Design of IoT-based Cyber–Physical Systems: A Driverless Bulldozer Prototype
Abstract
1. Introduction
2. Description of Communication Technologies
2.1. General Packet Radio Service (GPRS)
2.2. Message Queuing Telemetry Transport (MQTT)
3. System Design Setup and Diagram
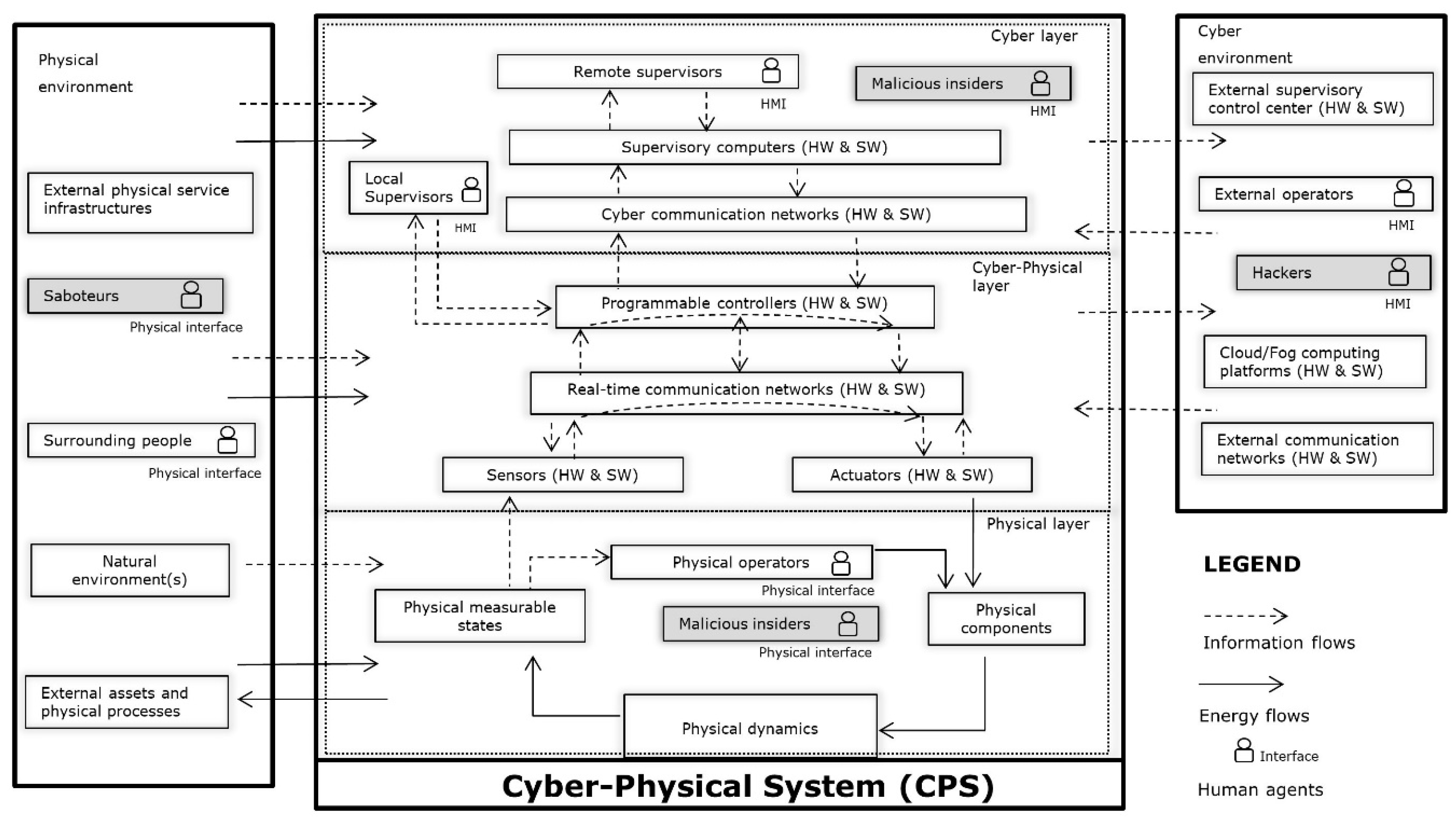
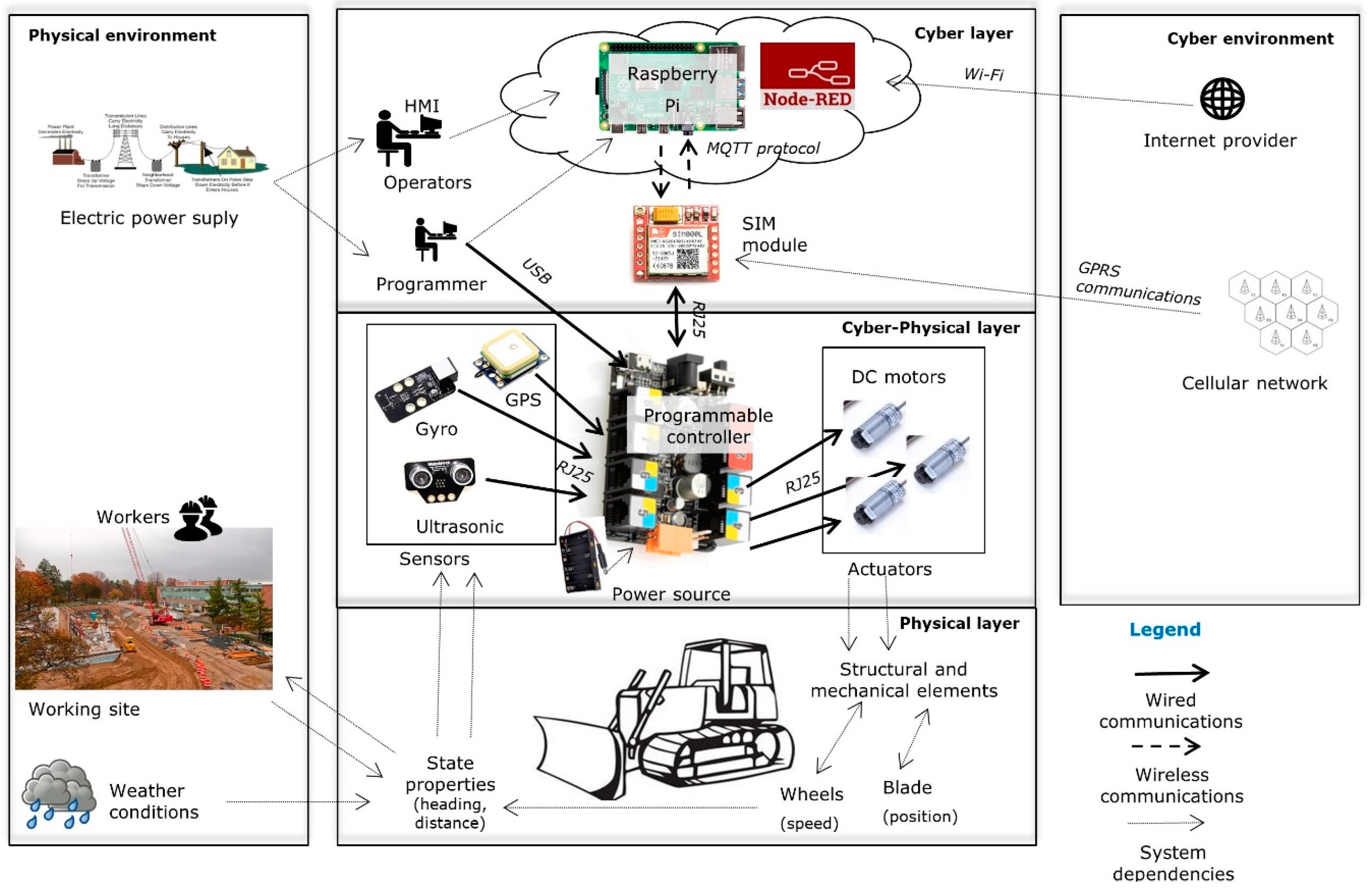
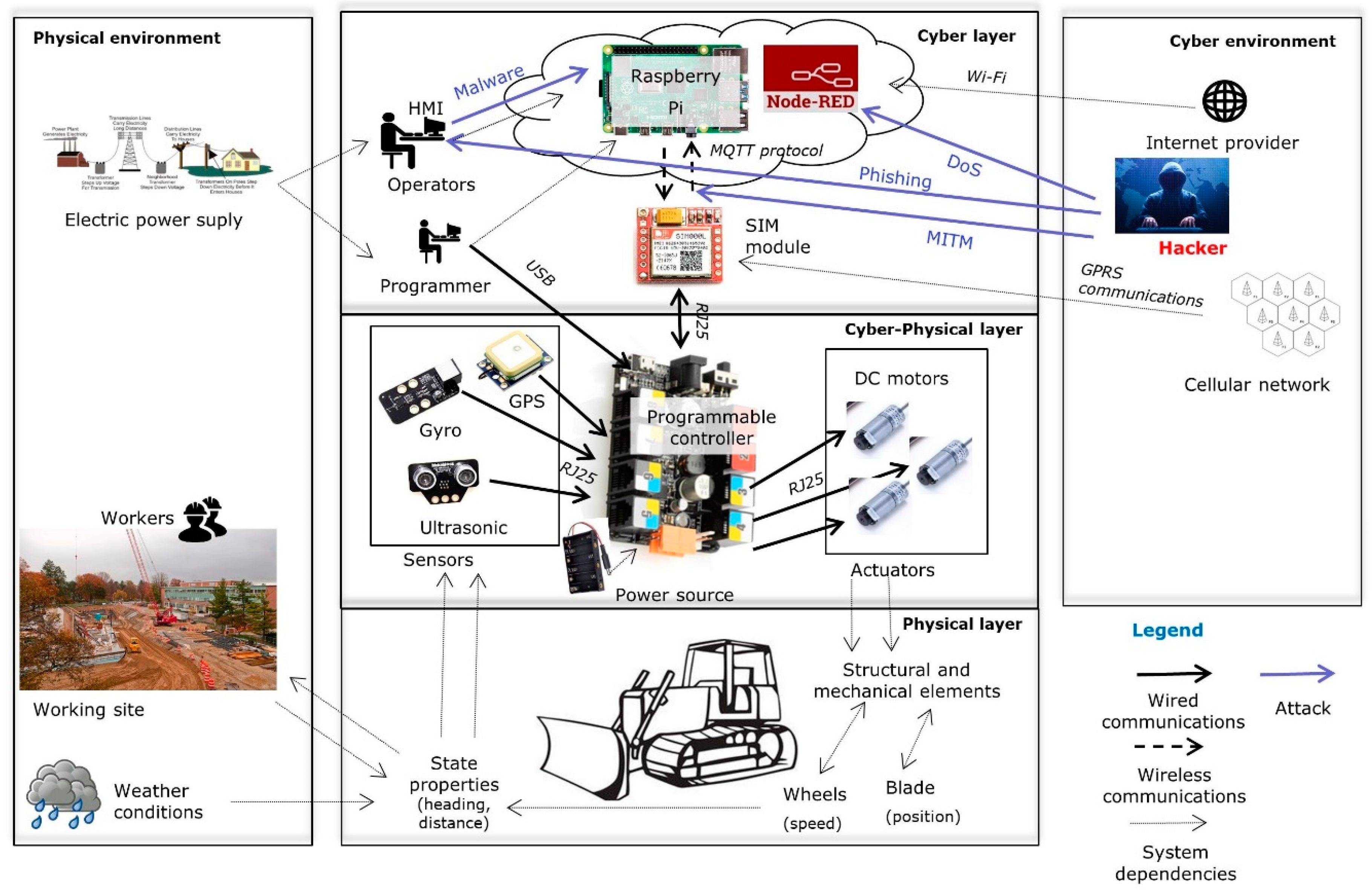
3.1. Layered Functional Diagram
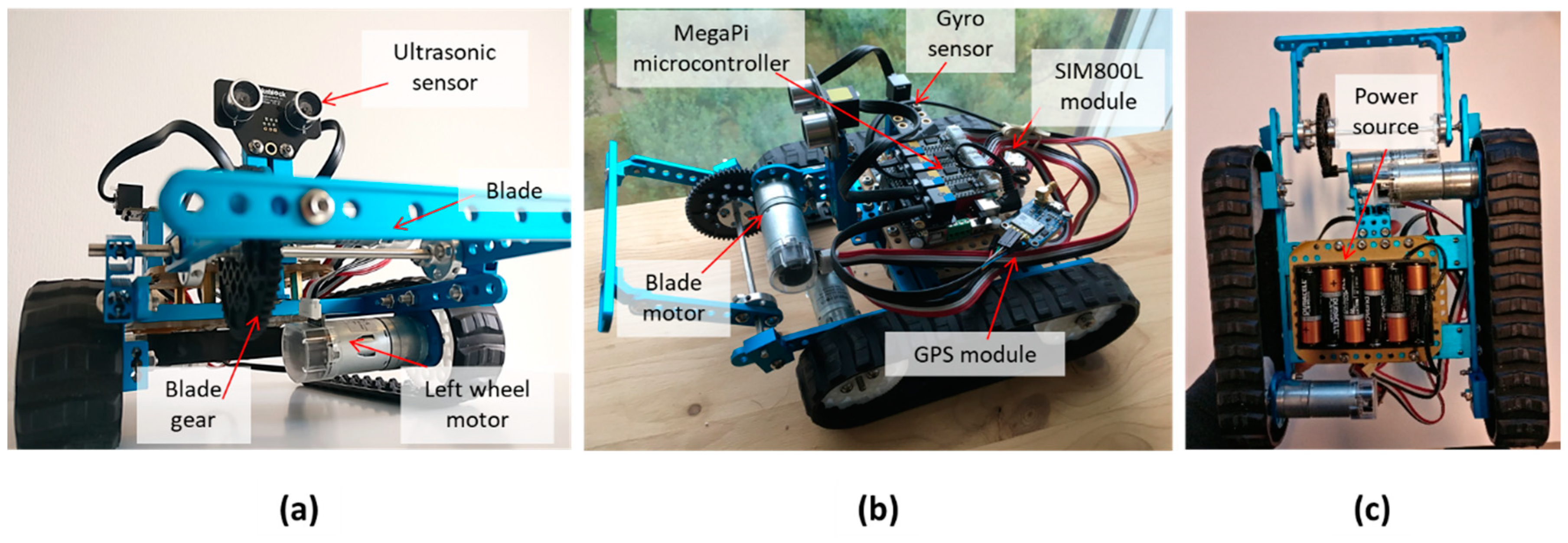
3.2. Bulldozer Physical Built System
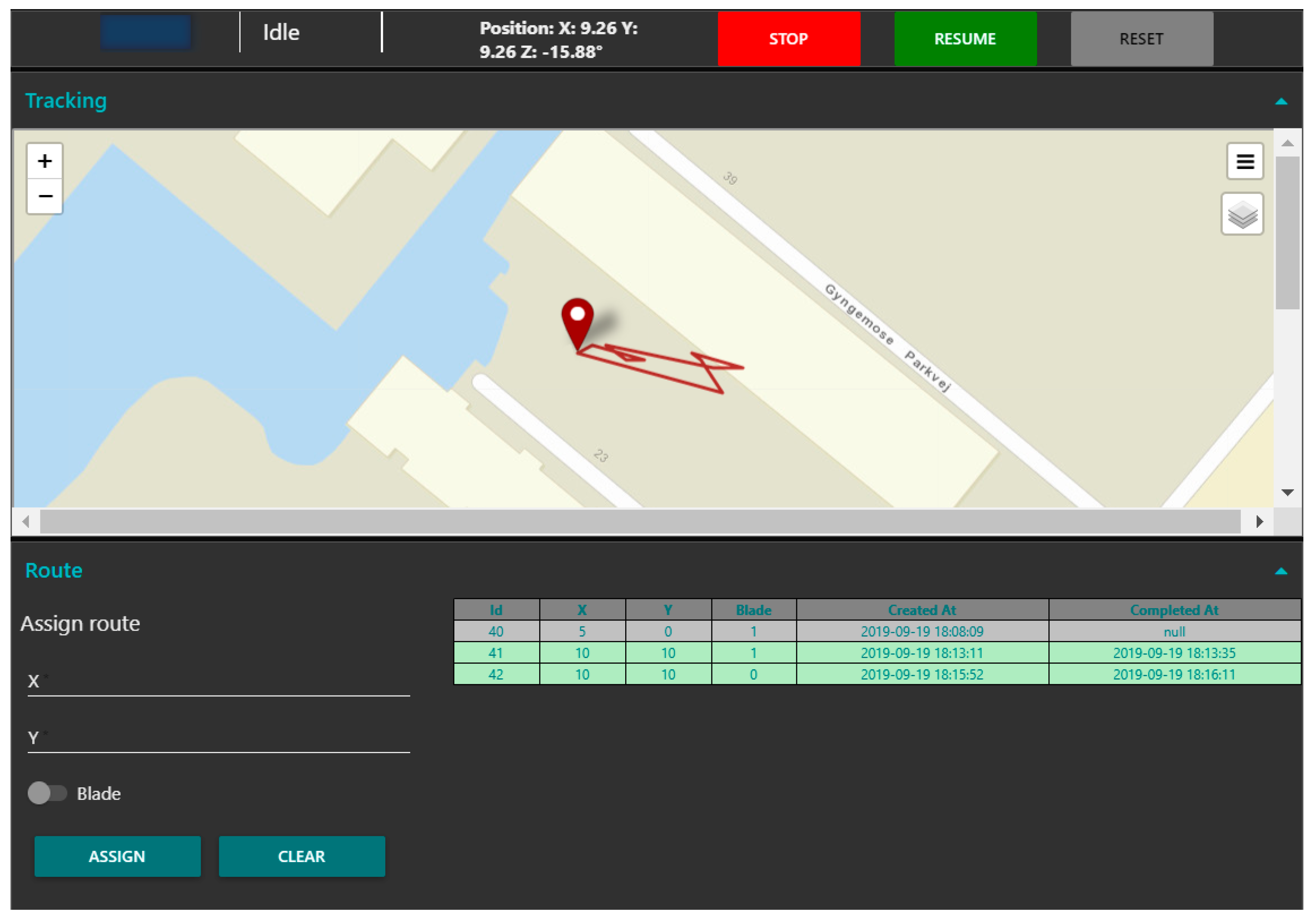
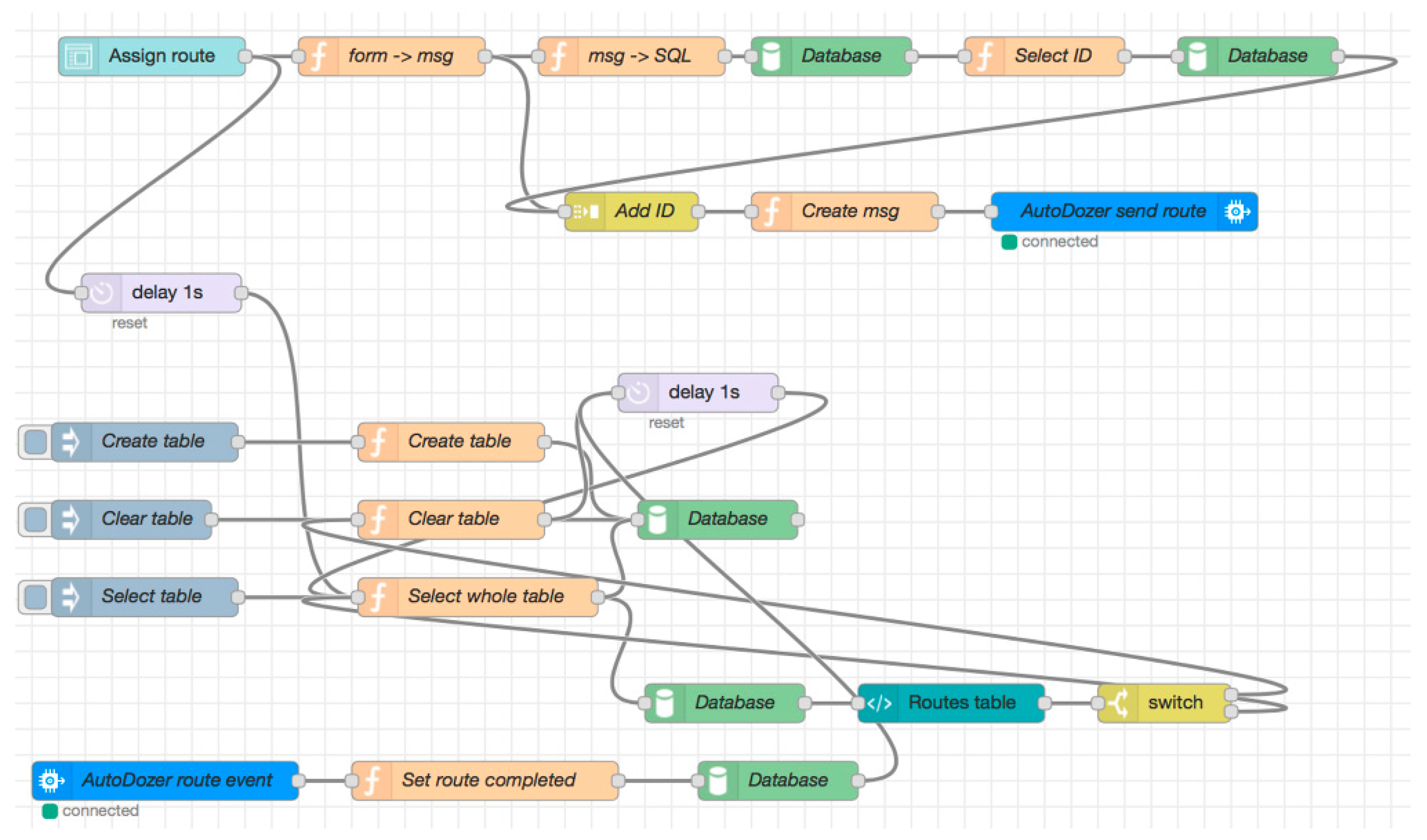
3.3. Cloud Application and User Interface
3.4. Conceptual Design of Physical Processes
4. Results
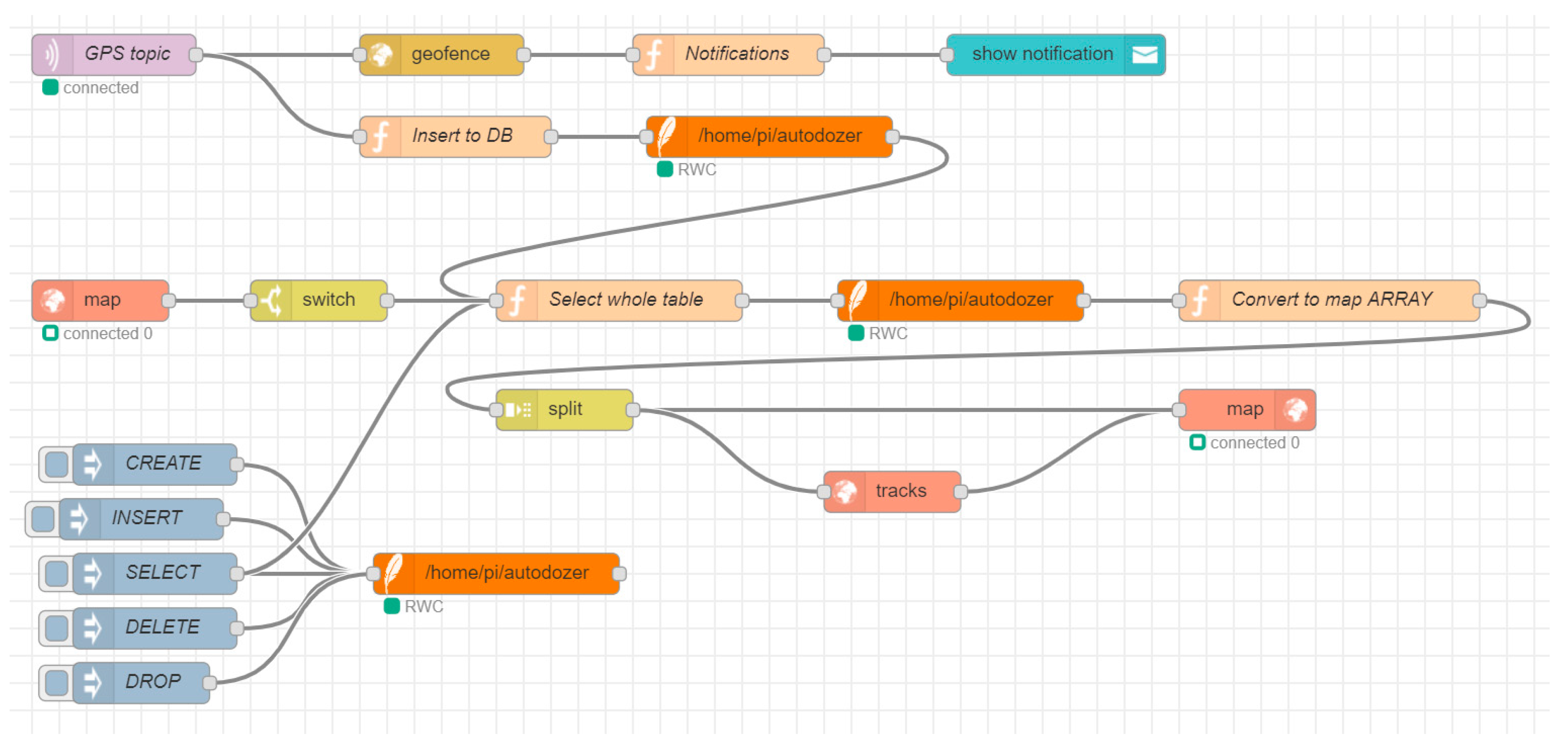
4.1. Discussion of GPS Tracking System
4.2. Preliminary Safety and Security Assessment
4.2.1. Scenario 1: Phishing Attack and Malware Infection
4.2.2. Scenario 2: Man-In-The-Middle (MITM) attack
4.2.3. Scenario 3: Denial of Service (DoS) attack
4.2.4. Discussion on Preliminary Safety and Security Assessment
5. Further Developments
6. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Guzman, N.H.C.; Wied, M.; Kozine, I.; Lundteigen, M.A. Conceptualizing the key features of cyber-physical systems in a multi-layered representation for safety and security analysis. Syst. Eng. 2019, 1–22. [Google Scholar] [CrossRef]
- Rajkumar, R.; Lee, I.L.I.; Sha, L.S.L.; Stankovic, J. Cyber-physical systems: The next computing revolution. In Proceedings of the Design Automation Conference, Anaheim, CA, USA, 13–18 June 2010; pp. 731–736. [Google Scholar]
- Lee, E.A.; Seshia, S.A. Introduction to Embedded Systems: A Cyber-Physical Systems Approach, 2nd ed.; The MIT Press: Cambridge, MA, USA, 2017. [Google Scholar]
- Ge, X.; Yang, F.; Han, Q.L. Distributed networked control systems: A brief overview. Inf. Sci. 2017, 380, 117–131. [Google Scholar] [CrossRef]
- Atzori, L.; Iera, A.; Morabito, G. The Internet of Things: A survey. Comput. Netw. 2010, 54, 2787–2805. [Google Scholar] [CrossRef]
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A vision, architectural elements, and future directions. Future Gener. Comput. Syst. 2013, 29, 1645–1660. [Google Scholar] [CrossRef]
- Monostori, L. Cyber-physical production systems: Roots, expectations and R & D challenges. Procedia CIRP 2014, 17, 9–13. [Google Scholar]
- Jazdi, N. Cyber physical systems in the context of Industry 4.0. In Proceedings of the 2014 IEEE International Conference on Automation, Quality and Testing, Robotics, Cluj-Napoca, Romania, 22–24 May 2014; pp. 1–4. [Google Scholar]
- European Commission. Mobile Machinery. In Growth: Internal Market, Industry, Entrepreneurship and SMEs; 2018; Available online: https://ec.europa.eu/growth/sectors/mechanical-engineering/mob_machinery_en (accessed on 5 July 2018).
- Simonite, T. Mining 24 Hours a Day with Robots. MIT Technol. Rev. 2016. Available online: https://www.technologyreview.com/s/603170/mining-24-hours-a-day-with-robots/ (accessed on 6 July 2018).
- Underwood, C. The Future of AI in Heavy Industry—Agriculture, Construction, Mining, and Beyond. Techemergence 2018. Available online: https://www.techemergence.com/future-ai-in-heavy-industry/ (accessed on 6 July 2018).
- Pedersen, S.M.; Fountas, S.; Have, H.; Blackmore, B.S. Agricultural robots—System analysis and economic feasibility. Precis. Agric. 2006, 7, 295–308. [Google Scholar] [CrossRef]
- Stentz, A.; Dima, C.; Wellington, C.; Herman, H.; Stager, D. A System for Semi—Autonomous Tractor Operations. Auton. Robots 2002, 13, 87–104. [Google Scholar] [CrossRef]
- Muoio, D. Google Just Made a Big Move to bring Down the Cost of Self-Driving Cars. Bus. Insider 2017. Available online: http://www.businessinsider.com/googles-waymo-reduces-lidar-cost-90-in-effort-to-scale-self-driving-cars-2017-1?r=US&IR=T&IR=T (accessed on 6 July 2018).
- Wilson, J.N. Guidance of agricultural vehicles - A historical perspective. Comput. Electron. Agric. 2000, 25, 3–9. [Google Scholar] [CrossRef]
- Mousazadeh, H. A technical review on navigation systems of agricultural autonomous off-road vehicles. J. Terramech. 2013, 50, 211–232. [Google Scholar] [CrossRef]
- Nørremark, M.; Griepentrog, H.W.; Nielsen, J.; Søgaard, H.T. The development and assessment of the accuracy of an autonomous GPS-based system for intra-row mechanical weed control in row crops. Biosyst. Eng. 2008, 101, 396–410. [Google Scholar] [CrossRef]
- Caterpillar Inc. Caterpillar Mining Technology: Autonomous Trucks. 2014. Available online: https://www.youtube.com/watch?v=VkanknGePhc (accessed on 26 April 2018).
- CNH Industrial. The CNH Industrial Autonomous Tractor Concept (Full Version). 2016. Available online: https://www.youtube.com/watch?v=T7Os5Okf3OQ (accessed on 26 April 2018).
- Guzman, N.H.C.; Mezovari, A.G.; Yan, Y.; Petersen, M.L. An IoT-Based Prototype of a Driverless Bulldozer. In Proceedings of the 2019 15th International Conference on Distributed Computing in Sensor Systems (DCOSS), Santorini Island, Greece, 29–31 May 2019; pp. 291–296. [Google Scholar]
- Tardy, I.; Aakvaag, N.; Myhre, B.; Bahr, R. Comparison of Wireless Techniques Applied to Environmental Sensor Monitoring. 2017. Available online: https://www.sintef.no/en/publications/publication/?pubid=CRIStin+1461936: (accessed on 4 November 2019).
- Vejlgaard, B.; Lauridsen, M.; Nguyen, H.; Kovacs, I.Z.; Mogensen, P.; Sorensen, M. Coverage and Capacity Analysis of Sigfox, LoRa, GPRS, and NB-IoT. In Proceedings of the 2017 IEEE 85th Vehicular Technology Conference, Sydney, NSW, Australia, 4–7 June 2017. [Google Scholar]
- Wang, H.; Fapojuwo, A.O. A Survey of Enabling Technologies of Low Power and Long Range Machine-to-Machine Communications. IEEE Commun. Surv. Tutor. 2017, 19, 2621–2639. [Google Scholar] [CrossRef]
- Al-Fuqaha, A.; Guizani, M. Internet of things: A survey on enabling technologies, protocols, and applications. IEEE Commun. Surv. Tutor. 2015, 17, 2347–2376. [Google Scholar] [CrossRef]
- Eclipse Foundation. Eclipse MosquittoTM. An Open Source MQTT Broker. Available online: https://mosquitto.org/ (accessed on 1 August 2018).
- Guzman, N.H.C.; Mezovari, A. Design of IoT-Based Cyber-Physical Systems: A Driverless Bulldozer Prototype (Open-Source Code). Available online: https://orbit.dtu.dk/en/projects/design-of-iotbased-cyberphysical-systems-a-driverless-bulldozer-prototype-opensource-code(7dc1c4e3-e706-42c4-86e2-589cb4f27631).html (accessed on 31 October 2019).
- Ublox. NEO-6 U-Blox 6 GPS Modules: Data Sheet. 2011. Available online: https://www.u-blox.com/sites/default/files/products/documents/NEO-6_DataSheet_(GPS.G6-HW-09005).pdf (accessed on 30 October 2019).
- Koscher, K.; Czeskis, A.; Roesner, F.; Patel, S.; Kohno, T.; Checkoway, S.; McCoy, D.; Kantor, B.; Anderson, D.; Shacham, H.; et al. Experimental security analysis of a modern automobile. In Proceedings of the 2010 IEEE Symposium on Security and Privacy, Berkeley/Oakland, CA, USA, 16–19 May 2010; pp. 447–462. [Google Scholar]
- Drozhzhin, A. Black Hat USA 2015: The full story of how that Jeep was hacked. Kaspersky Lab Dly. 2015. Available online: https://www.kaspersky.com/blog/blackhat-jeep-cherokee-hack-explained/9493/ (accessed on 10 December 2018).
- Guzman, N.H.C.; Kufoalor, D.K.M.; Kozine, I.; Lundteigen, M.A. Combined safety and security risk analysis using the UFoI-E method: A case study of an autonomous surface vessel. In Proceedings of the 29th European Safety and Reliability Conference, Lower Saxony, Germany, 22–26 September 2019. [Google Scholar]
| Feature | Cellular (GPRS) | Wifi (802.11ah) | LoRa | Sigfox | NB-IoT |
|---|---|---|---|---|---|
| Max range | 15 km | 1 km | 15 km | 50 km | 15 km |
| Max data rate (up/down) | 20/114 kbps | 7.8/7.8 Mbps | 100/100 kbps | 100/100 kbps | 64/128 kbps |
| Scalability | High | Limited | Very Low | Low | High |
| Power need | High | High | Low | Low | Medium |
| Cost | Low | Medium | High | Low | Medium |
| Frequency band | Reserved | Open | Open | Open | Reserved |
| Function | Mechanisms | Result |
|---|---|---|
| Store and report routes assigned and completed | (1) Database of routes assigned and completed reported in UI (2) Database of obstacles encountered reported in UI | Reliable execution |
| Geospatial visualization of bulldozer routes | (1) Map visualizations in UI (2) Bulldozer GPS route tracking displayed in UI | Accuracy 2.5 m and close to real-time (<30 s delay) |
| Human–Computer Interactions | (1) UI with visual and audio notifications (2) UI heading status reports | Reliable execution and real-time (<3 s delay) |
| Route assignment | (1) Route assignment fields(2) Route assignment buttons | Reliable execution |
| Obstacle detection function in bulldozer | (1) Detection sensor (ultrasonic) (2) Stop function in control logic in microcontroller | Limited range Unreliable execution |
| Route accuracy followed by bulldozer | (1) Encoder motors (2) Control logic in microcontroller | Reliable execution of commands Limited accuracy in turning and driving forward (average 10% path deviations in route points) |
| Two-way communications UI-microcontroller | (1) GSM module (2) MQTT protocol with eight different topics (3) Integration with Node-red UI | High classification reliability Medium connection reliability (partial disconnections approx. each 20–30 min) |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Carreras Guzman, N.H.; Mezovari, A.G. Design of IoT-based Cyber–Physical Systems: A Driverless Bulldozer Prototype. Information 2019, 10, 343. https://doi.org/10.3390/info10110343
Carreras Guzman NH, Mezovari AG. Design of IoT-based Cyber–Physical Systems: A Driverless Bulldozer Prototype. Information. 2019; 10(11):343. https://doi.org/10.3390/info10110343
Chicago/Turabian StyleCarreras Guzman, Nelson H., and Adam Gergo Mezovari. 2019. "Design of IoT-based Cyber–Physical Systems: A Driverless Bulldozer Prototype" Information 10, no. 11: 343. https://doi.org/10.3390/info10110343
APA StyleCarreras Guzman, N. H., & Mezovari, A. G. (2019). Design of IoT-based Cyber–Physical Systems: A Driverless Bulldozer Prototype. Information, 10(11), 343. https://doi.org/10.3390/info10110343





