Threat Assessment and Risk Analysis (TARA) for Interoperable Medical Devices in the Operating Room Inspired by the Automotive Industry
Abstract
1. Introduction
2. Background and State of the Art
2.1. Medical Communication Systems in the Operating Room
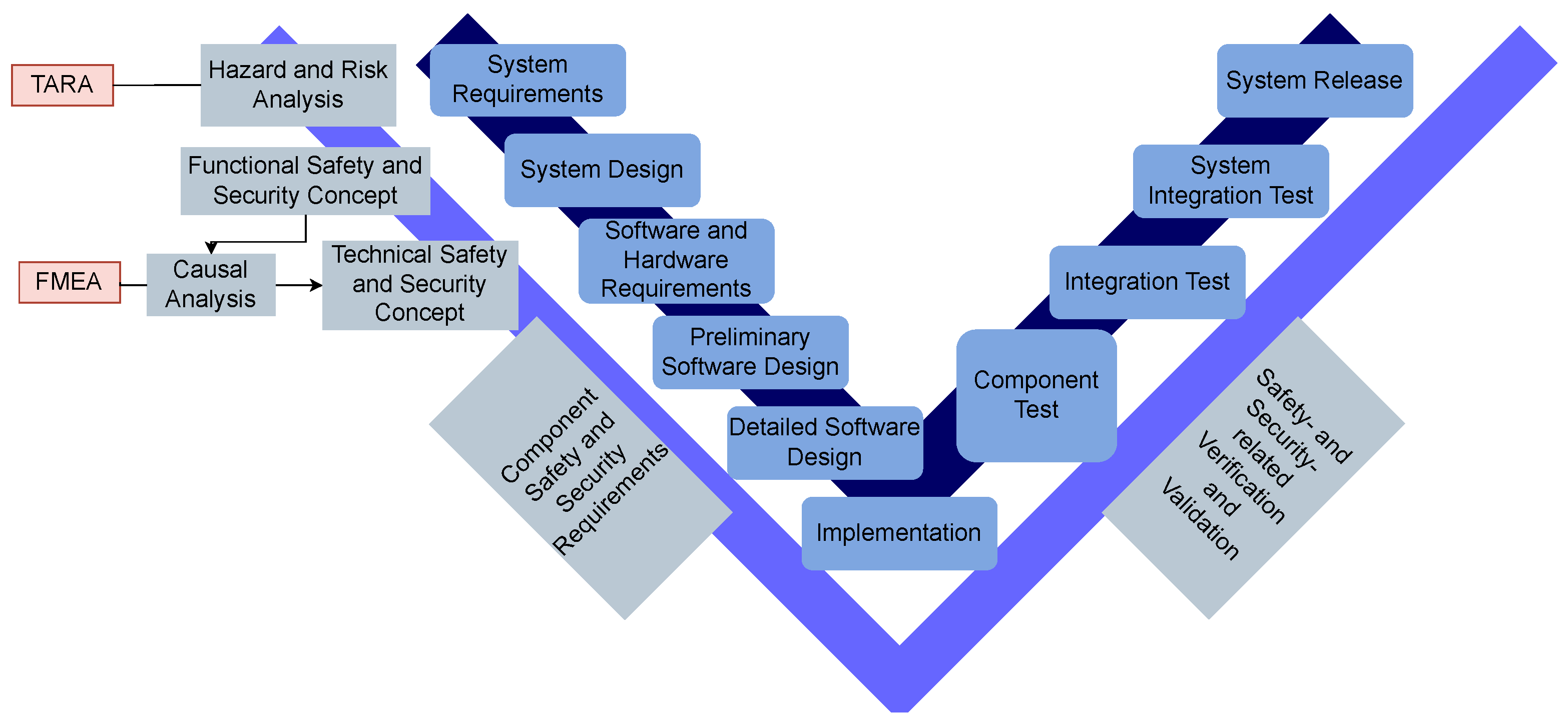
2.2. Safety and Security in Life Cycle Processes
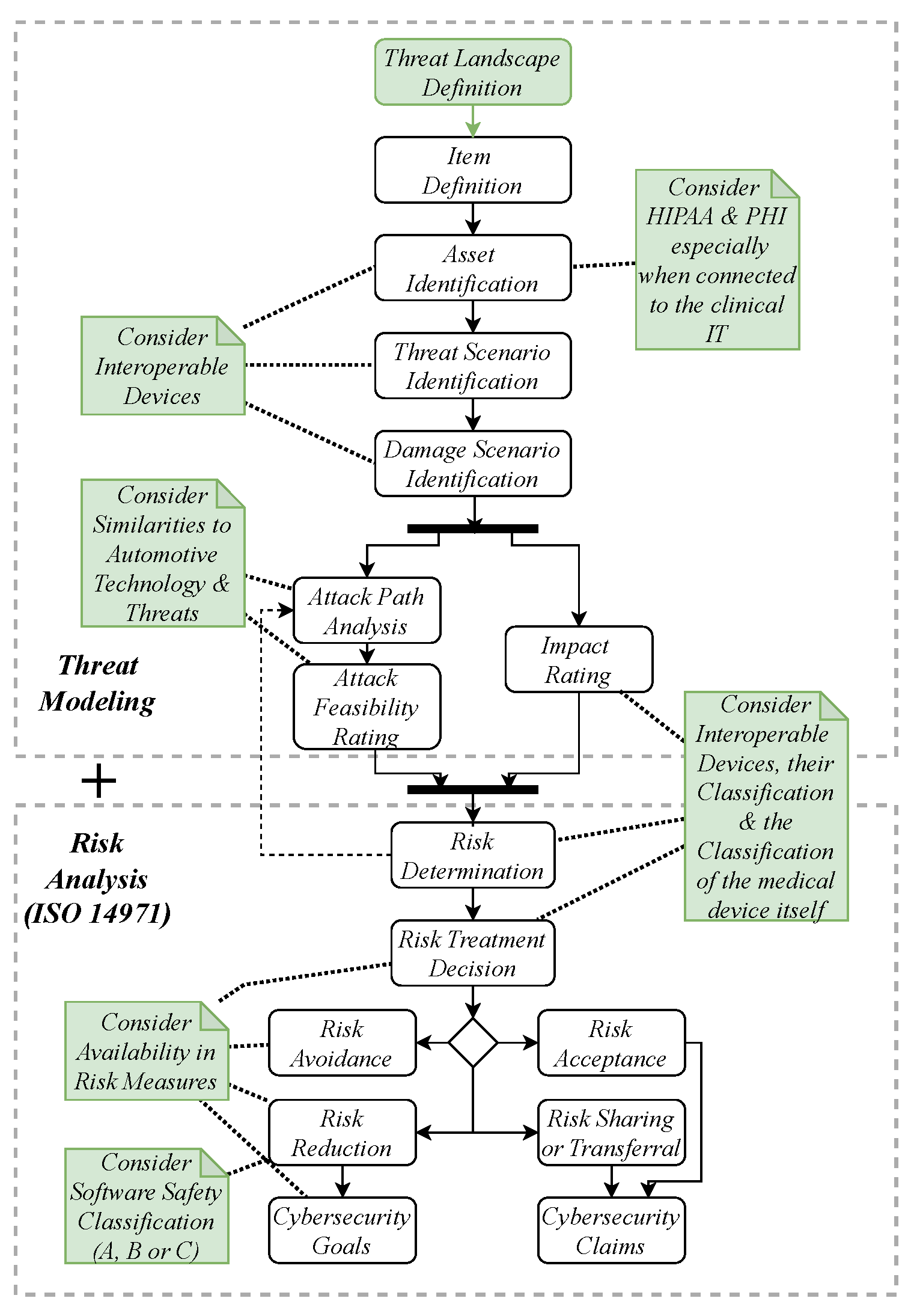
2.3. Threat Modeling
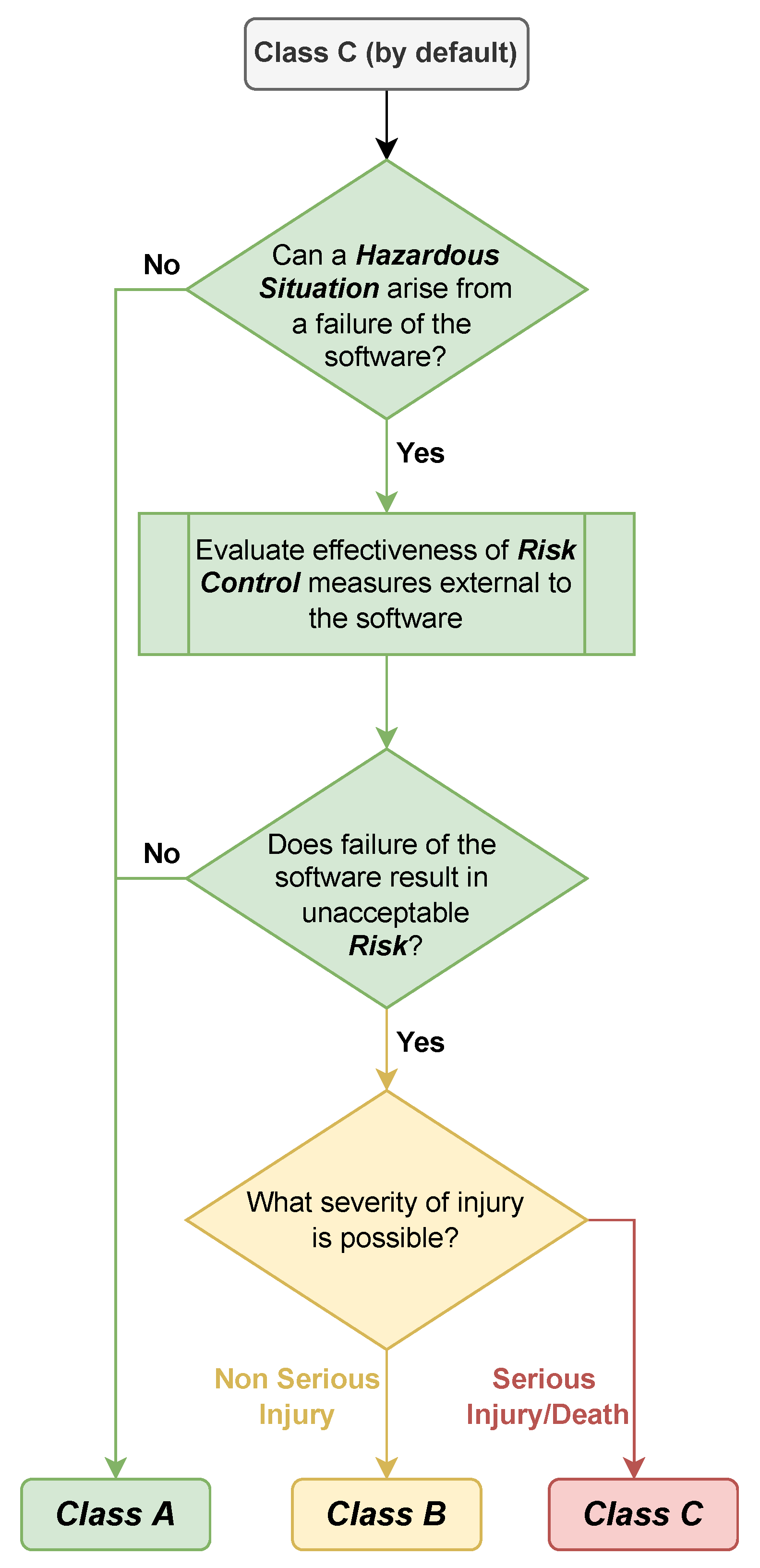
2.4. Safety and Risk Classification for Medical Devices
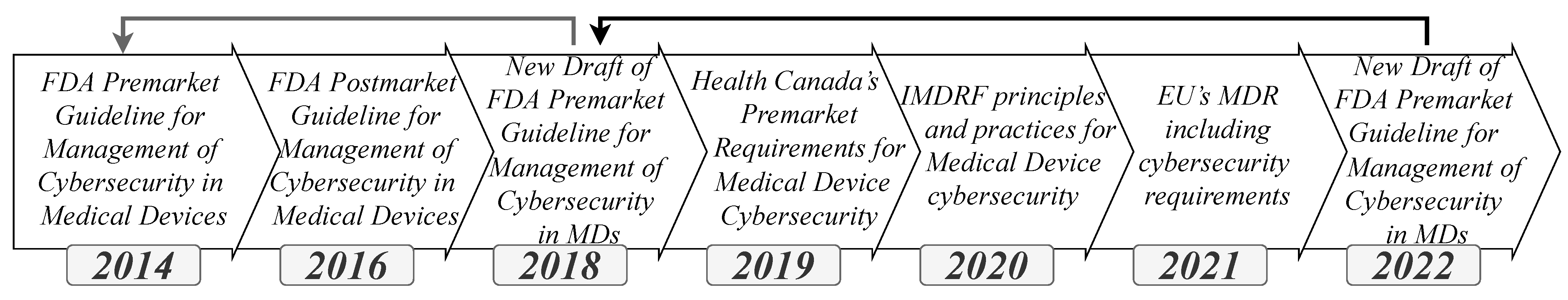
2.5. Medical Device Standards and Regulations
2.6. Automotive Systems Evaluation and Safety Integrity Level
2.7. Automotive Standards and Regulations
3. Related Work
3.1. Medical
3.2. Automotive
4. Threat and Risk Assessment (TARA) Adoption
4.1. Differences and Similarities in the Automotive and Medical Fields
4.2. Heavens 2.0 in Medical Context
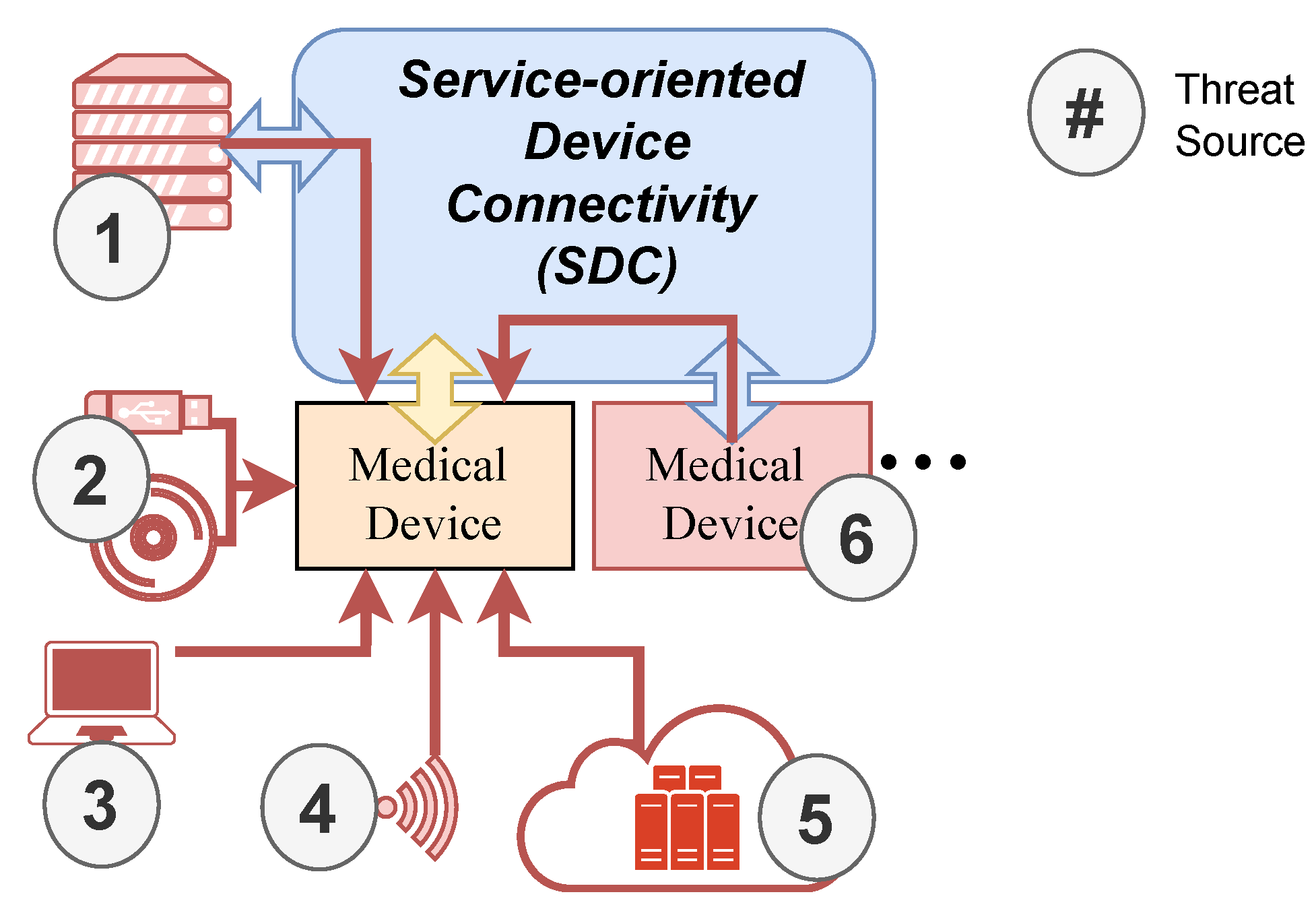
4.3. Threat Landscape in Operating Rooms
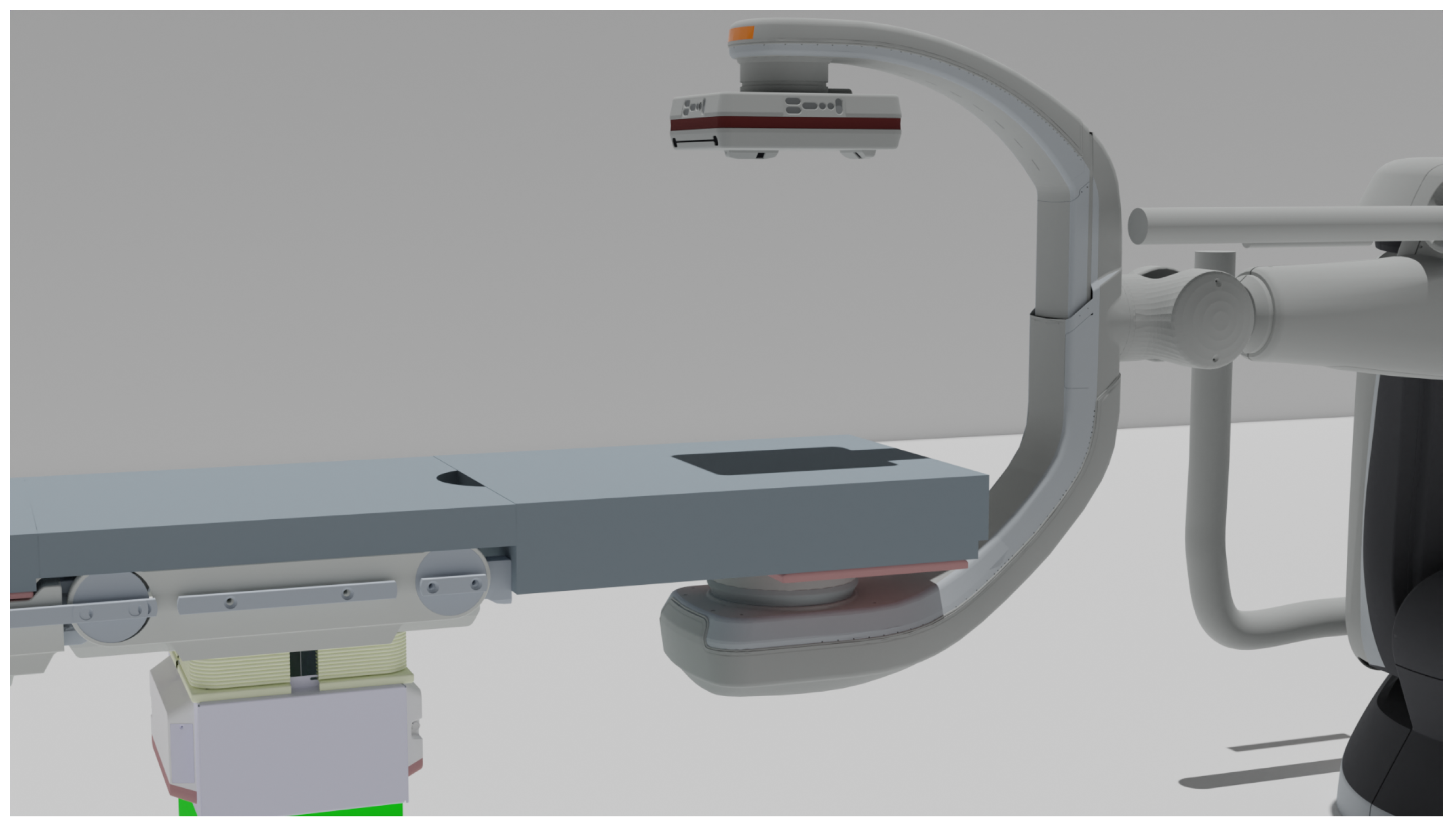
5. Heavens 2.0 Use Case
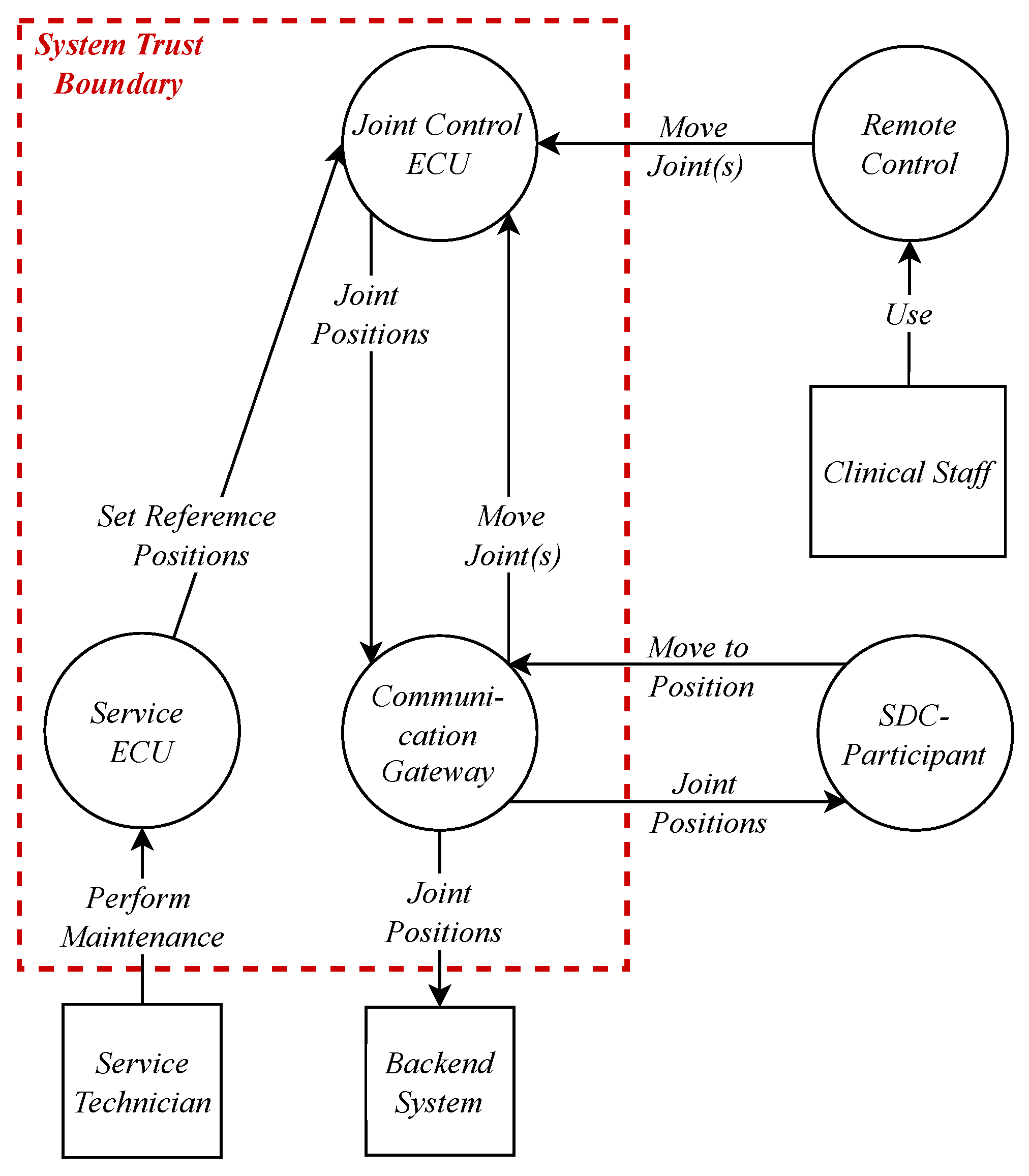
5.1. Data Flow Diagram for Item Definition and Asset Identification
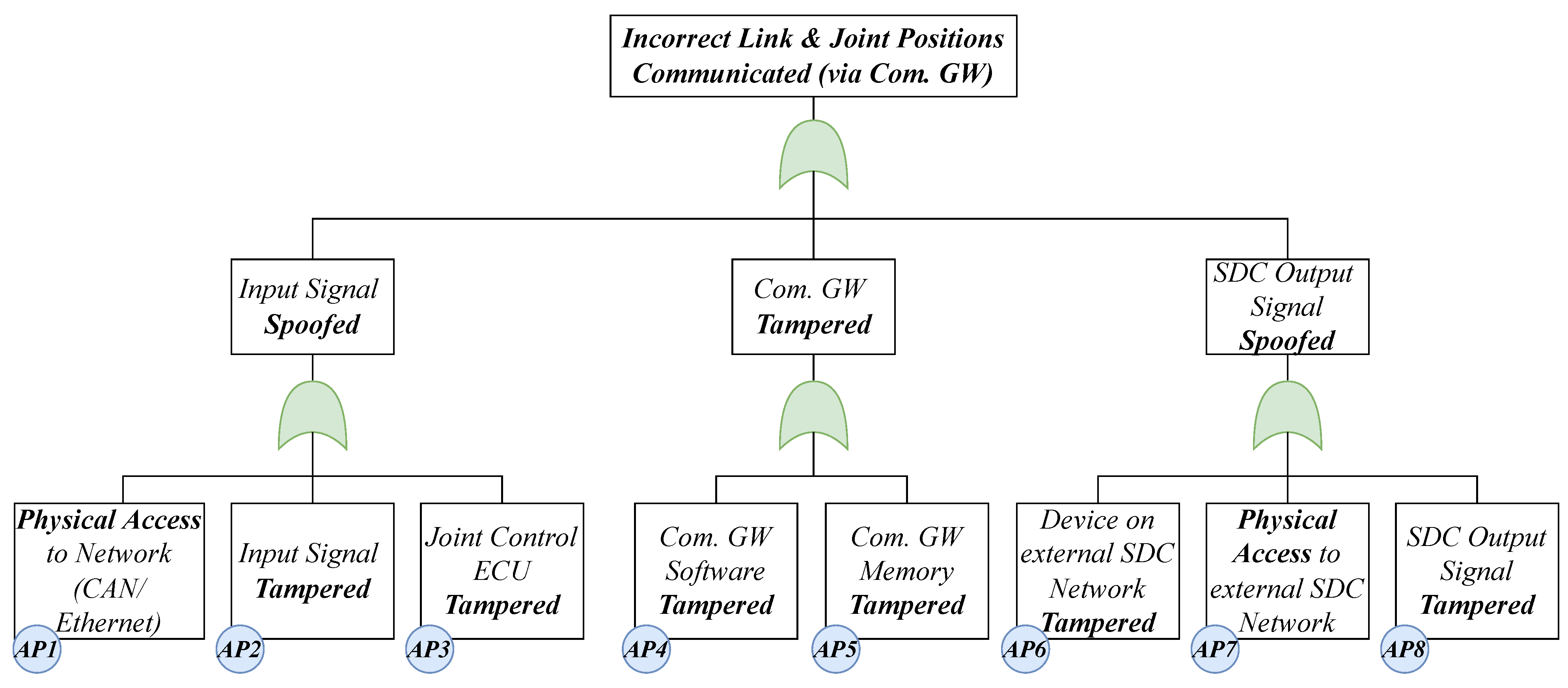
5.2. Threat and Damage Scenario Identification
5.3. Risk Assessment
5.4. Treatment Decision
5.5. Cybersecurity Goals
- R1
- Security properties (authenticity, integrity, confidentiality) must be ensured for network communication.
- R2
- Patient harm resulting from the misuse of connectivity interfaces needs to always be avoided by the system.
- R3
- The system must detect if the communicated joint positions are plausible.
- R4
- The system must be able to detect unknown attacks.
5.6. Relation to SFMEA
6. Results and Future Work
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| V2X Vehicle-to-Everything Communication |
| SOME/IP Scalable service-Oriented MiddlewarE over IP |
| OBD On-Board Diagnostics |
| ECU Electronic Control Unit |
| IT Information Technology |
| OEM Original Equipment Manufacturer |
| NIST National Institute of Standards and Technology |
| ASIL Automotive Safety Integrity Level |
| IDS Intrusion Detection System |
| IoT Internet of Things |
| SOA Service-Oriented Architecture |
| CPS Cyber-Physical System |
| IAM Identity and Access Management |
| ADAS Advanced Driver Assistance Systems |
| QM Quality Management |
| OTA Over The Air |
| OR Operating Room |
| HOR Hybrid Operating Room |
| SDC Service-oriented Device Connectivity |
| CPS Cyber Physical System |
| OR table Operating Room table |
| E/E architecture Electric/Electronic architecture |
| HEAVENS HEAling Vulnerabilities to ENhance Software Security and Safety |
| SOTA Software Over The Air |
| HIPAA Health Insurance Portability and Accountability Act |
| TARA Threat Analysis and Risk Assessment |
| FDA U.S. Food and Drug Administration |
| E/E Electric/Electronic |
| FMEA Failure Mode and Effects Analysis |
| SCOT® Smart Cyber Operating Theater® |
| ICE Integrated Clinical Environment |
| MDPnP Medical Device Plug and Play |
| CSMS Cybersecurity Management Systems |
| AFR Attack Feasibility Rating |
| IMDRF International Medical Device Regulators Forum |
| DFD Data Flow Diagram |
| SUMS Software Update Management System |
| MDR Medical Device Regulation |
| PASTA Process for Attack Simulation and Threat Analysis |
| CAPA Corrective and Preventive Action |
| ICU Intensive Care Unit |
| HIS Health Information System |
| POC Point of Care |
| PHD Personal Health Device |
| NIST National Institute of Standards and Technology |
| BfArM Federal Institute for Drugs and Medical Devices |
| RTOS Real-Time Operating System |
| SFMEA Software Failure Mode and Effects Analysis |
| CRC Cyclic Redundancy Check |
| OCTAVE Operationally Critical Threat, Asset, and Vulnerability Evaluation |
| SAHARA Security Aware Hazard Analysis and Risk Assessment |
| PHI Protected Health Information |
| PnP Plug and Play |
References
- Anisetti, M.; Ardagna, C.; Cremonini, M.; Damiani, E.; Sessa, J.; Costa, L. Security Threat Landscape. Available online: https://sesar.di.unimi.it/security-threat-landscape/ (accessed on 1 October 2022).
- US Department of Health and Human Services. The HIPAA Privacy Rule; US Department of Health and Human Services: Washington, DC, USA, 2008.
- Jones, R.W.; Katzis, K. Cybersecurity and the Medical Device Product Development Lifecycle. Inform. Empower. Healthc. Transform. 2017, 238, 76–79. [Google Scholar]
- Ahmed, M.A.; Sindi, H.F.; Nour, M. Cybersecurity in Hospitals: An Evaluation Model. J. Cybersecur. Priv. 2022, 2, 853–861. [Google Scholar] [CrossRef]
- Jalali, M.S.; Kaiser, J.P. Cybersecurity in Hospitals: A Systematic, Organizational Perspective. J. Med. Internet Res. 2018, 20, e10059. [Google Scholar] [CrossRef]
- Argaw, S.T.; Bempong, N.E.; Eshaya-Chauvin, B.; Flahault, A. The state of research on cyberattacks against hospitals and available best practice recommendations: A scoping review. BMC Med. Inform. Decis. Mak. 2019, 19, 1–11. [Google Scholar] [CrossRef] [PubMed]
- He, Y.; Aliyu, A.; Evans, M.; Luo, C. Health Care Cybersecurity Challenges and Solutions Under the Climate of COVID-19: Scoping Review. J. Med. Internet Res. 2021, 23, e21747. [Google Scholar] [CrossRef] [PubMed]
- ENISA. ENISA Threat Landscape 2021. Available online: https://www.enisa.europa.eu/publications/enisa-threat-landscape-2021 (accessed on 12 November 2022).
- Ralston, W. The Untold Story of a Cyberattack, a Hospital and a Dying Woman; WIRED UK: London, UK, 2020. [Google Scholar]
- FDA. [DRAFT] Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions Draft Guidance for Industry and Food and Drug Administration Staff. FDA, USA. Available online: https://www.fda.gov/regulatory-information/search-fda-guidance-documents/cybersecurity-medical-devices-quality-system-considerations-and-content-premarket-submissions (accessed on 10 November 2022).
- Koscher, K.; Czeskis, A.; Roesner, F.; Patel, S.; Kohno, T.; Checkoway, S.; McCoy, D.; Kantor, B.; Anderson, D.; Shacham, H.; et al. Experimental security analysis of a modern automobile. In Proceedings of the 2010 IEEE Symposium on Security and Privacy, Oakland, CA, USA, 16–19 May 2010; pp. 447–462. [Google Scholar]
- Finkle, J.; Woodall, B. UPDATE 1-Researcher Says Can Hack GM’s OnStar App, Open Vehicle, Start Engine. 2015. Available online: https://www.reuters.com/article/gm-hacking-idUSL1N10A3XK20150730 (accessed on 15 November 2022).
- Lautenbach, A.; Almgren, M.; Olovsson, T. Proposing HEAVENS 2.0—An automotive risk assessment model. In Proceedings of the Computer Science in Cars Symposium, Ingolstadt, Germany, 8 December 2022; Brücher, B., Krauß, C., Fritz, M., Hof, H.J., Wasenmüller, O., Eds.; ACM: New York, NY, USA, 2021; pp. 1–12. [Google Scholar] [CrossRef]
- Fuhr, T.; Makarova, E.; Silverman, S.; Telpis, V. Capturing the Value of Good Quality in Medical Devices. 2017. Available online: https://www.mckinsey.com/industries/life-sciences/our-insights/capturing-the-value-of-good-quality-in-medical-devices (accessed on 3 November 2022).
- Ferguson, N.; Schneier, B.; Kohno, T. Cryptography Engineering: Design Principles and Practical Applications/Niels Ferguson, Bruce Schneier, Tadayoshi Kohno; Wiley: Indianapolis, India, 2010. [Google Scholar]
- IEC 81001-5-1:2021; Health Software and Health IT Systems Safety, Effectiveness and Security: Part 5-1: Security—Activities in the Product Life Cycle. IEC: International Electrotechnical Commission: Geneva, Switzerland, 2021.
- Mayer, B. Security bei der US-Regierung: VPN, SMS-Codes und Passwörter sind out, Zero Trust ist in—Golem.de. Golem.de. 2022. Available online: https://www.golem.de/news/security-bei-der-us-regierung-vpn-sms-codes-und-passwoerter-sind-out-zero-trust-ist-in-2202-162871.html (accessed on 15 December 2022).
- Dell EMC. Medical Device Security: ADDRESSING THE EVOLVING THREAT LANDSCAPE OF MEDICAL DEVICE CYBERATTACKS. Available online: https://www.dell.com/en-us/learn/assets/business~solutions~whitepapers~en/documents~dell_emc_hc_meddevicesecurity_wp_final.pdf (accessed on 20 December 2022).
- Puder, A.; Henle, J.; Rumez, M.; Vetter, A. A Mixed E/E-Architecture for Interconnected Operating Tables Inspired by the Automotive Industry (Will be published Mid 2022). In Proceedings of the International Symposium on Medical Robotics, Atlanta, GA, USA, 13–15 April 2022. [Google Scholar]
- Lee, I.; Sokolsky, O.; Chen, S.; Hatcliff, J.; Jee, E.; Kim, B.; King, A.; Mullen-Fortino, M.; Park, S.; Roederer, A.; et al. Challenges and Research Directions in Medical Cyber–Physical Systems. Proc. IEEE 2012, 100, 75–90. [Google Scholar]
- Teber, D.; Engels, C.; Maier-Hein, L.; Ayala, L.; Onogur, S.; Seitel, A.; März, K. Wie weit ist Chirugie 4.0? Der Urologe. Ausg. A 2020, 59, 1035–1043. [Google Scholar] [CrossRef]
- Kasparick, M. Zuverlässige und herstellerübergreifende Medizingeräteinteroperabilität & Beiträge zur IEEE 11073 SDC-Normenfamilie. Ph.D. Thesis, Universität Rostock, Rostock, Germany, 2020. [Google Scholar] [CrossRef]
- ASTM. Medical Devices and Medical Systems: Essential Safety Requirements for Equipment Comprising the Patient-Centric Integrated Clinical Environment (ICE)—Part 1: General Requirements and Conceptual Model. 2013. Available online: https://rosdok.uni-rostock.de/resolve/id/rosdok_disshab_0000002524 (accessed on 23 October 2022).
- Pfeiffer, J.H.; Dingler, M.E.; Dietz, C.; Lueth, T.C. Requirements and architecture design for open real-time communication in the operating room. In Proceedings of the 2015 IEEE International Conference on Robotics and Biomimetics (ROBIO), Zhuhai, China, 6–9 December 2015; pp. 458–463. [Google Scholar] [CrossRef]
- Dröschel, W.; Wiemers, M. (Eds.) Das V-Modell 97: Der Standard für die Entwicklung von IT-Systemen mit Anleitung für den Praxiseinsatz; Oldenbourg Wissenschaftsverlag: Berlin, Germany; Boston, MA, USA, 2015. [Google Scholar] [CrossRef]
- National Institute of Standards and Technology. Framework for Improving Critical Infrastructure Cybersecurity, Version 1.1. 2018. Available online: https://nvlpubs.nist.gov/nistpubs/cswp/nist.cswp.04162018.pdf (accessed on 20 December 2022).
- FDA. Postmarket Management of Cybersecurity in Medical Devices: Guidance for Industry and Food and Drug Administration Staff. Available online: https://www.fda.gov/regulatory-information/search-fda-guidance-documents/postmarket-management-cybersecurity-medical-devices (accessed on 20 October 2022).
- Lechner, N.H. An Overview of Cybersecurity Regulations and Standards for Medical Device Software. In Proceedings of the Central European Conference on Information and Intelligent Systems, 28th CECIIS, Varazdin, Croatia, 27–29 September 2017. [Google Scholar]
- Drägerwerk AG & Co. KGaA. Dräger Cybersecurity: Sicherheit für Medizingeräte—Eine Gemeinsame Verantwortung. 2022. Available online: https://www.draeger.com/Library/Content/cybersecurity-wp-9111147-de-2111-1.pdf (accessed on 4 April 2022).
- Karahasanovic, A.; Kleberger, P.; Almgren, M. Adapting threat modeling methods for the automotive industry. In Proceedings of the 15th ESCAR Conference, Berlin, Germany, 7–8 November 2017; pp. 1–10. [Google Scholar]
- Morana, M.M.; Uceda Vélez, T. Risk Centric Threat Modeling: Process for Attack Simulation and Threat Analysis/Tony Ucedavélez and Marco M. Morana; John Wiley & Sons: Hoboken, NJ, USA, 2015. [Google Scholar]
- Alberts, C.J.; Dorofee, A.J.; Stevens, J.F.; Woody, C. Introduction to the OCTAVE Approach; Carnegie Mellon University Software Engineering Institute: Pittsburgh, PA, USA, 2003. [Google Scholar]
- Stanganelli, J. Selecting a Threat Risk Model for Your Organization, Part Two. eSecurityPlanet. 2016. Available online: https://www.esecurityplanet.com/networks/selecting-a-threat-risk-model-for-your-organization-part-two/ (accessed on 23 October 2022).
- Shevchenko, N.; Chick, T.A.; O’Riordan, P.; Scanlon, T.P.; Woody, C. Threat Modeling: A Summary of Available Methods; Carnegie Mellon University Software Engineering Institute: Pittsburgh, PA, USA, 2018. [Google Scholar]
- Hao, J.; Han, G. On the modeling of automotive security: A survey of methods and perspectives. Future Internet 2020, 12, 198. [Google Scholar] [CrossRef]
- Macher, G.; Sporer, H.; Berlach, R.; Armengaud, E.; Kreiner, C. SAHARA: A security-aware hazard and risk analysis method. In Proceedings of the 2015 Design, Automation & Test in Europe Conference & Exhibition (DATE), Grenoble, France, 9–13 March 2015; pp. 621–624. [Google Scholar]
- Frauenhofer SIT. EVITA: E-Safety vehicle INTRUSION Protected Applications. In Proceedings of the 7th Escar Embedded Security in Cars Conference, Dusseldo, Germany, 24–25 November 2009. [Google Scholar]
- IEC62304:2016; Medical Device Software: Software Life Cycle Processes. IEC: International Electrotechnical Commission: Geneva, Switzerland, 2021.
- IEC60601-1:2020; Medical Electrical Equipment: Part 1: General Requirements for Basic Safety and Essential Performance. IEC: International Electrotechnical Commission: Geneva, Switzerland, 2020.
- DAS EUROPÄISCHE PARLAMENT UND DER RAT DER EUROPÄISCHEN UNION. VERORDNUNG (EU) 2017/745 DES EUROPÄISCHEN PARLAMENTS UND DES RATES—vom 5. April 2017—über Medizinprodukte, zur Änderung der Richtlinie 2001/83/EG, der Verordnung (EG) Nr. 178/2002 und der Verordnung (EG) Nr. 1223/2009 und zur Aufhebung der Richtlinien 90/385/EWG und 93/42/EWG des Rates: MDR, 05.04.2017. Available online: https://www.medical-device-regulation.eu/download-mdr/ (accessed on 5 October 2022).
- Bundesinstitut für Arzneimittel und Medizinprodukte. Abgrenzung/Klassifizierung. 2022. Available online: https://www.bfarm.de/DE/Medizinprodukte/Aufgaben/Risikobewertung-und-Forschung/Cybersicherheit/_node.html (accessed on 24 April 2022).
- ISO 14971:2019; Medical Devices: Application of Risk Management to Medical Devices. ISO: International Organization for Standardization: Geneva, Switzerland, 2019.
- ISO 13485:2016; Medical Devices—Quality Management Systems: Requirements for Regulatory Purposes. ISO: International Organization for Standardization: Geneva, Switzerland, 2016.
- ISO. Medical Devices: Guidance on the Application of ISO 14971; ISO: International Organization for Standardization: Geneva, Switzerland, 2020. [Google Scholar]
- Bijan, E. Safety Risk Management for Medical Devices; Academic Press: Cambridge, MA, USA, 2018. [Google Scholar]
- Lindner, B. The FMEA in Medical Technology Industry. 2021. Available online: https://www.risknet.de/en/topics/news-details/the-fmea-in-medical-technology-industry/ (accessed on 19 November 2022).
- ISO 81001-1:2021; Health Software and Health IT Systems Safety, Effectiveness and Security: Part 1: Principles and Concepts. ISO: International Organization for Standardization: Geneva, Switzerland, 2021.
- MITRE. Playbook for Threat Modeling Medical Devices|MITRE. 2021. Available online: https://www.mitre.org/news-insights/publication/playbook-threat-modeling-medical-devices (accessed on 19 October 2022).
- International Medical Device Regulators Forum. Principles and Practices for Medical Device Cybersecurity. 2020. Available online: https://www.imdrf.org/sites/default/files/docs/imdrf/final/technical/imdrf-tech-200318-pp-mdc-n60.pdf (accessed on 19 October 2022).
- Health Canada. Guidance Document: Pre-Market Requirements for Medical Device Cybersecurity. 2019. Available online: https://www.canada.ca/en/health-canada/services/drugs-health-products/medical-devices/application-information/guidance-documents/cybersecurity.html (accessed on 21 October 2022).
- Sadhu, P.K.; Yanambaka, V.P.; Abdelgawad, A.; Yelamarthi, K. Prospect of Internet of Medical Things: A Review on Security Requirements and Solutions. Sensors 2022, 22, 5517. [Google Scholar] [CrossRef]
- Madinejad, M. Medical Device Cybersecurity in the Age of IoMT. 2020. Available online: https://www.medtechintelligence.com/column/medical-device-cybersecurity-in-the-age-of-iomt/ (accessed on 1 November 2022).
- ISO. Road Vehicles—Functional Safety; ISO: International Organization for Standardization: Geneva, Switzerland, 2018. [Google Scholar]
- Jang, H.A.; Kwon, H.M.; Hong, S.; Lee, M.K. A study on situation analysis for asil determination. J. Ind. Intell. Inf. 2015, 3, 152–157. [Google Scholar] [CrossRef]
- da Silva Azevedo, L.; Parker, D.; Walker, M.; Papadopoulos, Y.; Araújo, R.E. Assisted assignment of automotive safety requirements. IEEE Softw. 2013, 31, 62–68. [Google Scholar] [CrossRef]
- Baynal, K.; Sarı, T.; Akpınar, B. Risk management in automotive manufacturing process based on FMEA and grey relational analysis: A case study. Adv. Prod. Eng. Manag. 2018, 13, 69–80. [Google Scholar] [CrossRef]
- Pfeufer, H.J. FMEA—Fehler-Möglichkeits- und Einfluss-Analyse nach AIAG und VDA, 2nd ed.; Carl Hanser Verlag GmbH & Co. KG: München, Germany, 2021. [Google Scholar] [CrossRef]
- Guissouma, H.; Diewald, A.; Sax, E. A generic system for automotive software over the air (sota) updates allowing efficient variant and release management. In Information Systems Architecture and Technology: Proceedings of 39th International Conference on Information Systems Architecture and Technology—ISAT 2018; Springer: Cham, Switzerland, 2018; pp. 78–89. [Google Scholar]
- Grundhoff, S. Tesla setze den Standard: So funktionieren "Over the Air"-Updates im Auto. focus.de. 2021. Available online: https://www.focus.de/auto/news/werkstattbesuche-kaum-noch-noetig-tesla-setze-den-standard-so-funktionieren-over-the-air-updates-im-auto_id_13033679.html (accessed on 14 October 2022).
- Placho, T.; Schmittner, C.; Bonitz, A.; Wana, O. Management of automotive software updates. Microprocess. Microsyst. 2020, 78, 103257. [Google Scholar] [CrossRef]
- Uniform Provisions Concerning the Approval of Vehicles with Regards to Software Update and Software Updates Management System. 2017. Available online: https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A42021X0388 (accessed on 12 October 2022).
- Rumez, M.; Grimm, D.; Kriesten, R.; Sax, E. An overview of automotive service-oriented architectures and implications for security countermeasures. IEEE Access 2020, 8, 221852–221870. [Google Scholar] [CrossRef]
- ISO 24089; Road Vehicles—Software Update Engineering. ISO: International Organization for Standardization: Geneva, Switzerland, 2022.
- SAE International–Vehicle Cybersecurity Systems Engineering Committee. SAEJ3061-Cybersecurity Guidebook for Cyber-Physical Vehicle Systems; Society of Automotive Engineers, SAE International: Warrendale, PA, USA, 2016. [Google Scholar]
- Macher, G.; Schmittner, C.; Veledar, O.; Brenner, E. ISO/SAE DIS 21434 automotive cybersecurity standard-in a nutshell. In Proceedings of the International Conference on Computer Safety, Reliability, and Security, Lisbon, Portugal, 15 September 2020; pp. 123–135. [Google Scholar]
- Luckett, P.; McDonald, J.; Glisson, W. Attack-Graph Threat Modeling Assessment of Ambulatory Medical Devices. In Proceedings of the 50th Hawaii International Conference on System Sciences, Waikoloa Village, HI, USA, 4–7 January 2017. [Google Scholar] [CrossRef]
- Puder, A.; Rumez, M.; Grimm, D.; Sax, E. Generic Patterns for Intrusion Detection Systems in Service-Oriented Automotive and Medical Architectures. J. Cybersecur. Priv. 2022, 2, 731–749. [Google Scholar] [CrossRef]
- Vakhter, V.; Soysal, B.; Schaumont, P.; Guler, U. Threat Modeling and Risk Analysis for Miniaturized Wireless Biomedical Devices. IEEE Internet Things J. 2022, 9, 13338–13352. [Google Scholar] [CrossRef]
- Sion, L.; Yskout, K.; van Landuyt, D.; van den Berghe, A.; Joosen, W. Security Threat Modeling. In Proceedings of the IEEE/ACM 42nd International Conference on Software Engineering Workshops, Seoul, Republic of Korea, 27 June–19 July 2020; ACM: New York, NY, USA, 2020; pp. 254–257. [Google Scholar]
- Jofre, M.; Navarro-Llobet, D.; Agulló, R.; Puig, J.; Gonzalez-Granadillo, G.; Mora Zamorano, J.; Romeu, R. Cybersecurity and Privacy Risk Assessment of Point-of-Care Systems in Healthcare—A Use Case Approach. Appl. Sci. 2021, 11, 6699. [Google Scholar] [CrossRef]
- Fernandes, A.; Figueiredo, M.; Carvalho, F.; Neves, J.; Vicente, H. Threat Artificial Intelligence and Cyber Security in Health Care Institutions. In Artificial Intelligence for Cyber Security: Methods, Issues and Possible Horizons or Opportunities; Misra, S., Kumar Tyagi, A., Eds.; Springer International Publishing: Cham, Switzerland, 2021; Volume 972, pp. 319–342. [Google Scholar] [CrossRef]
- Radanliev, P.; de Roure, D. Advancing the cybersecurity of the healthcare system with self-optimising and self-adaptative artificial intelligence (part 2). Health Technol. 2022, 12, 923–929. [Google Scholar] [CrossRef] [PubMed]
- Silvestri, S.; Islam, S.; Papastergiou, S.; Tzagkarakis, C.; Ciampi, M. A Machine Learning Approach for the NLP-Based Analysis of Cyber Threats and Vulnerabilities of the Healthcare Ecosystem. Sensors 2023, 23, 651. [Google Scholar] [CrossRef]
- Ring, M.; Frkat, D.; Schmiedecker, M. Cybersecurity evaluation of automotive e/e architectures. In Proceedings of the ACM Computer Science In Cars Symposium (CSCS 2018), Munich, Germany, 13–14 September 2018. [Google Scholar]
- Macher, G.; Armengaud, E.; Brenner, E.; Kreiner, C. A review of threat analysis and risk assessment methods in the automotive context. In Proceedings of the International Conference on Computer Safety, Reliability, and Security, Trondheim, Norway, 21–23 September 2016; Springer: Cham, Switzerland, 2016; pp. 130–141. [Google Scholar]
- Henniger, O.; Apvrille, L.; Fuchs, A.; Roudier, Y.; Ruddle, A.; Weyl, B. Security requirements for automotive on-board networks. In Proceedings of the 2009 9th International Conference on Intelligent Transport Systems Telecommunications, (ITST), Lille, France, 20–22 October 2009; pp. 641–646. [Google Scholar]
- Guzman, Z. Hackers Remotely Kill Jeep’s Engine on Highway. cnbc.com. 2015. Available online: https://www.cnbc.com/2015/07/21/hackers-remotely-kill-jeep-engine-on-highway.html (accessed on 15 December 2022).
- Mahmud, S.M.; Shanker, S.; Hossain, I. Secure software upload in an intelligent vehicle via wireless communication links. In Proceedings of the IEEE Proceedings, Intelligent Vehicles Symposium, Las Vegas, NV, USA, 6–8 June 2005; pp. 588–593. [Google Scholar]
- Halder, S.; Ghosal, A.; Conti, M. Secure over-the-air software updates in connected vehicles: A survey. Comput. Netw. 2020, 178, 107343. [Google Scholar] [CrossRef]
- Howden, J.; Maglaras, L.; Ferrag, M.A. The security aspects of automotive over-the-air updates. Int. J. Cyber Warf. Terror. IJCWT 2020, 10, 64–81. [Google Scholar] [CrossRef]
- Islam, M.; Sandberg, C.; Bokesand, A.; Olovsson, T.; Broberg, H.; Kleberger, P.; Lautenbach, A.; Hansson, A.; Söderberg-Rivkin, A.; Kadhirvelan, S.P. Deliverable d2-security models. HEAVENS Proj. Deliv. D 2014, 2. [Google Scholar]
- Kreissl, J. Absicherung der SOME/IP Kommunikation bei Adaptive AUTOSAR. Master’s Thesis, University of Stuttgart, Stuttgart, Germany, 15 November 2017. [Google Scholar]
- Weschke, J.; Hesslund, F. Testing and Evaluation to Improve Data Security of Automotive Embedded Systems. Master’s Thesis, Chalmers University of Technology, Göteborg, Sweden, 2011. [Google Scholar]
- Winton, R. Hollywood hospital pays $17,000 in Bitcoin to Hackers; FBI Investigating. Los Angeles Times, 18 February 2016. [Google Scholar]
- Hackers Hit Two California Hospitals with Ransomware. Healthcare IT News, 23 March 2016.
- Pilieci, V. Ottawa Hospital Hit with Ransomware, Information on Four Computers Locked down|Ottawa Citizen. 2016. Available online: https://ottawacitizen.com/news/local-news/ottawa-hospital-hit-with-ransomware-information-on-four-computers-locked-down (accessed on 12 December 2022).
- Bundesinstitut für Arzneimittel und Medizinprodukte. Cybersicherheit—Dringende Sicherheitsinformation zu Robot Imager, Gantry Imager von Siemens Healthcare GmbH. 2017. Available online: https://www.bfarm.de/DE/Medizinprodukte/Aufgaben/Risikobewertung-und-Forschung/Cybersicherheit/_node.html?cms_gts=900664_unnamed%253DdateOfIssue_dt%252Basc (accessed on 11 December 2022).
- Bundesinstitut für Arzneimittel und Medizinprodukte. Cybersicherheit—Dringende Sicherheitsmitteilung für Reinigungs- und Desinfektionsgeräte PG 8527/8528/8535/8536, Miele & Cie. KG. 2017. Available online: https://www.bfarm.de/SharedDocs/Kundeninfos/DE/02/2017/03160-17_kundeninfo_de.html (accessed on 22 December 2022).
- U.S. Food & Drug Administration. FDA Warns Patients and Health Care Providers about Potential Cybersecurity Concerns with Certain Medtronic Insulin Pumps. 2019. Available online: https://medicalxpress.com/news/2022-09-fda-cybersecurity-medtronic-insulin.html (accessed on 2 December 2022).
- Klonoff, D.; Han, J. The First Recall of a Diabetes Device Because of Cybersecurity Risks. J. Diabetes Sci. Technol. 2019, 13, 817–820. [Google Scholar] [CrossRef] [PubMed]
- Cybersecurity Vulnerabilities Affecting Medtronic Implantable Cardiac Devices, Programmers, and Home Monitors: FDA Safety Communication. 2019. Available online: https://public4.pagefreezer.com/browse/FDA/16-06-2022T13:39/https://www.fda.gov/medical-devices/safety-communications/cybersecurity-vulnerabilities-affecting-medtronic-implantable-cardiac-devices-programmers-and-home (accessed on 21 December 2022).
- Bundesinstitut für Arzneimittel und Medizinprodukte. Cybersicherheit—Dringende Sicherheitsinformation zu GSS67H von Getinge Sterilization AB. 2019. Available online: https://www.bfarm.de/DE/Medizinprodukte/Aufgaben/Risikobewertung-und-Forschung/Cybersicherheit/_node.html?cms_gts=900664_unnamed%253Dtitle_text_sort%252Basc (accessed on 5 January 2023).
- U.S. Food & Drug Administration. Cybersecurity Vulnerabilities in Certain GE Healthcare Clinical Information Central Stations and Telemetry Servers: Safety Communication. 2020. Available online: https://www.moph.gov.lb/userfiles/files/Medical%20Devices/Medical%20Devices%20Recalls%202020/18-1-2020/CentralStationsandTelemetryServers.pdf (accessed on 4 December 2022).
- Kasparick, M.; Schmitz, M.; Andersen, B.; Rockstroh, M.; Franke, S.; Schlichting, S.; Golatowski, F.; Timmermann, D. OR.NET: A service-oriented architecture for safe and dynamic medical device interoperability. Biomed. Eng. Biomed. Tech. 2018, 63, 11–30. [Google Scholar] [CrossRef]
- Mbakoyiannis, D.; Tomoutzoglou, O.; Kornaros, G. Secure over-the-air firmware updating for automotive electronic control units. In Proceedings of the 34th ACM/SIGAPP Symposium on Applied Computing, Limassol, Cyprus, 8–12 April 2019; pp. 174–181. [Google Scholar]
- Grimm, D.; Weber, M.; Sax, E. An Extended Hybrid Anomaly Detection System for Automotive Electronic Control Units Communicating via Ethernet—Efficient and Effective Analysis using a Specification- and Machine Learning-based Approach. In Proceedings of the 4th International Conference on Vehicle Technology and Intelligent Transport Systems, SCITEPRESS—Science and Technology Publications, Funchal, Portugal, 16–18 March 2018; pp. 462–473. [Google Scholar] [CrossRef]
- Weber, M.; Klug, S.; Sax, E. Embedded Hybrid Anomaly Detection for Automotive CAN Communication. In Proceedings of the 9th European Congress on Embedded Real Time Software and Systems (ERTS 2018), Toulouse, France, 31 January–2 February 2018; HAL Science Ouverte: Toulouse, France, 2018. [Google Scholar]
- Choi, S.J.; Johnson, M.E.; Lehmann, C.U. Data breach remediation efforts and their implications for hospital quality. Health Serv. Res. 2019, 54, 971–980. [Google Scholar] [CrossRef] [PubMed]
- Hadžiosmanović, D.; Simionato, L.; Bolzoni, D.; Zambon, E.; Etalle, S. N-Gram against the Machine: On the Feasibility of the N-Gram Network Analysis for Binary Protocols. In Research in Attacks, Intrusions, and Defenses; Balzarotti, D., Stolfo, S.J., Cova, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7462, pp. 354–373. [Google Scholar] [CrossRef]
| Risk | FDA Class | MDR Class | Example |
|---|---|---|---|
| Low | Class I | Class I | Bandages |
| Moderate | Class II | Class IIa | X-Ray-Machines |
| Moderate to High | Class II/III | Class IIb | Defibrillators |
| High | Class III | Class III | Pacemakers |
| Category | Standard | Standard Title | Description |
|---|---|---|---|
| Development and Life Cycle Processes | IEC 62304 | Medical device software—Software life cycle processes | Specification of the software development process for medical device software, and requirements for design, testing, and validation of software |
| ISO 24089 | Road vehicles—Software update engineering | Design and implementation of processes for global software update standardization. | |
| ISO 26262 | Road vehicles—Functional safety | Guidelines for automotive functional safety addressing systems and components released or under development. | |
| Risk Analysis and Management | EN ISO 14971 | Medical devices—Application of risk management to medical devices | Terminology, principles, and the process for risk management of medical devices, including software and the process for recognition of hazards of medical devices |
| ISO 24971 | Medical devices—Guidance on the application of ISO 14971 | Guidance on the development, implementation, and maintenance of a risk management system for medical devices according to ISO 14971 | |
| - | Canadian Premarket Requirements for Medical Device Cybersecurity | Risk analysis and management methods for certain high-risk medical devices. | |
| SAE J1739 | Potential Failure Mode and Effects Analysis (FMEA) Including Design FMEA, Supplemental FMEA-MSR, and Process FMEA | Evaluation of the potential of a failure of a process, a system, and subsystems, services, or designs. | |
| Regulatory requirements and Approval processes | ISO 13485 | Medical devices—Quality management systems—Requirements for regulatory purposes | European standard outlining specific requirements for risk management in the life cycle of medical devices |
| - | International Medical Device Regulators Forum (IMDRF) | Outlines principles and practices for medical device cybersecurity. Advises use of threat models. Guidelines for efficient realization of regulatory models. | |
| UN Regulation No. 156 | Software update and software update management system | Approval of software updates and SUMS that, among others things, must fulfill safety and security requirements. Processes to protect software updates and verification and validation of functionality and functional safety need to be established by OEMs to be certified. | |
| UN Regulation No. 155 | Cybersecurity and cybersecurity management system | Approval processes of vehicles with regard to cybersecurity and CSMS. OEM is required to set up and implement a management system focusing on cybersecurity over the vehicle life cycle. | |
| Cybersecurity Processes and Management | IEC 81001-1, IEC 81001-5-1 | Health software and health IT systems safety, effectiveness and security—Part 5-1: Security—Activities in the product life cycle | Guidelines for the management of cybersecurity in healthcare technology. IEC 81001-1: general introduction to IEC overview of principles, concepts related to cybersecurity in healthcare technology. IEC 81001-5-1: specific guidance on how to manage cybersecurity risks in healthcare technology, structured approach for identifying and evaluating cybersecurity risks, implementing protection measures, and responding to/ recovering from cybersecurity events. |
| Article 103 of Regulation (EU) 2017/745 | Medical Device Coordination Group (MDCG): Guidance on Cybersecurity for medical devices | Guidelines for medical device manufacturers to fulfill relevant cybersecurity requirements. | |
| - | FDA Premarket Guidelines: Premarket Submissions for Management of Cybersecurity in Medical Devices | Recognizes need for continuous, iterative approach to device cybersecurity throughout the product life cycle. Provides security risk management strategy and advises manufacturers to be able to identify, assess, and mitigate cybersecurity vulnerabilities. Specifies documentation thereof. | |
| - | FDA Postmarket Guidelines: Postmarket Management of Cybersecurity in Medical Devices | Specific recommendations managing cybersecurity risks for medical devices in the market: cybersecurity throughout product life cycle: design, development, production, distribution, and deployment maintenance of the device | |
| SAE J3061 | Guidebook For Cyber-Physical Vehicle Systems | High-level guidance on cybersecurity processes, and recommendation for usage of threat analysis and risk assessment methods. Models for discovering threats, assessing the risk of these threats, and analyzing a risk level accordingly. | |
| ISO/SAE 21434 | Road vehicles—Cybersecurity engineering | Definition of an automotive-specific cybersecurity engineering standard concerning the whole vehicle life cycle. Key aspect: TARA for identification of security risks and threats to develop countermeasures and mitigation strategies. | |
| - | Health Insurance Portability and Accountability Act (HIPAA) | Rules appropriate physical, technical, and administrative safeguards to maintain the confidentiality, integrity, and availability of PHI. |
| Negligible | Minor | Serious | Critical | Catastrophic | |
|---|---|---|---|---|---|
| Frequent | Med. | Med. | Med. | High | High |
| Probable | Low | Med. | Med. | High | High |
| Occasional | Low | Low | Med. | Med. | High |
| Remote | Low | Low | Med. | Med. | High |
| Improbable | Low | Low | Low | Med. | Med. |
| Controllability | ||||
|---|---|---|---|---|
| Severity | Exposure | C1 Able to Control | C2 Able to Control | C1 Able to Control |
| S1: Light or Moderate Injury | E1: Very low E2: Low (<1%) E3: Medium (1–10%) E4: High (>10%) | QM QM QM QM | QM QM QM ASIL A | QM QM ASIL A ASIL B |
| S2: Severe Injury Survival Probable | E1: Very low E2: Low (<1%) E3: Medium (1–10%) E4: High (>10%) | QM QM QM ASIL A | QM QM ASIL A ASIL B | QM ASIL A ASIL B ASIL C |
| S3: Life Threatening Injury | E1: Very low E2: Low (<1%) E3: Medium (1–10%) E4: High (>ty10%) | QM QM ASIL A ASIL B | QM ASIL A ASIL B ASIL C | ASIL A ASIL B ASIL C ASIL D |
| Attack Path ID | Expertise | Knowledge of Item | Window of Opportunity | Equipment | Attack Feasibility Rating |
|---|---|---|---|---|---|
| AP1 | 2 | 1 | 0 | 2 | Low (42%) |
| AP2 | 2 | 2 | 2 | 3 | Med. (75%) |
| AP3 | 1 | 2 | 2 | 3 | Med. (67%) |
| AP4 | 1 | 2 | 3 | 2 | Med. (67%) |
| AP5 | 2 | 2 | 3 | 3 | High (83%) |
| AP6 | 2 | 2 | 3 | 3 | High (83%) |
| AP7 | 1 | 2 | 3 | 2 | Med. (67%) |
| AP8 | 2 | 2 | 3 | 2 | Med. (75%) |
| Threat Scenario | Attack Feasibility | Impact | Risk |
|---|---|---|---|
| Rating | Rating | Value | |
| Input Signal Spoofed | Medium | Severe | 5 |
| Com. GW Tampered | High | Severe | 5 |
| SDC Output Signal Spoofed | High | Severe | 5 |
| ID | Item | Function | Failure Mode | Cause of Failure | Potential Effect |
|---|---|---|---|---|---|
| R1 | Com. GW | Send Joint Positions | Receive Wrong Position | Incorrect Parsing | Collision |
| R2 | Com. GW | Send Joint Positions | Receive Wrong Position | Wrong Joint Reference Position | Collision |
| R3 | Com. GW | Send Joint Positions | Receive Wrong Position | Signal/Service Data Corruption | Collision |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Puder, A.; Henle, J.; Sax, E. Threat Assessment and Risk Analysis (TARA) for Interoperable Medical Devices in the Operating Room Inspired by the Automotive Industry. Healthcare 2023, 11, 872. https://doi.org/10.3390/healthcare11060872
Puder A, Henle J, Sax E. Threat Assessment and Risk Analysis (TARA) for Interoperable Medical Devices in the Operating Room Inspired by the Automotive Industry. Healthcare. 2023; 11(6):872. https://doi.org/10.3390/healthcare11060872
Chicago/Turabian StylePuder, Andreas, Jacqueline Henle, and Eric Sax. 2023. "Threat Assessment and Risk Analysis (TARA) for Interoperable Medical Devices in the Operating Room Inspired by the Automotive Industry" Healthcare 11, no. 6: 872. https://doi.org/10.3390/healthcare11060872
APA StylePuder, A., Henle, J., & Sax, E. (2023). Threat Assessment and Risk Analysis (TARA) for Interoperable Medical Devices in the Operating Room Inspired by the Automotive Industry. Healthcare, 11(6), 872. https://doi.org/10.3390/healthcare11060872