1. Introduction
Satellite communication makes up for the shortage of terrestrial networks with its advantages including wide coverage and support for massive access services, and the satellite–terrestrial integrated network is proposed to achieve ubiquitous connectivity [
1]. Satellite network guarantees reliable communication services for remote areas not covered by existing terrestrial networks, e.g., 4G and 5G [
2]. The integration expands the network coverage area and supports continuous service for massive Internet of Things (IoT) devices and mobile terminals, e.g., ships and aircraft. With the support for broadcast and multicast services, the satellite network offers data distribution services for users with a higher communication efficiency [
3]. Besides these technological benefits, the satellite–terrestrial integrated network brings some economic benefit for remote areas, in which the deployment of 5G terrestrial networks is economically prohibitive [
4].
Although the satellite–terrestrial integrated network has been seen as an important part of future B5G/6G networks, there are still many technological and economic challenges [
5]. The first challenge is the differentiated user requirements, which cannot be fulfilled within a single network domain. The second challenge is the technological compatibility when heterogeneous infrastructures have different communication standards, protocols, and systems on the ground and in the space. The third challenge is the limited resource constraint, especially when the user demand exceeds the transmission capacity [
6]. The last challenge is the service provider (SP) incentive, especially when network service providers in different domains need to cooperate with each other to serve user requests, and it becomes impossible to neglect the problem of how to encourage the participation and resource sharing from different operators.
As one of the key technologies in 5G, network slicing (NS) is proposed for solving the first and second challenges in the satellite–terrestrial integrated network and adopted in this study [
7]. Both intra-domain and inter-domain network slices have been considered before. In this paper, the inter-domain network slice was considered with multiple routes supported and without delegating the specific domains along the route as long as the service can be provided. For example, with the deployment of low-Earth-orbit (LEO) satellite constellations, cross-continent network slicing can be fulfilled with inter-satellite links involving only one domain (i.e., the satellite network). Alternatively, network slicing can be fulfilled with multiple domains on the ground, e.g., radio access networks, wide-area networks and submarine cables. Since the network slicing service cannot be accomplished alone for the network service providers in some domains, the cooperation among several network operators is required to establish a feasible slice. When considering the admission decision for a slice request, a joint decision is made with the involvement of multiple parties with their own interests, making the admission control problem far more complex than the single-domain case.
To solve the third challenge and improve the utilization efficiency of limited resources, slice admission control is introduced and formulated as a mechanism design problem, in which different combinations of users and service providers are considered, as long as the network slices can be formulated [
8]. While two-sided markets (e.g., buyers and sellers) have drawn much research attention in recent decades, multi-sided markets are much less seen in the literature due to both theoretical and practical challenges [
9]. The trade decision process in a two-sided market only involves a buyer and a seller, while in a multi-sided market, it becomes a combinatorial problem when more than one combination of participants can form a deal.
To solve the fourth challenge and encourage the participation and cooperation among different service providers, a multi-sided ascending-price auction mechanism is further proposed as a game theory-based solution for slice admission control and resource allocation, in which multiple strategic service providers maximize their own utilities by trading bandwidth resources. Existing solutions for the multi-domain network slicing admission control problem are mainly based on game theory, for example, matching games [
10], especially when the incentives of both users and network service providers are non-negligible. However, these existing solutions are not flexible, when only a single and fixed combination of associated users and service providers is permitted, e.g., with one-to-one matching between a user and a service provider, without allowing multiple potential routes for provisioning the network slicing service.
In this paper, we propose a multi-sided ascending-price mechanism for sliced network service provision with bandwidth requirements, in which the network resource to allocate is the network bandwidth represented as a positive quantity. We design a novel optimal trade scheme calculation method and a novel ascending-price auction mechanism, with the consideration for the continuous value space, instead of the binary value space as in the previous study [
11]. We also prove that, in the new and continuous setting, our proposed optimal trade scheme has a polynomial time complexity and performs as an upper bound for the auction mechanism, which is proven to be strongly budget-balanced, individually rational, and obviously truthful. Simulation experiments based on real-world data are designed to validate the effectiveness of the proposed ascending-price auction mechanism for the satellite–terrestrial integrated network.
The main contributions of this paper are summarized as follows:
The multi-domain network slicing admission control is formulated as a multi-sided mechanism design problem when multiple routes can be used simultaneously in the satellite–terrestrial integrated network.
A polynomial-time optimal trade mechanism is proposed as an upper bound that calculates the optimal trade scheme for the mechanism design problem.
A multi-sided ascending-price auction mechanism is proposed as a strongly budget-balanced, individually rational, and obviously truthful solution for the mechanism design problem, and its asymptotically optimal performance is validated with simulation experiments based on real-world data.
The rest of this paper is organized as follows. The relevant studies are reviewed and discussed in
Section 2. The system model and the multi-sided mechanism design formulation are defined in
Section 3. The proposed optimal trade mechanism and proof of its polynomial time complexity are presented in
Section 4. The proposed multi-sided ascending-price auction mechanism and the proof for its desirable properties are presented in
Section 5. Numerical experiments and results are discussed in
Section 6.
Section 7 concludes this paper with some potential future research directions.
The acronyms for terminologies used in this study are summarized in
Table 1 for reference.
3. System Model
In this section, we describe the mathematical system model for the scenario of the multi-domain network slicing service provision market in the satellite–terrestrial integrated network scenario. Compared with previous studies, our system model incorporates both competitive and cooperative relationships among different network service providers, with the simplest example as an illustration of a better and easier understanding. Some link properties are also simplified (e.g., delay and jitter) and the bandwidth and price are used to demonstrate the key ideas of our newly defined problem and proposed mechanisms. Our system model and proposed mechanisms can be easily extended to much more complex and realistic integrated satellite and terrestrial network scenarios without a heavy modification.
In our problem formulation, the optimization objectives of both the network service providers and users are to maximize their own utilities, which are mathematically defined in this section. Since the value of providing/using the network service is the private information, the participants may want to behave strategically through their bids for their own interests, which would damage the overall efficiency. Thus, our design goals are the economic properties, which include the budget balance, individually rationality, and obvious truthfulness, to inhibit such selfish behaviors. We also demonstrate that our proposed multi-sided ascending-price auction mechanism guarantees these economic properties with theoretical proofs in
Section 5 and achieves a desirable asymptotically optimal gain from trade with numeral experiments in
Section 6.
Table 3 provides a list of the major mathematical symbols used in this paper for a convenient reference.
3.1. Model Description
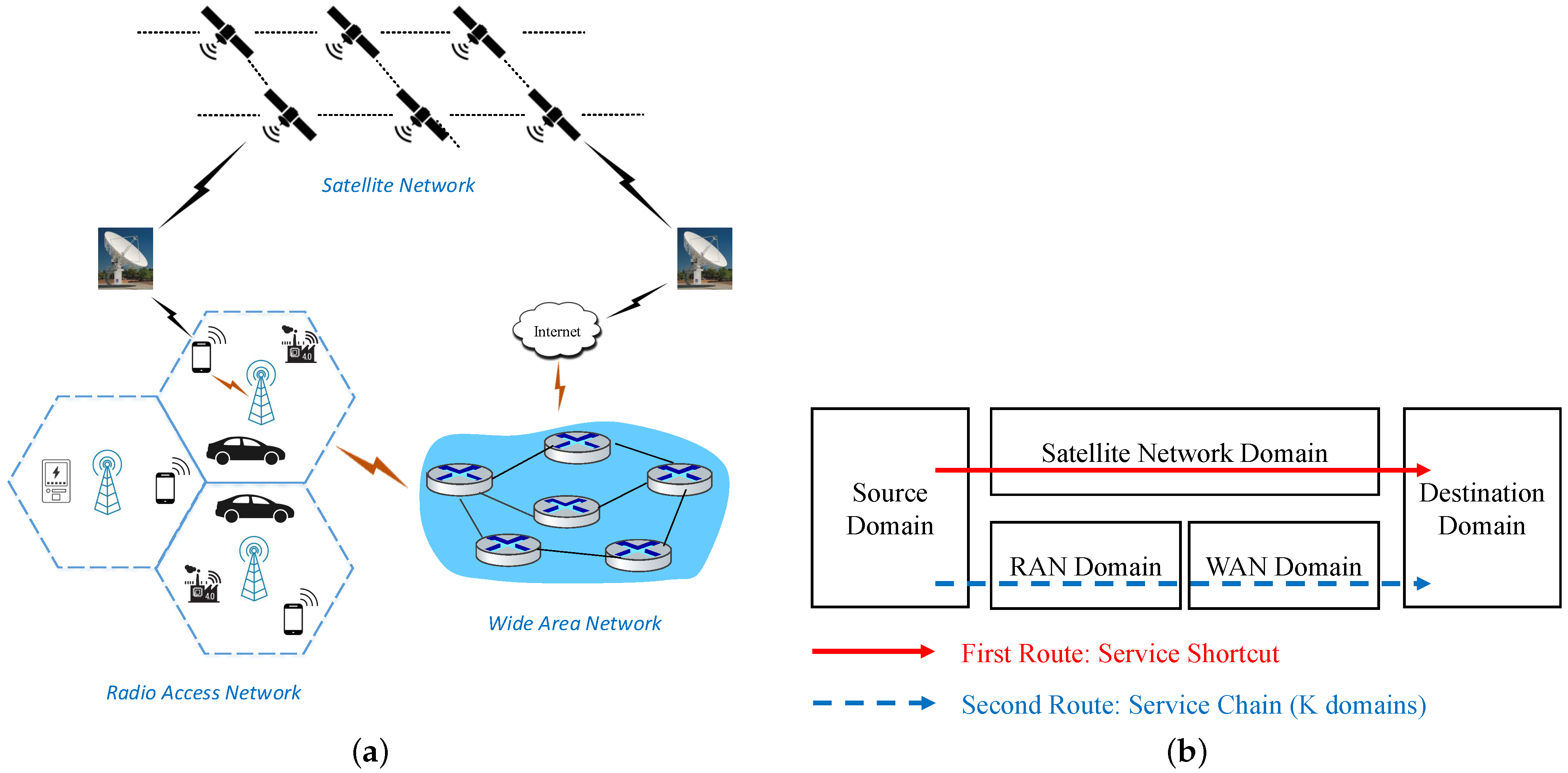
In this paper, a basic structure of the multi-domain network slicing service provision market is described and used, as shown in
Figure 1. Both users and network service providers are seen as participants. Users send network resource requests and network service providers serve user requests. The service providers from different domains are seen as different categories. In the example of
Figure 1, there are four categories of participants and the participant type set
G is denoted as
. In
Figure 1, the user set is denoted as
, which contains all users. The service provider set in the satellite network domain is denoted as
, which contains all satellite network service providers. The service provider set in the radio access network (RAN) domain is denoted as
, which contains all RAN service providers. And, the service provider set in the wide area network (WAN) domain is denoted as
, which contains all WAN service providers. We assume that the participant sets of different categories are pairwise-disjoint, e.g., a single service provider cannot appear in the satellite network domain and the RAN domain simultaneously. In more complex cases, the number of participant categories could be more than four.
A group of users with size
N (i.e.,
) aims to request the network slicing service between the source and destination domains. Two alternative routes are established to provide this network slicing service. The first route (the upper route in
Figure 1) is named a
service shortcut route, which only goes through a single domain. The second route (the lower route in
Figure 1) is named a
service chain route, which passes through
K different domains (e.g.,
in
Figure 1). It is worth mentioning that complex structures with more routes can also be described in a similar approach to the concepts we define in this section.
In a single timeslot, user i submits a network slice bandwidth request and a unit bid price for using the network service. The unit value of using the service is the user’s private information and if the user bids truthfully. We assume that the user’s utility is quasi-linear, which is the value minus the price the user pays, multiplied by the bandwidth, i.e., . We also assume that a binary admission decision is made for a user, i.e., either the user is admitted and served with the bandwidth amount , or the user is rejected without service. The user may behave strategically to maximize their own utility. We assume that the strategic behavior of users only exists in the submitted bid price information instead of the requested bandwidth information. In other words, if the submitted bandwidth is more than the user’s actual need, the extra part if served brings no excess benefit to the user, and if the submitted bandwidth is less than the user’s actual need, the network slicing service cannot be fulfilled as the user expects.
In each domain, we assume M service providers exist, each of which has the ability to provide the cross-domain network service. The same number of service providers is used for model description simplicity, i.e., (in practice, if the numbers of service providers from different domains are not equal, we can add dummy service providers with zero bandwidth resources to make this assumption hold). For the time period of interest, we assume that a service provider j submits a network slice bandwidth resource amount and a unit ask price for providing the network service. Similarly, the unit value of providing the service is the service provider’s private information and if the service provider bids truthfully. Note that the same mathematical symbols of the bandwidth and bid are used for the users and service providers. The value and price of the service providers are typically negative for representing the cost of deploying the infrastructure.
A similar quasi-linear utility format is assumed for the service provider, which is . While and are both negative, utility, as their difference, is typically required as a positive value for the service provider to participate willingly. Different from the binary admission decision for a user, a service provider may use all or part of its bandwidth resource. We also assume that the strategic behavior of the service provider is limited to price information, e.g., by imposing a prohibitory penalty if the service provider fails to fulfill the submitted bandwidth resource in practice.
Following the terminology borrowed from [
11], each possible route is formulated as a
recipe, which is a binary projection from the category set to a vector, e.g., the two routes in
Figure 1 are mapped as
and
, respectively. For example, in recipe
, a user is served by a satellite network service provider. Since we assume there is no loop in the routes, each recipe
R can be represented by a path in a tree, as shown in
Figure 2a. The user category is used as the root node for convenience so that each path from the root to a leaf is a feasible recipe. An example of the values and bandwidths of the participants is shown in
Figure 2b (note that the values and bandwidths are not necessarily integers in this paper. Integer values are used in examples for simplicity).
A procurement set S can be generated by following a recipe and adding the served bandwidth value. For example, by following the recipe , the user with a value of 17 can be served by the satellite network service provider with a value of −4, for the served bandwidth amount of 2. The gain from trade (GFT) of the procurement set S is defined as the sum of the values of all participants in S, i.e., , where is the served bandwidth amount, which satisfies . A trade scheme is a collection of procurement sets, with a gain from trade as the sum of the GFT of all procurement sets, i.e., .
3.2. Mechanism Design Problem Formulation
In this paper, multi-domain network slicing admission control is formulated as a mechanism design problem. The designed mechanism can be classified as deterministic or randomized. In a deterministic mechanism, the outcome is purely decided by the inputs. In a randomized mechanism, the outcome is decided by both the inputs and some random variable(s). A randomized mechanism can also be seen as a lottery over deterministic mechanisms. The designed mechanism can also be classified as direct or sequential. In a direct mechanism, the participant’s private information is revealed only once, e.g., when submitting the bandwidth and price information. In a sequential mechanism, the participant’s private information is revealed sequentially, e.g., by answering questions about whether a price is acceptable or not.
Specifically, a
deterministic direct mechanism aims to find a function that takes as input a bid vector
of bid/ask prices and a bandwidth vector
of bandwidth requests/resources and returns a trade scheme
and a price vector
. For the trade scheme
to be
bandwidth-feasible, the following constraints must be satisfied:
where Constraint (
1) requires that the admitted users are served exactly with the requested bandwidth and Constraint (
2) requires that the consumed bandwidth from the service providers cannot exceed their available resources.
The desirable properties of the designed mechanism include
optimality (i.e., with the maximum gain from trade),
individual rationality,
budget balance,
truthfulness. It is well known that these properties cannot be achieved simultaneously in a two-sided market [
54]. This impossibility theorem holds for the multi-sided market considered in this paper, which becomes a two-sided market when only one category of service providers exists.
A deterministic direct mechanism is optimal if the gain from trade of its trade scheme is maximum over all bandwidth-feasible trade schemes, regardless of the price vector.
A deterministic direct mechanism is truthful if a participant bids truthfully based on their value when maximizing their own utility. Formally, the participant’s utility is denoted by , the bid is and the bids of all other participants are denoted by . Then, a mechanism is truthful if, for every participant i and any fixed bids of all the other participants, .
A stronger propriety called
obvious truthfulness [
55] requires that the lowest utility for a participant by bidding truthfully is at least as high as the highest utility they may obtain by acting non-truthfully. Formally, a mechanism is obviously truthful if for every participant
i and bid vector
,
. In other words, the bids of all the other participants do not need to be fixed.
A deterministic direct mechanism is individually rational if a participant loses nothing to participate in the market. In other words, the participant’s utility should be non-negative, regardless of the bids of all other participants. For those participants that are not in any procurement set, the price should be zero.
A deterministic direct mechanism is weakly budget-balanced if the total amount paid by all participants together should be at least zero. Similar to the values and bids, the prices of the service providers are negative. A negative price for the service provider means that he pays a negative value to the market operator, which is equivalent to the case in which the service provider receives a positive payment from the market operator. A deterministic direct mechanism is strongly budget-balanced if the total amount paid by all participants together is exactly zero, which is more desirable when the market operator is non-profit.
A randomized direct mechanism can be seen as a lottery over deterministic direct mechanisms. The randomized direct mechanism has the above properties as long as they hold for all deterministic direct mechanisms.
A deterministic sequential mechanism considered in this paper uses a answer vector instead of the bid vector , in which each answer replies to a query about the participant’s value , e.g., whether a price is greater than or equal to the value . The direct mechanism can be seen as a special case of the sequential mechanism, when only one query is used, i.e., what is the value? If the participant answers truthfully, we would have . Similar properties can be defined for the deterministic sequential mechanism and a randomized sequential mechanism can be seen as a lottery over deterministic sequential mechanisms.
4. Optimal Trade Mechanism
Before presenting the proposed multi-sided ascending price algorithm, an optimal trade mechanism with a polynomial time complexity is described in this section as an upper bound for all possible solutions to the mechanism design problem in
Section 3.2. In this optimal trade mechanism, only the trade scheme is returned as the output regardless of the price vector and without considering the participant’s strategic behavior. The optimal trade mechanism is calculated assuming all bandwidths and values are known by the market operator. The algorithm for calculating the optimal trade scheme is based on the basic operations of
vertical contraction and
horizontal contraction with the recipe tree structure shown in
Figure 2a. The participants in each category are ordered with a decreasing value first.
The vertical contraction operation is used to combine the network service providers that cannot meet the end-to-end slice request solely, for example, the RAN service providers in
and the WAN service providers in
. In
Figure 1,
and
are two nodes and the purpose of vertical contraction is to combine them into a new node
. New values and bandwidths are also calculated by the vertical contraction operation for
, as shown in
Figure 3. The vertical contraction is used to combine a leaf node that is a single child with its parent node with the process shown in Algorithm 1. The combination process for the participants from the leaf node and its parent node is conducted iteratively. The combined values and bandwidths in the combined node are seen as “new participants" in the follow-up operations until only one node remains in the recipe tree. An example of the vertical contraction algorithm following
Figure 2b is shown in
Figure 3.
The horizontal contraction operation is used to combine the network service providers that can meet the end-to-end slice request into a single set, e.g., the satellite network service providers in
and the combined node
. The new node is denoted as
, with new values and bandwidths calculated by the horizontal contraction operation shown in
Figure 4. Similarly to the vertical contraction, the horizontal contraction is used to combine two sibling leaves into a new node with the process shown in the Algorithm 2. An example of the horizontal contraction algorithm following
Figure 3 is shown in
Figure 4. When there are more than two sibling leaves, a pairwise horizontal contraction can be conducted with two nodes combined in each operation. One may easily find that the combined result as one final node is irrelevant to the order of the pairwise horizontal contraction operations.
| Algorithm 1 The vertical contraction |
Input: A sorted value vector and a corresponding bandwidth vector of the participants from the leaf node, a sorted value vector and a corresponding bandwidth vector of the participants from the parent node. Output: A sorted value vector , a corresponding bandwidth vector , and a corresponding participant identity set .
- 1.
Initialization: , , . - 2.
If or : return , and . - 3.
If the first element of is smaller than or equal to the first element of , i.e., : Add to ; Add to ; Add a new participant identity to ; Remove from ; Remove from ; Remove from ; Update ; Go back to step 2.
- 4.
Else: Add to ; Add to ; Add a new participant identity to ; Remove from ; Remove from ; Remove from ; Update . Go back to step 2.
|
| Algorithm 2 The horizontal contraction |
Input: A sorted value vector and a corresponding bandwidth vector of the participants from the leaf node, a sorted value vector and a corresponding bandwidth vector of the participants from the sibling node. Output: A sorted value vector , a corresponding bandwidth vector , and a corresponding participant identity set .
- 1.
Initialization: , , . - 2.
If and : return , and . - 3.
If or the first element of is smaller than the first element of , i.e., : Add to ; Add to ; Add to ; Remove from ; Remove from ; Remove from ; Go back to step 2. - 4.
Else, if or : Add to ; Add to ; Add to ; Remove from ; Remove from ; Remove from ; Go back to step 2. - 5.
Else: Add to ; Add to ; Add a new participant identity to ; Remove from ; Remove from ; Remove from ; Remove from ; Remove from ; Remove from . Go back to step 2.
|
Figure 4.
The example of the horizontal contraction algorithm. (a) The result of the recipe tree after the horizontal contraction. (b) The result of combined values and bandwidths.
Figure 4.
The example of the horizontal contraction algorithm. (a) The result of the recipe tree after the horizontal contraction. (b) The result of combined values and bandwidths.
Based on the vertical and horizontal contraction operations, the algorithm to find the optimal trade scheme is shown in Algorithm 3. After the recipe tree is contracted to a single root node, only the participants with a positive value are incorporated in the output trade scheme. It would be easier to calculate the gain from trade for the trade scheme by adding the values multiplied by the served bandwidths, i.e.,
, where
and
are the outputs of Algorithm 3. It is not difficult to generate the procurement sets by referring to the recorded participant identity sets and decomposing the combined values and bandwidths to the corresponding original users and service providers. An example of the procurement sets generated by the optimal trade mechanism for
Figure 2b is shown in
Table 4. Note that a single user may be served by multiple network services as long as the sum of the served bandwidth is equal to the requested amount. For example, the user with a value of 17 is served in three procurement sets, as shown in the first three lines in
Table 4. In the first line of
Table 4, a bandwidth value of 1 is provided by the RAN and WAN providers together. In the second line of
Table 4, a bandwidth value of 2 is provided by the satellite network provider solely. And, in the third line of
Table 4, a bandwidth value of 2 is provided by the RAN and WAN providers together, in which the RAN provider has a higher price than the RAN provider in the first line. A service provider’s bandwidth resource may not be fully utilized. For example, only half of the bandwidth resource from the WAN provider with a value of −4 is utilized.
Two theorems are presented to conclude this section. Theorem 1 demonstrates that the trade scheme generated by Algorithm 3 is optimal. Theorem 2 demonstrates that Algorithm 3 runs with a polynomial time complexity.
Theorem 1. The trade scheme of Algorithm 3 is optimal, i.e., with the maximum gain from trade over all trade schemes.
| Algorithm 3 The optimal trade mechanism |
Input: A set of categories G, a set of participants for all , a recipe tree, the values and bandwidths of all participants. Output: A sorted value vector , a corresponding bandwidth vector , and a corresponding participant identity set .
- 1.
If the recipe tree has a single root node g: Return , and , where . - 2.
Otherwise, if there is a leaf that is a single child of its parent : Do a vertical contraction of into by Algorithm 1; Go back to step 1. - 3.
Else, if there is a leaf with a sibling leaf : Do a horizontal contraction of into by Algorithm 2; Go back to step 1.
|
Proof of Theorem 1. This proof is conducted by showing that no further improvement can be achieved with the trade scheme output of Algorithm 3. First, it is not hard to find that each value for the participant from the final single node is the value sum for a path from the root to a leaf, e.g., a recipe. Since all the positive values from the final single node are already counted, adding more procurement sets can only produce a zero or negative surplus. Conversely, removing any existing procurement sets from the trade scheme of Algorithm 3 can only cause a positive loss. Another observation is that both the users and service providers are chosen according to the decreasing value order before replacing any user or service provider with one that is not previously included in the trade scheme of Algorithm 3, which can only cause a decrease in the value sum. □
Theorem 2. The optimal trade scheme can be calculated in polynomial time with Algorithm 3.
Proof of Theorem 2. Denote
n as the total number of participants, e.g.,
for
Figure 2a. Denote
k as the total number of categories, e.g.,
for
Figure 2a. Usually, we assume
.
The time complexity for the pre-processing step of sorting the participants into different categories is at most , by adopting an efficient sorting algorithm, e.g., the quick sort algorithm or the merge sort algorithm. Note that the participants can be sorted together once and then assigned to each category.
The time complexity for Algorithm 1 or Algorithm 2 is at most since, in each loop, at least one participant is removed and only some linear operations are conducted. Then, the time complexity for Algorithm 3 is at most since, in each loop, either Algorithm 1 or Algorithm 2 is invoked to remove a category. The process of choosing the positive values in step 1 of Algorithm 3 is linear, i.e., .
Since we assume that , the overall time complexity for calculating the optimal trade scheme with Algorithm 3 is , which is bounded by and thus polynomial. □
5. Multi-Sided Ascending-Price Auction Mechanism
Generally, the proposed multi-sided ascending-price auction mechanism is a randomized sequential mechanism, in which each category g is charged with a unified price and the ascending price means that this price increased by in each step, accompanied by a query for each participant in a pre-specified order of whether the increased price is acceptable, e.g., whether the value is still higher than the price. Those who cannot accept the increased price would be permanently removed from the market, for example, those who would receive a potential negative utility if they stayed. The price sum for a recipe is monitored, and the auction terminates when this price sum crosses zero. The final procurement sets and prices are determined from the remaining participants. In practice, the bids and prices can be counted with a specific currency so that the quantity can be set as a currency unit, e.g., a dollar.
The general process of the proposed multi-sided ascending-price auction mechanism is shown in Algorithm 4. The first step is initialization, in which the initial prices are well designed with a sufficiently large value
V, which satisfies
for any participant
i. To determine the initial prices, the max depth
of the recipe tree
R and the depth
for each category
are calculated in advance. The initial prices are calculated for the non-leaf and leaf nodes separately so that the price sum in each path from the root to a leaf is the same.
| Algorithm 4 The ascending-price auction mechanism |
Input: A set of categories G, a set of participants for all , a recipe tree , the values and bandwidths of all participants. Output: The procurement sets and a price vector for all .
- 1.
initialization: Determine the initial price vector : For each non-leaf node g, set ; For each leaf node g, set . - 2.
Select for price ascending with Algorithm 5. - 3.
Price ascending: For each , ask each participant whether with a pre-specified order: If the answer is negative, then remove i from , and go back to step 2. If the answers from all participants for all are positive, then for all , update ; If, after the increase, the price sum of a recipe R crosses zero, i.e., , reset so that the price sum of a recipe is exactly zero. Then, go on to step 4. - 4.
Determine the final trade scheme with Algorithm 6.
|
The next part chooses a subset of categories to be used for the price ascending process, which is accomplished by Algorithm 5. Note that
represents the sum of bandwidths for category
g in our study, instead of the user numbers in ref. [
11]. The key idea is to use the supply and demand relationship to determine the prices to be increased. Generally, if the bandwidth sum of the root node, i.e., the user, is greater than the bandwidth sum of its children, i.e., the service providers, the price charged for the users is increased so that some user would leave the market. In the opposite situation, wherein the price charged for the service providers is increased (equally, the price paid for the service providers is decreased) so that some service providers would leave the market. A desirable property of Algorithm 5 is that the chosen subset contains exactly one price for each path from a root a leaf. Recall that the initial price sum in all recipes is set to be the same. By simultaneously increasing the prices in the chosen subset, the price sum in all recipes remains the same.
| Algorithm 5 The subset selection for price ascending |
Input: A set of categories G, a set of remaining participants for all , a recipe tree , the values and bandwidths of all remaining participants. Output: A subset of G containing categories whose prices are to be increased.
- 1.
Initialization: For each category , define =the bandwidth sum of participants of who remain in the market. - 2.
Denote as the root category: If has no children or , return ; Else for each child of , apply Algorithm 5 on the sub-tree rooted at recursively and take the union set of the outcome , i.e., return .
|
At some time step, the price sum of a recipe crosses zero, which triggers the termination of the price ascending process. To maintain the strong budget balance, the increased prices are reset so that the price sum of a recipe is exactly zero, as shown in Step 3 of Algorithm 5. After the auction is terminated and the price vector is finalized, the final trade scheme is further determined by Algorithm 6.
| Algorithm 6 The trade scheme determination |
Input: A set of categories G, a set of remaining participants for all , a recipe tree , the values and bandwidths of all remaining participants. Output: The procurement sets .
- 1.
If the recipe tree has a single root node g: Return the remaining participants in category g, with the original participant identity reversed from the recorded participant identity set. - 2.
Else, if the recipe tree has a single root node g and a single child : If , i.e., the bandwidth sum requested by the users is larger than the bandwidth resource provided by the service providers: Remove the participant in in a random order until ; Randomly order the participants in and ; Do a vertical contraction of into g by Algorithm 1; Go back to step 1. - 3.
Else, pick an arbitrary leaf . - 4.
If is the single child of its parent : Randomly order the participants in and ; Do a vertical contraction of into by Algorithm 1; Go back to step 1. - 5.
Else, choose a sibling of : Randomly order the participants in and ; Do a horizontal contraction of into by Algorithm 2; Go back to step 1.
|
Since the supply and demand of bandwidth resources may not be balanced after the auction terminates, some participants must be removed from the market in the trade scheme determination. To avoid non-truthful and strategic behaviors, the selection of the remaining participants is independent of the values but conducted in a random fashion, as shown in Algorithm 6. The vertical contraction algorithm defined in Algorithm 1 and the horizontal contraction algorithm defined in Algorithm 2 are both leveraged in the trade scheme determination, but with a randomized order of input participants, instead of the value-decreasing order, to maintain truthfulness. When the bandwidth sum requested by the users is larger than the bandwidth resource provided by service providers, some users are removed from the market as a binary decision of admission rejection, instead of being partially served, until the remaining users can be fully served.
An example is used to demonstrate the multi-sided ascending-price auction mechanism as shown in
Table 5, following the values and bandwidths from
Figure 2b, when
is set to 1. In the initialization step, the prices for the users, satellite network service providers, RAN service providers, and WAN service providers are set to
,
,
, and
, respectively. The initial price sums for recipes
and
are both
, i.e.,
.
In the first round of price ascending, the bandwidth sum of the users is less than the bandwidth sum of the satellite network service providers and RAN service providers, i.e., . The bandwidth sum of the RAN service providers is less than the WAN service providers, i.e., . Thus, the subset is chosen as , i.e., satellite network service providers and the WAN service providers. The prices are increased until the WAN provider with value of -6 exits the market. Afterwards, the price vector becomes and the price sum for a recipe becomes .
A similar process continues until the last line of
Table 5, when the price sum for a recipe crosses zero as
, and the auction terminates. An example of the procurement sets generated by the ascending-price auction mechanism is shown in
Table 6. Note that the served users are chosen at random instead of their values. The same rule applies for the service providers. Different users or network service providers in the same domain use the same price, making it indifferent for a user to choose between different routes or service providers, as long as the bandwidth requirement can be satisfied. One may easily validate the gain from trade for the trade scheme in
Table 6 (which is
) is less than that of the optimal trade scheme in
Table 4 (which is
).
To conclude this section, some theoretical analysis is given through Theorem 3, which demonstrates that the proposed multi-sided ascending-price auction mechanism satisfies the desirable properties.
Theorem 3. The multi-sided ascending-price auction mechanism of Algorithm 4 is strongly budget-balanced, individually rational, and obviously truthful.
Proof of Theorem 3. Since the proposed multi-sided ascending-price auction mechanism is a randomized mechanism, it is sufficient to prove that any deterministic variant with a pre-specified order of the participants satisfies these properties, i.e., all the random ordering operations in Algorithm 6 are conducted with a pre-specified order.
A strong budget balance is guaranteed by two properties of Algorithm 4. The first property is that the price sum of all the recipes is the same as the price ascending operation. The second property is that the auction is terminated with an exact zero price sum, guaranteed by the price reset step.
Individual rationality is guaranteed by the property of Algorithm 4 that only those participants with values greater than or equal to the prices would remain in the market. Otherwise, they should leave the market after the price increase to avoid negative utility.
To prove the obvious truthfulness, consider the behavior of a specific participant i from category g during the process of price ascending when asked whether .
If the true case is and the participant answers truthfully, the lowest possible utility they can expect is 0 since the mechanism is individually rational. However, if the participant answers untruthfully, they would be immediately removed from the market, with the highest possible utility of 0.
If the true case is and the participant answers truthfully, the lowest possible utility they can expect is 0 because they are removed from the market immediately. However, if the participant answers untruthfully, the highest possible utility they can expect from remaining in the market is 0, since the price can only increase and their utility can only decrease.
For the trade scheme determination, no strategic behaviors from the participant can change the result since the adopted order is pre-specified, regardless of their values. This completes the proof that the lowest possible utility of a participant acting truthfully is at least as high as the highest possible utility of acting untruthfully. □
6. Numerical Experiments
To evaluate the performance of the proposed multi-sided ascending-price auction approach for providing the multi-domain network slicing service, real-world data are leveraged in the simulation experiments in this section. Our main objectives in this section are to evaluate the gap between the proposed multi-sided ascending-price auction mechanism and the optimal trade mechanism, which is used as an upper bound without desirable economic properties, and to evaluate the influence of different parameters on the performance. To demonstrate the effectiveness of the proposed multi-sided ascending-price auction mechanism, a second-price auction is used as the baseline in this section. The second-price auction has the desirable truthfulness property and has been proven effective in previous relevant studies [
35]. However, since previous game theory-based solutions do not fit to our newly defined problem as shown in
Table 2 in
Section 2, the standard second-price auction is not applicable and a variant is designed as follows. The service providers from the service chain route with
K domains are paired up randomly and act as a coalition to compete with the service provider from the service shortcut route in a standard second-price auction approach.
6.1. Experiment Settings
For the recipe tree, we adopt the basic structure of a user group and two alternative routes, e.g., the first route as the service shortcut route and the second route as the service chain route (with
K different domains), as shown in
Figure 2a. More complex structures will be considered in our future studies.
The bandwidth amount requested by users is modeled with historical traffic data collected from the China Education and Research Network (CERNET). During this time period, the CERNET topology contained 14 nodes and 16 bi-directional links [
56]. The historical traffic is recorded for each node pair every five minutes from 19 February 2013 to 26 March 2013, with a total number of 9999 time slots used in the experiments. After filtering the node pairs with only zero values, a total of 159 node pairs remain, out of which
N node pairs are chosen at random and without replacement as the users (e.g., N = 10, 20, 50, 100, or 150). The historical traffic data distribution is shown in
Figure 5, in which 300 Mbps is approximately the 90th percentile value. Only the requested bandwidth from users is modeled as time-varying in the experiments.
The available bandwidth amount provided by service providers is drawn from a uniform distribution
, in which
is the service provider/user ratio. When the number of users is equal to the number of service providers in a domain, the uniform distribution becomes
. With a lower service provider/user ratio (i.e., a smaller
), the bandwidth resource provided by the remaining service provider increases accordingly to maintain the same expected total bandwidth for a fair comparison of the different service provider/user ratios in
Section 6.3.
The bid prices of users and the ask prices of service providers in the service shortcut route are drawn from a uniform distribution
, and the ask prices of service providers in the service chain route are drawn from a uniform distribution
, which is affected by the domain number in the service chain route. With a longer service chain (i.e., a larger
K), the ask price from the growing domains decreases accordingly to maintain the same expected total cost of using the service chain route for a fair comparison of different domain numbers in
Section 6.4. Otherwise, if the ask prices increase with the domain numbers linearly, then no users would prefer a longer service chain route and this comparison becomes trivial (and thus, the service chain route becomes economically prohibitive in practice). The economic intuition is that, if more service providers are meant to cooperate in the service chain route, the overall cost must be controlled to be competitive with the satellite service provider in the service shortcut route.
The parameters used in the experiments as well as their value ranges are summarized in
Table 7. Only the bandwidth information is derived from real-world historical traffic values and the user or price information is difficult to obtain, even from the existing terrestrial network service providers, as such information is usually their commercial secret. It is also impossible to obtain such information from the satellite network service provider, which is at the very early stage of providing commercial services. Instead, we set the similar parameters and the uniform distribution format following previous relevant studies [
8,
44,
57].
In each time slot, N user requests are generated, and the market operator attempts to admit or reject these requests based on the bandwidth and price information. Both the optimal trade mechanism and the proposed ascending auction mechanism are implemented and compared. To evaluate the admission results and quantify the influence of different parameter values, different evaluation metrics are defined and used in the experiments.
The first evaluation metric is the admission ratio within the range of 0–1, which calculates the ratio of the admitted requests to all the requests. The second evaluation metric is the served bandwidth per user in Mbps, in which both the admitted and rejected users are counted as the denominator to reflect the overall service ability of different mechanisms under different user sizes in a fair way. The third evaluation metric is the gain from trade per user, in which all the users are counted for the same reason. The gain from trade per user can be further divided into two parts, namely the user gain and the service provider profit, which are used in
Section 6.4.
6.2. Impact of User Numbers
Different user numbers correspond to different market sizes, e.g., thin, medium, and thick markets. In the experiments of this section, the user number and the service provider number in a single domain are assumed to be the same, i.e., . In other words, when the user number increases, the service provider number also increases, so that the supply and demand relationship remains stable.
The evaluation result of the impact with different user numbers is shown in
Figure 6. In a thicker market with more users, all three evaluation metrics of the proposed ascending auction mechanism increase. The performance of the ascending auction mechanism also becomes closer to the optimal trade mechanism, showing that it is asymptotically optimal with an increasing market size. This observation makes our proposed mechanism favorable in practice, with both a theoretical guarantee of economic properties and an asymptotically optimal service provision performance.
6.3. Impact of Service Provider/User Ratios
In the previous part, an assumption is made that the user number is the same as the service provider number in a single domain, which may not be the case in practice when a large number of users are actually served by a few telecommunications companies. To reflect this market feature, we alter the service provider/user ratio to a smaller value and evaluate its impact on the service provision performance of both the optimal trade and our proposed ascending auction mechanisms when the user number is fixed as (e.g., a thin market) and (e.g., a thick market). It is worth mentioning that even when the number of service providers decreases, each remaining service provider is endorsed with a stronger service ability (e.g., a bandwidth value drawn from a larger range) to maintain the overall service level. Otherwise, the outcome would be obvious and trivial because a lower overall service level would impair the performance of any mechanism.
The evaluation of different service provider/user ratios is shown in
Figure 7. With a more centralized market, i.e., in the case of a smaller service provider/user ratio, the performance of either the ascending auction mechanism or the optimal trade mechanism decreases, but to different degrees. The performance of the optimal trade mechanism is slightly affected, especially for the metrics of admission ratio and served bandwidth per user. However, the performance of the ascending auction mechanism is highly affected, e.g., the admission ratio drops by approximately 50% in
Figure 7a. The implication is that a diverse and fully competitive market with a large number of service providers is more favorable for our proposed ascending auction mechanism, in which its performance is closer to the optimal trade mechanism.
It is also found in
Figure 7 that the ascending auction mechanism is less affected in the thick market than in the thin market, which gives another implication that the thick market with more users is more robust to the centralization of service providers.
6.4. Impact of Domain Numbers
In this part, the impact of different domain numbers is further evaluated in both the thin market (i.e., ) and the thick market (i.e., ). The motivation is to validate whether it would be more difficult to provide network slicing services involving more domains in the service chain route and whether the service shortcut route would become more favorable or not. Similarly to the previous part, to avoid an unfair comparison, the ask price of the service providers from the domains in the service chain route decreases accordingly when the domain number decreases to maintain a stable overall service cost.
The evaluation of different domain numbers in the service chain route is shown in
Figure 8. Both the ascending auction and the optimal trade mechanisms are hardly affected by the increasing domain numbers in the service chain route, as long as the service cost for using the two alternative routes remains at the same level. Intuitively, when more domains with a fixed ask price level are required to build the network slices, fewer users who are capable of affording the increasing service cost remain. Our result implies that the difficulty of providing multi-domain network slicing services does not rely on the domain number but the overall service cost along the service chain route.
Figure 9 is used to compare the user gain and service provider profit with different domain numbers in the service chain route. The gain from trade per use is decomposed into two parts, namely, the user gain and the service provider profit, in the results of the ascending auction mechanism. The user gain is defined as the gap between the user’s value and the auction price. Similarly, the service provider profit is defined as the gap between the auction price and the service provider’s value. For the second route, i.e., the service chain route, the sum of the service provider profit is used to compare with the profit of the first route. As shown in
Figure 9, the service provider’s profit increases with a larger domain number, and the increase part is filled with the decrease in the user gain. This implies that more gain from trade is transferred from the user side to the service provider side when it becomes more cumbersome to provide the network slicing service in the service chain route involving more domains. In other words, the service provider can earn more profit, even without increasing the overall service cost and impairing the overall performance in the ascending auction mechanism. Furthermore, this internal impact is more obvious in a thin market (i.e.,
Figure 9a), compared with a thick market (i.e.,
Figure 9b). In other words, in a thin market with only 10 users or service providers, the decrease in the user gain is more obvious with the increase in the domain number
K, compared to that in a thick market with 100 users or service providers.
7. Conclusions
For implementing and operating the satellite-terrestrial integrated network, network slicing is adopted as a solution to meet the differentiated service requirements and orchestrate the underlying network infrastructures in a unified manner. To improve resource utilization efficiency and motivate the participation of different service providers, slice admission control is further introduced. However, admission control for multi-domain network slicing becomes much more complex when multi-sided participants are involved and there is no perfect solution to date.
In this paper, a multi-sided auction approach is proposed for modeling multi-domain network slicing admission control as a mechanism design problem. Theoretical analysis shows that the proposed ascending-price auction mechanism is individually rational, strongly budget balanced, and obviously truthful. Numerical experiments based on both real-world and simulated data demonstrate that the ascending-price auction mechanism is asymptotically optimal with the increase in users compared with the optimal trade mechanism.
Some potential future research directions are also considered. The first consideration is a more complex market structures, for example, more than two alternative routes are available, or a single domain may be used within multiple routes. From the user’s perspective, more choices bring more opportunities for using the network slicing service with a lower price. From the service provider’s perspective, both a deeper entangled cooperation relationship among the domains in the same route and a harsh competition relationship among the domains in the different routes exist. More numerical experiments are expected to be designed to evaluate the ascending-price auction mechanism in more complex and realistic settings.
Another consideration is the extension from the bandwidth requirements to more requirements, e.g., transmission delay and energy consumption constraints. Similar constraints have been considered in relevant multi-domain tasks, e.g., network slicing orchestration with impatient tenants [
58] and energy-efficient service function chaining orchestration [
57]. It is worth further consideration to incorporate these factors in the ascending-price auction mechanism, while maintaining the desirable properties.
In addition, some statistical analysis and analysis of variance can be conducted to demonstrate the statistical significance of the performance for the proposed ascending-price auction mechanism in future numerical experiments.