1. Introduction
Identity theft and account hacking are significant security threats in the digital era. Today’s societies are deeply interconnected and reliant on digitally offered services with most of the peoples’ everyday dealings, including banking and their payments, happening online and via mobile devices.
Have I been pwned (
https://haveibeenpwned.com/ Visited Oct 2020) is an online database comprising leaked credentials for accounts claiming to consist of over 10 billion usernames and passwords.
The consequences and effect propagation of identity theft are further intensified when considering the potential for social engineering through social media (SoMe) misuse. In the past, a multitude of hacked SoMe accounts have been exploited to disseminate lies, spearhead phishing campaigns, request and process illegitimate payments and even influence the stock markets. A well-known case of a high profile SoMe account that was hacked could be Skype’s Twitter account back in 2014 (
https://www.theverge.com/2014/1/1/5264540/skype-twitter-facebook-blog-accounts-hacked), that was employed by the attackers to post a tweet with the text “Do not use Microsoft emails...”.
Given the plethora of relevant attack vectors and the probable direct impact on the general population, it is essential to establish suitable awareness campaigns to enhance the security posture of the society and lessen the impact of such attacks, as discussed by Al-Charchafchi et al. [
1] who reviewed threats against information privacy and security in social networks. The initial step in this direction is to analyse how people perceive the risk they are exposed to when using SoMe and assess the impact of specific indicators (such as age and sex) when evaluating such risks. Such an analysis must be undertaken taking into account the national or regional context, such as ICT (Information and Communication Technologies) penetration, digital preparedness and acceptance metrics, avoiding unfounded generalisations across borders or groups. Thus, national and regional studies can offer a suitable mapping of the current societal security posture, preparedness and resilience, as well as suitable metrics to establish enhancement methods.
Accordingly, in this study we focus on the Norwegian population, measuring public risk perception on the use of SoMe, reviewing what people freely post and how an attacker can exploit this content, also focusing on how being a victim of identity theft affects a posteriori risk perception and usage patterns. This study was motivated by the fact that the Norwegian society is highly digitised, steadily achieving growing Digital Economy and Society Index (DESI) scores for the past years while consistently being evaluated above the EU average, with a 2020 score of 69.5 against an EU average of 52.6.
SoMe are extensively utilised while being an open platform where people tend to over-share. This over-sharing might cause break-ins, a stolen identity, stalking and more, physical or virtual consequences. For example, houses being targeted while people are on holiday or accounts being hijacked by an attacker using social engineering. The security risk might not be the primary thought of people when posting information online, even though they might volunteer more information than one might think is prudent, had they shared the same information in real life/in person.
The Norwegian data authority defines identity theft as: Identity theft is when someone obtains, possesses, transfers, uses or appears as the rightful holder of an identification card or the personal information of a person to commit financial fraud, fraud or other crime, while the Norwegian punitive law §202 stipulates:
a fine or imprisonment of up to 2 years, the person who unjustifiably takes possession of another person’s identity card, or acts with another’s identity or with an identity that is easily confused with another’s identity, with the intention to obtain an unjustified gain for himself or another, or inflict another loss or disadvantage.
Additionally, this paper examines variations in risk perceptions between digital natives and non-natives, where digital natives are defined as people born after 1987 [
2]. The contributions of this article are:
Investigate the following areas in sharing habits and exploitation for ID theft on SoMe in Norway.
- (a)
Are there differences in security routines between Digital natives and non-natives?
- (b)
Are there differences in security routines between genders?
- (c)
Does having suffered ID or account theft change security routines?
Investigate how people perceive the risk of ID theft on SoMe.
- (a)
Differences in risk perceptions across popular SoMe platforms (Facebook, Twitter, Reddit and Snapchat)
- (b)
Are there differences in risk perceptions between digital natives and non-natives?
- (c)
Are there differences in risk perceptions between genders?
- (d)
Does having suffered ID or account theft change risk perceptions on sharing habits?
How does ID theft occur and what are the consequences?
As detailed in the research questions above, the included SoMe platforms are Facebook, Twitter, Reddit and Snapchat. A brief description of these services is a follows (worldwide user estimates were collected from Oberlo.com for October 2020): Facebook is a social media platform that offers the opportunity to mostly vet who may see things about you and who can see your posts. Some information are not private by default, like friends list and information about the account holder. Facebook has 2.7 billion users. Twitter is a micro-blogging service where everything that is posted there is public by default. How one connects on Twitter is by actively choosing to follow different people. Compared to Facebook, where both parties have to actively accept becoming friends, one can follow whoever they want on Twitter without them having to say yes or no. The platform has a character count maximum of 240 characters, to keep the posts (tweets) short. Twitter is estimated to have 340 million users worldwide. Reddit is a social media that is more anonymous by nature, while very few subscribers use their name on their Reddit profiles. Reddit is partitioned into different subreddits where people can come together as various parties interested in the same thing; for example, there are subreddits for cats, politics and games. With how Reddit is structured there is a risk for Echo chambers to be formed, where people of the same thought keep agreeing to each other. Reddit is estimated to have 430 million users. Finally, Snapchat is a picture sharing service, where images one sends also get deleted after a set amount of time, and after the recipient has viewed an image, it gets deleted. If the recipient takes a screenshot of the image that they receive, the sender of the message receives a notification. Snapchat is estimated to have 230 million users worldwide.
A recent study by Studen [
3] investigated social media as a cultural and economic phenomenon, exploring their expected future developments through an international two-stage Delphi study. The study indicates that enhanced interaction on platforms, as well as platform diversification is expected, promoting social media as the predominant news distributor, also increasing their societal and psychological impact. Our principal contribution is knowledge regarding the risk perceptions concerning ID theft using SoMe platforms, and how users perceive the risk of conducting certain activities on the surveyed platforms. Our paper outlines which information assets the participants deem worthy of protection and what they fear on SoMe. Our paper proposes a novel threat model for SoMe users derived from the results. Finally, we go in depth into how ID theft occurs, and the suffered and perceived consequences of suffering a security breach.
We have structured the remainder of this article as follows: The following section presents related work focusing among others on the areas of risk perception, ID theft and social media.
Section 2 presents the methods used for this study discussing the instrument and the processes used for recruitment, data collection and analysis.
Section 3 presents the sample demographics and discusses the representativity of the sample. Furthermore,
Section 4 contains the complete analysis of the results, separating them into three major categories, firstly referring to routines, then risk perception and finally, risk perception alterations after suffering identity theft.
Section 5 summarises the results and discusses the research questions. Lastly, we present the conclusions, which provide key takeaways and close the paper. The conclusions also include research limitations, impacts and recommendations for future research.
2. Related Work
There are multiple studies on risk perception, compromised accounts and SoMe, in this section we will explore some of these works to give the reader a better impression of the foundations for the development of this paper.
Several studies focus on the foundations of risk perception measurement: Slovic, Fischhoff and Lichtenstein [
4] explored risk perception and explained that people, when asked about the risk of something, rarely have any data readily at hand to help them calculate the risk. With the lack of data to use as a reference, people usually end up using heuristics when assigning risk. These heuristics create misalignments between the actual risk and the perceived risk, that experts should try to close when discussing risk with a layperson. Additionally, Alhakami and Slovic [
5] explore how risk and benefit relate to each other. They observed that if the perceived risks were high, the perceived benefits would be perceived as low, and something that is perceived to have high benefit is commonly perceived to have low risk. The authors asked psychology students to rate how risky something was towards the US. The students could rate the risks on a scale from 1—not at all risky, to 7—very risky. They found that in fact, perceived risk and perceived benefit correlate to each other. Furthermore, Slovic et al. [
6] examined how experience changes how we perceive risk, and how heuristics change how a person perceives the risk of an event. They mention how risks can be perceived by a person in two different ways which they have from Loewenstein et al. [
7]; one is the rationale system, meaning how people rationally react to risk, this would be the common understanding of risk consequence times likelihood. The other way he mentions we react to risk is the emotional reaction when an event happens. Loewenstein mentions that researchers should take into account such an emotional reaction to risks. Worth mentioning are the findings by Gustafsod [
8], who wrote a paper about how men and women perceive risk differently. The findings document the existing around gender differences and risk perception. Most papers he saw that tackled risk perception had a quantitative method where you ended up with females having a higher perceived risk. He talks a bit about how the power relations between males and females on how women often fear crime and that this stems from fear of male sexual violence.
Other ground breaking work within the measurement of risk perception focus on the “Risk compensation model” by Adams [
9]; the “presentation of risk information” and the “Availability of risk information” discussed by Kahneman [
10]; the psychometric based “Expressed risk preferences” and the “Affect in risk perception” [
11] which evaluates the affect of heuristic in judgments of risks and benefits.
Accordingly, it becomes clear that a variety of theoretical and empirically supported approaches have been developed in order to support the understanding of how risk perceptions may be shaped, as discussed by Paul van Schaik [
12], whose study motivates further efforts into identifying the determinants of people’s behaviour towards cyber risk on the Internet. Furthermore, Yixin Zou [
13] conducted a survey investigating the acceptance of commonly recommended online safety practices (on security, privacy and identity theft protection), establishing both discrepancies and the respective reasons for non-compliance.
Another aspect that may influence risk perception is security awareness. Focusing on rural Norway, an earlier stydy by Gunleifsen et al. [
14] researched security awareness, perceptions and the culture of participants from rural Norway. They collected the sample from a broadband subscriber list and had n = 945 with 76% males and an average age of 56 years. The authors surveyed attitude toward IT, knowledge, risk evaluations, trust in authorities, training preferences and compare risk-evaluations with their online behaviour. The results show that the level of security awareness is highly subjective and that training programs and security awareness campaigns are both needed and requested by end-users. The risk perception part of Gunleifsen et al. measures confidence in the ability to judge what is safe or not in cyberspace, and how much the participants worry about certain abuse scenarios.
Additionally, like the study presented in this article, what happens to people after having been victims of identity theft is explored in the paper by Golladay and Holtfreter [
15] where they explore the health detriments, and the emotional harms that being a victim of identity theft, can cause. They found that, for example, age impacts the emotional response of a victim where older people get affected more than younger people. In a broader scope, a report by Newman [
16] discusses various aspects of ID theft, including its various types, victims demographics and the typology of the offenders, also including an analysis regarding the various costs of ID theft at the financial, personal and societal levels. This report, that has been funded by the U.S. Department of Justice, explicitly recommends future research on routine activities and decisions that lead to the victimisation of individuals, in order to identify vulnerable populations and identify behavioural patterns that may lead to effective interventions.
Additionally, a wide variety of studies has explored specific aspects of ID theft, focusing on specific target groups, application domains and technologies, or sectors.
Jagatic et al. wrote a paper [
17] where they tried to see if knowing the person who sends a phishing link affects the trust in the link provided, this was done by emailing different students at Indiana University where they spoofed the sender of the emails, to create more trust towards the phishing link and site provided by an attacker. They found that people were much more likely to click and expose their information if they provided the phishing link this way. They created one control group and one where they spoofed the email, the control group had a 16 percent success rate, while the spoofed email one had a 72 percent success rate, showing that trust in the sender makes a big difference in a successful phish. Milne, Rohm and Bahl [
18] looks at how consumers protect their personal information on the internet regarding the threat of identity theft and seeing if there are any predictors for the level of online protection is practiced. This study was done using three different surveys using multiple different demographics across the US. The surveys had some questions built upon the “best practices” for ensuring data privacy by the Centre for Democracy and Technology (2003). This paper was inspiring to look at for how they researched identity theft. One question they asked were if people “Refused to give information to a website because you felt it was too personal”.
Furthermore, Thomas et al. [
19] had a year-long study where they explored exposed credentials and the match rate with google accounts. They had three datasets they used for the leaked credentials during the study, one from just usual credential leaks, one from phishing kits and the last one from keyloggers. They found that from the credential leaks they looked at, there was a match rate of 6.9%, The phishing kits had a match rate of 24.8% and the keyloggers match rate was 11.9%. The match rate they talked about was still active and usable credentials. Finally, Nyblom et al. [
20] used a root cause method to find out what the root cause of compromised accounts were at a university. They found that one of the most significant contributors to compromised user accounts had been the reuse of credentials on different sites which made up 42% of the hacked accounts, the next was password strength at 25%, malware at 19% and phishing at 10%. As discussed earlier, these studies, although they may appear fragmented, are targeted by design to specific target groups, indicators or technologies, narrowing the scope and allowing the construction of a more complete and detailed picture regarding the determinants of human behaviour towards cyber risk.
Ur and Wang [
21] constructed a framework for what a user of social media should ask themselves, to have the users from a diverse set of backgrounds have a good enough privacy according to their culture. One layer in the framework was a legal layer, and here, the social media could ask themselves if they are compliant to for example European law, like the General Data Protection Regulation (GDPR).
Focusing on social media, the paper by Such and Cirado [
22] explores not just the privacy implications of one person sharing information about him or herself, but includes people getting information disclosed about themselves from others posting information on social media platforms. The paper also shows several coping strategies for how one can and should share information on social media, and what the major drawbacks these coping strategies might have. It also proposes some different strategies that can be used when posting multi-party privacy-related posts. A similar study to this one was conducted by Schaik et al. [
23], which measured risk perceptions of security and privacy in online social networking. The study applied psychometric methods to survey 201 Facebook users from the UK. Their primary findings was that the concern was highest for information-sharing related to privacy. An additional aspect that has been examined in the literature is specific strategies to protect the privacy of users, and potential impact of integrating privacy policies on the information-sharing behaviour of the users. Damion et al. investigated this aspect [
24], by analysing 51 papers on SoMe privacy, concluding that despite the user concern on ID theft and third party access to their information, integrated privacy policies do not directly affect the users information sharing behaviour. A variety of studies focus on the security implication of social media as platforms and also specifically their use, such as the study by Wu [
25] who reviewed social media security risks and existing mitigation techniques, and the book by Gonzales [
26] that draws a much broader picture on online activity, including aspects related with the collection, storage and use of data, the management of intellectual property and online activism.
Looking at what are the best practices for people to protect their social media account, we looked at a public advisory company called NorSIS and Nettvett which are governmental owned companies in Norway, that strive for cybersecurity awareness for the public and small/medium enterprises. Of their recommendations for how one can reduce the risk on ID theft when using the internet, one of their recommendations is for people to not give away personal information to unknown people on the internet, without the person giving away information being the one who instigates the information transfer (
https://nettvett.no/forebygge-identitetsverdi/). Nettvett also has some preventative measures for people who are exposed to blackmail on social media, in their list they suggest hiding friends lists, hiding the profile from search engines and making sure that the profiles timeline is just visible to friends (
https://slettmeg.no/seksuell-utpressing-pa-nett/).
There has been a lot of original works done on risk, risk perception and risk awareness that this study builds on. We usually define risk as the consequence and probability of something happening, but this definition might be a bit too narrow for when measuring risk in laypeople. As Slovic mentioned [
27], the heuristics of a person has an impact in how they perceive and rate risk. Bickerstaff K. [
28] mentioned that most risk perception studies at the time had been conducted mostly in with questionnaires, but that more recently more studies had used or supplemented their quantitative data with qualitative data. There does not seem to be many papers written about the risk perception of people in social media and especially how people perceive the risk of a compromised social media account. We want to contribute in filling this gap, by asking people about how they perceive the risk, what they think a compromised social media account can be used for and the experiences of people who have had their accounts compromised.
This study builds upon our earlier results at [
29] which focused on evaluating the conceptual models used by security experts when developing security solutions targeted towards the general public, [
2] which focused on analysing the security awareness divergences of digital natives across Norway and two other European countries, [
14] that focused on evaluating the security awareness within the rural Norwegian population, and [
20] which focused on identifying the root cause of compromised accounts at Norwegian university. These studies are complementary to each other, and to other national reports [
30], aiming to solidify a more clear understanding on the cyber security culture of the Norwegian society.
Furthermore, the literature study has revealed two aspects of risk perceptions that have not been addressed: Several studies measure risk perceptions on one SoMe platform [
12,
23], but they have made no comparisons of risk perceptions between services. Additionally, while ID theft and account compromise have received some attention [
17,
18,
19,
20], we did not find any studies on how suffering ID theft changes risk perceptions.
The results of these initiatives are of National interest, since they provide a more clear understanding regarding the current status of cybersecurity awareness, thus allowing for enhancements on the content (e.g., general, introductory, comprehensive), format (e.g., promotional, informational, enforcing) and delivery types of enhancement programs. Furthermore, the results are also of a wider interest, as Norway is one of the most highly digitised counties in the world, with significant penetration of information and communication technologies, while still operating within the wider European context. Thus, providing future perspectives, as digitization progresses across the continent.
6. Summary of Findings and Discussion
In this section, we discuss the findings with regards to the research questions, starting with sharing habits and exposure to ID theft. We discuss the findings on risk perceptions of ID theft on SoMe. We also discuss the differences and similarities between the analysed groups to answer the outlined hypothesizes. Finally, we discuss the findings regarding how ID theft occurs and the consequences of said event.
6.1. Sharing Habits and Exposure to ID Theft on Social Media in Norway
We started by exploring the update practices for the sample and found that the majority of the respondents updated their devices when asked by the operating system. Moreover, very few waited longer than two months to update their devices. For the generic assessment of password security, we also found that only 3% chose the weakest alternative “I always use the same password for everything”, while 29% used a password rule with small variations of a password on different sites. Using different passwords and enabling multi-factor authentication are both considered strong practices. There were no differences between the groups in this area.
The results were similar when we examined the limitations and restrictions the respondents put on the visibility of their account information, where the results show that the majority of the respondents put limitations on what they share on their profile. Between 54 and 84% of the answers fell into either 3 or 4, where the latter means as strict limitations as possible. Furthermore, we found that 58% had hidden everything that they could when we asked what information they had visible on their SoMe platforms. The results show that the sample as a whole was security-aware.
When we examined differences between the groups, we found differences between the digital natives and the non-natives in the analysis: The digital natives had stricter privacy settings on contact info and their SoMe posts. We also found this pattern when we examined the information the groups had visible on their profile, whereas non-natives were slightly more public with their contact information such as email addresses and phone numbers. Contact information is generally viewed as public information in Norway and is commonly listed in the Yellow pages; the personal risk assessment of sharing this information might be reduced over time.
Considering the differences between the sexes on the sharing issues, we found differences between males and females on sharing their friends list and their profile visibility to search engines. The pattern here was that males had stricter privacy settings. Furthermore, the results also showed that females share information more openly and share about relationships and family members. However, the scores for these variables were still low, and the differences were that females were slightly more open on their privacy settings and visible information.
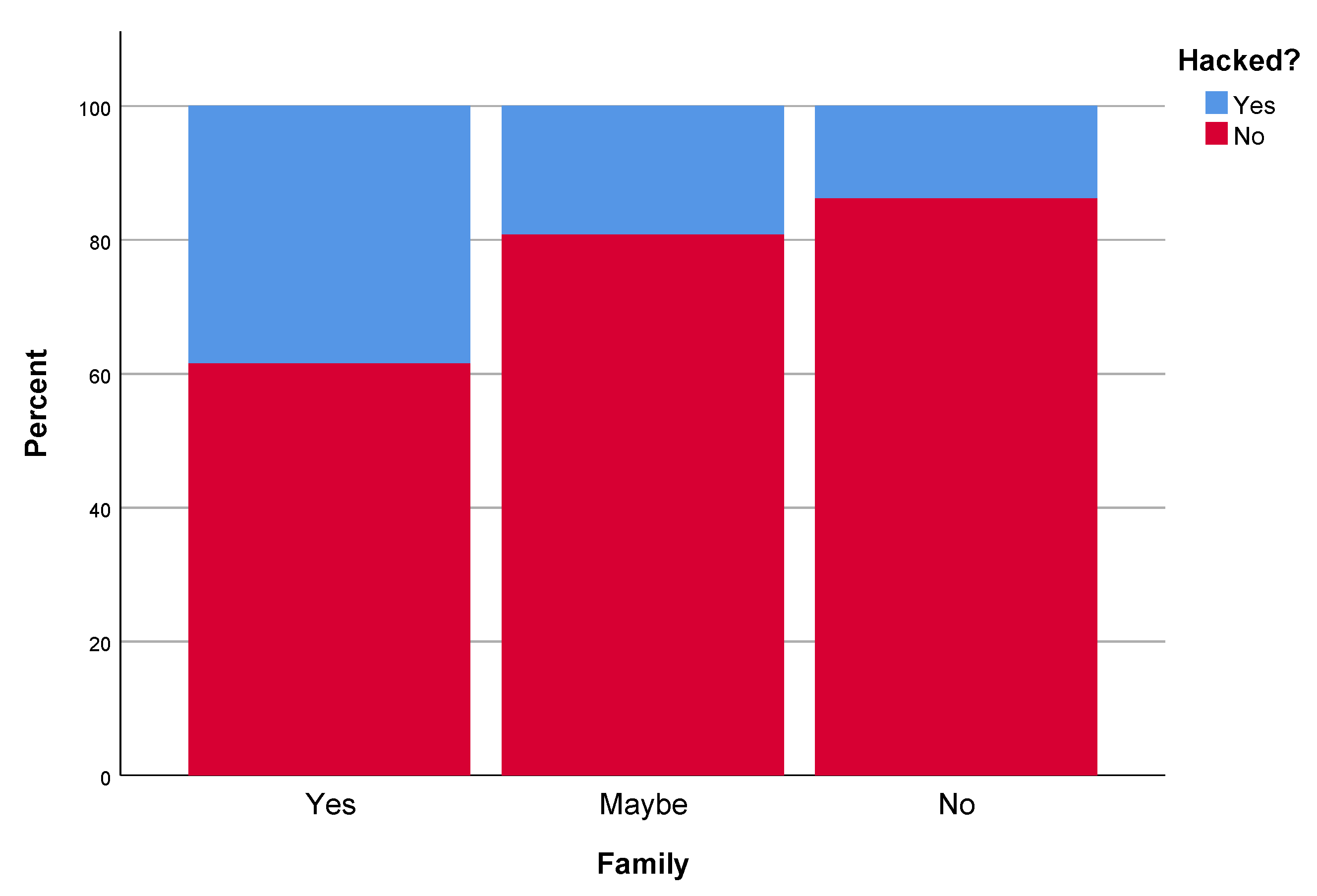
The group we were the most curious about was those who had suffered ID theft, and how this affected the security routines. When we analysed limitations on SoMe information, the group that had suffered ID theft scored lower on average across all of the five measured variables (
Table 11). Although the difference was minor in three of the five variables, the pattern was evident for this group. A hypothesis for future work could be to examine the relationship being exposing information and the risk of ID theft.
6.2. Risk Perceptions of Social Media Use
When we examined the risk perceptions of social media usage, we started by analysing the risk perceptions of posting various pieces of information on SoMe. The survey design was such that choosing a specific SoMe triggered questions about it. We compared the actions on Facebook, Twitter, Reddit and Snapchat. As an aggregated result, we found that the respondents considered Facebook and Twitter to be riskier than Reddit and Snapchat. This results might be due to Twitter being an open platform where everyone can read content unless one has strict privacy settings. However, the information on Facebook is arguably less accessible than Twitter as it has more protection by default than Twitter, but the results have these two close together. The risk perceptions of conducting activities on these two services follow each other closely (
Table 15), except posting about vacation, which is deemed a somewhat higher risk on Twitter than Facebook.
Reddit does not use real names by default and provides a level of anonymity for its users. This feature is likely the reason that it received the lowest overall risk score across all the measured variables except posting pictures and pets with names. Images can contain quite a bit of metadata which can be abused to figure out information about the camera and where the picture was taken (geo-tagging). This information can be used for stalking purposes, and one could figure out if the device that has taken a photo is vulnerable to some exploit, if the model and make are vulnerable. Information also become mostly public once it is posted on the forum. We assume that there are many highly competent IT users on Reddit, and the combination of these issues might be the reason why posting pictures is perceived as risky by the Reddit users. A note on sharing information shared about pets is that it, in some cases, easily can be abused to break security questions. In our comparison, Reddit has the lowest overall risk.
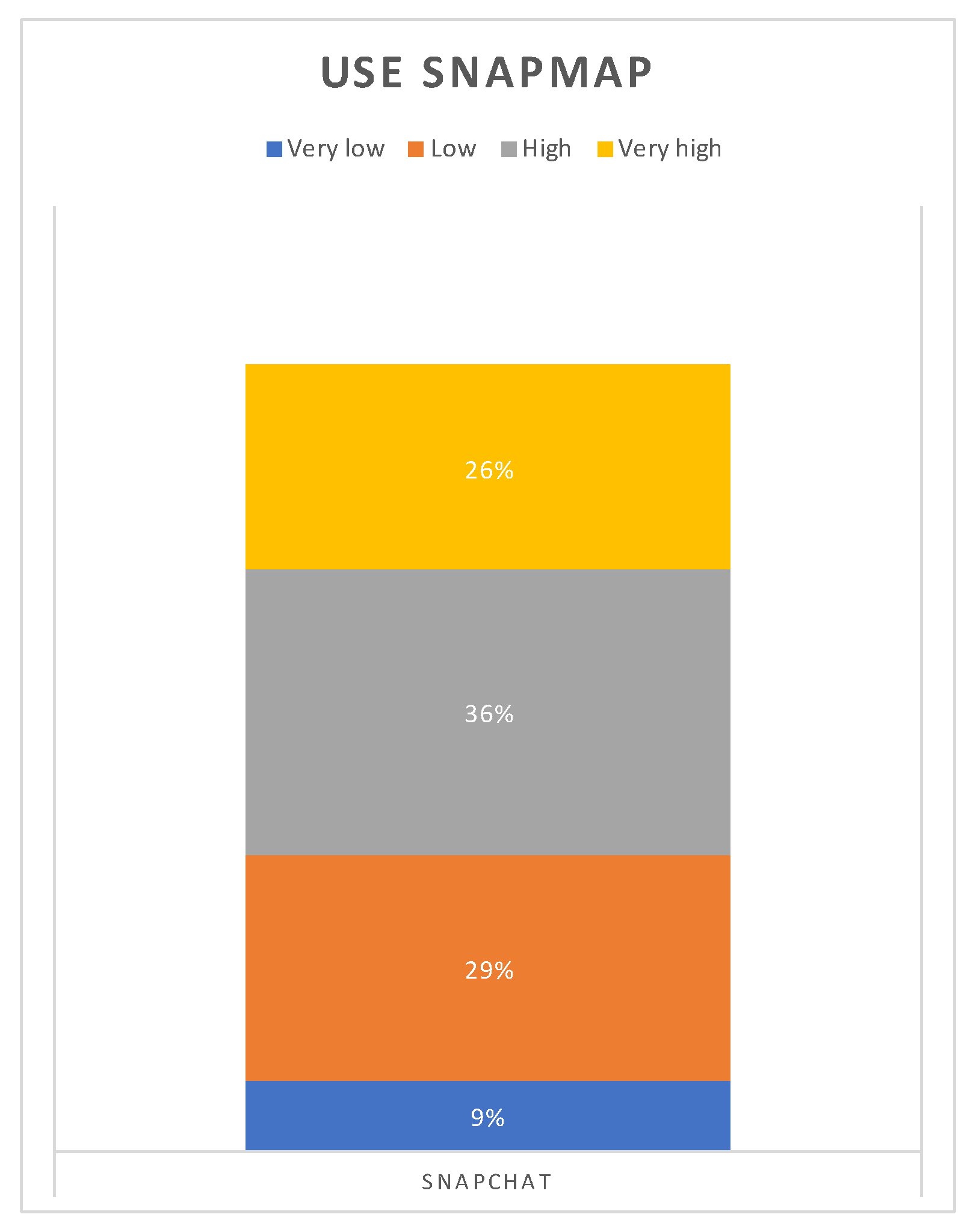
Examining Snapchat shows that it is close to Reddit in the overall score. Generally, sharing information on Snapchat is deemed to have a low risk by our participants. However, Snapchat also has the riskiest function, which was Snapmap. Snapchat also provides a level of anonymity on a username level, but using it for sharing pictures severely weakens the anonymity of the service. Snapchat has the lowest risk score for posting pictures, which makes sense as it is primarily a picture sharing service. Snapchat allows for strict control of who gets to see the shared information and, to the user, the data seems to disappear after a brief period. These are likely explanations of why Snapchat is deemed more secure as a whole. However, is there grounds for considering Snapchat as more secure for posting pictures than the other services? There are some further answers in the data to this question: Considering the results in
Table 15, each activity is ranked according to the platform on which it is conducted.
Table 16 provided the aggregated results of both platforms and activities. Considering the activities, we can induce the information assets and threats for each and propose a threat model,
Table 29. For example, if the main concern is stalking or burglary, the Snapmap would be the riskiest service as it reveals the location to potential stalkers and burglars. Expanding on the burglary risk, the secondary asset at risk would be valuables located at the property. Participating in an online debate is considered to be risky by our participants. This activity often reveals the political opinion of the debater, and this information is, in many cases, considered as sensitive personal information.
Furthermore, a debater exposes himself/herself to the public, and controversial opinions can have severe consequences if one gets targeted by the mob. Sharing a political opinion is similar to participating in debate, but often with less exposure. Our sample deemed these two activities as equally risky. Sharing a news story was mostly considered a benign activity by the respondents; however, most SoMe users have encountered the spreading of fake news online. Sharing news stories can also reveal political opinions.
From the categorical analysis of the issue, we found that females consistently rank risks higher for the majority of the measured activities. This finding is consistent with previous work on risk perception between men and women, where women express far greater concern than men about risks and hazards [
8,
32].
When asked to what degree specific information assets could be abused for ID theft, there were three that were ranked higher than others: account information and passwords, credit card numbers and social security numbers.
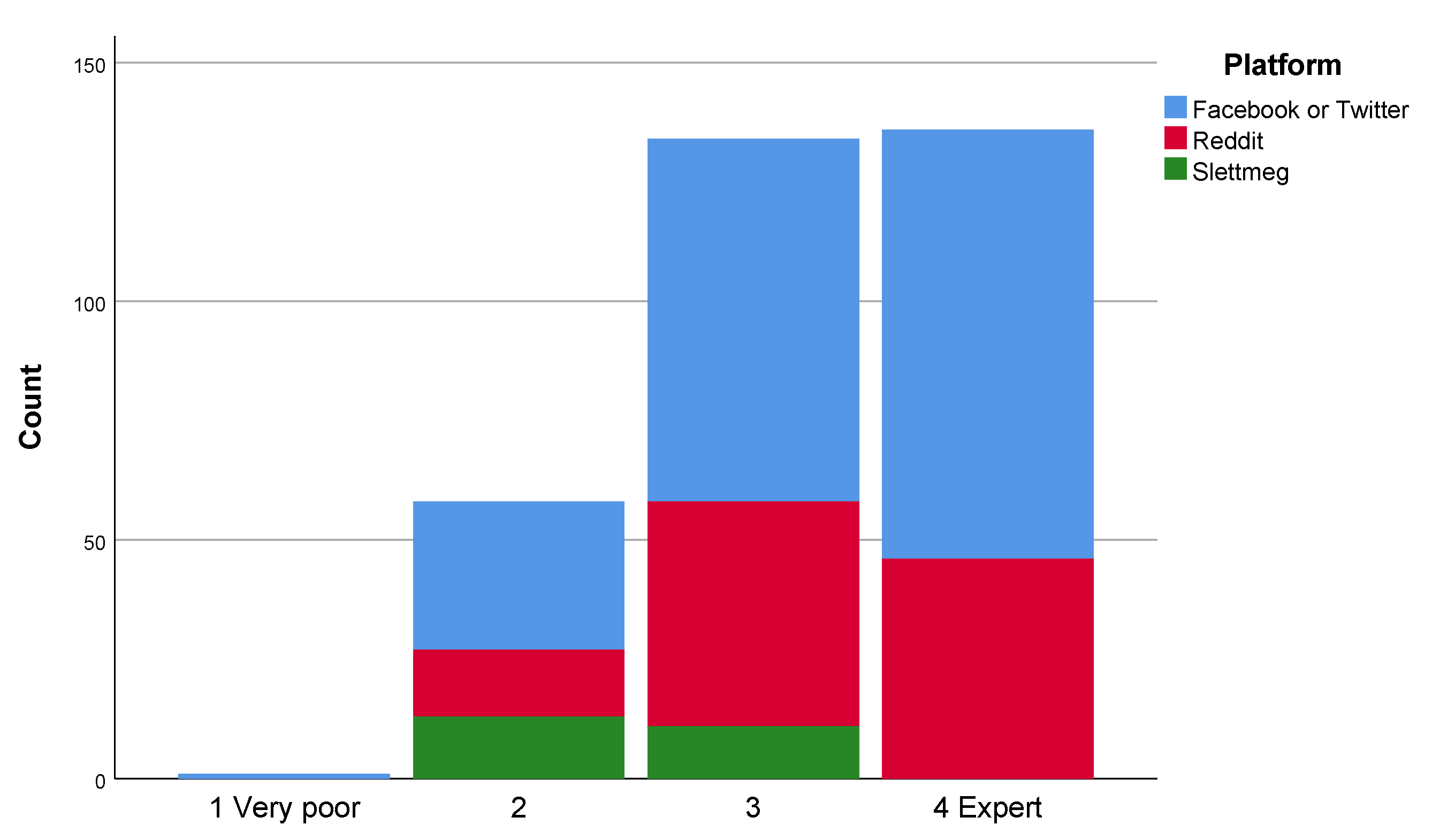
There were differences between the digital natives and non-natives, where the non-natives ranked five information assets as higher risk of abuse. These five included the three overall highest risk assets mentioned earlier. There can be several causes for this difference. Given that a portion of the natives are in their early twenties, they might not have as much capital at risk when considering abuse of credit card numbers. The value of account information and passwords may also increase over time, with the non-natives having accumulated more wealth, responsibility and higher risk. Understanding of technology may also be a factor in risk perception as better understanding of systems should lead to a more calibrated risk judgment. Previous studies have shown that natives tend to have increased confidence regarding technology [
2].
The difference between sexes are consistent with the previous results in this paper, as females rank all of the 11 variables as slightly riskier than males. An interesting finding is that the group that had suffered ID theft or account hacking ranked the variables full name and email as more risky. This information is generally considered open, but having suffered an incident seems to change the perception of this issue.
We also attempted to measure susceptibility to phishing attacks presenting the respondent with a common attack method employed in SoMe. This task attempted to measure how trust influence decision making in SoMe. The task hypothesizes that a message from an acquaintance has a lower probability of being clicked than from a person in close social circle. The results show differences, but more than 84% of the respondents answered no for all four options. The probability of clicking the link was highest if received from the close family group (6%), which is a low number, but high enough for these scams to succeed. If between 1 and 5% click the link and get compromised, these attacks will propagate quickly through SoMe. Our results also show that the group that had suffered ID theft were more trusting, which adds to the trend for this group of having slightly weaker security controls.
These differences of risk perceptions are a potential path for future work.
6.3. How does ID theft Occur and What are the Consequences?
This study had 50 participants who reported to have had their accounts compromised. This group ranked their IT competence as significantly lower than the remaining group (
Table 8). The results showed that as a cause of compromise, the majority chose either the
do not know (19) or the
hacked (15) option. The
hacked option is too broad to draw any conclusions. However, a phishing attempt had fooled eight, and two reported to have shared their password with someone in their close relations as the cause. Keyloggers (malware) had compromised two participants, and one participant wrote that a brute force password cracking attack was the cause.
The hacked account group consisted of 52% males and 48% females, which indicated an over-representation of females in this group compared to the sample as a whole. However, not if we compare to the Norwegian population as a whole. The group of 50 is not large enough to draw any conclusions, but this finding also aligns with previous work in Nyblom et al. [
20] where the hacked account owners also had an over-representation of females. Furthermore, comparing to the results in Nyblom et al., we find that phishing and malware infections are common causes. Weak password security is a re-occurring topic in account hacking, and we see varying practices within this area as well. Two respondents had gotten compromised by telling the password to someone. However, if we take into account the results from Thomas et al. [
19] and Nyblom et al. [
20], in which both had
password reuse as a common cause, we can assume that a large portion of the
hacked group too got hacked through password reuse.
The majority of the respondents did not suffer any severe consequences from the compromise. The most severe was an abuse of corporate accounts followed by psychological consequences and a withdrawal of SoMe. Additionally, one participant had his account abused for buying and selling.
Table 25 illustrates that compromised SoMe accounts have a broad potential for misuse.
Spamming and
phishing were the two most frequent forms of abuse. Both are a form of impersonation where the attacker exploits the SoMe account to distribute messages. Spamming is a way for the hacker to try to exploit the trust between two parties for financial gain, while phishing leverages the trust to harvest more credentials or credit card information. Two accounts were abused for blackmailing.
Of the more severe consequences, three people found their accounts to be inaccessible after they got hacked, it is probably challenging to ascertain whether it was the social media platform that deleted or closed down their account because of suspicious behaviour, or if it was the hackers that were performing some denial of service.
The presented findings align with the findings from asking the participants who had not suffered an ID theft what they thought would be the consequences,
Table 26: Impersonation was a major concern, followed by spamming, spreading malware, phishing. Stealing money, swindling and blackmailing were also among the perceived consequences. Destroying reputation was also a commonly perceived consequence. The results illustrate that the majority of the participants were aware of the risks posed by ID theft.
The results also document that several of the respondents benefited from having the notifications of new logins feature enabled. This mechanism allowed for a swift response to the compromise and mitigation of potential consequences.
7. Conclusions
This paper has focused on the Norwegian population, exploring how people perceive risks arising from the use of SoMe, focusing on the analysis of specific indicators such as age, sexes and differences among the users of distinct social media platforms. Some differences across the examined indicators were noticeable, most notably, that the group that had suffered ID theft had weaker security controls which may have increased their exposure in the first place. Furthermore, the results document differences in risk perception when using the four different SoMe platforms, where Reddit and Snapchat are considered as safest, and Facebook and Twitter as most risky. The riskiest activity on SoMe is considered to be using the Snapmap followed by debate participation. Additionally, there were consistent differences between males and females, where females consistently ranked the risks as higher. There were no differences between the age groups considering SoMe activities, but non-natives ranked the risk of sharing the most critical information assets as higher. Finally, considering our sample, having suffered ID or account theft did not influence risk perceptions on performing SoMe activities, but the participants perceived higher risk of sharing certain information assets. To summarise, the measured security routines in the sample were generally healthy, and the majority of participants seemed to have a sufficient understanding of security risks and awareness.
7.1. Study Implications
This paper explored the areas regarding different SoMe platforms and how people perceive risk when doing different activities on SoMe. It also looked at this issue in context with people who have had their accounts compromised. The study documents that the study participants consider uttering their political positions and participating in debates as very risky. This issue was prevalent on Facebook and Twitter, and especially females considered this as a high-risk activity. SoMe are political arenas, but our results document that many citizens dread participating because of the possible ramifications. Future research should study the implications of this finding in-depth, possibly together with the effects of cyber-bullying.
Our study further implies that suffering an ID theft changes risk perception within certain areas: such as valuing personally identifiable information like full name and email higher. We found the most significant differences when we looked at the sexes, where females generally perceived higher risk than males. This finding might imply that fewer females participate in discussions on SoMe platforms. Although the difference in risk perception between sexes is well-known, how it impacts participation in discussion and debates is not widely studied.
One of the measures that people chose to activate to secure their account were notifications on suspicious behaviour. Our results also showed that several who had their SoMe accounts compromised managed to take actions due to login notifications quickly. They managed to take mediating action before the hackers could do any noticeable harm. An implication here is that time is of the essence when dealing with hacked accounts and being able to regain control quickly is important for damage limitation. This finding was unexpected and warrant further research into the efficiency of account security mechanisms.
If we look at the proposed threat model for the different risks around sharing, we saw that Snapmap was the risk that people perceived as the worst, followed behind by debating, posts about vacation and sharing political opinions. We deduced that stalking, burglary, harassment and bullying were the primary concerns of the participants. This assessment needs further validation studies and can be used for understanding the risk perception of the user in future designs.
The study shows that some SoMe platforms are seen as higher risk than others, by their users. Facebook and Twitter have the highest aggregated risk, and are both quite a bit above Snapchat and Reddit. Both Twitter and Reddit are generally open SoMe platforms where everyone can see each others posts. The implication from this is that the privacy a closed SoMe like Facebook offers does not reduce the perceived risk when compared to a more open platform like Twitter, where everything is open and no invitation is needed.
7.2. Limitations
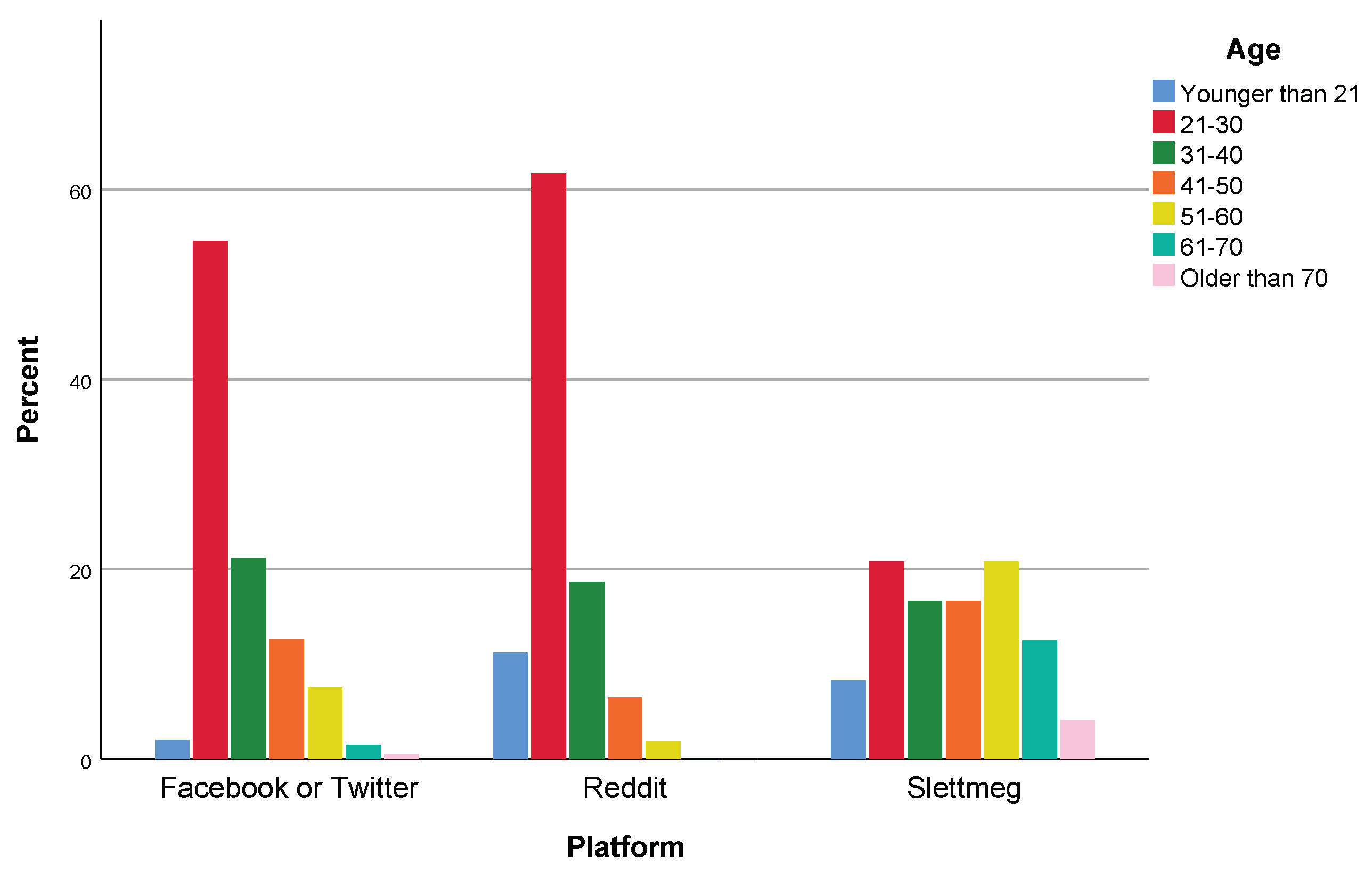
Although we do not know what the real demographic looks like for Norwegian SoMe users, we have some clear biases in the sample: 75% of the sample comes from the age group 21–40. The age distribution is highly skewed towards the younger generations. The majority of the sample was also males (68%). These two over-representations are most likely an effect of the participant recruitment strategy that utilized Facebook and Twitter through social media profiles to sample the general population. Many people from the age groups of the authors (20–40) answered the survey, which reflects the social network demographic and outreach of the authors. This difference might stem from a sampling bias caused by most of the sampling happening trough our social media network and receiving help with sharing the questionnaire from our existing network. The respondents also have a higher than average educational level, which might skew the risk perception a bit if a lot of the people who answered the questionnaire might have a more straight forward understanding of risk, with risk solely being consequence times probability of an event happening; like Slovic [
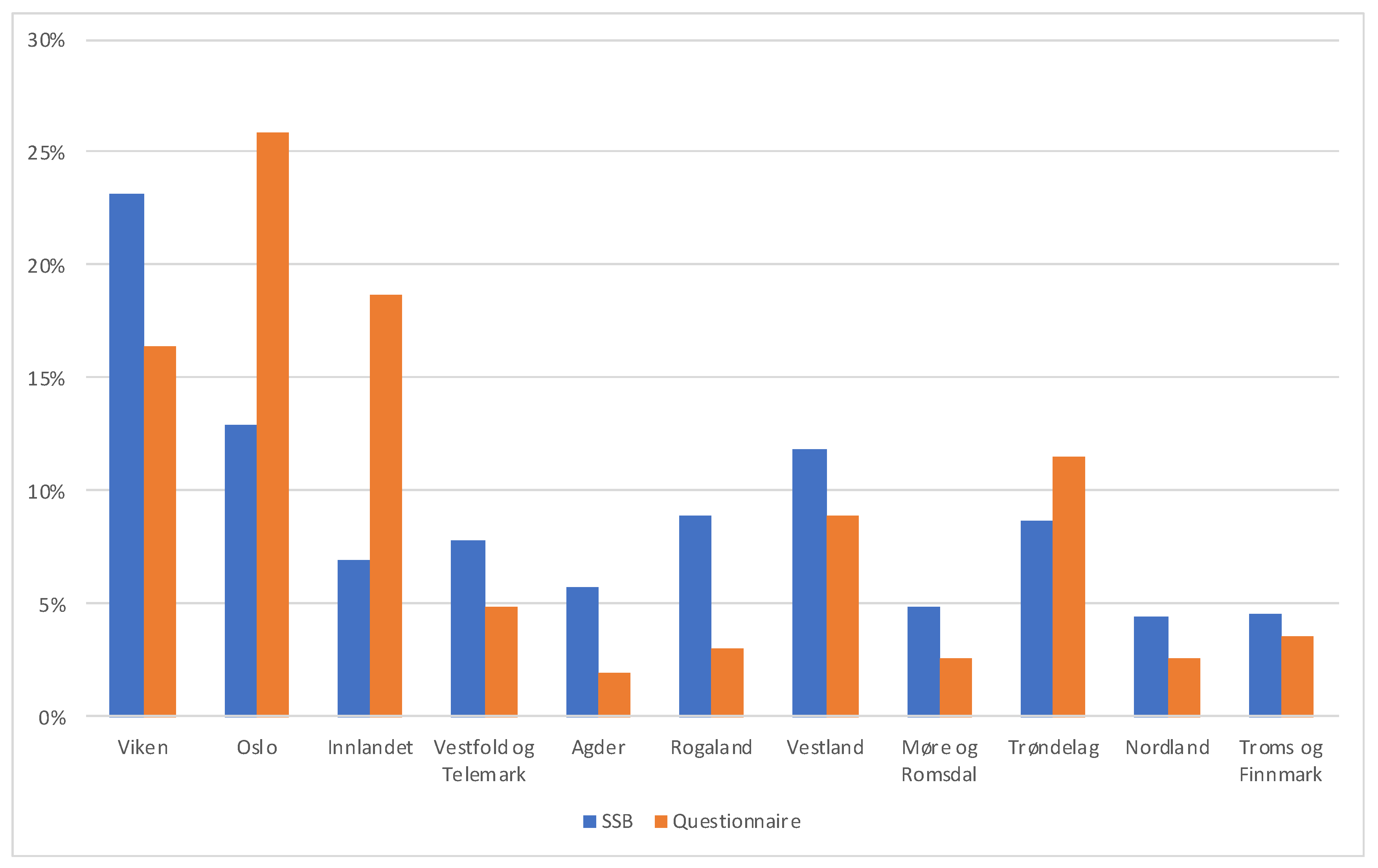
27] mentioned, there are differences in how laypeople and experts define risk. The discrepancy in counties compared to that of Norway in large probably will not impact the later answers because how people use social media is probably the same across the country. The sample has a representation from all the Norwegian counties, with a slight over-representation from the central/eastern counties. We do not expect county representation to have any impact on the results as the expected variance in culture is negligible.
The over-representation of males was not perceived as an issue in the analysis as the data contained answers from 99 females which is a large enough sample to conduct analysis. Furthermore, the age groups were split into digital natives and non-natives as this provided large samples for testing. Optimally, the results would have contained enough respondents for each age group to test for significance. Furthermore, another issue that needs to be discussed is the low response rates which are inherent to similar studies. Thus, although the number of responses is sufficient for the purposes of this analysis, we do notice a low response rate, down to 0.08% for Reddit, which are indicative of the difficulties to establish engagement with the general population.
7.3. Future Work
We mentioned some possible venues for future work under limitations; besides, we propose the following venues: Figure out if some hacked social media accounts are being used for different things than others. For example, are most Twitter accounts used to mass follow different accounts, or are they mostly used to spread propaganda if the user has many followers? Another reason to hack a Facebook account to be able to buy ads to spam people, or is it the main thing hackers try to do is send out spam/phishing messages to people.
Another venue could be if and how risk perception influences willingness to share their opinion and self-censorship, considering the consequence of participation as higher than the reward. How much does the perceived risk stifle them from saying their opinion, and is there any way to reduce this high perception of risk to make for a healthier debate climate? To get some more insight into this, one could ask people to rate how anonymous they find the given social media. This could have been an interesting data point that could have shone some more light on why some things are perceived as less risky than others. This point might have given some insight into why some social media platforms perceive the risk of posting/sharing as lower than others.
Additionally, more knowledge can be gathered regarding account abuse: In this study, we attempted to get insight into this with the questions about consequences. However, if the account had a more hostile takeover, where the name and picture got changed to phish or gain street cred, these consequences can have slipped peoples mind because the consequences were not necessarily connected to them anymore. We failed to get enough ID theft sufferers into an interview, but this is still an interesting venue for further research.
More research could also be done in the risk perception and security routines of hacked users. The questionnaire shed some light onto this demographic. However, recruitment could have been better, and this aspect would have benefited from some qualitative interviews, where one could really prod at how their security routines look.
It could also be interesting to explore the reasons for the discrepancy in risk perception between the hacked and non-hacked population: is there a special reason for why people who had been hacked had a lower perception of risk? Was it because they were hacked, or was the hacking a product of their low perceived risk?
Another point of interest could also be to look into why there is a difference between natives and non-natives in what information they perceive to have the highest risk associated with it.