Advanced Resources Reservation in Mobile Cellular Networks: Static vs. Dynamic Approaches under Vehicular Mobility Model
Abstract
:1. Introduction
- (1)
- Extension of MRSVP protocol with additional features inherited by NISIS, in order to dynamically manage NSIS-MIP and NSIS-MDP classes also during on-going calls;
- (2)
- Proposal of a utility-based rate adaptation scheme with the application of utility functions for the management of Best Effort (BE) associated to NSIS-MDP class and video traffic associated to NSIS-MIP class;
- (3)
- Proposal of a Hand-off Direction and CST based reservation schemes in order to meet adaptive QoS requirements during users’ movements. In-advance bandwidth reservations is proposed in order to reduce the QoS degradation and call dropping probability;
- (4)
- Static and Dynamic (threshold-based) reservation prediction schemes proposal considering real mobility traces;
- (5)
- Validation of the considered scheme through realistic mobility patterns.
2. Related Work
2.1. Reservation Schemes and Prediction in Literature
2.2. Mobility Applications in Literature
3. The Considered Architecture
3.1. Protocols and Service Classes
- (a)
- NSIS Mobility Independent Guaranteed (NSIS-MIG, which provides intolerant applications, with very stringent guarantees on packet delays and jitter);
- (b)
- NSIS Mobility Independent Predictive (NSIS-MIP, dedicated to elastic real-time applications, able to work with some resource bounds);
- (c)
- NSIS Mobility Dependent Predictive (NSIS-MDP, which can be compared with the best-effort class, subject to continuous QoS degradations and/or droppings).
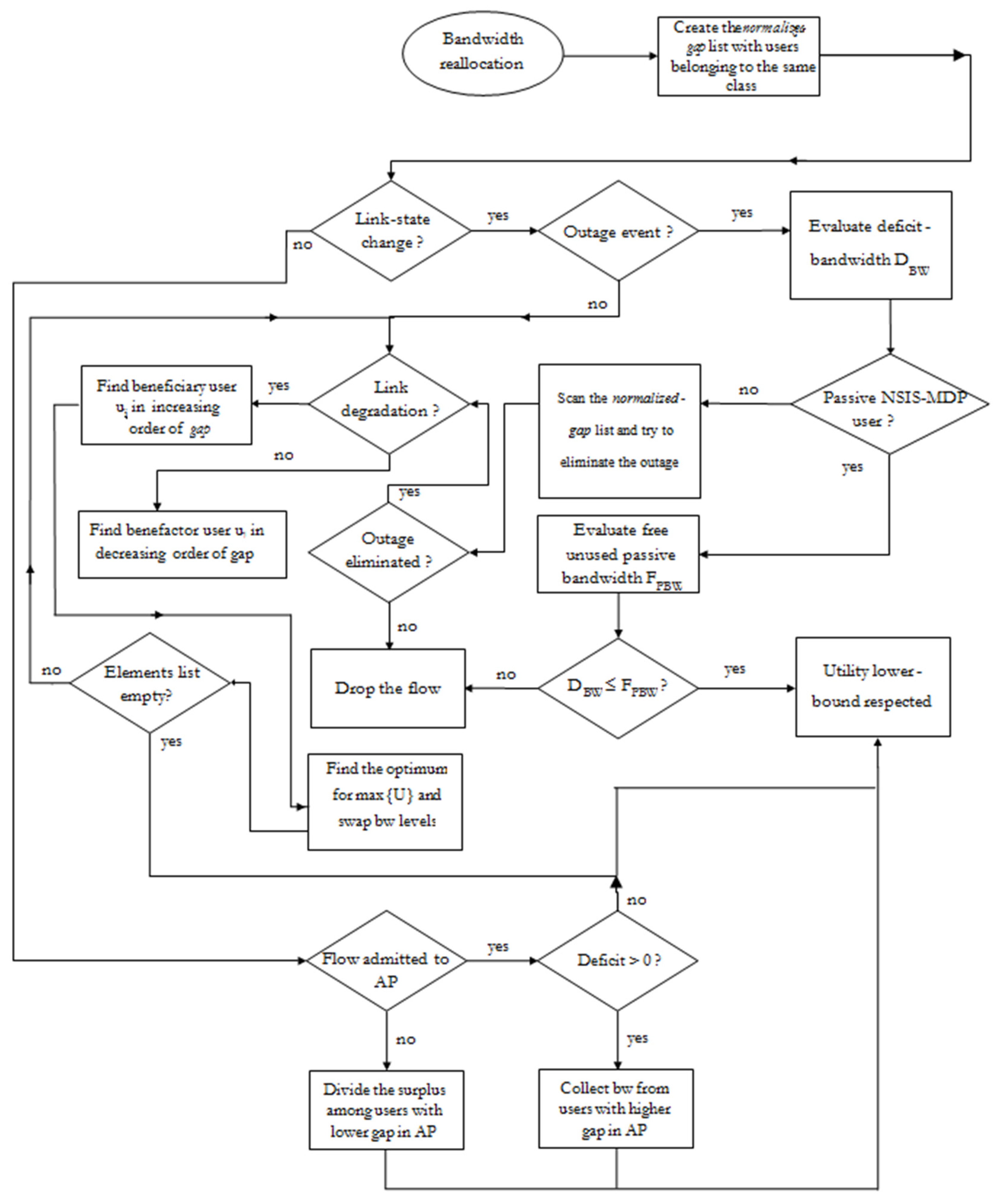
3.2. Advanced Resource Reservations with NSIS
- (a)
- local proxy agents, generally identified as the active cell in which a mobile host is making the service request (hence, the active reservation); NSIS-MDP users make use of local proxy agents only (they request the service only on the current cells);
- (b)
- remote proxy agents, generally identified as the passive cells which will be probably visited by mobile hosts (hence, dealing with passive reservations); NSIS-MIP make use of remote proxy agents in order to manage their passive requests remotely.
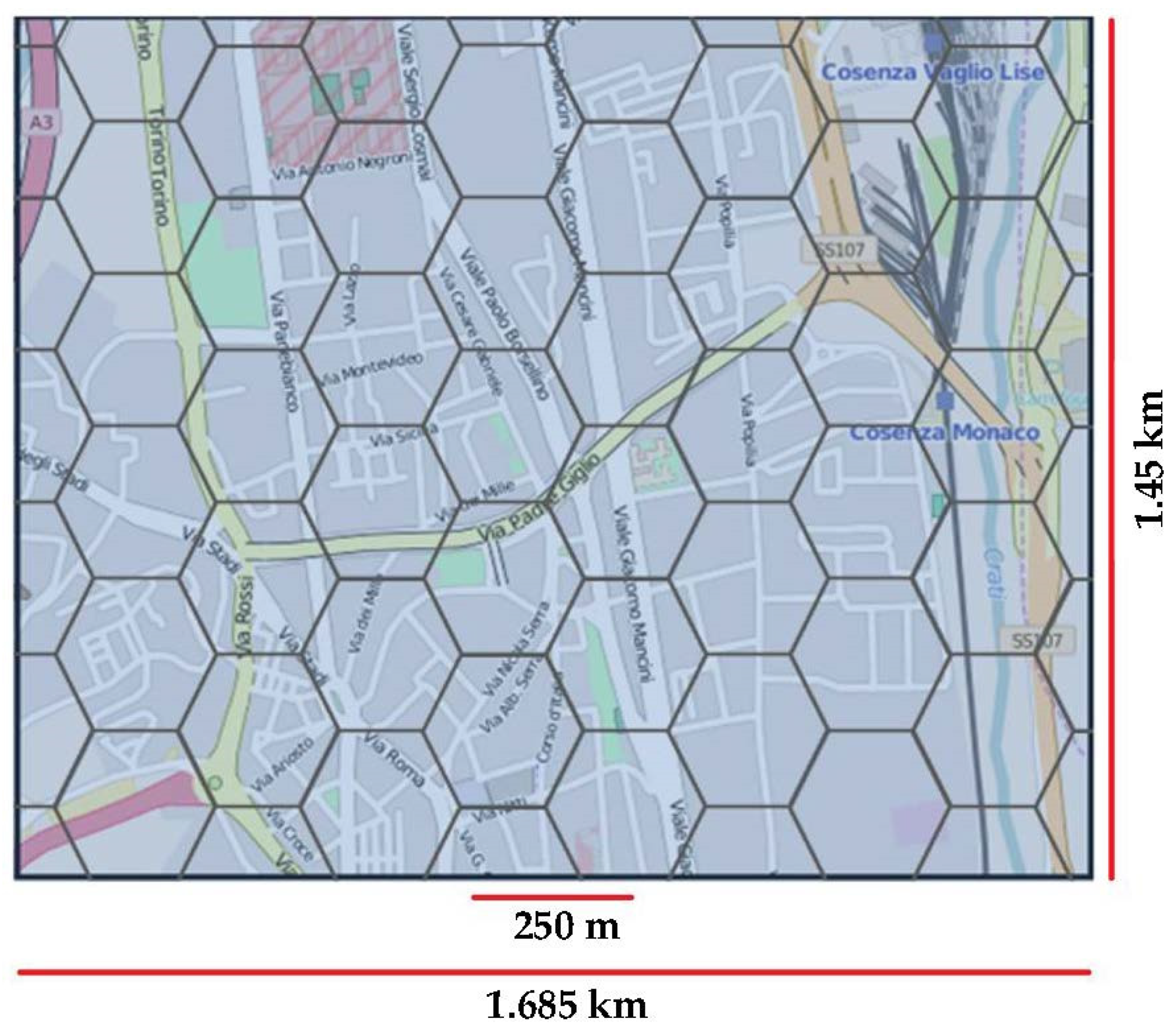
4. CityMob and C4R-GUI for Generating Real Mobility Traces
5. Traffic Models and Utility Functions
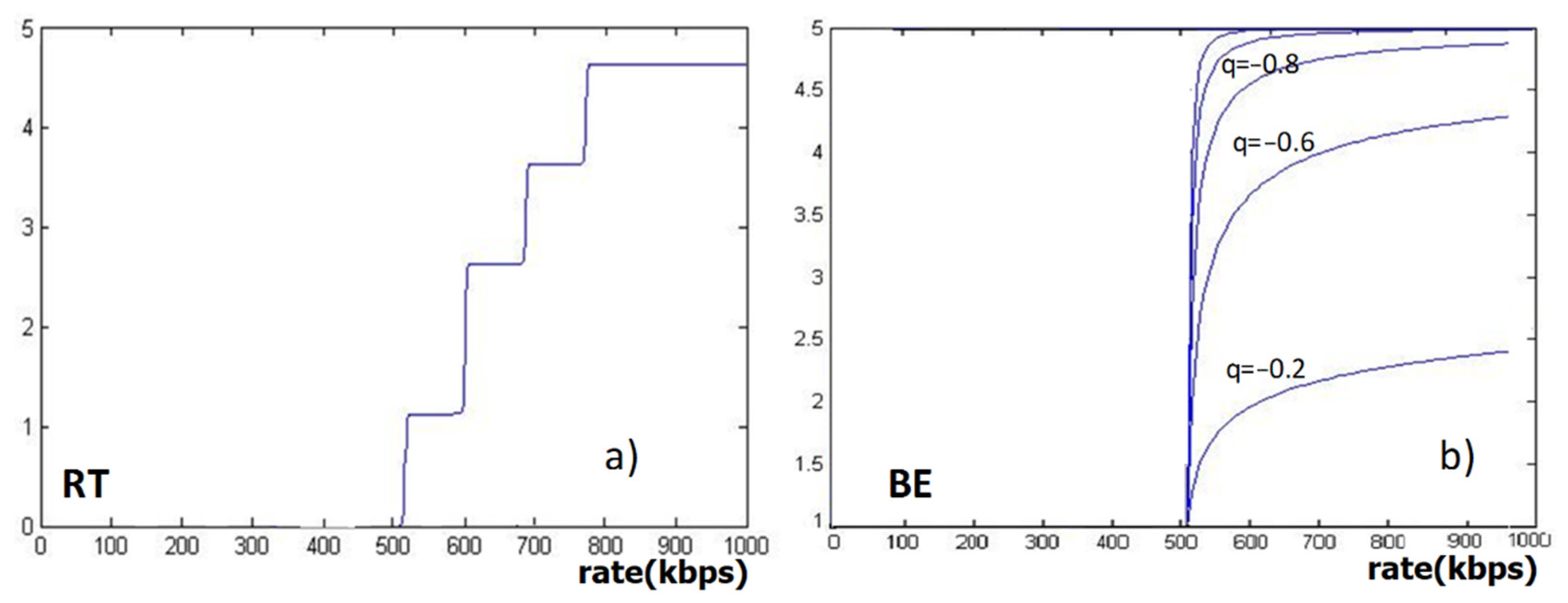
5.1. Real Time Video Traffic for Mobility Independent Predictive Services
5.2. Best Effort Traffic for Mobility Dependent Predictive Services
5.3. Utility-Based Bandwidth Management
6. Resource Reservation Schemes: Static vs. Dynamic
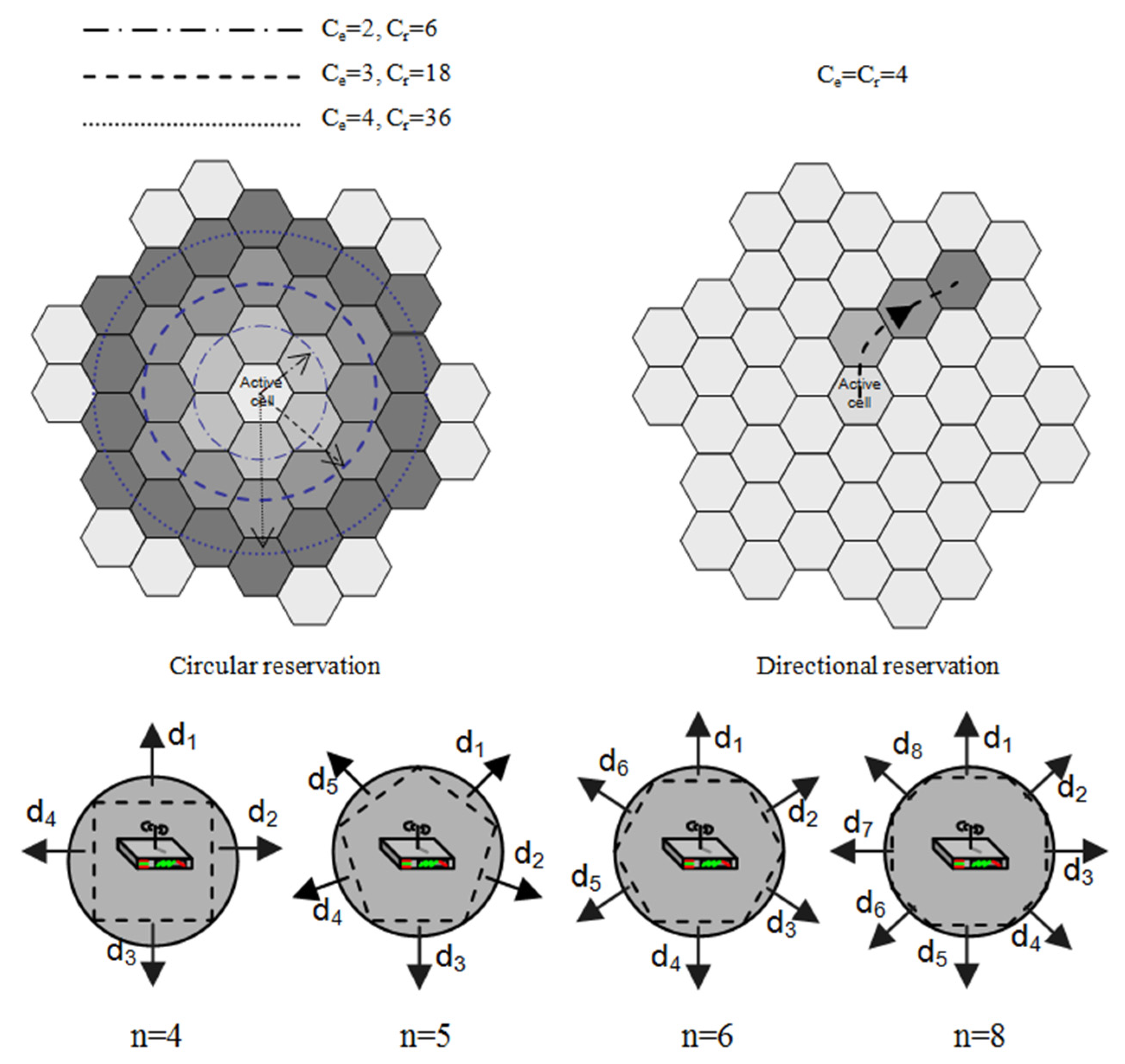
6.1. Static Scheme
- (1)
- Non-decreasing: each user i will reserve on an increasing number of cells for the increasing number of hand-over (i.e., Ci1 ≤ Ci2 ≤ … ≤ CiCei−1);
- (2)
- Non-increasing: each user i will reserve on a decreasing number of cells for the increasing number of hand-over (i.e., Ci1 ≥ Ci2 ≥ … ≥ CiCei−1);
- (3)
- Constant-trend: each user i will reserve on the same number of cells for every hand-over (Ci1 = Ci2 = … = CiCei−1).
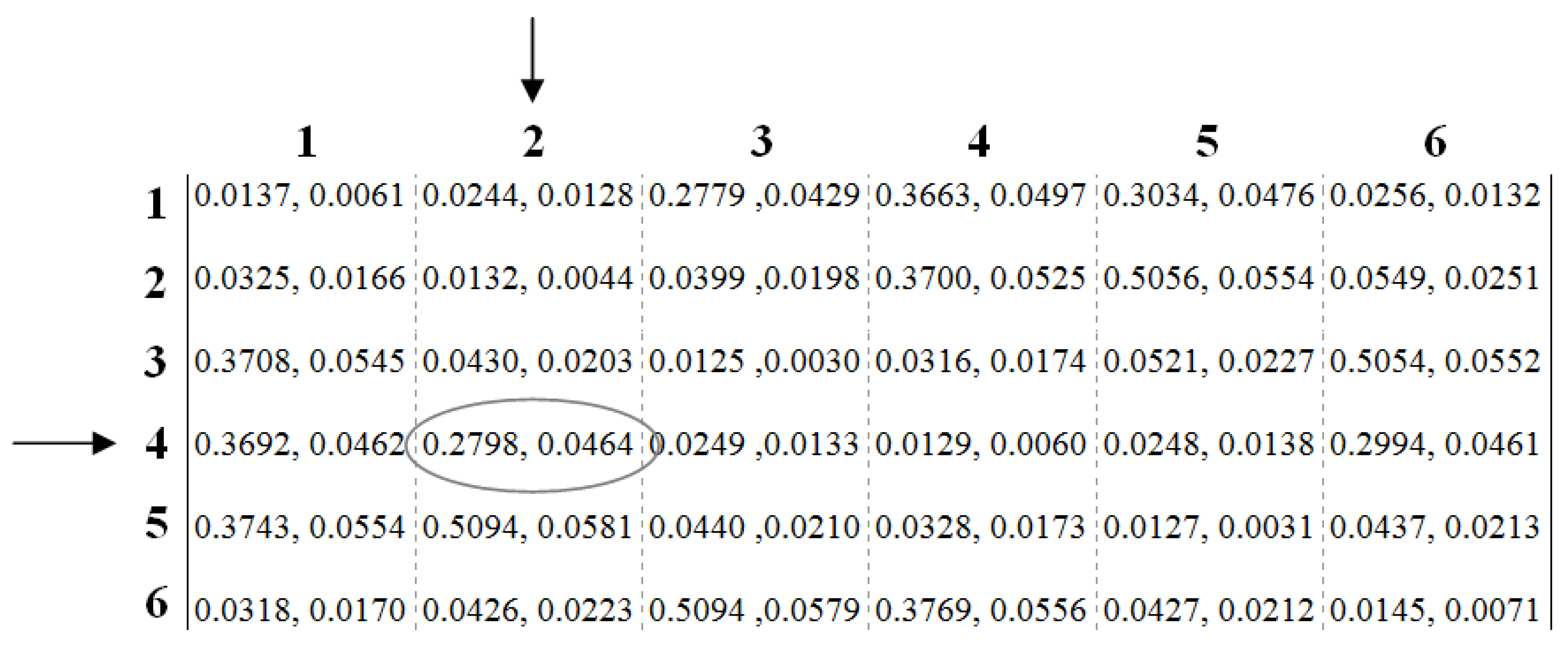
6.2. Dynamic Scheme
- (a)
- cell_id is a cell identifier;
- (b)
- from, to Sho are the hand-in and hand-out directions for the cell_id;
- (c)
- pcell_id is the probability that user will be covered by cell_id after the k-th hand-off.
7. Performance Evaluation
7.1. General Simulation Setup and Parameters
- (1)
- constant trend: Ci1 = Ci2 = Ci3 = 1;
- (2)
- increasing trend: Ci1 = 1, Ci2 = 2, Ci3 = 3;
- (3)
- decreasing trend: Ci1 = 3, Ci2 = 2, Ci3 = 1 with Cij = 1 j {4…Cei−1};
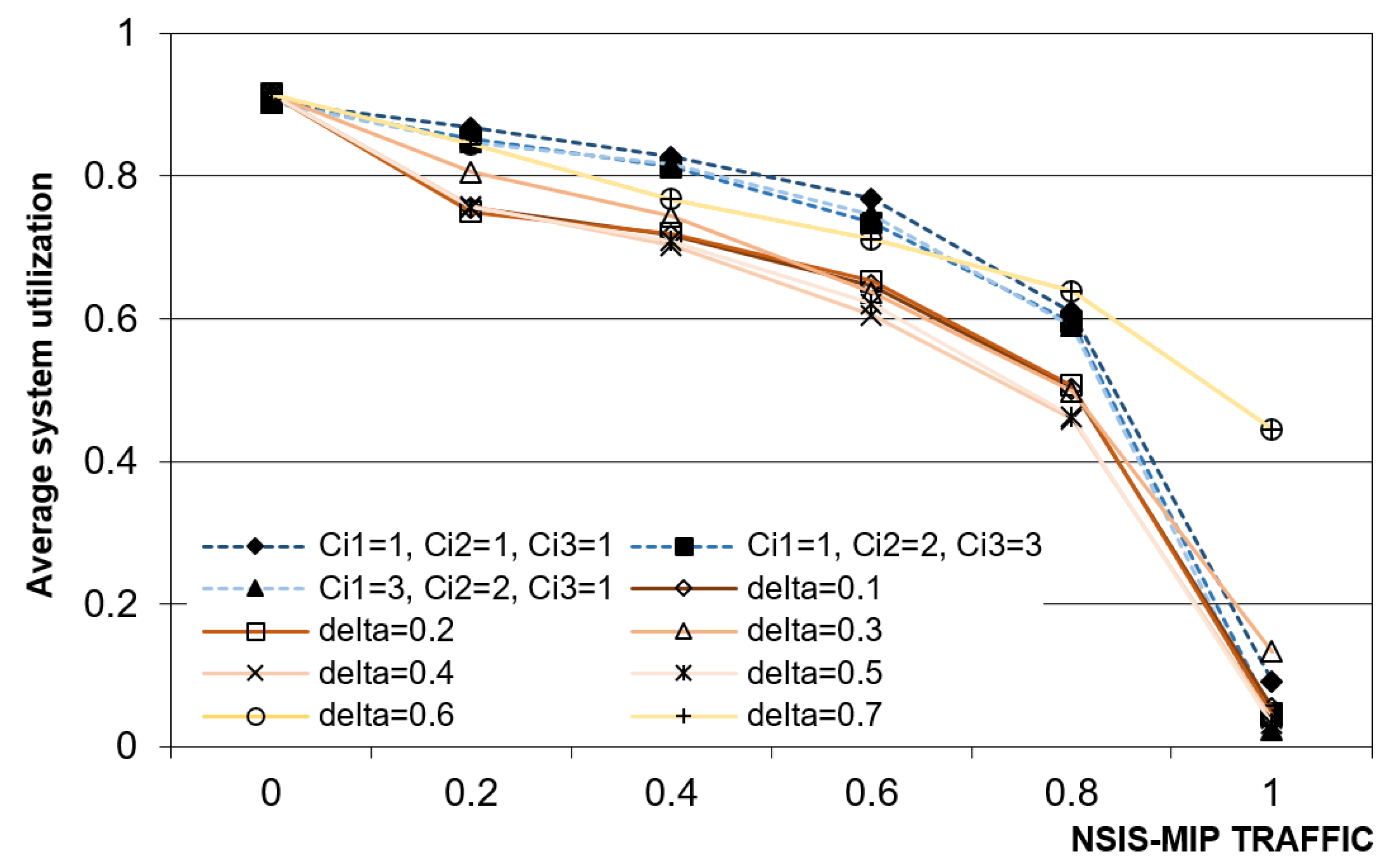
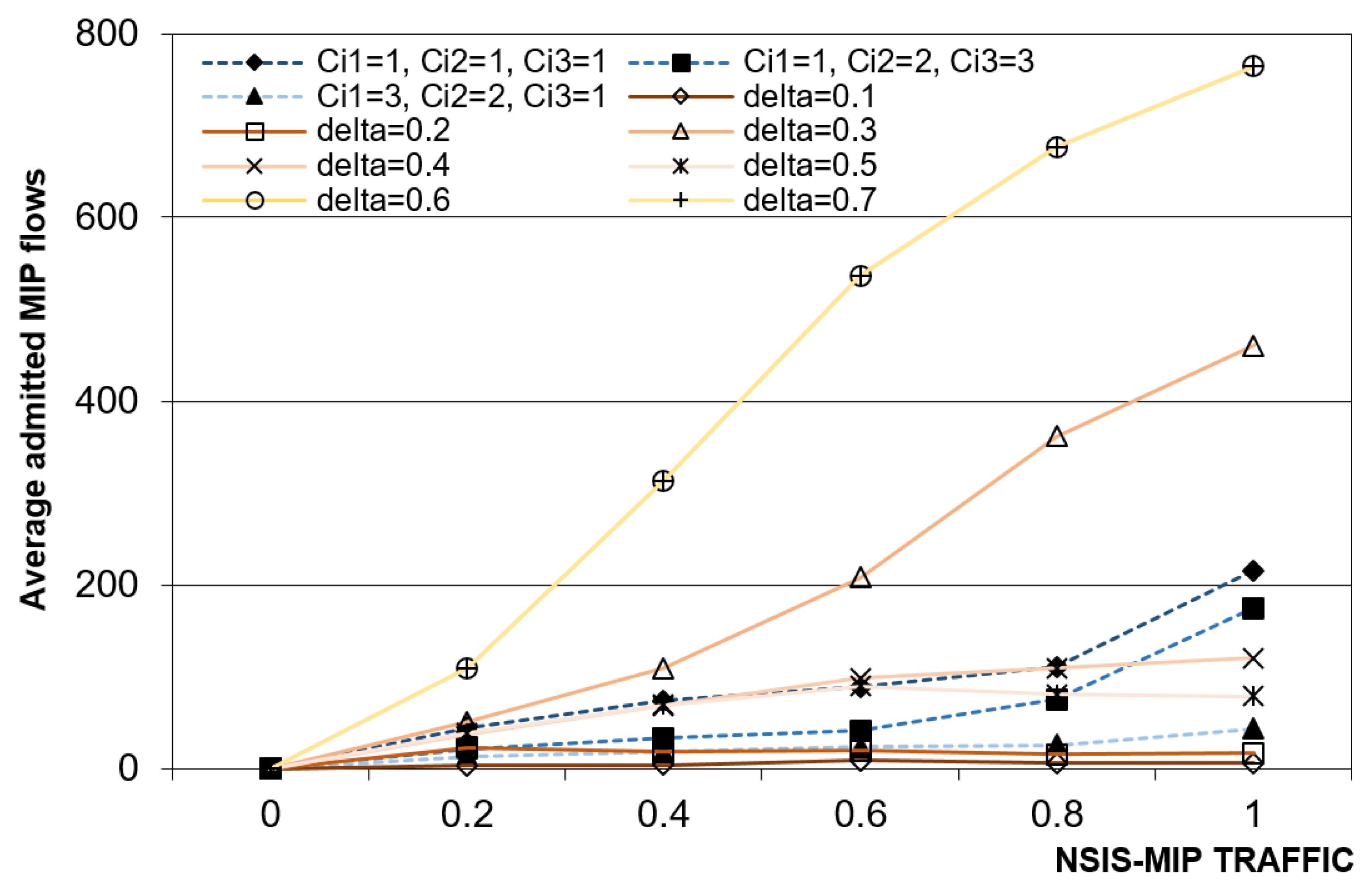
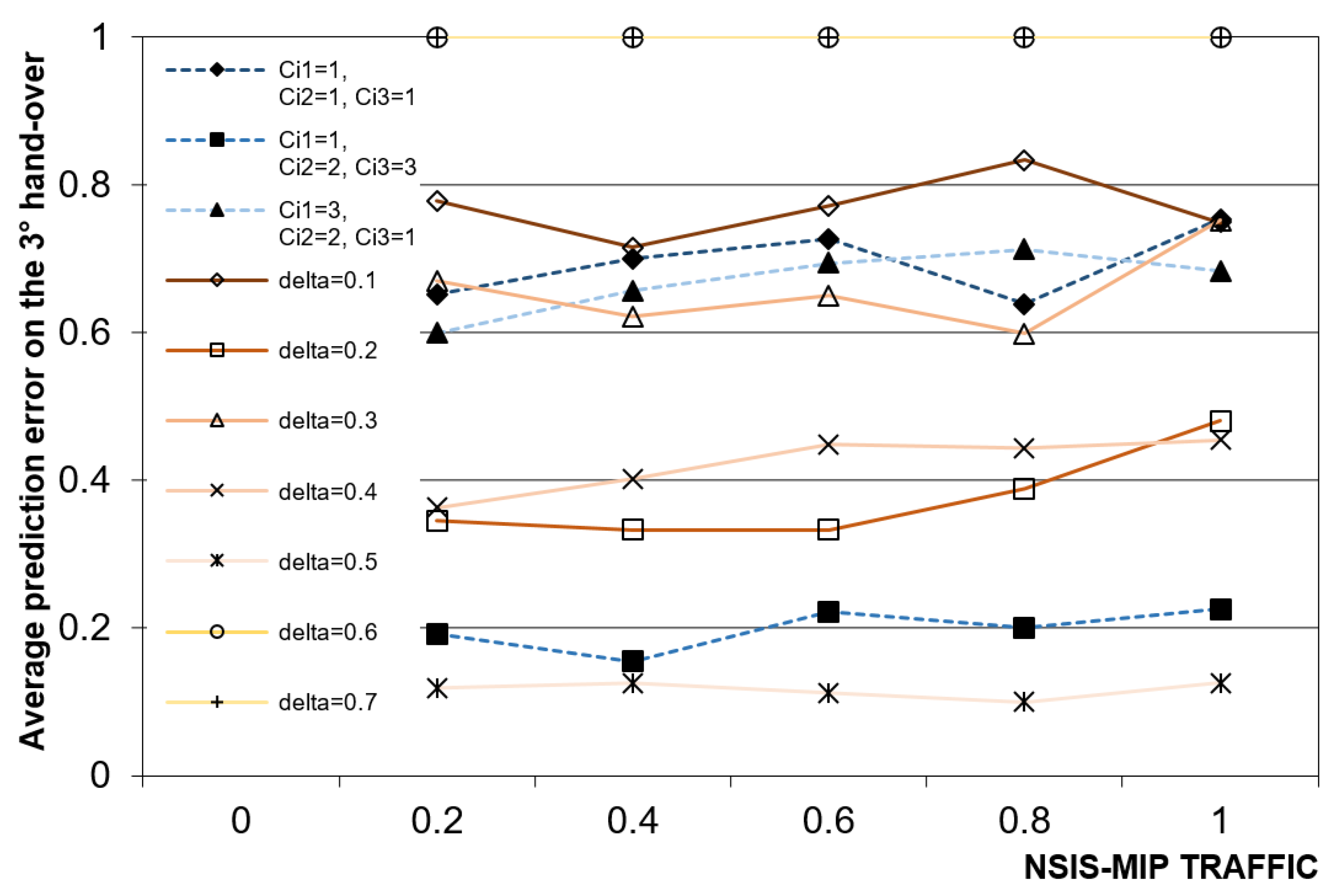
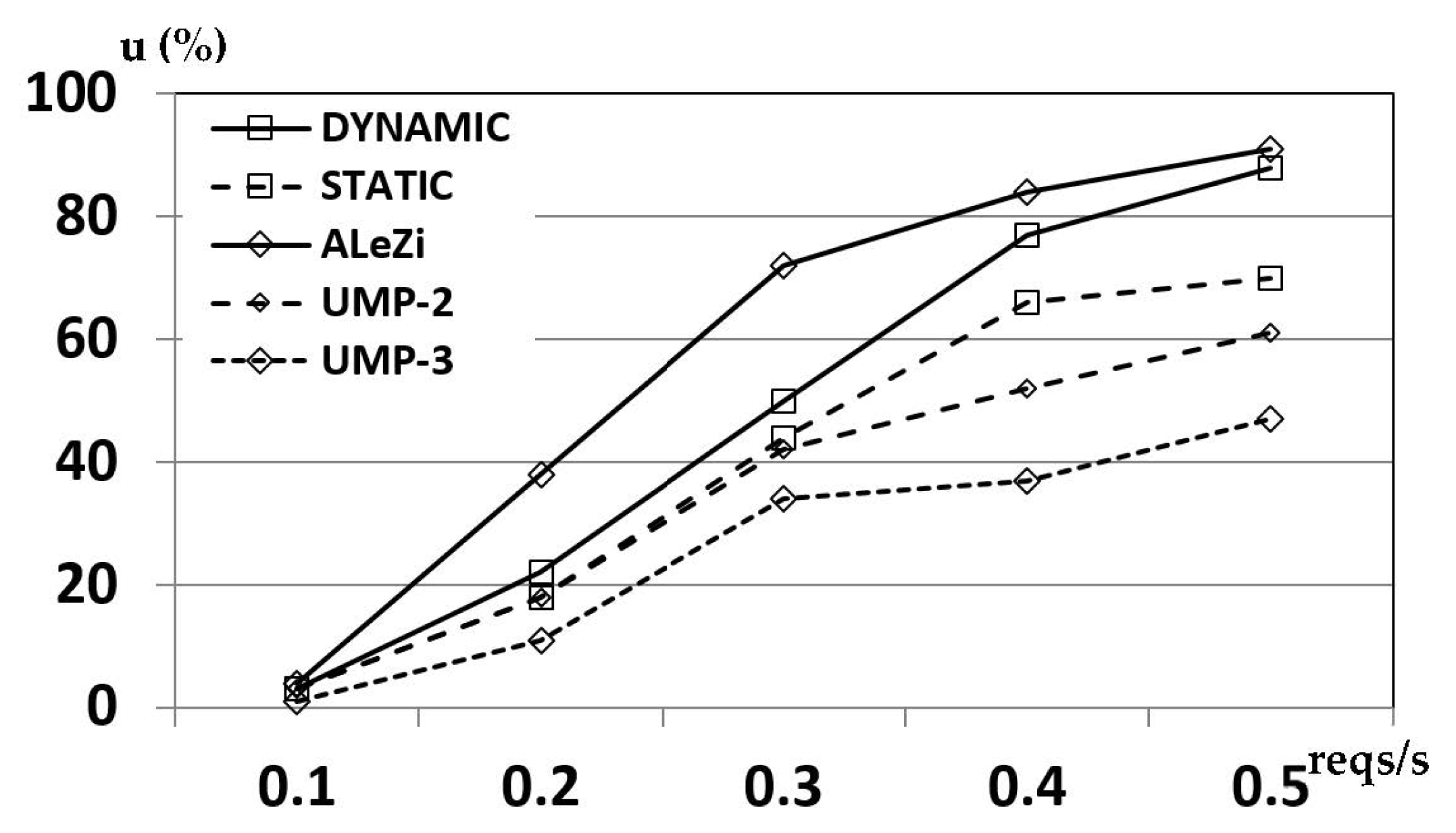
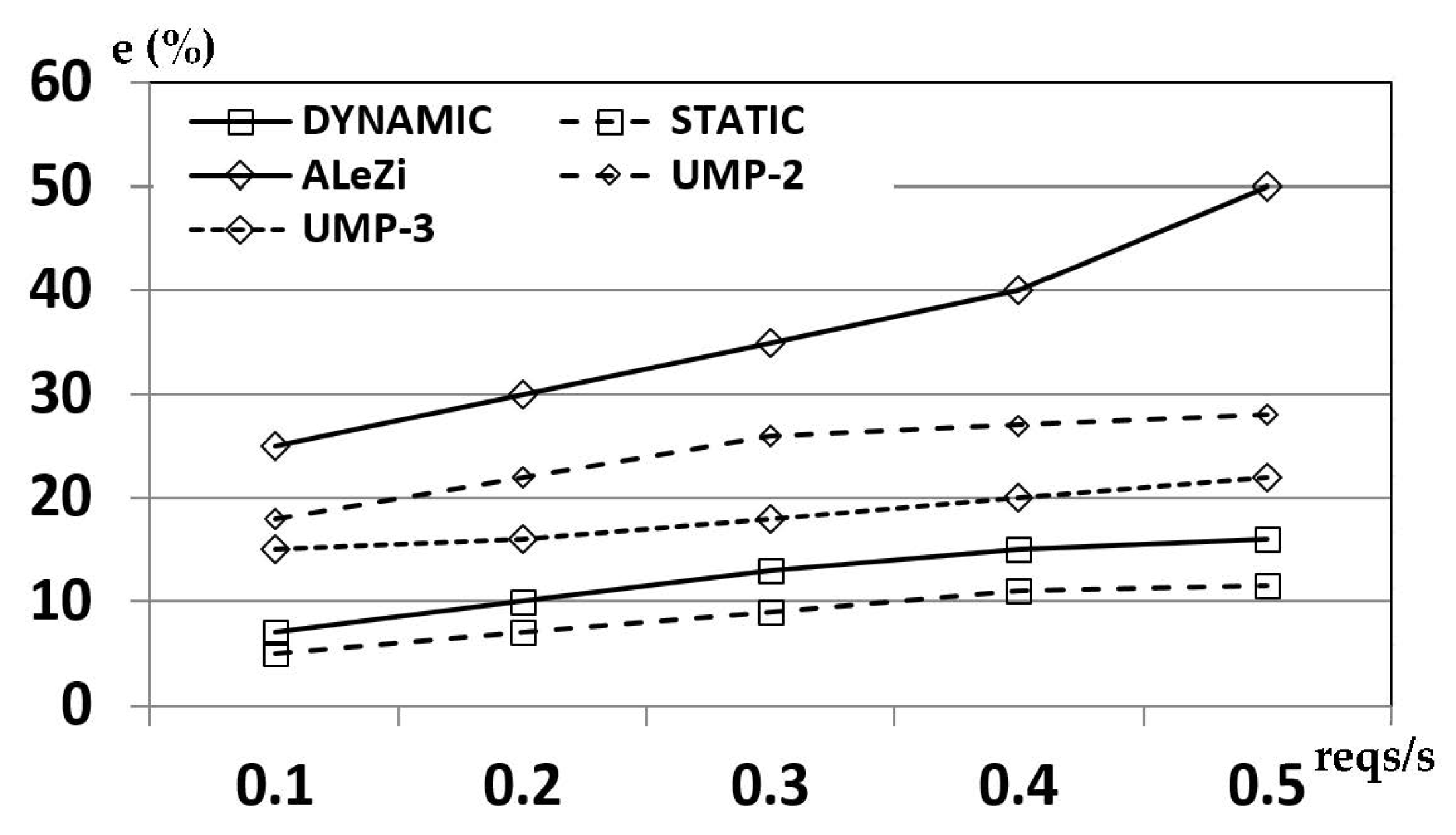
7.2. Main Reachable Results
7.3. Performance Comparison
8. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| ALeZi | Active Lempel-Ziv |
| AP | Access Point |
| BE | Best Effort |
| BER | Bit Error Rate |
| BRS | Bandwidth Reallocation Scheme |
| BS | Base Station |
| C4R | Citymob4Roadmaps |
| CAC | Call Admission Control |
| CAT | Call Arrival Time |
| CDP | Call Dropping Probability |
| CHT | Call Holding Time |
| CST | Cell Stay Time |
| DH | Historical Path Database |
| DRSVP | Dynamic resource ReServation Protocol |
| FSMC | Finite State Markov Chain |
| GIS | Geographic Information System |
| HDP | Hand-off Directions Probabilities |
| HMM | Hidden Markov Models |
| ISPN | Integrated Services Packet Network |
| KS | Kolmogorov Smirnov |
| MDP | Mobility Dependent Predictive |
| MIG | Mobility Independent Guaranteed |
| MIP | Mobility Independent Predictive |
| MRSVP | Mobile resource ReSerVation Protocol |
| NSIS | Next Steps in Signaling |
| NSLP | NSIS Signaling Layer Protocol |
| NTLP | NSIS Transport Layer Protocol |
| ODbL | Open Database License |
| OSMF | Open StreetMap Foundation |
| PD | Path Database |
| PoI | Point of Interest |
| PPM | Prediction Partial Matching |
| QoS | Quality of Service |
| RMM | Random Way Point Mobility Model |
| RSVP | ReSerVation Protocol |
| RTV | Real Time Video |
| SS | Switching Subnet |
| TRM | Trace Record Matrix |
| UMP | User Mobile Profile |
References
- Miyazaki, T.; Iwashita, K. Towards adaptive networking. In Proceedings of the 7th IEEE International Symposium on High Assurance Systems Engineering, Tokyo, Japan, 23–25 October 2002; pp. 151–158. [Google Scholar] [CrossRef]
- Wakamiya, N.; Murata, M. Autonomous and adaptive wireless networking with bio-inspired algorithms. In Proceedings of the 2011 Tenth International Symposium on Autonomous Decentralized Systems, Tokyo, Japan, 23–27 March 2011; pp. 597–602. [Google Scholar] [CrossRef]
- Wang, H.S.; Moayeri, N. Finite-state markov channel—A useful model for radio communication channels. IEEE Trans. Veh. Technol. 1995, 44, 163–171. [Google Scholar] [CrossRef]
- Susanto, H.; Kim, B.G. Congestion control and user utility function for real-time traffic. In Proceedings of the 2013 IEEE Globecom Workshops (GC Wkshps), Atlanta, GA, USA, 9–13 December 2013; pp. 974–979. [Google Scholar] [CrossRef]
- Talukdar, A.K.; Badrinath, B.R.; Acharya, A. MRSVP: A resource reservation protocol for an integrated services network with mobile hosts. Wirel. Netw. 2001, 7, 5–19. [Google Scholar] [CrossRef]
- Talukdar, A.K.; Badrinath, B.R.; Acharya, A. On accomodating mobile hosts in an integrated services packet network. In Proceedings of the IEEE INFOCOM ’97, Kobe, Japan, 7–11 April 1997. [Google Scholar]
- Soret, B.; Aguayo-Torres, M.C.; Entrambasaguas, J.T.; Paris, J.F. Utility based adaptive resource allocation for heterogeneous QoS requirements. In Proceedings of the 2006 3rd International Symposium on Wireless Communication Systems, Valencia, Spain, 6–9 September 2006; pp. 35–39. [Google Scholar] [CrossRef]
- Liao, R.-F.; Campbell, A.T. A utility-based approach to quantitative adaptation in wireless packet networks. ACM J. Wirel. Netw. 2001, 7, 541–557. [Google Scholar] [CrossRef]
- Gomez, J.; Campbell, A.T. Havana: Supporting application and channel dependent QOS in wireless networks. ACM J. Wirel. Netw. 2003, 9, 21–35. [Google Scholar] [CrossRef]
- De Rango, F.; Tropea, M. Energy saving and load balancing in wireless ad hoc networks through ant-based routing. In Proceedings of the 2009 International Symposium on Performance Evaluation of Computer & Telecommunication Systems, Istanbul, Turkey, 13–16 July 2009; Volume 41, pp. 117–124. [Google Scholar]
- Betstetter, C. Mobility modeling in wireless networks: Categorization, smooth movement, and border effects. ACM Sigmob. Mob. Comput. Commun. Rev. 2001, 5, 55–66. [Google Scholar] [CrossRef]
- Akyildiz, I.F.; Wang, W. The predictive user mobility framework for wireless multimedia networks. IEEE ACM Trans. Netw. 2004, 12, 1021–1035. [Google Scholar] [CrossRef]
- Magnano, A.; Fei, X.; Boukerche, A. Predictive mobile IP handover for vehicular networks. In Proceedings of the 2015 IEEE 40th Conference on Local Computer Networks (LCN), Clearwater Beach, FL, USA, 26–29 October 2015; pp. 338–346. [Google Scholar] [CrossRef] [Green Version]
- Zhao, T.; Hao, J.; Sun, L.; Li, J.; Ma, Y. On mobility models in vehicular communication system. In Proceedings of the 2nd IEEE International Conference on Broadband Network & Multimedia Technology, Beijing China, 18–20 October 2009; pp. 57–61. [Google Scholar] [CrossRef]
- Martinez, F.J.; Cano, J.-C.; Calafate, C.T.; Manzoni, P. CityMob: A mobility model pattern generator for VANETs. In Proceedings of the 2008 IEEE International Conference on Communications Workshops, Beijing, China, 19–23 May 2008; pp. 370–374. [Google Scholar]
- City for Roadmaps (C4R) Reference Manual. 2011. Available online: http://www.grc.upv.es/Software/c4r/usermanual.pdf (accessed on 25 August 2021).
- Baker, F.; Braden, B.; Bradner, S.; O’Dell, M.; Romanow, A.; Weinrib, A.; Zhang, L. Resource ReSerVation Protocol (RSVP)—Version 1 Applicability Statement Some Guidelines on Deployment; RFC2208; Mankin, A., Ed.; RFC Editor: Marina del Rey, CA, USA, 1997. [Google Scholar]
- Braden, R.; Zhang, L. Resource ReSerVation Protocol (RSVP)—Version 1 Message Processing Rules; RFC2209; RFC Editor: Marina del Rey, CA, USA, 1997. [Google Scholar]
- Lin, T.Y.; Tsai, C.Y.; Wu, K.R. EARC: Enhanced adaptation of link rate and contention window for IEEE 802.11 multi-rate wireless networks. IEEE Trans. Commun. 2012, 60, 2623–2634. [Google Scholar] [CrossRef]
- Kuo, G.S.; Ko, P.C. Dynamic RSVP protocol. IEEE Commun. Mag. 2003, 41, 130–135. [Google Scholar] [CrossRef]
- Mirhakkak, M.; Schult, N.; Thomson, D. Dynamic bandwidth management and adaptive applications for a variable bandwidth wireless environment. IEEE J. Sel. Areas Commun. 2004, 22, 719–726. [Google Scholar] [CrossRef]
- Jeon, H.; Yi, J. Performance analysis of mobile RSVP and hierarchical mobile RSVP. In Proceedings of the 2006 Asia-Pacific Conference on Communications, Busan, Korea, 31 August–1 September 2006. [Google Scholar]
- Fu, X.; Schulzrinne, H.; Bader, A.; Hogrefe, D.; Kappler, C.; Karagiannis, G. NSIS: A new extensible IP signalling protocol suite. IEEE Commun. Mag. 2005, 42, 133–141. [Google Scholar]
- Arumaithurai, M.; Fu, X.; Schloer, B.; Tschofenig, H. Performance study of NSIS QoS-NSLP protocol. In Proceedings of the 2008 IEEE Global Telecommunications Conference, New Orleans, LA, USA, 30 November–4 December 2008. [Google Scholar]
- Lytrivis, P.; Thomaidis, G.; Tsogas, M.; Amditis, A. An advanced cooperative path prediction algorithm for safety applications in vehicular networks. IEEE Trans. Intell. Transp. Syst. 2011, 12, 669–679. [Google Scholar] [CrossRef]
- Nadembega, A.; Hafid, A.; Taleb, T. A destination and mobility path prediction scheme for mobile networks. IEEE Trans. Veh. Technol. 2014, 64, 2577–2590. [Google Scholar] [CrossRef]
- Zhang, D.; Vasilakos, A.V.; Xiong, H. Predicting location using mobile phone calls. In Proceedings of the ACM SIGCOMM 2012 Conference on Applications, Technologies, Architectures, and Protocols for Computer Communication, Helsinki, Finland, 13–17 August 2012; pp. 295–296. [Google Scholar]
- Nadembega, A.; Hafid, A.; Taleb, T. Mobility Prediction-aware Bandwidth Reservation Scheme for Mobile Networks. IEEE Trans. Veh. Technol. 2014, 64, 2561–2576. [Google Scholar] [CrossRef]
- Tropea, M.; Marano, S. A novel pattern prediction and bandwidth management scheme in wireless networks with mobile hosts. In Proceedings of the 2013 IEEE 77th Vehicular Technology Conference (VTC Spring), Dresden, Germany, 2–5 June 2013; pp. 1–5. [Google Scholar]
- De Rango, F.; Fazio, P.; Marano, S. Utility-based predictive services for adaptive wireless networks with mobile hosts. IEEE Trans. Veh. Technol. 2009, 58, 1415–1428. [Google Scholar] [CrossRef]
- Fazio, P.; Tropea, M.; Marano, S. A distributed hand-over management and pattern prediction algorithm for wireless networks with mobile hosts. In Proceedings of the 2013 9th International Wireless Communications and Mobile Computing Conference (IWCMC), Sardinia, Italy, 1–5 July 2013; pp. 294–298. [Google Scholar]
- Fazio, P.; Tropea, M.; De Rango, F.; Voznak, M. Pattern prediction and passive bandwidth management for hand-over optimization in QoS cellular networks with vehicular mobility. IEEE Trans. Mob. Comput. 2016, 15, 2809–2824. [Google Scholar] [CrossRef]
- Fazio, P.; De Rango, F.; Tropea, M. Prediction and qos enhancement in new generation cellular networks with mobile hosts: A survey on different protocols and conventional/unconventional approaches. IEEE Commun. Surv. Tutor. 2017, 19, 1822–1841. [Google Scholar] [CrossRef]
- Wang, G.-G.; Wei, C.-L.; Wang, Y.; Pedrycz, W. Improving distributed anti-flocking algorithm for dynamic coverage of mobile wireless networks with obstacle avoidance. Knowl. Based Syst. 2021, 225, 107133. [Google Scholar] [CrossRef]
- Gao, X.; Fan, J.; Wu, F.; Chen, G. Cooperative sweep coverage problem with mobile sensors. IEEE Trans. Mob. Comput. 2020. early access. [Google Scholar] [CrossRef]
- Chowdhury, A.; De, D. FIS-RGSO: Dynamic fuzzy inference system based reverse glowworm swarm optimization of energy and coverage in green mobile wireless sensor networks. Comput. Commun. 2020, 163, 12–34. [Google Scholar] [CrossRef]
- Balsa-Barreiro, J.; Valero-Mora, P.M.; Berné-Valero, J.L.; Varela-García, F.A. GIS mapping of driving behavior based on naturalistic driving data. ISPRS Int. J. Geo-Inform. 2019, 8, 226. [Google Scholar] [CrossRef] [Green Version]
- Balsa-Barreiro, J.; Valero-Mora, P.M.; Pareja-Montoro, I.; Sánchez-García, M. Proposal of geographic information systems methodology for quality control procedures of data obtained in naturalistic driving studies. IET Intell. Transp. Syst. 2015, 9, 673–682. [Google Scholar] [CrossRef]
- Mirzamany, E.; Lasebae, A.; Gemikonakli, O. Efficient NSIS mobility support for mobile networks. In Proceedings of the 2013 IEEE 24th Annual International Symposium on Personal, Indoor, and Mobile Radio Communications (PIMRC), London, UK, 8–11 September 2013; pp. 3354–3359. [Google Scholar] [CrossRef]
- Open Street Map, by Steve Coast. Available online: https://www.openstreetmap.org/ (accessed on 10 August 2021).
- Simulation of Urban MObility (SUMO). Available online: http://www.dlr.de/ (accessed on 12 August 2021).
- Wagner, P. How human drivers control their vehicle. Eur. Phys. J. B 2006, 52, 427–431. [Google Scholar] [CrossRef]
- Kerner, B.S. Criticism of generally accepted fundamentals and methodologies of traffic and transportation theory: A brief review. Phys. A Stat. Mech. Appl. 2013, 392, 5261–5282. [Google Scholar] [CrossRef]
- Zhang, J.; Ansari, N. An application-oriented fair resource allocation scheme for EPON. IEEE Syst. J. 2010, 4, 424–431. [Google Scholar] [CrossRef]
- Jiang, Z.; Ye, G.; Li, Y.G. Max-utility wireless resource management for best-effort traffic. IEEE Trans. Wirel. Commun. 2005, 4, 100–111. [Google Scholar] [CrossRef]
- Hassan, M.; Krunz, M.M.; Matta, I. Markov-based channel characterization for tractable performance analysis in wireless packet networks. IEEE Trans. Wirel. Commun. 2005, 3, 821–831. [Google Scholar] [CrossRef]
- IEEE. Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications: Higher-Speed Layer Extension in the 2.4GHz Band; IEEE: Piscataway Township, NJ, USA, 1999. [Google Scholar]
- Fazio, P.; Tropea, M. A new markovian prediction scheme for resource reservations in wireless networks with mobile hosts. Adv. Electr. Electron. Eng. 2012, 10, 204–210. [Google Scholar] [CrossRef]
- Fazio, P.; Tropea, M.; Sottile, C.; Marano, S.; Voznak, M.; Strangis, F. Mobility prediction in wireless cellular networks for the optimization of call admission control schemes. In Proceedings of the IEEE 27th Canadian Conference on Electrical and Computer Engineering (CCECE), Toronto, ON, Canada, 4–7 May 2014. [Google Scholar]
- Montgomery, C. Applied Statistics and Probability for Engineers, 16th ed.; Wiley: Hoboken, NJ, USA, 2013. [Google Scholar]
- Hsu, L.-Y.; Chen, T.-L. Vehicle full-state estimation and prediction system using state observers. IEEE Trans. Veh. Technol. 2008, 58, 2651–2662. [Google Scholar] [CrossRef]
- Achir, M.; Ghamri-Doudane, M.; Pujolle, G. Predictive resource allocation in cellular networks using Kalman filters. In Proceedings of the on IEEE International Conference Communications (ICC), Anchorage, AK, USA, 11–15 May 2003; Volume 2, pp. 974–981. [Google Scholar]
- Banks, J.; Carson, J.S.; Nelson, B.; Nicol, D. Discrete-Event System Simulation, 15th ed.; Prentice Hall: Hoboken, NJ, USA, 2009. [Google Scholar]
- Park, K.; Kim, G.; Crovella, M. On the relationship between file sizes, transport protocols, and self-similar network traffic. In Proceedings of the 4th International Conference on Network Protocols (ICNP), Columbus, OH, USA, 29 October–1 November 1996. [Google Scholar]
- Carrion, A.-R.; Garcia-Rubio, C.; Campo, C. Performance evaluation of LZ-based location prediction algorithms in cellular networks. IEEE Commun. Lett. 2010, 14, 707–709. [Google Scholar] [CrossRef]
- Socievole, A.; De Rango, F.; Caputo, A. Wireless contacts, Facebook friendships and interests: Analysis of a multi-layer social network in an academic environment. In Proceedings of the 2014 IFIP Wireless Days (WD), Rio de Janeiro, Brazil, 12–14 November 2014; pp. 1–7. [Google Scholar]






| Mobility Parameters | P(1-1-1) | P(1-2-3) | P(3-3-3) | |||
|---|---|---|---|---|---|---|
| Cr(P) | Cr | Cr(P) | Cr | Cr(P) | Cr | |
| amax = 1.4 m/s2, amin = −2 m/s2, τ = 0.3 | ||||||
| µ = 29.26 s, σ = 0.45729 s | 5 | 60 | 22 | 60 | 52 | 60 |
| amax = 1 m/s2, amin = −2.5 m/s2, τ = 0.4 | ||||||
| µ = 62.22 s, σ = 5.09547 s | 2 | 6 | 3 | 6 | 4 | 6 |
| amax = 1.3 m/s2, amin = −2 m/s2, τ = 0.2 | ||||||
| µ = 32.46 s, σ = 8.18356 s | 4 | 36 | 16 | 36 | 21 | 36 |
| STATIC | DYNAMIC | |||||||||
|---|---|---|---|---|---|---|---|---|---|---|
| NSIS-MIP | 111 | 123 | 321 | 0.1 | 0.2 | 0.3 | 0.4 | 0.5 | 0.6 | 0.7 |
| 0 | 0.01213 | 0.01275 | 0.01542 | 0.01547 | 0.01551 | 0.01558 | 0.01571 | 0.01583 | 0.0163 | 0.018 |
| 0.2 | 0.01433 | 0.01455 | 0.01143 | 0.01278 | 0.01358 | 0.01945 | 0.01466 | 0.01448 | 0.01479 | 0.01483 |
| 0.4 | 0.01913 | 0.01874 | 0.01893 | 0.01932 | 0.01945 | 0.02013 | 0.01957 | 0.01961 | 0.01968 | 0.01973 |
| 0.6 | 0.0214 | 0.01973 | 0.01995 | 0.0214 | 0.01903 | 0.02988 | 0.02531 | 0.0174 | 0.02243 | 0.02673 |
| 0.8 | 0.0403 | 0.0413 | 0.042 | 0.0416 | 0.0435 | 0.0448 | 0.04532 | 0.04723 | 0.04831 | 0.04981 |
| 1 | ||||||||||
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Fazio, P.; Tropea, M. Advanced Resources Reservation in Mobile Cellular Networks: Static vs. Dynamic Approaches under Vehicular Mobility Model. Telecom 2021, 2, 302-327. https://doi.org/10.3390/telecom2040020
Fazio P, Tropea M. Advanced Resources Reservation in Mobile Cellular Networks: Static vs. Dynamic Approaches under Vehicular Mobility Model. Telecom. 2021; 2(4):302-327. https://doi.org/10.3390/telecom2040020
Chicago/Turabian StyleFazio, Peppino, and Mauro Tropea. 2021. "Advanced Resources Reservation in Mobile Cellular Networks: Static vs. Dynamic Approaches under Vehicular Mobility Model" Telecom 2, no. 4: 302-327. https://doi.org/10.3390/telecom2040020
APA StyleFazio, P., & Tropea, M. (2021). Advanced Resources Reservation in Mobile Cellular Networks: Static vs. Dynamic Approaches under Vehicular Mobility Model. Telecom, 2(4), 302-327. https://doi.org/10.3390/telecom2040020







