Context Sensing System Analysis for Privacy Preservation Based on Game Theory †
Abstract
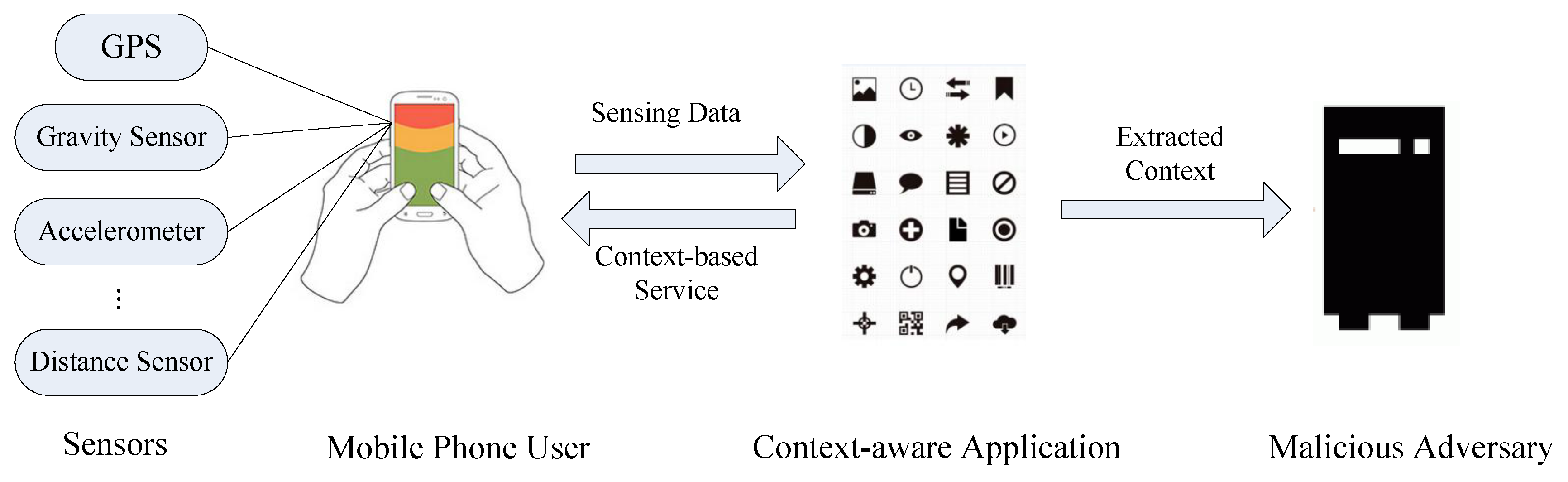
:1. Introduction
2. Related Work
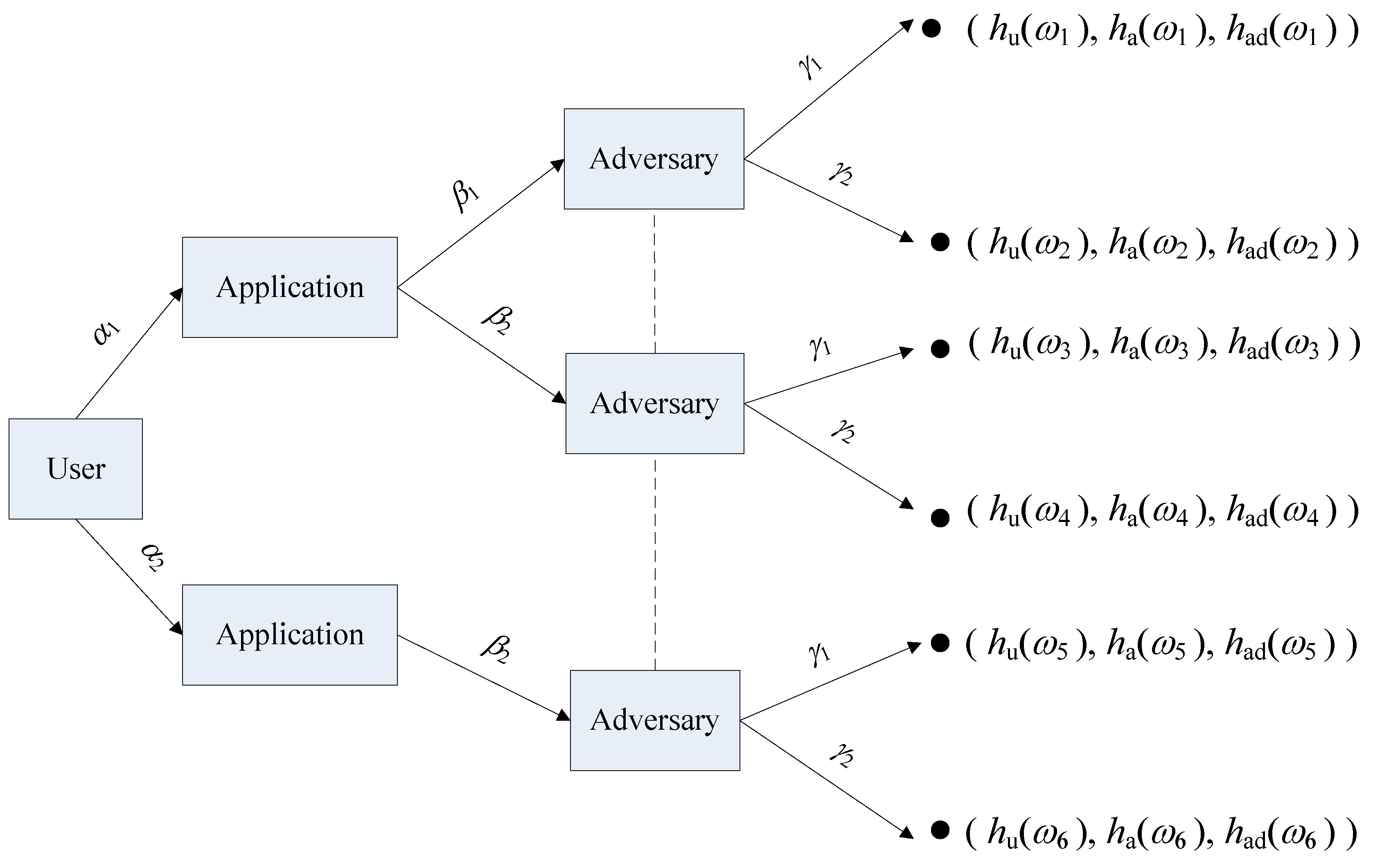
3. Single-Stage Game Analysis Based on the Extensive Form Game Formulation
3.1. Problem Statement and the Extensive Form Game Formulation
3.2. Payoff Function
3.2.1. The User’s Payoff Function
3.2.2. The Application’s Payoff Function
3.2.3. The Adversary’s Payoff Function
3.3. Solving and Analyzing the Nash Equilibrium
3.3.1. The Solution of the Nash Equilibrium
3.3.2. The Analysis of the Nash Equilibrium
4. Repeated Game Analysis
4.1. Not Concealing the Identity of the Application
4.2. Concealing the Identity of the Application
5. Numerical Analysis
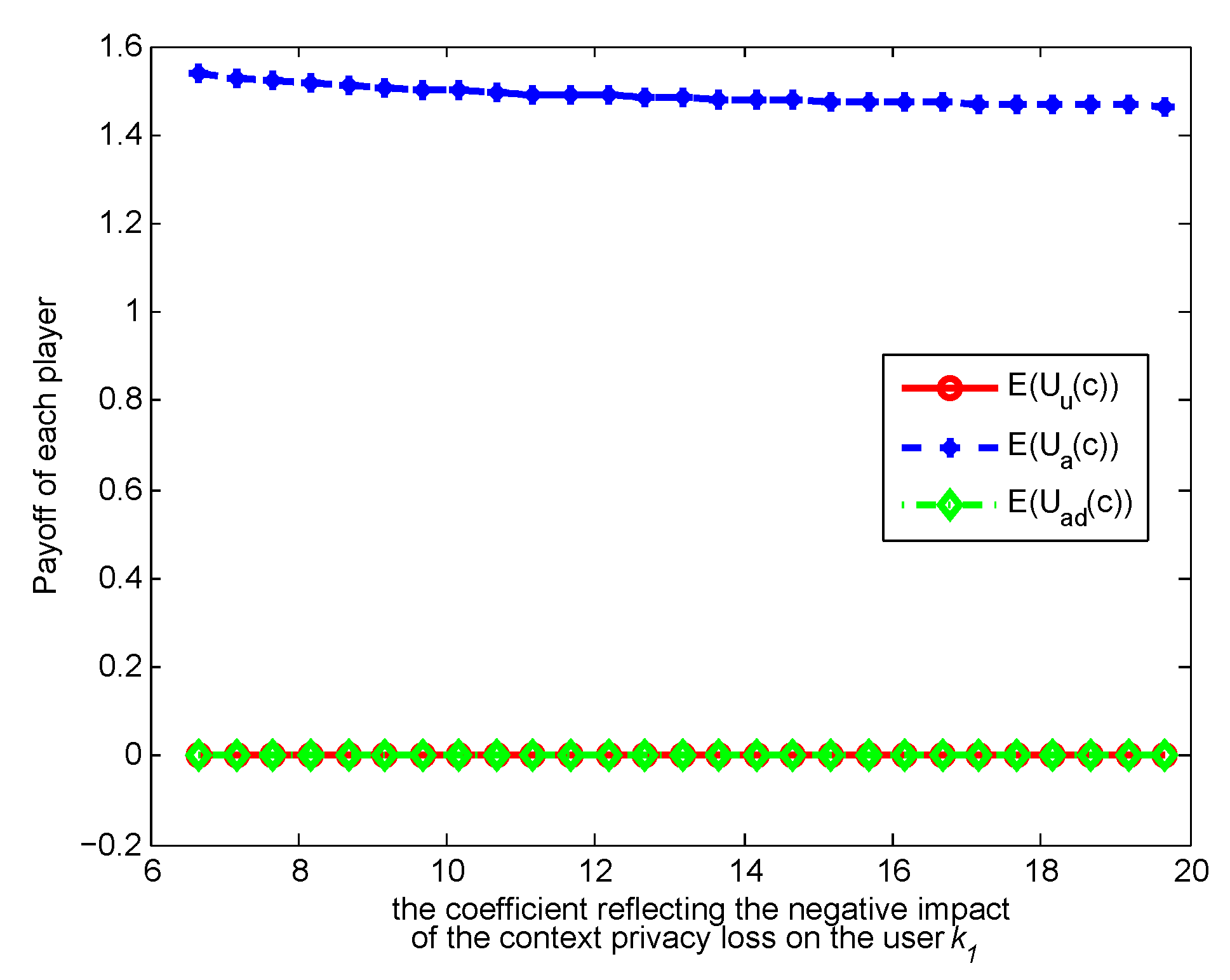
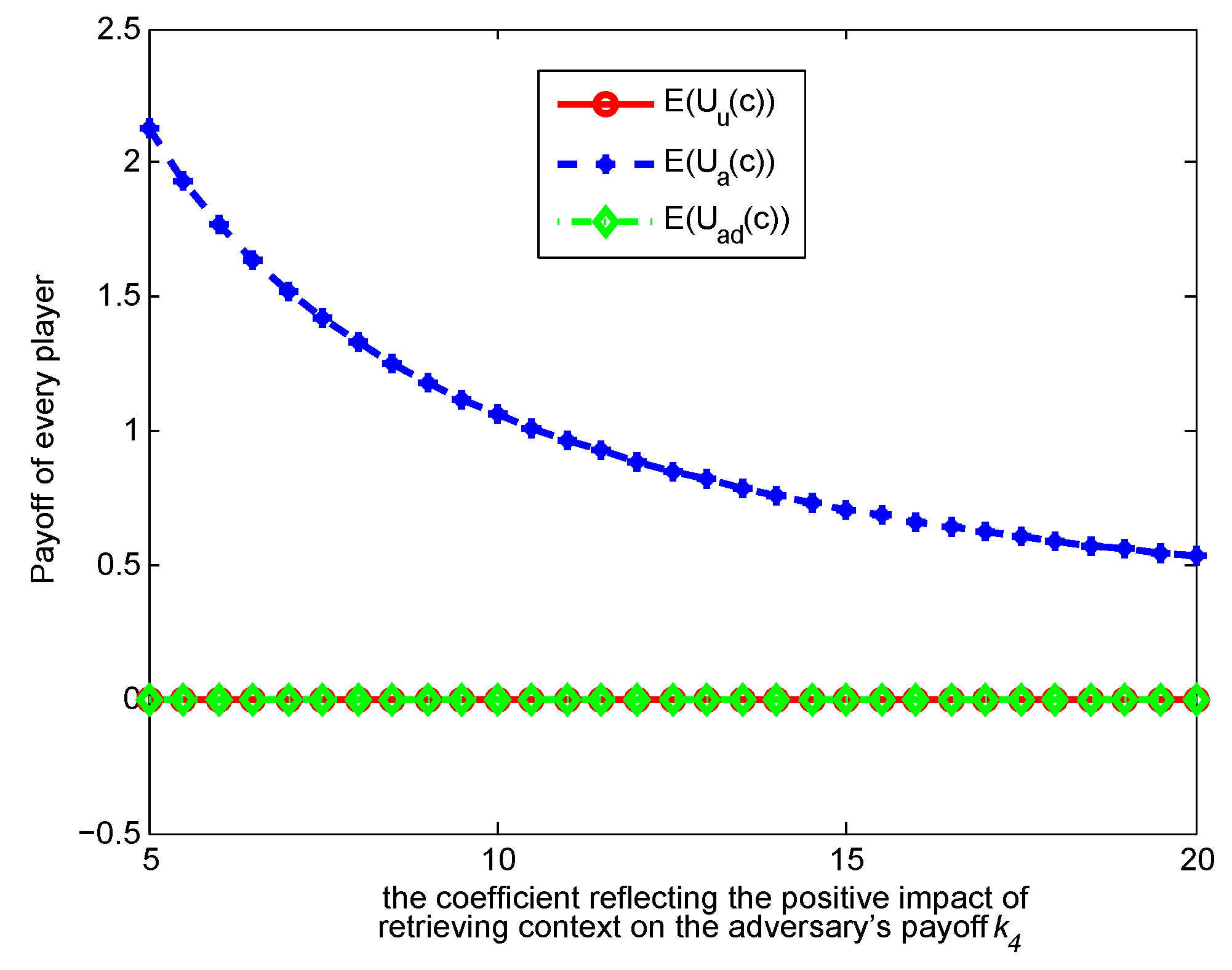
5.1. Numerical Analysis of the Single-Stage Game Model
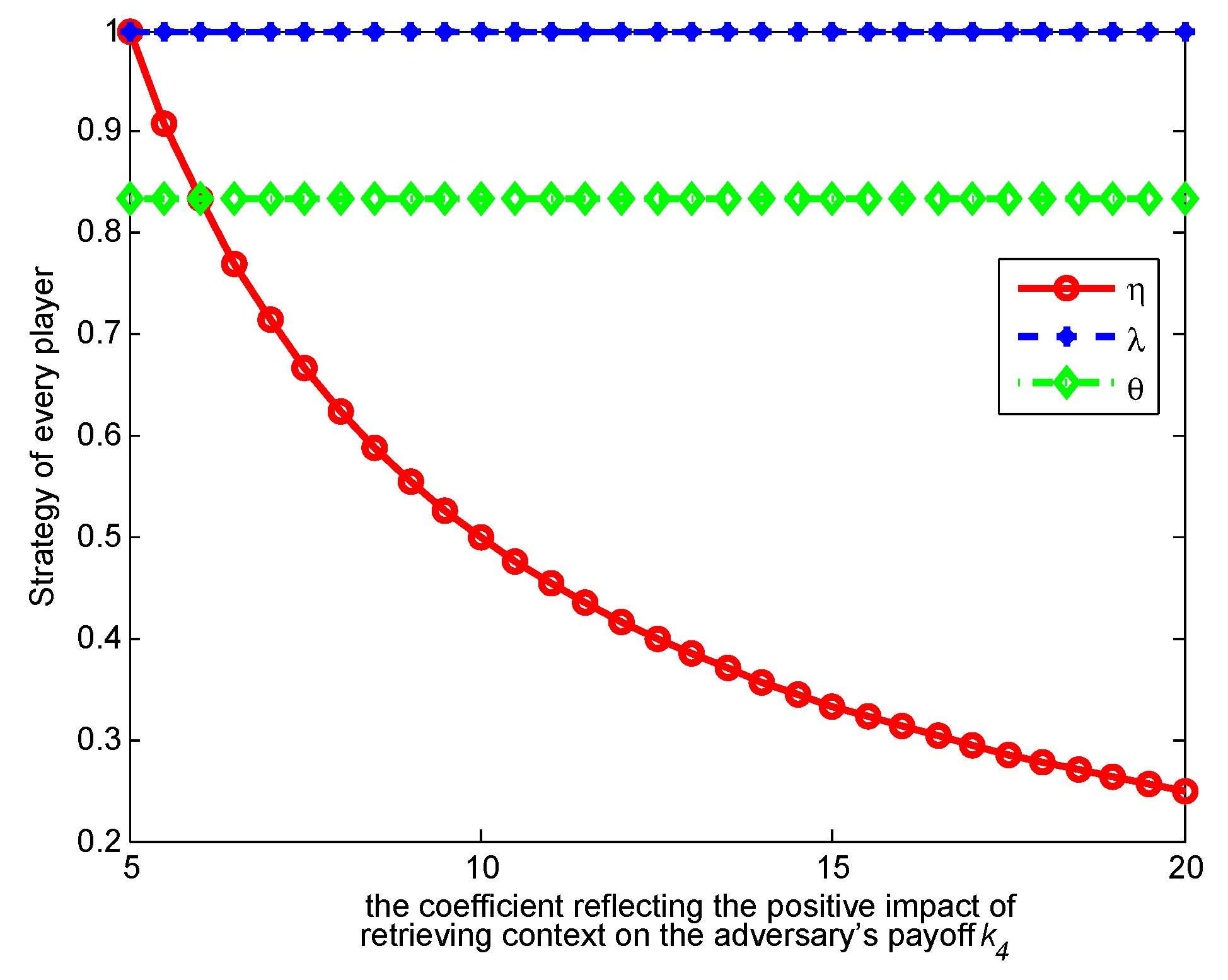
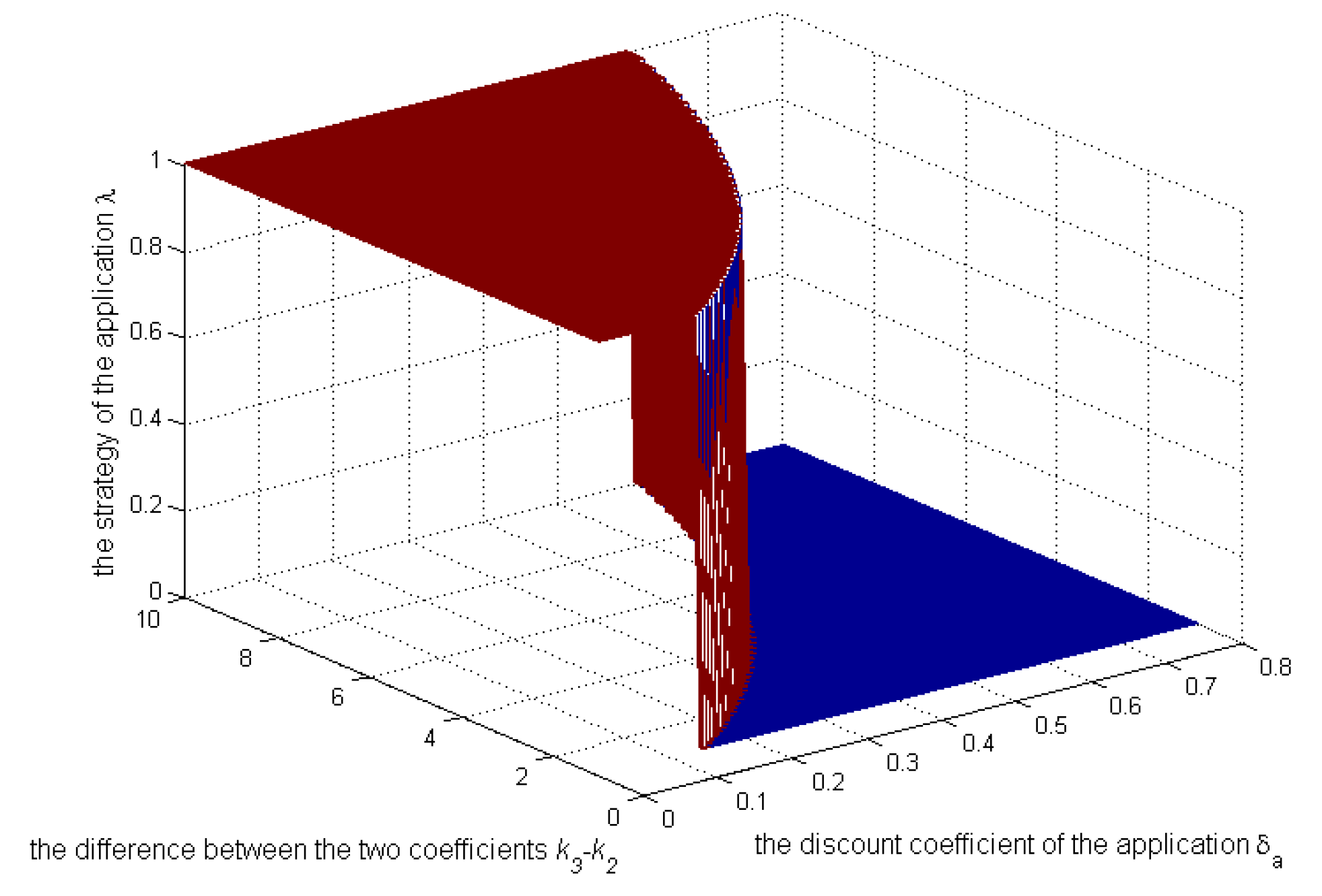
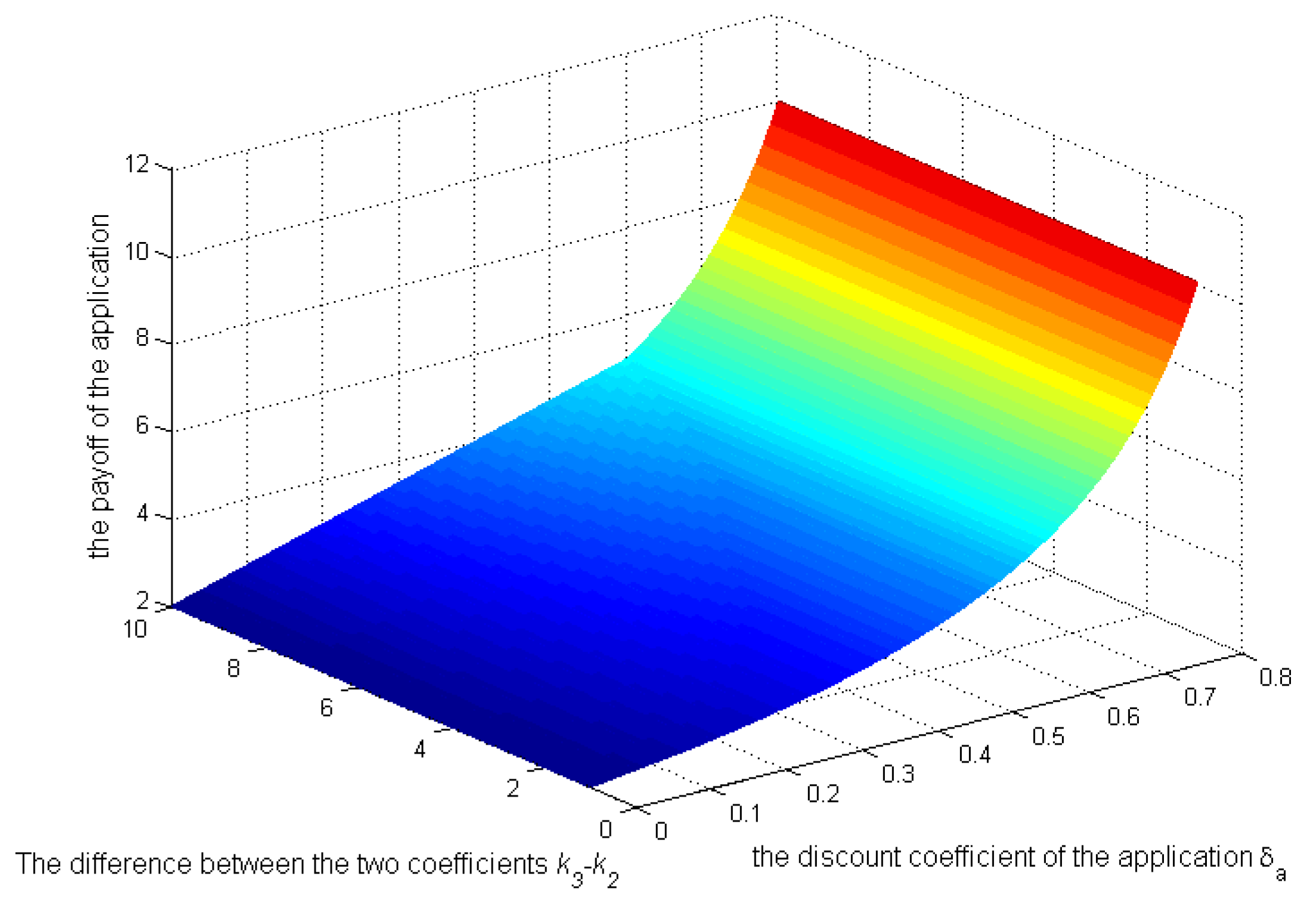
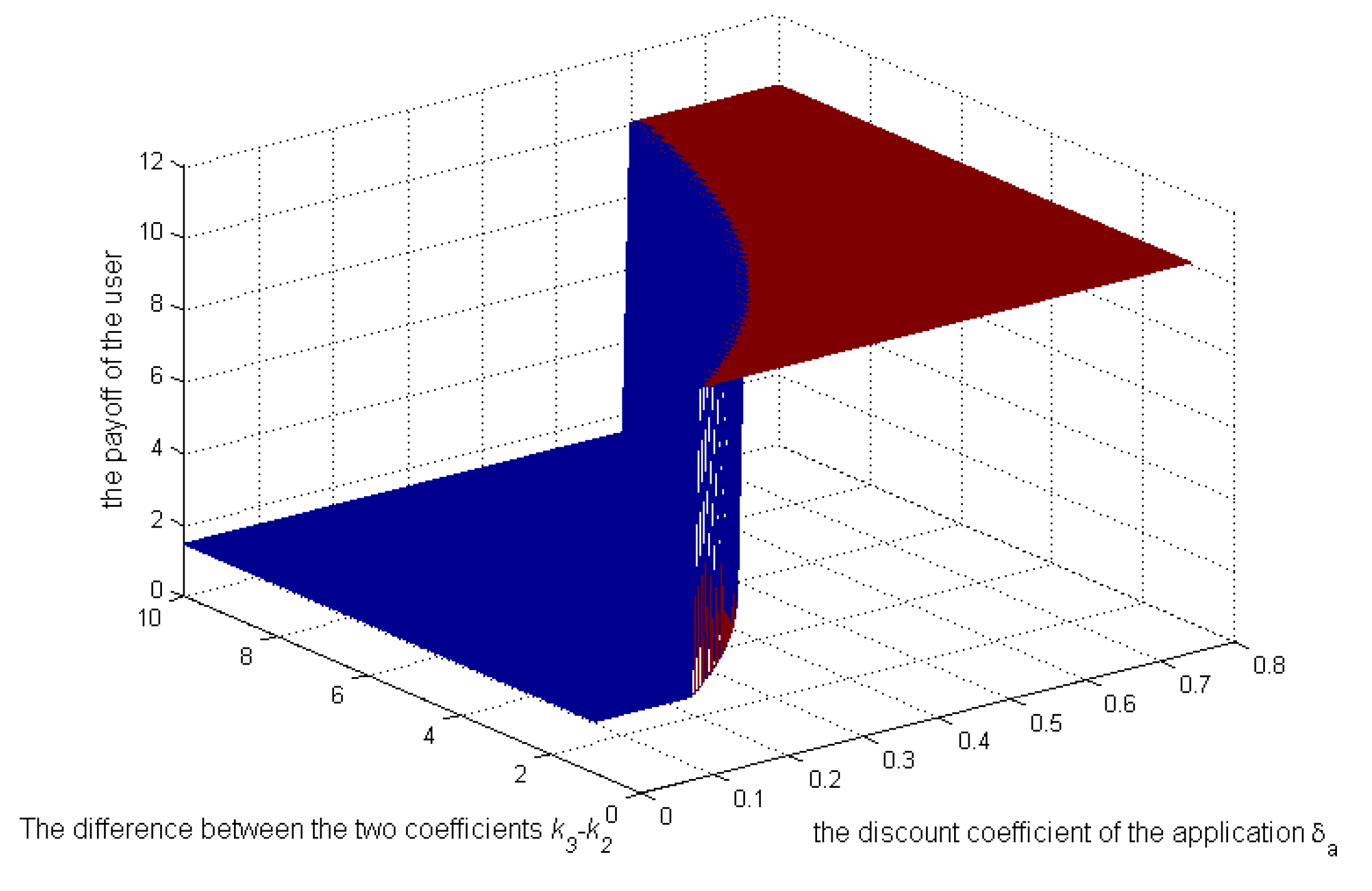
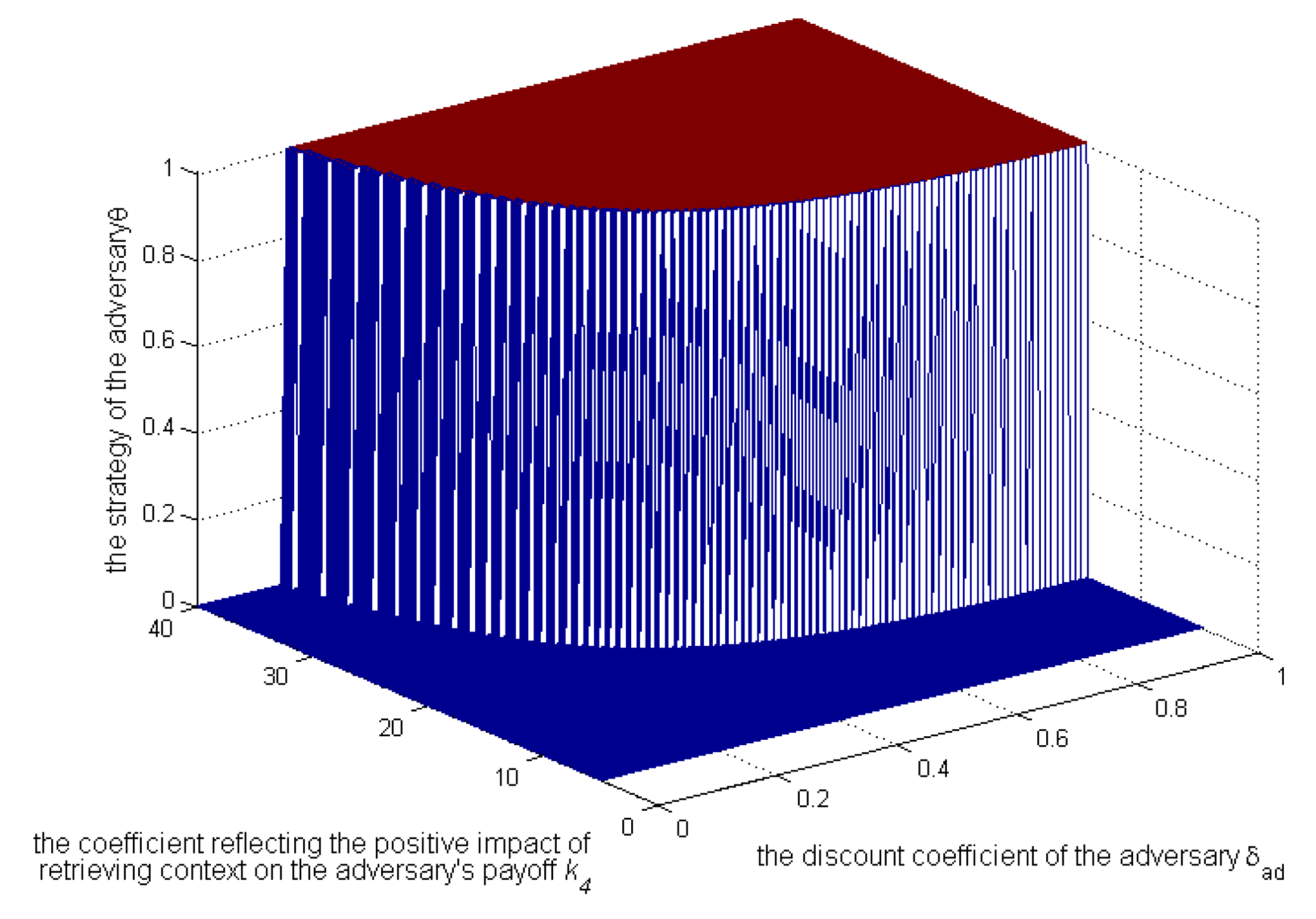
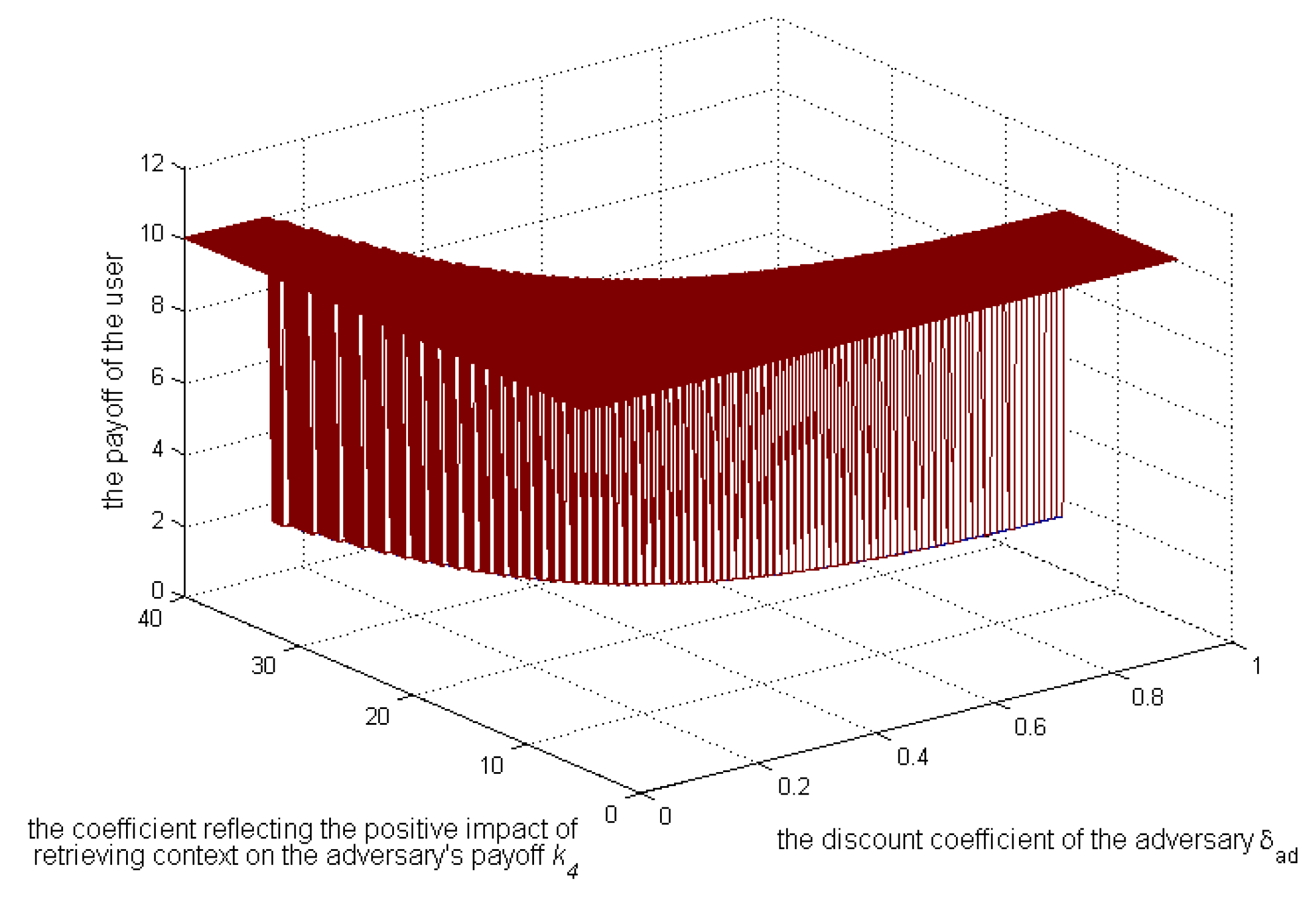
5.2. Numerical Analysis of the Repeated Game Model
6. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Götz, M.; Nath, S.; Gehrke, J. Maskit: Privately releasing user context streams for personalized mobile applications. In Proceedings of the 2012 ACM SIGMOD International Conference on Management of Data, Scottsdale, AZ, USA, 20–24 May 2012; pp. 289–300.
- Wang, W.; Zhang, Q. A stochastic game for privacy preserving context sensing on mobile phone. In Proceedings of the IEEE INFOCOM 2014—IEEE Conference on Computer Communications, Toronto, ON, Canada, 27 April–2 May 2014; pp. 2328–2336.
- Duan, Z.; Yan, M.; Cai, Z.; Wang, X.; Han, M.; Li, Y. Truthful Incentive Mechanisms for Social Cost Minimization in Mobile Crowdsourcing Systems. Sensors 2016, 16, 481. [Google Scholar] [CrossRef] [PubMed]
- Yang, P.; Cao, Z.; Dong, X.; Zia, T.A. An efficient privacy preserving data aggregation scheme with constant communication overheads for wireless sensor networks. IEEE Commun. Lett. 2011, 15, 1205–1207. [Google Scholar] [CrossRef]
- Wang, Y.; Cai, Z.; Yin, G.; Gao, Y.; Tong, X.; Wu, G. An incentive mechanism with privacy protection in mobile crowdsourcing systems. Comput. Netw. 2016, 102, 157–171. [Google Scholar] [CrossRef]
- Zhang, L.; Cai, Z.; Wang, X. FakeMask: A Novel Privacy Preserving Approach for Smartphones. IEEE Trans. Netw. Serv. Manag. 2016, 13, 335–348. [Google Scholar] [CrossRef]
- Groat, M.M.; He, W.; Forrest, S. KIPDA: K-indistinguishable privacy-preserving data aggregation in wireless sensor networks. In Proceedings of the 2011 Proceedings IEEE INFOCOM, Shanghai, China, 10–15 April 2011; pp. 2024–2032.
- Shin, M.; Cornelius, C.; Peebles, D.; Kapadia, A.; Kotz, D.; Triandopoulos, N. AnonySense: A system for anonymous opportunistic sensing. Pervasive Mob. Comput. 2011, 7, 16–30. [Google Scholar] [CrossRef]
- Vu, K.; Zheng, R.; Gao, L. Efficient algorithms for k-anonymous location privacy in participatory sensing. In Proceedings of the 2012 Proceedings IEEE INFOCOM, Orlando, FL, USA, 25–30 March 2012; pp. 2399–2407.
- Westhoff, D.; Girao, J.; Acharya, M. Concealed data aggregation for reverse multicast traffic in sensor networks: Encryption, key distribution, and routing adaptation. IEEE Trans. Mob. Comput. 2006, 5, 1417–1431. [Google Scholar] [CrossRef]
- Narayanan, A.; Thiagarajan, N.; Lakhani, M.; Hamburg, M.; Boneh, D. Location Privacy via Private Proximity Testing. In Proceedings of the Network and Distributed System Security Symposium, San Diego, CA, USA, 6–9 February 2011.
- Zhuang, J.; Bier, V.M. Balancing Terrorism and Natural Disasters—Defensive Strategy with Endogenous Attacker Effort. Oper. Res. 2007, 55, 976–991. [Google Scholar] [CrossRef]
- Kesete, Y.; Peng, J.; Gao, Y.; Shan, X.; Davidson, R.A.; Nozick, L.K.; Kruse, J. Modeling insurer-homeowner interactions in managing natural disaster risk. Risk Anal. 2014, 34, 1040–1055. [Google Scholar] [CrossRef] [PubMed]
- Peng, J.; Shan, X.G.; Gao, Y.; Kesete, Y.; Davidson, R.A.; Nozick, L.K.; Kruse, J. Modeling the integrated roles of insurance and retrofit in managing natural disaster risk: A multi-stakeholder perspective. Nat. Hazards 2014, 74, 1043–1068. [Google Scholar] [CrossRef]
- Shan, X.; Zhuang, J. Subsidizing to disrupt a terrorism supply chain: A four-player game. J. Oper. Res. Soc. 2014, 65, 1108–1119. [Google Scholar] [CrossRef]
- Shiyu, X. Economic Game Theory; Fudan University Publishing House: Shanghai, China, 2002; pp. 245–263. [Google Scholar]


| Play | |||||||
|---|---|---|---|---|---|---|---|
| Payoff | |||||||
| 0 | 0 | ||||||
| 0 | 0 | ||||||
| 0 | 0 | 0 | |||||
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license ( http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Wang, S.; Li, L.; Sun, W.; Guo, J.; Bie, R.; Lin, K. Context Sensing System Analysis for Privacy Preservation Based on Game Theory. Sensors 2017, 17, 339. https://doi.org/10.3390/s17020339
Wang S, Li L, Sun W, Guo J, Bie R, Lin K. Context Sensing System Analysis for Privacy Preservation Based on Game Theory. Sensors. 2017; 17(2):339. https://doi.org/10.3390/s17020339
Chicago/Turabian StyleWang, Shengling, Luyun Li, Weiman Sun, Junqi Guo, Rongfang Bie, and Kai Lin. 2017. "Context Sensing System Analysis for Privacy Preservation Based on Game Theory" Sensors 17, no. 2: 339. https://doi.org/10.3390/s17020339
APA StyleWang, S., Li, L., Sun, W., Guo, J., Bie, R., & Lin, K. (2017). Context Sensing System Analysis for Privacy Preservation Based on Game Theory. Sensors, 17(2), 339. https://doi.org/10.3390/s17020339





