On the Security of a Latin-Bit Cube-Based Image Chaotic Encryption Algorithm
Abstract
1. Introduction
- (1)
- The generation of Latin cubes in this algorithm is independent of plain image.
- (2)
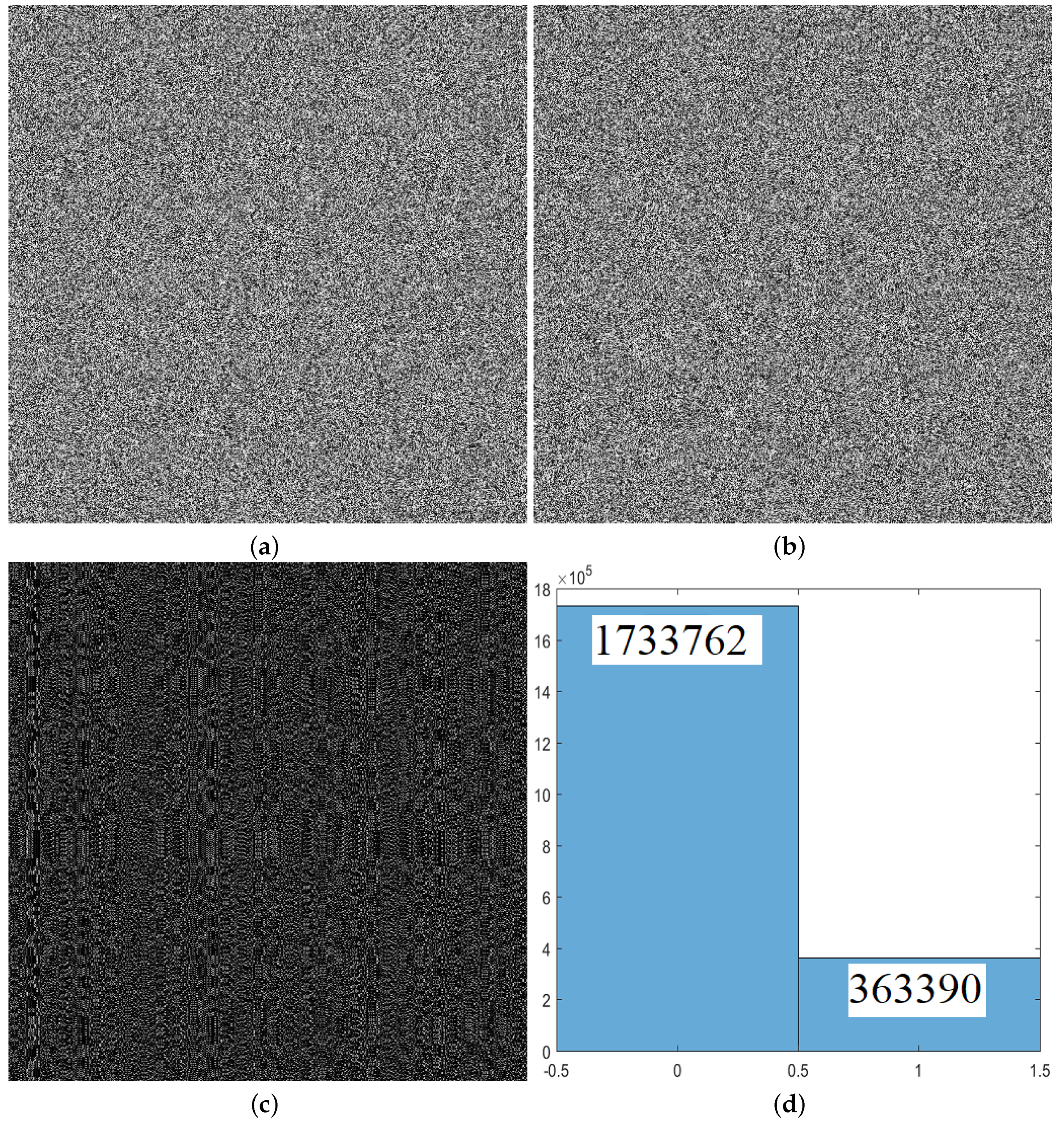
- When any one bit in the plain image changes, the corresponding number of bits in the cipher image follows the change with obvious regularity.
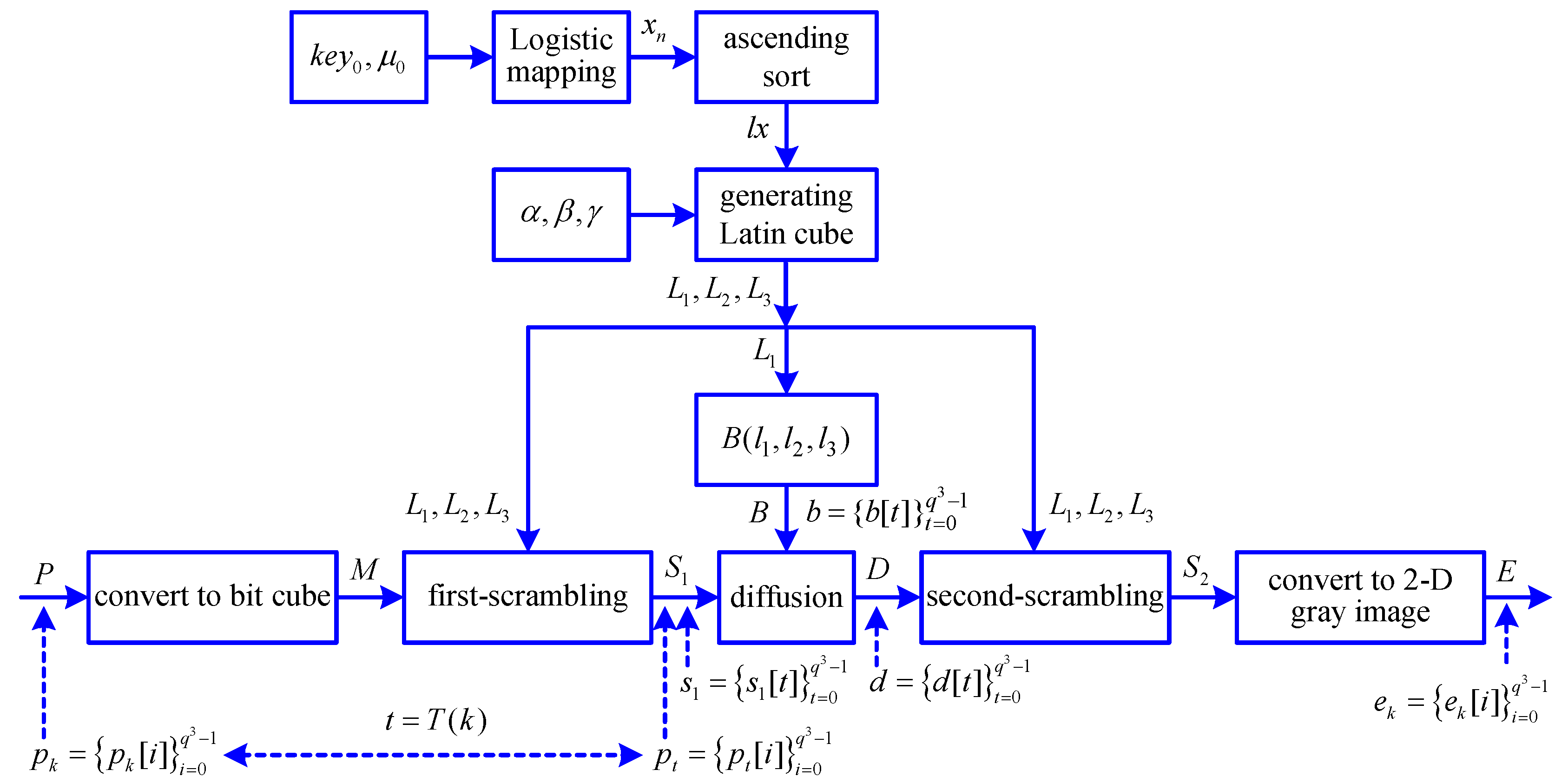
2. Description of an Image Chaotic Encryption Algorithm
2.1. A Brief View of an Image Chaotic Encryption Algorithm
2.2. Logistic Map
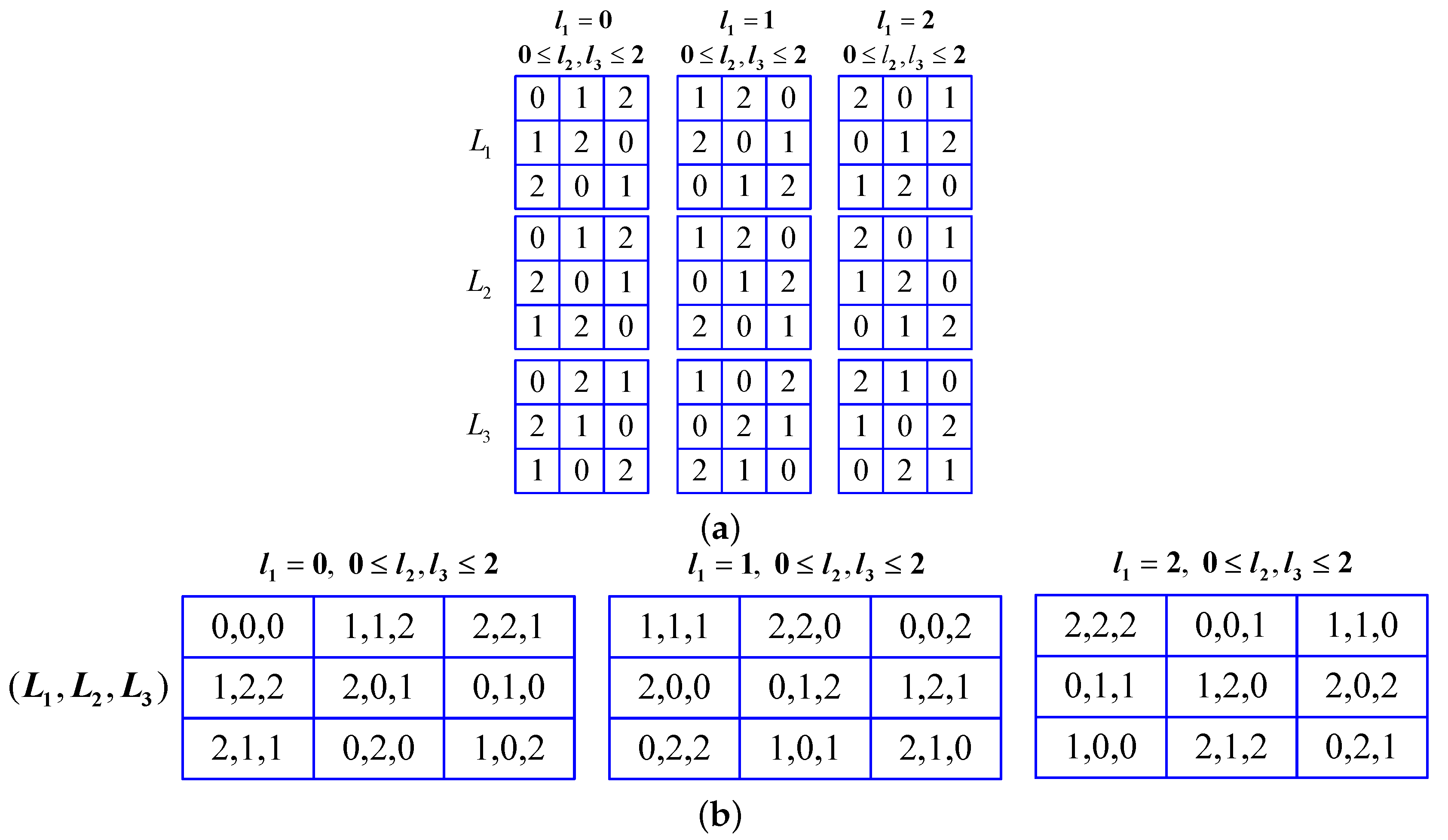
2.3. Generation of Latin Cubes
| Algorithm 1 Steps for Generation of Latin Cubes. |
| Input: Secret keys ; Side length ; Output: Three orthogonal Latin cubes , and ;
|
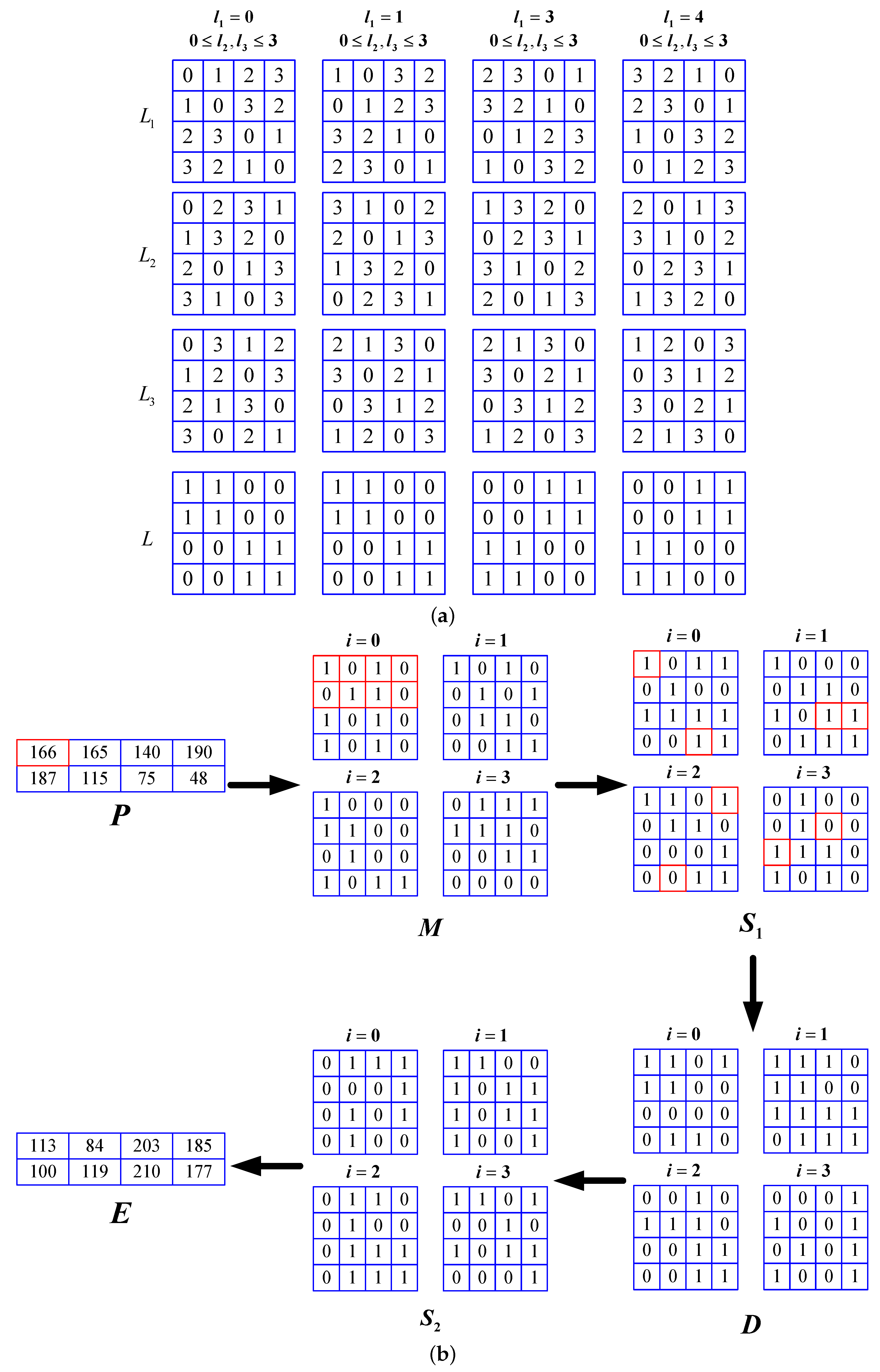
2.4. Steps for Image Chaotic Encryption
| Algorithm 2 Steps for Image Chaotic Encryption. |
| Input: Secret keys ; Plaintext image P; Output: Ciphertxet image E;
|
3. Security Analysis
3.1. Analysis of Chaotic Index Sequence
3.1.1. Relation between the First-Scrambling Image and the Plain Image M
3.1.2. The First Case for Analysis of Chaotic Index Sequence
3.1.3. The Second Case for Analysis of Chaotic Index Sequence
- (1)
- If , then one has
- (2)
- If , then one has
- (3)
- If , then one has
- (4)
- If , then one has
3.2. Analysis of Secret Keys , ,
3.3. Flowchart of Security Analysis
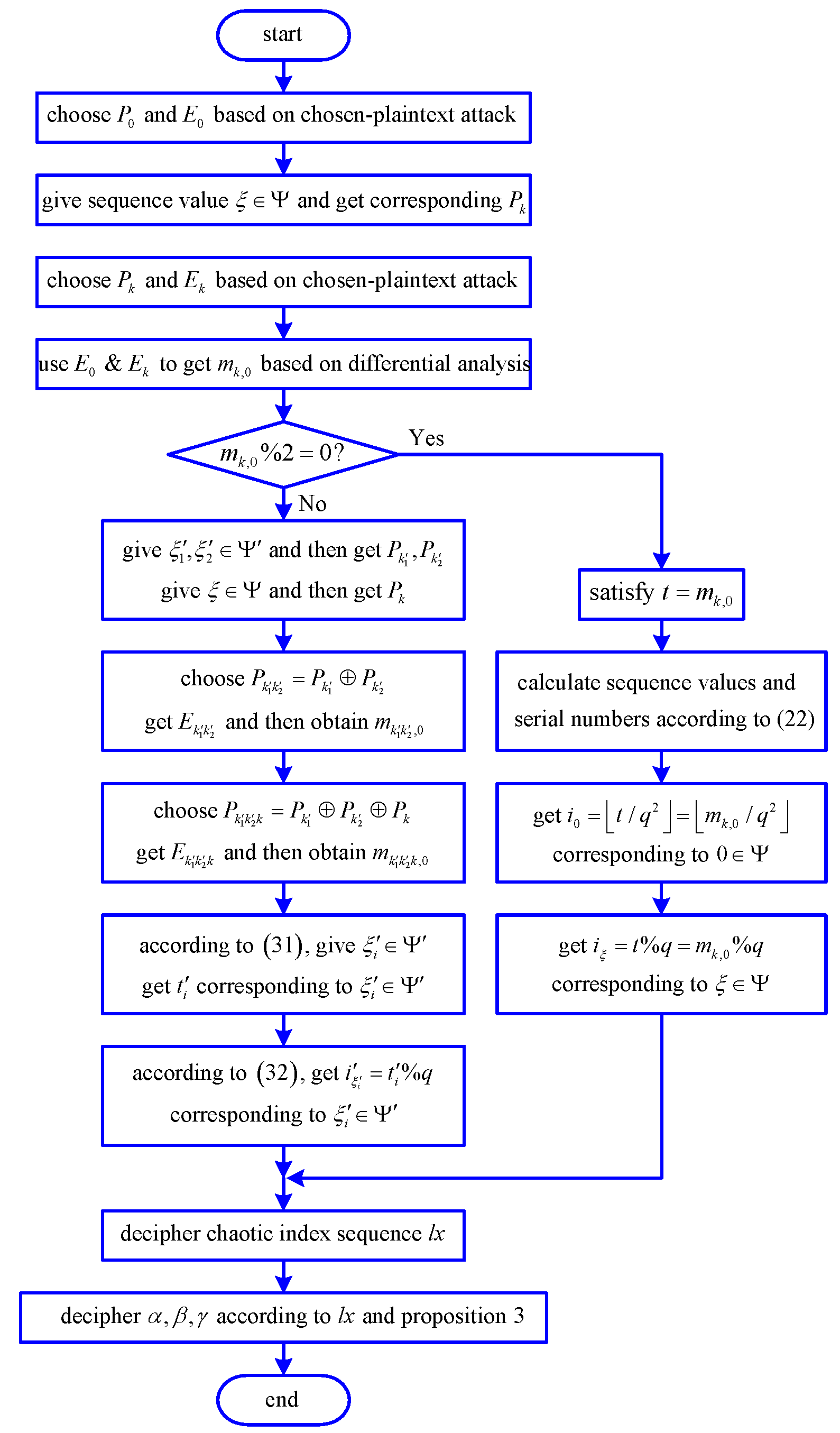
4. Steps for Deciphering the Image Chaotic Encryption Algorithm
| Algorithm 3 Steps for Deciphering Image Chaotic Encryption Algorithm. |
Output: The equivalent secret keys ;
|
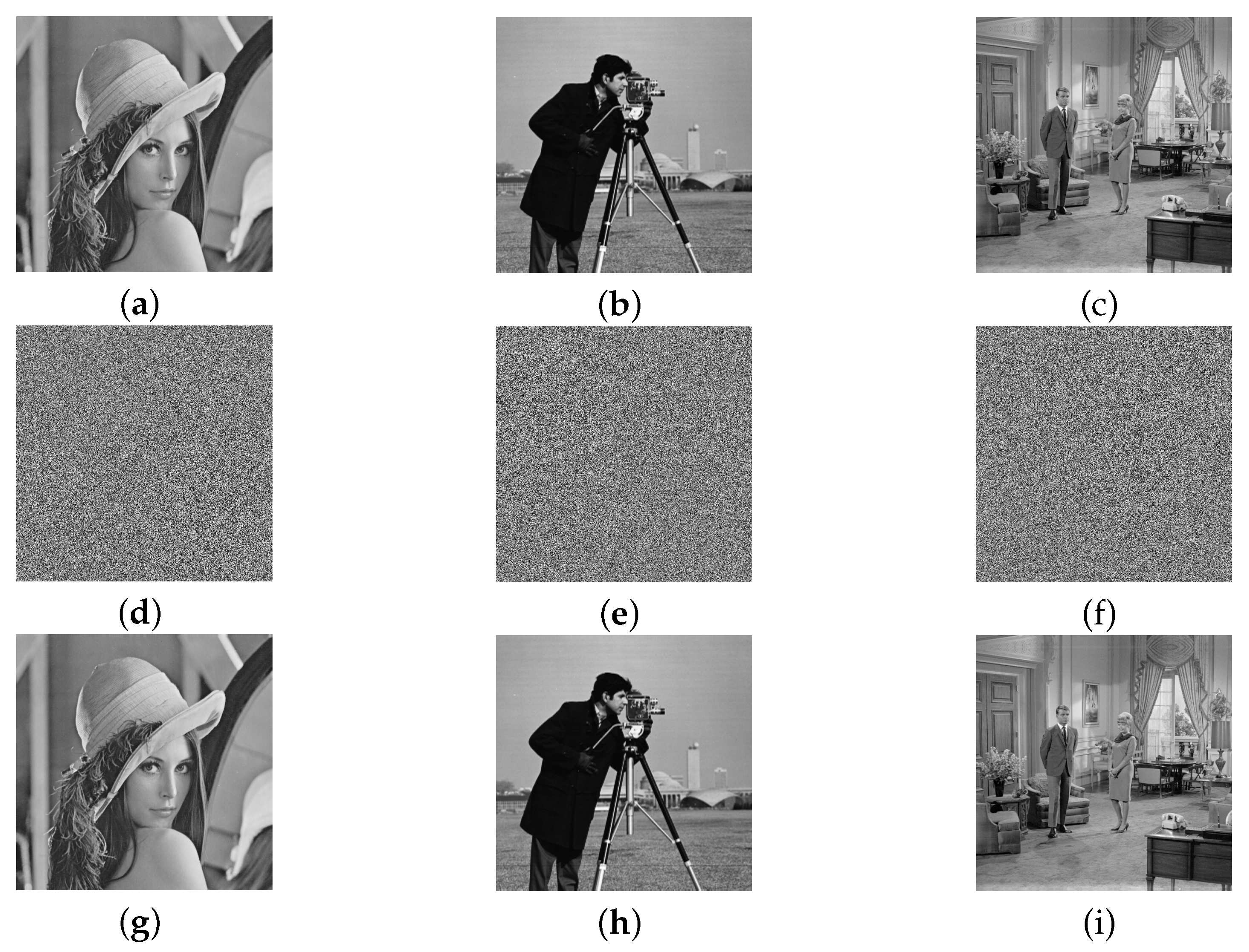
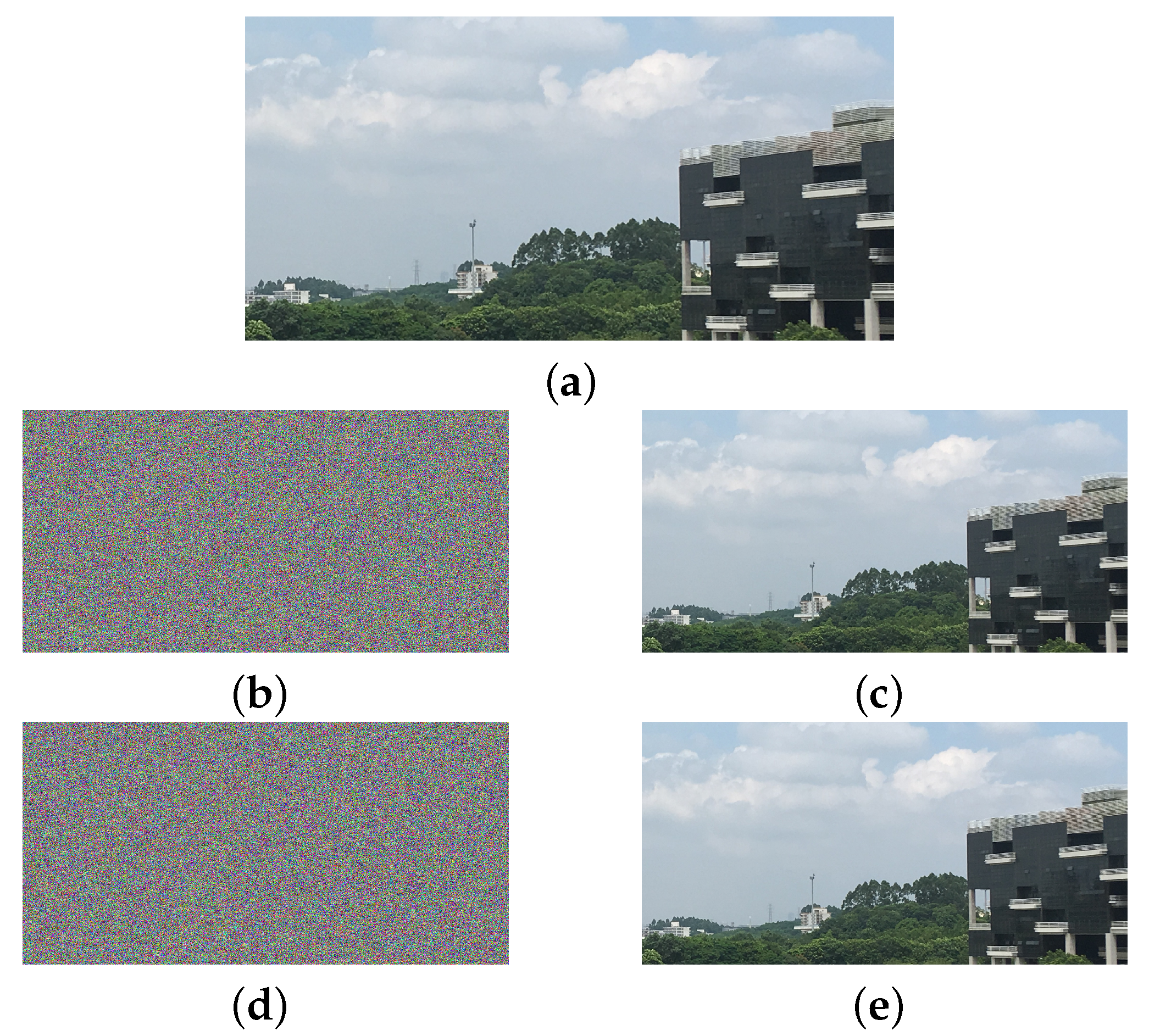
5. Numerical Simulation Experiments
6. Suggestions for Improvement
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Özkaynak, F. Brief review on application of nonlinear dynamics in image encryption. Nonlinear Dyn. 2018, 92, 305–313. [Google Scholar] [CrossRef]
- Abdallah, E.E.; Ben Hamza, A.; Bhattacharya, P. Video watermarking using wavelet transform and tensor algebra. Signal Image Video Process. 2010, 4, 233–245. [Google Scholar] [CrossRef]
- Abdallah, E.E.; Hamza, A.B.; Bhattacharya, P. MPEG Video Watermarking Using Tensor Singular Value Decomposition. In Image Analysis and Recognition; Kamel, M., Campilho, A., Eds.; Springer: Berlin/Heidelberg, Germany, 2007; pp. 772–783. [Google Scholar]
- Wang, J.; Ding, Q. Dynamic Rounds Chaotic Block Cipher Based on Keyword Abstract Extraction. Entropy 2018, 20, 693. [Google Scholar] [CrossRef]
- Wang, X.; Yang, L.; Liu, R.; Kadir, A. A chaotic image encryption algorithm based on perceptron model. Nonlinear Dyn. 2010, 62, 615–621. [Google Scholar] [CrossRef]
- Zhang, Y.; Wang, X. A new image encryption algorithm based on non-adjacent coupled map lattices. Appl. Soft. Comput. 2015, 26, 10–20. [Google Scholar] [CrossRef]
- Wang, X.; Liu, L.; Zhang, Y. A novel chaotic block image encryption algorithm based on dynamic random growth technique. Opt. Lasers Eng. 2015, 66, 10–18. [Google Scholar] [CrossRef]
- Liu, H.; Wang, X. Color image encryption based on one-time keys and robust chaotic maps. Comput. Math. Appl. 2010, 59, 3320–3327. [Google Scholar] [CrossRef]
- Liu, H.; Wang, X. Color image encryption using spatial bit-level permutation and high-dimension chaotic system. Opt. Commun. 2011, 284, 3895–3903. [Google Scholar] [CrossRef]
- Song, C.; Qiao, Y. A Novel Image Encryption Algorithm Based on DNA Encoding and Spatiotemporal Chaos. Entropy 2015, 17, 6954–6968. [Google Scholar] [CrossRef]
- Chai, X.; Fu, X.; Gan, Z.; Lu, Y.; Chen, Y. A color image cryptosystem based on dynamic DNA encryption and chaos. Signal Process. 2019, 155, 44–62. [Google Scholar] [CrossRef]
- Liu, H.; Wang, X.; kadir, A. Image encryption using DNA complementary rule and chaotic maps. Appl. Soft. Comput. 2012, 12, 1457–1466. [Google Scholar] [CrossRef]
- Wang, X.; Zhang, Y.; Bao, X. A novel chaotic image encryption scheme using DNA sequence operations. Opt. Lasers Eng. 2015, 73, 53–61. [Google Scholar] [CrossRef]
- Wang, X.; Feng, L.; Zhao, H. Fast image encryption algorithm based on parallel computing system. Inf. Sci. 2019, 486, 340–358. [Google Scholar] [CrossRef]
- Wang, X.; Gao, S. Image encryption algorithm for synchronously updating Boolean networks based on matrix semi-tensor product theory. Inf. Sci. 2019, 507, 16–36. [Google Scholar] [CrossRef]
- Yaghouti Niyat, A.; Moattar, M.H.; Niazi Torshiz, M. Color image encryption based on hybrid hyper-chaotic system and cellular automata. Opt. Lasers Eng. 2017, 90, 225–237. [Google Scholar] [CrossRef]
- Chai, X.; Gan, Z.; Yang, K.; Chen, Y.; Liu, X. An image encryption algorithm based on the memristive hyperchaotic system, cellular automata and DNA sequence operations. Signal Process.-Image Commun. 2017, 52, 6–19. [Google Scholar] [CrossRef]
- Wang, X.; Li, Z. A color image encryption algorithm based on Hopfield chaotic neural network. Opt. Lasers Eng. 2019, 115, 107–118. [Google Scholar] [CrossRef]
- Bigdeli, N.; Farid, Y.; Afshar, K. A robust hybrid method for image encryption based on Hopfield neural network. Comput. Electr. Eng. 2012, 38, 356–369. [Google Scholar] [CrossRef]
- Xu, M.; Tian, Z. A novel image cipher based on 3D bit matrix and latin cubes. Inf. Sci. 2019, 478, 1–14. [Google Scholar] [CrossRef]
- Xu, M.; Tian, Z. A novel image encryption algorithm based on self-orthogonal Latin squares. Optik 2018, 171, 891–903. [Google Scholar] [CrossRef]
- Chen, J.; Zhu, Z.; Fu, C.; Zhang, L.; Zhang, Y. An efficient image encryption scheme using lookup table-based confusion and diffusion. Nonlinear Dyn. 2015, 81, 1151–1166. [Google Scholar] [CrossRef]
- Zhang, Y.; Wang, X. A symmetric image encryption algorithm based on mixed linear–nonlinear coupled map lattice. Inf. Sci. 2014, 273, 329–351. [Google Scholar] [CrossRef]
- Li, M.; Lu, D.; Wen, W.; Ren, H.; Zhang, Y. Cryptanalyzing a Color Image Encryption Scheme Based on Hybrid Hyper-Chaotic System and Cellular Automata. IEEE Access 2018, 6, 47102–47111. [Google Scholar] [CrossRef]
- Wen, H.; Yu, S.; Lü, J. Breaking an Image Encryption Algorithm Based on DNA Encoding and Spatiotemporal Chaos. Entropy 2019, 21, 246. [Google Scholar] [CrossRef]
- Li, C.; Lo, K. Optimal quantitative cryptanalysis of permutation-only multimedia ciphers against plaintext attacks. Signal Process. 2011, 91, 949–954. [Google Scholar] [CrossRef]
- Jolfaei, A.; Wu, X.; Muthukkumarasamy, V. On the Security of Permutation-Only Image Encryption Schemes. IEEE Trans. Inf. Forensic Secur. 2016, 11, 235–246. [Google Scholar] [CrossRef]
- Feng, W.; He, Y.; Li, H.; Li, C. Cryptanalysis and Improvement of the Image Encryption Scheme Based on 2D Logistic-Adjusted-Sine Map. IEEE Access 2019, 7, 12584–12597. [Google Scholar] [CrossRef]
- Hua, Z.; Zhou, Y. Image encryption using 2D Logistic-adjusted-Sine map. Inf. Sci. 2016, 339, 237–253. [Google Scholar] [CrossRef]
- Lin, Z.; Yu, S.; Lü, J.; Cai, S.; Chen, G. Design and ARM-Embedded Implementation of a Chaotic Map-Based Real-Time Secure Video Communication System. IEEE Trans. Circuits Syst. Video Technol. 2015, 25, 1203–1216. [Google Scholar]
- Lin, Z.; Yu, S.; Feng, X.; Lü, J. Cryptanalysis of a Chaotic Stream Cipher and Its Improved Scheme. Int. J. Bifurc. Chaos 2018, 28, 1850086. [Google Scholar] [CrossRef]
- Hu, G.; Xiao, D.; Wang, Y.; Li, X. Cryptanalysis of a chaotic image cipher using Latin square-based confusion and diffusion. Nonlinear Dyn. 2017, 88, 1305–1316. [Google Scholar] [CrossRef]
- Wang, H.; Xiao, D.; Chen, X.; Huang, H. Cryptanalysis and enhancements of image encryption using combination of the 1D chaotic map. Signal Process. 2018, 144, 444–452. [Google Scholar] [CrossRef]
- Pak, C. A new color image encryption using combination of the 1D chaotic map. Signal Process. 2017, 138, 129–137. [Google Scholar] [CrossRef]
- Wu, J. Cryptanalysis and enhancements of image encryption based on three-dimensional bit matrix permutation. Signal Process. 2018, 142, 292–300. [Google Scholar] [CrossRef]
- Zhang, W.; Yu, H.; Zhao, Y.; Zhu, Z. Image encryption based on three-dimensional bit matrix permutation. Signal Process. 2016, 118, 36–50. [Google Scholar] [CrossRef]
- Wang, X.; Teng, L.; Qin, X. A novel colour image encryption algorithm based on chaos. Signal Process. 2012, 92, 1101–1108. [Google Scholar] [CrossRef]
- Arkin, J.; Straus, E.G. Latin k-cubes. Fibonacci Q. 1974, 12, 288–292. [Google Scholar]
- Berlekamp, E.; Rumsey, H.; Solomon, G. On the solution of algebraic equations over finite fields. Inf. Comput. 1967, 10, 553–564. [Google Scholar] [CrossRef]
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zhang, Z.; Yu, S. On the Security of a Latin-Bit Cube-Based Image Chaotic Encryption Algorithm. Entropy 2019, 21, 888. https://doi.org/10.3390/e21090888
Zhang Z, Yu S. On the Security of a Latin-Bit Cube-Based Image Chaotic Encryption Algorithm. Entropy. 2019; 21(9):888. https://doi.org/10.3390/e21090888
Chicago/Turabian StyleZhang, Zeqing, and Simin Yu. 2019. "On the Security of a Latin-Bit Cube-Based Image Chaotic Encryption Algorithm" Entropy 21, no. 9: 888. https://doi.org/10.3390/e21090888
APA StyleZhang, Z., & Yu, S. (2019). On the Security of a Latin-Bit Cube-Based Image Chaotic Encryption Algorithm. Entropy, 21(9), 888. https://doi.org/10.3390/e21090888



