Personal Social Network Profile Authentication through Image Steganography †
Abstract
:1. Introduction
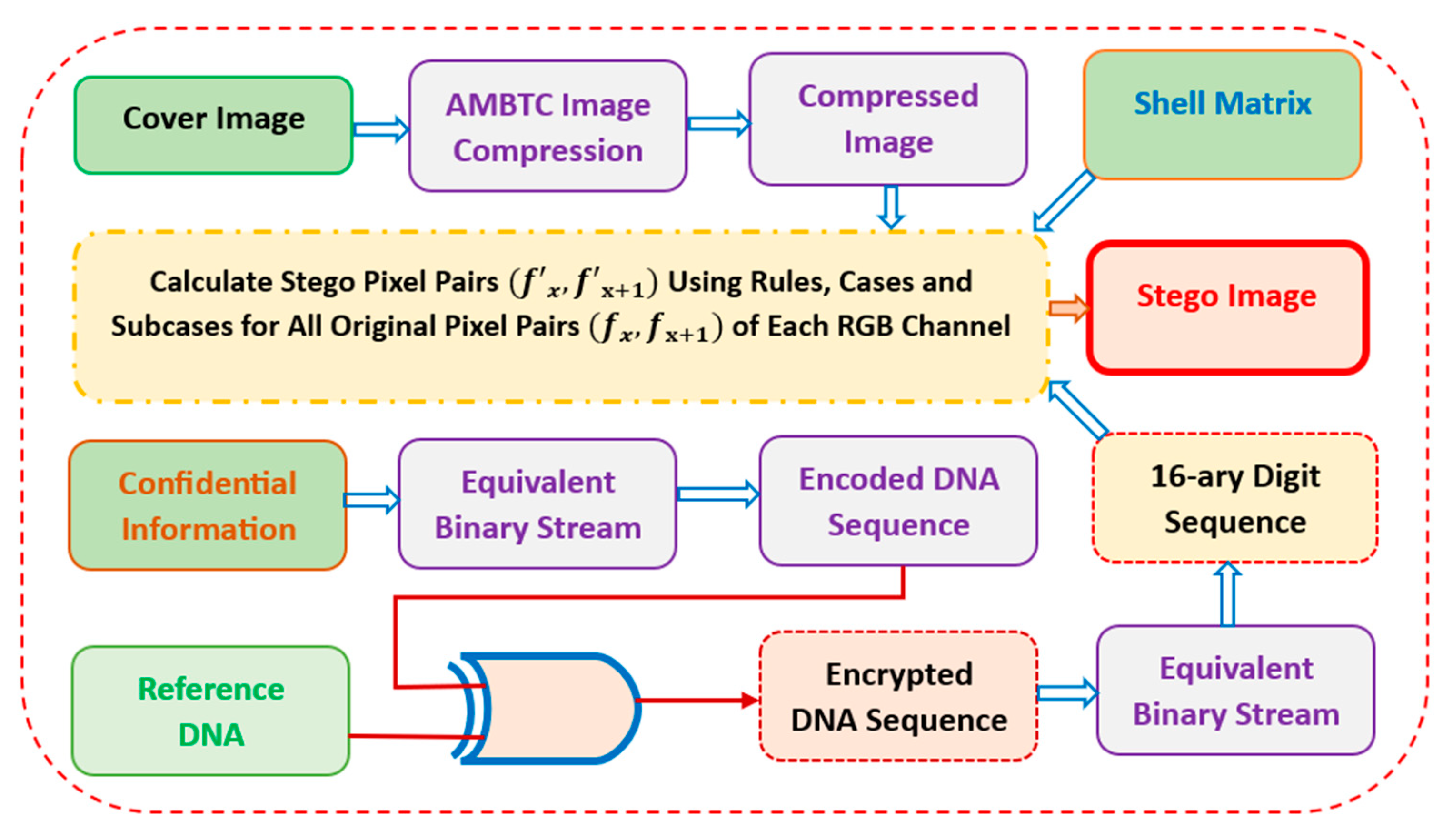
2. Proposed Work
2.1. Embedding Procedure
2.2. Extraction Procedure
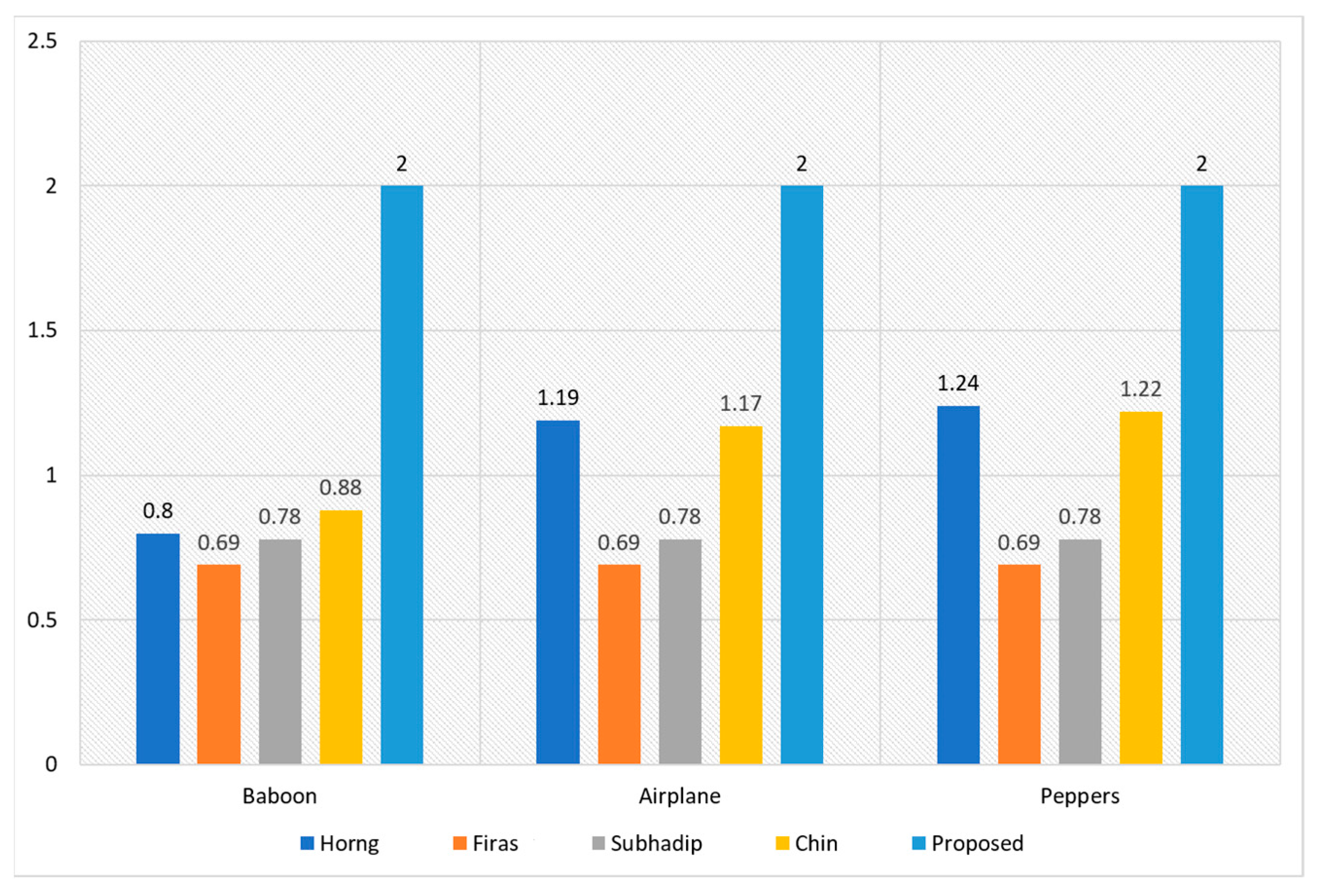
3. Experimental Results
4. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Mukherjee, S.; Sarkar, S.; Mukhopadhyay, S. Pencil shell matrix based image steganography with elevated embedding capacity. J. Inf. Secur. Appl. 2021, 62, 102955. [Google Scholar] [CrossRef]
- Chen, T.H.; Yan, J.Y. Enhanced Steganography for High Dynamic Range Images with Improved Security and Capacity. Appl. Sci. 2023, 13, 8865. [Google Scholar] [CrossRef]
- Tao, F.; Cao, C.; Li, H.; Zou, B.; Wang, L.; Sun, J. Adversarial Attack for Deep Steganography Based on Surrogate Training and Knowledge Diffusion. Appl. Sci. 2023, 13, 6588. [Google Scholar] [CrossRef]
- Chang, C.C.; Liu, Y.; Nguyen, T.S. A novel turtle shell based scheme for data hiding. In Proceedings of the 2014 Tenth International Conference on Intelligent Information Hiding and Multimedia Signal Processing, Kitakyushu, Japan, 27–29 August 2014; pp. 89–93. [Google Scholar] [CrossRef]
- Kurup, S.; Rodrigues, A.; Bhise, A. Data hiding scheme based on octagon shaped shell. In Proceedings of the 2015 International Conference on Advances in Computing, Communications and Informatics (ICACCI), Kochi, India, 10–13 August 2015; pp. 1982–1986. [Google Scholar] [CrossRef]
- Liu, L.; Chang, C.C.; Wang, A. Data hiding based on extended turtle shell matrix construction method. Multimed. Tools Appl. 2017, 76, 12233–12250. [Google Scholar] [CrossRef]
- Xie, X.Z.; Chang, C.C. Hiding data in dual images based on turtle shell matrix with high embedding capacity and reversibility. Multimed. Tools Appl. 2021, 80, 36567–36584. [Google Scholar] [CrossRef]
- Mukherjee, S.; Mukhopadhyay, S.; Sarkar, S. A shell-matrix-based image steganography technique for multimedia security and covert communication. Innov. Syst. Softw. Eng. 2022. [Google Scholar] [CrossRef]
- Mukherjee, S.; Sarkar, S.; Mukhopadhyay, S. Octagon Shell Based Image Steganography for Avoiding Human Visual System with Lower Computational Time. In Proceedings of the 2022 Second International Conference on Advances in Electrical, Computing, Communication and Sustainable Technologies (ICAECT), Bhilai, India, 21–22 April 2022; pp. 1–5. [Google Scholar] [CrossRef]
- Abdullatif, F.A.; Abdullatif, A.A.; Taha, N.A. Data hiding using integer lifting wavelet transform and DNA computing. Period. Eng. Nat. Sci. 2020, 8, 58–66. [Google Scholar]
- Mukherjee, S.; Sarkar, S.; Mukhopadhyay, S. An Image Steganography Technique Based on Fake DNA Sequence Construction. In Proceedings of the International Joint Conference on Advances in Computational Intelligence: IJCACI 2021, New Delhi, India and Dhaka, Bangladesh Jointly, 23–24 October 2021; pp. 613–621. [Google Scholar] [CrossRef]
- Lee, C.F.; Chang, C.C.; Li, G.L. A Data Hiding Scheme Based on Turtle-shell for AMBTC Compressed Images. KSII Trans. Internet Inf. Syst. 2020, 14, 2554–2575. [Google Scholar] [CrossRef]
- Horng, J.H.; Chang, C.C.; Li, G.L. Steganography using quotient value differencing and LSB substitution for AMBTC compressed images. IEEE Access 2020, 8, 129347–129358. [Google Scholar] [CrossRef]
- USCID Image Database. Available online: http://sipi.usc.edu/database/ (accessed on 14 July 2023).
- European Bioinformatics Institute. Available online: http://www.ebi.ac.uk/ (accessed on 15 July 2023).
- NCBI Database. Available online: http://www.ncbi.nlm.nih.gov/ (accessed on 15 July 2023).
- Bandyopadhyay, S.; Sarkar, S.; Mukherjee, S.; Mukhopadhyay, S. Pixel Interpolation Followed by Prediction Error Expansion-Based Reversible Information Hiding Algorithm for Securing Healthcare Data. In Proceedings of the Frontiers of ICT in Healthcare: Proceedings of EAIT; Kolkata, India, 30–31 March 2022, pp. 375–385. [CrossRef]
- Mukherjee, S.; Sarkar, S.; Mukhopadhyay, S. A LSB substitution-based steganography technique using DNA computing for colour images. In Proceedings of the International Conference on Innovations in Software Architecture and Computational Systems: ISACS 2021, Kolkata, India, 2–3 April 2021; pp. 109–117. [Google Scholar] [CrossRef]
- Bandyopadhyay, S.; Mukherjee, S.; Jana, B.; Chowdhuri, P. A Data Hiding Technique Based on QR Code Decomposition in Transform Domain. In Proceedings of the International Conference on Frontiers in Computing and Systems: COMSYS 2021, Shillong, India, 29 September–1 October 2021; pp. 425–432. [Google Scholar] [CrossRef]

| Image | Payload (Bits) | PSNR (dB) | EC (bpp) |
| Tree | 65,536 | 34.44 | 1.00 |
| 131,072 | 29.52 | 2.00 | |
| Baboon | 65,536 | 34.94 | 1.00 |
| 131,072 | 29.67 | 2.00 | |
| Airplane | 65,536 | 34.19 | 1.00 |
| 131,072 | 29.54 | 2.00 | |
| Peppers | 65,536 | 34.65 | 1.00 |
| 131,072 | 29.81 | 2.00 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mukherjee, S.; Mukhopadhyay, S.; Sarkar, S. Personal Social Network Profile Authentication through Image Steganography. Eng. Proc. 2023, 56, 129. https://doi.org/10.3390/ASEC2023-16635
Mukherjee S, Mukhopadhyay S, Sarkar S. Personal Social Network Profile Authentication through Image Steganography. Engineering Proceedings. 2023; 56(1):129. https://doi.org/10.3390/ASEC2023-16635
Chicago/Turabian StyleMukherjee, Subhadip, Somnath Mukhopadhyay, and Sunita Sarkar. 2023. "Personal Social Network Profile Authentication through Image Steganography" Engineering Proceedings 56, no. 1: 129. https://doi.org/10.3390/ASEC2023-16635
APA StyleMukherjee, S., Mukhopadhyay, S., & Sarkar, S. (2023). Personal Social Network Profile Authentication through Image Steganography. Engineering Proceedings, 56(1), 129. https://doi.org/10.3390/ASEC2023-16635