Digital Signatures with Quantum Candies
Abstract
1. Introduction
2. Computationally Secure Digital Signatures
2.1. Digital Signatures-Motivation
2.2. Definition and the Lamport Scheme
The Lamport Scheme
- Private key generation For each value of , Alice generates a random string . Both serve as the private keys of Alice.
- Public key distribution For each value of b, Alice calculates and publicly announces . Both serve as the public keys.
- Signed messaging If Alice wishes to send Bob a signed one-bit message m, she sends . I.e., the signature of the message m is (Note that in this construction, ).
- Verification When receiving from Alice, Bob (who knows H and ) accepts the message if and only if .
- Arbitration A dispute occurs when Bob claims Alice sent a message m, and Alice denies it. If Bob is dishonest, this is the forgery attempt case. If Alice is dishonest, this is the repudiation attempt case. A dispute is settled in the following way: Bob sends Charlie the value of he claims he received from Alice, . Charlie then checks if , and if so, he declares Alice as the dishonest one. If not, he declares Bob as the dishonest one.
3. One-Time Pad Signatures
3.1. Protocol Assumptions
3.2. Protocol Specification
- Private Key Generation For each future message bit , Alice generates two random strings (Total of four strings).
- “Public” Key Distribution For each future message bit , Alice sends to Bob and to Charlie, using OTP.
- “Public” Key Symmetrization For each future message bit , each of Bob and Charlie decides on a random subset of bits from () and forwards them (value and index) to the other, using OTP. Bob’s decision on the forwarded subset is independent of Charlie’s.
- Signed Messaging For signing a specific bit , Alice sends Bob the string via an authenticated classical channel.
- Verification Bob accepts Alice’s signature if it matches his key and the indices of Charlie sent him. As the keys are classical, error-free, and authenticated, we can assume the final shared keys must be fully identical (if the parties are honest).
- Arbitration In case of a future dispute regarding the message content, Bob forwards to Charlie the string he obtained from Alice. Charlie counts the mismatches between Bob’s forwarded keys versus his key and the parts of the key Bob sent him in Step 3, and accepts only if:
- (a)
- There is no mismatch between Bob’s forwarded and the parts of Charlie received from Bob in Step 3.
- (b)
- The number of mismatches between Bob’s forwarded and Charlie’s is less than , where is the arbiter’s verification threshold parameter.
Charlie accepting means he accepts Bob’s forwarded message as valid, i.e., Alice is the dishonest party, and a rejection means Bob’s forwarded message is invalid, i.e., Bob is the dishonest party.
4. Quantum Candies
5. A Digital Signature Protocol with Qandies
5.1. Protocol Assumptions
- Alice is in possession of standard qandy generation capabilities: she can create qandies of the four types . Alice also has an ideal coin, i.e., she can generate random classical bits; such an assumption is automatically satisfied using qandies measuring devices (e.g., generate a color qandy and measure its taste).
- Between each two parties, there exists a lossless but potentially insecure “qandy channel”, namely: for each qandy sent by a sender, some qandy is received by the receiver (although it may be corrupted by noise or eavesdropping activities).
- Bob and Charlie possess standard qandy measurement capabilities: they can either look at or taste the qandies.
- Bob and Charlie possess a “qandy memory” capability, namely they can store received qandies indefinitely and measure them later.
- Between each two parties there exists an authenticated classical channel (using a small number of pre-shared bits); no eavesdropper or noise can change the classical bits sent between the parties.
- The assumption in Item 4 is not strictly necessary (the original protocol P1 in [9], does not make it). We later discuss how the protocol may be defined without it, but we make it here to simplify the description.
- In the original protocol in [9], another assumption was made: between each two parties there exists an authenticated quantum channel, i.e., no eavesdropper or noise can change the qandies sent between the parties. We note the implementation of an authenticated quantum channel is a far-from-trivial task [23], and it is unclear whether such an authenticated channel can be implemented using qandies. However, as stated by [9], the requirement of authenticated quantum channels may be dropped if the parties use the first step of most standard QKD technique: the step of comparing measurement results (TEST), after sending quantum states to one another and measuring some of them (and aborting if the effective noise level, , is too high). Such a technique may easily be implemented using qandies [12,13], and we thus assume no authenticated “qandy channels” are needed for this protocol.
- Adding TEST somewhat modifies the security analysis to make it more complicated; a detailed analysis is beyond the scope of this paper, and is left for future work.
- We assume that n is very large and thus that the relevant law of large numbers will work well, and any exponentially small tail can be safely neglected.
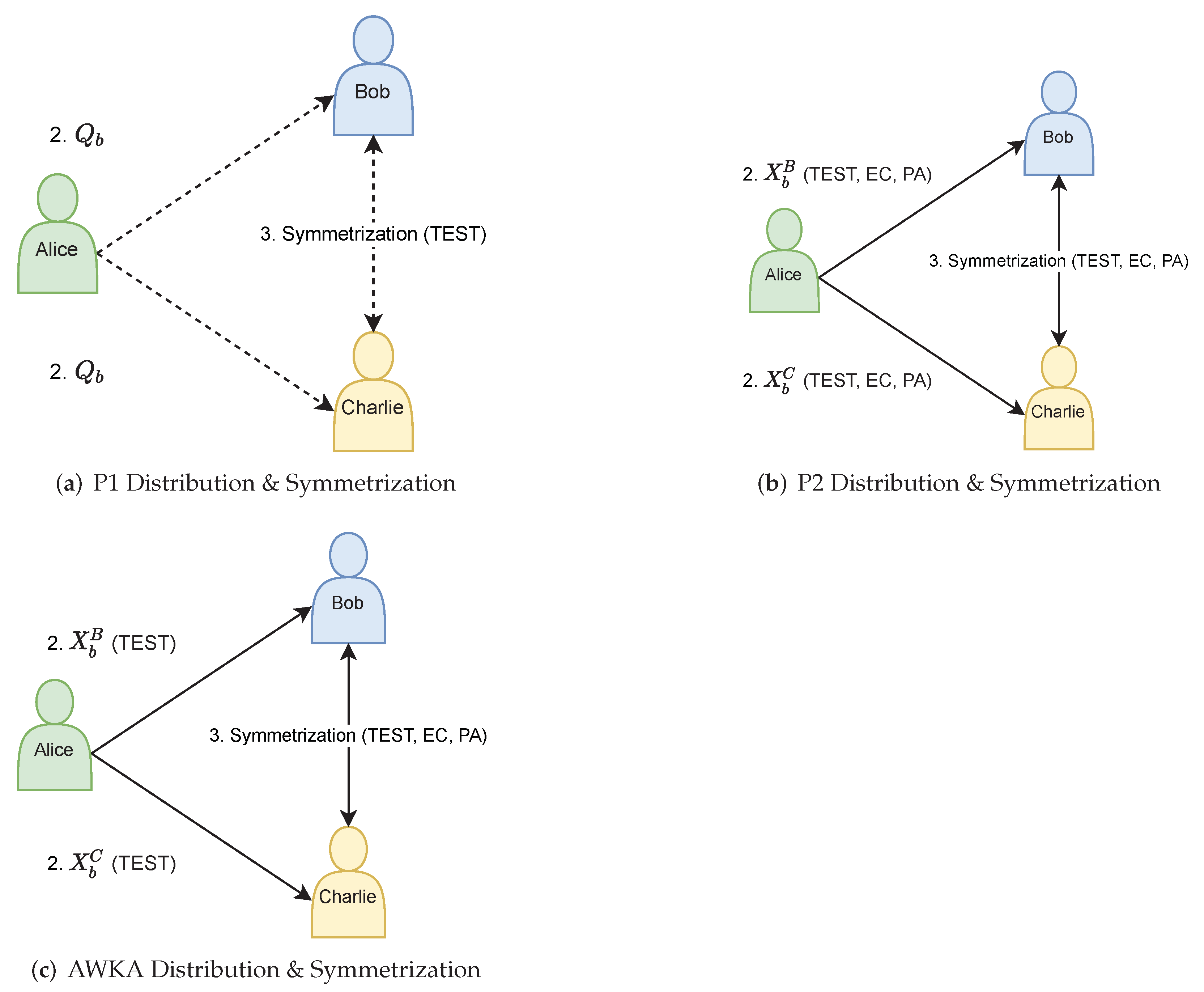
5.2. Protocol Specification
- Private Key Generation For each future message bit , Alice generates a random string (“private key”) of characters from the set ‘R’, ‘G’, ‘C’, ‘V’ (each character can be represented by 2 bits). The key length n is the security parameter of the protocol.
- “Public” Key Distribution For each future message bit , Alice creates two copies of qandy strings (“public keys”) using her qandy generating machine-each qandy according to the private key character . Alice sends one copy of to Bob and the other to Charlie.
- “Public” Key Symmetrization For each future message bit :
- (a)
- Bob (Charlie) decides on a random subset of qandies from his copy of and forwards them to Charlie (Bob), without measuring. The decision on the forwarded subset is independent of the other party.
- (b)
- Bob (Charlie) randomly looks at or tastes each of the qandies he has kept, as well as the qandies received from Charlie (Bob), and writes down the measurement results.
- (c)
- Alice discloses part of the qandies to Bob and Charlie (via an authenticated classical channel), for TEST. There are two TESTs:
- i.
- Between Alice and Charlie, in order to make sure Bob did not attempt to eavesdrop in Step 2 (distribution).
- ii.
- Between Alice and Bob, in order to make sure Alice did not attempt to eavesdrop in Step 3 (symmetrization).
In both TESTs, both parties choose which indices they want to reveal.Bob and Charlie abort the protocol if the noise rate is higher than . is the recipient’s verification threshold parameter that depends on the parameters of the qandy channel and equals in the ideal case. is a small parameter (function of n), such that the probability of a noise rate higher than on the unmeasured (non-TESTED) qandies is exponentially small. Several additional notes about the TESTs:- Both TESTs have to be done with Alice’s participation, because only Alice knows the true values of the qandies she sent and may reveal them to Bob and Charlie as necessary.
- In the TESTs, qandies with conjugate measurement bases (e.g., Alice sent a color Qandy but Bob tasted it) are removed from the statistics and do not contribute towards the noise rate calculation.
At this stage, Bob and Charlie do not yet know the indices of the qandies that were received from the other and were not TEST qandies. - Signed Messaging For signing a specific bit , Alice sends Bob the string (via an authenticated classical channel)
- Verification At this stage, Bob and Charlie disclose to one another all the indices of the qandies they forwarded in Step 3, via an authenticated classical channel. Bob counts the number of mismatched indices between his measurement results of from Step 3b and Alice’s candidate private key .A mismatch for index i occurs when Alice’s private key character contradicts Bob’s measurement result for that index: for example, is ‘’ but Bob has a measurement that says is G. On the other hand, if is ‘’ but Bob decided to taste and measured C, then this is not a contradiction as he chose the wrong basis.Bob accepts Alice’s signature if the number of mismatches is smaller than , and rejects it otherwise.
- Arbitration In case of a future dispute regarding the message content, Bob forwards to Charlie the string he obtained from Alice. Charlie counts the mismatches similarly to Bob, but accepts (i.e., agrees with Bob) only if the number of mismatches is less than , where is the arbiter’s verification threshold parameter.
5.2.1. No-Cloning of Qandies
5.2.2. Usage of Memory
5.2.3. Possibilities of Elimination
5.3. Security Analysis
5.3.1. Security against Forgery
5.3.2. Security against Repudiation
5.3.3. Probability of an Honest Abort
5.3.4. Choosing the Optimal Thresholds
6. Alternative Signature Protocols
6.1. Protocol P2 of WDKA15 with Qandies
6.2. Classical Public Keys
6.3. Usage of Memory
6.4. Verification Threshold
Protocol Security
6.5. Protocol of AWKA16 with Qandies
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| QIP | Quantum Information Processing |
| DS | Digital Signatures |
| QDS | Quantum Digital Signatures |
| QKD | Quantum Key Distribution |
| OWF | One-Way Function |
| OTP | One Time Pad |
| OTP-S | One Time Pad Signature |
| EC | Error Correction |
| PA | Privacy Amplification |
Appendix A
Appendix A.1. Classical Digital Signature—Formal Definition
Appendix A.1.1. Syntax
- Gen().
- Sign.
- Ver ACC/REJ.
Appendix A.1.2. Correctness
Appendix A.1.3. Security
- Gen
Appendix A.2. Lamport Scheme—Intuitive and Formal Definition
- Private key generation For each value of , Alice generates a random string . Both serve as the private keys of Alice (so ).
- Public key distribution For each value of b, Alice calculates and publicly announces . Both serve as the public keys (so . These two procedures, 1 and 2, define Gen).
- Signed messaging If Alice wishes to send Bob a signed one-bit message m, she sends (so Sign). I.e., the signature of the message m is (Note that in this construction, ).
- Verification When receiving from Alice, Bob (who knows H and ) accepts the message if and only if (This defines Ver).
- Arbitration A dispute occurs when Bob claims Alice sent a message m, and Alice denies it. If Bob is dishonest, this is the forgery attempt case. If Alice is dishonest, this is the repudiation attempt case. A dispute is settled in the following way: Bob sends Charlie the value of he claims he received from Alice, . Charlie then checks if , and if so, he declares Alice as the dishonest one. If not, then he declares Bob as the dishonest one.
References
- Feynman, R.P. Simulating physics with computers. Int. J. Theor. Phys. 1982, 21, 467–488. [Google Scholar] [CrossRef]
- Diffie, W.; Hellman, M. New directions in cryptography. IEEE Trans. Inf. Theory 1976, 22, 644–654. [Google Scholar] [CrossRef]
- Lamport, L. Constructing Digital Signatures from a One-Way Function; Technical Report; SRI International: Menlo Park, CA, USA, 1979. [Google Scholar]
- Shor, P.W. Polynomial-Time Algorithms for Prime Factorization and Discrete Logarithms on a Quantum Computer. SIAM Rev. 1999, 41, 303–332. [Google Scholar] [CrossRef]
- Gottesman, D.; Chuang, I. Quantum digital signatures. arXiv 2001, arXiv:quant-ph/0105032. [Google Scholar]
- Bennett, C.H.; Brassard, G. Quantum cryptography: Public key distribution and coin tossing. In Proceedings of the International Conference on Computers, Systems and Signal Processing, Bangalore, India, 9–12 December 1984; pp. 175–179. [Google Scholar]
- Andersson, E.; Curty, M.; Jex, I. Experimentally realizable quantum comparison of coherent states and its applications. Phys. Rev. A 2006, 74, 022304. [Google Scholar] [CrossRef]
- Dunjko, V.; Wallden, P.; Andersson, E. Quantum Digital Signatures without Quantum Memory. Phys. Rev. Lett. 2014, 112, 040502. [Google Scholar] [CrossRef] [PubMed]
- Wallden, P.; Dunjko, V.; Kent, A.; Andersson, E. Quantum digital signatures with quantum-key-distribution components. Phys. Rev. A 2015, 91, 042304. [Google Scholar] [CrossRef]
- Amiri, R.; Wallden, P.; Kent, A.; Andersson, E. Secure quantum signatures using insecure quantum channels. Phys. Rev. A 2016, 93, 032325. [Google Scholar] [CrossRef]
- Amiri, R.; Andersson, E. Unconditionally Secure Quantum Signatures. Entropy 2015, 17, 5635–5659. [Google Scholar] [CrossRef]
- Lin, J.; Mor, T. Quantum Candies and Quantum Cryptography. In Theory and Practice of Natural Computing; Martín-Vide, C., Vega-Rodríguez, M.A., Yang, M.S., Eds.; Springer International Publishing: Cham, Switzerland, 2020; pp. 69–81. [Google Scholar]
- Lin, J.; Mor, T.; Shapira, R. Illustrating quantum information with quantum candies. arXiv 2021, arXiv:2110.01402. [Google Scholar]
- Deutsch, D.; Jozsa, R. Rapid solution of problems by quantum computation. Proc. R. Soc. London Ser. Math. Phys. Sci. 1992, 439, 553–558. [Google Scholar] [CrossRef]
- Goldreich, O. Foundations of Cryptography; Cambridge University Press: Cambridge, UK, 2001; Volume 1. [Google Scholar] [CrossRef]
- Hanaoka, G.; Shikata, J.; Zheng, Y.; Imai, H. Unconditionally Secure Digital Signature Schemes Admitting Transferability. In Advances in Cryptology—ASIACRYPT 2000; Okamoto, T., Ed.; Springer: Berlin/Heidelberg, Germany, 2000; pp. 130–142. [Google Scholar]
- Swanson, C.M.; Stinson, D.R. Unconditionally Secure Signature Schemes Revisited. In Information Theoretic Security; Fehr, S., Ed.; Springer: Berlin/Heidelberg, Germany, 2011; pp. 100–116. [Google Scholar]
- Chaum, D.; Roijakkers, S. Unconditionally Secure Digital Signatures. In Proceedings of the 10th Annual International Cryptology Conference on Advances in Cryptology, Santa Barbara, CA, USA, 11–15 August 1990; CRYPTO ’90; Springer: Berlin/Heidelberg, Germany, 1990; pp. 206–214. [Google Scholar]
- Carter, J.; Wegman, M.N. Universal classes of hash functions. J. Comput. Syst. Sci. 1979, 18, 143–154. [Google Scholar] [CrossRef]
- Wegman, M.N.; Carter, J. New hash functions and their use in authentication and set equality. J. Comput. Syst. Sci. 1981, 22, 265–279. [Google Scholar] [CrossRef]
- Jacobs, K.; (Technion—Israel Institute of Technology, Haifa, Israel). Private communication, 2009.
- Svozil, K. Staging quantum cryptography with chocolate balls. Am. J. Phys. 2006, 74, 800–803. [Google Scholar] [CrossRef]
- Barnum, H.; Crepeau, C.; Gottesman, D.; Smith, A.; Tapp, A. Authentication of quantum messages. In Proceedings of the The 43rd Annual IEEE Symposium on Foundations of Computer Science, Vancouver, BC, Canada, 19 November 2002; pp. 449–458. [Google Scholar] [CrossRef]
- Pirandola, S.; Andersen, U.L.; Banchi, L.; Berta, M.; Bunandar, D.; Colbeck, R.; Englund, D.; Gehring, T.; Lupo, C.; Ottaviani, C.; et al. Advances in quantum cryptography. Adv. Opt. Photon. 2020, 12, 1012–1236. [Google Scholar] [CrossRef]
- Wallden, P.; Dunjko, V.; Andersson, E. Minimum-cost quantum measurements for quantum information. J. Phys. A 2014, 47, 125303. [Google Scholar] [CrossRef][Green Version]
- Collins, R.J.; Amiri, R.; Fujiwara, M.; Honjo, T.; Shimizu, K.; Tamaki, K.; Takeoka, M.; Sasaki, M.; Andersson, E.; Buller, G.S. Experimental demonstration of quantum digital signatures over 43 dB channel loss using differential phase shift quantum key distribution. Sci. Rep. 2017, 7, 3235. [Google Scholar] [CrossRef] [PubMed]
- Thornton, M.; Scott, H.; Croal, C.; Korolkova, N. Continuous-variable quantum digital signatures over insecure channels. Phys. Rev. A 2019, 99, 032341. [Google Scholar] [CrossRef]
- Zhao, W.; Shi, R.; Shi, J.; Huang, P.; Guo, Y.; Huang, D. Multibit quantum digital signature with continuous variables using basis encoding over insecure channels. Phys. Rev. A 2021, 103, 012410. [Google Scholar] [CrossRef]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mor, T.; Shapira, R.; Shemesh, G. Digital Signatures with Quantum Candies. Entropy 2022, 24, 207. https://doi.org/10.3390/e24020207
Mor T, Shapira R, Shemesh G. Digital Signatures with Quantum Candies. Entropy. 2022; 24(2):207. https://doi.org/10.3390/e24020207
Chicago/Turabian StyleMor, Tal, Roman Shapira, and Guy Shemesh. 2022. "Digital Signatures with Quantum Candies" Entropy 24, no. 2: 207. https://doi.org/10.3390/e24020207
APA StyleMor, T., Shapira, R., & Shemesh, G. (2022). Digital Signatures with Quantum Candies. Entropy, 24(2), 207. https://doi.org/10.3390/e24020207





