Construction of Fractional Repetition Codes with Variable Parameters for Distributed Storage Systems
Abstract
:1. Introduction
2. Preliminaries
2.1. Regenerating Codes and Fractional Repetition Codes
- ;
- for ;
- each symbol of belongs to exactly ρ subsets in .
2.2. Related Works
2.3. Perfect Difference Families
- (1)
- A PDF exists for .
- (2)
- A QPDF exists for .
- (3)
- A PDF exists for or .
- (4)
- PDFs are known for but for no other values in .
- (5)
- There is no PDF for .
- ;
- ;
- ;
- ;
- ;
3. FR Codes Based on PDFs or QPDFs
3.1. Construction
- 1.
- Choose n, α, and ρ so that they satisfy
- (i)
- ,
- (ii)
- , where t is an integer,
- (iii)
- is an integer which satisfies the condition for the existence of (Q)PDF shown in Theorem 1,
- (iv)
- if PDF exists, or if QPDF exists.
- 2.
- Construct a (Q)PDF , .
- 3.
- Select t subsets , from the (Q)PDF of subsets.
- 4.
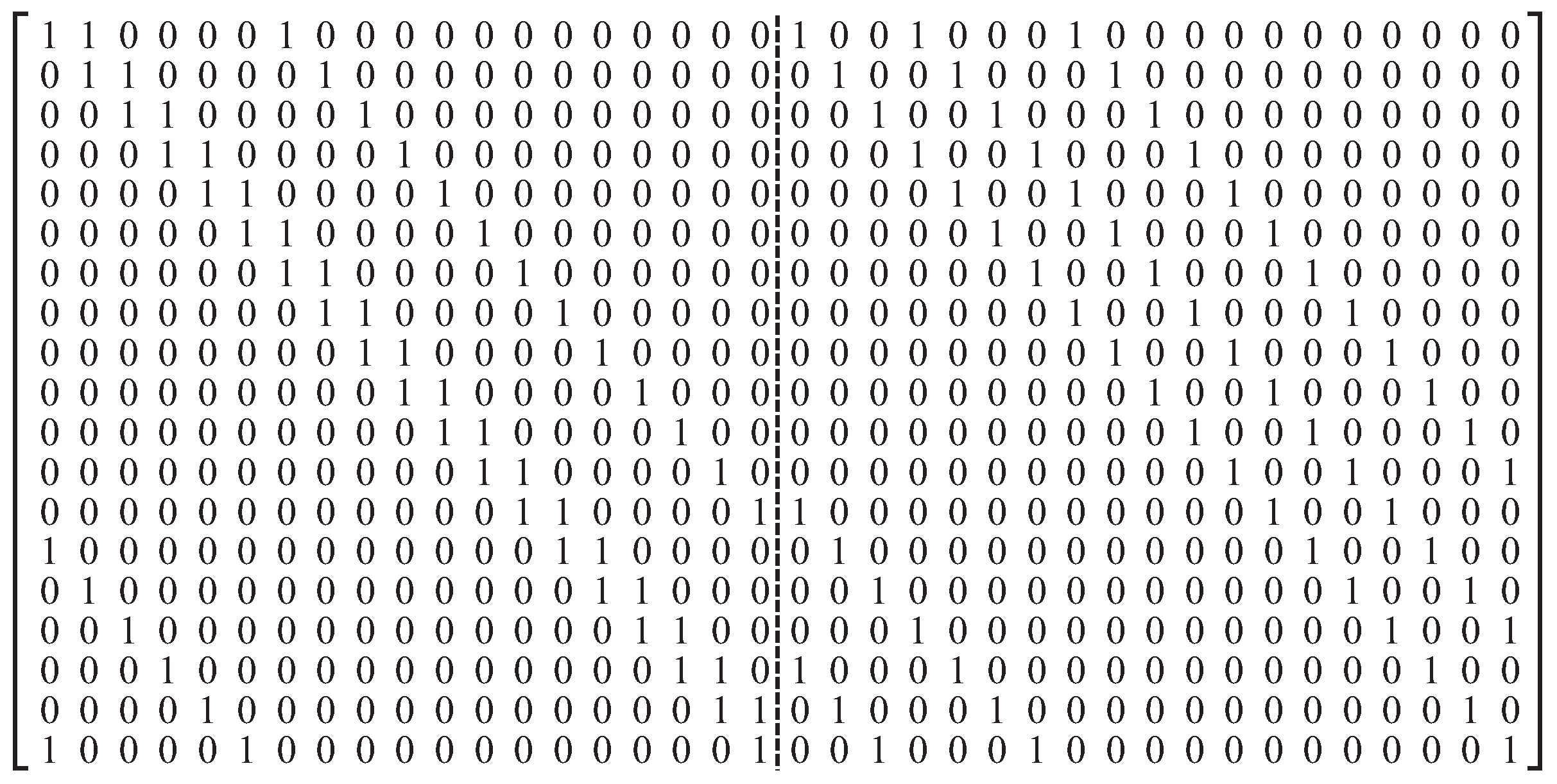
- Construct an FR code such that the set of locations of 1’s in the j-th row of the incidence matrix is , , , .
3.2. Analysis of the Proposed Construction
3.3. Comparison with Existing Codes
4. Concluding Remarks
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Kim, S.-H.; Lee, I.-Y. Block access token renewal scheme based on secret sharing in Apache Hadoop. Entropy 2014, 16, 4185–4198. [Google Scholar] [CrossRef]
- Tamura, Y.; Yamada, S. Reliability analysis based on a jump diffusion model with two Wiener processes for cloud computing with big data. Entropy 2015, 17, 4533–4546. [Google Scholar] [CrossRef]
- Gopalan, P.; Huang, C.; Simitci, H.; Yekhanin, S. On the locality of codeword symbols. IEEE Trans. Inf. Theory 2012, 58, 6925–6934. [Google Scholar] [CrossRef]
- Papailiopoulos, D.S.; Dimakis, A.G. Locally repairable codes. IEEE Trans. Inf. Theory 2014, 60, 5843–5855. [Google Scholar] [CrossRef]
- Song, W.; Dau, S.H.; Yuen, C.; Li, J. Optimal locally repairable linear codes. IEEE J. Sel. Areas Commun. 2014, 32, 1019–1036. [Google Scholar] [CrossRef]
- Song, W.; Yuen, C. Binary locally repairable codes—Sequential repair for multiple erasures. In Proceedings of the 2016 IEEE Global Communications Conference, Washington, DC, USA, 4–8 December 2016.
- Dau, S.H.; Kiah, H.M.; Song, W.; Yuen, C. Locally encodable and decodable codes for distributed storage systems. In Proceedings of the 2015 IEEE Global Communications Conference, San Diego, CA, USA, 6–10 December 2015.
- Dimakis, A.G.; Godfrey, P.B.; Wainwright, M.J.; Ramchandran, K. Network coding for distributed storage systems. In Proceedings of the 2007 IEEE International Conference on Computer Communications, Anchorage, AK, USA, 6–12 May 2007; pp. 2000–2008.
- Wu, Y.; Dimakis, A.G.; Ramchandran, K. Deterministic regenerating codes for distributed storage. In Proceedings of the 2007 Annual Allerton Conference on Communication, Control, and Computing, Monticello, IL, USA, 28–30 September 2007.
- Van, V.T.; Yuen, C.; Li, J. Non-homogeneous distributed storage systems. In Proceedings of the Annual Allerton Conference on Communication, Control, and Computing, Monticello, IL, USA, 1–5 October 2012; pp. 1133–1140.
- Pernas, J.; Yuen, C.; Gastón, B.; Pujol, J. Non-homogeneous two-rack model for distributed storage systems. In Proceedings of the 2013 IEEE International Symposium on Information Theory, Istanbul, Turkey, 7–12 July 2013; pp. 1237–1241.
- Rashmi, K.V.; Shah, N.B.; Kumar, P.V. Optimal exact-regenerating codes for distributed storage at the MSR and MBR points via a product-matrix construction. IEEE Trans. Inf. Theory 2011, 57, 5227–5239. [Google Scholar] [CrossRef]
- Tian, C. Characterizing the rate region of the (4, 3, 3) exact-repair regenerating codes. IEEE J. Sel. Areas Commun. 2014, 32, 967–975. [Google Scholar] [CrossRef]
- Rouayheb, S.E.; Ramchandran, K. Fractional repetition codes for repair in distributed storage systems. In Proceedings of the Annual Allerton Conference on Communication, Control, and Computing, Urbana-Champaign, IL, USA, 29 September–1 October 2010; pp. 1510–1517.
- Koo, J.C.; Gill, J.T., III. Scalable constructions of fractional repetition codes in distributed storage systems. In Proceedings of the Annual Allerton Conference on Communication, Control, and Computing, Urbana-Champaign, IL, USA, 28–30 September 2011; pp. 1366–1373.
- Olmez, O.; Ramamoorthy, A. Fractional repetition codes with flexible repair from combinatorial designs. IEEE Trans. Inf. Theory 2016, 62, 1565–1591. [Google Scholar] [CrossRef]
- Zhu, B.; Shum, K.W.; Li, H.; Hou, H. General fractional repetition codes for distributed storage systems. IEEE Commun. Lett. 2014, 18, 660–663. [Google Scholar] [CrossRef]
- Zhu, B.; Shum, K.W.; Li, H. Heterogeneity-aware codes with uncoded repair for distributed storage systems. IEEE Commun. Lett. 2015, 19, 901–904. [Google Scholar] [CrossRef]
- Silberstein, N.; Etzion, T. Optimal fractional repetition codes based on graphs and designs. IEEE Trans. Inf. Theory 2015, 61, 4164–4180. [Google Scholar] [CrossRef]
- Pawar, S.; Noorshams, N.; Rouayheb, S.E.; Ramchandran, K. DRESS codes for the storage cloud: Simple randomized constructions. In Proceedings of the 2011 IEEE International Symposium on Information Theory, St. Petersburg, Russia, 31 July–5 August 2011; pp. 2338–2342.
- Yu, Q.; Sung, C.W.; Chan, T.H. Irregular fractional repetition code optimization for heterogeneous cloud storage. IEEE J. Sel. Areas Commun. 2014, 32, 1048–1060. [Google Scholar] [CrossRef]
- Colbourn, C.J.; Dinitz, J.H. Handbook of Combinatorial Designs, 2nd ed.; CRC Press: Boca Raton, FL, USA, 2007. [Google Scholar]


© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Park, H.; Kim, Y.-S. Construction of Fractional Repetition Codes with Variable Parameters for Distributed Storage Systems. Entropy 2016, 18, 441. https://doi.org/10.3390/e18120441
Park H, Kim Y-S. Construction of Fractional Repetition Codes with Variable Parameters for Distributed Storage Systems. Entropy. 2016; 18(12):441. https://doi.org/10.3390/e18120441
Chicago/Turabian StylePark, Hosung, and Young-Sik Kim. 2016. "Construction of Fractional Repetition Codes with Variable Parameters for Distributed Storage Systems" Entropy 18, no. 12: 441. https://doi.org/10.3390/e18120441
APA StylePark, H., & Kim, Y.-S. (2016). Construction of Fractional Repetition Codes with Variable Parameters for Distributed Storage Systems. Entropy, 18(12), 441. https://doi.org/10.3390/e18120441






