily, A.; Cheng, X. Secure Authentication Scheme Using Dual Channels in Rogue Access Point Environments. In Wireless Algorithms, Systems, and Applications; Springer: Cham, Switzerland, 2014; pp. 554–563. [Google Scholar]
- Aloul, F.; Zahidi, S.; El-Hajj, W. Two factor authentication using mobile phones. In Proceedings of the 2009 IEEE/ACS International Conference on Computer Systems and Applications (AICCSA 2009), Rabat, Morocco, 10 May–13 May 2009; pp. 641–644. [Google Scholar]
- Weir, C.S.; Douglas, G.; Carruthers, M.; Jack, M. User perceptions of security, convenience and usability for ebanking authentication tokens. Comput. Secur. 2009, 28, 47–62. [Google Scholar] [CrossRef]
- Laput, G.; Yang, C.; Xiao, R.; Sample, A.; Harrison, C. Em-sense: Touch recognition of uninstrumented, electrical and electromechanical objects. In Proceedings of the 28th Annual ACM Symposium on User Interface Software & Technology (ACM), Charlotte, NC, USA, 11–15 November 2015; pp. 157–166. [Google Scholar]
- Nandakumar, R.; Chintalapudi, K.K.; Padmanabhan, V.; Venkatesan, R. Dhwani: Secure peer-to-peer acoustic NFC. In ACM SIGCOMM Computer Communication Review; ACM: New York, NY, USA, 2013; Volume 43, pp. 63–74. [Google Scholar]



| Abbreviation | Description |
|---|---|
| S | The individual who sends the payment |
| R | The individual who receives the payment |
| ATM | Automatic Teller Machine |
| ATML | Automatic Teller Machine Location |
| TVP | Transaction Validity Period |
| VA | Virtual Account |
| PIN | Personal Identification Number |
| OTP | One Time PIN |
| m | The mobile phone number of the payee |
| Local Operator A | Local Operator B | International Operator | ||||
|---|---|---|---|---|---|---|
| 3G | LTE | 3G | 4G | 3G | 4G | |
| Average | 4.85 | 1.57 | 3.79 | 2.75 | 7.39 | 7.33 |
| Min | 2.98 | 1.03 | 3.01 | 1.95 | 5.20 | 4.93 |
| Max | 6.98 | 2.50 | 5.01 | 3.41 | 11.69 | 9.33 |
| Std dev | 1.13 | 0.45 | 0.48 | 0.43 | 1.46 | 1.23 |
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Alhothaily, A.; Alrawais, A.; Song, T.; Lin, B.; Cheng, X. QuickCash: Secure Transfer Payment Systems. Sensors 2017, 17, 1376. https://doi.org/10.3390/s17061376
Alhothaily A, Alrawais A, Song T, Lin B, Cheng X. QuickCash: Secure Transfer Payment Systems. Sensors. 2017; 17(6):1376. https://doi.org/10.3390/s17061376
Chicago/Turabian StyleAlhothaily, Abdulrahman, Arwa Alrawais, Tianyi Song, Bin Lin, and Xiuzhen Cheng. 2017. "QuickCash: Secure Transfer Payment Systems" Sensors 17, no. 6: 1376. https://doi.org/10.3390/s17061376
APA StyleAlhothaily, A., Alrawais, A., Song, T., Lin, B., & Cheng, X. (2017). QuickCash: Secure Transfer Payment Systems. Sensors, 17(6), 1376. https://doi.org/10.3390/s17061376




