Abstract
The blind signature is widely used in cryptography applications because it can prevent the signer from gaining the original message. Owing to the unconditional security, the quantum blind signature is more advantageous than the classical one. In this paper, we propose a new provable secure quantum blind signature scheme with the nonorthogonal single-photon BB84-state and provide a new method to encode classical messages into quantum signature states. The message owner injects a randomizing factor into the original message and then strips the blind factor from the quantum blind signature signed by the blind signer. The verifier can validate the quantum signature and announce it publicly. At last, the analytical results show that the proposed scheme satisfies all of the security requirements of the blind signature: blindness, unforgeability, non-repudiation, unlinkability, and traceability. Due to there being no use of quantum entanglement states, the total feasibility and practicability of the scheme are obviously better than the previous ones.
1. Introduction
The security of classical signature cryptography depends on solving some difficult mathematical problems, such as factoring large integers and solving the discrete logarithm. It is known that these problems will become rather simple with the emergence of quantum computers. The quantum algorithm proposed by Shor [1] in 1994 can solve the problem of integer factorization in polynomial time. Accordingly, quantum cryptography will make a revolutionary impact on the classical one. One of the known examples of quantum cryptography is the quantum key distribution (QKD) [2,3,4,5], which offers a solution of the shared key exchange with information-theoretical security. Quite a few branches of QKD have attracted a great deal of attention, and many effective results have been proposed, including quantum private query (QPQ) [6,7,8], quantum digital signature (QDS) [9,10,11,12,13] and so on.
The first QDS scheme, which is analogous to the classical Lamport’s signature scheme, was proposed by Gottesman et al. [9] in 2001. In 2002, Zeng et al. [10] first proposed the arbitrated QDS scheme with GHZstates based on symmetric cryptography. In 2014, Dunjko et al. [11] proposed the first QDS scheme with no quantum memory, which made the quantum signature feasible and practicable under the current quantum technology. Wallden et al. [12] presented a QDS scheme with quantum-key-distribution components in 2015. In 2016, Amiri et al. [13] proposed a QDS scheme that did not require trusted quantum channels and only relied on secret shared keys generated using QKD. With the proposal of the measurement device-independent (MDI) QKD by Lo et al. [14], Puthoor et al. [15] first presented an MDI-QDS scheme, which is secure against all detector side-channel attacks. In 2017, Yin et al. [16] and Roberts et al. [17] made the attempt to implement experimentally the MDI-QDS.
The blind signature was first proposed by Chaum [18] in 1982. The blind signature can effectively prevent the blind signer from getting the original message because of its blindness, so it has a wide range of applications in the fields of E-commerce and block-chain. So far, some quantum blind signature (QBS) schemes [19,20,21,22,23,24,25,26,27,28,29,30,31,32,33] have been presented. In 2009, Wen et al. [19] first proposed the weak QBS scheme based on EPRpairs. In 2010, Su et al. [20] proposed a QBS scheme based on EPR with two-state vector formalism, and then, Yang et al. [21] pointed out some attacks on Su’s scheme [20] and proposed an enhanced one. However, Zhang et al. [22] declared that the dishonest signer could obtain some secret keys in Yang’s improved scheme [21]. In 2014, Khodambashi et al. [23] proposed a sessional QBS based on EPR, where the message signature cannot be forged by the dishonest verifier. In 2015, Shi et al. [24] proposed a new QBS scheme with unlinkability based on EPR and quantum teleportation. In 2017, Luo et al. [25] pointed out a security loophole of forgery in Shi’s QBS scheme [24]. With the -type entangled states, Yin et al. [26] proposed a QBS scheme in 2012. With the GHZ states, Wang et al. [27] proposed a QBS scheme in 2013. Zuo et al. [28] found that the dishonest verifier could forge the blind signature in [19,26,27]. Accordingly, Zuo et al. [28] and Ribeiro et al. [29] advised that a trusted center should be involved in QBS schemes. Based on offline trusted repositories, Ribeiro et al [29] presented a perfectly secure QBS scheme, which used Bell states, unitary operations, and so on, in 2015. With the two-photon entangled coding matrix to pass the secret shared key, Lai et al. [30] presented a QBS scheme in 2017. Besides the above QBS schemes with multiple photons, Wang et al. [31] proposed a fair QBS scheme with a single photon in 2010. However, He et al. [32] and Zou et al. [33] found that this scheme was vulnerable to non-forgeability attack. All these QBS schemes [19,20,21,22,23,24,25,26,27,28,29,30,31,32,33] are mainly divided into two broad categories: multi-photon entanglement QBS [19,20,21,22,23,24,25,26,27,28,29,30] and single-photon QBS [31,32,33]. Unlike the proposed QBS schemes with the single photon in [31,32,33], in this paper, we propose a new single-photon QBS scheme encoding with the indistinguishable BB84-state. To guarantee the unconditional security of the proposed scheme, we employ the quantum fingerprint [34] and Zhang et al.’s improved key-controlled-“T” quantum one time pad (QOTP) [35,36] based on Boykin and Roychowdhury’s QOTP [37]. In the proposed scheme, we give the hypothesis that a trusted arbitrator is known by all participants prior to the execution of the protocol. We give a proof of the correctness of the scheme. Security analyses show that the scheme satisfies all the properties of the blind signature: blindness, unforgeability, non-repudiation, unlinkability, and traceability.
2. Preliminary Theory
2.1. Properties of the Blind Signature
In general, a blind signature protocol includes four stages, namely message blinding, blind message signing, message unblinding, and signature verification. The original message owner, Alice, first makes a blind transformation on the original message m and gets blind message . Alice sends the transformed blind data to the blind signer, Bob. Then, Bob signs the and obtains the blind signature , and the signature is sent back to Alice. Alice strips the blind factor from the and gets the signature of the original message m. The verifier, Charlie, can verify the correctness of .
Generally speaking, a perfect blind signature should satisfy the following properties [18].
- Unforgeability: No one can generate an effective blind signature except the signer himself/herself. This is one of the most basic requirements.
- Non-repudiation: Once a signer has signed a message, he/she cannot deny his/her signature of the message.
- Blindness: Although a signer has signed a message, he/she cannot get the concrete content of the message.
- Unlinkability: Once the signature of the message is public, the signer cannot determine whether he/she has signed the message.
- Traceability: Once a dispute happens, the verifier can trace the signature.
The blind signature satisfying the above properties is considered to be secure. These five properties are the criteria that we should follow in designing blind signatures. The performance of the blind signature is also judged based on these properties.
2.2. Quantum Fingerprint
The quantum fingerprint [34], proposed by Buhrman et al. in 2001, is the most appealing protocol in quantum communication complexity (QCC) protocols [38,39]. In this model, two parties (Alice and Bob) select separately inputs x, and send their quantum fingerprints messages to a third party, called the Referee. The Referee must determine whether x equals y or not with a small error probability . To construct a large set of nearly orthogonal quantum states explicitly, consider an error-correcting code where the distance between distinct code words and is at least , here , , . For each , define the -qubit state:
Note that two distinct code words can be equal in at most positions for any . Consequently, each pair has an inner product . When the Referee receives the quantum fingerprints and , he measures and outputs the first qubit of the states -. By measuring the first qubit of this state with computational basis , the Referee outputs (meaning that ) with probability . The probability is zero if and at least if . Thus, the test determines which case holds with one-sided error probability . This error probability can be reduced to any by setting the fingerprint to for a suitable .
So far, several experiments [40,41,42,43,44] have reported successful attempts at implementing the quantum fingerprint.
2.3. Improved QOTP Encryption
In 2003, Boykin and Roychowdhury presented the QOTP encryption [37], which is used to encrypt securely n-qubit quantum states with the secret classical -bit key. Denote the n-qubit quantum message by and the n-qubit ciphertext message by , where , , = , . With the secret classical -bit key k, the QOTP encryption on can be described by and the corresponding decryption on by = . Since the original QOTP [37] is a bitwise protocol, Zhang et al. [35,36] pointed out that it would encounter forgery attack when it is used in the quantum signature. Now, some improved QOTP encryption schemes have been proposed, such as those in [35,36,45]. Since the location permutation of the quantum state is supplemented in the original QOTP, the improved QOTP schemes are no longer the bitwise encryption and provide higher security.
In order to use the improved QOTP to encrypt the classical message, some methods must be used to transform the classical message to the quantum one. Here, we give a simple example to demonstrate this one-to-one correspondence between them. Let us denote the n-bit classical message by and its corresponding n-qubit quantum one by = , where . When i is odd, encode with the rectilinear basis, namely , . When i is even, encode with the diagonal basis, namely , . According to the parity of the position of each quantum state, a different basis is used to measure the decrypted quantum state, so that the classical message can be recovered when decrypting. Because of the permutation of the quantum position, attacker cannot obtain M from the disordered quantum ciphertext by measurement without the secret key. For the sake of brevity and readability, the improved QOTP encryption on classical M is denoted by with the secret key k. Once the length of the message M exceeds n, we can divide M into several segments of length n and then encrypt them separately.
3. Quantum Blind Signature Scheme
We first give an encoding method of BB84-state so as to establish the one-to-one correspondence between the classical bit and the quantum one. With the BB84-state encoding, we then propose our new QBS scheme.
3.1. BB84-State Encoding
Let , where is the ith-bit in p (, in q, r, respectively), . We give an encoding rule that maps , to a quantum BB84-state in set and define:
For n-qubit , we define:
According to Equation (2), it is easy to draw the following conclusions, where ⊕ is the exclusive-or (XOR) operation and the symbol ≅ denotes the equivalence relation between two quantum states, which are different from constant coefficient (for instance, ).
Corollary 1.
Corollary 2.
Corollary 3.
.
Corollary 4.
.
Corollary 5.
.
Corollary 6.
, where ζ is an imaginary unit satisfying .
3.2. The Proposed Quantum Blind Signature Scheme
Substituting the quantum states for all or part of the classical messages, the so-called QBS inherits the definition and signature framework of the classical one. The QBS could achieve unconditional security through a combination of quantum theory and classical cryptography. The proposed signature scheme consists of the initial phase, the blinding phase, the signing phase, the unblinding phase, and the verifying phase.
3.2.1. Initial Phase
According to the different responsibilities in our proposed QBS scheme, there are five different roles: message owner, blind signer, verifier, arbitrator, and external attacker. Let Alice be the original message owner, Bob the blind signer, Charlie the signature verifier, Trent the arbitrator, and Eve the malicious external attacker. In the scheme, we give the hypothesis that Trent is known by all participants prior to the execution of the protocol and acts as the trusted arbitrator. In the remainder of this paper, we abbreviate Alice to A, Bob to B, Charlie to C, Trent to T, and Eve to E just for brevity. C shares each 2n-bit secret key and with A and B, respectively. T shares each 2n-bit secret key and with A and C, respectively. At the same time, A shares a 2n-bit secret key with B. These keys can be generated in a secure manner, e.g., direct face-to-face contact and QKD protocols with unconditional security such as [2,3,4,5].
3.2.2. Blinding Phase
Step B1. The message owner A first prepares the original message m of the n-bit string. Then, A selects randomly the blind factor w of the n-bit string and blinds m to blind message based on the formula .
Step B2. According to Equations (2) and (3), A generates n-qubit blind states with the n-bit blind message and key , where the n-bit is derived from the 2n-bit shared key satisfying , . According to Equation (1), A generates quantum fingerprint for blind message . With the shared key and , A applies the improved QOTP [35,36,45], which is described in Subsection 2.3, to encrypt her classical message m and blind factor w, and then obtains , where the notation denotes the concatenation of strings.
Step B3. A denotes and transmits to B through the quantum channel, where represents two copies of .
3.2.3. Signing phase
Step S1. Analogous to the method in Step B1, B obtains the n-bit key from the shared 2n-bit key between A and B. If the is zero, B selects the diagonal basis , otherwise rectilinear basis . According to this basis rule, B measures all the qubits of the indistinguishable BB84-state corresponding in and gets the blind message with the key .
Step S2. According to Equation (1), B generates quantum fingerprint . B then compares the generated with state from and judges whether they are equal based on quantum fingerprint theory in [34]. If they are not equal, then B stops the scheme, otherwise draws the conclusion and goes on.
Step S3. B first selects randomly two n-bit strings u and v. According to Equation (2) and Equation (1), B then generates respectively the QBS BB84-state and quantum fingerprint with u, v, and . With the shared key , B encrypts his strings u and v and then gets . From the receiving , B decrypts the with his shared key and gets , then encrypts it with his shared key and obtains . B denotes .
Step S4. B transmits and to A through the quantum channel.
3.2.4. Unblinding Phase
Step U1. After receiving the blind signature for blind message signed by B, A applies to with her blind factor w and gets , which is a quantum signature for the original message m. With the shared key , A generates and . A denotes .
Step U2. A generates and transmits it to T through the quantum channel.
Step U3. T decrypts the received and gets and . Then, T performs the C-SWAPtest [34] to compare the two copies of in . The same test is also done on . Once an unequal result of the comparison occurs, T draws the conclusion that the signature is invalid and aborts the process. After T finishes the comparison tests successfully, he preserves one copy of and to be prepared to solve disputes when they arise in the future. Finally, T generates with another copy of and and transmits it to C through the quantum channel.
3.2.5. Verifying Phase
Step V1. C first gets and from the received with his shared key . Then, C decrypts the in with his shared key , gets , and performs the C-SWAP test [34] to compare it with in . If the result of the comparison is not equal, C draws the conclusion that the signature is invalid and aborts the process. Otherwise, C then applies the key-controlled-“T” QOTP to decrypt with his shared key and finally gets (m, w).
Step V2. After getting from the , C decrypts with his shared key and then gets (u, v).
Step V3. From the received , C decrypts with his shared key and gets . With the m obtained in Step V1, C applies to and gets .
Step V4. With the u, v obtained in Step V2, C performs single-particle measurements on the n-qubit obtained in Step V3 and gets . The rules of measurement are as follows. According to Corollary 2, C uses diagonal basis to measure the BB84-state if , otherwise rectilinear basis . Based on the measurement result and Equation (2), C can deduce the corresponding , . C aborts the process if or for some , otherwise goes on.
Step V5. C generates quantum fingerprint with the deduced (u, v) and (m, w) and then compares it with in from B. If the result of comparison is equal, C draws the conclusion that the signature is valid, otherwise declares that the signature is not valid.
Step V6. According to Equation (2), C regenerates the quantum BB84-state signature with the known m, u, and v. C announces publicly the QBS correctness and declares the signature to the public.
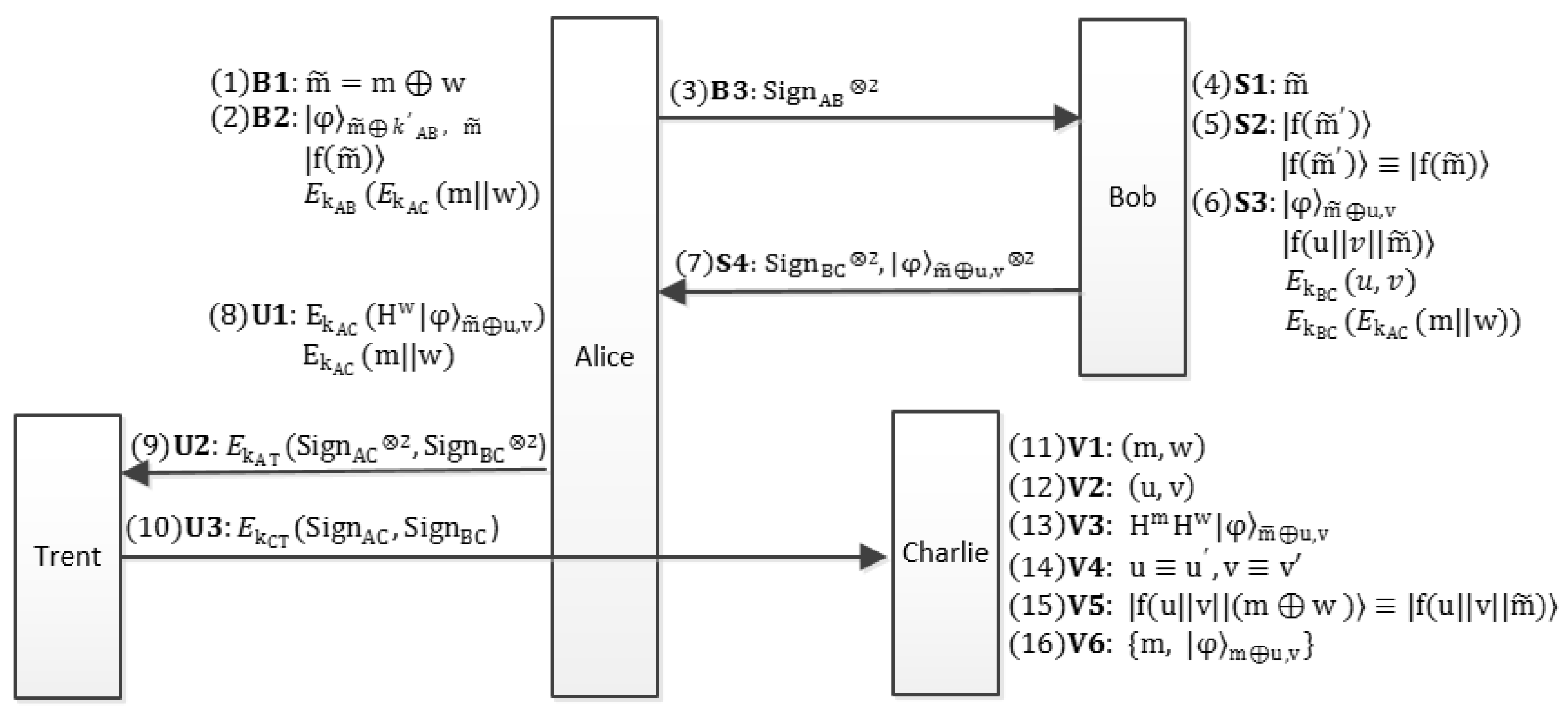
The whole flow-process diagram of the proposed QBS scheme is given in Figure 1.
Figure 1.
The flow-process diagram of the proposed QBS scheme. Alice blinds the message m with blind factor w and passes to Bob. With the proposed encoding method of the BB84-state, Bob signs with u and v and then sends the blind signature back to Alice. Two copies of the unblinding signature are sent to Trent. After Trent’s identical verification for the two signatures, one of the signatures is transmitted to Charlie. Once Charlie verifies the validity of the signature, he publishes the signature .
4. Security Analyses
In this section, we show that the proposed scheme is correct and satisfies the properties of blind signatures described in the preliminary section.
4.1. Correctness
Theorem 1.
The QBS scheme is correct.
Proof.
We prove the correctness of the scheme in two cases.
(1) B can correctly recover the blind message from A.
In the blinding phase, B received the from A. According to Corollary 2, the correct chosen basis (diagonal or rectilinear) to measure is determined by . In the cases in which A is an honest blind message sender and no eavesdropper E exists in the quantum channel, as long as B measures in the correct basis determined by the shared key , B will always get the correct blind message with the probability one by comparison of his measurement results with Equation (2). However, if A is not an honest blind message sender or eavesdropper E exists in the quantum channel, B will find, with high probability, a contradiction with the measurement results and aborts.
(2) C can correctly validate the quantum signature for A’s original message m.
After recovering the blind message from , B signs with his u and v and gets QBS based on Equation (2). Once A gets the QBS from B, she strips the blind factor w by applying to and gets quantum signature . In fact, according to Corollary 5, A obtains the result:
In Step V3, after receiving from A, C decrypts it and gets with his shared key , then applies to to generate , i.e.,
With the decrypted u and v from B, C selects a suitable basis and measures (namely, ). It is obvious that the measurement results must match u and v. Thus, we can draw the conclusion that C can correctly validate the quantum signature for A’s original message m. □
4.2. Against External Attack
It is impossible for external attacker E to attack a legitimate signature. Being external, the attacker has less available resources than A or B. The only way for him/her to obtain information is to intercept the quantum states or eavesdrop on the quantum channel. In the proposed scheme, there are three forms of quantum states on the quantum channel: quantum fingerprint states, BB84-states, and encrypted quantum states.
For the quantum fingerprint in the quantum channel, it is impossible for E to deduce conversely the original input on the basis of [34]. At the same time, if any quantum states are measured or replaced, this attack is detected by participants’ comparison of quantum fingerprint states. Therefore, it is impossible for E to forge the scheme by attacking the quantum fingerprint states.
Both BB84-states and encrypted quantum states, which are n-qubit tensor products, consist of elements in set . Assuming that the secret keys and signature parameters are uniformly distributed, each qubit is randomly located in one of two conjugate bases. Thus, the quantum states are essentially the same as the BB84 QKD one. According to the quantum indistinguishability, non-cloning, and immeasurability, E cannot distinguish the nonorthogonal states. E cannot perform the correct unitary operation for each photon. In terms of mathematical probability, he/she only speculates each photon state with the correct probability . Therefore, the probability of misjudgment for n photons is:
Obviously, this probability infinitely tends to one with the increase of n. E cannot obtain any message from the transmitted particles yet. Consider the density matrix of n particles,
This illustrates that the quantum states distribute in a uniform way so that no information might be leaked to the eavesdropper E. Consequently, external attack would not take effect.
4.3. Blindness
In the blinding phase, A sends the BB84-state , which contains blind message , to B. To measure using the corresponding basis matching the shared key , B can recover the blind message from A. For ; thus, B cannot recover m directly from known without w.
However, the blind signer B has two strategies to find some original message if A’s quantum signature is transmitted in the form (namely,) in . B’s first strategy is to measure A’s with computational basis or diagonal basis . Suppose ; once B measures the (namely, ) with the computational basis and gets the measurement result , he can come to the conclusion that cannot be and must be . This shows that Alice’s original message must be . On average, Bob’s strategy thus reveals bits of A’s original message. The result is the same for the use of the diagonal basis. B’s second strategy is to perform the C-SWAP test [34] between his and A’s if B can certainly confirm that A’s stripped signature corresponds to his blind signature . According to the comparison result, B can come to the conclusion that () if = (≠), and then, B can get A’s original message .
To avoid the two extreme strategies of B existing in his blind signature and A’s stripped one, the quantum signature is encrypted with the key in the proposed scheme, and then, is transmitted to C in Step U2. In such circumstances, the two strategies of B become invalid. Thus, our proposed scheme meets the standard of blindness.
4.4. Unforgeability
There are two kinds of forgeries. One forgery is done by the internal participants and the other by the external attacker E. The attacks of the internal participants involve message owner A, blind signer B, and the signature verifier C. With the following analyses, it can be shown that the two kinds of forgery cannot forge legitimate signatures so as to achieve the purpose of passing C’s verification.
The message owner A cannot forge the quantum signature. For the blind message corresponding to original message and blind factor , A would reach her purpose of forgery if she succeeds in forging message pair (, ) to replace the true message (, ) and making C validate it. Obviously, must be equal to , otherwise C will find the inconformity in Step V5. There are two ways for A to forge. One way is that A prepares the original message pair (, ) in Step B1 and in Step B2 and at the same time generates and in Step U1. In this way, C will find that (, ) is not equal (, ) and abort this signature. Thus, this strategy is unsuccessful. Another way for A’s forgery is to generate and in Step U1. This way can pass C’s examination in Step V1, but C would still find this strategy in Step V3 and Step V4. In Step V3, C applies to and gets:
Obviously, if the is not equal and thus is not equal to u, C would find this strategy with the examination in Step V4 for this way. Thus, the two forgery ways for A are not effective, and the unforgeability of the proposed scheme holds.
It is impossible for the blind signer B to forge a legitimate signature. The forgery way of B is to masquerade as the message owner A to sign the message alone and attempt to let the verifier C verify this forged signature. At first, B generates the forged message and the blind parameter . Then, B takes the place of A to get the unblinding quantum signature in Step U1. According to our scheme, and must be encrypted with the shared key , and then, will be transmitted to C. In Step V1, C decrypts with the shared key , but C cannot get the correct and because of B’s random guess key . In Step V4, C will find the forgery trick because the equations are not satisfied.
The signature verifier C cannot forge the quantum signature. After the arbitrator T receives the two copies of signatures encrypted with the shared key from A, he retains one copy and then encrypts another to C with shared key . If C forges a blind signature and tries to cheat the message owner A, it will cause a dispute. In this dispute, T can judge that C is the forger. This is because T retains a legitimate signature. According to the signature data provided by C, T can regenerate C’s signature. With the C-SWAP test [34], T can compare the preserved signatures with C’s forged signature and will find the inconformity, so C’s forgery strategy fails. Therefore, with the help of the trusted arbitrator T, C’s forgery strategy is not feasible.
4.5. Non-Repudiation
There are three possible ways for participants to repudiate the quantum signature afterwards. The first way is that A, the original message owner, repudiates that she has ever blinded message m to with random w in the blinding phase and stripped blind factor w from blind signature in the unblinding phase. The second way is that B, the blind signer, repudiates that he has signed the blind message with the random parameters u and v. The third way is that the signature verifier C denies that he has verified the legitimate signature from message owner A.
For A, she cannot repudiate her blinding behavior because she transmits the blind message encoding the quantum BB84-state with the shared key and the quantum fingerprint to B in the blinding phase. She cannot also repudiate her unblinding behavior because she encrypts the blind factor w with shared key and transmits to C in the unblinding phase.
For B, he encrypts his blind signature parameters u and v with the shared key and passes to C, so he cannot repudiate the behavior of his choosing of the parameters. Meanwhile, in the verifying phase, C generates and compares it to the receiving from B and thus further validates the signature parameters and denies A’s repudiation and B’s one as a whole.
For C, his undeniable attribute is determined by his declaration behavior in the verifying phase. That is to say, in several consecutive judgments, once C announces the correct judgment of the signature, he cannot deny all previous declarations including this one. The received , which is encrypted with his shared key , comes from the trusted arbitrator T. In Step V1 of the verifying phase, it indicates that the is equal in and . C confirms the fact of C not aborting the signature verification procedure. If so, C can not deny this verification step. In Step V4 of the verifying phase, C performs single-particle measurements on the quantum signature and deduces B’s signature parameters and . C would aborts the process if he finds disagreement between the derivative results and received results . Thus, C cannot deny his actions in this step. In Step V5 of the verifying phase, C validates the quantum fingerprint and judge A’s blind parameter w. Similarly, his announcement for A’s blindness cannot be disavowed. In the whole process, it shows that C has accepted the process of signature verification and cannot deny his validation fact if C does not abandon the verification in the verifying phase.
4.6. Unlinkability
Once the original message m and its quantum signature are public, the proposed scheme guarantees that the blind signer B cannot determine whether the open message m is associated with the blind message or not. Suppose C opens publicly two different signatures and ; the blind signer B can certainly validate the correctness of each signature with the open () and his secret u and v. Meanwhile, B can recover his blind signature with A’s blind message and B’s . Because B does not know A’s blind factors and , facing the open messages and , B cannot be sure whether his blind message is associated with the open message or besides only verifying the correctness of these signatures. Thus, this proposed scheme is shown to admit the property of unlinkability.
4.7. Traceability
The scheme is verified to satisfy the security demand of full traceability. Under the supervision of trusted arbitrator T, the verifier C is provided with traceability when the dispute occurs. Because the message owner A’s blind parameter w and original message m are all encrypted and transmitted to C, C can trace the whole original message sender A’s process. At the same time, C is traceable to B’s blind signature process because B’s blind signature parameters u and v are also encrypted and transmitted to C. Thus, this signature scheme satisfies the condition of traceability.
5. Conclusions
In this paper, we presented a new provable QBS scheme with the nonorthogonal single-photon BB84-state. We supposed that the arbitrator was trusted by everyone. Following the classical blind signature, our scheme consisted of the initial, blinding, signing, unblinding, and verifying phases. The original message owner was responsible for the blinding and unblinding messages. The duty of blind signer was to sign the blinding message without knowing the original message. When a dispute occurred, the trusted arbitrator could open the quantum signature to identify the original message owner, blind signer, or signature message verifier. Based on quantum indistinguishability, the quantum encryption algorithm, the quantum fingerprint, and so on, the scheme provided unconditional security. Differing from the previous QBS schemes with some security vulnerability in basis security requirements, the security analyses showed that the proposed scheme satisfied the five properties of the blind signature protocol. Therefore, our scheme could be safely applied in some special environments.
Based on the current development level of quantum experiment technology, it is not ideal enough to achieve multi-photon quantum entanglement in practice. Our scheme uses only the single-photon BB84-state instead of quantum multi-photon entanglement states. Therefore, under the current technology and experiment condition, our scheme is realizable. The technical threshold is low, so our scheme is practical and feasible.
Until now, all the current quantum signature schemes, including our proposed QBS scheme, have used quantum symmetric encryption technology, which would lead to some problems, such as the management, storage, and transmission of shared keys. It will be more convenient to realize the quantum signature if it does not rely on the quantum encryption technology, but quantum public-key cryptography as the classical signature. However, the current quantum public-key cryptography is still in the initial stage of research and not yet mature for use in the quantum digital signature. It is believed that the quantum signature will become more concise and easier to realize with the continuing development of quantum public-key cryptography in the future.
Author Contributions
F.-L.C. designed the scheme and wrote the manuscript; Z.-H.W. and Y.-M.H. analyzed the scheme’s security properties and approved the final manuscript.
Funding
This work was supported in part by the Natural Science Foundation of the Education Department of Anhui Province (Grant Nos. KJ2018A0363, KJ2017A356), the National Natural Science Foundation of China (Grant No. 61702012), and the University Outstanding Young Talent Support Project of Anhui Province of China (Grant No. gxyq2017026).
Conflicts of Interest
The authors declare that there is no conflict of interest regarding the publication of this paper.
References
- Shor, P.W. Algorithms for quantum computation: Discrete logarithms and factoring. In Proceedings of the 35th Annual Symposium on Foundations of Computer Science, Santa Fe, NM, USA, 20–22 November 1994; pp. 124–134. [Google Scholar]
- Bennett, C.H.; Brassard, G. Quantum cryptography: Public key distribution and coin tossing. Theor. Comput. Sci. 2014, 560, 7–11. [Google Scholar] [CrossRef]
- Bennett, C.H. Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 1992, 68, 3121–3124. [Google Scholar] [CrossRef]
- Ekert, A.K. Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 1991, 67, 661–663. [Google Scholar] [CrossRef] [PubMed]
- Sasaki, T.; Yamamoto, Y.; Koashi, M. Practical quantum key distribution protocol without monitoring signal disturbance. Nature 2014, 509, 475–478. [Google Scholar] [CrossRef] [PubMed]
- Giovannetti, V.; Lloyd, S.; Maccone, L. Quantum private queries. Phys. Rev. Lett. 2008, 100, 230502. [Google Scholar] [CrossRef] [PubMed]
- Liu, B.; Gao, F.; Huang, W.; Wen, Q.Y. QKD-Based quantum private query without a failure probability. Sci. China-Phys. Mech. Astron. 2015, 58, 100301. [Google Scholar] [CrossRef]
- Wei, C.Y.; Cai, X.Q.; Liu, B.; Wang, T.-Y.; Gao, F. A Generic Construction of Quantum-Oblivious- Key-Transfer-Based Private Query with Ideal Database Security and Zero Failure. IEEE Trans. Comput. 2018, 67, 2–8. [Google Scholar] [CrossRef]
- Gottesman, D.; Chuang, I. Quantum digital signatures. arXiv, 2001; arXiv:quant-ph/0105032. [Google Scholar]
- Zeng, G.H.; Keitel, C.H. Arbitrated quantum-signature scheme. Phys. Rev. A 2002, 65, 042312. [Google Scholar] [CrossRef]
- Dunjko, V.; Wallden, P.; Andersson, E. Quantum digital signatures without quantum memory. Phys. Rev. Lett. 2014, 112, 040502. [Google Scholar] [CrossRef]
- Wallden, P.; Dunjko, V.; Kent, A.; Andersson, E. Quantum digital signatures with quantum key distribution components. Phys. Rev. A 2015, 91, 042304. [Google Scholar] [CrossRef]
- Amiri, R.; Wallden, P.; Kent, A.; Andersson, E. Secure quantum signatures using insecure quantum channels. Phys. Rev. A 2016, 93, 032325. [Google Scholar] [CrossRef]
- Lo, H.-K.; Curty, M.; Qi, B. Measurement-Device-Independent Quantum Key Distribution. Phy. Rev. Lett. 2012, 108, 130503. [Google Scholar] [CrossRef]
- Puthoor, I.V.; Amiri, R.; Wallden, P.; Curty, M.; Andersson, E. Measurement-device-independent quantum digital signatures. Phy. Rev. A 2016, 94, 022328. [Google Scholar] [CrossRef]
- Yin, H.L.; Wang, W.L.; Tang, Y.L.; Zhao, Q.; Liu, H.; Sun, X.-X.; Zhang, W.-J.; Li, H.; Puthoor, I.V.; You, L.-X.; et al. Experimental measurement-device-independent quantum digital signatures over a metropolitan network. Phy. Rev. A 2017, 95, 042338. [Google Scholar] [CrossRef]
- Roberts, G.L.; Lucamarini, M.; Yuan, Z.L.; Dynes, J.F. Experimental measurement-device-independent quantum digital signatures. Nat. Comun. 2017, 8, 1098. [Google Scholar] [CrossRef] [PubMed]
- Chaum, D. Blind signature for untraceable payments. In Advances in Cryptology; Springer: Boston, MA, USA; pp. 199–203.
- Wen, X.; Niu, X.; Ji, L.; Tian, Y. A weak blind signature scheme based on quantum cryptography. Opt. Commun. 2009, 282, 666–669. [Google Scholar] [CrossRef]
- Qi, S.; Zheng, H.; Wen, Q.; Li, W. Quantum blind signature based on two-state vector formalism. Opt. Commun. 2010, 283, 4408–4410. [Google Scholar] [CrossRef]
- Yang, C.W.; Hwang, T.; Luo, Y.P. Enhancement on “quantum blind signature based on two-state vector formalism”. Quantum Inf. Process. 2012, 12, 109–117. [Google Scholar] [CrossRef]
- Zhang, M.; Xu, G.A.; Chen, X.B.; Yang, S.; Yang, Y.-X. Attack on the improved quantum blind signature protocol. Int. J. Theor. Phys. 2013, 52, 331–335. [Google Scholar] [CrossRef]
- Khodambashi, S.; Zakerolhosseini, A. A sessional blind signature based on quantum cryptography. Quantum Inf. Process. 2014, 13, 121–130. [Google Scholar] [CrossRef]
- Shi, W.M.; Zhang, J.B.; Zhou, Y.H.; Yang, Y.G. A new quantum blind signature with unlinkability. Quantum Inf. Process. 2015, 14, 3019–3030. [Google Scholar] [CrossRef]
- Luo, Y.P.; Tsai, S.L.; Hwang, T.; Kao, S.H. On “a new quantum blind signature with unlinkability”. Quantum Inf. Process. 2017, 16, 87. [Google Scholar] [CrossRef]
- Yin, X.; Ma, W.; Liu, W. A blind quantum signature scheme with χ-type entangled states. Int. J. Theor. Phys. 2012, 51, 455–461. [Google Scholar] [CrossRef]
- Wang, M.M.; Chen, X.B.; Yang, Y.X. A blind quantum signature protocol using the GHZ states. Sci. China Phys. Mech. Astron. 2013, 56, 1636–1641. [Google Scholar] [CrossRef]
- Zuo, H.J. Cryptanalysis of quantum blind signature scheme. Int. J. Theor. Phys. 2013, 52, 322–329. [Google Scholar] [CrossRef]
- Ribeiro, J.; Souto, A.; Mateus, P. Quantum blind signature with an offline repository. Int. J. Quantum Inf. 2015, 13, 1550016. [Google Scholar] [CrossRef]
- Lai, H.; Luo, M.X.; Pieprzyk, J.; Qu, Z.G.; Li, S.; Orgun, M.A. An efficient quantum blind digital signature scheme. Sci. China Inf. Sci. 2017, 60, 082501. [Google Scholar] [CrossRef]
- Wang, T.Y.; Wen, Q.Y. Fair quantum blind signatures. Chin. Phys. B 2010, 19, 0307. [Google Scholar]
- He, L.B.; Huang, L.S.; Yang, W.; Xu, R. Cryptanalysis of fair quantum blind signatures. Chin. Phys. B 2012, 21, 030306. [Google Scholar] [CrossRef]
- Zou, X.F.; Qiu, D.W. Attack and improvements of fair quantum blind signature schemes. Quantum Inf. Process. 2013, 12, 2071–2085. [Google Scholar] [CrossRef]
- Buhrman, H.; Cleve, R.; Watrous, J.; De, W.R. Quantum Fingerprinting. Phys. Rev. Lett. 2001, 87, 167902. [Google Scholar] [CrossRef] [PubMed]
- Zhang, K.J.; Zhang, W.W.; Li, D. Improving the security of arbitrated quantum signature against the forgery attack. Quantum Inf. Process. 2013, 12, 2655–2669. [Google Scholar] [CrossRef]
- Zhang, K.J.; Qin, S.J.; Sun, Y.; Song, T.T.; Su, Q. Reexamination of arbitrated quantum signature: the impossible and the possible. Quantum Inf. Process. 2013, 12, 3127–3141. [Google Scholar] [CrossRef]
- Boykin, P.; Roychowdhury, V. Optimal encryption of quantum bits. Phys. Rev. A 2003, 67, 042317. [Google Scholar] [CrossRef]
- Brassard, G. Quantum communication complexity (a survey). arXiv, 2001; arXiv:quant-ph/0101005. [Google Scholar]
- Buhrman, H.; Cleve, R.; Massar, S.; Wolf, R.D. Non-Locality and communication complexity. Rev. Mod. Phys. 2009, 82, 665–698. [Google Scholar] [CrossRef]
- Horn, R.T.; Babichev, S.A.; Marzlin, K.P.; Lvovsky, A.I.; Sanders, B.C. Single-Qubit optical quantum fingerprinting. Phys. Rev. Lett. 2005, 95, 150502. [Google Scholar] [CrossRef]
- Du, J.; Zou, P.; Peng, X.; Oi, D.K.L.; Kwek, L.C.; Oh, C.H.; Ekert, A. Experimental quantum multimeter and one-qubit fingerprinting. Phys. Rev. A 2006, 74, 042319. [Google Scholar] [CrossRef]
- Xu, F.; Miguel, A.J.; Wei, K.; Wang, W.; Palacios-Avila, P.; Feng, C.; Sajeed, S.; Lütkenhaus, L.; Lo, H.-K. Experimental quantum fingerprinting with weak coherent pulses. Nat. Commun. 2015, 6, 8735. [Google Scholar] [CrossRef] [PubMed]
- Arrazola, J.M.; Lutkenhaus, N. Quantum fingerprinting with coherent states and a constant mean number of photons. Phys. Rev. A 2014, 89, 062305. [Google Scholar] [CrossRef]
- Guan, J.Y.; Xu, F.; Yin, H.L.; Li, Y.; Zhang, Y.-J.; Chen, S.-J.; Yang, X.-Y.; Li, L.; You, L.-X.; Chen, T.-Y.; et al. Observation of Quantum Fingerprinting Beating the Classical Limit. Phys. Rev. Lett. 2016, 116, 240502. [Google Scholar] [CrossRef]
- Li, F.G.; Shi, J.H. An arbitrated quantum signature protocol based on the chained CNOT operations encryption. Quantum Inf. Process 2015, 14, 2171–2181. [Google Scholar] [CrossRef]
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).