Breaking Users’ Mobile Phone Number Based on Geographical Location: A Case Study with YY
Abstract
:1. Introduction
2. Problem Presentation
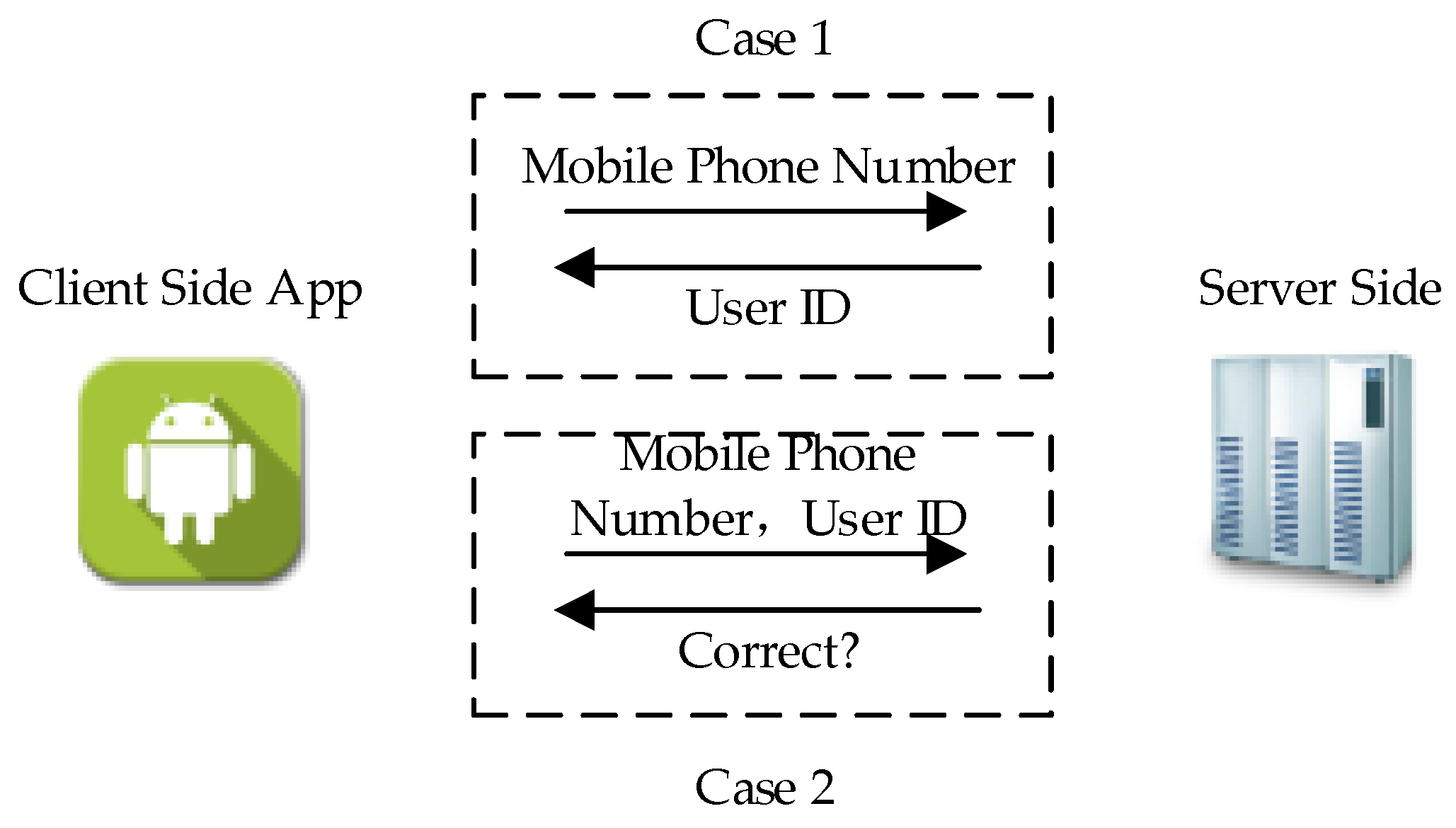
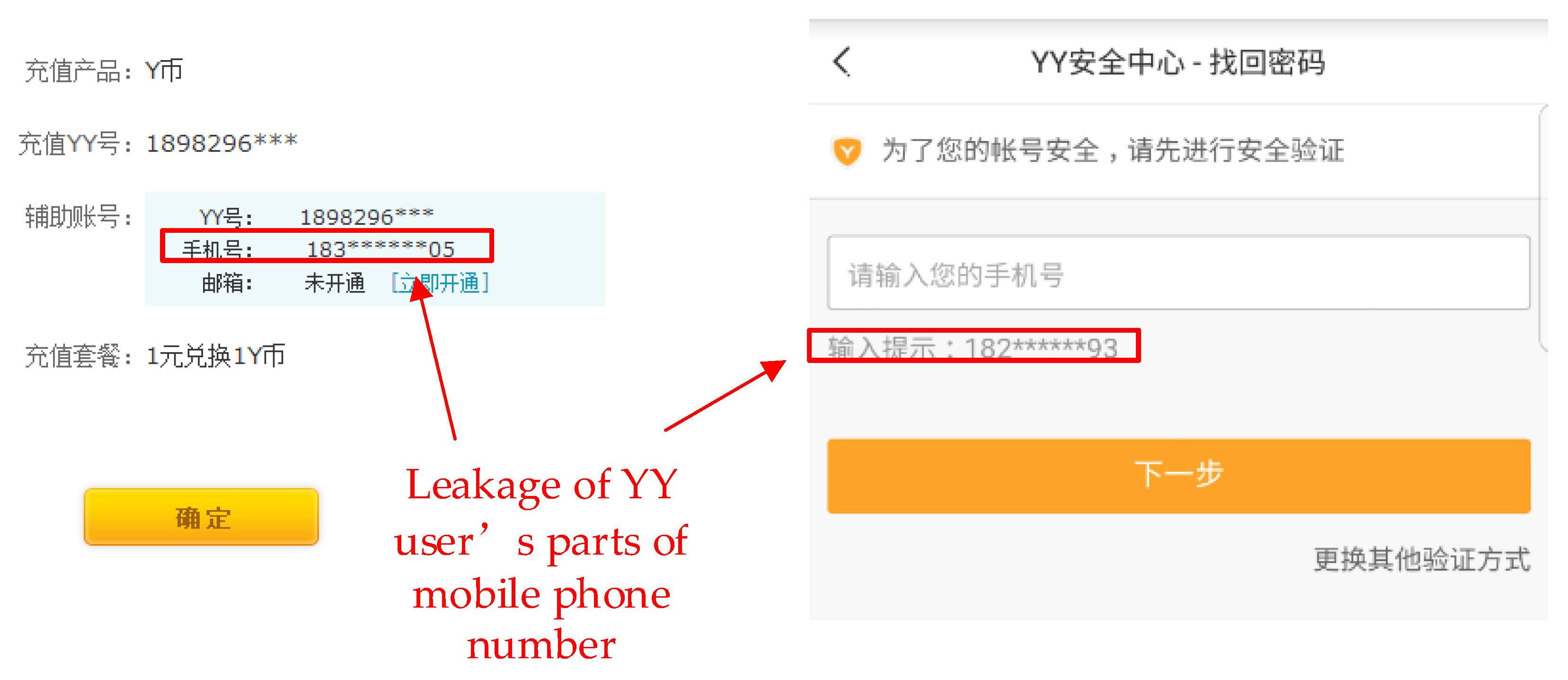
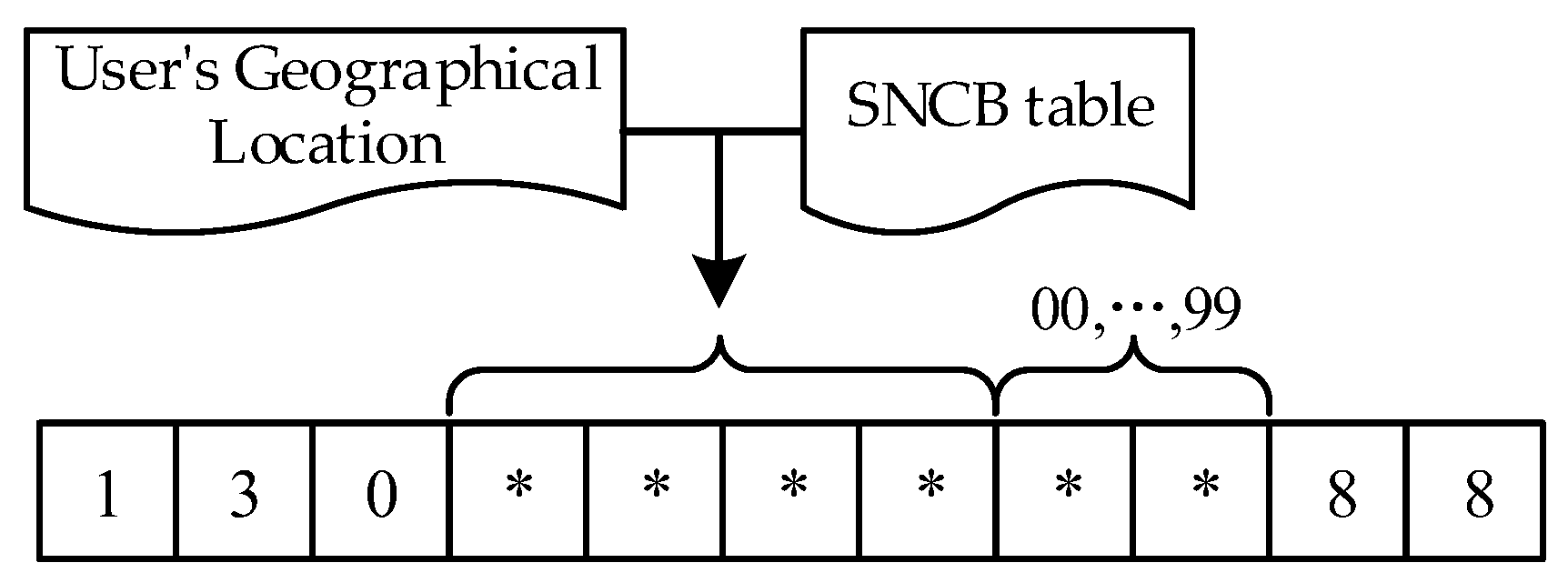
2.1. App Exposes Users’ Geographical Location and Parts of Mobile Phone Number
2.2. Discussion on the Possibility of Breaking the Mobile Phone Number
3. Background Knowledge of YY
3.1. Usage of YY
3.2. Channel and User Identity Level
3.3. YY Account
4. Vulnerability Details
4.1. Leakage of Users’ Geographical Location
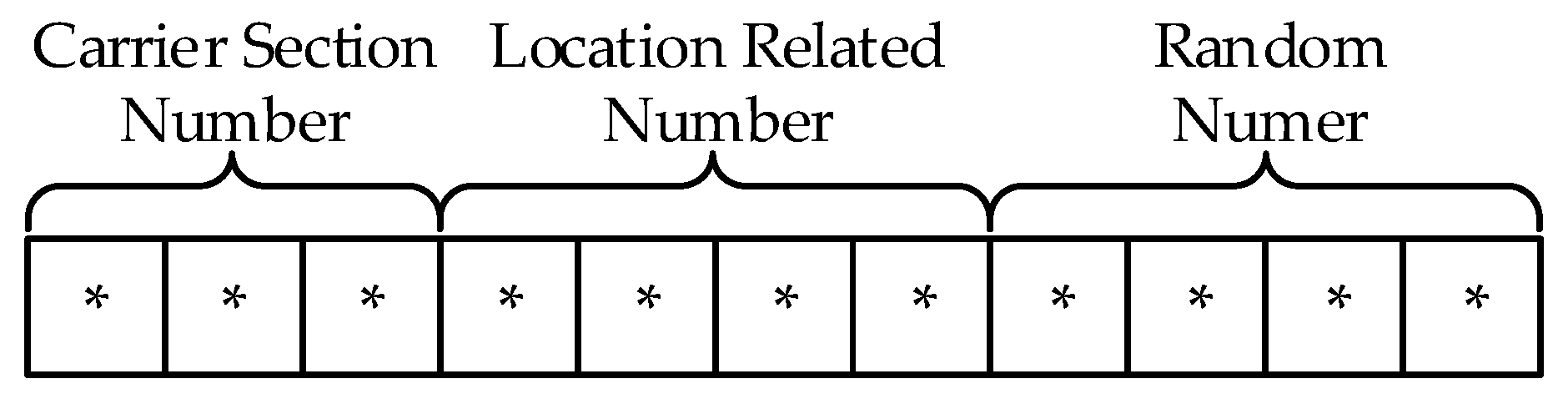
4.2. Mobile Phone Number with a Mask
4.3. Leakage of the Relationship between Mobile Phone Number and User ID
5. Breaking Method
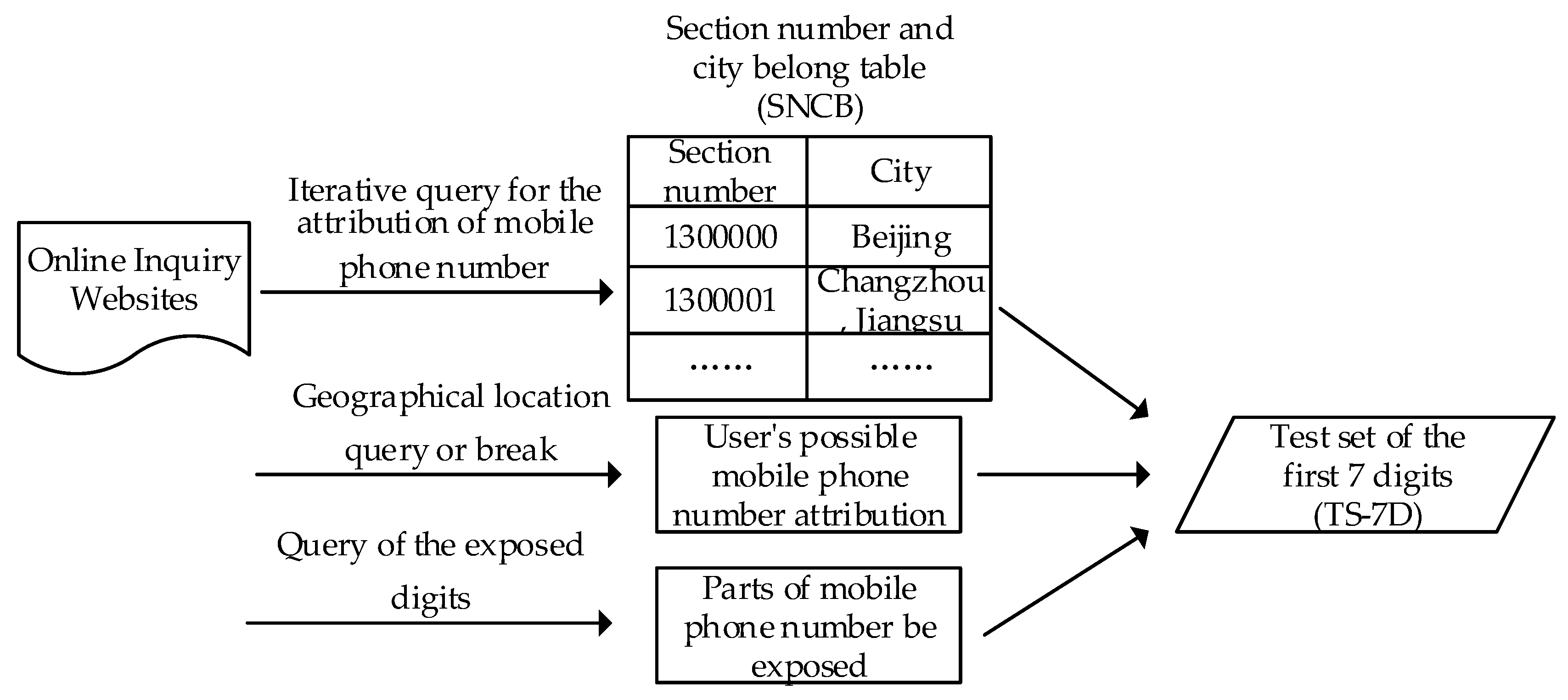
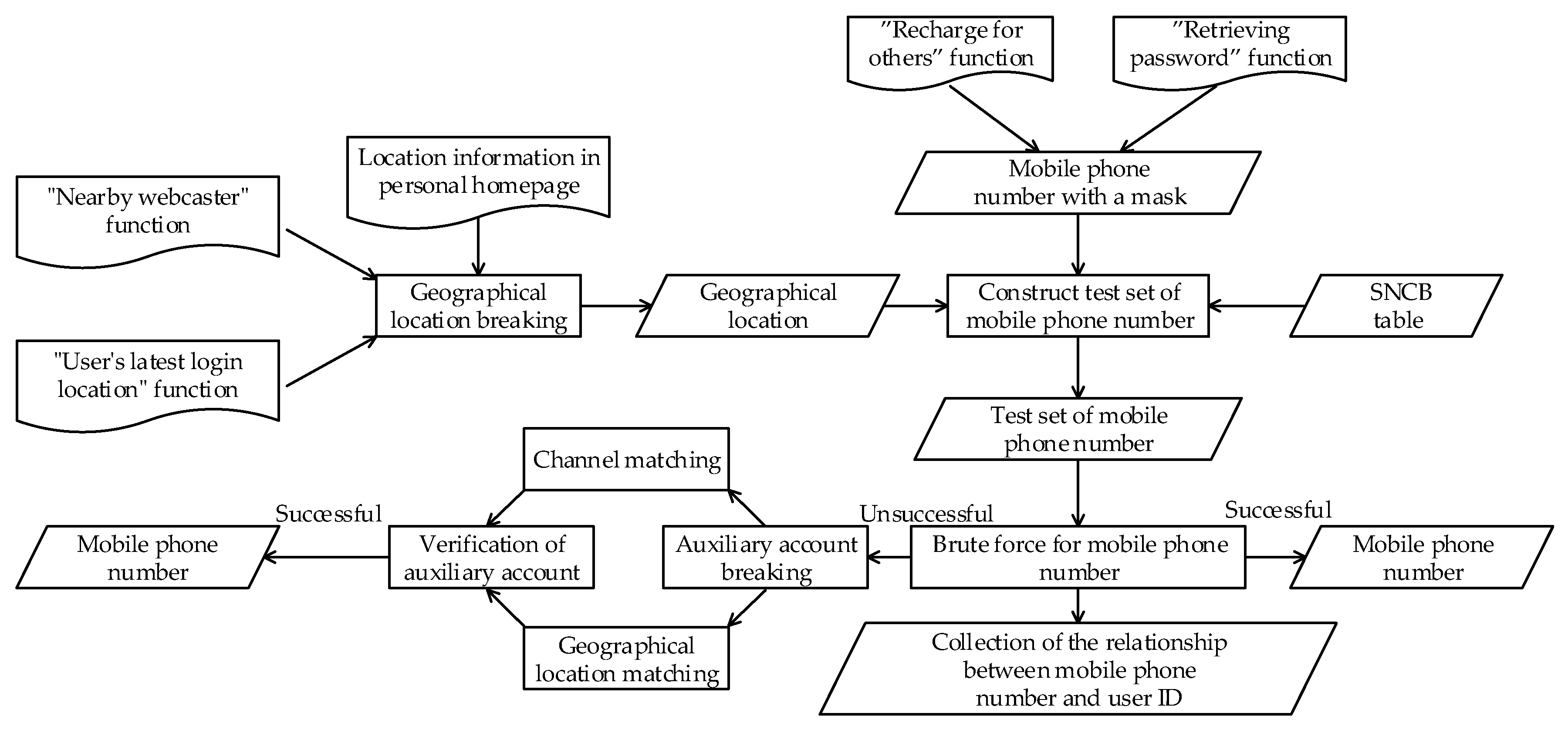
5.1. Overall Breaking Process
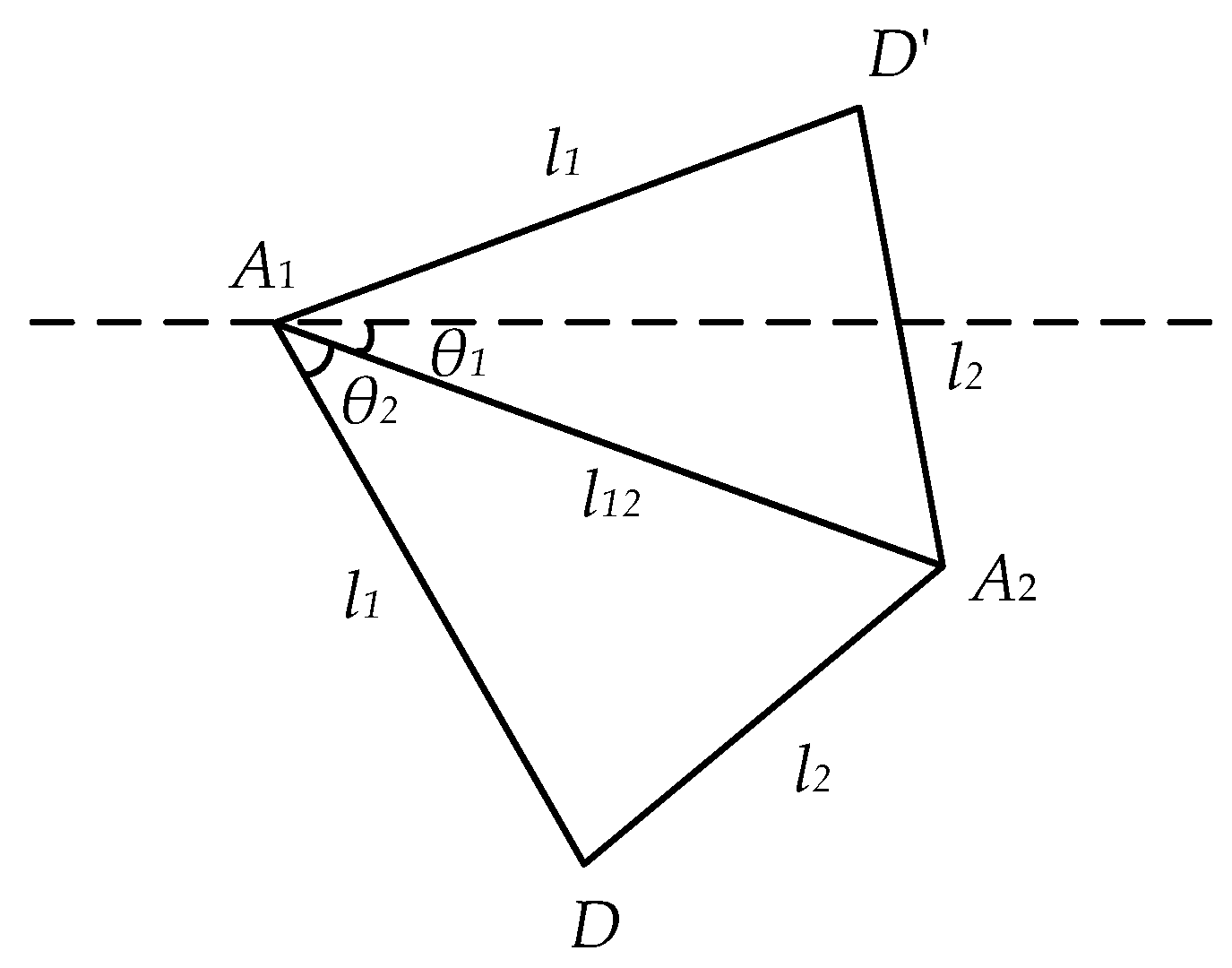
5.2. Location Calculation
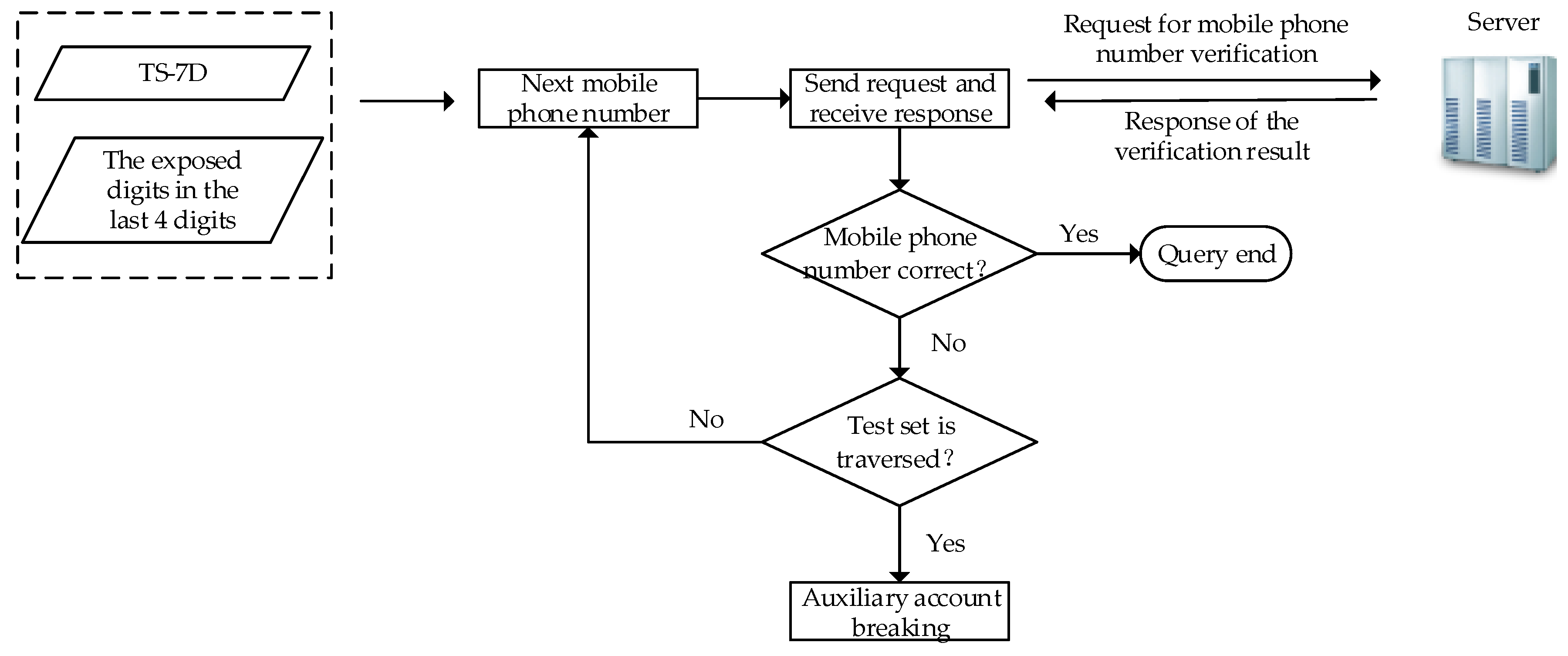
5.3. Mobile Phone Number Breaking and Auxiliary Account Breaking
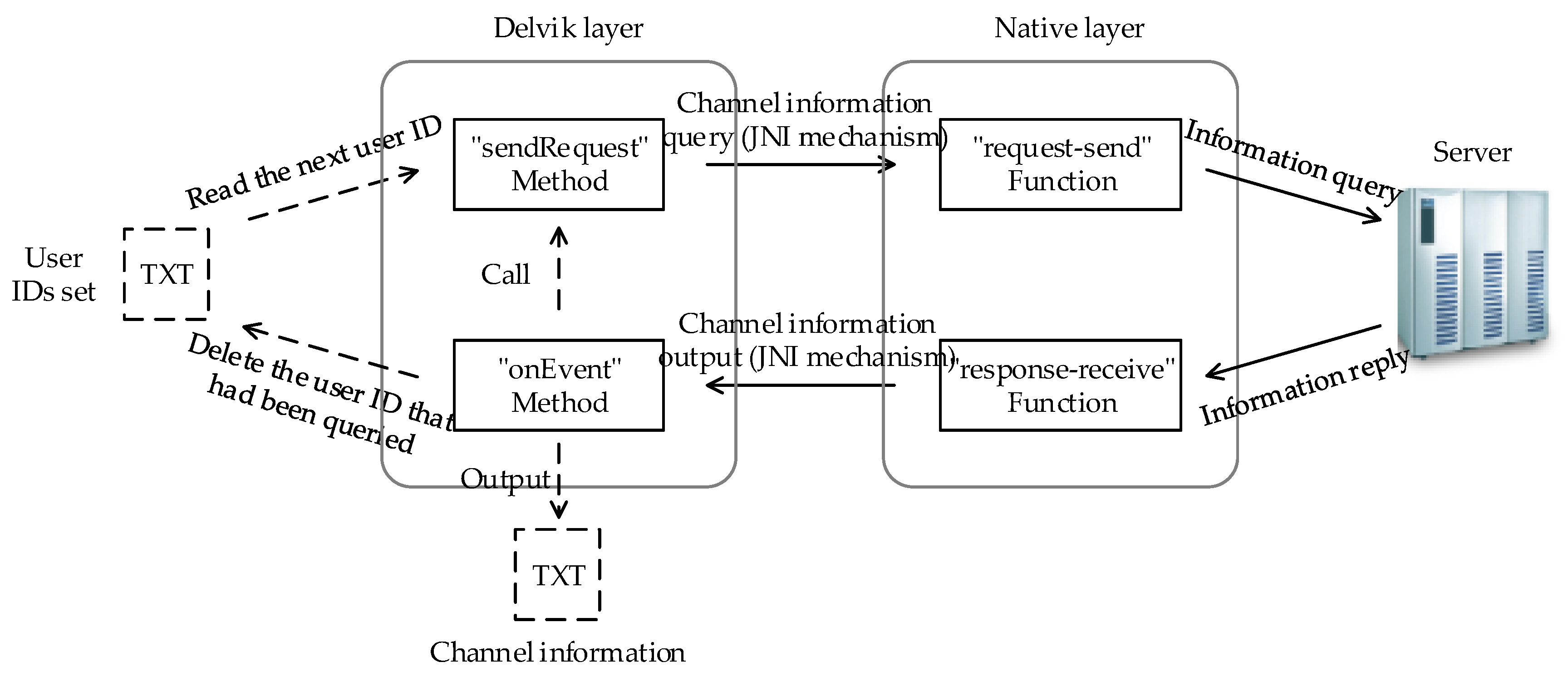
6. Technical Implementation
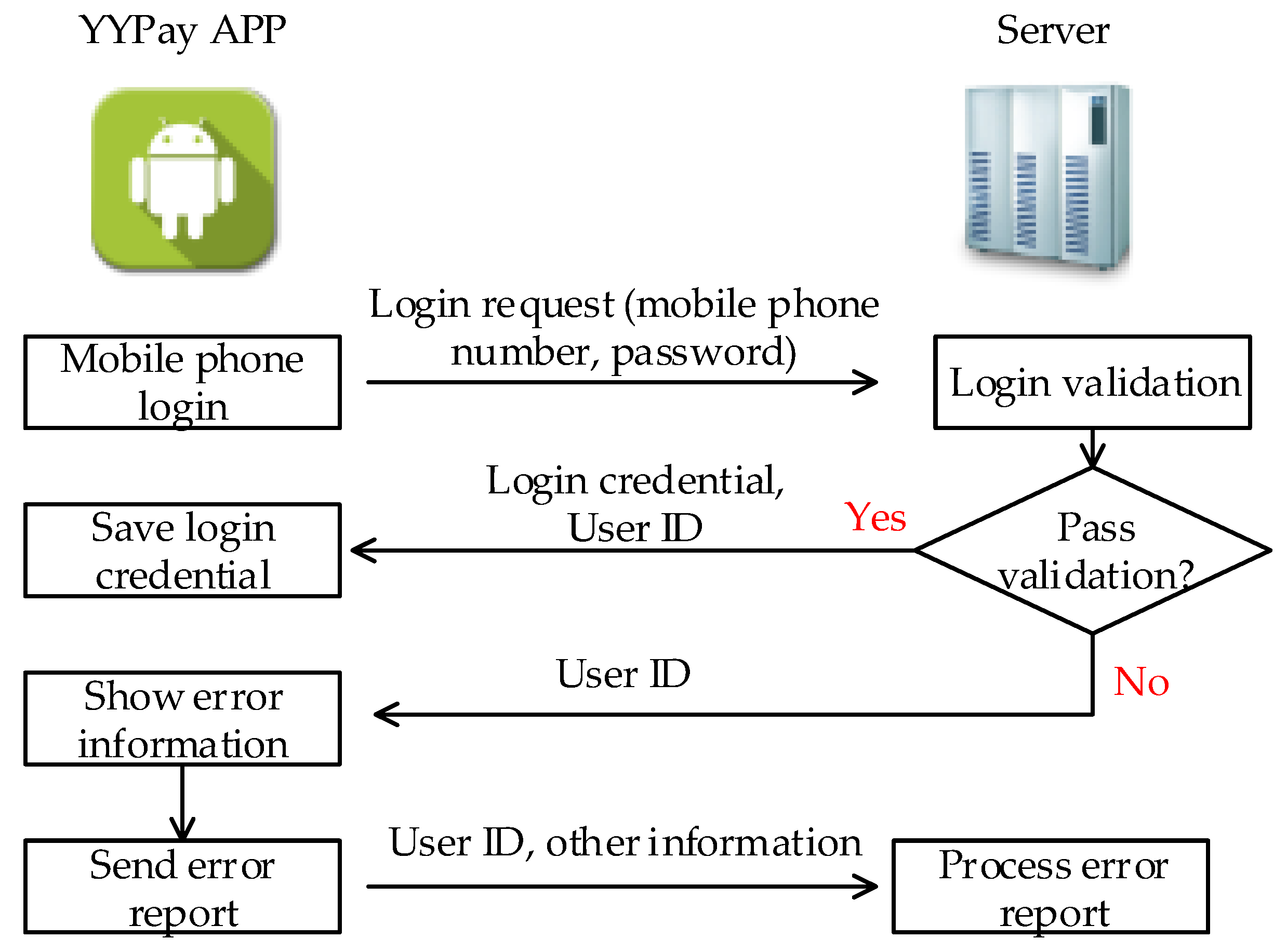
6.1. Login Process Simulation
6.2. Information Query Technique Based on Method-Hook
6.3. Implementation of Trilateration Localization
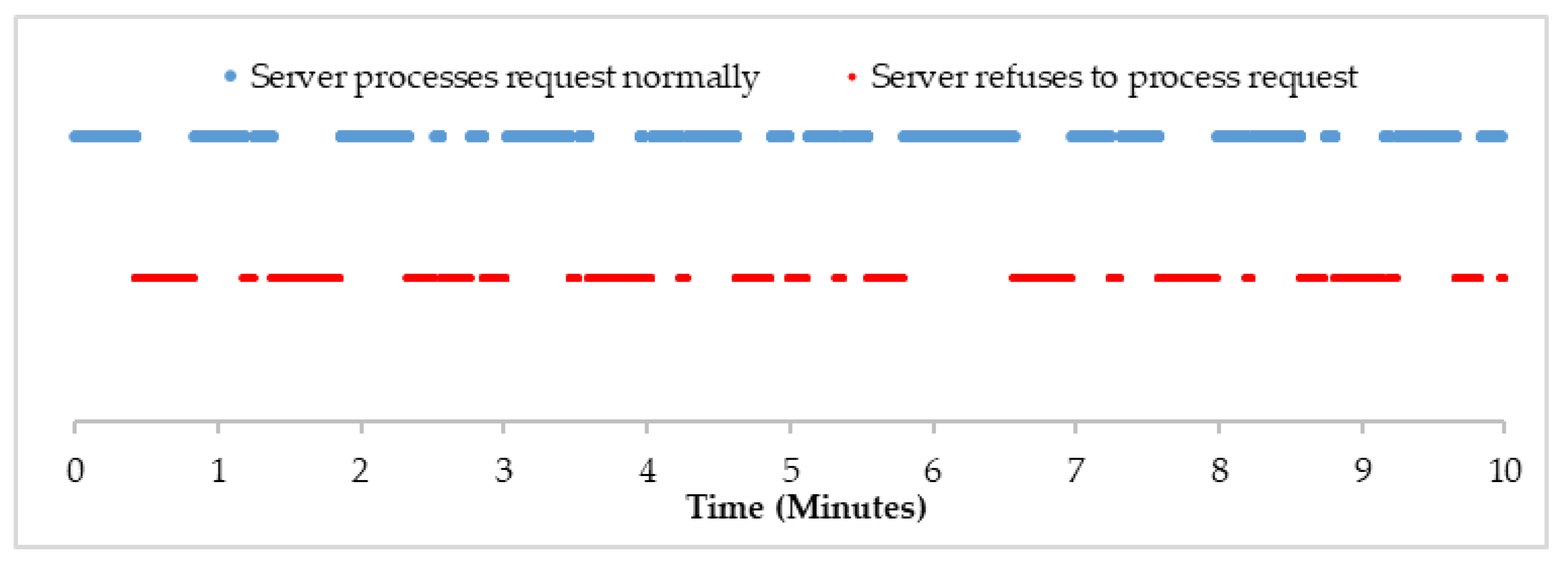
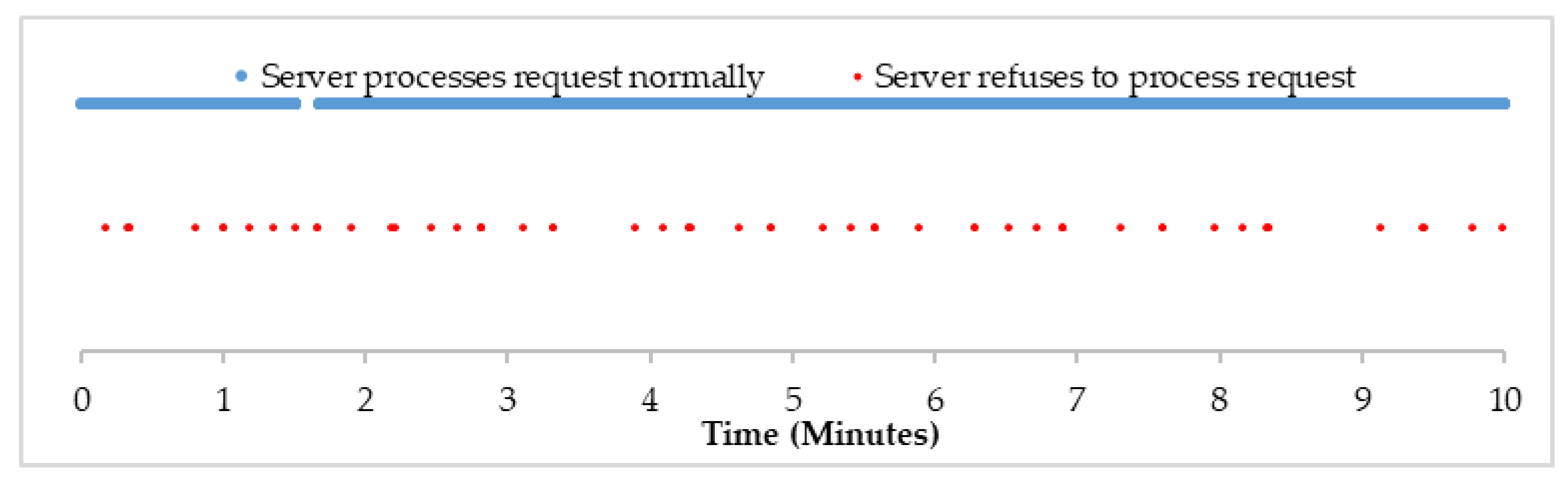
7. Breaking Effect
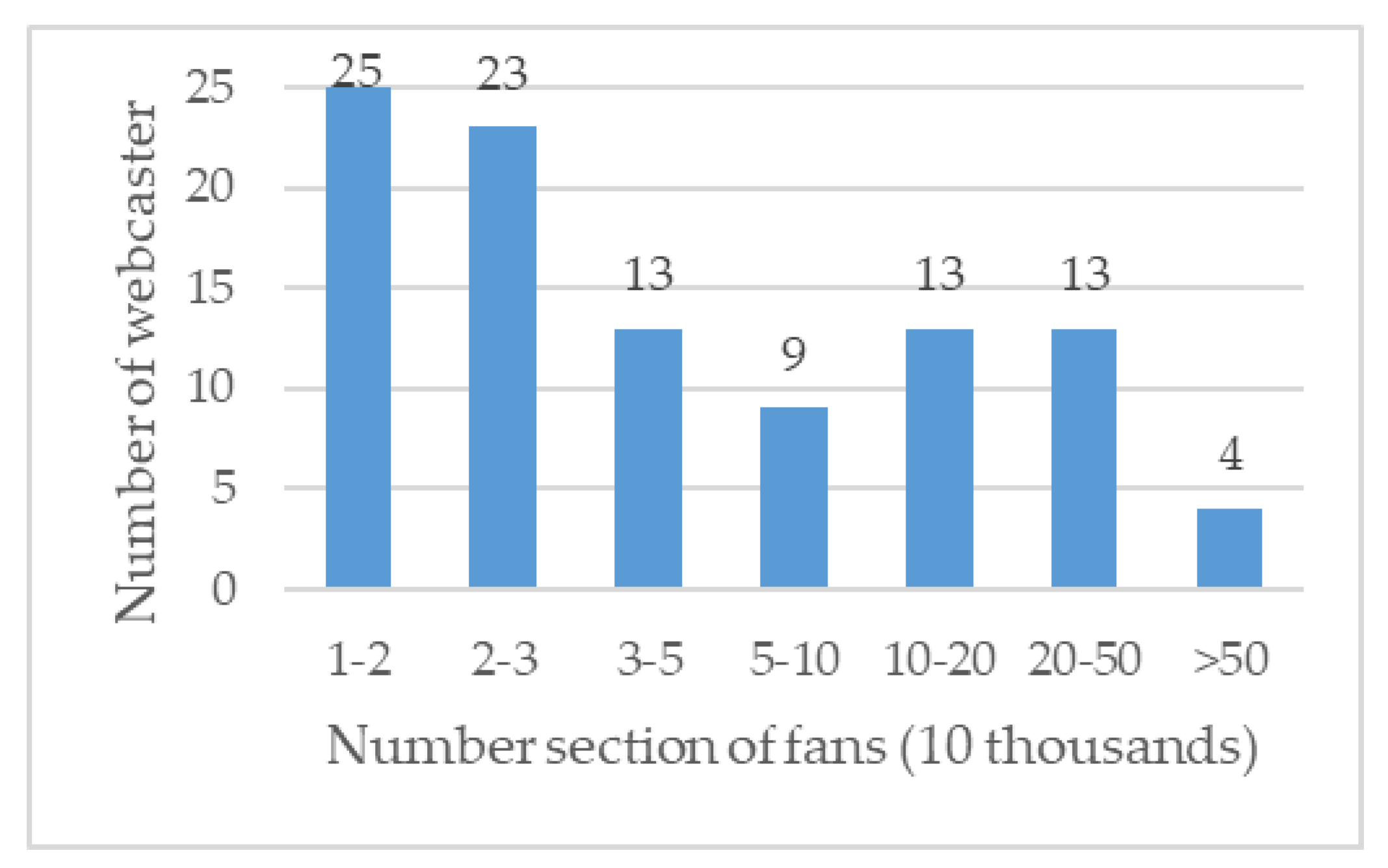
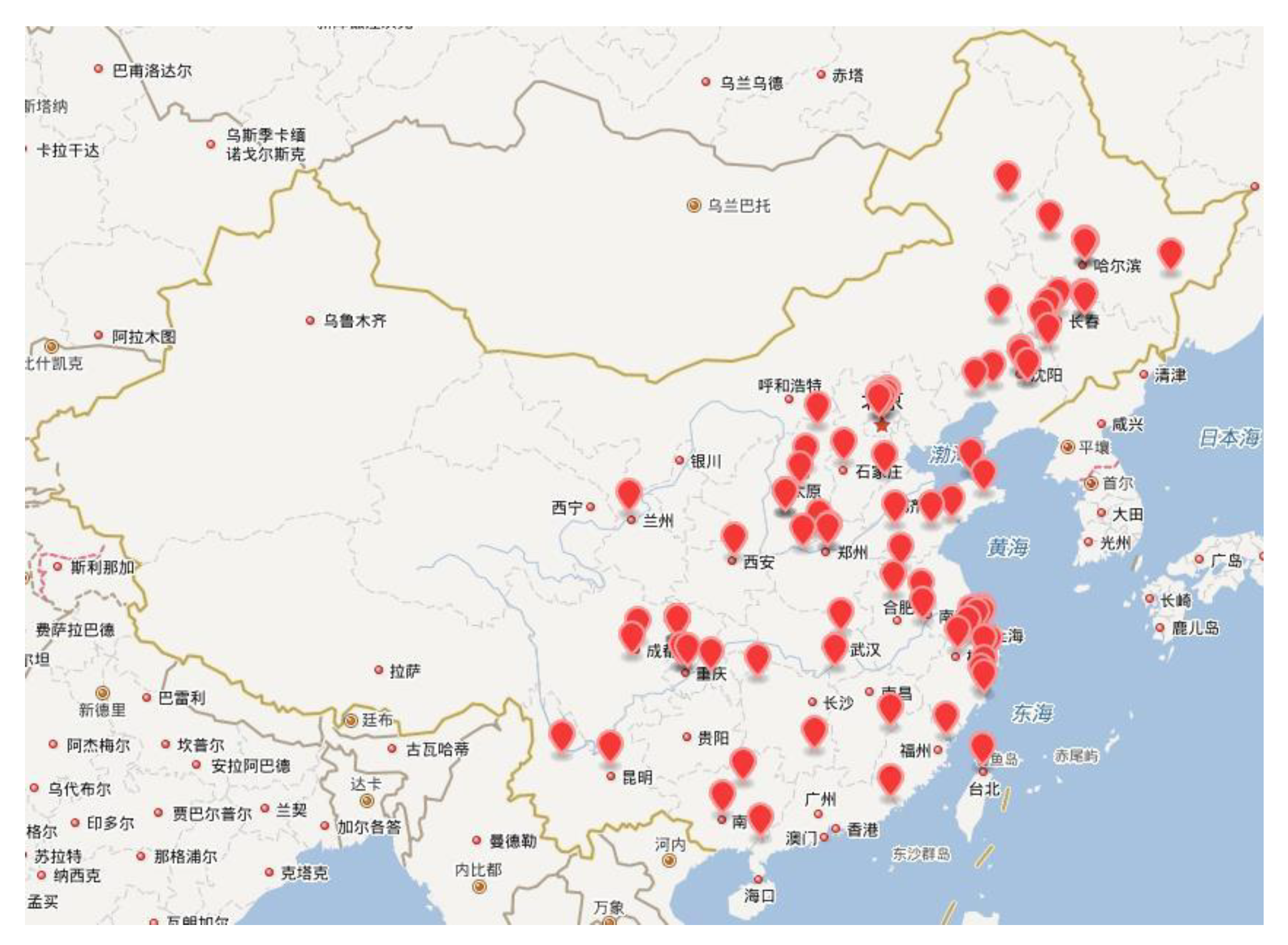
7.1. Test Set Construction
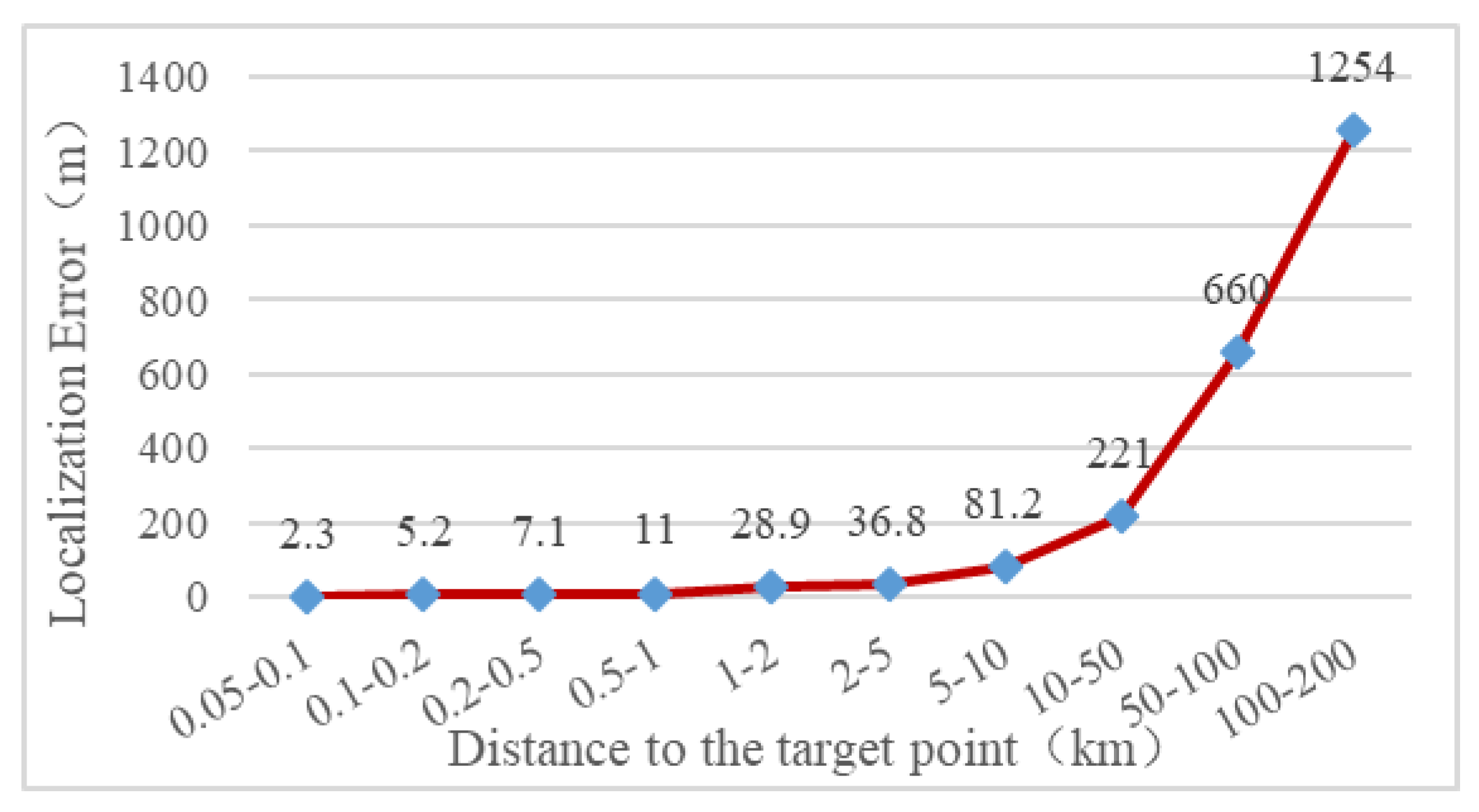
7.2. Localization Effect
7.3. Effect of Mobile Phone Number Breaking
8. Security Precaution Suggestions
9. Related Work
10. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Andrienko, G.; Gkoulalas-Divanis, A.; Gruteser, M. Report from Dagstuhl: The liberation of mobile location data and its implications for privacy research. ACM SIGMOBILE Mob. Comput. Commun. Rev. 2013, 17, 7–18. [Google Scholar] [CrossRef]
- Kushwaha, A.; Kushwaha, V. Location based services using android mobile operating system. Int. J. Adv. Eng. Technol. 2011, 1, 14–20. [Google Scholar]
- Li, M.; Zhu, H.; Gao, Z.; Chen, S.; Yu, L.; Hu, S.; Ren, K. All your location are belong to us: Breaking mobile social networks for automated user location tracking. In Proceedings of the 15th ACM International Symposium on Mobile ad Hoc Networking and Computing, Philadelphia, PA, USA, 11–14 August 2014; pp. 154–196. [Google Scholar]
- Polakis, I.; Argyros, G.; Petsios, T.; Sivakorn, S.; Keromytis, A.D. Where’s Wally?: Precise user discovery attacks in location proximity services. In Proceedings of the 22nd ACM SIGSAC Conference on Computer and Communications Security, Denver, CO, USA, 12–16 October 2015; pp. 817–828. [Google Scholar]
- Xue, M.; Liu, Y.; Ross, K.W.; Qian, H. I know where you are: Thwarting privacy protection in location-based social discovery services. In Proceedings of the 2015 IEEE Conference on Computer Communications Workshops, Hong Kong, China, 26 April–1 May 2015; pp. 179–184. [Google Scholar]
- Hoang, N.P.; Asano, Y.; Yoshikawa, M. Your neighbors are my spies: Location and other privacy concerns in dating apps. In Proceedings of the 18th International Conference on Advanced Communication Technology, Pyeongchang, Korea, 31 January–3 February 2016; pp. 715–721. [Google Scholar]
- Fawaz, K.; Feng, H.; Kang, G.S. Anatomization and protection of mobile apps’ location privacy threats. In Proceedings of the 24th USENIX Security Symposium, Washington, DC, USA, 12–14 August 2015; pp. 753–768. [Google Scholar]
- Hallsteinsen, S.; Jorstad, I.; Thanh, D.V. Using the mobile phone as a security token for unified authentication. In Proceedings of the 2nd International Conference on Systems and Networks Communications, Cap Esterel, France, 25–31 August 2007; p. 68. [Google Scholar]
- Bertino, E.; Sandhu, R. Database security—Concepts, approaches, and challenges. IEEE Trans. Dependable Secur. Comput. 2005, 2, 2–19. [Google Scholar] [CrossRef]
- Halfond, W.G.J.; Viegas, J.; Orso, A. A classification of SQL-injection attacks and countermeasures. In Proceedings of the 2006 IEEE International Symposium on Secure Software Engineering, McLean, VA, USA, 13–15 March 2006. [Google Scholar]
- Fleizach, C.; Liljenstam, M.; Johansson, P.; Voelker, G.M.; Mehes, A. Can you infect me now?: Malware propagation in mobile phone networks. In Proceedings of the 5th ACM Workshop on Recurring Malcode, Alexandria, VA, USA, 2 November 2007; pp. 61–68. [Google Scholar]
- Felt, A.P.; Finifter, M.; Chin, E.; Hanna, S.; Wagner, D. A survey of mobile malware in the wild. In Proceedings of the 1st ACM Workshop on Security and Privacy in Smartphones and Mobile Devices, Chicago, IL, USA, 17 October 2011; pp. 3–14. [Google Scholar]
- Cheng, Y.; Ying, L.; Jiao, S.; Su, P.; Feng, D. Bind your phone number with caution: Automated user profiling through address book matching on smartphone. In Proceedings of the 8th ACM SIGSAC Symposium on Information, Computer and Communications Security, Hangzhou, China, 8–10 May 2013; pp. 335–340. [Google Scholar]
- Kim, E.; Park, K.; Kim, H.; Song, J. Design and analysis of enumeration attacks on finding friends with phone numbers: A case study with KakaoTalk. Comput. Secur. 2015, 52, 267–275. [Google Scholar] [CrossRef]
- Gupta, S.; Gupta, P.; Ahamad, M.; Kumaraguru, P. Exploiting phone numbers and cross-application features in targeted mobile attacks. In Proceedings of the 6th Workshop on Security and Privacy in Smartphones and Mobile Devices, Vienna, Austria, 24 October 2016; pp. 73–82. [Google Scholar]
- Schrittwieser, S.; Fruehwirt, P.; Kieseberg, P.; Leithner, M.; Mulazzani, M.; Huber, M.; Weippl, E. Guess who is texting you? Evaluating the security of smartphone messaging applications. In Proceedings of the 19th Annual Network & Distributed System Security Symposium, San Diego, CA, USA, 5–8 February 2012. [Google Scholar]
- Kim, E.; Park, K.; Kim, H.; Song, J. I’ve got your number: Harvesting users’ personal data via contacts sync for the KakaoTalk Messenger. In Proceedings of the 15th International Workshop on Information Security Applications, Jeju Island, Korea, 25–27 August 2014. [Google Scholar]
- Gupta, S. Emerging threats abusing phone numbers exploiting cross-platform features. In Proceedings of the 2016 IEEE/ACM International Conference on Advances in Social Networks Analysis and Mining, San Francisco, CA, USA, 18–21 August 2016; pp. 1339–1341. [Google Scholar]
- Murphy, W.; Hereman, W. Determination of a Position in Three Dimensions Using Trilateration and Approximate Distances; Technical Report: MCS-95-07; Department of Mathematical and Computer Sciences, Colorado School of Mines: Golden, CO, USA, 1995. [Google Scholar]







| App | Ways of Exposing Geographical Location | Number of Digits Be Exposed | Ways of Exposing Mobile Phone Number |
|---|---|---|---|
| Sina Weibo | Personal homepage | 6 | Retrieve password |
| Alipay | Personal homepage | 5 | Retrieve password |
| KuGou | Citywide user search | 6 | Retrieve password |
| Personal homepage, nearby user search | 3 | Retrieve password | |
| Baidu Account | Citywide user search | 5 | Retrieve password |
| 360 Account | Citywide user search | 6 | Retrieve password |
| YY | Personal homepage, location of the user’s recent login | 5 | Retrieve password, recharge for others |
| Carrier | First Three Digits of Mobile Phone Number |
|---|---|
| China Unicom | 139, 138, 137, 136, 135, 134, 159, 158, 157, 150, 151, 152, 147, 188, 187, 182, 183, 184, 178 |
| China Mobile | 130, 131, 132, 156, 155, 186, 185, 145, 176 |
| China Telecom | 133, 153, 189, 180, 181, 177 |
| Platform | Login Method | Registration Method |
|---|---|---|
| PC-end Software | YY account number, mobile phone number, username, email | Mobile phone number, username, email |
| Mobile App | YY account number, mobile phone number, Username, email, Weibo, WeChat, QQ, mobile phone verification code | Mobile phone number |
| Webpage | YY account number, mobile phone number, username, email, Weibo, WeChat, QQ | Mobile phone number, email |
| L1 | L1 = Null | L1 ≠ Null | Total | |
|---|---|---|---|---|
| L2 | ||||
| L2 = Null | 26 | 38 (L1 = L2) | 88 | |
| 24 (L1 ≠ L2) | ||||
| L2 ≠ Null | 2 | 10 | 12 | |
| Total | 28 | 72 | 100 | |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Yue, H.; Guo, H.; Ma, X. Breaking Users’ Mobile Phone Number Based on Geographical Location: A Case Study with YY. Information 2018, 9, 200. https://doi.org/10.3390/info9080200
Yue H, Guo H, Ma X. Breaking Users’ Mobile Phone Number Based on Geographical Location: A Case Study with YY. Information. 2018; 9(8):200. https://doi.org/10.3390/info9080200
Chicago/Turabian StyleYue, Hongzhou, Huaping Guo, and Xingpo Ma. 2018. "Breaking Users’ Mobile Phone Number Based on Geographical Location: A Case Study with YY" Information 9, no. 8: 200. https://doi.org/10.3390/info9080200
APA StyleYue, H., Guo, H., & Ma, X. (2018). Breaking Users’ Mobile Phone Number Based on Geographical Location: A Case Study with YY. Information, 9(8), 200. https://doi.org/10.3390/info9080200






