Reliable Delay Based Algorithm to Boost PUF Security Against Modeling Attacks †
Abstract
:1. Introduction
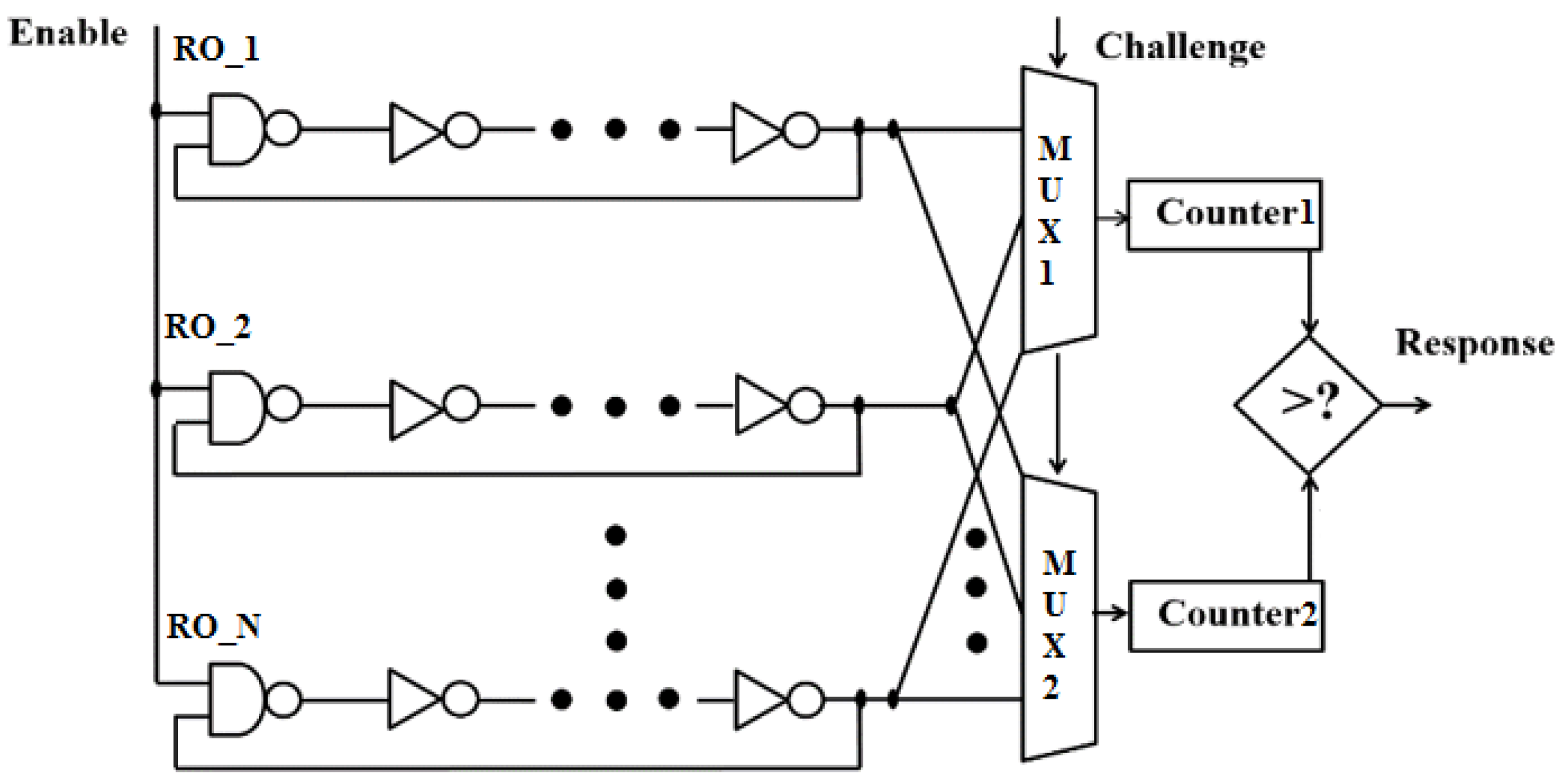
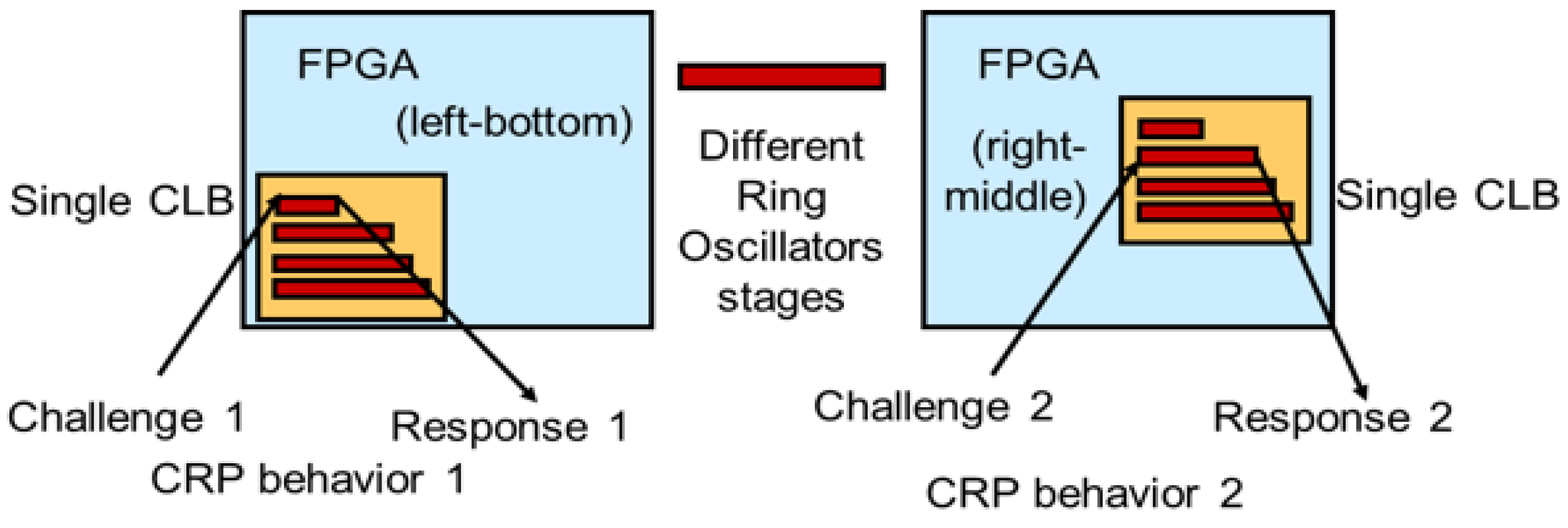
- A dynamic RO based PUF primitive architecture is proposed and demonstrated that is reliable over temperature and voltage (VT) variations.
- The proposed PUF primitive can be automatically configured to output updated secret keys based on the updated behavior of CRP space.
- Based on process variability of the dynamic RO structures, the proposed technique provides a reliable and large number of challenge response pairs (CRPs) to protect the PUF entity against modeling attacks.
- The proposed PUF primitive can further generate a larger number of reliable secret keys using a proposed Optimal Time Delay Algorithm (OTDA).
2. Research Background
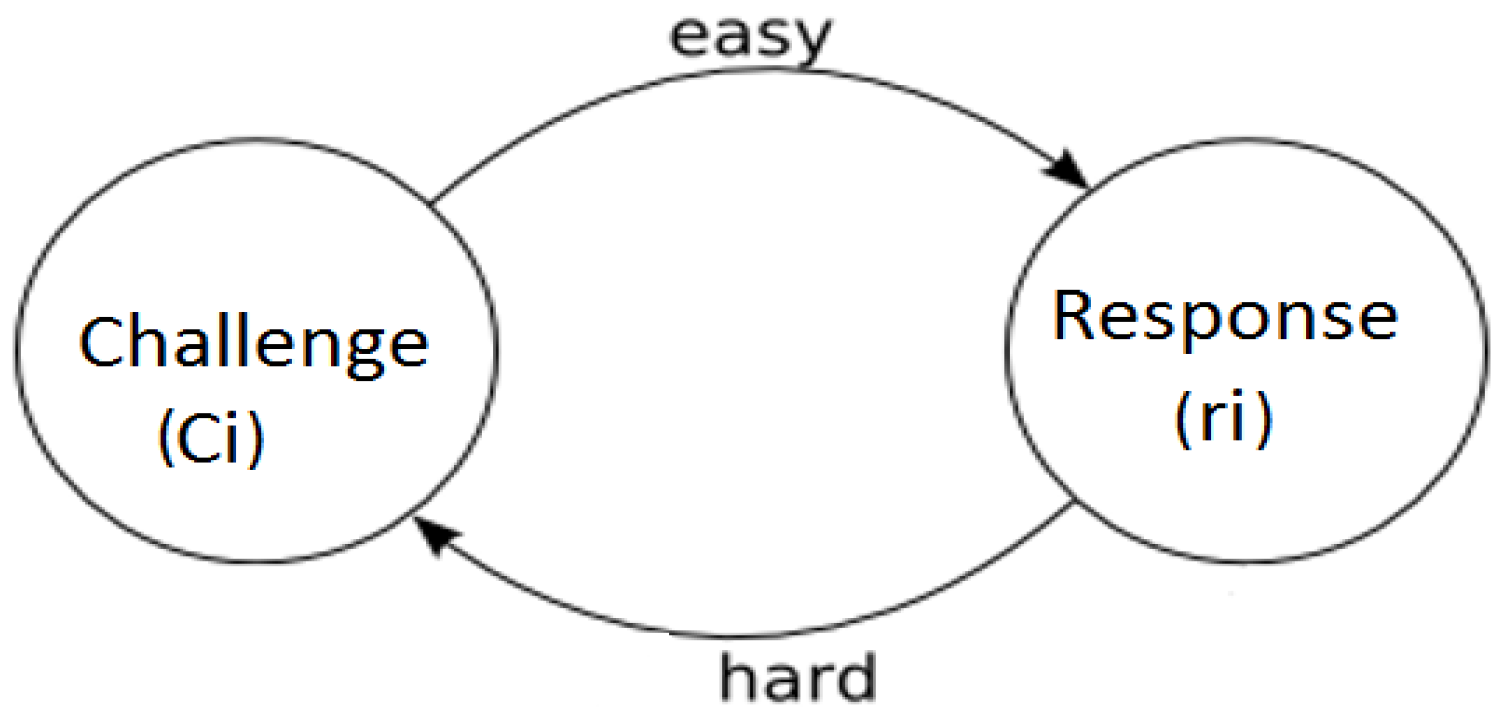
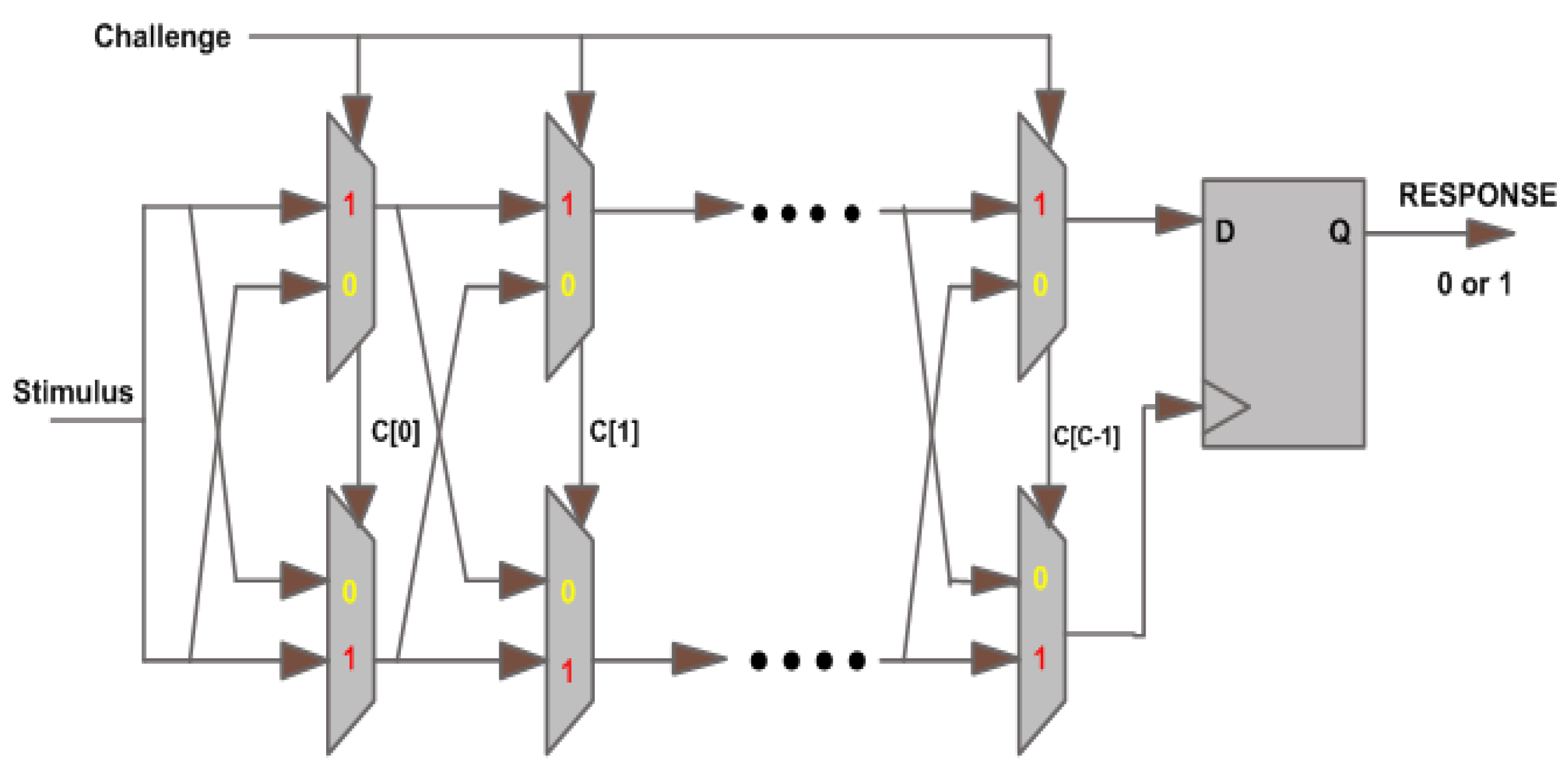
2.1. Silicon Physical Unclonable Functions
2.2. Cyber Attacks on Silicon PUFs
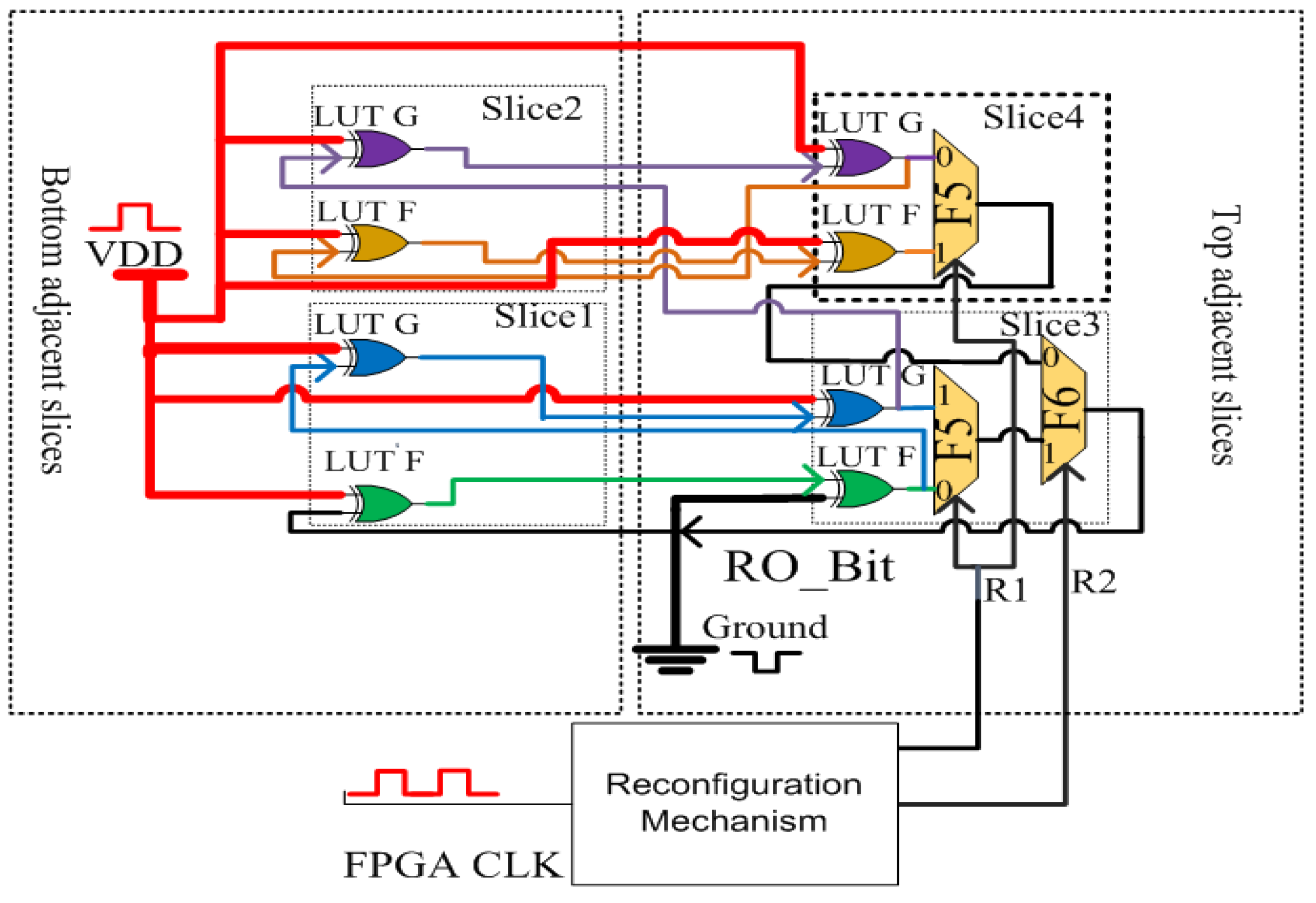
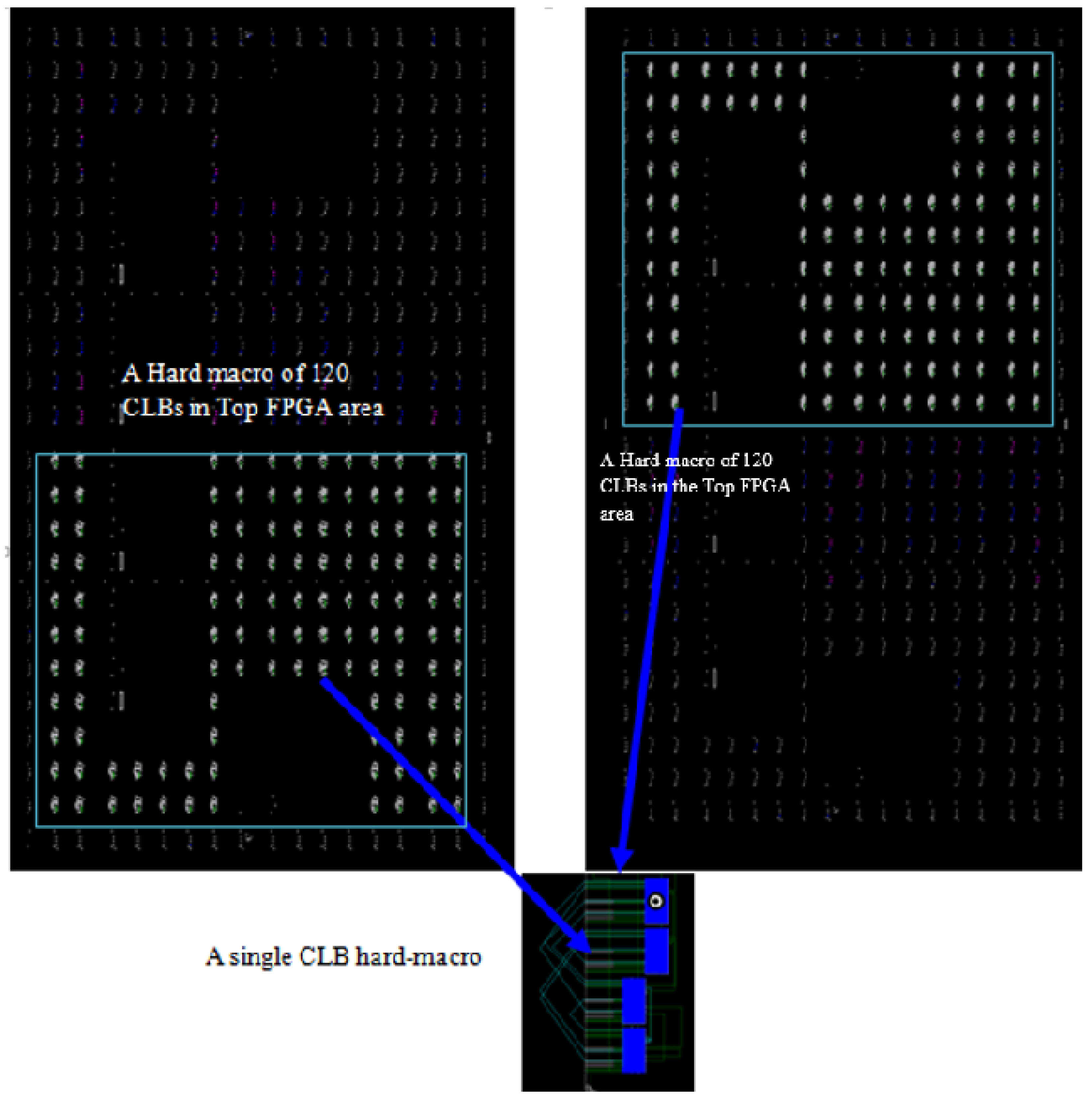
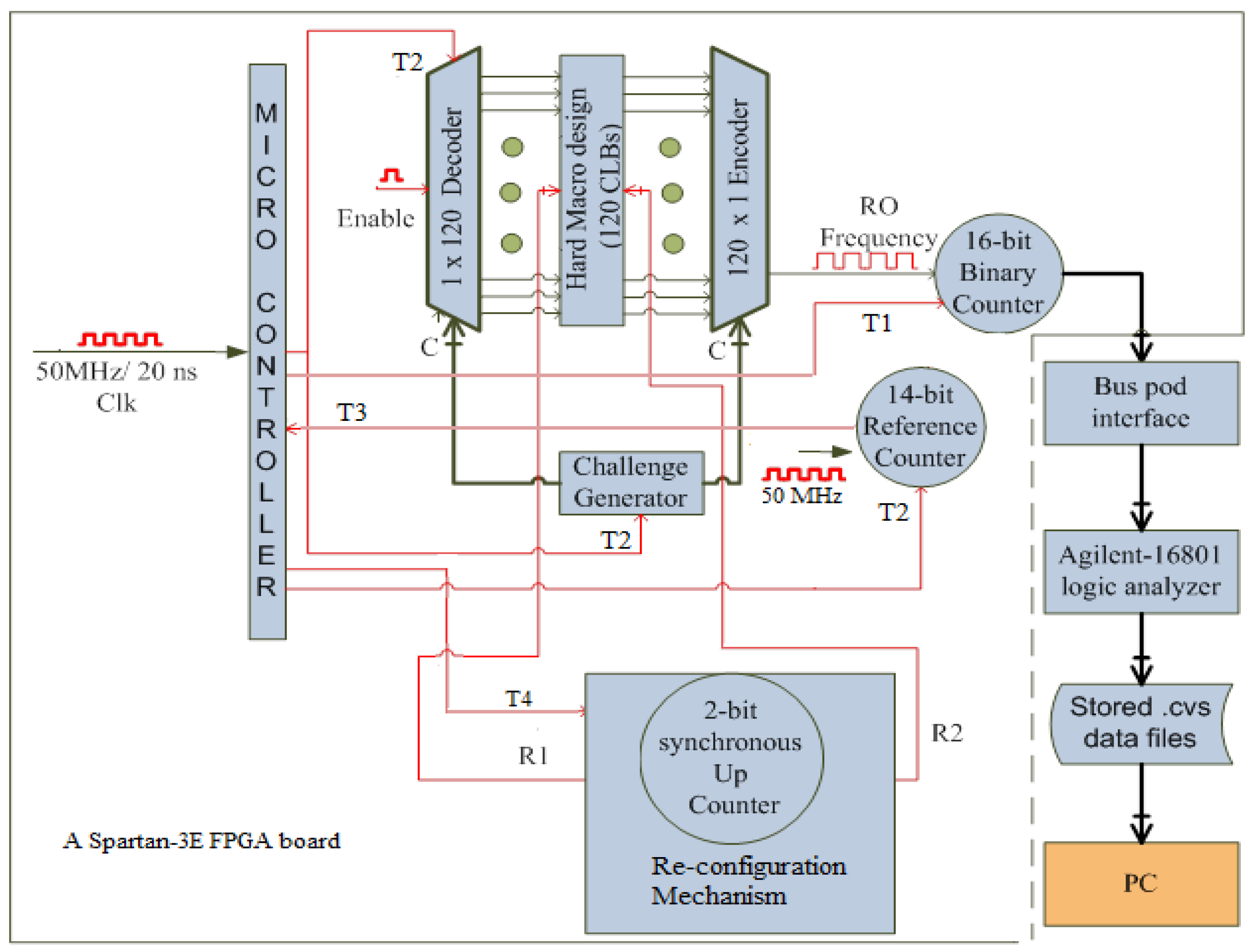
3. Proposed Dynamic Ring Oscillator Technique
4. Experimental Results and Discussions
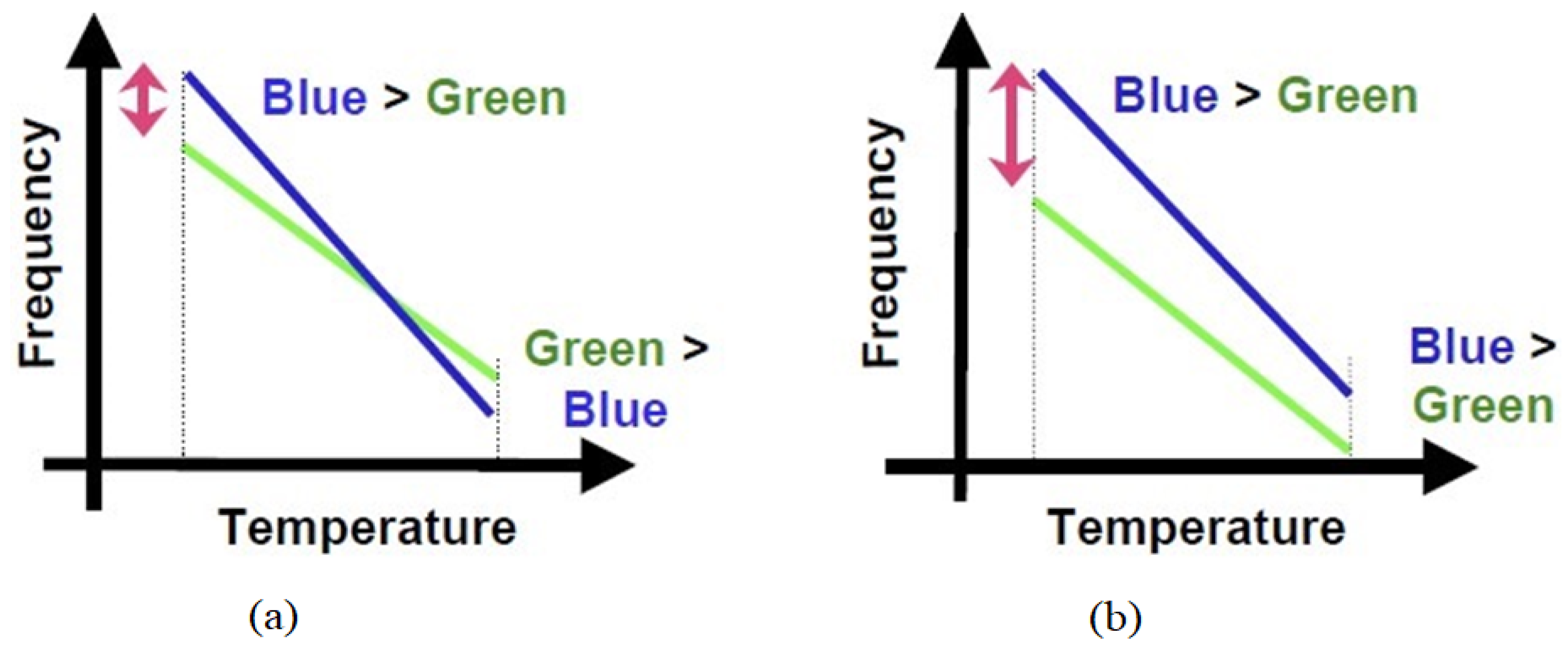
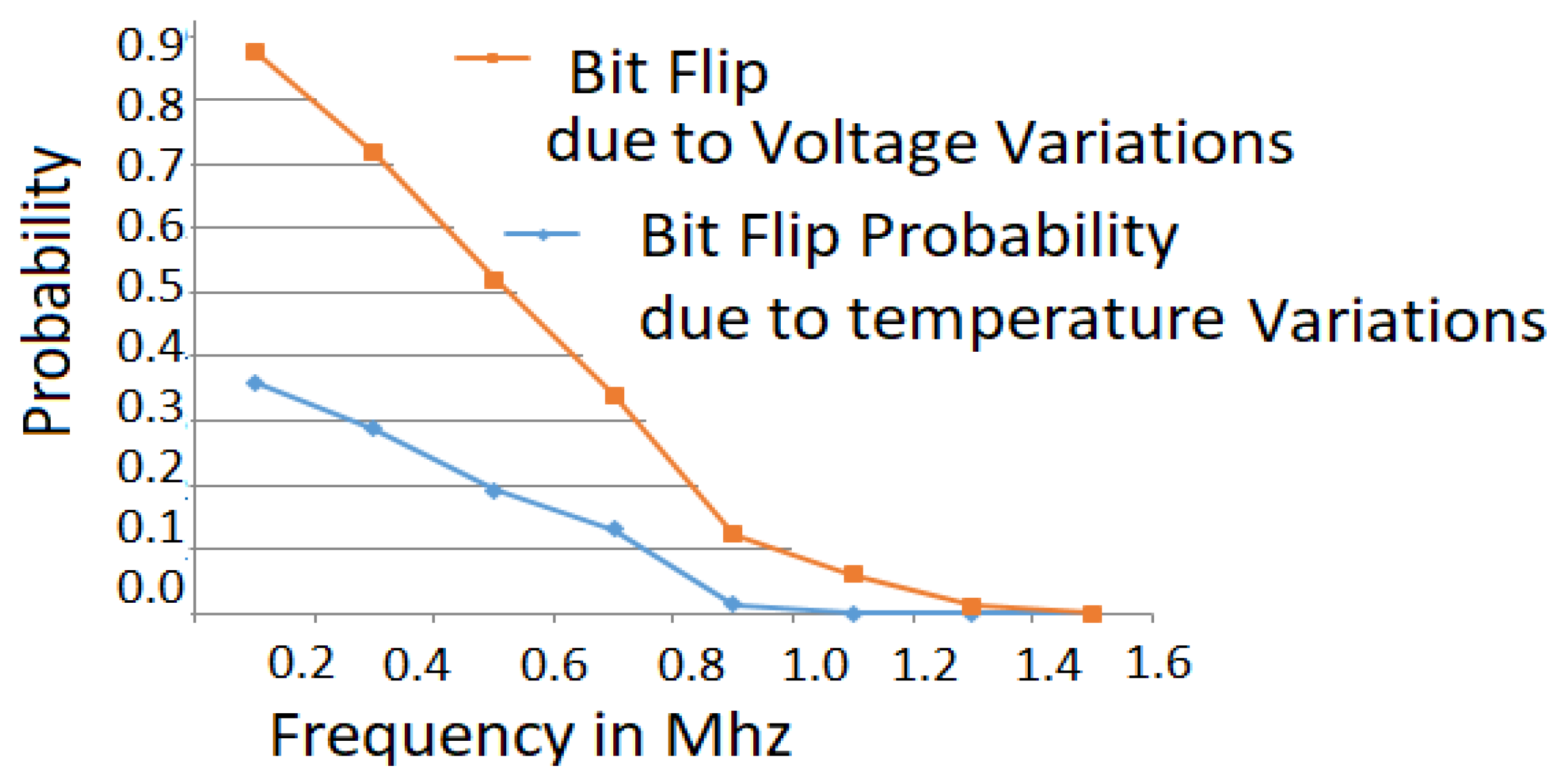
4.1. Reliability and Bit Flips
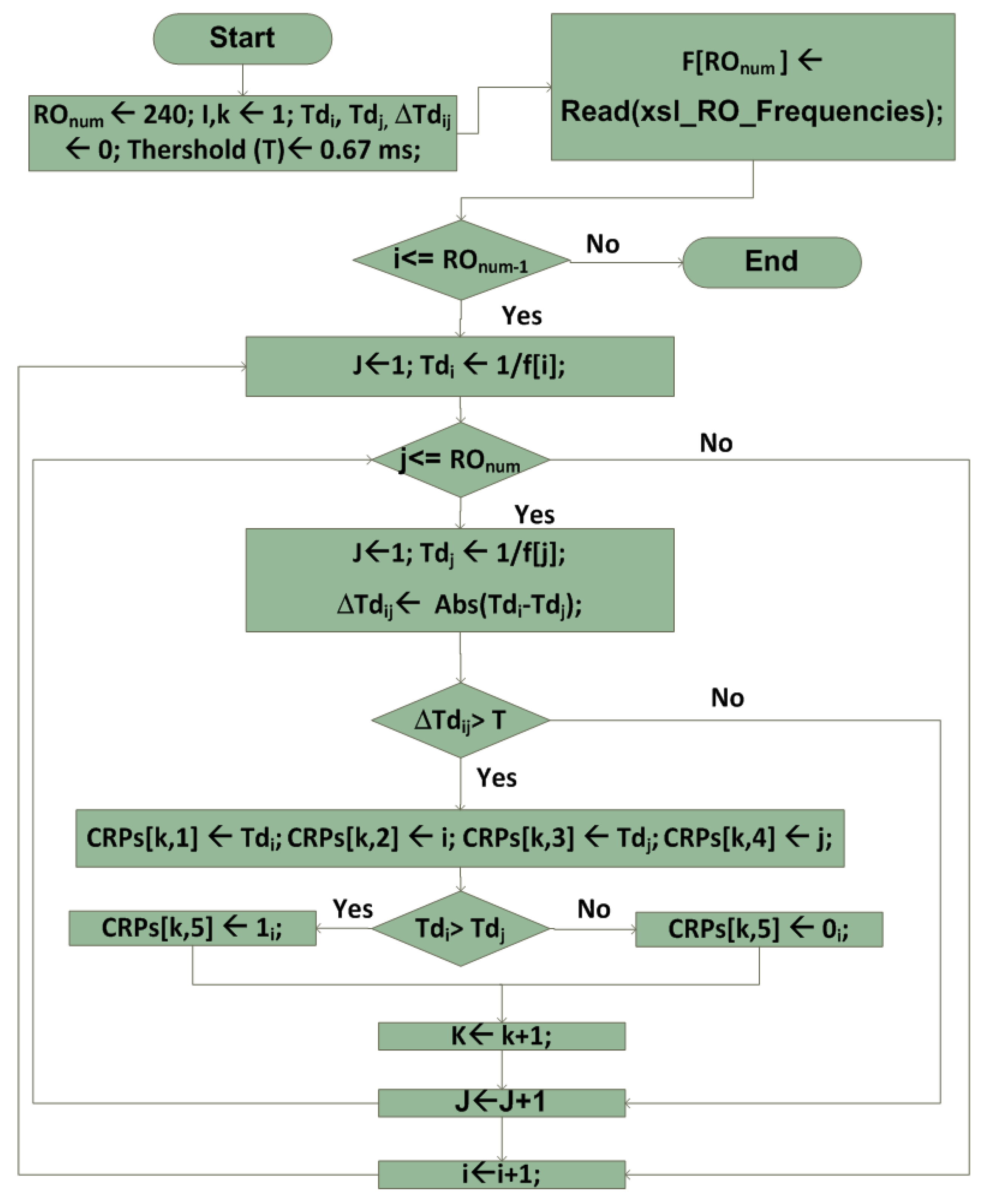
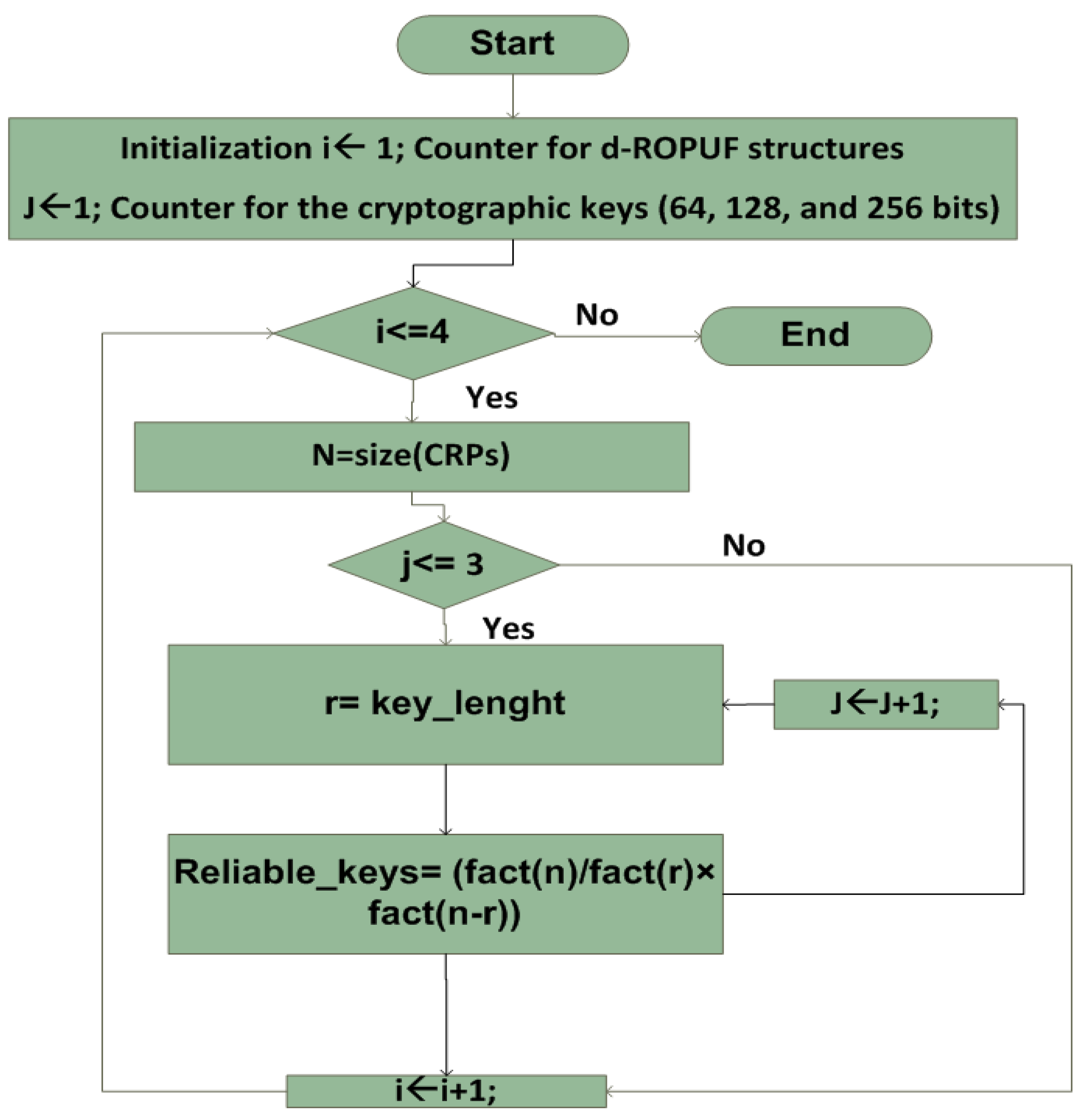
4.2. Optimal Time Delay Algorithm (OTDA)
| Algorithm 1 OTD algorithm step1: Reliable CRPs generation |
| procedure Generation() ▹ (number of RO frequencies of each d-ROPUF structure) ▹ (i, j are loop counters for the location of reliable RO frequency pairs) ▹ (k is row counter (k rows) of reliable challenge-response array CRPs[k,5]) ▹ (Initialize RO Time delays) ▹ (Assign the reliable threshold value) ▹ (Store RO frequencies of d-ROPUF in an f array) while do while do if () then if ( then else end if end if end while end while end procedure |
- Inputs: 240 frequencies extracted for one, three, five, and seven stages of d-ROPUF structures represented as .
- Output: List of the possible reliable RO frequency pairs stored in an array, named CRPs(n:5), in n rows and five columns, where .
- Inputs: CRP[i,j] the set of the reliable response bits for 1, 3, 5, 7 stages of ROs that is the result of Algorithm 1.
- Output: The list of all possible m reliable cryptographic keys (64, 128, 256).
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Maiti, A.; Schaumont, P. Improving the quality of physical unclonable function using configurable ring oscillators. In Proceedings of the 2009 International Conference on Field Programmable Logic and Applications, Prague, Czech Republic, 31 August–2 September 2009. [Google Scholar]
- Xin, X.; Jens, P.; Kris, K. A Configurable RO-Based PUF for Xilinx FPGAs. In Proceedings of the 14th Euromicro Conference on Digital System Design, Oulu, Finland, 31 August–2 September 2011. [Google Scholar]
- Amsaad, F.; Hoque, T.; Niamat, M. Analyzing the performance of a configurable ROPUF design controlled by programmable XOR gates. In Proceedings of the IEEE 58th International Midwest Symposium on Circuits and Systems, Fort Collins, CO, USA, 2–5 August 2015. [Google Scholar]
- Kursawe, K.; Sadeghi, A.; Schellekens, D.; Skoric, B.; Tuyls, P. Re-configurable physical unclonable functions-enabling technology for tamper-resistant storage. In Proceedings of the 2009 IEEE International Workshop on Hardware-Oriented Security and Trust (HOST), Francisco, CA, USA, 27 July 2009. [Google Scholar]
- Mustapa, M.; Alam, M.; Killian, T.; Niamat, M. Frequency uniqueness in ring oscillator Physical Unclonable Functions on FPGAs. In Proceedings of the 2013 IEEE 56th International Midwest Symposium on Circuits and Systems (MWSCAS), Columbus, OH, USA, 4–7 August 2013. [Google Scholar]
- Amsaad, F.; Choudhury, M.; Chaudhuri, C.; Niamat, M. An innovative delay-based algorithm to boost PUF security against machine learning attacks. In Proceedings of the Annual IEEE Connecticut Conference on Industrial Electronics, Technology and Automation (CT-IETA), Bridgeport, CT, USA, 14–15 October 2016. [Google Scholar]
- Amsaad, F.; Pundir, N.; Niamat, M. A Dynamic Area-Efficient Technique to Enhance ROPUFs Security Against Modeling Attacks. In Computer and Network Security Essentials; Springer: Cham, Switzerland, 2018; pp. 407–425. [Google Scholar]
- Lim, D.; Lee, J.W.; Gassend, B. Extracting secret keys from integrated circuits. IEEE Trans. Very Large Scale Integr. Syst. 2005, 13, 1200–1205. [Google Scholar]
- Edward Suh, G.; Devadas, S. Physical unclonable functions for device authentication and secret key generation. In Proceedings of the 2007 44th ACM/IEEE Design Automation Conference, San Diego, CA, USA, 4–8 June 2007. [Google Scholar]
- Pundir, N.; Hazari, N.; Amsaad, F.; Niamat, M. A novel hybrid delay based physical unclonable function immune to machine learning attacks. In Proceedings of the 2017 IEEE National Aerospace and Electronics Conference (NAECON), Dayton, OH, USA, 27–30 June 2017. [Google Scholar]
- Pundir, N.; Amsaad, F.; Choudhury, M.; Niamat, M. Novel technique to improve the strength of weak arbiter PUF. In Proceedings of the 2017 IEEE 60th International Midwest Symposium on Circuits and Systems (MWSCAS), Boston, MA, USA, 6–9 August 2017. [Google Scholar]
- Helfmeier, C.; Boit, C.; Nedospasov, D.; Seifert, J. Cloning Physically Unclonable Functions. In Proceedings of the 2013 IEEE International Symposium on Hardware-Oriented Security and Trust (HOST), Austin, TX, USA, 2–3 June 2013. [Google Scholar]
- Nedospasov, D.; Seifert, J.; Helfmeier, C.; Boit, C. Invasive PUF Analysis. In Proceedings of the 2013 Workshop on Fault Diagnosis and Tolerance in Cryptography, Santa Barbara, CA, USA, 20 August 2013. [Google Scholar]
- Merli, D.; Schuster, D.; Stumpf, F.; Sigl, G. Semi-invasive EM attack on FPGA RO PUFs and countermeasures. In Proceedings of the Workshop on Embedded Systems Security, Taipei, Taiwan, 9–14 October 2011. [Google Scholar]
- Azhar, M.; Amsaad, F.; Köse, S. Duty-Cycle-Based Controlled Physical Unclonable Function. IEEE Trans. Very Large Scale Integr. Syst. 2018. [Google Scholar] [CrossRef]
- Deb Nath, A.; Amsaad, F.; Choudhury, M.; Niamat, M. Hardware-based novel authentication scheme for advanced metering infrastructure. In Proceedings of the 2016 IEEE National Aerospace and Electronics Conference (NAECON) and Ohio Innovation Summit (OIS), Dayton, OH, USA, 25–29 July 2016. [Google Scholar]
- Amsaad, F.; Chaudhuri, C.; Deb Nath, A.; Niamat, M. A novel security technique to generate truly random and highly reliable reconfigurable ROPUF-based cryptographic keys. In Proceedings of the 2016 IEEE International Symposium on Hardware-Oriented Security and Trust (HOST), McLean, VA, USA, 3–5 May 2016. [Google Scholar]
- Hoque, T.; Mustapa, M.; Amsaad, F.; Niamat, M. Assessment of NAND based ring oscillator for hardware Trojan detection. In Proceedings of the 2015 IEEE 58th International Midwest Symposium on Circuits and Systems (MWSCAS), Fort Collins, CO, USA, 2–5 August 2015. [Google Scholar]
- Herder, C.; Koushanfar, F.; Devadas, S. Physical Unclonable Functions and Applications: A Tutorial. Proc. IEEE 2014, 102, 1126–1141. [Google Scholar] [CrossRef]
- Amsaad, F.; Chaudhuri, C.; Niamat, M. Reliable and reproducible PUF based cryptographic keys under varying environmental conditions. In Proceedings of the 2016 IEEE National Aerospace and Electronics Conference (NAECON) and Ohio Innovation Summit (OIS), Dayton, OH, USA, 25–29 July 2016. [Google Scholar]
- Chaudhuri, C.; Amsaad, F.; Niamat, M. Impact of temporal variations on the performance and reliability of configurable ring oscillator PUF. In Proceedings of the 2016 IEEE National Aerospace and Electronics Conference (NAECON) and Ohio Innovation Summit (OIS), Dayton, OH, USA, 25–29 July 2016. [Google Scholar]
- Rührmair, U.; Sölter, J.; Sehnke, F. PUF Modeling Attacks on Simulated and Silicon Data. IEEE Trans. Inf. Forensics Secur. 2013, 8, 1876–1891. [Google Scholar] [CrossRef] [Green Version]
- Ye, J.; Guo, Q.; Hu, Y.; Li, H.; Li, X. Modeling Attacks on Physical Unclonable Functions. In Proceedings of the 2018 IEEE 36th VLSI Test Symposium (VTS), San Francisco, CA, USA, 22–25 April 2018. [Google Scholar]
- Delvaux, J.; Verbauwhede, I. Side channel modeling attacks on 65nm arbiter PUFs exploiting CMOS device noise. In Proceedings of the 2013 IEEE International Symposium on Hardware-Oriented Security and Trust (HOST), Austin, TX, USA, 2–3 June 2013. [Google Scholar]
- Kumar, S.; Guajardo, J.; Maes, R.; Schrijen, G.; Tuyls, P. FPGA intrinsic PUFs and their use for IP protection. In Proceedings of the 2008 IEEE International Workshop on Hardware-Oriented Security and Trust, Anaheim, CA, USA, 9 June 2008. [Google Scholar]
- Rostami, M.; Wendt, J.; Potkonjak, M.; Koushanfar, F. Security based on Physical Unclonability and Disorder. In Proceedings of the 2014 Design, Automation and Test in Europe Conference and Exhibition, Dresden, Germany, 24–28 March 2014. [Google Scholar]
- Öztürk, E.; Hammouri, G.; Sunar, B. Towards robust low-cost authentication for pervasive devices. In Proceedings of the 2008 Sixth Annual IEEE International Conference on Pervasive Computing and Communications (PerCom), Hong Kong, China, 17–21 March 2008. [Google Scholar]

| FPGA | Reliable Response | 64-Bits | 128-Bits | 256-Bits | 512-Bits |
|---|---|---|---|---|---|
| 1 | 828 | 3.67 × 10 | 2.63× 10 | 5.40× 10 | 3.44× 10 |
| 2 | 834 | 5.93× 10 | 7.18× 10 | 1.61× 10 | 1.07× 10 |
| 3 | 834 | 5.93× 10 | 7.18× 10 | 3.20× 10 | 1.07× 10 |
| 4 | 870 | 9.13× 10 | 2.14× 10 | 5.93× 10 | 9.97× 10 |
| 5 | 804 | 4.76× 10 | 3.70× 10 | 5.22× 10 | 6.51× 10 |
| 6 | 851 | 2.10× 10 | 1.00× 10 | 1.45× 10 | 3.40× 10 |
| 7 | 827 | 3.38× 10 | 2.22× 10 | 1.85× 10 | 1.31× 10 |
| 8 | 877 | 1.55× 10 | 6.51× 10 | 3.75× 10 | 4.82× 10 |
| 9 | 834 | 5.48× 10 | 6.08× 10 | 2.70× 10 | 4.10× 10 |
| 10 | 840 | 9.56× 10 | 1.94× 10 | 1.89× 10 | 3.10× 10 |
| 11 | 888 | 3.84× 10 | 4.26× 10 | 1.77× 10 | 1.60× 10 |
| 12 | 896 | 6.96× 10 | 1.47× 10 | 1.33× 10 | 1.47× 10 |
| 13 | 825 | 2.66× 10 | 1.34× 10 | 1.77× 10 | 7.22× 10 |
| 14 | 883 | 2.64× 10 | 1.95× 10 | 1.85× 10 | 2.15× 10 |
| 15 | 824 | 2.45× 10 | 1.13× 10 | 5.13× 10 | 2.73× 10 |
| 16 | 874 | 1.23× 10 | 4.05× 10 | 1.76× 10 | 3.44× 10 |
| 17 | 816 | 1.28× 10 | 2.92× 10 | 4.86× 10 | 1.07× 10 |
| 18 | 800 | 3.71× 10 | 2.19× 10 | 8.57× 10 | 3.08× 10 |
| 19 | 813 | 1.08× 10 | 2.07× 10 | 2.90× 10 | 1.48× 10 |
| 20 | 896 | 6.47× 10 | 1.26× 10 | 5.96× 10 | 6.32× 10 |
| 21 | 831 | 4.67× 10 | 4.35× 10 | 8.93× 10 | 6.12× 10 |
| 22 | 850 | 2.10× 10 | 1.00× 10 | 9.16× 10 | 3.40× 10 |
| 23 | 845 | 1.31× 10 | 3.75× 10 | 9.56× 10 | 1.30× 10 |
| 24 | 887 | 3.56× 10 | 3.65× 10 | 5.99× 10 | 6.81× 10 |
| 25 | 893 | 5.17× 10 | 7.94× 10 | 1.53× 10 | 4.93× 10 |
| 26 | 820 | 1.92× 10 | 6.83× 10 | 8.57× 10 | 1.46× 10 |
| 27 | 852 | 2.45× 10 | 1.39× 10 | 1.45× 10 | 2.14× 10 |
| 28 | 869 | 8.42× 10 | 1.82× 10 | 6.30× 10 | 4.09× 10 |
| 29 | 844 | 1.31× 10 | 3.75× 10 | 5.78× 10 | 1.31× 10 |
| 30 | 888 | 3.56× 10 | 3.65× 10 | 8.67× 10 | 6.81× 10 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Amsaad, F.; Niamat, M.; Dawoud, A.; Kose, S. Reliable Delay Based Algorithm to Boost PUF Security Against Modeling Attacks. Information 2018, 9, 224. https://doi.org/10.3390/info9090224
Amsaad F, Niamat M, Dawoud A, Kose S. Reliable Delay Based Algorithm to Boost PUF Security Against Modeling Attacks. Information. 2018; 9(9):224. https://doi.org/10.3390/info9090224
Chicago/Turabian StyleAmsaad, Fathi, Mohammed Niamat, Amer Dawoud, and Selcuk Kose. 2018. "Reliable Delay Based Algorithm to Boost PUF Security Against Modeling Attacks" Information 9, no. 9: 224. https://doi.org/10.3390/info9090224
APA StyleAmsaad, F., Niamat, M., Dawoud, A., & Kose, S. (2018). Reliable Delay Based Algorithm to Boost PUF Security Against Modeling Attacks. Information, 9(9), 224. https://doi.org/10.3390/info9090224




