TripSense: A Trust-Based Vehicular Platoon Crowdsensing Scheme with Privacy Preservation in VANETs
Abstract
:1. Introduction
- First, we establish the trust system based on Dirichlet distribution to evaluate the sensing accuracy of all sensing vehicles in our proposed TripSense scheme. The historical sensed data will be evaluated and finally form a reputation score. Therefore, the sensing accuracy will be improved greatly when the data are always collected from those high reputation sensing vehicles.
- Second, we propose the TripSense scheme by taking advantages of the unique features of vehicular platooning. In this scheme, platoon head vehicles firstly authenticate all sensing vehicles inside the platoon and then select some of them according to their trust values. Later, the sensed data from sensing vehicles will be collected and aggregated by platoon head vehicles before they are finally uploaded to the server. Compared with previous works, our proposed scheme reduces the communication overhead and hence is more suitable for the dynamic and ephemeral vehicular ad hoc network.
- Third, we design a privacy-preserving sensing vehicle selection scheme based on our trust system and a privacy-preserving data aggregation scheme based on the efficient commitment scheme in [13] such that platoon head vehicles can collect the data without leaking sensing vehicles’ privacy.
2. Problem Statement
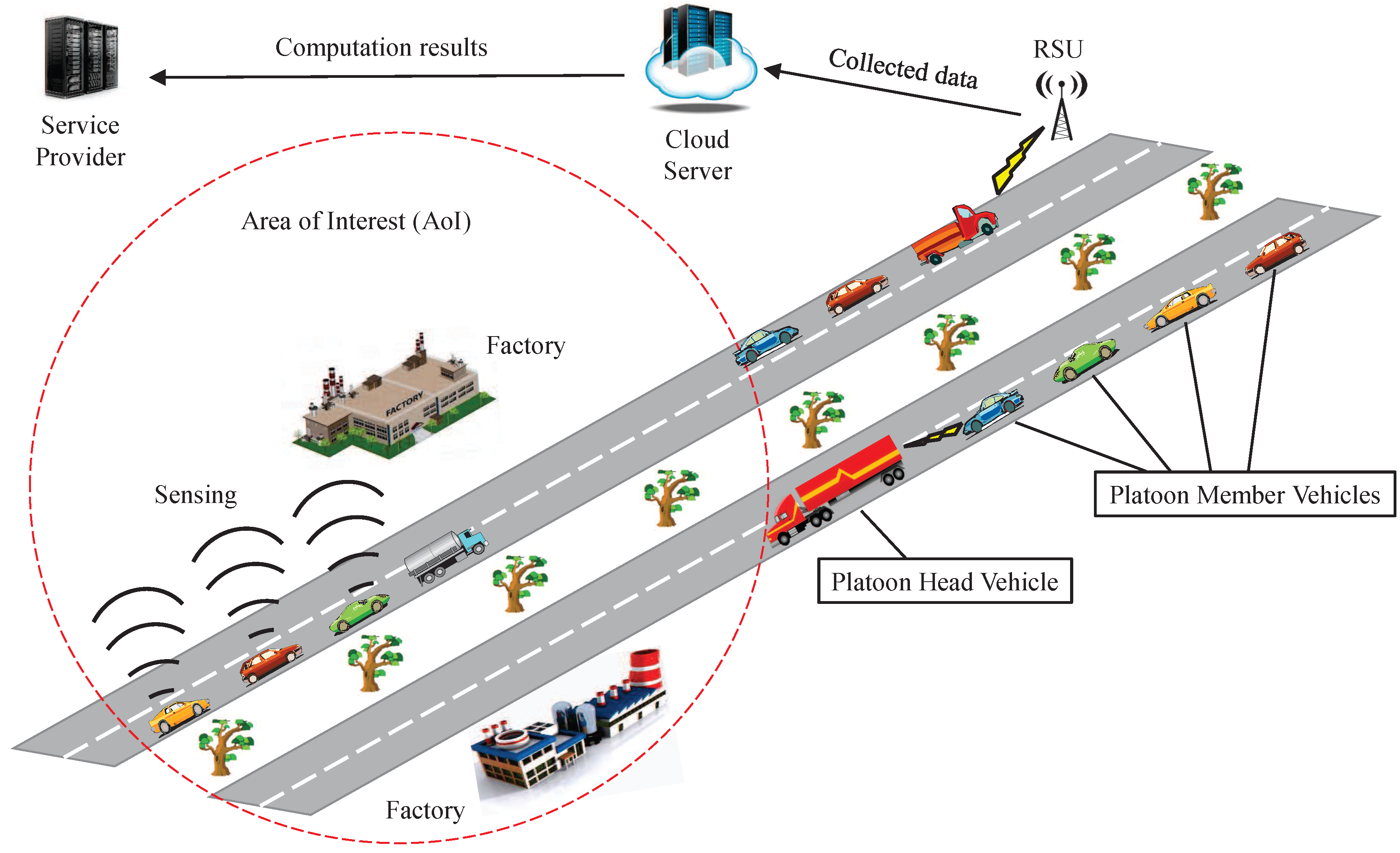
2.1. System Model
- Platoon Head (PH) Vehicles : PH vehicles take full control of the whole platoon when driving on the highway, and they are responsible for the safety and user experience of all platoon member vehicles. Apart from that, they also claim a sensing task and submit sensed data to RSUs through V-2-I communication. PH vehicles are also honest but curious about the privacy of platoon member vehicles. In fact, PH vehicles could be malicious and provide untruthful aggregated data to server in order to subvert the system, or they may even collude with a bunch of PM vehicles with the objective to victimize other PM vehicles. However, in this work, we do not consider this issue since it is not the main focus of this work.
- Platoon Member (PM) Vehicles : Each PM vehicle is equipped with various types of powerful sensors to meet the requirements of different tasks. Through V-2-V communication, a member vehicle authenticates itself and then submits its sensed data to the PH vehicles. Some of the PM vehicles are compromised by adversaries launch attacks, while other PM vehicles are all honest but curious.
2.2. Security Model
- Impersonation attack: The first kind of adversary may try to impersonate a PM vehicle to ask for a sensing task. However, this PM vehicle may not be qualified in the system. Once chosen to fulfill the task, these unqualified vehicles may submit inaccurate sensed data.
- Malicious sensing attack: The second kind of more capable adversary is able to control a small fraction of the vehicles in the system who submit inaccurate sensed data deliberately to subvert the system. Another possible case is that the PM vehicle is selfish, so it reports arbitrary data without using sensors to save power.
- Trust score association attack: PH vehicles are honest but curious, in this case, if the trust score of a PM is directly given to its PH vehicle, its driving pattern will be disclosed. As described in Section 1, the reason is because every time the PH vehicle can associate a PM vehicle in platoon according to the same trust score collected in different trips, even though the pseudo-id has been changed.
- Data analysis attack: Due to the curious characteristics of both PH vehicles and PM vehicles, they may eavesdrop on the transmission of sensed data and try to analyze the data. On the other hand, a cloud server (CS) is also curious about the sensed data. If the data is not encrypted, these attackers can easily analyze the data in transmission.
2.3. Design Goal
- Ensuring the sensed data reliability and accuracy. According to our adversary model, the existence of selfish and malicious vehicles who submit corrupted sensed data will make the final results inaccurate and unreliable. Hence, our proposed scheme should be able to improve the sensed data accuracy by excluding selfish and malicious vehicles’ data.
- Achieving privacy-preserving sensing vehicle selection, sensed data aggregation and evaluation. The proposed scheme should achieve privacy requirements of PM vehicles. Particularly, (i) the real identity of PM vehicles will never be disclosed; (ii) when a PM vehicle replies to the PH vehicle, the PH vehicle can never know the exact trust score of this PM vehicle; (iii) when a PH vehicle collects and aggregates the sensed data, it can never know what the data is; (iv) the CS can never know the aggregated sensed data and the evaluations on that data.
- Resisting against attacks launched by adversaries. The proposed scheme should also be secure and reliable in VANET. Once an outside adversary launches some attacks, e.g., impersonation attack or data analysis attack, the proposed scheme should be able to detect them.
3. Preliminaries
3.1. Bilinear Pairing
3.2. Beta Distribution
3.3. Dirichlet Distribution
4. Proposed TripSense Scheme
4.1. System Initialization
- SP first chooses a random number and uses to compute pseudo-IDs , where each pseudo-ID is computed as with a fresh random number . Then, for each , SP calculates its corresponding private key by and public key by . Finally, SP sends and the corresponding public and private keys back to via a secure channel.
- After receiving pseudo-IDs and their private keys, verifies the correctness of each private key by checking .
- For a registered PM vehicle with trust score , where , SP makes signatures for each of its pseudonyms as , where is the timestamp for updating the trust score of .
4.2. Trust-Based Privacy-Preserving Sensing Vehicle Selection
- Since the trust scores of PM vehicles are two decimal places, we need to expand them by 100 times before they can be encrypted. If ’s trust score is with trust level where , encrypts the expanded trust score as , with a fresh random number .
- Similarly, the sensed data are all collected and expanded by 100 times. For one category in , encrypts the expanded sensed data as , where is a random number in .
- chooses a pseudonym and a random element to calculate the following:
- randomly chooses , , and computes , .
- calculates the proofs as:
4.3. Privacy-Preserving Sensed Data Aggregation
4.4. Aggregated Sensed Data Retrieval
4.5. Privacy-Preserving Sensed Data Accuracy Evaluation
- SP encrypts the sensed result as: , where , and sends to CS.
- CS pairs the encrypted sensed data from and the inverse of encrypted sensed result, , as: . In the case that , CS also pairs the data as: . After calculation, CS passes the results together with the ’s pseudo-ID to SP.
- Upon receiving CS’s message, SP first finds the real identity of according to its pseudo-ID , then retrieves using the same method of exhaustion proposed in Section 4.4.
4.6. Dirichlet-Based Trust Management
5. Security Analysis
5.1. The Proposed TripSense Scheme Is Privacy-Preserving for PM Vehicles
- PM vehicle’s identity privacy and location privacy are preserved in the proposed TripSense scheme: In our proposed TripSense scheme, each PM vehicle uses pseudo-ID instead of a real identity in the network. Hence, the identity privacy can be achieved. In addition, to preserve the location privacy of the PM vehicle, changes its unlinkable pseudo-IDs at different trips and locations to ensure that its past and future trip and location information will not be linked by pseudo-IDs.However, as analyzed in Section 2.2, still suffers from trust score link attack. Thus, in our proposed scheme, when a PH vehicle checks whether its PM vehicle ’s trust score satisfies the task requirement, it uses discrete trust levels in place of accurate trust scores. In other words, can prove itself a highly trusted vehicle in front of without revealing its exact trust score. In addition, ’s trust score is encrypted as and its trust level is in PS’s signature , which makes it impossible for the other PM vehicles to get either ’s trust score or trust level.
- The sensed data privacy preservation is achieved: Once the sensed data are aggregated by a PM vehicle , they are encrypted as: . In the whole process of local aggregation and global aggregation, those data are all aggregated without decryption until SP is reached, where SP is able to recover with its private key p. Therefore, unless the other vehicles know the private key p, the sensed data information will never be disclosed.
5.2. The Proposed TripSense Scheme Achieves Robustness Against Attacks Launched by Adversary
- Resilience to malicious sensing attack: According to our proposed scheme, the selfish or malicious vehicles that submit arbitrary sensed data will get low evaluation scores in the trust system. Those low evaluation scores will be accumulated and finally lead to low trust scores if they keep behaving in that way. When their trust scores are lower than threshold , their sensed data will be excluded from data aggregation or they will be given a low weight in data aggregation due to low trust scores. In both ways, the attacker will be mitigated in our proposed scheme.
- Resilience to Trust Score Spoofing Attack: We assume that the majority of PM vehicles follow the scheme honestly, but we do not rule out a possibility that a small fraction of PM vehicles cheat PH vehicles by using the fake trust scores. There are two possible cases: one case is that the PM vehicle spoofs a higher trust score with the hope to participate in a sensing task. However, in this case, when is using pseudo-ID , ’s trust score is signed by SP as , where , , indicate the trust level, private key and updating timestamp, respectively. Therefore, without knowing the spoofed trust score ’s master key , is unable to launch attack. Another case is that provides a fake trust score after encryption as , . To deal with this type of attack, PH vehicle needs to check , it won’t hold once the original C and E are changed to and .
- Resilience to Impersonation Attack: Both PH vehicle and PM vehicle could be impersonated by unqualified vehicles that want to take part in the sensing tasks. Specifically, for an impersonated PM vehicle, it may submit false data and escape punishments; for a PH vehicle, it may collect sensed data without submitting to CS and render the sensed data results incomplete. However, this attack can be thwarted by our proposed scheme. In the initialization phase in Section 4.1, both PH and PM vehicles will be given a pair of private and public keys once they are registered. In Section 4.2, a PM vehicle first checks PH vehicle by checking before it accepts ’s sensing task requirement. The timestamp is used to resist against replay attack. Similarly, the PH vehicle also checks before accepting the sensed data from . As a result, our proposed TripSense scheme is resistant against impersonation attacks.
6. Performance Evaluation
6.1. Simulation Settings
6.2. Modeling the Sensing Behaviors of PM Vehicles
6.3. Simulation Results
6.3.1. Correctness
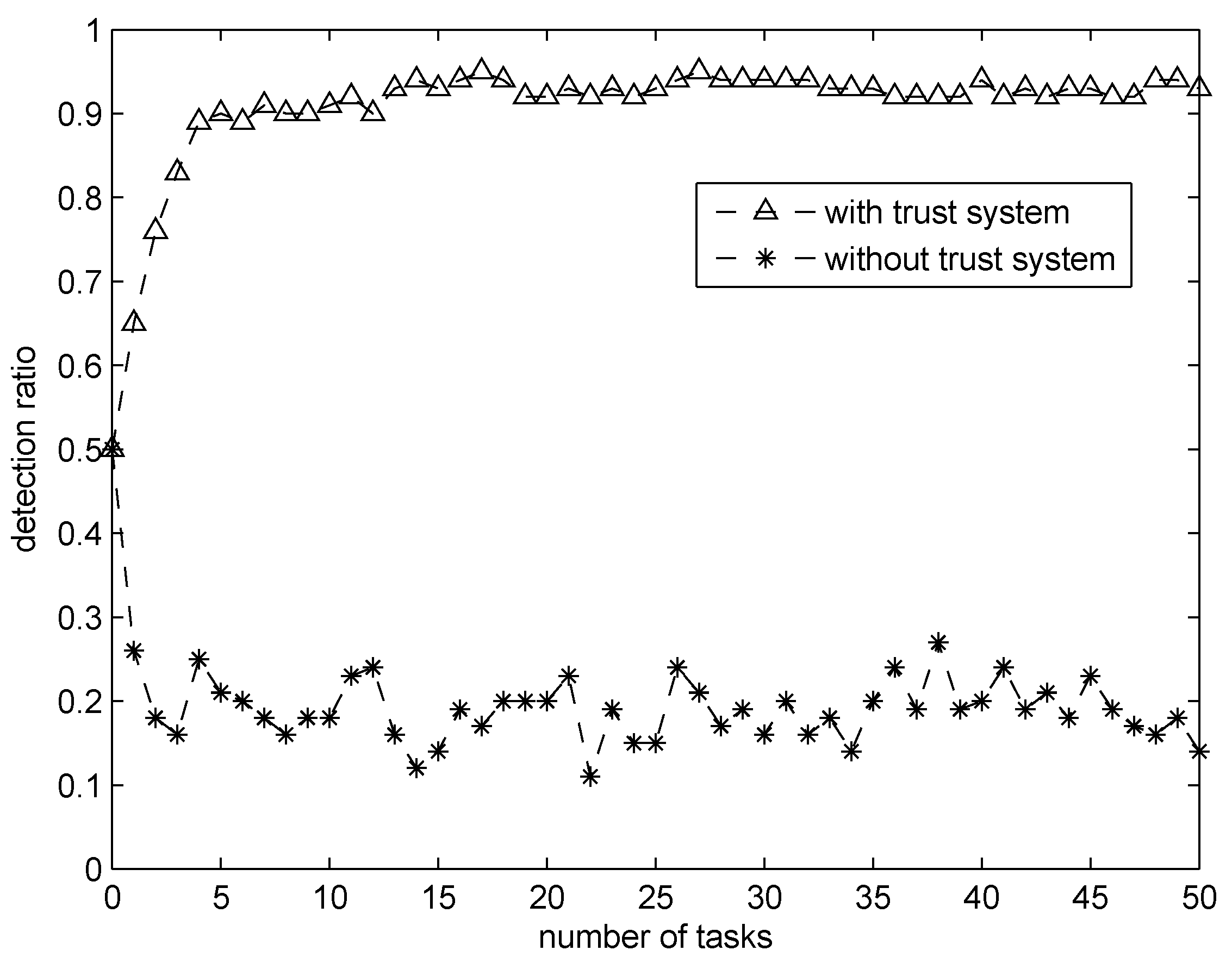
6.3.2. Effectiveness
7. Related Work
8. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Bergenhem, C.; Shladover, S.; Coelingh, E.; Englund, C.; Tsugawa, S. Overview of platooning systems. In Proceedings of the 19th ITS World Congress, Vienna, Austria, 22–26 October 2012.
- Hu, H.; Lu, R.; Zhang, Z.; Shao, J. Replace: A reliable trust-based platoon service recommendation scheme in vanet. IEEE Trans. Veh. Technol. (submitted). [CrossRef]
- Alam, A.A.; Gattami, A.; Johansson, K.H. An experimental study on the fuel reduction potential of heavy duty vehicle platooning. In Proceedings of the 13th International IEEE Conference on Intelligent Transportation Systems (ITSC), Funchal, Portugal, 19–22 September 2010; pp. 306–311.
- Guo, B.; Yu, Z.; Zhou, X.; Zhang, D. From participatory sensing to mobile crowd sensing. In Proceedings of the 2014 IEEE International Conference on Pervasive Computing and Communication Workshops, PerCom 2014 Workshops, Budapest, Hungary, 24–28 March 2014; pp. 593–598.
- Ganti, R.K.; Ye, F.; Lei, H. Mobile crowdsensing: Current state and future challenges. IEEE Commun. Mag. 2011, 49, 32–39. [Google Scholar] [CrossRef]
- Huang, K.L.; Kanhere, S.S.; Hu, W. Are you contributing trustworthy data: The case for a reputation system in participatory sensing. In Proceedings of the 13th International Symposium on Modeling Analysis and Simulation of Wireless and Mobile Systems, MSWiM 2010, Bodrum, Turkey, 17–21 October 2010; pp. 14–22.
- Wang, X.O.; Cheng, W.; Mohapatra, P.; Abdelzaher, T.F. Artsense: Anonymous reputation and trust in participatory sensing. In Proceedings of the IEEE INFOCOM 2013, Turin, Italy, 14–19 April 2013; pp. 2517–2525.
- Dua, A.; Bulusu, N.; Feng, W.-C.; Hu, W. Towards trustworthy participatory sensing. In Proceedings of the 4th USENIX Conference on Hot Topics (SecurityHotSec’ 09), Montreal, QC, Canada, 5 June 2009; p. 8.
- Lu, R.; Lin, X.; Luan, T.H.; Liang, X.; Shen, X.S. Pseudonym changing at social spots: An effective strategy for location privacy in vanets. IEEE Trans. Veh. Technol. 2012, 61, 86–96. [Google Scholar]
- Raya, M.; Hubaux, J.-P. Securing vehicular ad hoc networks. J. Comput. Secur. 2007, 15, 39–68. [Google Scholar] [CrossRef]
- Buttyán, L.; Holczer, T.; Vajda, I. On the effectiveness of changing pseudonyms to provide location privacy in vanets. In Security and Privacy in Ad-hoc and Sensor Networks; Springer: Cambridge, UK, 2007; pp. 129–141. [Google Scholar]
- Zhang, C.; Lin, X.; Lu, R.; Ho, P.; Shen, X. An efficient message authentication scheme for vehicular communications. IEEE Trans. Veh. Technol. 2008, 57, 3357–3368. [Google Scholar] [CrossRef]
- Arfaoui, G.; Lalande, J.F.; Traoré, J.; Desmoulins, N.; Berthomé, P.; Gharout, S. A practical set-membership proof for privacy-preserving NFC mobile ticketing. CoRR 2015, 2015, 25–45. [Google Scholar] [CrossRef]
- Jøsang, A.; Haller, J. Dirichlet reputation systems. In Proceedings of the The Second International Conference on Availability, Reliability and Security, Vienna, Austria, 10–13 April 2007; pp. 112–119.
- Jøsang, A.; Ismail, R. The beta reputation system. In Proceedings of the 15th bled electronic commerce conference, Bled, Slovenia, 17–19 June 2002; pp. 2502–2511.
- Fung, C.J.; Zhang, J.; Aib, I.; Boutaba, R. Dirichlet-based trust management for effective collaborative intrusion detection networks. IEEE Trans. Netw. Serv. Manage. 2011, 8, 79–91. [Google Scholar] [CrossRef]
- Sun, Y.L.; Han, Z.; Yu, W.; Liu, K.J.R. A trust evaluation framework in distributed networks: Vulnerability analysis and defense against attacks. In Proceedings of the 25th IEEE International Conference on Computer Communications INFOCOM 2006, Joint Conference of the IEEE Computer and Communications Societies, Barcelona, Catalunya, Spain, 23–29 April 2006.
- Zhang, J. A survey on trust management for vanets. In Proceedings of the 25th IEEE International Conference on Advanced Information Networking and Applications, AINA 2011, Biopolis, Singapore, 22–25 March 2011; pp. 105–112.
- Patwardhan, A.; Joshi, A.; Finin, T.; Yesha, Y. A data intensive reputation management scheme for vehicular ad hoc networks. In Proceedings of the 3rd Annual International ICST Conference on Mobile and Ubiquitous Systems: Computing, Networking and Services, MOBIQUITOUS 2006, San Jose, CA, USA, 17–21 July 2006; pp. 1–8.
- Raya, M.; Papadimitratos, P.; Gligor, V.D.; Hubaux, J.-P. On data-centric trust establishment in ephemeral ad hoc networks. In Proceedings of INFOCOM 2008. 27th IEEE International Conference on Computer Communications, Joint Conference of the IEEE Computer and Communications Societies, Phoenix, AZ, USA, 13–18 April 2008.
- Hu, H.; Lu, R.; Zhang, Z. Tpsq: Trust-based platoon service query via vehicular communications. Peer-to-Peer Netw. Appl. (submitted). [CrossRef]
- Xing, K.; Wan, Z.; Hu, P.; Zhu, H.; Wang, Y.; Chen, X.; Wang, Y.; Huang, L. Mutual privacy-preserving regression modeling in participatory sensing. In Proceedings of the IEEE INFOCOM 2013, Turin, Italy, 14–19 April 2013; pp. 3039–3047.
- He, W.; Liu, X.; Nguyen, H.; Nahrstedt, K.; Abdelzaher, T.F. PDA: Privacy-preserving data aggregation in wireless sensor networks. In Proceedings of the 26th IEEE International Conference on Computer Communications, Joint Conference of the IEEE Computer and Communications Societies, Anchorage, AK, USA, 6–12 May 2007; pp. 2045–2053.
- Bilogrevic, I.; Freudiger, J.; De Cristofaro, E.; Uzun, E. What’s the gist? Privacy-preserving aggregation of user profiles. In Proceedings of the Computer Security—ESORICS 2014—19th European Symposium on Research in Computer Security, Wroclaw, Poland, 7–11 September 2014; pp. 128–145.
- Burke, J.A.; Estrin, D.; Hansen, M.; Parker, A.; Ramanathan, N.; Reddy, S.; Srivastava, M.B. Participatory sensing. In Proceedings of the International Workshop on World-Sensor-Web (WSW’2006), Boulder, CO, USA, 31 October 2006.
- Yu, B.; Gong, J.; Xu, C. Catch-up: A data aggregation scheme for vanets. In Proceedings of the Fifth International Workshop on Vehicular Ad Hoc Networks, VANET 2008, San Francisco, CA, USA, 15 September 2008; pp. 49–57.
- Lochert, C.; Scheuermann, B.; Mauve, M. Probabilistic aggregation for data dissemination in vanets. In Proceedings of the Fourth International Workshop on Vehicular Ad Hoc Networks, VANET 2007, Montréal, QC, Canada, 10 September 2007; pp. 1–8.


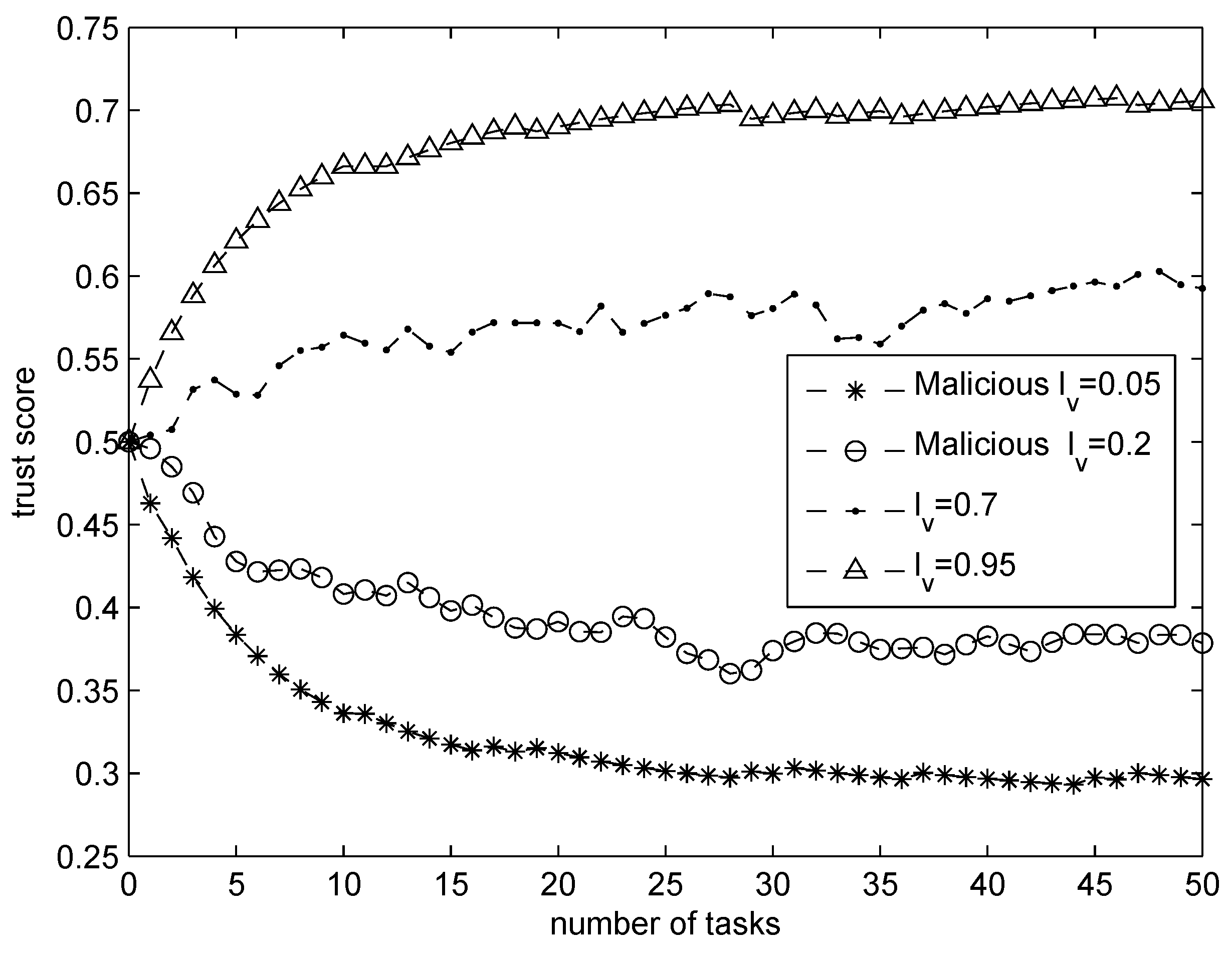
| Notation | Definition | Value |
|---|---|---|
| n | registered PM vehicle number | 500 |
| ρ | malicious PH vehicle proportion | 20% |
| sensing accuracy level (SAL) | 0.05; 0.2; 0.7; 0.95 | |
| m | number of tasks for each PM vehicle | 50 |
| initial belief weight | 1 | |
| forgetting factor parameter | 1 | |
| variance sensitivity | 10 | |
| forgetting factor parameter | 1 | |
| initial trust score | 0.5 |
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hu, H.; Lu, R.; Huang, C.; Zhang, Z. TripSense: A Trust-Based Vehicular Platoon Crowdsensing Scheme with Privacy Preservation in VANETs. Sensors 2016, 16, 803. https://doi.org/10.3390/s16060803
Hu H, Lu R, Huang C, Zhang Z. TripSense: A Trust-Based Vehicular Platoon Crowdsensing Scheme with Privacy Preservation in VANETs. Sensors. 2016; 16(6):803. https://doi.org/10.3390/s16060803
Chicago/Turabian StyleHu, Hao, Rongxing Lu, Cheng Huang, and Zonghua Zhang. 2016. "TripSense: A Trust-Based Vehicular Platoon Crowdsensing Scheme with Privacy Preservation in VANETs" Sensors 16, no. 6: 803. https://doi.org/10.3390/s16060803
APA StyleHu, H., Lu, R., Huang, C., & Zhang, Z. (2016). TripSense: A Trust-Based Vehicular Platoon Crowdsensing Scheme with Privacy Preservation in VANETs. Sensors, 16(6), 803. https://doi.org/10.3390/s16060803






