Maritime Robotics and Autonomous Systems Operations: Exploring Pathways for Overcoming International Techno-Regulatory Data Barriers
Abstract
1. Introduction
2. Materials and Methods
3. Results
3.1. Theoretical Construct: Dissecting the Dimensions of Data
- Governance mechanisms:
- Identification of the data owner/data manager/data consumer
- allocation of responsibilities
- decision-making authority
- organizational policies and standards
- coordination with the stakeholders;
- Application of governance mechanisms on the organizational scope, data scope, and domain scope:
- Quality and integrity of project-related organizational data
- data governance between firms
- machine-generated data
- privacy requirements
- data architecture
- data lifecycle
- data storage;
- Antecedents of data governance:
- Internal and external factors that precede data governance practices, such as organizational culture and industry;
- Outcomes of data governance:
- Measurement of data governance effectiveness on organizational strategy and business performance [25].
3.2. Carving Out the Stakeholders of Non-Personal Data
3.3. RAS and the Internet of Robotic Things: Through the Prism of Data
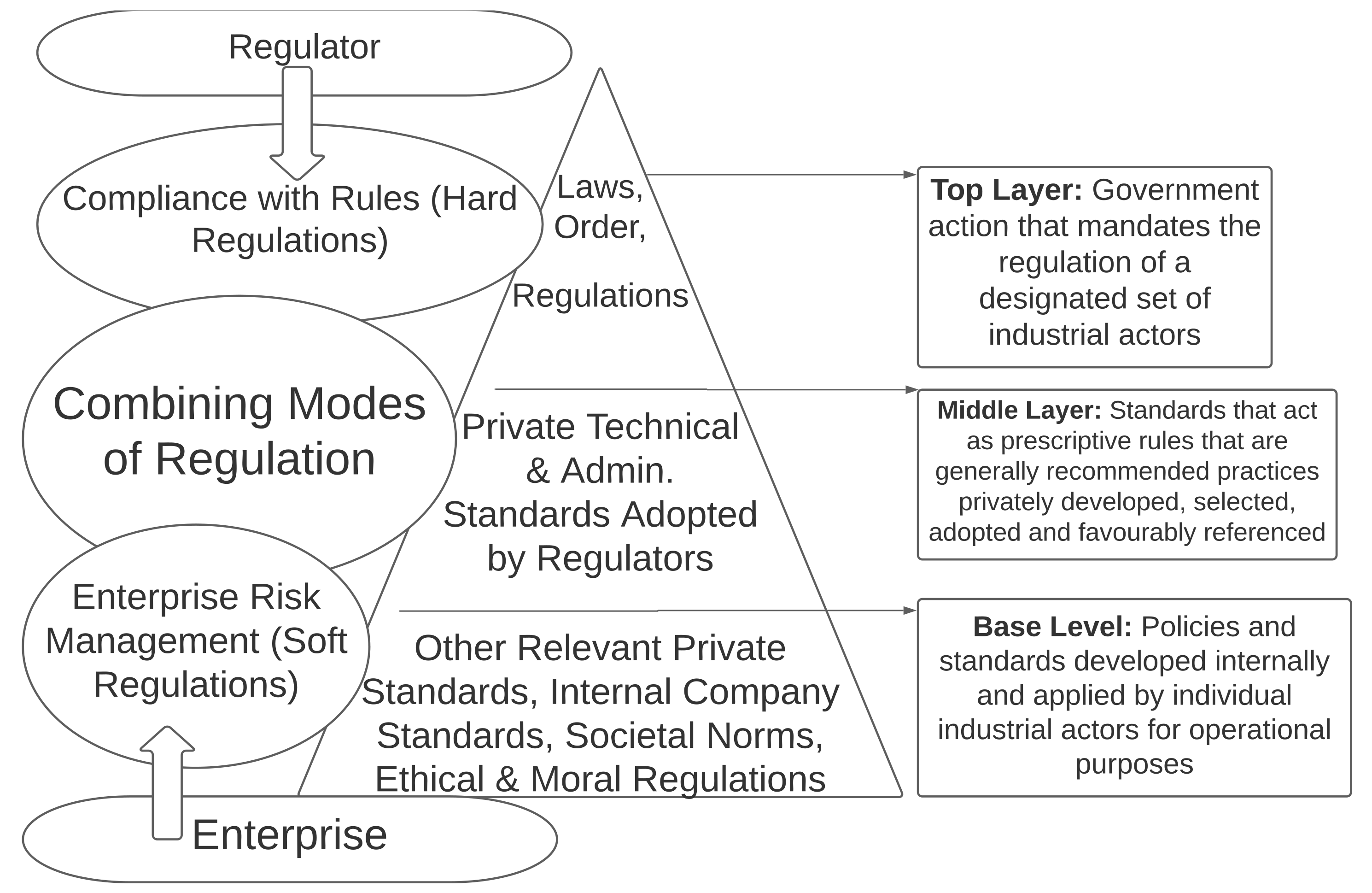
3.4. International Maritime Data Governance Standards
“Goal-based standards (GBS) are high-level standards and procedures that are to be met through regulations, rules and standards for ships. GBS are comprised of at least one goal, functional requirement(s) associated with that goal, and verification of conformity that rules/regulations meet the functional requirements including goals. In order to meet the goals and functional requirements, classification societies acting as recognized organizations (ROs) and/or national Administrations will develop rules and regulations accordingly. These detailed requirements become a part of a GBS framework when they have been verified, by independent auditors and/or appropriate IMO organs, as conforming to the GBS”.
“When computers are used for the acquisition, processing, recording, reporting, storage, measurement assessment and monitoring of data, the ability of computer software to satisfy the intended application shall be documented and confirmed by the service supplier. This shall be undertaken prior to initial use and reconfirmed as necessary.”[62]
3.5. Comparative Insight: RAS Data Governance Best Practices
3.6. Hovering over RAS Governance Gray Areas
4. Discussion Based on Priori Synthesis: Ways Forward
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Appendix A. Tabular Amalgamation of Published Literature and Primary Sources Based on Selection Criteria
| Selection Criteria: Literature on Data and Information | |
| Author(s) | Title (Year of Publication) |
| Zins, C. | What is the meaning of “data”, “information”, and “knowledge”? |
| Selection Criteria: Literature on Data and Asset | |
| Author(s) | Title (Year of Publication) |
| Lake, P.; Crowther, P. | Data an Organizational Asset. In Concise Guide to Databases (2013) |
| Selection Criteria: Literature on Big Data | |
| Author(s) | Title (Year of Publication) |
| Boyd, D.; Crawford, K. | Critical Questions for Big Data: Critical Questions for Big Data (2012) |
| Zhang, S.; Gao, H.; Yang, L. and Song, J. | Research on big data governance based on actor-network theory and Petri nets. In IEEE 21st International Conference on Computer Supported Cooperative Work in Design (CSCWD) (2017) |
| Johansson, T.; Long, R.; Dalaklis, D. | The Role of WMU-Sasakawa Global Ocean Institute in the Era of Big Data (2019) |
| Selection Criteria: Data Governance | |
| Author(s) | Title (Year of Publication) |
| McGilvray, D. | Data governance: The Missing Link for Data Quality Success. San Francisco Bay Area (2006) |
| Khatri, V.; Brown, C.V. | Designing data governance. Communications of the ACM (2010) |
| Al-Badi, A; Tarhini, A.; Khan, A.I. | Exploring Big Data Governance Frameworks (2018) |
| Al-Ruithe, M.; Benkhelifa, E.; Hameed, K. | Data Governance Taxonomy: Cloud versus Non-Cloud. MDPI, Open Access Journal (2018) |
| Al-Ruithe, M.; Benkhelifa, E.; Hameed, K. | A systematic literature review of data governance and cloud data governance. Personal and Ubiquitous Computing (2019) |
| Benfeldt, O.; Persson, J.S.; Madsen, S; | Data Governance as a Collective Action Problem. Information Systems Frontier (2020) |
| Janssen, M.; Brous, P.; Estevez, E., Barbosa, L. S and Janowski, T. | Data governance: Organizing data for trustworthy Artificial Intelligence (2020) |
| Chakravorty, R. | Common challenges of data governance (2020) |
| Thuraisingham, B. | Cloud Governance. In IEEE 13th International Conference on Cloud Computing (CLOUD) (2020) |
| Selection Criteria: Data Privacy and User Rights | |
| Author(s) | Title (Year of Publication) |
| Mattoo A.; Meltzer, J. P. | International data flows and privacy: the conflict and its resolution. Journal of International Economic Law (2018) |
| Chatzimichali, A.; Chrysostomou, D. | Human-data interaction and user rights at the personal robot era. In 4th International Conference on Robot Ethics and Standards: ICRES 2019, (2019) |
| Selection Criteria: Personal and Non-Personal Data | |
| Author(s) | Title (Year of Publication) |
| Finck, M.; Pallas F. | They who must not be identified-distinguishing personal from non-personal data under the GDPR (2020) |
| Somaini, L. | Regulating the Dynamic Concept of Non-Personal Data in the EU: From Ownership to Portability (2020) |
| Selection Criteria: Actor–Network Theory | |
| Author(s) | Title (Year of Publication) |
| Montenegro, L. M.; Bulgacov, S. | Reflections on actor-network theory, governance networks, and strategic outcomes (2004) |
| Latour, B. | Reassembling the Social: An Introduction to Actor-Network Theory (2005) |
| Dincer, D. | The Act-Shifts Between Humans and Nonhumans in Architecture: A Reading of Bruno Latour’s Actor-Network Theory (2020) |
| Selection Criteria: Internet of Robotic Things | |
| Author(s) | Title (Year of Publication) |
| Ray, P.P. | Internet of Robotic Things: Concept, Technologies and Challenges (2017) |
| Yousif, R. | A Practical Approach of an Internet of Robotic Things Platform, Master of Science Thesis, KTH Royal Institute of Technology (2018) |
| Selection Criteria: IACS Primary Sources | |
| The International Association of Classification Societies | UR Z17, Procedural Requirements for Service Suppliers (1997) |
| The International Association of Classification Societies | Guidelines for Surveys, Assessment and Repair of Hull Structure–Corr. 1 (Recommendation 76) (2008) |
| Selection Criteria: Class Society Primary Sources on Drones, Crawlers, and ROV | |
| Author(s) | Title (Year of Publication) |
| Lloyds Register | Guidance Notes for Inspection Using Unmanned Aircraft Systems (2016) |
| Lloyds Register | Remote Inspection Technique Systems (RITS): Assessment Standard for Use on LR Class Surveys of Steel Structure (2018) |
| American Bureau of Shipping | Guidance Notes on the Use of Remote Inspection (2019) |
| Bureau Veritas | Approval of Service Suppliers (2020) |
| China Classification Society | Guidelines for Use of Unmanned Aerial Vehicles (2018) |
| China Classification Society | Rules for Classification of Sea-going Steel Ships (2015) |
| Det Norske Veritas | Approval of Service Supplier Scheme (2016) |
| Korean Register | Rules for the Classification of Steel Ships (2017) |
| Nippon Kaiji Kyokai | Rules for Approval of Manufacturers and Service Suppliers (2020) (Part 1 Chapter 1) |
| Registro Italiano Navale | Rules for the Certification of Service Suppliers (2020) |
| Russian Maritime Register of Shipping | RIT Requirements: Annex 39 (Guidelines for the Use of Remote Inspection Techniques for a Survey of Ships and Marine Structures) |
| Russian Maritime Register of Shipping | ROV Requirements: Annex I (Procedure for In-water Survey of Ships and Offshore Installations) of Guidelines on Technical Supervision of Ships in Service, Russian Maritime Register of Shipping |
| Selection Criteria: Data Management | |
| Authors(s) | Title (Year of Publication) |
| Loshin, D. | Master data management (2008) |
| Vilminko-Heikkinen, P.; Pekkola, S. | Changes in roles, responsibilities and ownership in organizing master data management (2019) |
| Earley, S.; Henderson, D.; Data Management Association | DAMA-DMBOK: Data Management Body of Knowledge (2017) |
| Brous P.; Janssen M.; Vilminko-Heikkinen R. | Coordinating Decision-Making in Data Management Activities: A Systematic Review of Data Governance Principles (2016) |
References
- Zins, C. What Is the Meaning of “Data”, “Information”, and “Knowledge”? Available online: https://pciucr.files.wordpress.com/2011/03/what-is-the-meaning-of-data.pdf (accessed on 1 April 2021).
- Cambridge English Dictionary. Available online: https://dictionary.cambridge.org/dictionary/english/data (accessed on 1 April 2021).
- Senn, J.A. Information Systems in Management, 2nd ed.; Cengage South-Western: Boston, MA, USA, 1982. [Google Scholar]
- Clare, C.P.; Loucopoulos, P. Business Information Systems; Paradigm: London, UK, 1987. [Google Scholar]
- Avison, D.E.; Fitzgerald, G. Information Systems Development: Methodologies, Techniques and Tools, 2nd ed.; McGraw-Hill: Maidenhead, UK, 1995. [Google Scholar]
- Bughin, J.; Chui, M.; Manyika, J. Clouds, Big Data, and Smart Assets: Ten Tech-Enabled Business Trends to Watch. Mckinsey Quarterly 2010, 56, 75–86. [Google Scholar]
- Lake, P.; Crowther, P. Data an Organizational Asset. In Concise Guide to Databases; Springer: London, UK, 2013. [Google Scholar]
- Arsana, A.; Rizos, C.; Schofield, C. The Application of GIS in Maritime boundary Delimitation, Innovations in 3D Geo Information Systems. In Proceedings of the First International Workshop on 3D Geoinformation, Kuala Lumpur, Malaysia, 7–8 August 2006. [Google Scholar] [CrossRef]
- Graham, C.H.; Elith, J.; Hijmans, R.J.; Guisan, A.; Peterson, A.T.; Loiselle, B.A. Nceas Predicting Species Distributions Working Group. The influence of spatial errors in species occurrence data used in distribution models. J. Appl. Ecol. 2008, 45, 239–247. [Google Scholar] [CrossRef]
- Davenport, T. Submarine Communications Cables and Science: A New Frontier in Ocean Governance? In Science, Technology and New Challenges to Ocean Law; Scheiber, H.N., Kraska, J., Kwon, M.-S., Eds.; Brill-Nijhoff: Leiden, The Netherlands, 2015; pp. 209–252. ISBN 9789004299610. [Google Scholar]
- Martjin, N.; Hulstjin, J.; De Bruijne, M.; Yao-Hua, T. Determining the Effects of Data Governance on the Performance and Compliance of Enterprises in the Logistics and Retail Sector. In Proceedings of the 14th IFIP Conference on e-Business, e-Services, and e-Society, Delft, The Netherlands, 13–15 October 2015; Janssen, M., Mäntymäki, M., Hidders, J., Klievink, B., Lamersdorf, W., Van Loenen, B., Zuiderwijk, A., Eds.; Springer: Delft, The Netherlands, 2015; pp. 454–466. [Google Scholar] [CrossRef]
- Boyd, D.; Crawford, K. Critical Questions for Big Data: Critical Questions for Big Data. Inf. Commun. Soc. 2012, 15, 662–679. [Google Scholar] [CrossRef]
- Johansson, T.; Long, R.; Dalaklis, D. The Role of WMU-Sasakawa Global Ocean Institute in the Era of Big Data. J. Ocean Technol. 2019, 14, 22–29. [Google Scholar]
- Toyota. TMC Announces New Big Data Traffic Information Service. 2013. Available online: https://global.toyota/en/detail/70065 (accessed on 12 March 2021).
- Dalaklis, D. Unleashing the Power of Data to Optimise Vessel Performance. In Proceedings of the Vessel Optimisation Webinar Week (Virtual Event), London, UK, 8 September 2020. [Google Scholar] [CrossRef]
- Bureau Veritas-Seeing Remotely—In Safety: Bureau Veritas Performs First Survey by Drone. Available online: https://marine-offshore.bureauveritas.com/newsroom/seeing-remotely-safety-bureau-veritas-performs-first-survey-drone (accessed on 10 March 2021).
- American Bureau of Shipping. Guidance Notes on the Use of Remote Inspection Technologies. 2019. Available online: https://ww2.eagle.org/content/dam/eagle/rules-and-guides/current/other/242-gn-remote-inspection-tech/rit-gn-feb19.pdf (accessed on 1 April 2021).
- Chynoweth, P. Legal Research. In Advanced Research Methods in the Built Environment; Knight, A., Ruddock, L., Eds.; Wiley: Blackwell, UK, 2009; pp. 28–38. [Google Scholar]
- Al-Ruithe, M.; Benkhelifa, E.; Hameed, K. A systematic literature review of data governance and cloud data governance. Pers. Ubiquitous Comput. 2019, 23, 839–859. [Google Scholar] [CrossRef]
- Benfeldt, O.; Persson, J.S.; Madsen, S. Data Governance as a Collective Action Problem. Inf. Syst. Front. 2020, 22, 299–313. [Google Scholar] [CrossRef]
- Earley, S.; Henderson, D.; Data Management Association. DAMA-DMBOK: Data Management Body of Knowledge, 2nd ed.; Technics Publications, LLC: Bradley Beach, NJ, USA, 2017. [Google Scholar]
- Alhassan, I.; Sammon, D.; Daly, M. Data governance activities: An analysis of the literature. J. Decis. Syst. 2016, 25, 64–75. [Google Scholar] [CrossRef]
- Ransbotham, S.; Kiron, D.; Analytics as a Source of Business Innovation. MIT Sloan Management Review. 2017. Available online: https://sloanreview.mit.edu/projects/analytics-as-a-source-of-business-innovation/ (accessed on 26 March 2021).
- Al-Ruithe, M.; Benkhelifa, E.; Hameed, K. Data Governance Taxonomy: Cloud versus Non-Cloud. Sustainability 2018, 10, 95. [Google Scholar] [CrossRef]
- Abraham, R.; Schneider, J.; Vom Brocke, J. Data governance: A conceptual framework, structured review, and research agenda. Int. J. Inf. Manag. 2019, 49, 424–438. [Google Scholar] [CrossRef]
- Mattoo, A.; Meltzer, J.P. International data flows and privacy: The conflict and its resolution. J. Int. Econ. Law 2018, 21, 769–789. [Google Scholar] [CrossRef]
- Chatzimichali, A.; Chrysostomou, D. Human-data interaction and user rights at the personal robot era. In Proceedings of the 4th International Conference on Robot Ethics and Standards: ICRES 2019, London, UK, 20 October 2019. [Google Scholar] [CrossRef]
- Finck, M.; Pallas, F. They who must not be identified—Distinguishing personal from non-personal data under the GDPR. Int. Data Priv. Law 2020, 10, 11–36. [Google Scholar] [CrossRef]
- GDPR; European Union. Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the Protection of Natural Persons with Regard to the Processing of Personal Data and on the Free Movement of Such Data, and Repealing Directive 95/46/EC (General Data Protection Regulation). Available online: https://eur-lex.europa.eu/eli/reg/2016/679/oj (accessed on 1 April 2021).
- Somaini, L. Regulating the Dynamic Concept of Non-Personal Data in the EU: From Ownership to Portability. Eur. Data Prot. Law Rev. 2020, 6, 84–93. [Google Scholar] [CrossRef]
- European Union. Regulation (EU) 2018/1807 of the European Parliament and of the Council of 14 November 2018 on a Framework for the Free Flow of Non-Personal Data in the European Union European Union’s (EU) Regulation 2018/1807 on a Framework for the Free Flow of Non-Personal Data in the European Union. Available online: https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A32018R1807 (accessed on 1 April 2021).
- Khatri, V.; Brown, C.V. Designing data governance. Commun. ACM 2010, 53, 148–152. [Google Scholar] [CrossRef]
- Janssen, M.; Brous, P.; Estevez, E.; Barbosa, L.S.; Janowski, T. Data governance: Organizing data for trustworthy Artificial Intelligence. Gov. Inf. Q. 2020, 37, 1–8. [Google Scholar] [CrossRef]
- McGilvray, D. Data Governance: The Missing Link for Data Quality Success; Data Management Association Presentation for DAMA Day; Granite Falls Consulting Inc.: San Francisco, CA, USA, 2006. [Google Scholar]
- Brous, P.; Janssen, M.; Vilminko-Heikkinen, R. Coordinating Decision-Making in Data Management Activities: A Systematic Review of Data Governance Principles. Lect. Notes Comput. Sci. 2016, 115–125. [Google Scholar] [CrossRef]
- Lucas, A. Towards Corporate Data Quality Management. Port. J. Manag. Stud. 2010, 15, 173–196. [Google Scholar]
- Al-Badi, A.; Tarhini, A.; Khan, A.I. Exploring Big Data Governance Frameworks. Procedia Comput. Sci. 2018, 141, 271–277. [Google Scholar] [CrossRef]
- Chakravorty, R. Common challenges of data governance. J. Secur. Oper. Custody 2020, 13, 23–43. [Google Scholar]
- Morabito, V. Big Data and Analytics Strategic and Organizational Impacts, 1st ed.; Springer: Switzerland, Zurich, 2005. [Google Scholar] [CrossRef]
- Dell Technologies. 2020. Available online: https://www.delltechnologies.com/sv-se/storage/data-storage.htm (accessed on 12 March 2021).
- Zhang, S.; Gao, H.; Yang, L.; Song, J. Research on big data governance based on actor-network theory and Petri nets. In Proceedings of the IEEE 21st International Conference on Computer Supported Cooperative Work in Design (CSCWD), Wellington, New Zealand, 26–28 April 2017. [Google Scholar] [CrossRef]
- Latour, B. Science in Action: How to Follow Scientists and Engineers through Society; Harvard University Press: Cambridge, MA, USA, 1988. [Google Scholar]
- Latour, B. Reassembling the Social: An Introduction to Actor-Network Theory; Oxford University Press: Oxford, UK, 2005. [Google Scholar]
- Montenegro, L.M.; Bulgacov, S. Reflections on actor-network theory, governance networks, and strategic outcomes. Braz. Adm. Rev. 2014, 11, 107–124. [Google Scholar] [CrossRef]
- Dincer, D. The Act-Shifts between Humans and Nonhumans in Architecture: A Reading of Bruno Latour’s Actor-Network Theory. In Contemporary Applications of Actor Network Theory; Williams, I., Ed.; Palgrave Macmillan: Singapore, 2020; pp. 33–50. [Google Scholar] [CrossRef]
- Thuraisingham, B. Cloud Governance. In Proceedings of the IEEE 13th International Conference on Cloud Computing (CLOUD), Beijing, China, 18–24 October 2020; pp. 86–90. [Google Scholar] [CrossRef]
- Loshin, D. Master Data Management, 1st ed.; Kaufmann: Burlington, MA, USA, 2008. [Google Scholar]
- International Telecommunication Union. Series Y: Global Information Infrastructure, Internet Protocol Aspects and Next-Generation Networks. 2012. Available online: https://www.itu.int/rec/T-REC-Y.2060-201206-I (accessed on 20 April 2021).
- Yousif, R. A Practical Approach of an Internet of Robotic Things Platform. Master’s Thesis, KTH Royal Institute of Technology, Stockholm, Sweeden, 2018. Available online: https://www.diva-portal.org/smash/get/diva2:1290401/FULLTEXT01.pdf (accessed on 20 April 2020).
- Ray, P.P. Internet of Robotic Things: Concept, Technologies and Challenges. IEEE Access 2017, 4, 9489–9500. [Google Scholar] [CrossRef]
- Dalaklis, D. Exploring the issue of technology trends in the “era of digitalisation”. In Proceedings of the World Maritime Day Parallel Event (IMO 70: Our Heritage—Better Shipping for a Better Future), Szczecin, Poland, 13 June 2018. [Google Scholar] [CrossRef]
- Tsaganos, G.; Nikitakos, N.; Dalaklis, D.; Ölcer, A.I.; Papachristos, D. Machine Learning Algorithms in Shipping: Improving Engine Fault Detection and Diagnosis via Ensemble Methods. WMU J. Marit. Aff. 2020, 19, 51–72. [Google Scholar] [CrossRef]
- Open Category—Civil Drone. Official Homepage of European Union Aviation Safety Agency. Available online: https://www.google.com/search?q=EASA&oq=EASA+&aqs=chrome..69i57j0l4j69i60j69i65j69i60.1240j0j4&sourceid=chrome&ie=UTF-8 (accessed on 18 April 2020).
- Fernandez, R.A.S.; Sanchez-Lopez, J.L.; Sampedro, C.; Bavle, H.; Molina, M.; Campoy, P. Natural User Interfaces for Human-drone Multi-modal Interaction. In Proceedings of the 2016 International Conference on Unmanned Aircraft Systems (ICUAS), Arlington, VA, USA, 7–10 June 2016. [Google Scholar] [CrossRef]
- Sattar, T.P. Chapter 3.4: Wall Climbing Crawlers for Nondestructive Testing. In Topics on Nondestructive Evaluation (TONE): Volume 4: Automation, Miniature Robotics and Sensors for Nondestructive Evaluation and Testing; Bar-Cohen, Y., Ed.; ASNT Publications: Columbus, OH, USA, 2000; Volume 4, pp. 77–100. [Google Scholar]
- Fondahl, K.; Eich, M.; Wollenberg, J.; Kirchner, F. A Magnetic Climbing Robot for Marine Inspection Services. In Proceedings of the 11th International Conference on Computer and IT Applications in the Maritime Industries (COMPIT ’12), Liege, Belgium, 16–18 April 2012. [Google Scholar]
- Remouit, F. Underwater Electrical Connections and Remotely Operated Vehicles. Licensiate Thesis, Uppsala Universitet, Uppsala, Sweden, 2016. [Google Scholar]
- Garcia-Valdovinos, L.G.; Salgado-Jimenez, T.; Bandala-Sanchez, M.; Nava-Balanzar, L.; Hernandez-Alvarado, R.; Cruz-Ledesma, J.A. Modelling, Design and Robust Control of a Remotely Operated Underwater Vehicle. Int. J. Adv. Robot. Syst. 2014, 11, 1. [Google Scholar] [CrossRef]
- International Association of Classification Societies. Classification Societies. What, Why and How? Available online: http://www.iacs.org.uk/media/3785/iacs-class-what-why-how.pdf (accessed on 1 April 2021).
- Johansson, T. International Standards for Hull Inspection and Maintenance of Robotics and Autonomous. In Emerging Technology and the Law of the Sea; Kraska, J., Part, Y.-K., Eds.; Cambridge University Press: Cambridge, UK, 2021; in press. [Google Scholar]
- Lindøe, P.H.; Michael, S.; Baram, M.S. The Role of Standards in Hard and Soft Approaches. In Standardization and Risk Governance; Odd Einar Olsen, O.E., Juhl, K., Lindøe, P.H., Engen, O.A., Eds.; Routledge: London, UK, 2020; pp. 235–254. [Google Scholar]
- The International Association of Classification Societies (IACS). UR Z17, Procedural Requirements for Service Suppliers. 1997. Available online: http://www.iacs.org.uk/publications/unified-requirements/ur-z/?page=2 (accessed on 10 March 2021).
- International Association of Classification Societies. Classification Societies (IACS). Guidelines for Surveys, Assessment and Repair of Hull Structure (1994)—Corr. 1 (Recommendation 76). September 2008. Available online: http://www.iacs.org.uk/publications/recommendations/61-80/rec-76-rev2-corr1-cln/ (accessed on 10 March 2021).
- DNV, Det Norske Veritas-Germanischer Lloyd. Approval of Service Supplier Scheme. 2019. Available online: http://rules.dnvgl.com/docs/pdf/DNVGL/CP/2019-02/DNVGL-CP-0484.pdf (accessed on 31 March 2021).
- Lloyds Register. Procedures for Approval of Service Suppliers. 2020. Available online: https://www.lr.org/en/approval-of-service-suppliers/ (accessed on 10 March 2021).
- Lloyds Register. Remote Inspection Technique Systems (RITS) Assessment Standard for Use on LR Class Surveys of Steel Structure. 2018. Available online: https://www.cdinfo.lr.org/information/Documents/Approvals/Remote%20Inspection%20Techniques/Remote_Inspection_Technique_Systems_RITS_Assessment_Standard_for_use_on_LR_Class_Surveys_of_Steel_Structure.pdf (accessed on 20 March 2021).
- Lloyds Register. Guidance Notes for Inspection Using Unmanned Aircraft Systems. 2016. Available online: https://www.lr.org/en/latest-news/lloyds-register-releases-guidance-notes-for-inspection-with-uas/ (accessed on 10 March 2021).
- China Classification Society. Guidelines for Use of Unmanned Aerial Vehicles for Surveys. 2018. Available online: https://www.ccs.org.cn/ccswzen/articleDetail?id=201910000000003817 (accessed on 2 April 2021).
- China Classification Society Guidelines for Ship Remote Surveys. 2019. Available online: https://www.ccs.org.cn/ccswzen/articleDetail?id=201910000000003625 (accessed on 2 April 2021).
- Nippon Kaiji Kyokai. Rules for Approval of Manufacturers and Service Suppliers. 2020. Available online: https://www.classnk.or.jp/hp/pdf/Rules_Guidance/publish/371_servicesuppliers_e_2020.pdf (accessed on 10 March 2021).
- Korean Register. Guidance Relating to the Rules for the Classification of Steel Ships. 2017. Available online: https://eclass.krs.co.kr/KRRules/KRRules2017/KRRulesE.html#%EC%84%A0%EA%B8%89%20%EB%B0%8F%20%EA%B0%95%EC%84%A0%EA%B7%9C%EC%B9%99/%EC%A0%81%EC%9A%A9%EC%A7%80%EC%B9%A8 (accessed on 10 March 2021).
- Russian Maritime Register of Shipping, Guidelines on Technical Supervision of Ships in Service. 2019. Available online: https://rs-class.org/upload/iblock/1ed/1ed89e7715ca8ae9d2d65f5a990177f3.pdf (accessed on 20 March 2021).
- UNCTAD. Data Protection and Privacy Legislation Worldwide. Available online: Unctad.org/page/data-protection-and-privacy-legislation-worldwide (accessed on 26 March 2021).
- de Búrca, G. Introduction to the Symposium on the GDPR and International Law. AJIL Unbound 2020, 114, 1–4. [Google Scholar] [CrossRef]
- Tikk, E. International Law in Cyberspace: Mind the Gap; Cyber Policy Institute: Jyväskylä, Finland, 2020; Available online: https://eucyberdirect.eu/wp-content/uploads/2020/03/tikk_rif-forpublication.pdf (accessed on 3 April 2021).
- Dalaklis, D.; Schröder-Hinrichs, J.U. The Cyber-Security Element of Hybrid Warfare: Is there a Need to “Formalise” Training Requirements? In Proceedings of the 10th NMIOTC Annual Conference (Countering Hybrid Threats: An Emerging Maritime Security Challenge), Chania, Greece, 4 June 2019. [Google Scholar] [CrossRef]
- Silvola, R.; Jaaskelainen, O.; Kropsu-Vehkapera, H.; Haapasalo, H. Managing one master data—Challenges and preconditions. Ind. Manag. Data Syst. 2011, 111, 146–162. [Google Scholar] [CrossRef]
- Vilminko-Heikkinen, P.; Pekkola, S. Changes in roles, responsibilities and ownership in organizing master data management. Int. J. Inf. Manag. 2019, 47, 76–87. [Google Scholar] [CrossRef]
- UNCTAD. Review of Maritime Transport, United Nations Conference on Trade and Development; UNCTAD/RMT/2019/Corr.1, U.N. Sales No. E.19.II.D.20, U.N. Doc.; UNCTAD: Geneva, Switzerland, 2020. [Google Scholar]
- UNCLOS. United Nations Convention on the Law of the Sea pt. XIII, Dec. 10, 1982, 1833 U.N.T.S. 397.
- Christensen, G. Definition: 6G 2020. Available online: https://searchnetworking.techtarget.com/definition/6G (accessed on 1 April 2021).
- Pastra, A.; Koufopoulos, D.N.; Samac, N.; Johansson, T. Behavioral integration in the boardroom. Team Perform. Manag. 2021. [Google Scholar] [CrossRef]
- Pastra, A.; Koufopoulos, D.N.; Skintzti, V.; Johansson, T.; Samac, N. Exploring trust in the boardroom: The case of Nordic region. Team Perform. Manag. 2021. [Google Scholar] [CrossRef]
- Theodoropoulos, P.; Spandonidis, C.C.; Themelis, N.; Giordamlis, C.; Fassois, S. Evaluation of Different Deep-Learning Models for the Prediction of a Ship’s Propulsion Power. J. Mar. Sci. Eng. 2021, 9, 116. [Google Scholar] [CrossRef]
- Spandonidis, C.; Theodoropoulos, P.; Giordamlis, C. Combined Multi-layered Big Data and Responsible AI Techniques for Enhanced Decision Support in Shipping. In Proceedings of the International Conference on Decision Aid Sciences and Applications (DASA20), Sakheer, Bahrain, 8–9 November 2020; pp. 669–673. [Google Scholar]
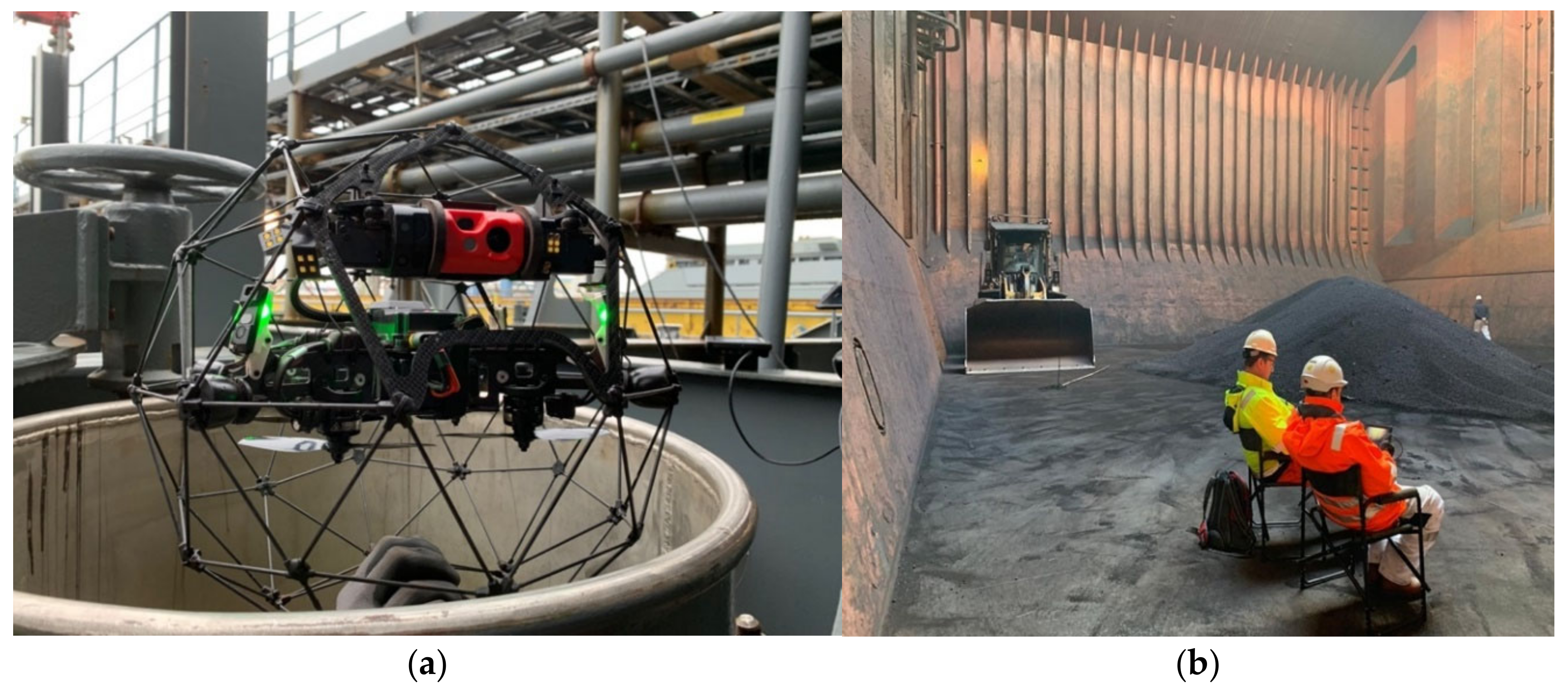
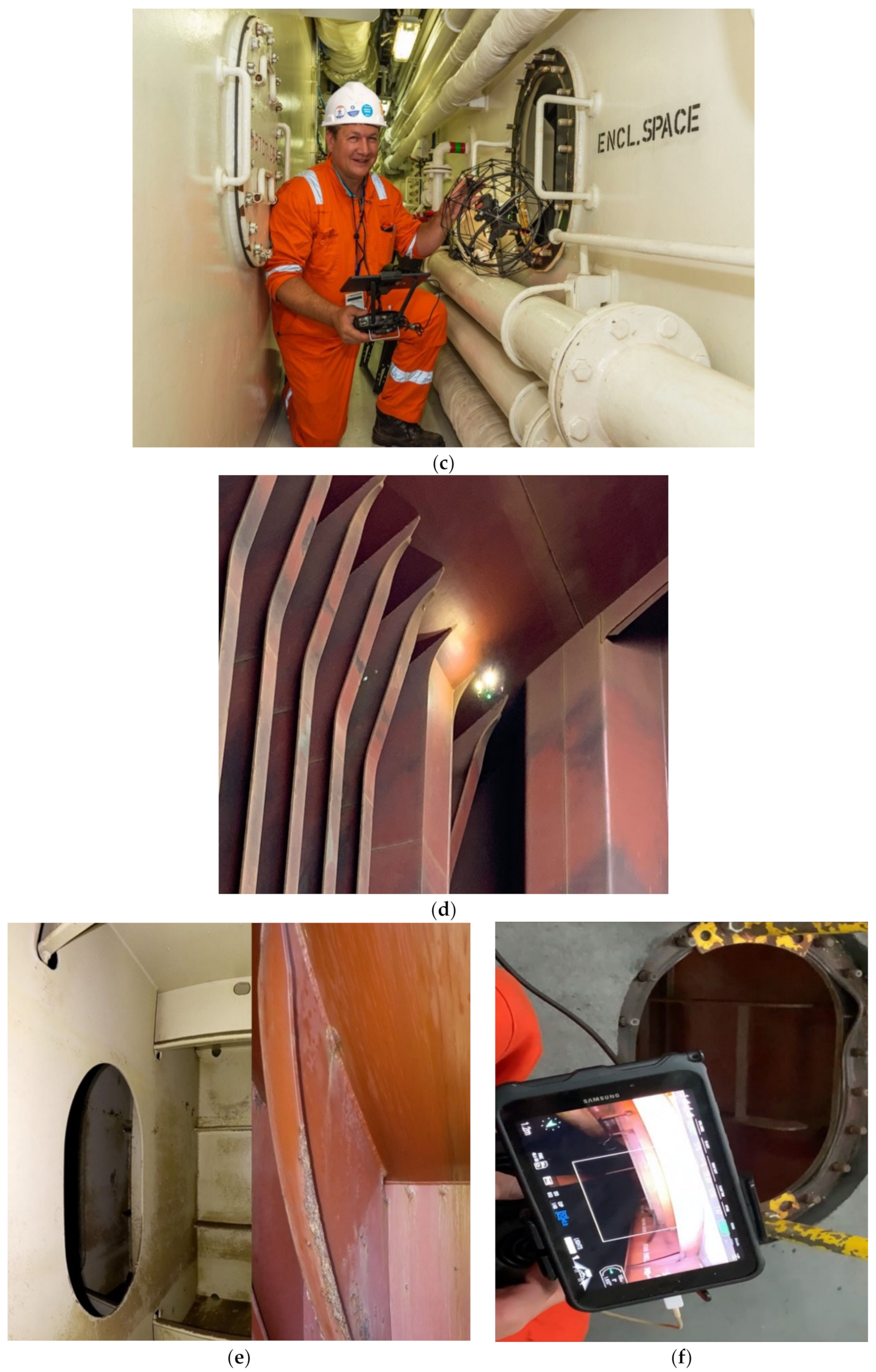
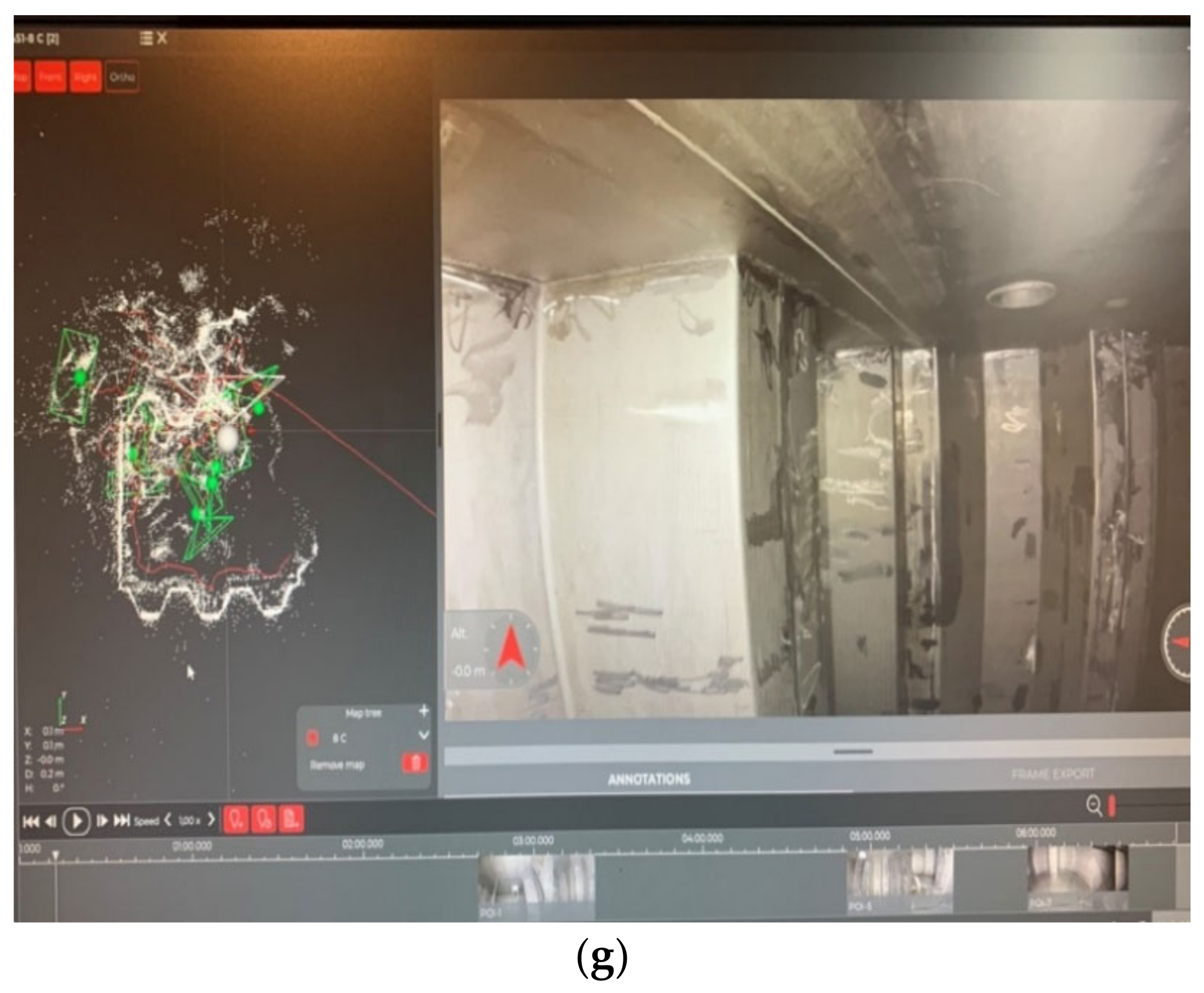
| Maritime Drones: Aviation/Air | |||
| Titles in usage | State of autonomy | Classes | User interface |
| micro aerial vehicle, unmanned aerial vehicle (UAV), uncrewed aerial vehicle, remote inspection technology, remote inspection vehicle, multidrone system, multi-UAV, drone | Supervised autonomy (machine–human); remotely controlled | A1 (<250 g to <500 g): fly over people but not assemblies; A2 (<2 kg): fly close to people; A3 (<25 kg): fly far from people; CO (<250 g): can fly in subcategory A1 and A3; C1 (<900 g): can fly in subcategory A1 and A3; C2 (<4 kg): can fly in subcategory A1 and A2; C3 and C4 (<25 kg): can fly in subcategory A3). * Note: European Union Aviation Safety requires completion of training and passing of exams defined by the national authority for operating drones under category A1, A2, A3, C1, C2, C3, and C4 [53]. | High-performance data processing task can be achieved using computer graphical user interface (GUI) or natural user interface (NUI). GUI comprises a control panel, parameter viewer, camera viewer, and requested behaviors viewer. On the other hand, NUI types include visual body interaction, visual marker interaction, hand gesture interaction, and speech command interaction [54] |
| Crawlers: Climbers on Structures (Predominantly Above Water): | |||
| Titles in usage | State of autonomy | Classes | User interface |
| Magnetic crawler, vertical surface magnetic crawler robot, remote inspection technology, remote inspection vehicle, magnetic utility crawler, magnetic crawler solutions, crawler | Supervised autonomy (machine–human); remotely controlled | Vacuum adhesion type: pneumatic climbing robot, articulated-limb crawler using rubber suction cups; magnetic adhesion type: electromagnetic wheeled crawlers; propeller type: see [55] | High-performance data processing task can be achieved using a 3D tracking concept and robot operating system. Specific location information is transmitted by tracking unit and visuals are communicated by built-in cameras [56]. |
| ROVs: Underwater (Liquid Environment): | |||
| Titles in usage | State of autonomy | Classes | User interface |
| ROV, remotely operated underwater vehicle submersible, autonomous underwater vehicle, remote inspection technology, remote inspection vehicle | Supervised autonomy, supervised autonomy (machine–human), remotely controlled using cable and tether | Observation class (up to 100 kg, 300 m typical depth rating): DC voltage, 110/220 V DC/AC voltage); mid-sized class (from 100 kg to 1000 kg, 2000 m typical depth rating): 440/480 V, AC voltage; work-class (>1000 kg, >3000 m typical depth rating): 440/480V [57]. | The electronic architecture is fitted with computers—one is located at the surface and is connected to a monitor through which the user can view images taken by the camera and other sensors, and the second is located in the ROV’s electronic contained. Both computers control the thruster and the underwater arm to read and process the sensor signal whereby all tasks are performed using data acquisition cards and National Instruments hardware. Communication is materialized via Ethernet protocol [58]. |
| Underlying Element | Action Item |
|---|---|
| Interorganizational consultation | Action Item 1 in conjunction with Action Item 2: Creation of a forum to take part in revisions and reforms undertaken by IACS in relation to Unified Requirements. |
| Categorization based on capacity | Action Item 3: Classify based on capacity and determine whether MAVs, AUVs, and crawlers fall under the scope of “mobile robots”. |
| Standalone definitions | Action Item 4: Consider standalone definitions (in the following manner) for MAVs, AUVs, and crawlers rather than referring to all technologies under the overarching term “remote inspection technologies”. |
| Classification pursuant to degree of autonomy | Action Item 5: In order for procedural rules and requirements to keep pace with technological innovation (towards full autonomy), service robots require a form of categorization along the lines of degree of autonomy. A potential way forward is to follow closely the degrees rendered to vessels and how the different stages were set by IMO’s MASS (as the first step in scoping exercise). |
| Operational limitations and conditions for service robotics | Action Item 6: Consider operational limitations for MAVs, AUVs, and crawlers that help ensure effective completion of survey process. Action Item 7: Consider pre-operation, in-operation, and post-operation conditions for service robots. |
| Expand existing provisions on “alterations” | Action Item 8: Revise provisions in relation to survey and inspection planning, and consider all potential risk assessment options. Action Item 9: Indicate in detail the procedures in cases where the service supplier alters the certified system, which in turn affects the quality system. Action Item 10: Consider revision to include provisions on certification of multisite organizations under the rules concerning certification. Action item 11: Consider revision of existing provisions related to survey procedures) to include a client service system (CSM), live-streaming during remote survey, and real-time collection of survey process information, solutions in case of problem with live-streaming, recording of process and conclusion in the ship log, and conditions for certification. Action item 12: Consider technological platforms for facilitation collection and delivery of survey-related information such as computers, intelligent remote glasses, and digital cameras for live-streaming purposes. Action Item 13: Consider using more a factual and objective post-reporting system. |
| Safety management system | Action Item 14: Consider incorporating valuable provisions related to a safety management system, with explicit reference to safety policy, safety risk management, safety assurance, and safety promotion. |
| Liability clause | Action Item 15: Consider incorporating a liability clause in UR Z17 for maintaining third-party liability insurance in case of accidents or deaths. |
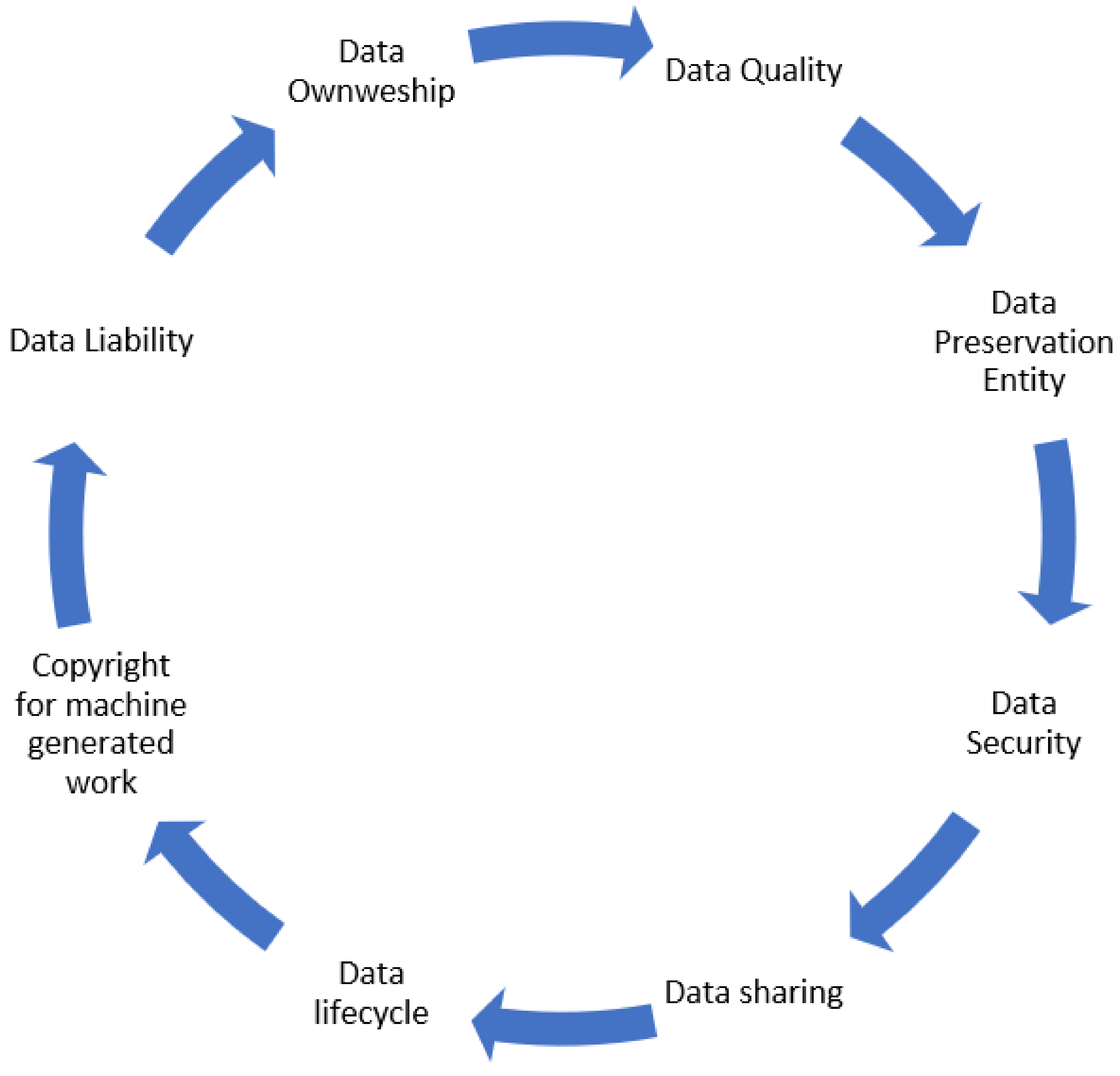
| Data governance and management | Action Item 16: Hull inspection data should be kept confidential as this may constitute a trade secret for the shipowner. Legitimate practices should be in place for the collection, storage, and use of unpublished data of economic significance. For overcoming barriers to data governance and data management, explicit provisions are needed in the form of a contract that specifies the allocation of responsibilities and roles for the ownership, storage, security, and sharing of information between service suppliers, classification societies, and shipowners. Sound data governance principles are essential to help minimize risks and keep external cyber securities threats out of their networks. The contract should be signed during the planning stage of hull inspection. Action Item 17: IACS guidelines should elaborate on their provisions about data management from the use of remote techniques. Action Item 18: Data ownership, which is one of the most critical parts of the data governance process, defines the rightful owner of the data elements, sharing policy, and access rights to third parties granted by the data owner. During the planning stage of hull inspection, a clear understanding between service suppliers, classification societies, and ship owners/managers should be maintained about data ownership. Action Item 19: Digital data preservation gives reliable protection to information and systems needed to ensure the long-term usability of data and metadata. Clear allocation of responsibility should be given to the party that is responsible for data and image preservation. Action Item 20: Distributed data between the different stakeholders intensifies data security efforts between participants in the data process. Cloud environments encounter increased security threats due to inadequate access management and system vulnerabilities. Measures should be in place for the security and confidentiality of remote inspection technology data by all the relevant stakeholders to ensure a sound data governance process. Action Item 21: During the planning stage of hull inspection, it should be specified how the data are shared between the different stakeholders to ensure secure data transfer between data owners and users. Provisions should exist about the sharing of data in the formal agreement. A secure industry platform could be utilized for secure data transfer between data owners and users, when saving and sharing the video stream from the remote survey. Action Item 22: The current copyright regime does not protect computer-generated data; thus, explicit provisions in the contract should be made to safeguard computer-generated works. Action Item 23: Potential liability issues that stem from the use of data should be underlined in the contract. Input material supplied by the asset owner to the service supplier before the hull inspection (i.e., images, drawings, and designs) should not infringe the copyright or other rights of a third party. |
| Harmonizing statutory and class rules with reference to close-up survey | Action Item 24: Consider aligning the definition of a “close-up survey” found in IMO’s Enhanced Survey Programme, given that the current definition of close-up survey is inadequate as the IACS created the possibility to use RITs for remote inspection, allowing the surveyor to conduct close-up surveys through sensors. |
| Controlling variety for optimum quality performance by regulating technical and operational standards | Action Item 25: Develop a methodology to establish standards based on product categorization with the aim of reducing variety to identify the best product from all categories of RITs. |
| Creating a remote inspection technology “trustworthy ecosystem” | Action Item 26: There should not only be efforts to market quality products so that smooth integration is possible but also efforts to create lawful, ethical, and robust service robots that can render end-users trust in the products deployed for survey and maintenance tasks. |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Johansson, T.M.; Dalaklis, D.; Pastra, A. Maritime Robotics and Autonomous Systems Operations: Exploring Pathways for Overcoming International Techno-Regulatory Data Barriers. J. Mar. Sci. Eng. 2021, 9, 594. https://doi.org/10.3390/jmse9060594
Johansson TM, Dalaklis D, Pastra A. Maritime Robotics and Autonomous Systems Operations: Exploring Pathways for Overcoming International Techno-Regulatory Data Barriers. Journal of Marine Science and Engineering. 2021; 9(6):594. https://doi.org/10.3390/jmse9060594
Chicago/Turabian StyleJohansson, Tafsir Matin, Dimitrios Dalaklis, and Aspasia Pastra. 2021. "Maritime Robotics and Autonomous Systems Operations: Exploring Pathways for Overcoming International Techno-Regulatory Data Barriers" Journal of Marine Science and Engineering 9, no. 6: 594. https://doi.org/10.3390/jmse9060594
APA StyleJohansson, T. M., Dalaklis, D., & Pastra, A. (2021). Maritime Robotics and Autonomous Systems Operations: Exploring Pathways for Overcoming International Techno-Regulatory Data Barriers. Journal of Marine Science and Engineering, 9(6), 594. https://doi.org/10.3390/jmse9060594








