1. Introduction
The rise and staying power of the Islamic State of Iraq and Syria (ISIS) created enormous regional instability that survives after its territorial collapse. Although ISIS’s predecessor Al-Queda in Iraq (AQI) presented a threat as a traditional insurgency, ISIS operates in an entirely different manner. Terming ISIS an insurgency is difficult because they functioned openly. Likewise, explanations that ISIS is a messianic religious cult or some form of mafia discounts how ISIS governed and looked to establish civic institutions in territory it controlled. So, what was ISIS? What strategies can contain or defeat it? Can the ISIS phenomena replicate elsewhere and under what conditions?
This paper proposes a new theory of a non-state actor, called an emerging-state actor, and presents the dynamic hypothesis that ISIS is a case-study of this type of actor. Emerging-state actors operate in fundamentally different modes than other non-state actors like insurgents or terrorists and this difference helps explain the rapid growth of ISIS and why other insurgencies might shift to this mode of conflict in the future. The theory of emerging-state actors is located within an existing framework of non-state actors. We develop a dynamic hypothesis of an emerging-state actor through a series of logical statements connected in a causal-loop diagram. Confidence is built in the theory through experiments on the propositions of the dynamic hypothesis. These experiments leverage a detailed system dynamics simulation called the Emerging-State Actor Model (E-SAM) [
1]. (Please see
Supplementary Materials for full model documentation.) The paper finishes with a conclusion that summarizes the insights, discusses limitations, and identifies future opportunities for research with the emerging-state actor theory as well as the simulation model created for this effort.
2. Problem Description
In 2003 AQI appeared as a potent threat to the stability of Iraq. The strength of AQI peaked in 2006 before declining as the result of three circumstances: a troop surge of United States (U.S.) Forces, a Sunni-Shia civil war that AQI helped spark, and the indigenous resistance to AQI growing out of the Anbar Awakening. In 2013 ISIS seized Ar-Raqqah, a medium sized city in eastern Syria with an estimated 13,200 militants. By late 2014, ISIS had grown to between 50,000–80,000 militants strong, taken control of thirty per cent of the territory in Syria and Iraq, and threatened regional stability. It took the joint intervention of over five different international forces, of which the US led-coalition was just one, plus the joint militaries and local militias of Syria and Iraq to remove ISIS from the territory it held. The rapid growth of ISIS and its staying power created a problem in the study of insurgencies and how to contain them. How did ISIS grow so quickly between 2013 and 2014? What made ISIS so difficult to confront? What would have happened had the foreign interventions not occurred?
3. Literature Review
Immediately after 9/11 and through the beginning of the Iraq War research focused on the individual-as-terrorist. Atran and Taylor both wrote on the psychological conditions by which someone becomes a suicide-terrorist [
2,
3]. This reflected the circumstances of the time. From 2001–2003 the Taliban were in retreat and the insurgency in Iraq had not yet materialized. Even as the Iraq insurgency began demanding more attention, high profile terrorist attacks in Madrid and London continued to drive a focus on research around individuals. Works by Sageman and Hoffman contrasted whether the process of radicalization for such attackers was a bottom-up (“swarm”) or a top-down (“fisherman”) and what role foreign-terrorist organizations played in threats to the homeland [
3].
As insurgency morphed into civil war in Iraq old theories and new tactics were being intermingled on the ground by military commanders working side-by-side with theorists. A key advisor to the US military, David Kilcullen, made a case in 2009 for a shift in methods for studying irregular conflict. While acknowledging the benefits of “stakeholder analysis, nodal analysis or link analysis” [
4] (loc. 3281) as popular tools of the time—he argued that systems theory and tools which analyzed systems as a whole might provide better insights [
4] (loc. 3233).
System dynamics is one such method of numerically simulating complex systems. Unfortunately, there are only a handful of quantitative system dynamic efforts dealing with insurgencies or irregular warfare in the manner described by Kilcullen. Khalid Saeed conducted an early multi-polar examination of conditions that give rise to internal violence in developing economies was in 1983. The paper analyzed how social and political factors influenced long term growth. Instability in the form of dissidence and subversive activities were modeled, but not explicitly as a violent insurgency or with resources becoming controlled by the dissidents [
5]. In 2010 Turnley et al., specifically modeled an irregular warfare environment enabling a computational representation of the interdependence between kinetic and non-kinetic aspects of a battlefield. The model highlights the interaction of latent structure as it is affected by kinetic activity, but Turnley does not model the organization of the insurgency itself as a key factor in the dynamics of how it operates [
6].
In an infamous case a model produced within the military on insurgent dynamics was leaked and misreported on by the New York Times which mistook it for a power-point slide [
7]. Although that model was never formally published, portions of it were leaked. What appears to be an appendix explaining many of the causal loops in the “spaghetti diagram” surfaced as well. While it is a sophisticated approach to understanding the causal interactions between dynamic factors of an insurgency, it is not clear that the model is simulatable. Nor is there enough detail in the leaked documents to replicate the model or articulate its key insights. A thirty page appendix with a high-level overview is attributed to Brett Pierson, a military Captain at the time, but has a “PA Consulting” copyright mark on it [
8]. Due to the leaked nature and copyright we didn’t incorporate elements of this model in creating E-SAM.
In 2011 Anderson used actual data from the Anglo–Irish War of 1919–1921 to model insurgency and counterinsurgency theories showing potential gaps in the theory when compared to simulation results. However, the IRA was never able to seize and hold territory with this approach and may not best represent the dynamics of an actor like ISIS which seizes territory to the exclusion of all other actors [
9].
In 2013 Saeed et al. developed a generic structure to model political conflict which could include insurgencies [
10]. The model, like Turnley, focuses on decision-making and choices of the population rather than the explicit structure of how an insurgency like ISIS might operate.
In 2014 Aamir presented a paper on modeling terrorist organizations using existing system dynamic models of business entities. However, except for Attacks and Agency the models Aamir used were from existing system dynamics literature on business models, built generically, rather than aiming to model the performance of any one insurgent group [
11].
This paper seeks to build upon the work of this existing literature by proposing a dynamic hypothesis that ISIS is a new form of insurgency created by an “emerging-state” actor. In this effort we will adopt Turnley’s approach of using U.S. military definition of terms, the aspects of modeling ISIS as a firm or state from Aamir and pay close attention to the causal mechanisms (financing, recruiting, gaining equipment) that allows ISIS to operate and achieve its goals missing from the theoretical structure of Anderson and the generic structure of Saeed. The model makes explicit internal organizational processes such as financial budgeting, personnel management. Also modeled are the crucial feedback loops between state and non-state actor discussed by Saeed.
My contribution to the literature in this paper is the theory of an emerging-state actor, that ISIS is such an actor and the testable propositions of what constitutes such an actor. I test the propositions of the emerging-state actor theory in simulation experiments to see whether they are valid within the context of the model boundaries and build confidence in those boundaries. Finally, I have contributed a detailed simulation model in E-SAM that can simulate the performance of a wide variety of unconventional conflicts between state and non-state actors. Military planners or research analysts can use E-SAM for planning or analysis. The model contains a combat simulator configurable by scenarios to represent different terrain and types of environments as well as starting conditions [
12]. The model serves as a platform for conducting a portfolio of policy tests to understand the behavior of an emerging-state actor versus an insurgent non-state actor or clandestine terrorist network—but as well conduct policy tests on interventions against such actors. It has organizational structure and internal decision-making processes for actors missing from earlier work. For example, state and non-state actors can have essential, non-essential and overseas expenditures. The priority given to distributing available funds based on current and perceived reserves reflects loose or tight monetary controls which affect actor performance and can drive declines as actors have to deal with scarce resources and insufficient funding (See
Supplementary Materials Section A-4.6 Revenue & Expenses for more details on simulating actor’s finances.) Likewise organizational transparency—the ability of “ground truth” to reach higher levels of leadership—is modeled through perception structures to represent more transparent, or opaque, organizational designs. Current perception can result in more aggressive or conservative allocation of fighting forces that could be reacting inaccurately to “fog of war” or delayed information (See
Supplementary Materials Section A-5.6 Territory Dynamics for more details on how perception of momentum is structured
.). This allows for different organizational styles to be numerically represented and tested with plausible fidelity [
1]. The model is fully published in the
Supplementary Materials and replicable. The level of aggregation remains at the level of state, emerging-state and non-state actors. It does not reach deep into individual motivations of the kind discussed by Atran, Taylor, Sageman and Hoffman—but instead focuses on aggregate causes and dynamic. In addition to state and non-state actions, this also includes ethnographic groups and their selection of sides to offer support, or resistance, to the actors.
4. Hypothesis Development: What is the Islamic State of Iraq and Syria?
Developing a hypothesis that ISIS was an emerging-state actor first requires identifying the existing perspectives on terrorism, insurgencies and irregular warfare then locating ISIS within this typology of non-state actors. Part of that effort involves making explicit the modeling boundaries and problem slices. This section concludes with the proposed hypothesis of ISIS as an emerging state actor [
13].
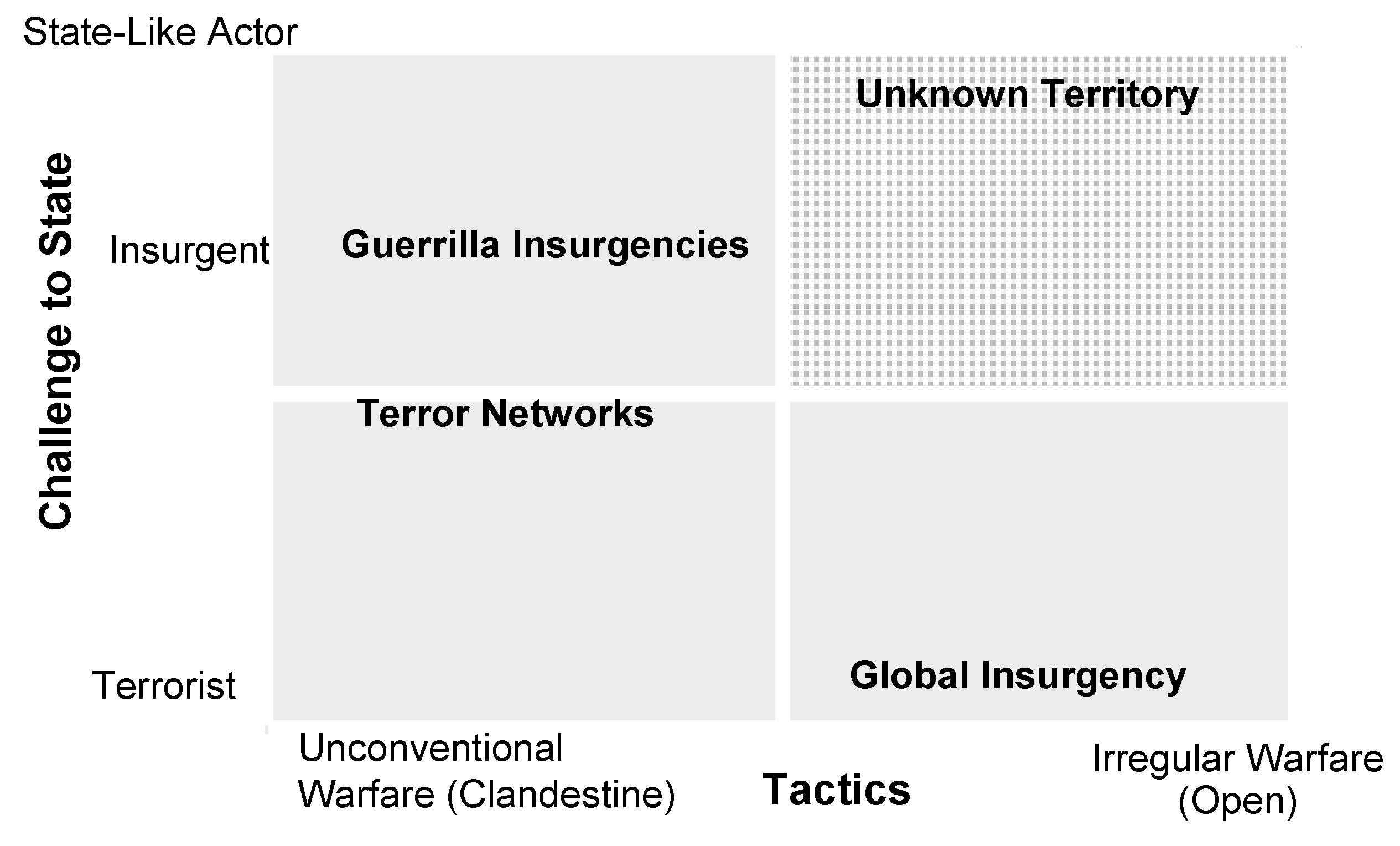
Existing terms often do not distinguish between tactics used by a non-state actor and threat to the state by a non-state actor. The two figures below,
Figure 1 and
Figure 2, both stand for continuums along axes. Beginning with “tactics”, a continuum of the methods of operations employed in furthering an agenda by non-state actors can be notionally established using terms and definitions from the U.S. Military. In
Figure 2, at the left of the continuum, are non-state actors who seek to achieve their agenda through unconventional warfare defined as “…operating through or with an underground, auxiliary, and guerrilla force in a denied area” [
14] (p. 261)
On the right side of the continuum are those non-state actors who further their agenda through a “…violent struggle among state and non-state actors for legitimacy and influence over the relevant population(s),” [
14] (p. 125), the key distinction being to what extent the non-state actors are operating in a clandestine or more open fashion and seeking legitimacy over the local population. The continuum ends at irregular warfare excluding conventional full-spectrum operations and nuclear war as being beyond the reach of non-state actors.
Figure 2, “Threat to the state”, represents the extent to which the agenda of a non-state actor represents an existential threat to the survival and continuance of a state. Agendas which seek change in government policy, release of prisoners, or financial demands are fundamentally different from agendas with goals to remove or replace current leadership or violently overthrow the state itself. Kilcullen distinguishes between “terrorist” and “insurgent” based on the question of how much of a threat to the state the non-state actor poses. He describes how in “Western popular culture the conception of terrorism became that of disembodied cells of radicalized, nihilistic individuals [who]…could not and did not tap into a mass base that drew its legitimacy from popular grievances, as traditional insurgents” [
4] (loc. 3123). But many insurgencies, Kilcullen continues, especially those of the 21st Century, operate in a conflict where the insurgents “challenge the state by making it impossible for the government to perform its functions, or by usurping those functions—most commonly, local-level political legitimacy; the rule of law; monopoly on the use of force; taxation; control of movement; and regulation of the economy” [
4] (loc. 2529). So, insurgencies differ from terrorism in their intent of challenging the state, however most insurgencies still operate in a clandestine fashion. This is because an insurgency does not yet have a monopoly on the activities within the territory they occupy, so the non-state actor can neither operate nor govern openly. This territorial control leading to open-governing distinction is vital amongst the non-state actors. Once an insurgency controls territory to the exclusion of any other force establishes enforcement of law, commerce, and social activity, they have evolved to something more than an insurgency. In 2007 the United States military published the Joint Operating Concept on Irregular Warfare to guide future joint force commanders on a wide variety of types of irregular warfare. The Joint Operating Concept briefly treats this concept of insurgencies acting in sovereign fashion in a footnote “[s]tate-like adversaries refer to non-traditional adversaries that have evolved to the point of attaining state-like power, authority, and influence over a population” and later acknowledging that “these adaptive actors may possess some of the power of states and adopt state-like structures” [
6]. This final definition allows the creation of a vertical continuum of the threat to the state. At the bottom, small groups of individuals pursue policy change but have little chance of disrupting state function. In the middle, an insurgency begins to threaten the governing of a state by disrupting the means to do so. At the top, an insurgency has begun to capture territory and govern openly becoming a state-like actor. The only difference at that point remaining from a state-like actor and a state is international recognition. Using the defined horizontal and vertical axes, non-state actors are now plottable based on where they fall on both continuums, as illustrated in
Figure 3.
Further segmentation can be arrived at by illustratively separating the graph into four quadrants representing the four natural distinctions of a two-axis arrangement as: high-challenge to the state with unconventional means, high challenge to the state with irregular warfare means, low challenge to the state with unconventional means, and so on. Existing terms can define three of the four quadrants.
It is worth noting that “Guerrilla Insurgencies” do not top the “challenge to state” axis. It follows logically that meeting the definition of a state-like actor would require the guerrilla insurgency to abandon clandestine or underground methods characteristic of unconventional warfare and begin operating in the open. Therefore, as a guerrilla insurgency gains territory and begins governing, it shifts to the right upper quadrant currently named “Unknown Territory”. The actors who occupy this space are those who conduct irregular warfare and yet present a threat to the state of equal or higher magnitude than guerilla insurgencies. Defining the characteristics of this “unknown territory” quadrant occurs below.
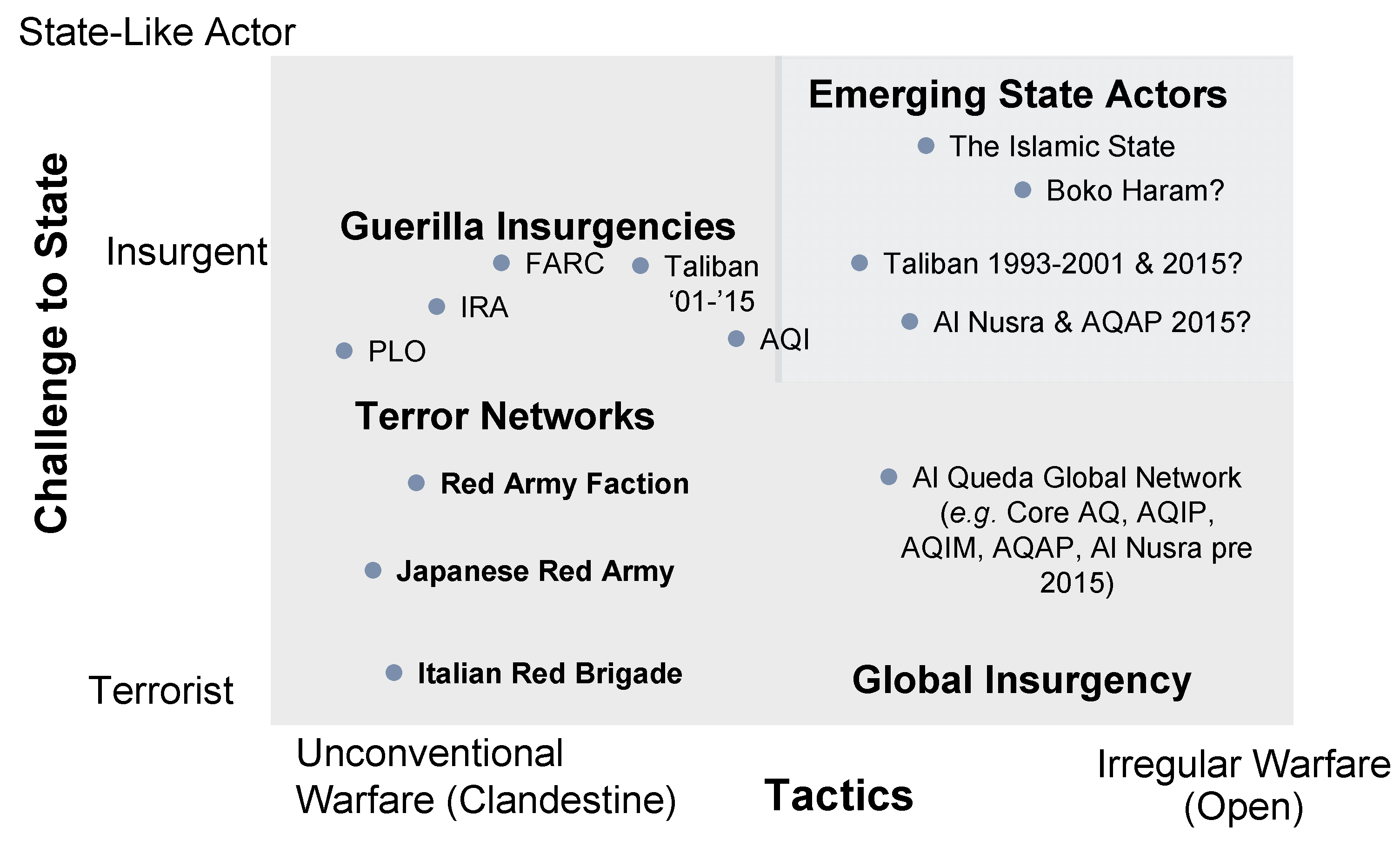
First, we must trace the path of ISIS’s history and shifting modes of operation. Before 2003 what would become AQI operated as at best a terrorist network of cells, the lower left quadrant. From 2003–2013 as AQI operated as an insurgency in the upper left quadrant threatening various governments conducting attacks, gaining criminal revenues all from within clandestine networks hidden within the population. However, AQI never openly governed any population. With the capture of Ar-Rakkah in 2013 this mode shifted from clandestine to open territorial seizure—moving to the highest point on the vertical scale. ISIS no longer sought to just deny governmental functions to the states (Syria and Iraq), but through the seizure of territory and establishment of governance create their own state. Although ISIS continued its clandestine methods, it also began attacking in the open with uniformed troops and marked vehicles. This was more a form of irregular than unconventional war. Because of this shift in approach and end goals, ISIS at this time was better located in the upper-right quadrant and deserving of a term representative of insurgencies that govern openly and no longer execute solely unconventional operations but embrace all aspects of irregular warfare. As ISIS set up courts of law, collected taxes, established government services, and enforced social norms the group began operating as a “state-like” actor, and given its rise might be better termed “emerging-state” or “proto-state” actor. Indeed, the qualities of an “emerging-state” actor fit well within the upper right portion of the previously established quadrant. Locating ISIS in this space along with illustratively placing other non-state actor groups, the graph now appears as in
Figure 4.
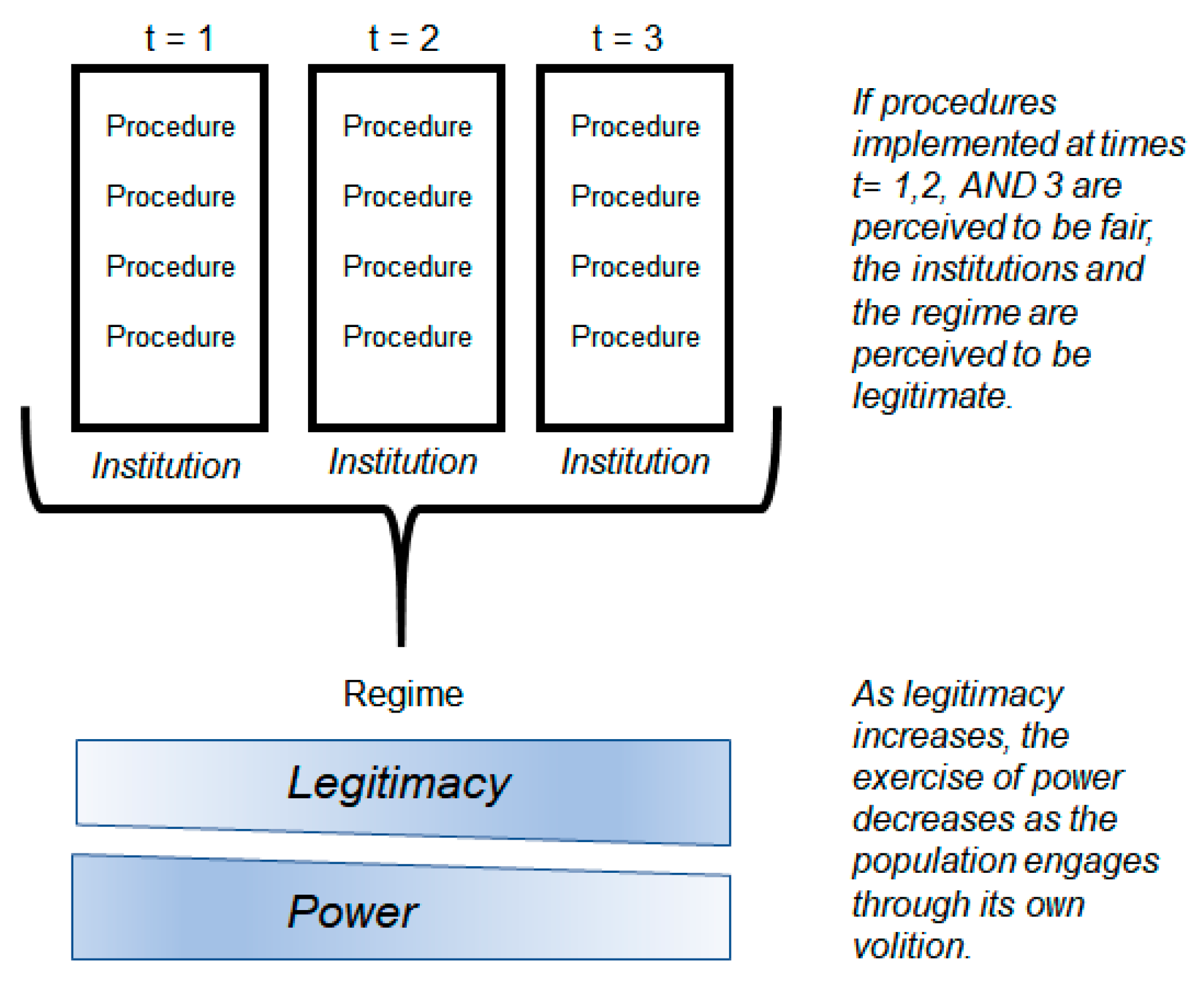
This structure now provides a shaping context for the discussion of “what is ISIS” and a point of alignment in the modeling effort: the amount of relevant population under some form of control by ISIS. From Turnley, two forms of control over a population are the control through coercive power and control through government via legitimacy. Coercive power results from the exercise of “coercion and reward” and is “particularistic as it is support for a specific action or specific person, not for an institution or a system of government.” Coercive power is more resource intensive as it “requires the investment… to induce compliance whenever necessary” [
6] (p. 37). Legitimacy is a form of power that relies on the function of procedures that the governed considers fair established with credibility over time. Unlike coercive power used to ensure compliance, control by others is replaced by self-control, which socially is a much cheaper way to ensure social order” [
6] (pp. 38–40). Turnley illustrates the transitioning distribution of a population controlled through coercive power and governed through legitimacy with a diagram presented as
Figure 5.
Institutions created at times t1, t2 and t3, each deploya series of procedures to execute their purpose. As each actor deploys a procedure and its perceived as “fair”, the amount of power (coercive power) decreases as legitimacy (governed through legitimacy) increases. Additionally, the succession of credible and fair institutions also decreases the amount of power needed versus legitimacy. This means legitimacy is a function of the successful execution of each process as well as the accumulation over time of the repetition of successful execution. Likewise, the length of time it takes to transition a population from control through coercive power to legitimacy determines the overall resources required to govern that population. A middle-stage, lying between Coercion and legitimacy, identified by Hurd in 1999, is a stage of “self-interest.” Or, calculated legitimacy lying between Coercion and legitimacy. The difference between Coercion and calculated legitimacy as described by Hurd: “is that an application of coercion leaves the coerced actor worse off than it was beforehand…whereas a self-interest perspective sees the actor as better off than it would be taking any other available path” [
15] (p. 386). The in-between state more accurately captures some of the complex patronage relationships where out of purely self-interested ethnographic groups will temporarily align with the local power, but quickly remove that alignment if their interests diverge. In summary, by creating credible institutional procedures replicated over time provisioning both punishments and services any state-actor will affect the distribution of a target ethnographic group among Coerced, calculated legitimacy and Governed that indicates along a continuum the extent of external-threat vs. self-restraint that is necessary to achieve compliance of that population to the state.
5. Modeling Boundaries and Approach
Prior to creating a simulation model, the proposed theory benefits from development as logical arguments. In system dynamics these logical structures are visual and explicit with causal loop diagrams (CLD) that distill into to a key feedback loops the hypothesis of what is generating the proposed behavior. From this CLD, the construction of a detailed simulation model proceeds. However, since models can never truly represent reality, boundary selections confine the work to a reasonable scope. Reasonable boundaries for proposed hypothesis can be selected through a “slicing approach” to complex systems as advocated by Saeed in 1992 [
16]. In complex systems modes of behavior can exist in time, geography (both a geography of “terrain” and a geography of ”things”), and simultaneous modes. In this paper the complex system is “sliced” as described in
Table 1. (See
Supplementary Materials Section B-2 Boundary Adequacy for additional commentary on boundary selection validity.)
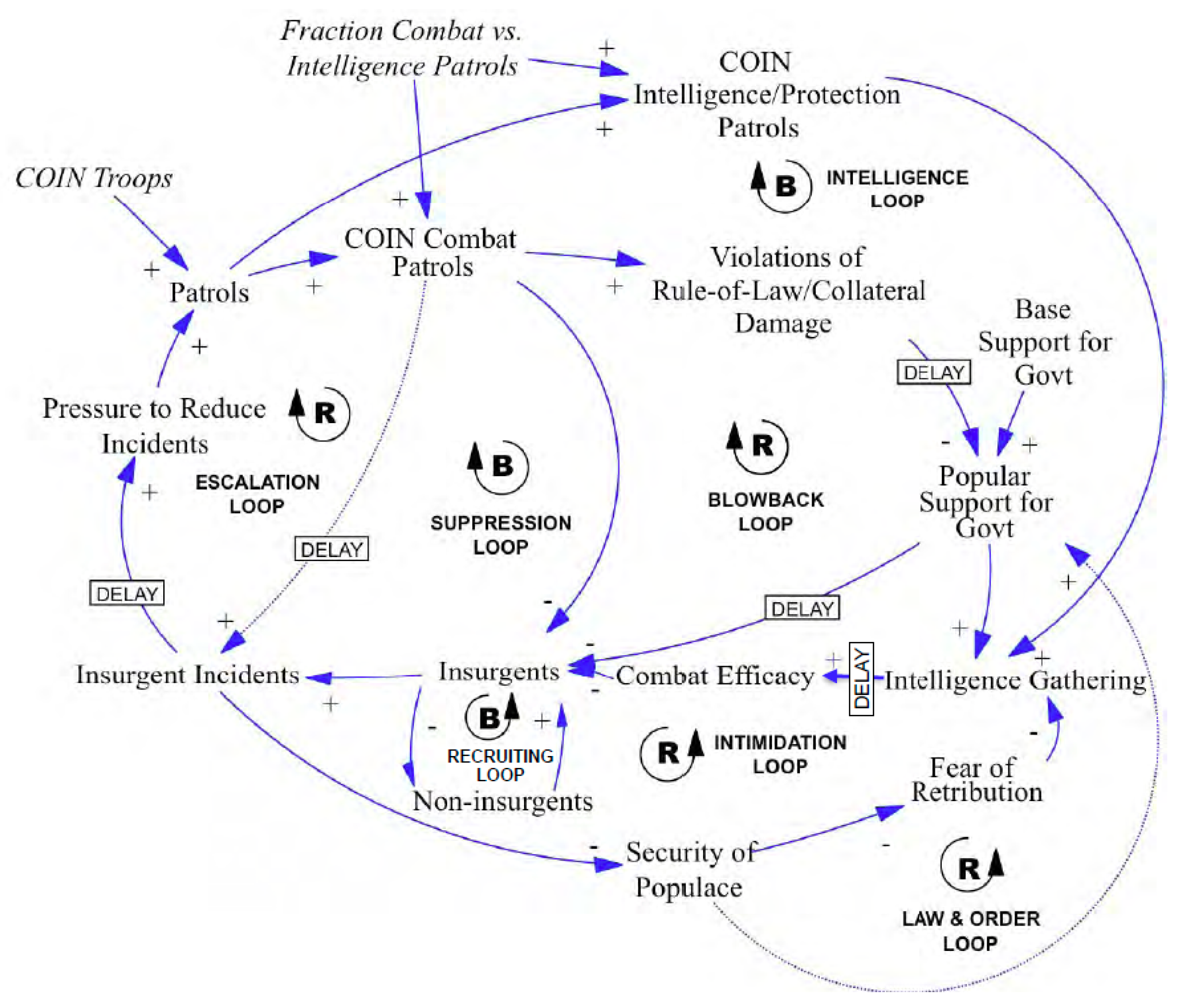
6. Hypothesis Design through Causal Loop Analysis
Few existing causal loop structures for insurgencies are in the literature. Because the models used by Aamir were already extant, he did not provide an integrated causal loop structure [
11] (p. 8). In their “Farmers, Bandits, and Soldiers” model Saeed et al., likewise did not depict a causal loop diagram [
10]. Only in Anderson’s paper was a causal loop diagram of his theoretical construct created, as depicted in
Figure 6 [
9] (p. 8).
Anderson’s model struggles to examine ISIS and other emerging state actors using irregular warfare. This is because Anderson’s model is built on the premise that insurgents are fighting a “classic” insurgency following O’Neill’s definition that largely confines insurgents to operating in a guerrilla manner, e.g., “raids, ambushes, bombings, etc.” [
9] (p. 3). This is consistent with the Joint Forces definition of unconventional warfare of “operating through or with an underground, auxiliary, and guerrilla force in a denied area” [
14] (p. 261). This does not comport with behavior that is state-like, nor defined above as emerging-state behavior.
Causal loop diagrams can aid in demonstrating transition states between phases already identified: clandestine terror networks, insurgencies and emerging-state actors. An can operate in all three phases to greater or lesser degrees within the same systems. But the differences between an actor acting predominantly in one aspect or another manifest in the theory of emerging-state actor behavior and performance. These differences are testable in the simulation model for validation against the hypothesis that ISIS is an emerging state actor.
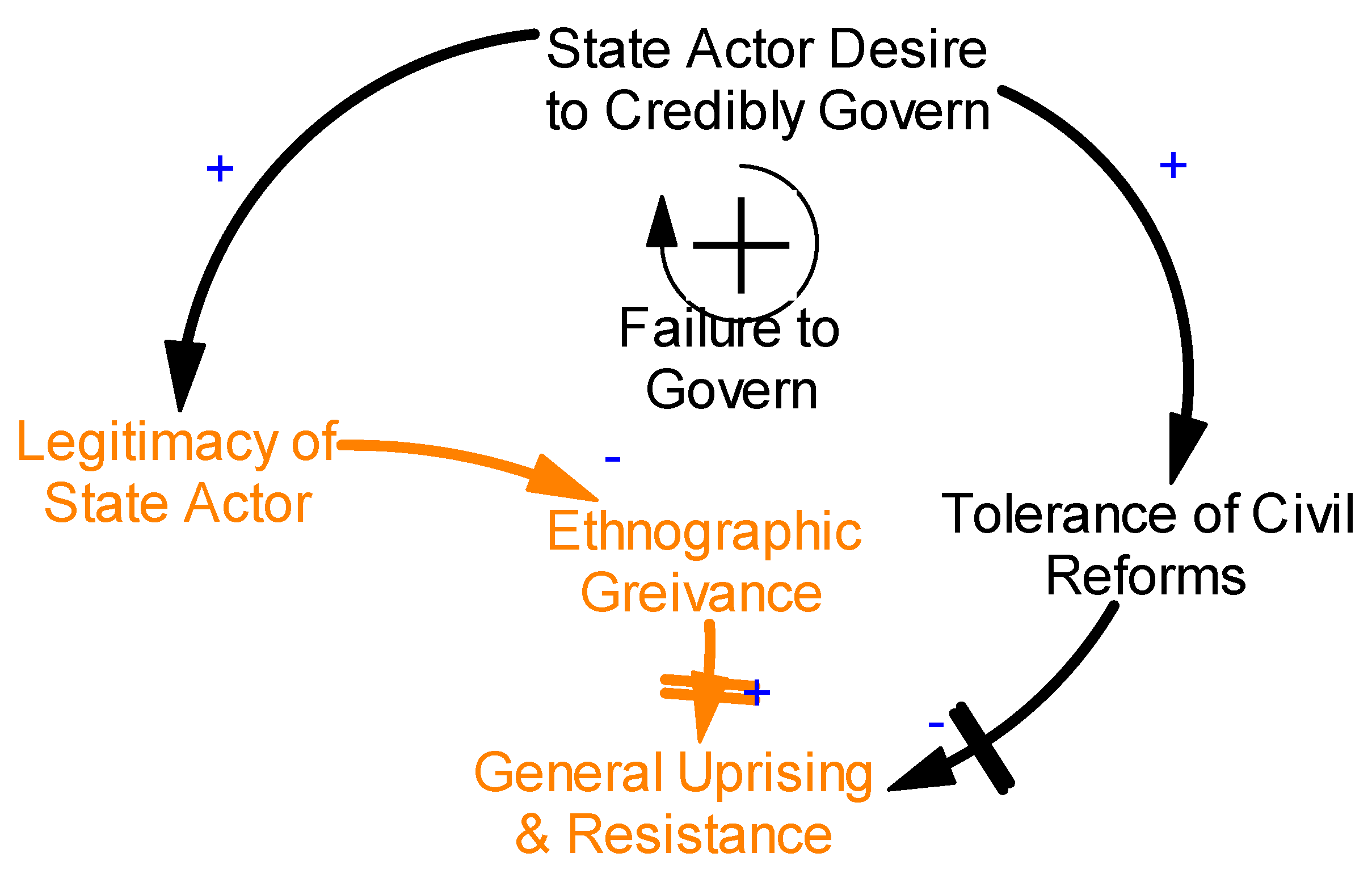
This paper proposes that this cycle begins with a state actor and the desire to credibly govern a specific ethnographic group. The higher that desire, the higher the legitimacy of the state actor within that ethnographic group. This desire also exhibits a tolerance of civil reforms. This means when grievances do arise—resolution can occur through less-than-violent means. However, if a state actor has a low desire to credibly govern, this decreases their legitimacy to the ethnographic group, increasing grievance, and the unwillingness to allow civil reforms leads over time to general uprising and resistance.
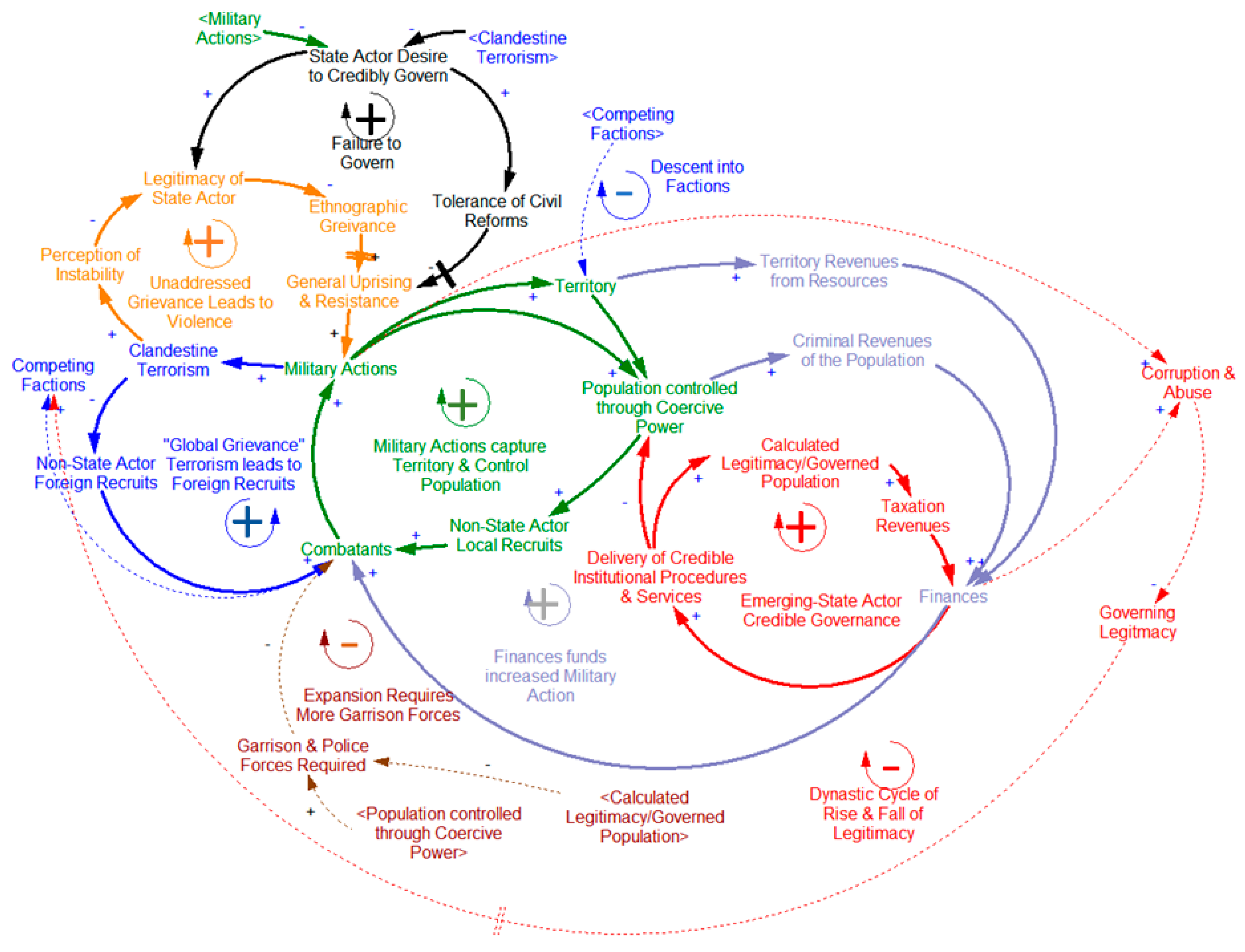
Figure 7 depicts this initial stage below.
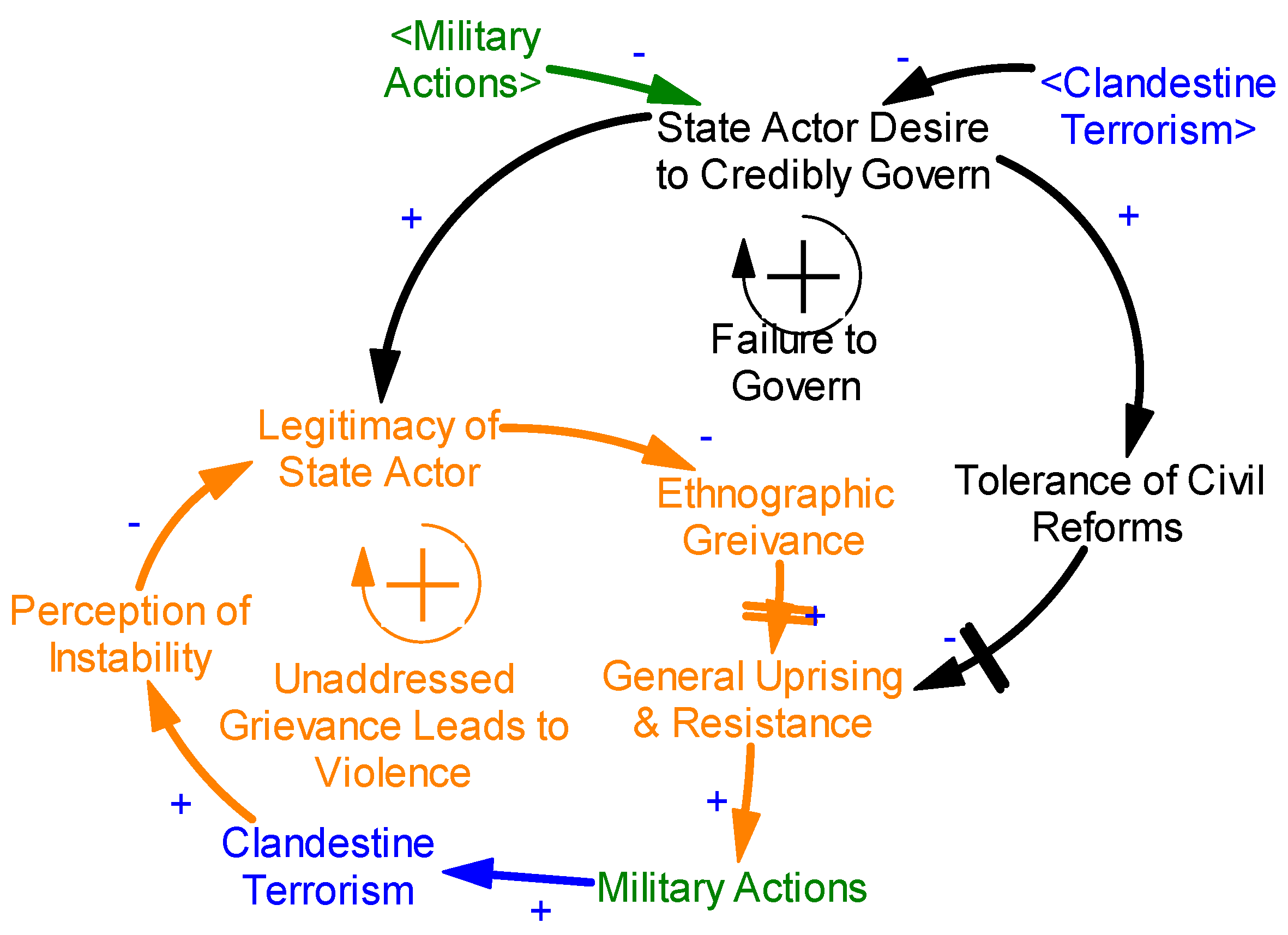
If the State still refuses participation in civil reforms, the General Uprising and Resistance will manifest at the extremes as military actions of which clandestine terrorism will be the first. This is the Clandestine Terrorist Network stage where the first two positive feedback loops emerge as shown in
Figure 8.
In this stage the extremists use clandestine terrorism to target the population or the government. This increases a perception of instability within the targeted population that weakens the legitimacy of government perceived as being unable to control the violence. Simultaneously, the state actor desire to credibly govern the targeted ethnographic group often declines in response to the violence of terrorism and other military actions. This cycle can exist for a great deal of time and never evolve past this stage. But if it does it is because the military actions performed by extremists within the general uprising and resistance begin to focus on recruiting into organized formal groups. These groups begin to exert a shadow-influence on the population—gaining support from some and intimidating others. Criminal activities gain finances which fund further military actions. This is when a clandestine terror stage morphs into an insurgency stage of conflict as shown in
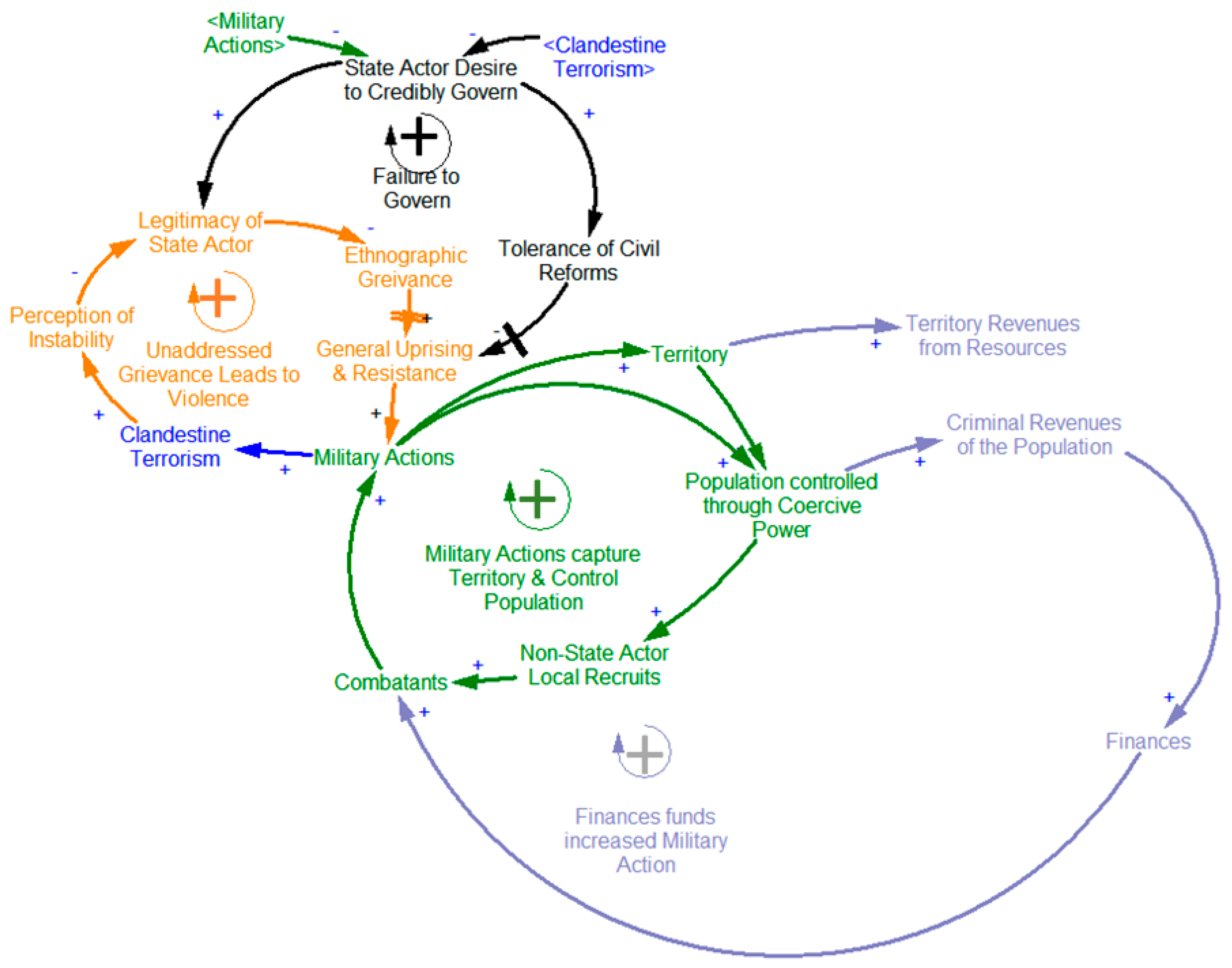
Figure 9.
The logic of an insurgent is to leverage the local legitimate grievances of an ethnographic group and leverage that into finances and manpower to conduct violence against the state. This adds two more positive feedback loops to the existing. As local grievances increase, so do militants, and if local grievances were to decrease, militants and their actions would also decrease. This is illustrative of the importance of resolving local grievances, through political reform and changing the desire of the State to credibly govern, as a sustained approach to ending an insurgency over time [
4] (loc. 173–199). These could be criminal activities targeting populations that are not aligned with the insurgents such as ransoms, extortion, reselling of stolen property, looting, and selling of blood-antiquities (stolen historical artifacts). Criminal activities also include activities which are illegal globally but tolerated locally such as the illegal drug trade. Finally, criminal revenues include informal taxation schemas that bear more resemblance to extortion than a formal state levied tax. These funds increase non-state actor insurgent’s finances, allowing them to support and pay more combatants. Logically, a sustained reduction in local grievances through reconciliation, ability to gain finances, or reduction of combatants through military action all hold the potential to reduce the reinforcing feedback effect that powers the classic non-state actor insurgent, especially when applied in combination. The means of these reductions are accessible both to the State and to a lesser degree the local ethnography.
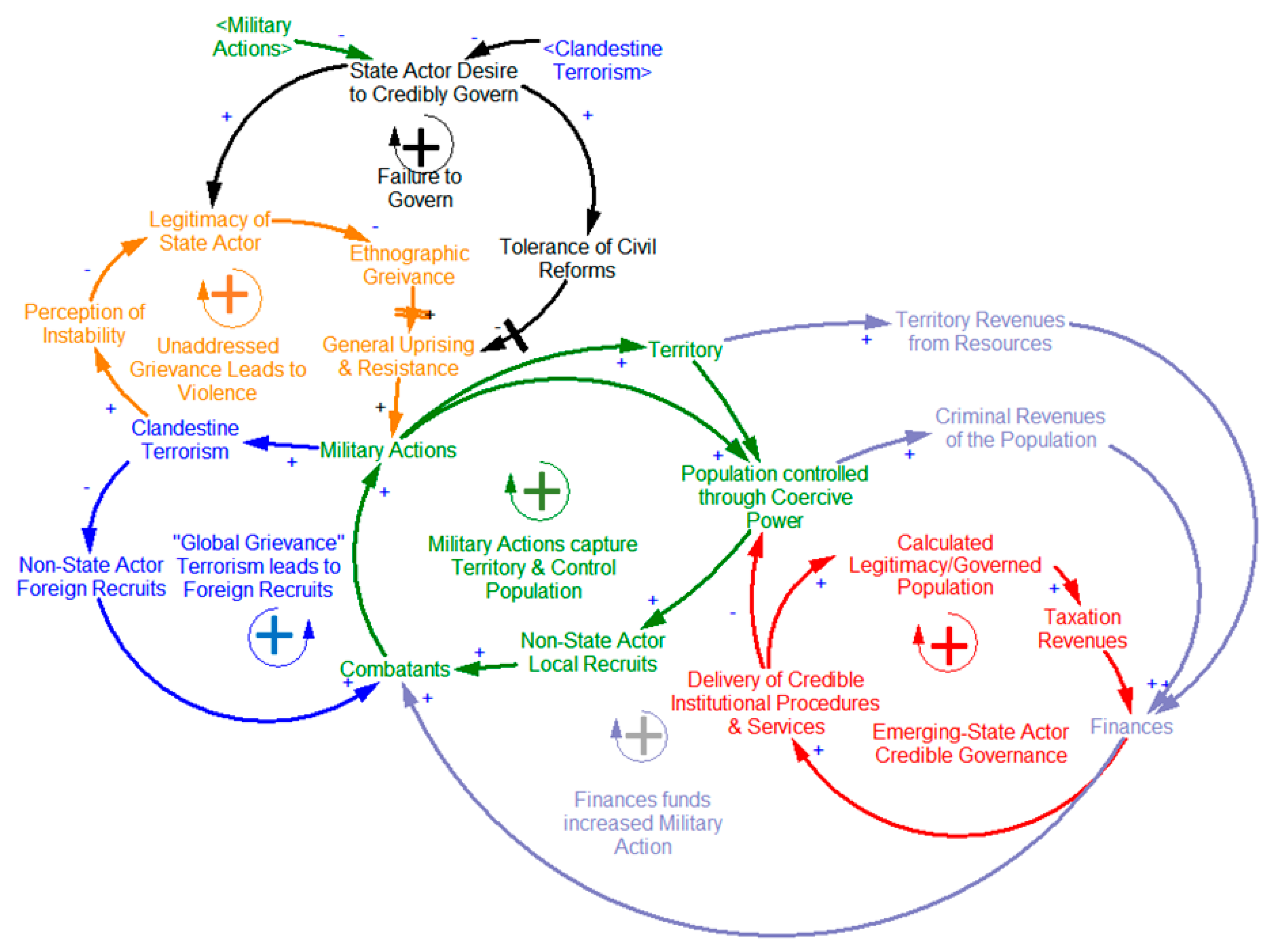
The first difference with the emerging state actor CLD is the input of non-local grievances that bring foreign recruits to an area. These militants align to the local grievances at first, but a reduction in local grievances will not result in a reduction of foreign intervention since those grievances are non-local. The second difference is that military actions in this model not only terrify or intimidate populations, but also seizes territory. This territory then enables an additional feedback loop of “territorial revenues” from land-intensive resources to activate. Control of territory allows a non-state actor to control the resource extractions that occur in that territory. These territorial revenues require coordination of workers and leveraging infrastructure, and they are difficult to secure when an insurgency operates in a classical clandestine manner. In Afghanistan the Taliban took advantage of opium farming, while in Nigeria Boko Haram helps fund itself through oil while in Columbia the Revolutionary Armed Forces of Colombia (FARC) exploited the production of cocaine. For ISIS, the territorial revenue is oil located in the territories they seize. These additional financial inputs produced from lucrative, fungible, globalized trade charge the reinforcing feedback loop that runs through finances to obtain more militants, conduct more military actions and thus gain more territory.
Seizing territory opens another powerful feedback loop of enabling non-state actors to begin governing the population. This creates the processes by which coercive power shift to calculated legitimacy and legitimate governing power. Populations controlled through legitimacy are less resource intensive to control since the population “self-controls” and allows taxation of normal commerce and individuals. The shift to legitimacy also feeds back on itself. The more people governed through legitimacy, the easier collecting finances through taxation, which fund local governance mechanisms. These local governance mechanisms can provide the services that only a sovereign state actor can provide: law enforcement, judicial proceedings, building infrastructure, social services, and other government services that may have been lacking in the area.
When we add these aspects to our existing CLD structure, three loops emerge: seizure of territory, control of population through legitimacy, and foreign recruiting by playing on global grievances.
Figure 10 depicts the larger CLD.
The summary of emerging state actor theory to this point is:
- (1)
A failure of governance by the state-actor and inability to tolerate civil reforms decreases legitimacy, increases grievance and leads to general uprising and resistance.
- (2)
This resistance manifests first in the form of clandestine terrorism which increases the perception of instability, further decreasing the legitimacy of the state. Likewise, violent acts reduce incentives of the state actor to credibly govern the ethnographic group from within which these actions emerge.
- (3)
Local grievances create militants who join a local non-state actor or bring one in from afar.
- (4)
The non-state actor uses militants and finances to conduct military actions.
- (5)
As the non-state actor increases the controlled population, it begins extracting coercive revenues through criminal activities and recruiting locally from within this population.
- (6)
Within its territory, the non-state actor attempts to monopolize the use of force, taxation, control of movement, and regulation of the economy. By operating in a sovereign manner, the non-state actor shifts to an emerging state actor.
- (7)
Coercive revenues and territorial revenues finance governing mechanisms which can begin building legitimacy to shift the controlled population into a governed population.
- (8)
As the emerging-state actor gains a governed population, it also gains taxation revenue and increases its draw of non-local foreign recruits by propagandizing its non-local grievances, which may or may not align to local grievances.
- (9)
The loops complete into a positive feedback loop of exponential growth. More militants mean more military actions, which means more territory and access to controlled populations, which become governed, fueling finances, which fund more militants and military actions.
The shift from a classic non-state actor insurgency to an emerging-state actor, in this sequence, begins at Step 6 and completes in Step 7. Described in another way, for a non-state actor to become an emerging-state actor it must at some point:
- (A)
Control territory to the exclusion of all other state actors.
- (B)
Seek to govern that territory in an open manner that creates legitimacy.
In the case of ISIS’s predecessor AQI, the group was able to reach Step 5 and partially Step 6. Even though AQI certainly influenced a population and extracted criminal revenues from them, AQI was never able to meet the two criteria above to complete the transition from insurgency to emerging-state actor. In this formulation, an emerging-state actor are a foregone conclusion once militants enter the system. Additional balancing loops complete the CLD by representing various limits to growth.
Figure 11 depicts these loops.
These are endogenous limits on the emerging-state actor which even absent external pressure, can and will engage to slow down or reverse the growth over time. The “Expansion Requires More Garrison Forces” loop activates as an emerging-state actor controls more population—requiring more forces to garrison than population to prevent uprisings against their rule. This reduces the number of combatants available to gain more territory. Furthermore, the force ratios for garrisoning a population controlled through coercive power are higher, ranging from 8:1 to as high as 55:1 than the ratios necessary to police a population, ~2.8:1, governed through legitimacy. This loop can also act in the same way the “Failure to Govern” loop does for the state actor, starting a general uprising against the emerging-state actor. Another negative feedback loop in the emerging-state actor theory is “Descent into Factions”. ISIS owes its existence to the activation of this loop within Al-Queda as a previous incarnation split from the global terrorist network in 2013. A third negative feedback loop, the “Dynastic Cycle” loop begins with the corruption and abuse of arbitrary power available to a state, similar to Katouzian’s theory of arbitrary state and society [
17] (p. 7). These abuses erode governing by legitimacy, feeding both the Uprising and Resistance loop and the Descent into Factions loop. However, Descent into Factions and the Dynastic Cycle loops have significant delay functions and therefore may develop well after an emerging-state actor has established itself. As modeled by Langarudi, the Katouzian dynastic cycle can take decades to manifest [
17] (pp. 10–16). The Afghanistan Taliban, as an emerging-state actor, maintained its governing legitimacy despite widespread abuses until the post-9/11 U.S. invasion in 2001. The attached E-SAM has all these balancing loops modeled numerically so the conditions for their activation are testable.
The emerging-state actor theory can help explain not only the rise of ISIS in 2013, but the collapse of AQI forces in 2006–2007. The inability of AQI to establish institutions and processes with which to govern legitimately meant it relied only on coercive and often abusive power. This activated the “Expansion Requires More Garrison Forces” negative feedback loop from local fighters. Beginning in the Anbar Awakening of 2006, followed soon thereafter with an U.S. troop surge AQI faced local-opposition fighters. AQI as a classical insurgent could not sustain itself in that environment. A lesson perhaps learned by its members and carried forward into the new incarnation of ISIS.
7. Hypothesis That Islamic State of Iraq and Syria Is an Emerging State Actor
Based on the previous theoretical development, I propose the following dynamic hypothesis: the Islamic State (ISIS) is an emerging-state actor, which uses methods of irregular warfare to capture territory to influence populations (“coercive power”), which it then attempts to govern in furtherance of its objective to become a functioning state (“legitimate power”). I recognize that although the term for this category might be new in this application, the behavior and model is not, as other actors, such as the Taliban in Afghanistan and Hezbollah in Lebanon have taken this route as indicated by the segmentation.
To test the hypothesis, I created a simulation model of sufficient detail to test the propositions of the emerging-state actor theory and the hypothesis that ISIS is an emerging-state actor. The model consists of two sections: a strategic architecture of both the state government named the “Green Actor” and ISIS, named the “Red Actor.” The strategic architecture identifies the resources and capabilities that determine performance at any point in time. The second section is a World Model within which these two Actors compete against one another over control of a variety of ethnographic groups and with varying degrees of foreign intervention. This strategy-dynamics approach to modeling recognizes that these resources accumulate or deplete driven by flow-rates and the changes in the resource [
18]. Sub-systems representing the constants, parameters, information flow, and leadership decisions, behaviors and side-choosing of ethnographic groups, as well as the influence of other resource levels, all combine to affect the rates of change. Reinforcing and balancing feedback interactions between these resources can explain the dynamics of strategic performance.
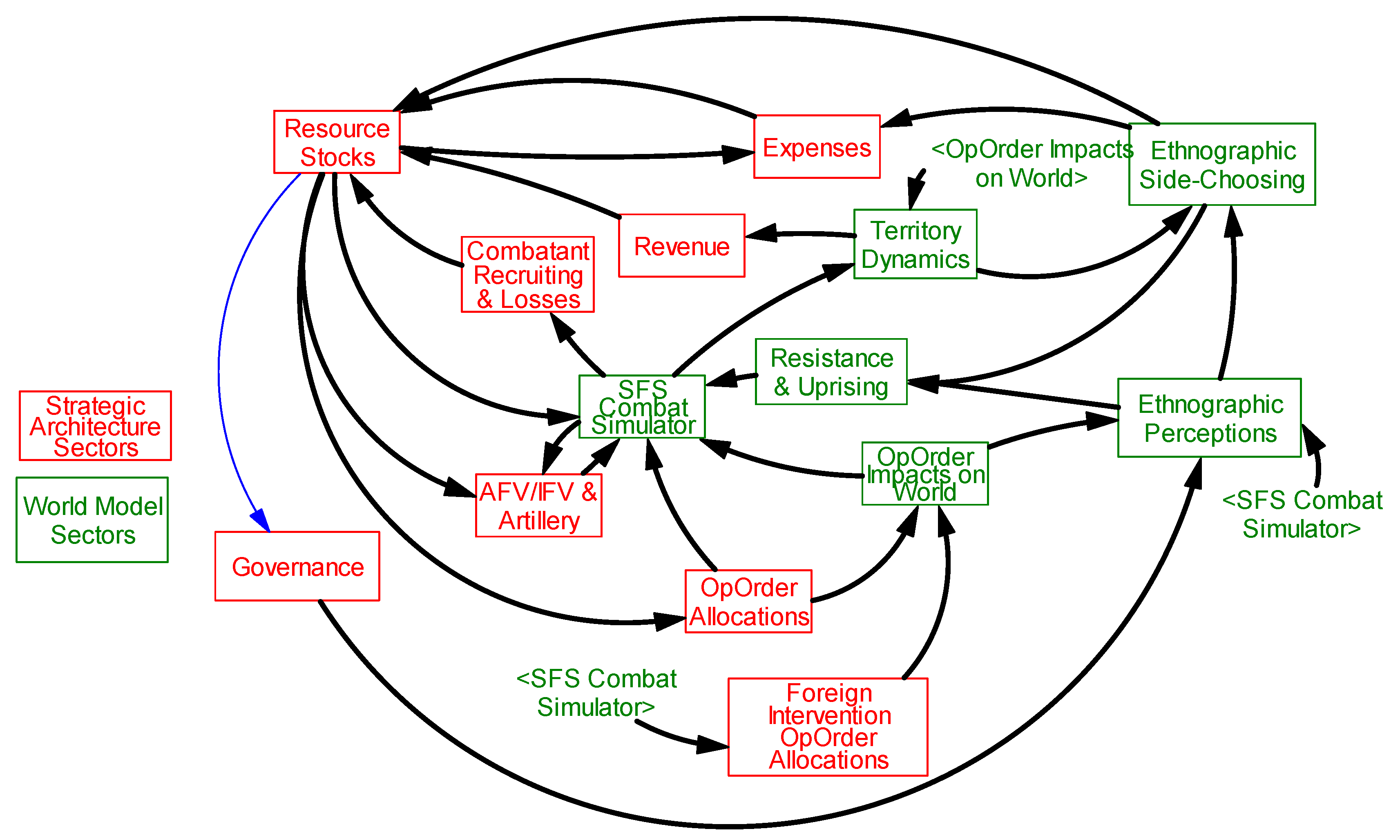
Figure 12 shows the aggregate strategic architecture in sectors alongside world model sectors.
The strategic architecture, sectors marked in red, represents the resources, capabilities, and skills of each the Green and Red Actor. The world model, sectors marked in green, defines the “environment” within which subsystems interact.
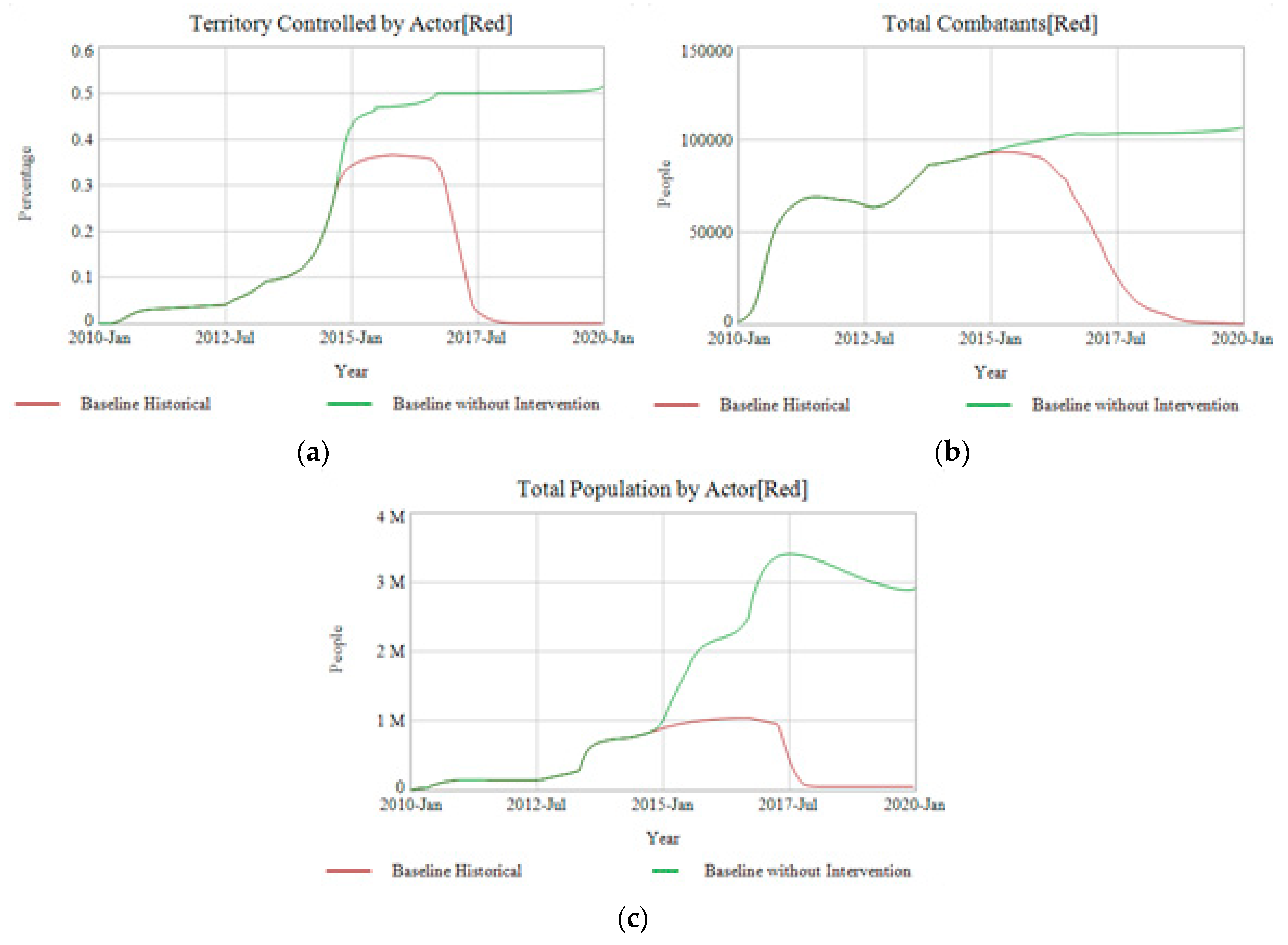
Two simulations seek to replicate the conditions in Syria and Iraq beginning in 2010, the grievances of the Arab Suuni’s that led to the rise and expansion of ISIS. The Baseline Historical scenario then includes the significant foreign interventions that occurred beginning in 2014. The Baseline without Intervention takes a counter-factual that this intervention never occurred and projects what might have occurred with ISIS absent foreign involvement. When simulated in this fashion the Baseline Historical replicates sufficiently, though not exactly, the rise of ISIS through stages of clandestine terrorism, insurgency and emerging-state actor. It also charts the decline and collapse of ISIS under pressure of foreign interventions and increasing coordinated activities against it on multiple fronts.
Figure 13 charts three primary measures-of-effectiveness of the Red Actor: Territory Controlled, Total Combatants, and Population for the Baseline Historical.
The Baseline Historical simulation successfully replicates the behavior mode on which the dynamic hypothesis is based as well as the early growth and resilience of ISIS.
Figure 14 then compares the Historical Baseline with the Baseline without Intervention to demonstrate that E-SAM can produce substantially different behaviors.
In
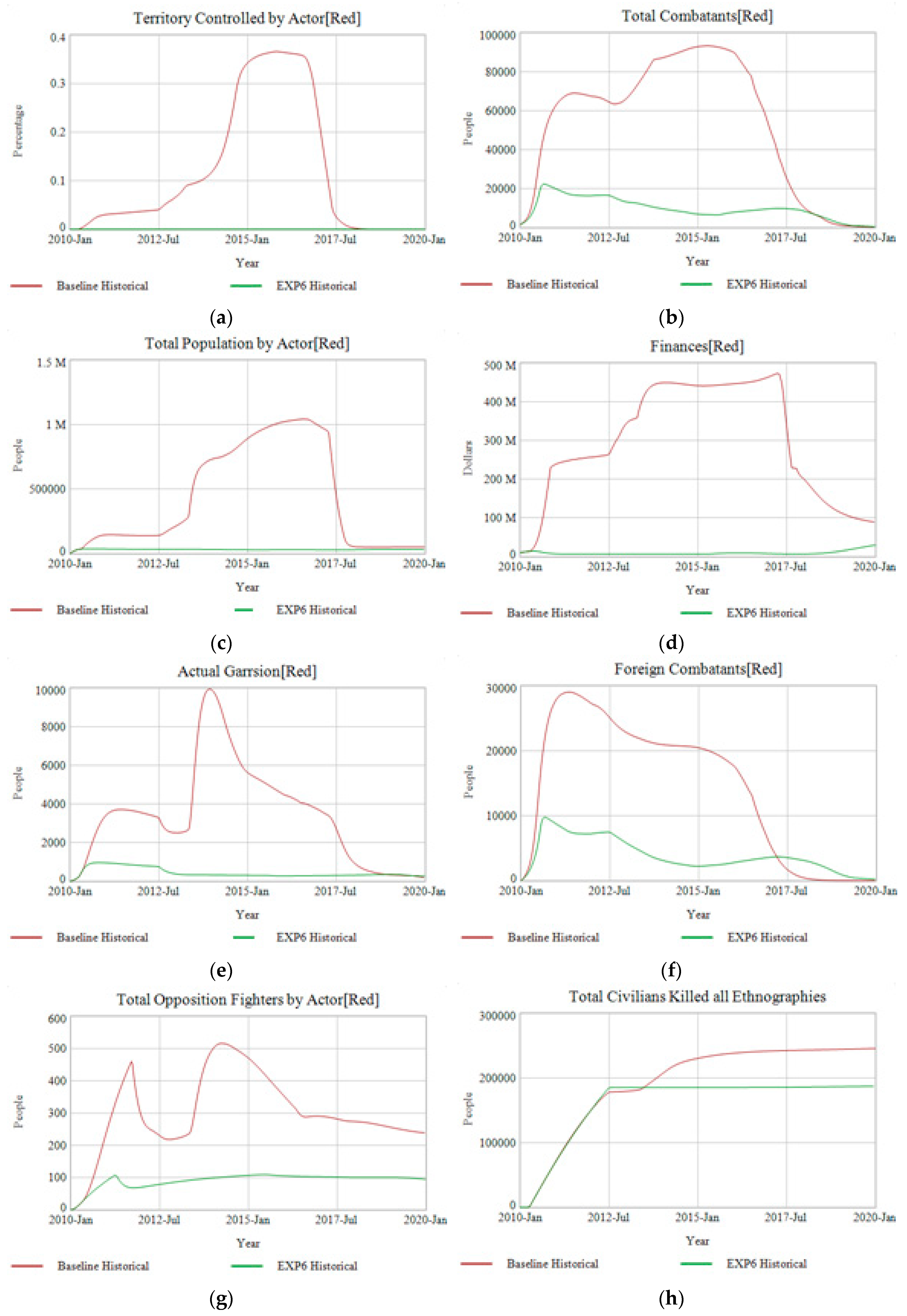
Figure 15 below a “Dashboard of Performance” compares results from both scenarios across a wide variety of measures.
In the Baseline Historical, the defeat of ISIS (Red Actor) results from a combination of measures. The growth of its population requires an increasing amount of Garrison troops just as foreign intervention begins increasing and fewer Foreign Combatants are arriving. In the Baseline without Intervention ISIS reaches an “outer envelope” of expansion at about ~60% of available territory. Three factors create this limit. First the Green Actor opposition to ISIS becomes heaviest as they reach the strongly defended cities of Aleppo, Baghdad, Kirkuk etc. Second, the territories on which ISIS must fight to gain that next incremental amount of territory consists of densely packed urban areas that are not as favorable to its style of fighting. Third, the ethnographic makeup of the population in the territory conquered shifts away from ISIS’s favor, reducing their ability to recruit local militants. What was once a 9:1 ratio of local to foreign militants drops to 1:1. This activates the Resistance and Uprising limit to growth negative loop identified in the CLD. Even though by converting their populations to governed over time, reducing the rate at which opposition fighters accumulate, the aggregate external and internal threats mean “just staying still” for ISIS is not sufficient. The emerging-state actor must continue recruiting locally and from abroad to hold onto what they have. ISIS has reached its limit to growth—at least for the remainder of the simulation duration.
8. Experimentation to Test the Hypothesis
Having formed a logical construct of the hypothesis and its simulated baseline, it is worth returning to the proposed dynamic hypothesis: the Islamic State (ISIS) is an emerging-state actor which is using methods of irregular warfare to capture territory in order to influence populations (“coercive power”) which it then attempts to govern in furtherance of its objective to become a functioning state (“legitimate power”). Testing this hypothesis requires experimentation via simulation. Six propositions emerge from the dynamic hypothesis. Propositions 1–5 are individual experiments where a simulation is run ceteris paribus with the only change being the stated formulation change to the subject proposition. Significantly worse experimental performance from baseline indicates potential validity of the proposition within the boundaries of the model, e.g., without this element ISIS would have performed much worse. These propositions are:
- (1)
The emerging-state actor must take and hold territory.
- (2)
That territory must have valuable resources on it that the emerging-state actor can exploit.
- (3)
Transition of a coerced population to legitimacy cannot take too long for an emerging-state actor.
- (4)
The emerging-state actor must be able to exploit local grievances to attract local recruits.
- (5)
The emerging-state actor must also be able to attract foreign recruits.
- (6)
Can a classical insurgency perform as well as the baseline observed in the ISIS case? (Combine experiments #1 and #3.)
Where appropriate, contingencies in each proposition are tested to identify the boundaries of validity, such as the value of the underlying resource or the time the transition to legitimacy may take. The full list of experiments and formulation changes are included in the
Supplementary Materials. (See
Supplementary Materials Section D-7 Experiment Test Parameters & Results.)
These tests are against the Baseline Historical and Baseline without Intervention. The results of these tests and final values against four measures compared to the two baseline scenarios are in in
Table 2.
The evidence for Experiment 1 and 2a indicates that an emerging-state actor must take both territory and have some valuable resource upon that territory to fund expansion beyond ~20,000 Total Combatants, the upper size of most insurgencies. However, the contingency tests of 2b and 2c indicate that the resource need not be all that valuable relative to the expenses of maintaining the emerging-state actor. ISIS still grows just as strongly when black market oil sells for
$22/barrel (bbl) and
$11/bbl respectively vs.
$45/bbl. The reason why is the path-dependency of the positive feedback loops identified in emerging-state actor systems above in
Figure 11. Once ISIS has reached a tipping point of sufficient population in either calculated legitimacy or Governed, the territorial based resource revenues become less important as they can rely on population-based taxation.
Experiments 3a–d confirm that using government services and credible institutional procedures is important to maximize growth. But as with territorial resources, there are contingencies. When ISIS is willing to credibly govern at 75% or even 50% they perform well in terms of maximum expansion and combatants. However, at below 50% desire to credibly govern ISIS’s performance significantly drops. Part of the reason they still have so many Combatants at max is that their territorial expansion is so limited—they have not provoked a major response from Iraq or Syria. Like an insurgency in a remote region that the government leaves alone for the most part.
Experiments 4 and 5 confirm that both local recruiting and foreign recruiting are essential. Although it may not be surprising that local recruiting is essential, the significant difference foreign recruiting makes in comparing Proposition 5 performance to the Baseline is noteworthy.
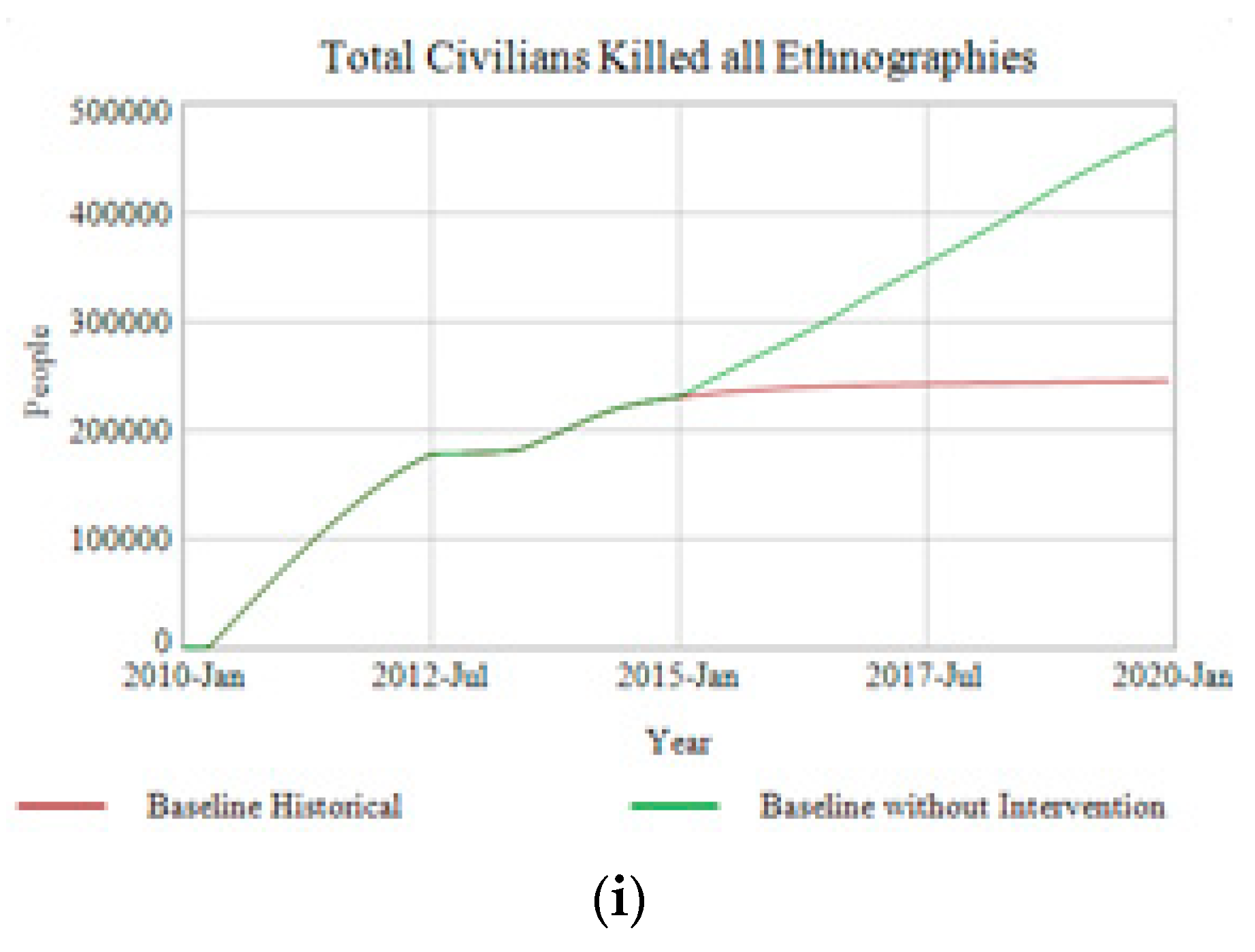
The final experiment, simulating a “classical insurgency” (EXP6 Historical) removes two key elements of emerging-state theory, the seizure of territory and open governance. This allows a comparison of ISIS as an insurgency versus ISIS as an emerging-state actor (Baseline Historical) in
Figure 16.
In both simulations ISIS begins gaining combatants quickly but ISIS as an insurgency-quickly stalls out and begins a general decline. As it never seizes territory the “insurgency” does not present an obvious target for military offensives as the emerging-state actor ISIS does. It still contains a great deal of lethal capacity as seen in the Total Civilians Killed all Ethnographies, but the key chart is in the bottom right—which charts the calculated legitimacy an Actor presents to ethnographies. Whereas ISIS acting in the fashion of an emerging-actor can generate this form of strategic side-choosing at least among Sunni Arabs, ISIS as an insurgency never gains even this limited form of legitimacy from the population. The insurgency ISIS dwindles away to end up in similar straits as the emerging-state actor version, but never having obtained the massive success and ability to create a worldwide brand. It is possible that AQI suffered a scenario such as this in 2006 when it rapidly gained coercive control of a population of nearly one million civilians but was unable to openly seize territory in its area of influence nor transition to an open system of governance due to the requirements to remain clandestine due to the presence of US forces. AQI also showed little interest in even a show of providing services. All lessons learned by its successor ISIS.
How do we know that these results are not just reflective of the terrain on which an insurgency arises? That emerging-state actor behavior favors deserts but would fare better, or worse, in mountains or rougher terrains. This is testable because the combat-simulator in E-SAM tracks the “Terrain Type” on which conflict occurs with values representing Open, Mixed, Rough, Urban and Mountainous. In a series of experiments replacements are made for any value of “Open” in the terrain map with “Mixed”, “Rough”, and “Mountainous” respectively. (See
Supplementary Materials Section D-7 Experiment Test Parameters & Results.) These are simulated with the historical case, including interventions and compared against the Baseline Historical in
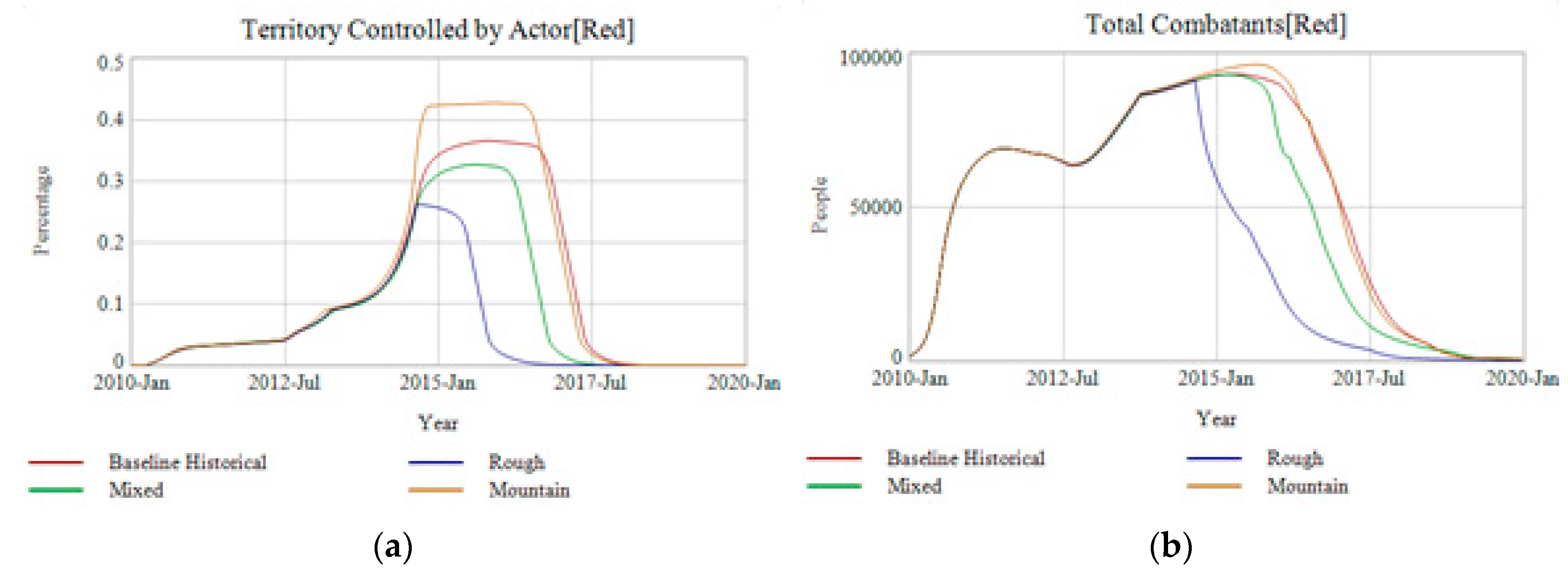
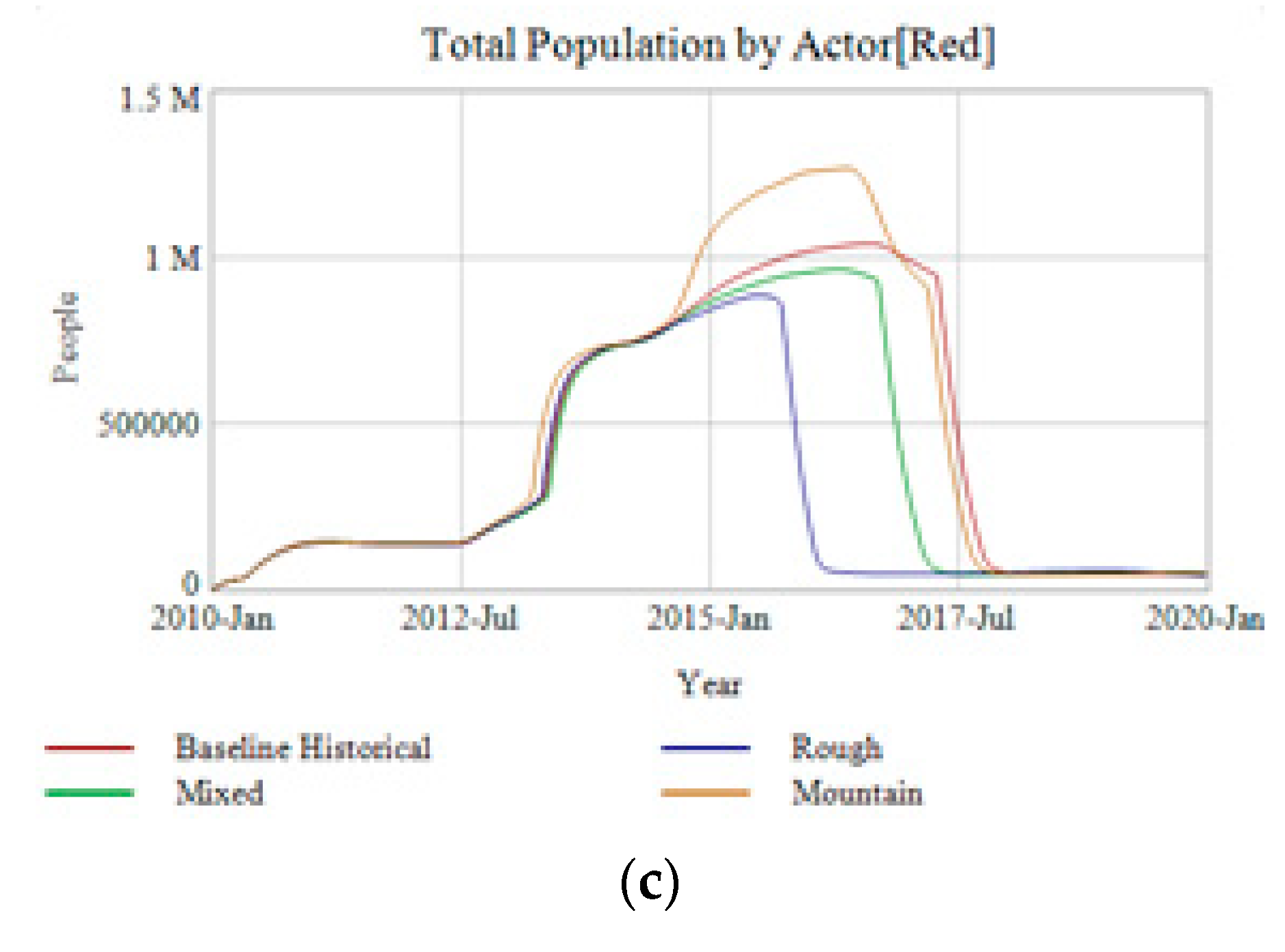
Figure 17 below.
The introduction of differing terrains adjusts ISIS performance in specific point-values, but does not change the general behavior mode. In
Figure 17a, the territory, ISIS gains less territory in Rough and Mixed than the Historical Baseline because fighting in those conditions is harder and each victory does not generate as much forward movement of control (see
Supplementary Materials.) ISIS does perform better in the Mountainous scenario however because ISIS does not rely on armored vehicles and artillery as the Green Actor does. And these heavy vehicles and pieces of equipment perform poorly in mountains. As the peak value of territory adjusts (a) so to do the total combatants (b) and population under control change (c) as well. Less captured territory means less population to control and recruit from. But these are only tactical differences. At a strategic level across the entire simulation, the sharp increase in territory occurs at nearly the same time across all runs. Although the collapse portion varies as to when it occurs, it does not significantly vary in shape. In no scenario is ISIS able to sustain itself against the combined foreign interventions either at its height or lower values. This same outcome repeats in
Figure 17b,c, where the behavior modes of total combatants and total population do not significantly vary in shape or outcome. Changing terrain types definitely has a point-value impact on the simulation, but does not appear to create dramatic changes in results.
This leads to an interesting thought-experiment. Given the US intervention in Vietnam—and keeping everything else equal—if the terrain had been a desert rather than a jungle would the outcome have been different? Likewise, the US invasion of Iraq, accepting as premise the invasion occurs and all policy choices remain consistent would replacing the desert terrain with jungle would the path of insurgency have altered substantially?
The simulation results suggest an interesting answer: terrain matters tactically, but not strategically. What may matter more than physical terrain is the human-terrain, specifically the ethnographic groups and their perception of legitimacy to both the state and non-state actors that are competing. This is hinted at in sensitivity analysis conducted during confidence building tests of E-SAM. (See
Supplementary Materials Section B-12 Sensitivity Analysis.) Each Actor has a supporting or opposed ethnographic group—one which naturally favors them and one that dislikes them. In the Baseline Historical the Red Actor enjoys more support, and thus higher starting perception, from Arab Sunni while Arab Shia support the Green actor. Likewise, the Green Actor is more opposed to Arab Sunni and Red Actor opposed to Arab Shia. What the analysis revealed was that from a policy space the starting ethnographic perceptions matter more in relation to the Green Actor, than to the Red. And furthermore, that it is the ethnographic perception of the group opposing the Green Actor that matters the most. In other words that the Arab Suuni who were more opposed to the Green Actor happened to live in a desert is less important to the outcome than the extent and depth of opposition to the Green Actor’s legitimacy. One could virtually swap out terrain types underneath this population, replacing desert with mountains or jungles and the key outcomes remain similar.
Although policy implications are beyond the scope of this paper this suggests that mapping the ethnographic-terrain could be just as, if not more important, than understanding the physical terrain in which a conflict occurs. This need not be reduced to a simplistic “winning hearts and minds” but does suggest that a nuanced understanding of grievances and perceptions between ethnographic groups and actors is important for policy analysis. These results also indicate that emerging-state actors are a phenomena not confined, or aided, by certain terrain features. And that terrain-based arguments for the difficulty of a conflict may be overlooking latent structures such as grievances or lack of legitimacy.
9. Conclusions
In this paper I used the case of ISIS to formulate and test the theory of an emerging-state actor. Gains in confidence of the theory result from simulation tests on key propositions. Calling upon local and global grievances the emerging-state actor recruits locally and draws foreign fighters to seize territory upon which it exercises sovereign control and begins openly governing. The use of governing mechanisms shifts the population from control through coercion to perceptions of legitimacy. This frees up garrison troops to continue expansion and territorial gain. The dynamic hypothesis that the so-called Islamic State in Iraq and Syria was an emerging-state actor is plausible. That ISIS used irregular warfare to usurp existing state-actors and gain control of target populations. This dynamic hypothesis is better able to explain ISIS’s behavior pattern than traditional insurgency models. This paper also offers a detailed scenario-based simulation model for future use with clandestine terror networks, insurgencies and other emerging-state actors. We conducted a full suite of validation and confidence building tests for the E-SAM model. (See
Supplementary Materials Section B Validation & Confidence Building.) These tests revealed that the E-SAM can replicate at least plausible behavior in different regions and contexts including a hypothetical counter-terrorism campaign in Indonesia upon the return of expatriated ISIS fighters home. Additionally, tests on the influence of terrain showed that the dynamics were not limited to the kind of terrain ISIS began in. These indicate that the dynamics demonstrated by ISIS may not be confined to Iraq and Syria, but subsume a more general structure. A larger potential limitation is the significant use of group-behaviors in the simulation by ethnographic groups and leadership of both ISIS and Syria and Iraq. Without substantial data on these qualitative dynamics there remains room for parameter error.
Future work could build upon initial policy analysis for determining intervention and containment policies against ISIS or emerging-state actors [
13]. Modeling and simulation of this kind still faces significant methodological challenges of which this model only addresses a few [
12]. Future work on emerging-state actor theory would continue building confidence by demonstrating applicability in more regional and historical contexts as well as improving methods. This could include additional testing of ISIS as well as other emerging-state actors in different time and regional spaces such as the Taliban in Afghanistan, East India Company in India, the Angles in England etc. Finally using a similar simulation approach to model individual radicalization processes that drive an individual to terrorism can help clarify and test theories of Atran, Taylor, Sageman and Hoffman. Whether the individual terrorist is acting as part of a group or a so-called “lone-wolf” terrorist. Even as ISIS’s influence decreases the long-tail of its radicalization efforts may remain a source of threat.