The Flash Loan Attack Analysis (FAA) Framework—A Case Study of the Warp Finance Exploitation
Abstract
1. Introduction
- (i)
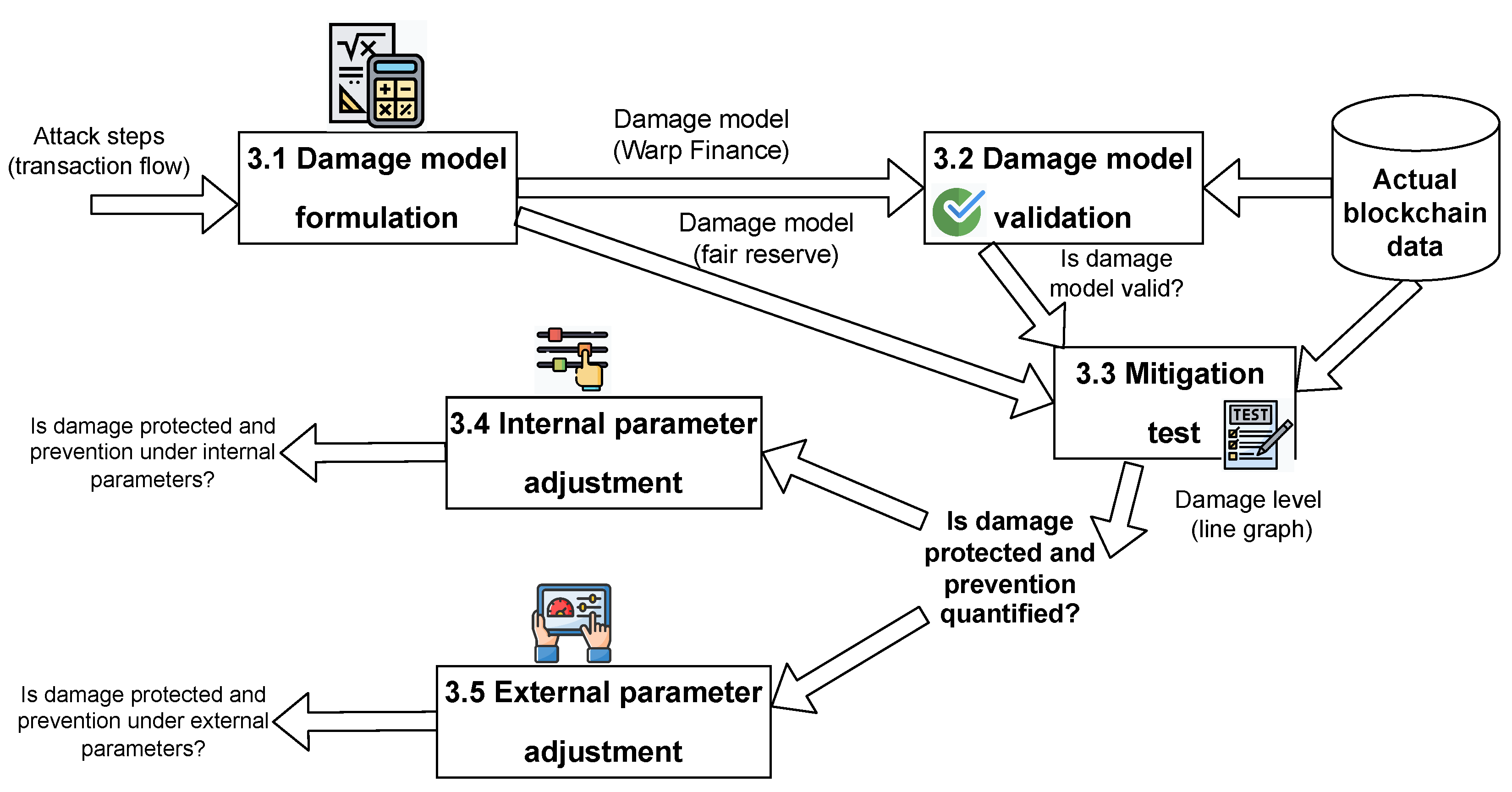
- We proposed the FAA framework that allows security researchers to simulate attacks in different environments and a suitable and versatile risk countermeasure for the DeFi platform (see details in Section 3.1 and Section 3.2).
- (ii)
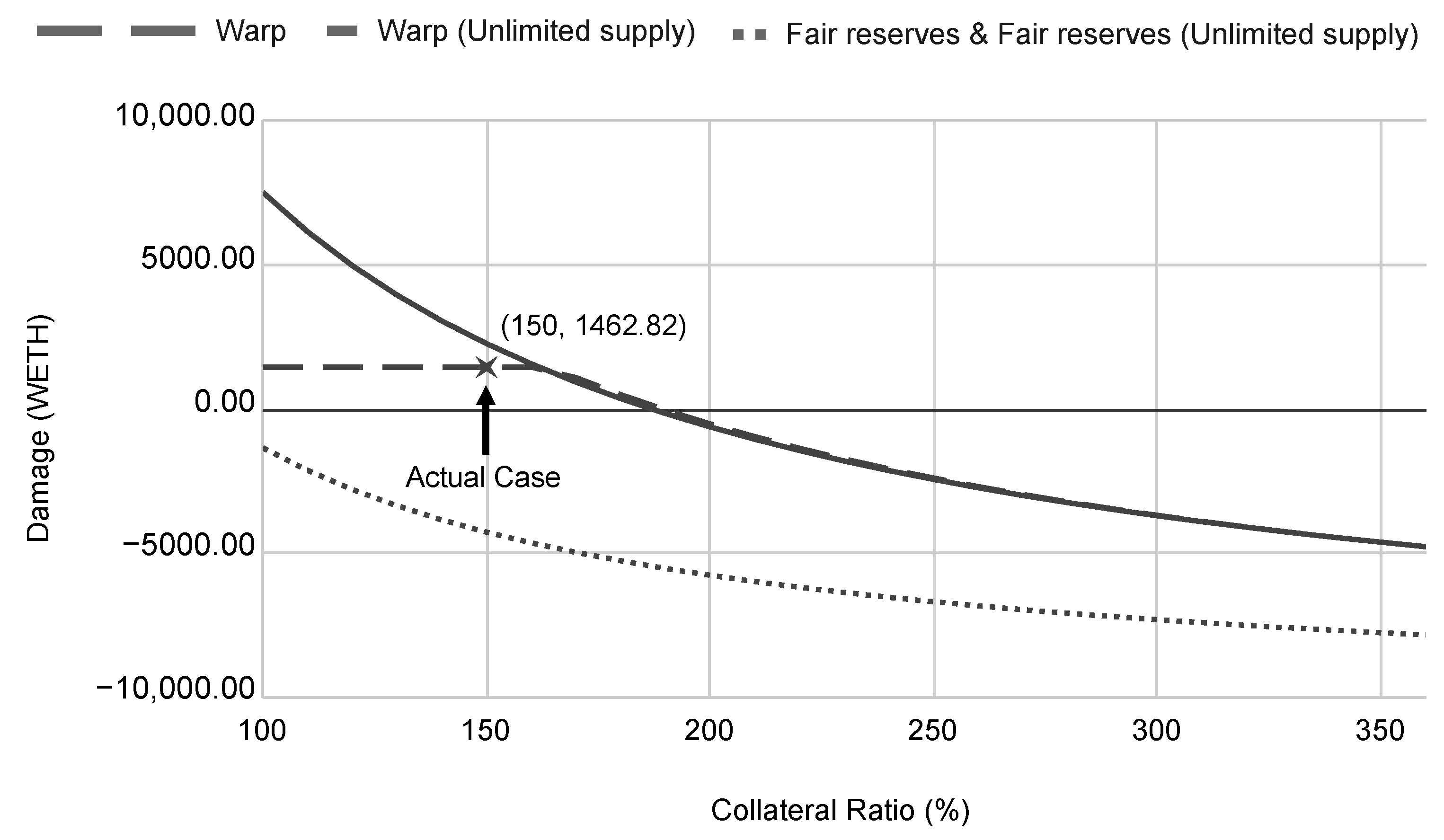
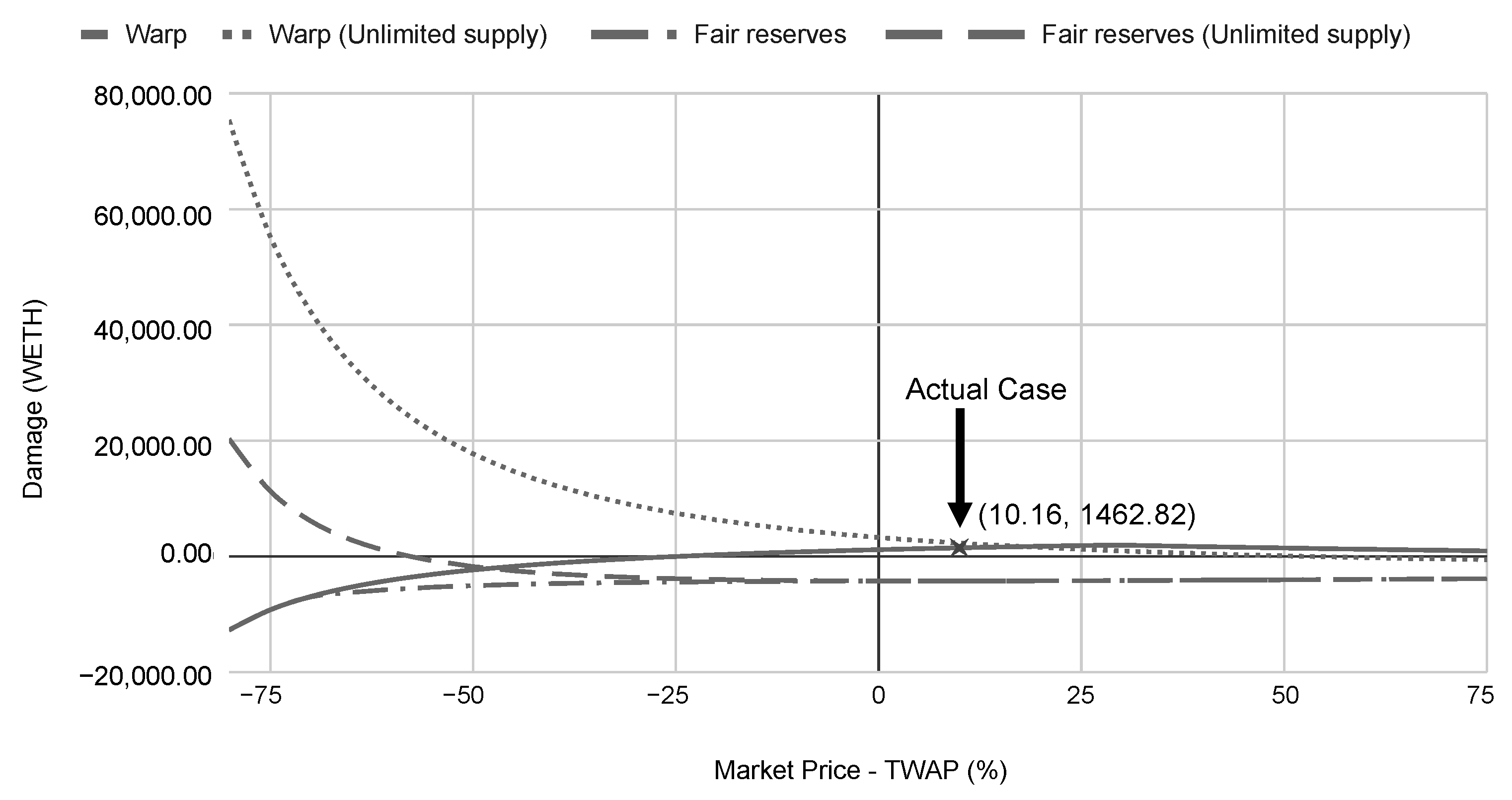
- We analyzed the efficiency of the existing fair reserves model by determining the potential damage prevented by the model in many circumstances. The report from the proposed FAA framework provides insight validation of the fair reserves protocol. It is crucial to ensure that the model is well validated before applying it to prevent potential damage (details are given in Section 3.3).
- (iii)
- We conducted simulations on flash loan sizes, collateral ratios, and market conditions to predict the degree of damage on the DeFi platform. Our analyses unveil the strengths and weaknesses of the existing TWAP and fair reserves models with respect to various internal and external conditions. Details of the analyses are discussed in Section 3.4 and Section 3.5, while our insights are presented in Section 4.
- (iv)
- We suggested a holistic prevention approach, which consists of the top six (6) best countermeasures to flash loan attacks (Section 5).
2. Related Work
2.1. Blockchain, DeFi, and Smart Contract
2.1.1. DeFi Vulnerability
- (i)
- (ii)
- (iii)
- Smart contract exploits: These attacks take advantage of vulnerabilities in the smart contracts that underlie DeFi platforms, allowing attackers to steal or redirect funds. For instance, the smart contract weakness classification (SWC) [23], reentrancy attack [24], front-running attack [25], and rug pull scam [26].
2.1.2. Defi Risk Assessment Framework
2.2. Flash Loans
2.2.1. Arbitrageur
2.2.2. Collateral Swap
2.2.3. Self-Liquidation
2.2.4. Lower Transaction Fees
2.3. Flash Loan Attacks
2.4. Flash Loan Attack Prevention
3. A Novel DeFi Attack Risk Analysis Framework
3.1. Damage Model Formulation
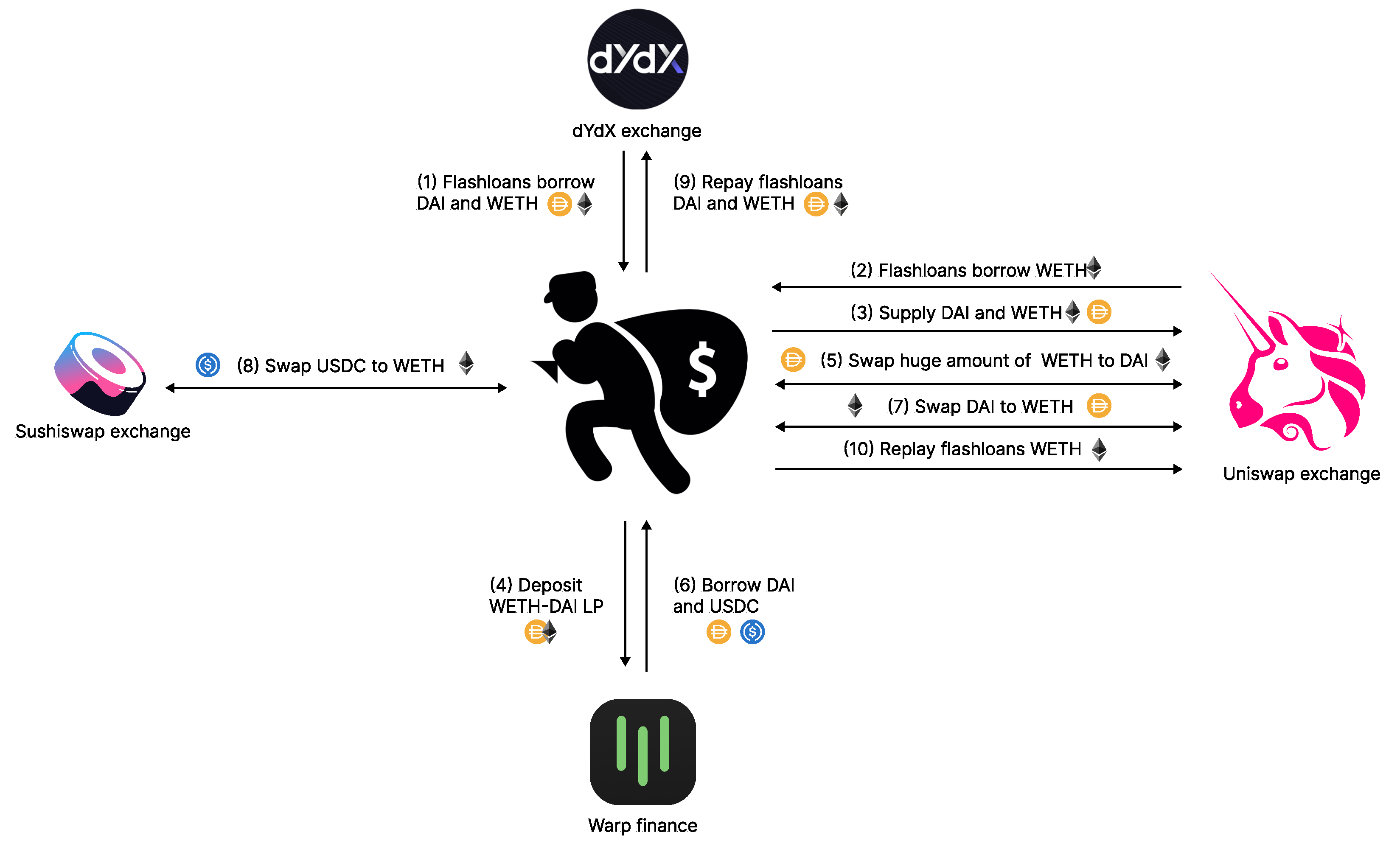
- (i)
- The attacker used flash loans to borrow DAI from dYdX solo margin pools. The amount of the borrowed DAI is denoted as .
- (ii)
- WETH is borrowed from the Uniswap and dYdX solo margin pools using flash loans. Let denote the maximum amount of WETH the attacker can borrow.
- (iii)
- DAI and WETH were supplied to Uniswap’s WETH-DAI pool to mint WETH-DAI LP tokens, which would be used as collateral for borrowing tokens from Warp Finance. Note that the values of the supplied DAI and WETH must be equal. Let and denote the amount of DAI and WETH in the pool, respectively.
- (iv)
- The attacker supplied all DAI () and the equivalent WETH () to the pool:The minted LP token amount (D), where represents the total supply of WETH-DAI tokens before supplying, is determined by the following equation:After adding liquidity, the pool reserved, and the total LP token supply was changed as follows:
- (v)
- Since the exploitation occurred while Warp finance was using their equation, the LP token price () was calculated using TWAP and real-time reserves, where and denote DAI and WETH TWAP, respectively:According to the report [6], the root cause of the exploitation related to the LP token price () calculation. Hence, we define the LP token price model (i.e., Equation (7)) as the core submodel, which is to be used in the upcoming steps.All the minted WETH-DAI LP tokens (D) were supplied to Warp Finance as collateral. LP token value in USD is denoted as (). The attacker was able to borrow tokens from Warp Finance. The borrowing limit (B) is the deposited LP token value divided by 1.5, which is the constant collateral value defined by the Warp Finance protocol.
- (vi)
- The attacker swapped the remaining WETH () for DAI () using the Uniswap WETH-DAI pool,Since the token swapping fee is 0.3%, is multiplied by 0.997. Thus, the trading output can be determined as:This step was the core of the attack as the attacker was able to substantially increase the amount of WETH (i.e., the expensive token) in the pool. The reserve amount changed dramatically after the trade:
- (vii)
- At this stage, the changing of real-time reserves causes LP token price updates. The manipulated LP token price is denoted as .The changing of LP token price affects borrow limit value. The manipulated borrow limit () is determined as follows:
- (viii)
- The attacker borrowed as much DAI as possible from the DAI Warp vault (). DAI was the priority borrowed token because the attacker could swap WETH back at a lower rate in the manipulated WETH-DAI pool. USDC () was borrowed as the secondary token after the vaults were emptied of DAI. The actual borrowed amounts ( and ) are thus determined by the minimum value between the borrowing limit and the available liquidity in the vaults:
- (ix)
- To accomplish the exploit, the attacker had to repay all flash loan positions, particularly, and . As the attacker received DAI from the first swap () and borrowing (), he or she could spare DAI for flash loan repayment. However, he or she did not have WETH. Hence, he or she swapped all the remaining DAI for WETH from the manipulated WETH-DAI pool. Here, we can calculate and as:As the WETH that was swapped for DAI was insufficient for repayment, the attacker used all the borrowed USDC to buy WETH from the Sushiswap WETH-USDC pool. Therefore,
- (x)
- This exploit damaged Warp Finance because the attacker borrowed more tokens than the proper limit. When the excess amount borrowed was sufficient for flash loan repayment plus the borrowing fee, the attack was considered successful. The damage from the attack can be evaluated by the number of tokens the attacker received after the success of the transaction. We therefore can calculate the value of tokens stolen from the platform (denoted ) as follows:
3.1.1. Warp Finance Model
3.1.2. Fair Reserves Model
3.2. Damage Model Validation
3.3. Mitigation Strategies Evaluation
3.4. Internal Parameter Test
3.5. External Parameter Test
4. Our Insights
5. Flash Loan Countermeasures
5.1. TWAP Update Threshold Technique
5.2. Delay Requirement Technique
5.3. Sanity Check Technique
5.4. Minting Limit Technique
5.5. Multiple Price Source Technique
5.6. Suggested Practice for TWAP Implementation
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| USDT/USDC | US Dollars pegged, an asset-backed cryptocurrency stablecoin. USDT and USDC |
| are managed by Tether company limited, Hong Kong and Centre consortium, | |
| respectively [56]. | |
| ETH | Ether, an unstable token for the Ethereum chain [57]. |
| WETH | Wrapped Ether is an ERC-20 token that represents a wrapped version of |
| Ethereum [57]. | |
| DAI | A stable token whose value is kept close to one USD using a smart contract |
| system [42]. | |
| LP | A token from a liquidity provider, which is given to users who loan their tokens |
| to a liquidity pool [37]. | |
| DEX | Decentralized exchange, a marketplace where transactions occur directly between |
| crypto traders [40]. | |
| TWAP | Time Weighted Average Price, the average price of an asset over a specific period |
| of time [9]. | |
| TWAR | Time-Weighted-Average Reserve, the average amount of tokens in a pool of the |
| platform [8]. |
References
- Tolmach, P.; Li, Y.; Lin, S.W.; Liu, Y. Formal analysis of composable DeFi protocols. In Proceedings of the International Conference on Financial Cryptography and Data Security, Virtual Event, 1–5 March 2021; Springer: Berlin/Heidelberg, Germany, 2021; pp. 149–161. [Google Scholar]
- Böhme, R.; Christin, N.; Edelman, B.; Moore, T. Bitcoin: Economics, technology, and governance. J. Econ. Perspect. 2015, 29, 213–238. [Google Scholar] [CrossRef]
- Angeris, G.; Kao, H.T.; Chiang, R.; Noyes, C.; Chitra, T. An Analysis of Uniswap markets. Cryptoecon. Syst. 2021, 1, 1–30. [Google Scholar] [CrossRef]
- Khan, R. Crypto Banking and Decentralized Finance—A New Frontier in Financial Services. 2022. Available online: https://www.forbes.com/sites/roomykhan/2022/04/11/crypto-banking-and-decentralized-finance–a-new-frontier-in-financial-services/?sh=66f1b5391b6d (accessed on 30 April 2022).
- Wang, D.; Wu, S.; Lin, Z.; Wu, L.; Yuan, X.; Zhou, Y.; Wang, H.; Ren, K. Towards a first step to understand flash loan and its applications in DeFi ecosystem. In Proceedings of the Ninth International Workshop on Security in Blockchain and Cloud Computing, Virtual Event, Hong Kong, 7 June 2021; pp. 23–28. [Google Scholar]
- Warp Finance. Warp Finance. 2020. Available online: https://warpfinance.medium.com/warp-finance-exploit-summary-recovery-of-funds-5b8fe4a11898 (accessed on 12 September 2021).
- Dopple; Twindex Team. Twindex Post-Mortem—Following an Incident on 2 OCT 2021. 2021. Available online: https://dopple-ecosystem.medium.com/twindex-post-mortem-following-an-incident-on-2-oct-2021-76ded3a5538a (accessed on 12 April 2021).
- Pitimanaaree, N. Fair Uniswap’s LP Token Pricing. 2020. Available online: https://blog.alphaventuredao.io/fair-lp-token-pricing/ (accessed on 27 December 2021).
- Shao, T. A Guide on Uniswap v3 TWAP Oracle. 2021. Available online: https://medium.com/blockchain-development-notes/a-guide-on-uniswap-v3-twap-oracle-2aa74a4a97c5 (accessed on 12 April 2021).
- Chukleang, T.; Jandaeng, C. Security Enhancement in Smart Logistics with Blockchain Technology: A Home Delivery Use Case. Informatics 2022, 9, 70. [Google Scholar] [CrossRef]
- Daramola, O.; Thebus, D. Architecture-centric evaluation of blockchain-based smart contract e-voting for national elections. Informatics 2020, 7, 16. [Google Scholar] [CrossRef]
- Nanayakkara, S.; Perera, S.; Senaratne, S.; Weerasuriya, G.T.; Bandara, H.M.N.D. Blockchain and smart contracts: A solution for payment issues in construction supply chains. Informatics 2021, 8, 36. [Google Scholar] [CrossRef]
- Zhu, H.; Zhou, Z.Z. Analysis and outlook of applications of blockchain technology to equity crowdfunding in China. Financ. Innov. 2016, 2, 29. [Google Scholar] [CrossRef]
- Karode, T.; Werapun, W.; Arpornthip, T. Blockchain-based global travel review framework. Int. J. Adv. Comput. Sci. Appl. 2020, 11, 90–99. [Google Scholar] [CrossRef]
- Karode, T.; Werapun, W. Robustness against fraudulent activities of a blockchain-based online review system. Peer-to-Peer Netw. Appl. 2022, 15, 92–106. [Google Scholar] [CrossRef]
- Werapun, W.; Arpornthip, T.; Sangiamkul, E.; Wetprasit, R.; Karode, T. A Blockchain-based Renewable Energy Investment Management Platform: Decentralized Sustainable Development (DeSDev). J. Comput. Sci. 2020, 16, 1657–1668. [Google Scholar] [CrossRef]
- Guo, Y.; Liang, C. Blockchain application and outlook in the banking industry. Financ. Innov. 2016, 2, 24. [Google Scholar] [CrossRef]
- Cao, Y.; Zou, C.; Cheng, X. Flashot: A snapshot of flash loan attack on DeFi ecosystem. arXiv 2021, arXiv:2102.00626. [Google Scholar]
- Qin, K.; Zhou, L.; Livshits, B.; Gervais, A. Attacking the defi ecosystem with flash loans for fun and profit. In Proceedings of the International Conference on Financial Cryptography and Data Security, Virtual Event, 1–5 March 2021; Springer: Berlin/Heidelberg, Germany, 2021; pp. 3–32. [Google Scholar]
- Holub, A.; O’Connor, J. COINHOARDER: Tracking a ukrainian bitcoin phishing ring DNS style. In Proceedings of the 2018 APWG Symposium on Electronic Crime Research (eCrime), San Diego, CA, USA, 15–17 May 2018; pp. 1–5. [Google Scholar] [CrossRef]
- PancakeSwap. DNS Incident Recap. 2021. Available online: https://medium.com/pancakeswap/dns-incident-recap-36a183a2aee6 (accessed on 19 March 2021).
- Russo, C. Arbs Exploit DeFi to Make $900k in Seconds; Provoke Soul-Searching in the Process. 2020. Available online: https://newsletter.thedefiant.io/p/arbs-exploit-defi-to-make-900k-in (accessed on 12 July 2021).
- Songsom, N.; Werapun, W.; Suaboot, J.; Rattanavipanon, N. The SWC-Based Security Analysis Tool for Smart Contract Vulnerability Detection. In Proceedings of the 6th IEEE International Conference on Information Technology (InCIT) 2022, Nonthaburi, Thailand, 10–11 November 2022; pp. 1–6. [Google Scholar]
- Cecchetti, E.; Yao, S.; Ni, H.; Myers, A.C. Compositional security for reentrant applications. In Proceedings of the 2021 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 24–27 May 2021; pp. 1249–1267. [Google Scholar]
- Daian, P.; Goldfeder, S.; Kell, T.; Li, Y.; Zhao, X.; Bentov, I.; Breidenbach, L.; Juels, A. Flash boys 2.0: Frontrunning, transaction reordering, and consensus instability in decentralized exchanges. arXiv 2019, arXiv:1904.05234. [Google Scholar]
- Mazorra, B.; Adan, V.; Daza, V. Do Not Rug on Me: Zero-Dimensional Scam Detection. Cryptology ePrint Archive, Paper 2022/350. 2022. Available online: https://eprint.iacr.org/2022/350 (accessed on 20 December 2022).
- Hamrick, J.; Rouhi, F.; Mukherjee, A.; Feder, A.; Gandal, N.; Moore, T.; Vasek, M. The Economics of Cryptocurrency Pump and Dump Schemes. Available at SSRN 3310307. 2018. Available online: https://tylermoore.utulsa.edu/weis19pump.pdf (accessed on 1 May 2021).
- Kamps, J.; Kleinberg, B. To the moon: Defining and detecting cryptocurrency pump-and-dumps. Crime Sci. 2018, 7, 18. [Google Scholar] [CrossRef]
- Xu, J.; Livshits, B. The Anatomy of a Cryptocurrency Pump-and-Dump Scheme. In Proceedings of the 28th USENIX Security Symposium (USENIX Security 19), Santa Clara, CA, USA, 14–16 August 2019; pp. 1609–1625. [Google Scholar]
- Russo, C. bZx Hacked for $8M after Security-Focused Relaunch. 2020. Available online: https://thedefiant.io/bzx-hacked-for-8m-after-security-focused-relaunch/ (accessed on 10 January 2021).
- Gudgeon, L.; Perez, D.; Harz, D.; Livshits, B.; Gervais, A. The decentralized financial crisis. In Proceedings of the 2020 IEEE Crypto Valley Conference on Blockchain Technology (CVCBT), Rotkreuz, Switzerland, 11–12 June 2020; pp. 1–15. [Google Scholar]
- Stevens, R. After DeFi Lost $100 Million to Flash Loan Attacks, Curve Pushes Chainlink. 2020. Available online: https://decrypt.co/49758/after-100-million-lost-to-flash-loan-attacks-curve-pushes-chainlink (accessed on 12 July 2021).
- Xia, P.; Gao, B.; Su, W.; Yu, Z.; Luo, X.; Zhang, C.; Xiao, X.; Xu, G. Demystifying Scam Tokens on Uniswap Decentralized Exchange. arXiv 2021, arXiv:2109.00229. [Google Scholar]
- Gronde, F. Flash Loans and Decentralized Lending Protocols: An In-Depth Analysis. Master’s Thesis, Center for Innovative Finance, University of Basel, Basel, Switzerland, 2012. [Google Scholar]
- Gudgeon, L.; Werner, S.; Perez, D.; Knottenbelt, W.J. Defi protocols for loanable funds: Interest rates, liquidity and market efficiency. In Proceedings of the 2nd ACM Conference on Advances in Financial Technologies, Zurich, Switzerland, 21–23 October 2020; pp. 92–112. [Google Scholar]
- Xia, P.; Wang, H.; Gao, B.; Su, W.; Yu, Z.; Luo, X.; Zhang, C.; Xiao, X.; Xu, G. Trade or Trick? Detecting and Characterizing Scam Tokens on Uniswap Decentralized Exchange. Proc. ACM Meas. Anal. Comput. Syst. 2021, 5, 1–26. [Google Scholar] [CrossRef]
- Avara UI Labs Ltd. Aave—Open Source Liquidity Protocol. 2021. Available online: https://docs.aave.com/hub/ (accessed on 12 December 2021).
- Bai, S.; Robinson, F. Automated Triangular Arbitrage: A Trading Algorithm for Foreign Exchange on a Cryptocurrency Market. 2019. Available online: https://www.diva-portal.org/smash/get/diva2:1322682/FULLTEXT02 (accessed on 10 February 2020).
- Bell, P. Arbitrage Trading Strategy in Gold Futures. 2019. Available online: https://mpra.ub.uni-muenchen.de/id/eprint/96124 (accessed on 12 January 2020).
- Boonpeam, N.; Werapun, W.; Karode, T. The arbitrage system on decentralized exchanges. In Proceedings of the 2021 18th IEEE International Conference on Electrical Engineering/Electronics, Computer, Telecommunications and Information Technology (ECTI-CON), Chiang Mai, Thailand, 19–22 May 2021; pp. 768–771. [Google Scholar]
- Uniswap Labs. Uniswap Protocol. 2021. Available online: https://uniswap.org/ (accessed on 12 December 2021).
- Makerdao.com. The Maker Protocol: MakerDAO’s Multi-Collateral Dai (MCD) System. 2021. Available online: https://makerdao.com/whitepaper/White%20Paper%20-The%20Maker%20Protocol_%20MakerDAO%E2%80%99s%20Multi-Collateral%20Dai%20(MCD)%20System-FINAL-%20021720.pdf (accessed on 12 December 2021).
- Gandal, N.; Hamrick, J.; Moore, T.; Oberman, T. Price manipulation in the Bitcoin ecosystem. J. Monet. Econ. 2018, 95, 86–96. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A peer-to-peer electronic cash system. 2008. Available online: https://www.debr.io/article/21260-bitcoin-a-peer-to-peer-electronic-cash-system (accessed on 6 April 2021).
- Harvest Finance. Harvest Flashloan Economic Attack Post-Mortem. 2020. Available online: https://medium.com/harvest-finance/harvest-flashloan-economic-attack-post-mortem-3cf900d65217 (accessed on 12 April 2021).
- Sigalos, M. DeFi Bug Accidentally Gives $90 Million to Users, Founder Begs Them to Return It. 2021. Available online: https://www.cnbc.com/2021/10/01/defi-protocol-compound-mistakenly-gives-away-millions-to-users.html (accessed on 4 December 2021).
- Zafar, T. Visor Finance Suffers Another DeFi Hack as Losses Mount Up to $8.2M. 2021. Available online: https://finance.yahoo.com/news/visor-finance-suffers-another-defi-094645929.html (accessed on 2 February 2022).
- Uniswap Labs. Uniswap Oracle. 2021. Available online: https://docs.uniswap.org/concepts/protocol/oracle (accessed on 29 December 2021).
- Julien, B. Warp Finance—Rekt. 2020. Available online: https://rekt.news/warp-finance-rekt/ (accessed on 17 December 2021).
- Ethtx.info. Ethtx.info Analysis 0x8bb8dc5c7c830bac85fa48acad250. 2021. Available online: https://ethtx.info/mainnet/0x8bb8dc5c7c830bac85fa48acad2505e9300a91c3ff239c9517d0cae33b595090/ (accessed on 20 December 2021).
- Nomic Foundation. Hardhat|Ethereum Development. 2020. Available online: https://hardhat.org/ (accessed on 27 December 2021).
- Etherscan. Ethereum (ETH) Blockchain Explorer. 2020. Available online: https://etherscan.io/ (accessed on 27 December 2021).
- Li, Y.; Liu, H.; Yang, Z.; Wang, B.; Ren, Q.; Wang, L.; Chen, B. Protect Your Smart Contract Against Unfair Payment. In Proceedings of the 2020 International Symposium on Reliable Distributed Systems (SRDS), Shanghai, China, 21–24 September 2020; pp. 61–70. [Google Scholar] [CrossRef]
- Lai, W.J.; Hsueh, C.W.; Wu, J.L. A Fully Decentralized Time-Lock Encryption System on Blockchain. In Proceedings of the 2019 IEEE International Conference on Blockchain (Blockchain), Atlanta, GA, USA, 14–17 July 2019; pp. 302–307. [Google Scholar] [CrossRef]
- Breidenbach, L.; Cachin, C.; Coventry, A.; Juels, A.; Miller, A. Chainlink Off-Chain Reporting Protocol. 2021. Available online: https://research.chain.link/ocr.pdf (accessed on 24 December 2021).
- Thanh, B.N.; Hong, T.N.V.; Pham, H.; Cong, T.N.; Anh, T.P.T. Are the stabilities of stablecoins connected? J. Ind. Bus. Econ. 2022, 1–11. [Google Scholar] [CrossRef]
- Vujičić, D.; Jagodić, D.; Ranđić, S. Blockchain technology, bitcoin, and Ethereum: A brief overview. In Proceedings of the 2018 17th IEEE International Symposium Infoteh-Jahorina (Infoteh), East Sarajevo, Bosnia and Herzegovina, 21–23 March 2018; pp. 1–6. [Google Scholar]

| Variable | Value | Description |
|---|---|---|
| 58,010,988.36 | The amount of DAI in the DAI-WETH Uniswap pool | |
| 90,409.01 | The amount of WETH in the DAI-WETH Uniswap pool | |
| 1,887,324.80 | Total LP tokens in the DAI-WETH Uniswap pool | |
| 1.00 | The real-time price of DAI retrieved from the DAI-USDC Uniswap pool | |
| 644.46 | The real-time price of WETH retrieved from the WETH-USDC Uniswap pool | |
| 1.00 | The time-weighted-average price of DAI retrieved from the DAI-USDC Uniswap pool | |
| 585.00 | The time-weighted-average price of WETH retrieved from the WETH-USDC Uniswap pool | |
| 2,900,029.98 | The available amount of DAI in flash loan services | |
| 269,299.92 | The available amount of WETH in the Uniswap flashswap service | |
| 76,436.76 | The available amount of WETH in the flash loan service | |
| 345,736.68 | The available amount of WETH in flash loan services | |
| 70,837,678.78 | The amount of USDC in the USDC-WETH Sushiswap pool | |
| 110,167.37 | The amount of WETH in the USDC-WETH Sushiswap pool | |
| 3,862,646.61 | The amount of DAI in Warp Vault | |
| 3,917,983.81 | The amount of USDC in Warp Vault | |
| c | 810.90 | The Uniswap flashswap service fee () |
| Variable | Model | Remark | |
|---|---|---|---|
| Standard | Fair Reserves | ||
| 1462.81 | 0 | ||
| 342,252.88 | 341,993.69 | ||
| 5757.51 | 0 | ||
| 436,145.69 | 436,145.69 | ||
| 13,288,687.37 | 13,288,687.37 | ||
| 341,217.04 | 341,217.04 | ||
| 4519.64 | 4519.64 | ||
| 60,911,018.34 | 60,911,018.34 | ||
| 94,928.65 | 94,928.65 | ||
| 47,622,330.97 | 47,622,330.97 | ||
| 48,584,947.6 | 48,414,505.16 | ||
| 3,862,646.61 | 3,692,204.17 | ||
| 3,917,983.81 | 0 | ||
| 8,520,374.39 | 3,692,204.17 | ||
| 135.46 | 58.70 | ||
| D | 94,349.34 | 94,349.34 | |
| 1,981,674.14 | 1,981,674.14 | ||
| k | n/a | 5,782,200,741,141.44 | |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Werapun, W.; Karode, T.; Arpornthip, T.; Suaboot, J.; Sangiamkul, E.; Boonrat, P. The Flash Loan Attack Analysis (FAA) Framework—A Case Study of the Warp Finance Exploitation. Informatics 2023, 10, 3. https://doi.org/10.3390/informatics10010003
Werapun W, Karode T, Arpornthip T, Suaboot J, Sangiamkul E, Boonrat P. The Flash Loan Attack Analysis (FAA) Framework—A Case Study of the Warp Finance Exploitation. Informatics. 2023; 10(1):3. https://doi.org/10.3390/informatics10010003
Chicago/Turabian StyleWerapun, Warodom, Tanakorn Karode, Tanwa Arpornthip, Jakapan Suaboot, Esther Sangiamkul, and Pawita Boonrat. 2023. "The Flash Loan Attack Analysis (FAA) Framework—A Case Study of the Warp Finance Exploitation" Informatics 10, no. 1: 3. https://doi.org/10.3390/informatics10010003
APA StyleWerapun, W., Karode, T., Arpornthip, T., Suaboot, J., Sangiamkul, E., & Boonrat, P. (2023). The Flash Loan Attack Analysis (FAA) Framework—A Case Study of the Warp Finance Exploitation. Informatics, 10(1), 3. https://doi.org/10.3390/informatics10010003








