Analysis of Latency Performance of Bluetooth Low Energy (BLE) Networks
Abstract
: Bluetooth Low Energy (BLE) is a short-range wireless communication technology aiming at low-cost and low-power communication. The performance evaluation of classical Bluetooth device discovery have been intensively studied using analytical modeling and simulative methods, but these techniques are not applicable to BLE, since BLE has a fundamental change in the design of the discovery mechanism, including the usage of three advertising channels. Recently, there several works have analyzed the topic of BLE device discovery, but these studies are still far from thorough. It is thus necessary to develop a new, accurate model for the BLE discovery process. In particular, the wide range settings of the parameters introduce lots of potential for BLE devices to customize their discovery performance. This motivates our study of modeling the BLE discovery process and performing intensive simulation. This paper is focused on building an analytical model to investigate the discovery probability, as well as the expected discovery latency, which are then validated via extensive experiments. Our analysis considers both continuous and discontinuous scanning modes. We analyze the sensitivity of these performance metrics to parameter settings to quantitatively examine to what extent parameters influence the performance metric of the discovery processes.1. Introduction
Bluetooth Low Energy (BLE) is a new wireless communication technology for short-range communication with enhanced low-cost and low-power properties. A major and fundamental change has been made in the BLE radio architecture to enable short-range communication in BLE [1–4]. BLE has a very low power consumption rate with a similar communication range. Devices that use BLE for communication are normally powered by coin-cell batteries and it can be operated for months and even for years [1,2].
BLE technology provides support of novel data transfer functionality and hence it can be used in sensor technologies for transmitting bulk data [3]. The BLE technology offers a more advanced and robust connectivity by re-establishing the connections with the devices once they come back into the range of each other. This novel data transfer functionality make BLE more favorable for short-range communication in wireless sensor networks.
Recently, most technologies are using the ISM band for communication and hence it has become more congested and crowded, therefore, BLE uses a frequency-hopping mechanism in both its advertising and data channels to avoid congestion during communication. The classical Bluetooth has 79 channels, each of which has a width of 1 MHz, while the BLE is designed to operate on 2.4 GHz ISM band using 40 channels, each with a width of 2 MHz. Out of these 40 channels, three channels, that is channels number 37, 38, and 39, are used for broadcasting purposes, i.e., device discovery, etc., and the remaining 37 channels are responsible for data transmission. The device discovery process is more simplified by designing a concise state-machine which also helps in supporting the power saving functionality [3,5].
These properties of BLE make it more favorable for short-range communication technologies. The Bluetooth Special Interest Group (SIG) recommended a number of markets for BLE technology such as Body Area Networks (BAN) and Internet of Things (IoT), these includes automotive, consumer electronics, health issues and wellness, sports activities and fitness, and smart homes [6].
Since BLE is developed for these short-range wireless applications, a fast and convenient discovery process becomes as one of the important feature which can be addressed and attached to the existing BLE technologies. The BLE standard clearly elaborated and published the communication process but many areas still need to be studied and researched such as the device discovery latency and energy efficiency of the system [4]. The BLE technology recommended a wide range of parameter settings for the device discovery mechanism and its proper tuning to balance and optimize the performance for a wide range of applications in context of latency and energy consumption [3].
Keeping these challenges in mind, this paper focuses on the discovery process of BLE networks, and an analytical model is proposed to investigate the discovery probability, as well as expected discovery latency, which are then validated via extensive simulation experiments. In addition, we also analyze the sensitivity of those performance metrics to quantitatively evaluate to what extent parameter setting would influence the performance metrics.
The rest of this paper is organized as follows: related work covering the classical Bluetooth standards and BLE device discovery process is presented in Section 2. A comprehensive detailed overview of BLE and its discovery mechanism are provided in Section 3. An analytical model for the BLE process is presented in Section 4. Section 5 validates our model, and finally conclusions are given in Section 6.
2. Related Works
Recently, the device discovery performance of classical Bluetooth protocols has been intensively investigated through real time experiments, simulations, and formal modeling methods [3]. The related work section is further divided into two parts, the first part explaining the performance evaluation of classical Bluetooth networks and second part explains the device discovery process of BLE in detail.
A detailed analysis on device discovery performance for classical Bluetooth Version 1.1 and 1.2 has been presented in [7]. The probabilistic model checking technique and the PRISM tool were used to compute the performance bounds of device discovery in terms of the mean time and the mean power consumption [3]. Their study has proved that a low-level analysis can produce exact results like those derived from simulation techniques, but if the analysis is performed on a high number of nodes it can produce insignificant results and thus it can be applied in a congested environment.
A comprehensive experiment on real devices, exploring the parameter space to determine the relationship between parameter settings and mean discovery latency or power consumption values has been proposed in [8]. An algorithm is proposed to adaptively determine parameter settings, depending on a mobility context to reduce the mean power consumption for Bluetooth devices. The tradeoff between different parameters is not clearly explained. It looks like that by increasing the value of one parameter a significant change can be seen in another parameter. Thus the work proposed in that research cannot be applied to the next generation networks like IoT and BAN. Similarly, a simulative study on device discovery in multi-hop Bluetooth networks, i.e., Bluetooth Scatternet, by means of classical Bluetooth inquiry procedure has been addressed in [9]. Different types of experiments were performed to show that even though it required a long time for each node to become aware of all its neighbors, the Bluetooth topologies can be obtained in about 6 s after the connection setup through those discovered devices [3]. This amount of time is very high for applications where a fast topology construction is important.
In [10], the authors implemented an end-to-end Bluetooth-based mobile service framework. The framework relied on machine-readable visual tags for out-of-band device and service selection rather than using the standard Bluetooth device discovery model to detect nearby mobile services. Their work demonstrated that a tag-based connection establishment technique could offer significant improvements over the standard Bluetooth device discovery model. Although there have been intensive studies presented for classical Bluetooth device discovery, but unfortunately, these studies cannot be applied to BLE, since the Bluetooth standard made a fundamental change in the device discovery mechanism of BLE. Very little research work related to the performance evaluation of the BLE discovery process has been published. Some literature covering the BLE discovery mechanism is reviewed in the following section.
An analytical model for device discovery in BLE networks by developing a new BLE extension accounting for all the protocols based on original Bluetooth and its validation through simulation results in NS-2 was proposed in [3]. They compared the analytical results with those obtained through simulation [3]. Since intermittent connections are frequently encountered in practical BLE scenarios, the modeling results can provide a beneficial guidance to customize the advertising or scanning behavior towards the required performance [5]. The model can be used to determine some important performance metrics, such as mean latency or mean energy consumption during the course of discovering neighbors, but many parameters and metrics bust bed define and tested for the implementation of said proposed scheme in real world scenarios.
In [11], the authors introduced an analytical model, based on classical ALOHA analysis, to investigate two metrics, such as discovery latency and connection setup latency, in WBAN applications. The probability of successful device discovery was also computed. They studied the performance of BLE device discovery, particularly with multiple devices. The average latency of device discovery is given by:
In [3], the authors focused on the modeling and performance of the device discovery process in BLE networks. A general model for device discovery in multi-channel scenarios was proposed primarily, and then the model was tailored and simplified for the BLE network with three broadcasting channels. The average discovery latency was derived through theoretical analysis. They revealed that improper parameter settings can significantly deteriorate the device discovery latency and increase meaningless energy consumption. They consequently proposed a solution to adaptively reduce the discovery latency when encountering an exceptionally long delay to be discovered by any scanner. Based on that, they devised three different strategies which significantly enhanced the latency performance regarding to the parameter settings. Through extensive simulation, they validated the accuracy of the model, showing the effectiveness of their strategies in overcoming the traps of the standard towards fast and efficient device discovery in BLE networks.
The previous studies on BLE discovery are still far from thorough. Since intermittent device discovery is commonplace in BLE networks, it is important to know to what extent parameter setting would influence the discovery process [3,4,7]. In fact, wide-range settings of the parameters provide new features for BLE devices to customize their performance in specific applications [2,5,11]. In other words, an advertiser should be capable of selecting appropriate parameters that meet the requirements for practical BLE networks. It is thus necessary to develop a new, accurate discovery model for existing BLE architectures. This motivates our study of modeling the discovery process of BLE and performing an intensive simulative evaluation.
3. Background of BLE Discovery
3.1. Operation of BLE
A BLE device may operate in three different modes depending on required functionality: advertising, scanning and initiating, as shown in Figure 1. A device in advertising mode, named advertiser, periodically transmits advertising information in three advertising channels (index = 37, 38, 39) [3]. As shown in Figure 1a, an advertiser keeps sending ADV_IND Packet Data Units (PDUs) in sequence over each of the three advertising channels in advertising event, which is composed by a fixed AdvInterval (hereafter denoted by τAI) and a pseudo-random AdvDelay (hereafter denoted by δ) generated by the Link Layer [2,3]. The random variety AdvDelay to the advertising interval is used to separate the advertisement interval when two or more advertisers are getting close [3]. Since BLE advertisers set the time randomly between consecutive advertising PDUs, advertisings on the three channels become completely asynchronous, then the successful advertising probability will reach an optimum value [3,11]. If all advertisers are set with the same advertising interval between consecutive advertising PDUs, then collisions on the first channel will pass to the second and the third channels [3,11].
Generally, there are two kinds of advertising events for BLE: undirected and directed. The undirected advertising event contains ADV_IND, which is used for detecting unknown devices yet allows different responses [11]. Different from undirected events, the directed advertising event is used for establishing connections with already known devices. It contains just one PDU type ADV_DIRECT_IND, and has no defined random delay between advertising events [11]. According to the standard, the AdvInterval should be an integer multiple of 0.625 ms in the range of 20 ms to 10.24 s, the AdvDelay should be within the range of 0 ms to 10 ms. According to the specification, an advertisement period for each channel (denoted by τWA) shall be less than or equal to 10 ms [11]. After each sending of the advertising packets, the advertiser will be listening on the same channel for a while to check if there is a response coming from any scanner [4].
On the other hand, a BLE device in scanning mode, named scanner, periodically scans the advertising channels and listens to advertising information of advertisers [5]. On receiving an advertising channel packet, the scanner will send back a response. As shown in Figure 1b, by each ScanInterval (denoted by τSI) the scanner scans on a different advertising channel for the duration of ScanWindow (denoted by τSW) [5]. According to the standard, the ScanInterval and ScanWindow should be less than or equal to 10.24 s. Table 1 shows the list of major timing parameters specified in BLE standard.
The scanner shares a similar process except that they can only respond to specific types of advertising packets. For example, the scanner responds to ADV_SCAN_IND PDU by transmitting a SCAN_REQ to request additional information of the advertiser. If the advertiser receives a SCAN_REQ that contains its device address from a scanner allowed by the advertising filter policy, it shall reply with SCAN_RSP PDU on the same advertising channel index [2,5]. Hereinafter, however, we generically refer to both ADV_SCAN_IND and ADV_DIRECT_IND just as “ADV_IND” since the distinction between them is irrelevant to our analysis. In addition, since multiple scanners may respond to an advertiser simultaneously, back-off procedures are used by each scanner to minimize collision [5].
3.2. Types of BLE PDU
Some details about packets related to discovery are presented in terms of the format and the length, which are important factors for discovery analysis. A BLE link layer packet has four components: preamble, access address, PDU and Cyclic Redundancy Check (CRC). The PDU has different types, and is further composed of a header and a payload. The packet length is decided by the length of the payload, ranging from 0 octets to 37 octets [3].
As previously described, the advertiser sends an ADV_IND over each advertising channel and is listening on the same channel to respond to SCAN_REQ from any scanner. The scanning procedure is defined as an operation where the scanner replies a SCAN_REQ PDU upon receiving an ADV_IND from the advertiser on the same advertising channel. The time needed for handshaking control messages in the scanning procedure is denoted by TS (=TSCAN_REQ + TSCAN_RSP + 2TIFS) as shown in Figure 2. Figure 2 shows the list of PDU transmission times and handshaking times for exchanging control messages between the advertiser and the scanner for device discovery, which are derived from the length of each PDU over bit rate (1 Mbps).
4. Analytical Model
We investigate the performance of the BLE device discovery from the perspective of theoretical model in full accordance with the BLE specification to investigate performance metrics. We first present an analytical model for the probability of device discovery, which will be used as a basis to derive an analytical model for mean discovery latency. The sensitivity index is evaluated to what extent parameter settings influence those performance metrics. The proposed analytical analysis is derived on investigating the cases where a particular pair of the advertiser and scanner (called A1 and S1) successfully discover each other and establish a connection between them. Different from other wireless networks, BLE exploits three advertising channels and employs tiny-sized frames, and advertisers do not examine the channel state before transmission, that is, the medium is accessed in a completely unsynchronized manner [4].
According to BLE standard, an advertiser sends an ADV_IND at the beginning of each advertising period (denoted by τWA) per advertising channel. The advertiser changes its advertising channel in a circular way (37→38→39→37…) with a period of τWA, and the scanner also changes its scanning channel in the same way every ScanInterval (with a period of τSI). We consider both continuous and discontinuous scanning modes to build analytical models. In the continuous scanning mode, BLE device scans each advertising channel without sleeping (therefore, τSW = τSI) as shown in Figure 3. On the contrary, the discontinuous scanning refers to a mode in which BLE device alternatively repeats scanning and sleeping every ScanInterval. So, τSW should be shorter than τSI in the discontinuous scanning mode as illustrated in Figure 3. We introduce a duty cycle to express how long a BLE device spends time on scanning process during a given ScanInterval. The duty cycle is defined as the proportion of time during which a BLE device is waking up for scanning, and is denoted by ρ = τSW/τSI. There is no doubt that 0 ≤ ρ ≤ 1. In particular, ρ becomes equal to one in the continuous scanning mode.
It should be noted that τWA is usually much longer than the handshaking time needed to exchange control packets for discovery. For example, the advertiser spends about 0.6 ms to exchange SCAN_REQ and SCAN_RSP between any scanner on each advertising channel for device discovery, so we can assume that the advertiser A1 has enough time to exchange control packets after sending an ADV_IND to successfully discover S1 and establish a connection.
4.1. Probability of Successful Discovery
We define six events to clearly express under what conditions advertiser A1 can successfully discover S1, as listed in Table 2. Using these events, we can derive situations where A1 can successfully discover S1.
4.1.1. 1:1 Network
In order to clearly elaborate the proposed analytical model, considering a network, in which one device acts as an advertiser and other works as a scanner. For successful discovery, the advertiser should rendezvous with the scanner at one of three advertising channels (37, 38, and 39). This case can be expressed by E1 ∩ E4 using events in Table 2.
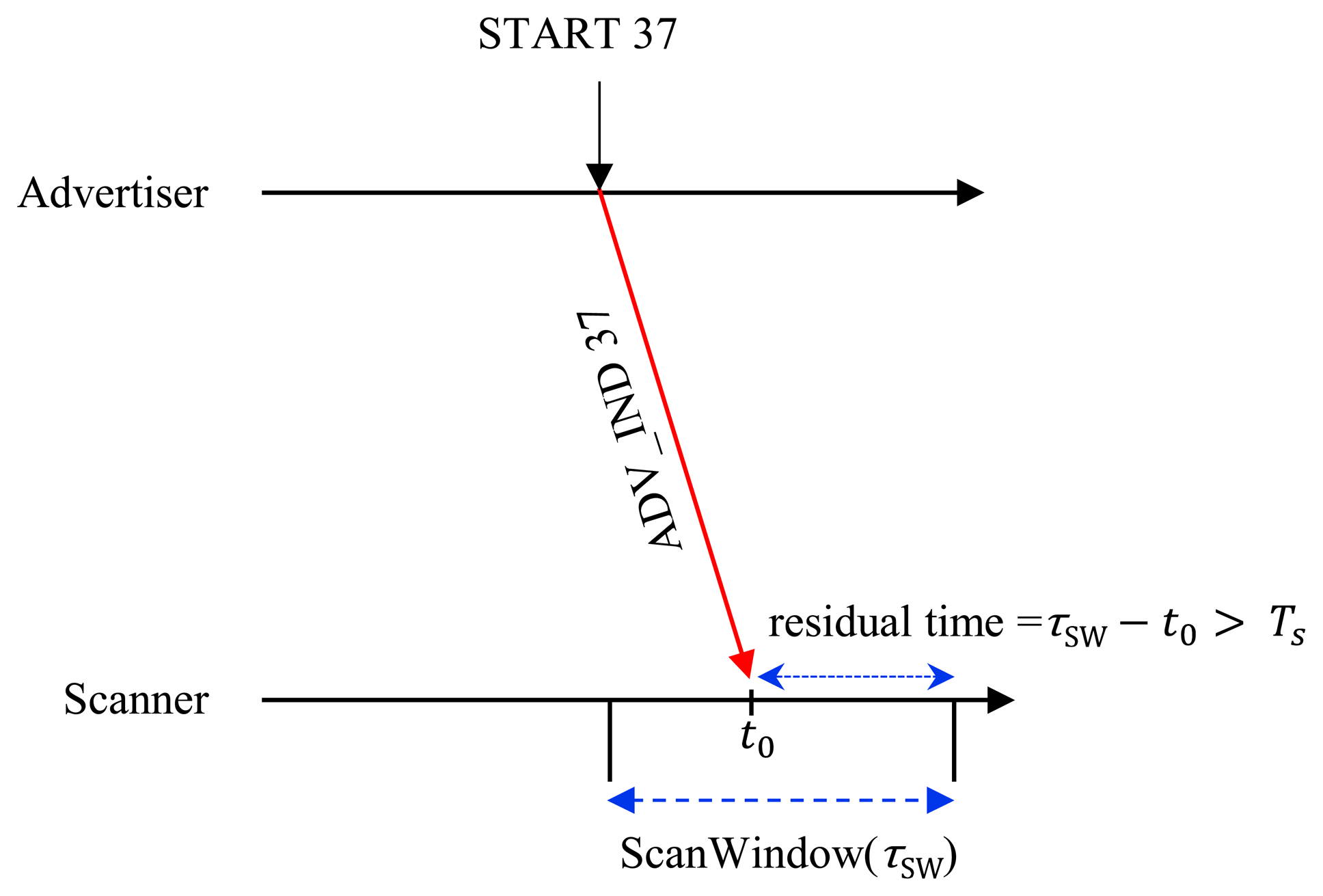
At the same time, the scanner should have a sufficient residual time to interact with the advertiser by handshaking of control messages after receiving an ADV_IND, so the advertiser can successfully discover the scanner if the following case is satisfied as shown in Figure 4.
The probability that the scanner rendezvous with the advertiser on receipt of the first ADV_IND is given by is the probability of selecting a specific channel out of three channels (37, 38 and 39). Assuming that the scanner receives the first ADV_IND at an arbitrary time instance of t0, the residual time until completion of ScanWindow is given by (τSW − t0). For successful discovery, the scanner should reply to ADV_IND with a SCAN_REQ message and should receive a SCAN_RSP from the advertiser within the residual time. In other words, the scanner should have a sufficient residual time greater than TS (=TSCAN_REQ + TSCAN_RSP + 2TIFS) until completion of ScanWindow for exchanging control messages with the advertiser. The probability that there is sufficient residual time is given by under assumption of continuous scanning scenario. So, we have the probability of successful discovery on the first advertising channel α1,by:
Since the advertiser sends another ADV_IND on the next advertising channel after a duration of τWA, the scanner receives the second ADV_IND att0 + τWA, so, the residual time for the second ADV_IND until completion of ScanWindow is (a τSI + τSW − t0 − τWA) where (⌊x⌋ means the largest integer not greater than x) as shown in Figure 4. The probability that the scanner has enough time for handshaking control messages for the second ADV_IND until completion of ScanWindow is given by . Since the probability that the scanner rendezvous with the advertiser on receipt of the second ADV_IND is given by , we have the probability of discovery successful on the second advertising channel by:
Similarly, the arrival time of the third ADV_IND at the scanner is t0 + 2τWA, and thus the residual time for the third ADV_IND until completion of the ScanWindow is given by (bτSI + τSW − t0 − 2τWA) where . Thus, we have the probability of discovery successful on the third advertising channel by:
We can rewrite Equations (1)–(3) into a more compact form as follows:
If τSI = τWA, we can see that α1 = α2 = α3 from Equation (4).
4.1.2. 1:2 Networks
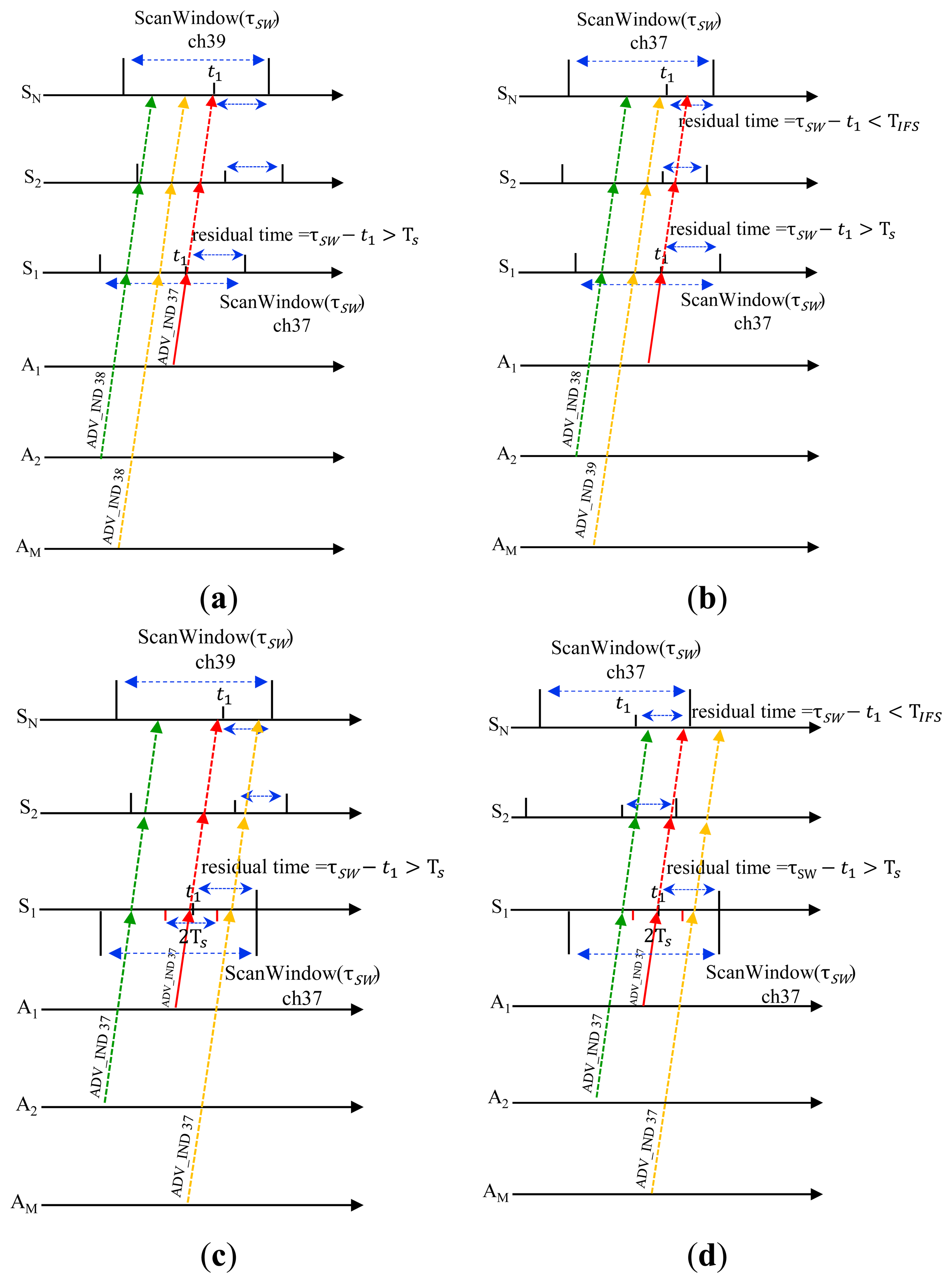
Assume that there are three BLE devices in the network, and one device acts as an advertiser and the other two (called S1 and S2) work as scanners. In this case, the advertiser can successfully discover the scanner S1 if one of the following cases is satisfied as shown in Figure 5:
We can easily get the probability of case 2 by:
The advertiser and two scanners can rendezvous at one of three advertising channels with a probability of . The probability that only S1 has a sufficient residual time for handshaking control messages is given by . And, the probability that S2 cannot send any message since its residual time is shorter than TS is given by . So, we get the probability of case 3 by:
Now, we have:
4.1.3. M:N Network
Now, we inspect a more general case for a network with (N+M) BLE devices, where M devices (called A1, A2, …, AM) act as advertisers and the other N devices (called S1, S2, …, SN) work as scanners. In this case, the advertiser A1 can successfully discover S1 if one of four cases shown in Figure 6 is satisfied.
In the same way as previously, we get:
Summing Equations (8)–(11), we have the probability of successful discovery on the first advertising channel by:
The above equation becomes identical to Equation (4), by substitute M = 1 and N = 1, respectively, in Equation (12). Similarly, we can get the probability of successful discovery on the second and third advertising channel, respectively, by
4.2. Expected Discovery Latency
The discovery latency is defined as the interval for the advertiser from entering into the first advertising event by sending an ADV_IND until it successfully receives a SCAN_REQ from the scanner as illustrated in Figure 7. The time to successful discovery depends on the number of failures experienced in attempts during the discovery process as shown in Table 3, where α1, α2, α3 means the probability of successful discovery on the first, the second, and the third advertising channel, respectively, as previously discussed.
From Table 3, we can get the expected discovery latency, denoted by πD, by:
Using algebra , we get:
The expected discovery latency of M:N networks can be determined using Equation (13) respectively, by substituting the corresponding probability of successful discovery in Equation (15).
4.3. Sensitivity Analysis
In order to investigate to what extent parameter setting influences the performance metrics, The sensitivity index (SQ,x) is defined as follows:
By substitution of τSW with τSW(1 + γ) and subtraction in Equation (13), we can get Δα1 by:
Thus, the sensitivity of discovery probability (Sα1,SW) becomes:
We can also find the sensitivity of the expected discovery latency to τAI in M:N network using Equations (13) and (15):
Similarly, the sensitivity of the expected discovery latency to other parameters is obtained such as τSW and τWA in M:N network using Equations (13) and (15), but we do not present the final expressions of SD,SW and SD,WA since they have very complicated forms since α1, α2, α3 are functions of τSW and τWA as seen in Equation (13).
5. Simulation Validation
In order to validate the analytical models, we have developed a BLE simulation program which fully complies with the BLE specification. The simulative settings are in accordance with the standard definition as previously described, and we compare the analytical results with those obtained via simulations. We simulate over 10 times for each scenario to get the average results, where parameter settings are selected with values listed in Table 4.
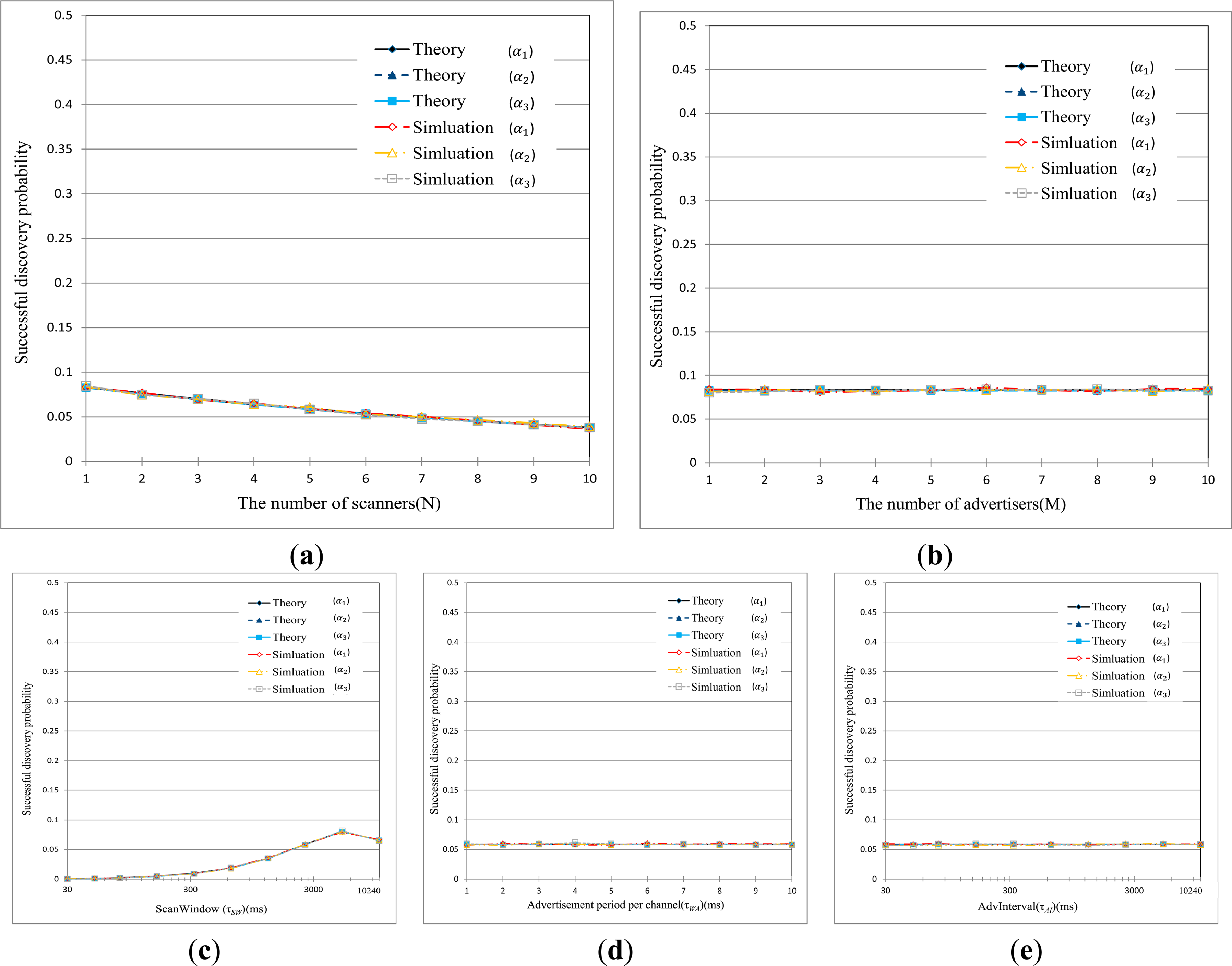
Figures 8 show the results of performance evaluation relating to the discovery probability, respectively, in terms of different sets of parameters such as τAI, τWA, and τSW in BLE network. The graphs are obtained by varying one parameter while setting the other two parameters to their default values listed in Table 4. From these figures, it is first found the theoretical curves practically coincide with the simulation results over the entire range of parameters. We can see that the discovery probability is very low, although there are not so many devices in the network. For example, the scanner experiences the success probability of about 0.3 in discovering process in even 1:1 network, which is totally different from the behavior of other wireless networks. This is because BLE devices can be synchronized with one of three advertising channels with a probability of 1/3 to discover each other. Further, as the number of devices increases in the network, the discovery process fails more frequently due to collision of the abundant control packets, such as SCAN_REQ, SCAN_RSP, during discovery process.
It can be seen from following graphs, the discovery probability is somewhat comparatively affected by τWA and τSW. The scanning duration is only dependent on τSW and the number of scans per advertisement is determined by the ratio of τSW to τWA. As τSW increases, the probability that the scanner successfully discovers the advertiser increases very gradually when τSW < 100 ms, and remains almost constant when τSW exceeds 100 ms. This is because the scanner can stay a long time on each channel for scanning in spite of decreasing number of scans as τSW is increased. So, we can say that the scanner loses many chances of device discovery if τSW is shorter than the expectation needed by the advertiser. In particular, if τWA = τSW, α2 and α3 becomes identical to α1 which implies that discovery on the first channel will pass to the second and the third channel.
On the contrary, the discovery probability is not affected by τAI since this parameter influences neither scanning duration nor the number of scans. Instead, τAI is only used to determine when the advertiser initiates the next advertisement process. Figures 8 indicates that inappropriately setting of parameters significantly deteriorates the successful device discovery, respectively.
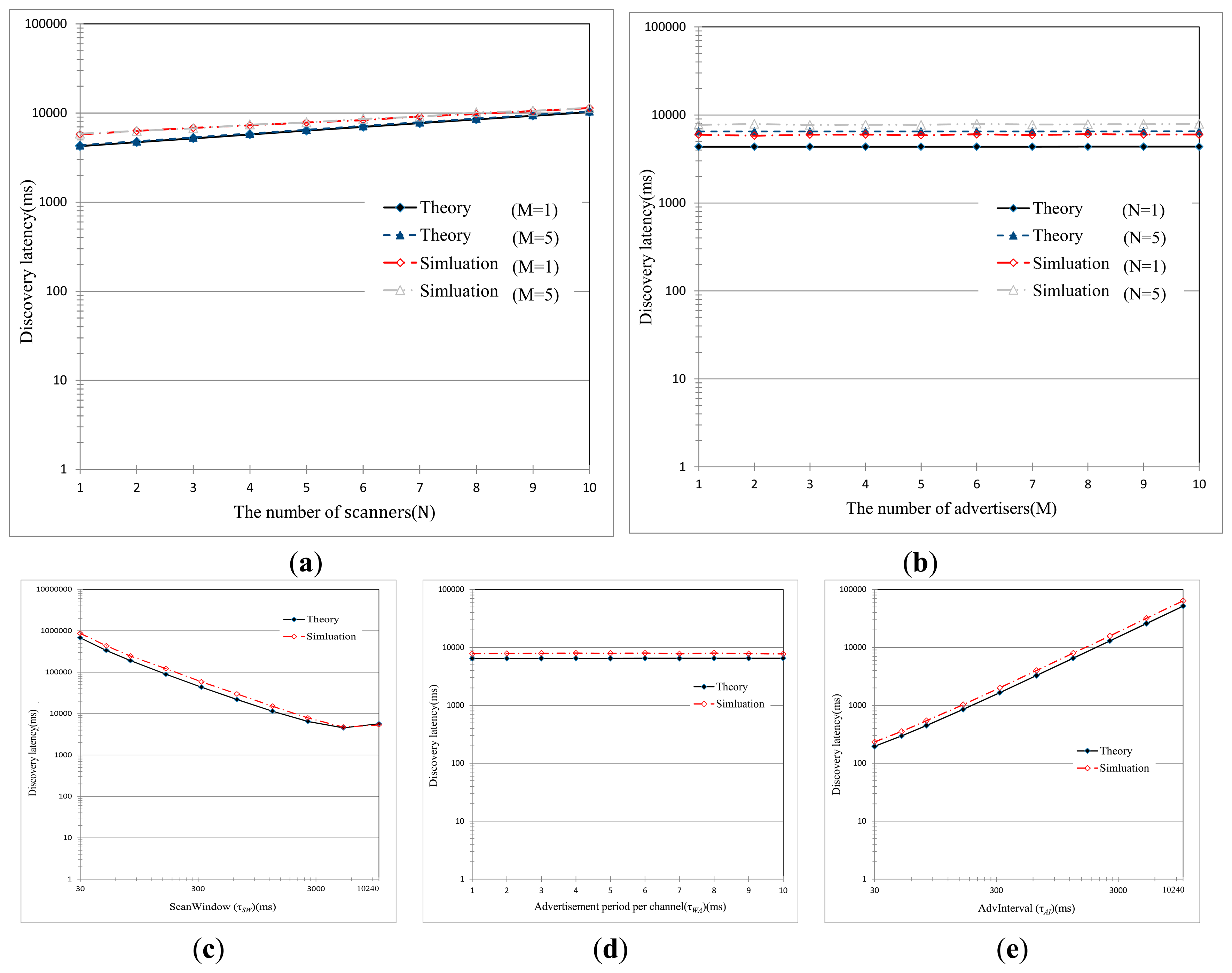
Figure 9 shows the mean discovery latency in terms of different sets of parameters, such as τAI, τWA, and τSW. We can find that the theoretical results match with the simulative ones over the entire range of parameters. The low success probability, as seen in Figures 8, causes a significant and exponential rise in the mean discovery latency as the number of BLE devices increased. As explained above, this is because of collisions of the abundant control packets. From the figure, an interesting thing can be discovered. The mean discovery latency decreases very gradually with τSW when τSW < 100 ms, and remains almost constant when τSW > 100 ms. And, the mean discovery latency is not affected much by τWA (a negligible change though). As previously described, τSW and τWA mainly affect the rendezvous chance of the advertiser and the scanner on one of three advertising channels, but they do not have a significant impact on the discovery latency. On the contrary, the mean discovery latency linearly increases with τAI. Since advertisers initiate the advertisement intervals according to the value of τAI, the discovery latency is strongly dependent on τAI. Figure 9 also indicates that the improper setting of parameters significantly deteriorates the discovery latency.
As for the sensitivity shown in Figure 10, it is shown that the theoretical results are practically the same with simulation results. The sensitivity of the mean discovery latency to τSW or τWA roughly remains around 0, which implies that change in τSW or τSW does not have a significant impact on the discovery latency. On the contrary, the sensitivity of discovery latency to τAI is almost 1 as γ is varied over a range from −0.5 to 0.5. This means that the discovery latency is identically proportional to τAI, which is in accordance with the results shown in Figures 9 and 10.
6. Conclusions
There is a significant increase in the applications of BLE in different areas, which is capable of making BLE one of the leading technologies for short-range communication in the next generation of networks. The Bluetooth standard defined the BLE communication model in a clear and detailed way, but still there are many other parts which can be addressed. Therefore, we create an accurate analytical model for these parts such as the discovery latency, as well as the discovery probability in BLE networks. These are then validated via extensive simulation experiments. We also analyze the sensitivity of those performance metrics to quantitatively evaluate to what extent parameter setting would influence the performance metrics. It is shown the theoretical results match the simulated ones. With increasing number of BLE devices, delays of device discovery show an exponential growth despite the usage of three advertising channels and tiny-sized frames. This implies that there exist severe contentions among multiple BLE devices. We find that the inappropriate parameter settings considerably impair the efficiency of BLE devices, and the wide range of BLE parameters provides high flexibility for BLE devices to be customized for different applications. As far as we know, this work is one of the first in-depth and accurate models for BLE discovery, including sensitivity analysis.
Acknowledgments
This research is funded by “Technology development for performance enhancement of BLE networks” Project by Samsung Electronics Co., Ltd.
Author Contributions
Keuchul Cho, Gisu Park, Wooseong Cho, Jihoon Seo and Kijun Han contributed to the theoretical analysis and proofs. Keuchul Cho, Wooseong Cho and Kijun Han contributed to the simulation. Woojin Park and Moonki Hong contributed to building the analytical models and validating their correctness.
Conflicts of Interest
The authors declare no conflicts of interest.
References
- Patel, M.; Wang, J. Applications, challenges, and prospective in emerging body area networking technologies. IEEE Wirel. Commun. 2010, 17, 80–88. [Google Scholar]
- Liu, J.; Chen, C. Energy Analysis of Neighbor Discovery in Bluetooth Low Energy Networks; Technical Report; Nokia Research Center/Radio System Lab: Beijing, China, 2012. [Google Scholar]
- Liu, J.; Chen, C.; Ma, Y. Modeling and performance analysis of device discovery in bluetooth low energy networks. Proceedings of the IEEE on Global Communications Conference (GLOBECOM), Anaheim, CA, USA, 3–7 December 2012; pp. 1538–1543.
- Liu, J.; Chen, C.; Ma, Y.; Xu, Y. Energy analysis of device discovery for bluetooth low energy. Proceedings of the 78th Vehicular Technology Conference (VTC Fall), Las Vegas, NV, USA, 2–5 September 2013; pp. 1–5.
- Liu, J.; Chen, C.; Ma, Y. Modeling neighbor discovery in bluetooth low energy networks. IEEE Commun. Lett. 2012, 16, 1439–1441. [Google Scholar]
- Bluetooth SIG, Bluetooth Core Specification Version 4.0. Specification of the Bluetooth System 2010.
- Duflot, M.; Kwiatkowska, M.; Norman, G.; Parker, D. A formal analysis of bluetooth device discovery. Int. J. Softw. Tools Technol. Transf. 2006, 8, 621–632. [Google Scholar]
- Drula, C.; Amza, C.; Rousseau, F.; Duda, A. Adaptive energy conserving algorithms for neighbor discovery in opportunistic bluetooth networks. IEEE J. Sel. Areas Commun. 2007, 25, 96–107. [Google Scholar]
- Basagni, S.; Bruno, R.; Petrioli, C. Device discovery in Bluetooth networks: A scatternet perspective. In NETWORKING 2002: Networking Technologies, Services, and Protocols; Performance of Computer and Communication Networks; Mobile and Wireless Communications; Springer: Berlin/Hidelberg, Germany, 2002; pp. 1087–1092. [Google Scholar]
- Scott, D.; Sharp, R.; Madhavapeddy, A.; Upton, E. Using visual tags to bypass bluetooth device discovery. Mob. Comput. Commun. Rev. 2005, 9, 41–53. [Google Scholar]
- Liu, J.; Chen, C.; Ma, Y.; Xu, Y. Adaptive device discovery in bluetooth low energy networks. Proceedings of the 77th Vehicular Technology Conference (VTC Spring), Dresden, Germany, 2–5 June 2013; pp. 1–5.






| Notation | Meaning | Recommended Specification |
|---|---|---|
| τWA | Advertising period per channel (Max allowable waiting time for SCAN_REQ after sending ADV_IND on each channel) | ≤10 ms |
| τAI | Advertisement Interval for three advertising channels | Integer multiple of 0.625 ms in [20∼10,240] ms |
| δ | AdvDelay (Uniform random delay chosen from [0, δmax] to determine Advertisement Interval) | [0, δmax] |
| δmax | Upper bound to choose a random delay δ | ≤10 ms |
| τSI | Scan Interval | Integer multiple of 0.625 ms in [2.5∼10,240] ms |
| τSW | Scan Window | Integer multiple of 0.625 ms in [2.5∼10,240] ms τSW ≤ τSI |
| Event | Meaning |
|---|---|
| E1 | S1 is synchronous with A1 |
| E2 | All of S2, S3,… and SN are not synchronous with A1 |
| E3 | All of A2, A3 …, and AM are not synchronous with S1 |
| E4 | S1 has enough time to reply to ADV_IND until ScanWindow is finished |
| E5 | All of S2, S3,… and SN are sleeping or do not have enough time to reply to ADV_IND until ScanWindow is finished |
| E6 | S1 does not receive ADV_IND from A2, A3 …, and AM in an interval [t1 − Ts, t1 + Ts] |
| Advertising Interval | Channel ID | Elapsed Time to Successful Discovery | Probability of Successful Discovery |
|---|---|---|---|
| 1 | 1st | τWA | α1 |
| 2nd | 2τWA | (1 − α1)α2 | |
| 3rd | 3τWA | (1 − α1) (1 − α2)α3 | |
| 2 | 1st | (1 − α1) (1 − α2) (1 − α3)α1 | |
| 2nd | (1 − α1) (1 − α2) (1 − α3)α2 | ||
| 3rd | (1 − α1)2 (1 − α2)2 (1 − α3)α3 | ||
| … | … | … | … |
| I | 1st | (1 − α1)i −1 (1 − α2)i −1 (1 − α3)i −1α1 | |
| 2nd | (1 − α1)i (1 − α2)i −1 (1 − α3)i −1α2 | ||
| 3rd | (1 − α1)i (1 − α2)i (1 − α3)i −1α3 | ||
| Parameters | Value |
|---|---|
| Number of advertises (M) | 1∼10 |
| Number of scanners (N) | 1∼10 |
| τWA | 1∼10 (ms) |
| τAI | 30∼10,240 (ms) |
| δmax | 10 (ms) |
| τSI | 30∼10,240 (ms) |
| τSW | 30∼10,240(ms) |
| TADV_IND | 0.128 (ms) |
| TSCAN_REQ | 0.176 (ms) |
| TSCAN_RSP | 0.128 (ms) |
| TIFS | 0.150 |
| TS | 0.604 |
© 2015 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license ( http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Cho, K.; Park, W.; Hong, M.; Park, G.; Cho, W.; Seo, J.; Han, K. Analysis of Latency Performance of Bluetooth Low Energy (BLE) Networks. Sensors 2015, 15, 59-78. https://doi.org/10.3390/s150100059
Cho K, Park W, Hong M, Park G, Cho W, Seo J, Han K. Analysis of Latency Performance of Bluetooth Low Energy (BLE) Networks. Sensors. 2015; 15(1):59-78. https://doi.org/10.3390/s150100059
Chicago/Turabian StyleCho, Keuchul, Woojin Park, Moonki Hong, Gisu Park, Wooseong Cho, Jihoon Seo, and Kijun Han. 2015. "Analysis of Latency Performance of Bluetooth Low Energy (BLE) Networks" Sensors 15, no. 1: 59-78. https://doi.org/10.3390/s150100059
APA StyleCho, K., Park, W., Hong, M., Park, G., Cho, W., Seo, J., & Han, K. (2015). Analysis of Latency Performance of Bluetooth Low Energy (BLE) Networks. Sensors, 15(1), 59-78. https://doi.org/10.3390/s150100059




