Correcting Errors in Color Image Encryption Algorithm Based on Fault Tolerance Technique
Abstract
:1. Introduction
2. Preliminaries
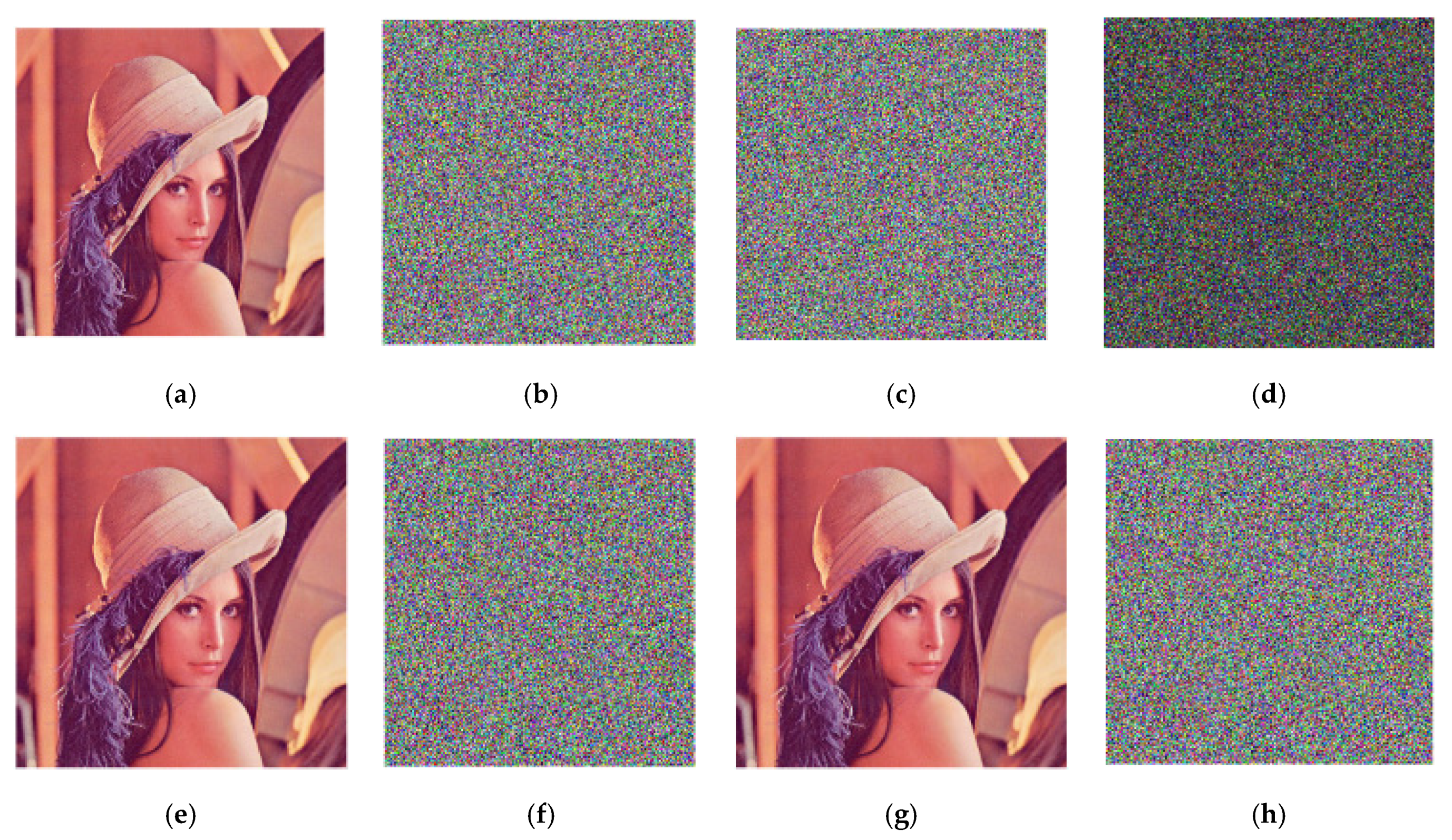
2.1. Fractional-Order Hyperchaotic System
2.2. DNA Encoding
2.3. Fault Tolerance Technique
3. Proposed Cryptosystem
3.1. Synthesis of the Hyperchaptic Sequence
3.2. Pixel Level Encryption
- Organize pixels, bits, and acid bases into a one-dimensional vector V with L = H × W/H × W × 8/H × W × 4.
- Extract a subsequence from with the length of vector V and sort in ascending order to obtain ix, x = 1, 2,…, L.
- A new vector V′ is created by rearranging V according to ix as follows:
3.3. Bit Level Encryption
- Create a subsequence of the chaotic sequence of length L = H
- Reorder the plane p to get p′ by ascending the index sequence ix. x = 1, 2,… L
3.4. DNA Encoding and Level Encryption
3.5. DNA Decoding
3.6. Fault Tolerance
4. Simulation Results
5. Security and Performance Analysis
5.1. Key Size
5.2. Key Sensitivity
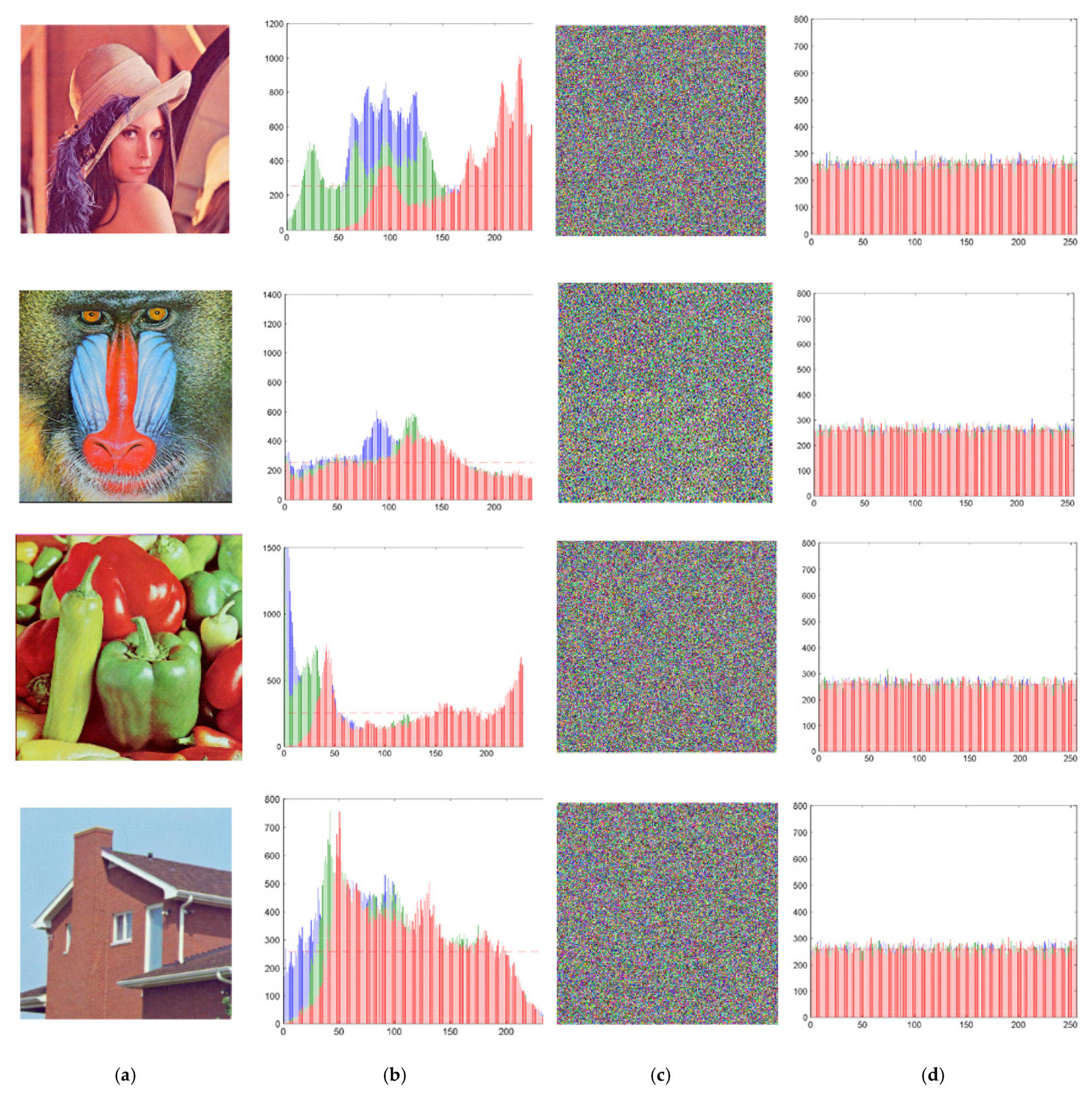
5.3. Histogram Analysis
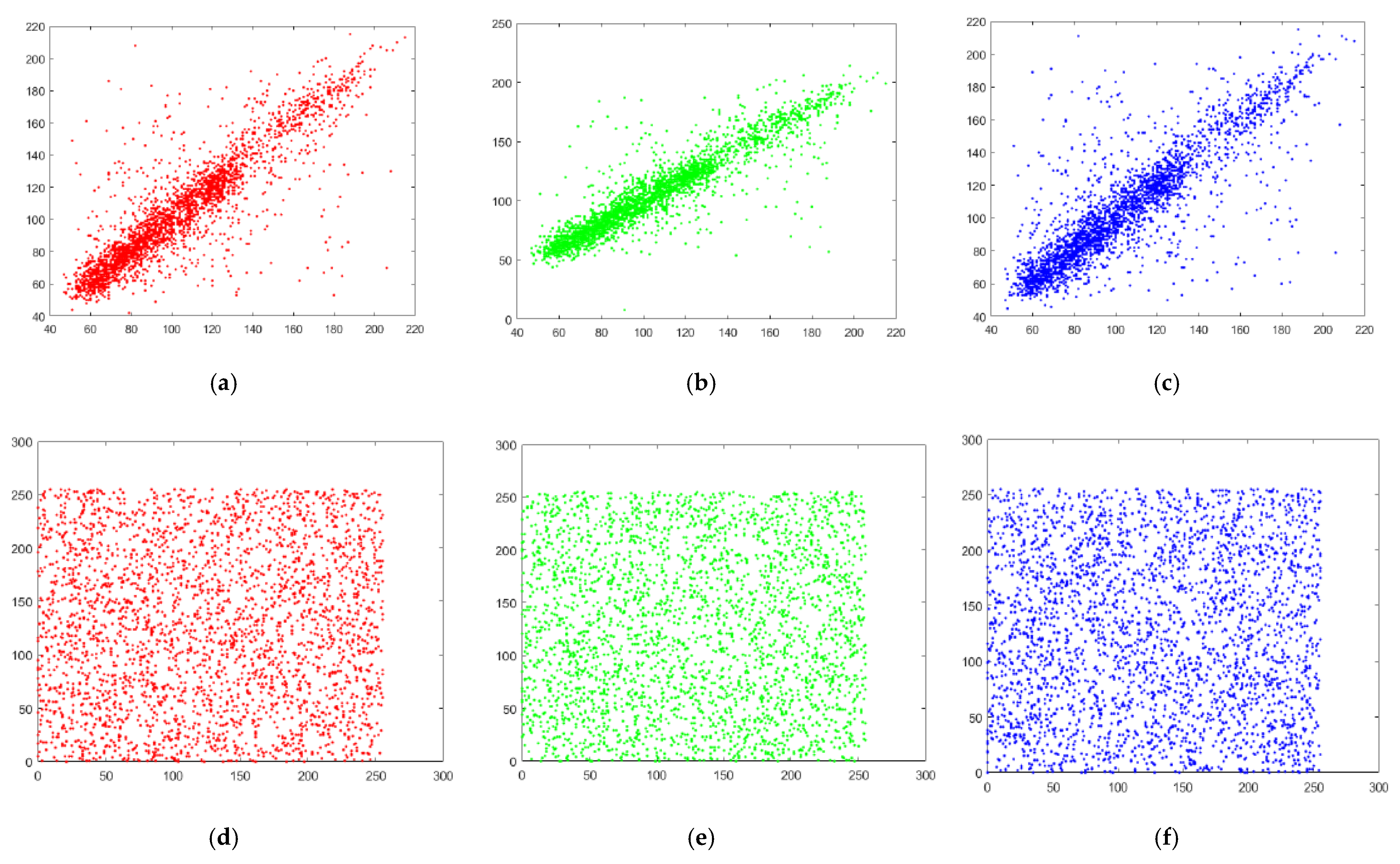
5.4. Correlation Factor Analysis
5.5. Plaintext Senstivity
5.6. Information Entropy
5.7. Data Loss Attacks
5.8. Computational Speed
6. Conclusions
Author Contributions
Funding
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Ding, L.; Ding, Q. A Novel Image Encryption Scheme Based on 2D Fractional Chaotic Map, DWT and 4D Hyper-chaos. Electronics 2020, 9, 1280. [Google Scholar] [CrossRef]
- Dagadu, J.C.; Li, J.; Aboagye, E.O.; Ge, X. Chaotic medical image encryption based on Arnold transformation and pseudorandomly enhanced logistic map. Structure 2017, 4, 8096–8103. [Google Scholar]
- Chai, X.; Bi, J.; Gan, Z.; Liu, X.; Zhang, Y.; Chen, Y. Color image compression and encryption scheme based on compressive sensing and double random encryption strategy. Signal Process. 2020, 176, 107684107684. [Google Scholar] [CrossRef]
- Ding, M.; Jing, F. Digital image encryption algorithm based on improved Arnold transform. In Proceedings of the 2010 International Forum on Information Technology and Applications, Kunming, China, 16–18 July 2010; pp. 174–176. [Google Scholar]
- Hou, W.B.; Wu, C.M. Image encryption and sharing based on Arnold transform. J. Comput. Appl. 2011, 10, 2682–2686. [Google Scholar]
- Lorenz, E. Deterministic Non-period Flows. J. Atmos. Sci. 1972, 20, 130–141. [Google Scholar] [CrossRef] [Green Version]
- Matthews, R. On the derivation of a “chaotic” encryption algorithm. Cryptologia 1989, 13, 29–42. [Google Scholar] [CrossRef]
- Li, Z.; Peng, C.; Li, L.; Zhu, X. A novel plaintext-related image encryption scheme using hyper-chaotic system. Nonliear Dyn. 2018, 94, 1319–1333. [Google Scholar] [CrossRef]
- Zhang, Y. The unified image encryption algorithm based on chaos and cubic S-Box. Inf. Sci. 2018, 450, 361–377. [Google Scholar] [CrossRef]
- Batool, S.I.; Waseem, H.M. A novel image encryption scheme based on Arnold scrambling and Lucas series. Multimed. Tools Appl. 2019, 78, 27611–27637. [Google Scholar] [CrossRef]
- Wang, X.; Çavuşoğlu, Ü.; Kacar, S.; Akgul, A.; Pham, V.-T.; Jafari, S.; Alsaadi, F.E.; Nguyen, X.Q. S-box based image encryption application using a chaotic system without equilibrium. Appl. Sci. 2019, 9, 781. [Google Scholar] [CrossRef] [Green Version]
- Zhang, Y.; Chen, A.; Tang, Y.; Dang, J.; Wang, G. Plaintext-related image encryption algorithm based on perceptron-like network. Inf. Sci. 2020, 526, 180–202. [Google Scholar] [CrossRef]
- Li, Z.; Peng, C.; Tan, W.; Li, L. A Novel Chaos-Based Color Image Encryption Scheme Using Bit-Level Permutation. Symmetry 2020, 12, 1497. [Google Scholar] [CrossRef]
- Podlubny, I.; Petráš, I.; Vinagre, B.M.; O’Leary, P.; Dorčák, Ľ. Analogue realizations of fractional-order controllers. Nonlinear Dyn. 2002, 29, 281–296. [Google Scholar] [CrossRef]
- Wang, Z.; Huang, X.; Li, Y.-X.; Song, X.-N. A new image encryption algorithm based on the fractional-order hyperchaotic Lorenz system. Chin. Phys. B 2013, 22, 010504. [Google Scholar] [CrossRef]
- Wu, X.; Kan, H.; Kurths, J. A new color image encryption scheme based on DNA sequences and multiple improved 1D chaotic maps. Appl. Soft Comput. 2015, 37, 24–39. [Google Scholar] [CrossRef]
- Zhao, J.; Wang, S.; Chang, Y.; Li, X. A novel image encryption scheme based on an improper fractional-order chaotic system. Nonlinear Dyn. 2015, 80, 1721–1729. [Google Scholar] [CrossRef]
- Huang, X.; Sun, T.; Li, Y.; Liang, J. A color image encryption algorithm based on a fractional-order hyperchaotic system. Entropy 2014, 17, 28–38. [Google Scholar] [CrossRef]
- Adleman, L.M. Molecular computation of solutions to combinatorial problems. Science 1994, 266, 1021–1024. [Google Scholar] [CrossRef] [Green Version]
- Gehani, A.; LaBean, T.; Reif, J. DNA-based cryptography. In Aspects of Molecular Computing; Springer: New York, NY, USA, 2003; pp. 167–188. [Google Scholar]
- Wang, X.; Wang, Y.; Zhu, X.; Luo, C. A novel chaotic algorithm for image encryption utilizing one-time pad based on pixel level and DNA level. Opt. Lasers Eng. 2020, 125, 105851. [Google Scholar] [CrossRef]
- Zheng, J.; Luo, Z.; Zeng, Q. An efficient image encryption algorithm based on multi chaotic system and random DNA coding. Multimed. Tools Appl. 2020, 79, 29901–29921. [Google Scholar] [CrossRef]
- Siddartha, B.; Ravikumar, G. An efficient data masking for securing medical data using DNA encoding and chaotic system. Int. J. Electr. Comput. Eng. 2020, 10, 6008–6018. [Google Scholar]
- Wang, T.; Wang, M.H. Hyperchaotic image encryption algorithm based on bit-level permutation and DNA encoding. Opt. Laser Technol. 2020, 132, 106355. [Google Scholar] [CrossRef]
- Zefreh, E.Z. An image encryption scheme based on a hybrid model of DNA computing, chaotic systems and hash functions. Multimed. Tools Appl. 2020, 79, 24993–25022. [Google Scholar] [CrossRef]
- Babaei, A.; Motameni, H.; Enayatifar, R. A new permutation-diffusion-based image encryption technique using cellular automata and DNA sequence. Optik 2020, 203, 164000. [Google Scholar] [CrossRef]
- Zhang, Q.; Liu, L.; Wei, X. Improved algorithm for image encryption based on DNA encoding and multi-chaotic maps. AEU Int. J. Electron. Commun. 2014, 68, 186–192. [Google Scholar] [CrossRef]
- Xie, T.; Liu, Y.; Tang, J. Breaking a novel image fusion encryption algorithm based on DNA sequence operation and hyper-chaotic system. Optik 2014, 125, 7166–7169. [Google Scholar] [CrossRef]
- Liu, Y.; Tang, J.; Xie, T. Cryptanalyzing a RGB image encryption algorithm based on DNA encoding and chaos map. Opt. Laser Technol. 2014, 60, 111–115. [Google Scholar] [CrossRef] [Green Version]
- Patel, J.H.; Fung, L.Y. Concurrent error detection in ALU’s by recomputing with shifted operands. IEEE Trans. Comput. 1982, C-31, 589–595. [Google Scholar] [CrossRef]
- Gulati, R.K.; Reddy, S.M. Concurrent error detection in VLSI array structures. In Proceedings of the IEEE International Conference on Computer Design: VLSI in Computers and Processors, (ICCD), Austin, TX, USA, 7–9 October 1986; pp. 488–491. [Google Scholar]
- Kuhn, R.H. Yield Enchancement by Fault-Tolerant Systolic Arrays in VLSI and Modern Signal Processing; Prentice-Hall: Hoboken, NJ, USA, 1985; pp. 178–184. [Google Scholar]
- Al-Yamani, A.A.; Oh, N.; McCluskey, E.J. Performance Evaluation of Checksum Based ABFT. In Proceedings of the IEEE International Symposium on Defect and Fault Tolerance in VLSI Systems, San Francisco, CA, USA, 24–26 October 2001; p. 461. [Google Scholar]
- Zhang, C.N. Integrated Approach for Fault Tolerance and Digital Signature in RSA. IEEE Proc. Comput. Digit. Tech. 1999, 146, 151–159. [Google Scholar] [CrossRef]
- Lee, N.; Tsai, W. Efficient Fault-tolerant Scheme basd on the RSA system. IEEE Proc. Comput. Digit. Tech. 2003, 150, 17–20. [Google Scholar] [CrossRef]
- Lin, I.-C.; Wang, H.-L. An Improved Digital Signature Scheme with Fault Tolerance in RSA. In Proceedings of the Sixth International Conference on Intelligent Information Hiding and Multimedia Signal Processing, Darmstadt, Germany, 15–17 October 2010. [Google Scholar]
- Acharya, S.; Kotekar, S.; Joshi, S.S.; Shetty, S.; Lobo, S. Implementing Digital Signature based Secured Card System for Online Transactions. Int. J. Comput. Appl. 2013, 65, 27–32. [Google Scholar]
- Elkamchouchi, H.; Mohamed, H.G.; Ahmed, F.; ElKamchouchi, D.H. A Secure Digital Signature Scheme with Fault Tolerance Based on the Improved RSA System. In Proceedings of the Fifth International Conference on Cryptography and Information Security (CRYPIS-2016), Sydney, Australia, 28–29 May 2016; pp. 35–44. [Google Scholar]
- Elkamchouchi, H.; Mohamed, H.G.; Ahmed, F.; ElKamchouchi, D.H. New Secure Proxy Signature Scheme with Fault Tolerance Based on Factoring and Discrete Logarithm. Int. J. Sci. Technol. Res. Eng. (IJSTRE) 2016, 1, 106–113. [Google Scholar]
- Li, Y.; Tang, W.K.S.; Chen, G.R. Generating hyperchaos via state feedback control. Int. J. Bifurc. Chaos Appl. Sci. Eng. 2005, 15, 3367–3375. [Google Scholar] [CrossRef]
- Wang, X.Y.; Wang, M.J. A hyperchaos generated from Lorenz system. Physica 2008, 387, 3751–3758. [Google Scholar] [CrossRef]
- Wang, X.Y.; Song, J.M. Synchronization of the fractional order hyperchaos Lorenz systems with activation feedback control. Commun. Nonlinear Sci. Numer. Simul. 2009, 14, 3351–3357. [Google Scholar] [CrossRef]
- Wang, S.; Wu, R. Dynamic analysis of a 5D fractional order hyperchaotic system. Int. J. Control. Autom. Syst. 2017, 15, 1003–1010. [Google Scholar] [CrossRef]
- He, J.; Yu, S.; Cai, J. A method for image encryption based on fractional-order hyperchaotic systems. J. Appl. Anal. Comput. 2015, 5, 197–209. [Google Scholar]
- Wu, X. A color image encryption algorithm using the fractional-order hyperchaotic systems. In Proceedings of the 5th International Workshop on Chaos-Fractals Theories and Applications, IWCFTA (12), Liaoning, China, 18–21 October 2012; pp. 196–201. [Google Scholar]
- Sebastian, A.; Delson, T. Secure magnetic resonance image transmission and tumor detection techniques. In Proceedings of the 2016 International Conference on Circuit, Power and Computing Technologies (ICCPCT), Nagercoil, India, 18–19 March 2016; pp. 1–5. [Google Scholar]
- Wang, Q.; Zhang, Q.; Zhou, C. A multilevel image encryption algorithm based on chaos and DNA coding. In Proceedings of the 2009 Fourth International on Conference on Bio-Inspired Computing (BICTA 09), Beijing, China, 16–19 October 2009; pp. 70–74. [Google Scholar]
- Zhang, Y.; He, Y.; Li, P.; Wang, X. A new color image encryption scheme based on 2dnlcml system and genetic operations. Opt. Lasers Eng. 2020, 128, 106040. [Google Scholar] [CrossRef]
- Tariq, S.; Khan, M.; Alghafis, A.; Amin, M. A novel hybrid encryption scheme based on chaotic lorenz system and logarithmic key generation. Multimed. Tools Appl. 2020, 79, 23507–23529. [Google Scholar] [CrossRef]
- Alghafis, A.; Munir, N.; Khan, M.; Hussain, I. An encryption scheme based on discrete quantum map and continuous chaotic system. Int. J. Theor. Phys. 2020, 59, 1227–1240. [Google Scholar] [CrossRef]
- Munir, N.; Khan, M.; Wei, Z.; Akgul, A.; Amin, M.; Hussain, I. Circuit implementation of 3d chaotic self-exciting single-disk homopolar dynamo and its application in digital image confidentiality. Wirel. Netw. 2020, 1–18. [Google Scholar] [CrossRef]
- Kang, X.; Guo, Z. A new color image encryption scheme based on dna encoding and spatiotemporal chaotic system. Signal Process. Image Commun. 2020, 80, 115670. [Google Scholar] [CrossRef]




| Rule | DNA Nucleotides | |||
|---|---|---|---|---|
| A | T | G | C | |
| R#1 | 00 | 11 | 01 | 10 |
| R#2 | 00 | 11 | 10 | 01 |
| R#3 | 11 | 00 | 01 | 10 |
| R#4 | 11 | 00 | 10 | 01 |
| R#5 | 10 | 01 | 11 | 00 |
| R#6 | 01 | 10 | 11 | 00 |
| R#7 | 10 | 01 | 00 | 11 |
| R#8 | 01 | 10 | 00 | 11 |
| Images | Size (W × H) |
|---|---|
| Lena | 256 × 256 |
| Baboon | 512 × 512 |
| Peppers | 280 × 270 |
| House | 360 × 344 |
| Correlation Factors | Components | Direction of Adjacent Pixels | ||
|---|---|---|---|---|
| Horizontal | Vertical | Diagonal | ||
| Plain | R | 0.9429 | 0.9741 | 0.9592 |
| G | 0.9352 | 0.9633 | 0.9410 | |
| B | 0.9179 | 0.9504 | 0.9278 | |
| Cipher | R | 0.0085 | 0.0015 | −0.0021 |
| G | −0.0047 | −0.0043 | 0.0035 | |
| B | −0.0013 | 0.0025 | 0.0008 | |
| Algorithm | Direction of Adjacent Pixels | ||
|---|---|---|---|
| Horizontal | Vertical | Diagonal | |
| Proposed | 0.0012 | 0.0009 | −0.0003 |
| [48] | −0.0082 | 0.0118 | −0.0012 |
| [49] | 0.0019 | 0.0014 | −0.0028 |
| [50] | 0.0032 | 0.0015 | −0.0018 |
| [51] | −0.0022 | −0.0010 | 0.0005 |
| [52] | −0.0031 | 0.0027 | 0.00011 |
| Images | NPCR (%) | UACI (%) | ||||
|---|---|---|---|---|---|---|
| R | G | B | R | G | B | |
| Lena | 99.6243 | 99.6173 | 99.6292 | 33.4932 | 33.5781 | 33.6019 |
| Baboon | 99.6182 | 99.6191 | 99.6023 | 33.5354 | 33.4995 | 33.9971 |
| Peppers | 99.6205 | 99.6301 | 99.6183 | 33.6009 | 33.6053 | 33.4982 |
| House | 99.6394 | 99.6297 | 99.6136 | 33.9737 | 33.5864 | 33.8654 |
| Algorithms | Average NPCR | Average UACI |
|---|---|---|
| Proposed | 99.6387 | 33.5498 |
| [48] | 99.6051 | 33.4294 |
| [49] | 99.6218 | 33.4809 |
| [50] | 99.6164 | 33.4650 |
| [51] | 99.2975 | 33.4999 |
| [52] | 99.1507 | 33.4380 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mohamed, H.G.; Alrowais, F.; ElKamchouchi, D.H. Correcting Errors in Color Image Encryption Algorithm Based on Fault Tolerance Technique. Electronics 2021, 10, 2890. https://doi.org/10.3390/electronics10232890
Mohamed HG, Alrowais F, ElKamchouchi DH. Correcting Errors in Color Image Encryption Algorithm Based on Fault Tolerance Technique. Electronics. 2021; 10(23):2890. https://doi.org/10.3390/electronics10232890
Chicago/Turabian StyleMohamed, Heba G., Fadwa Alrowais, and Dalia H. ElKamchouchi. 2021. "Correcting Errors in Color Image Encryption Algorithm Based on Fault Tolerance Technique" Electronics 10, no. 23: 2890. https://doi.org/10.3390/electronics10232890
APA StyleMohamed, H. G., Alrowais, F., & ElKamchouchi, D. H. (2021). Correcting Errors in Color Image Encryption Algorithm Based on Fault Tolerance Technique. Electronics, 10(23), 2890. https://doi.org/10.3390/electronics10232890






