Perspectives on Cyber Security for Offshore Oil and Gas Assets
Abstract
1. Introduction
- (a)
- An overview of available literature in the field of cyber security for offshore (upstream) oil and gas assets. As part of the literature review, any material exploring cyber security aspects involving the onshore assets and processes supporting the upstream sector will also be considered. The midstream and downstream sectors of the oil and gas industry are not covered in this paper as they are not part of the authors’ research scope.
- (b)
- An up-to-date view of the offshore oil and gas industry’s perception of cyber security based on a survey of personnel active in the specific sector.
2. Digitalization and Cyber Integration in the Upstream Oil and Gas Sector
3. Literature Review on the Subject of Cyber Security in the Offshore Oil and Gas Domain
- (a)
- Cyber security adversaries, threats, and vulnerabilities;
- (b)
- Cyber systems integration as well as risk analysis and management;
- (c)
- Industry and governmental initiatives.
3.1. Cyber Security Adversaries, Threats, and Vulnerabilities
- (a)
- Cyber criminals: These comprise hackers, organized criminals, etc., seeking financial benefit through use of stolen digital information or manipulation of physical assets.
- (b)
- State adversaries: They comprise hostile states seeking political advantage, espionage, destruction of digital assets, sabotage, etc.
- (c)
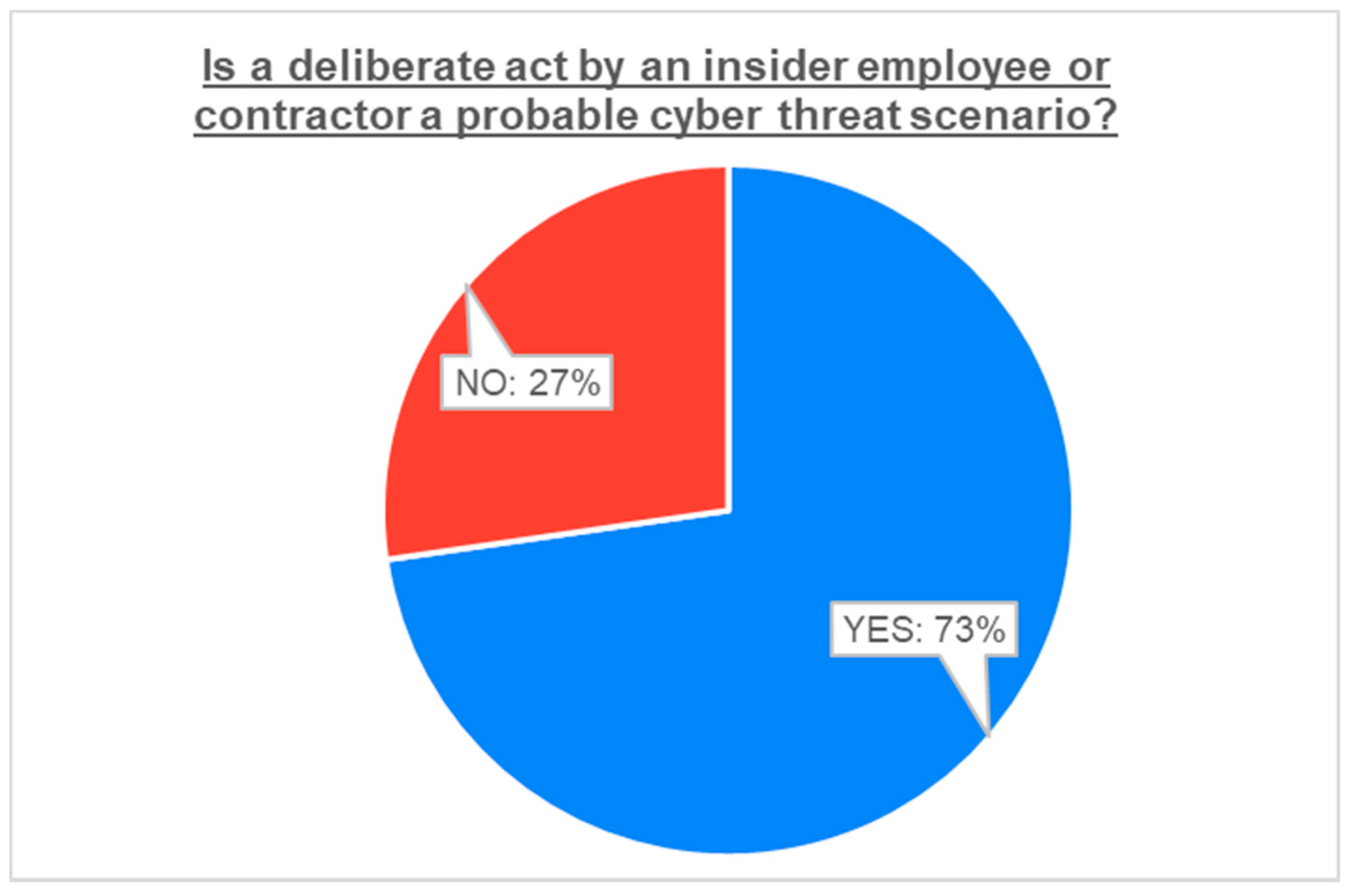
- Insiders: They comprise disgruntled employees seeking personal benefit through targeted theft of digital information, destruction of digital assets, sabotage, etc., or negligent employees causing unwanted incidents [14].
- (d)
- Cyber terrorists [15]: These are terrorist groups seeking sabotage or destruction of physical assets, and they exploit cyber and physical vulnerabilities for political or ideological reasons.
- (e)
- Cyber activists: These comprise hacktivists and activist groups causing sabotage to cyber infrastructure through targeted cyber attacks for political or ideological purposes.
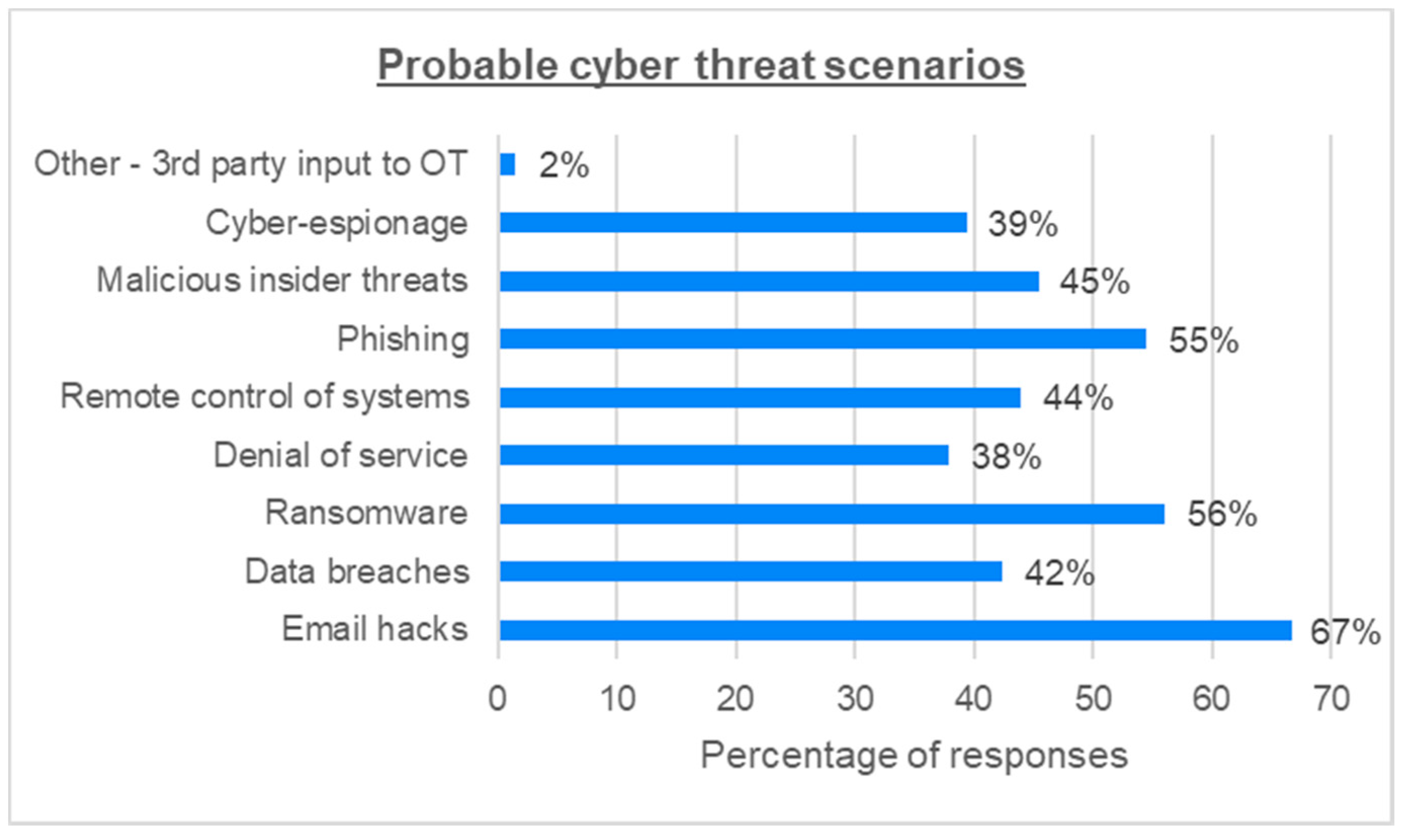
- Remote data hijacking and manipulation for targeted physical attacks to maritime and offshore oil and gas assets [16];
- Sabotage of IT and OT systems by an employee for personal benefit [15];
- A cyber attack scenario on an offshore natural gas asset by the altering of parameters in the gas hydrate system [21];
- Compromise of a third-party and original equipment manufacturer (OEM) [20], aiming at the cyber espionage and hacking of IT/OT systems, and infiltrating internal cyber security barriers of offshore oil and gas assets and organizations;
- Cyber attack against shore-based electric power generation and supply entity of shore-to-offshore power distribution, aiming at the disruption of upstream and midstream oil and gas asset operations [20].
- Infrastructure sabotage: This refers to the use of malware or malicious software for the manipulation and damage of IT/OT infrastructure, as well as the alteration of data and equipment operating parameters, all leading to the malfunction and/or damage/destruction of assets, systems, etc. One example is the Stuxnet virus used in the attacks against the Iranian uranium-enriching facilities’ OT systems, which also affect IT systems from the U.S. oil and gas company Chevron [31]. Another example is the targeted cyber espionage campaign against gas pipeline companies to gather data for sabotage operations [29].
- Data leaks: These are caused by the unsafe handling or storage of data through web or file servers as well as through targeted hacking attacks.
- Insider malicious cyber incidents: These comprise insider-led destruction or alteration of data, theft of intellectual property, and data leakage.
- Attacks on webmail and corporate VPN servers: This is achieved through DNS (Domain Name Server) hijacking or targeted phishing attacks.
- DNS (domain name server) hijacking: This involves the modification of corporate domain name servers for the theft of corporate credentials, email communication interception, access to internal and VPN networks, etc.
- Espionage and data theft: This involves intrusion into corporate IT systems for the theft of data and/or monitoring of financial transactions, corporate data processing, etc. This threat scenario was confirmed by the ENISA report ETL 2020 on the cyber espionage threat landscape [32].
- External emails: These are data leaks caused by the use of external email communication through corporate or personal computer systems, whereby the unsafe storage or transmission of data becomes a risk.
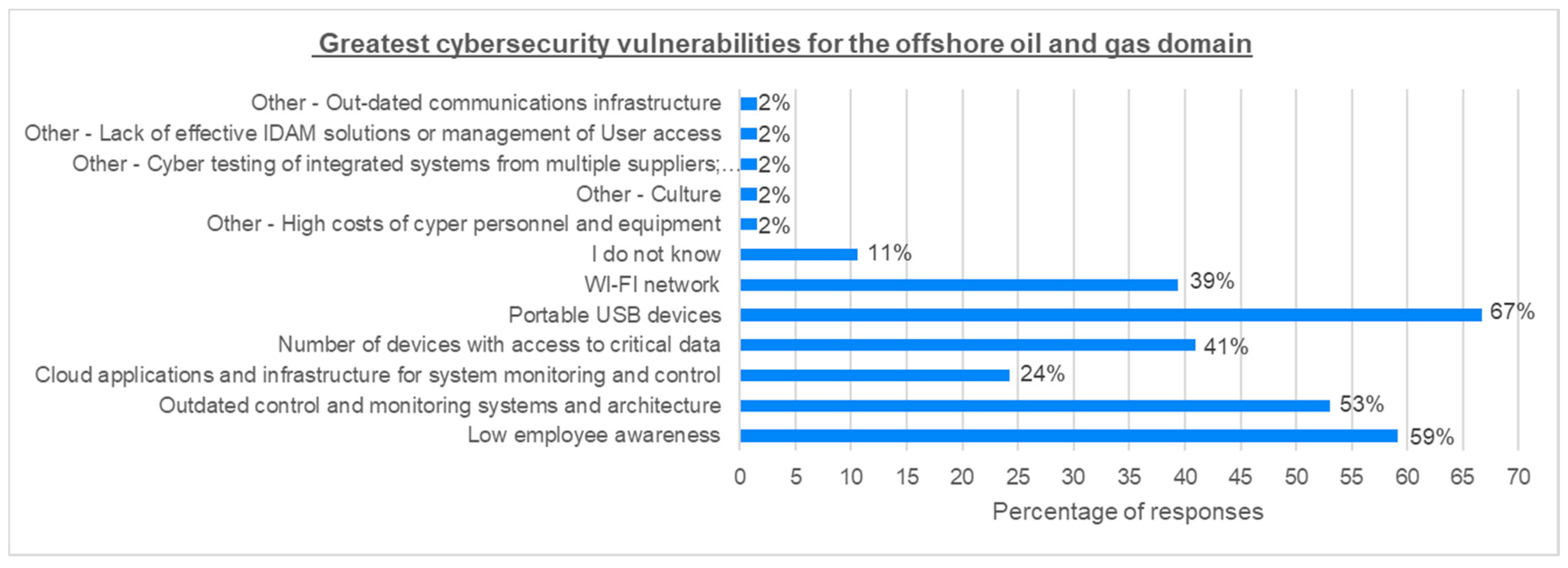
- (a)
- Lack of cyber security awareness and training of employees
- (b)
- Remote work during operations and maintenance
- (c)
- Using commercial type IT products with known vulnerabilities in the production environment
- (d)
- An inadequate cyber security culture among vendors, suppliers and contractors
- (e)
- Insufficient separation and segmentation of data networks
- (f)
- The use of mobile devices and storage units including smartphones
- (g)
- Data networks between on- and offshore facilities
- (h)
- Insufficient physical security of data rooms, cabinets, etc.
- (i)
- Vulnerable software
- (j)
- Outdated and ageing control systems in facilities
3.2. Cyber Systems Integration and Risk Analysis and Management
3.3. Industry and Governmental Initiatives
3.4. COVID-19 and Its Cyber Security Implications in the Offshore Oil and Gas Domain
4. Industry-Wide Survey on Cyber Security for Offshore Oil and Gas Assets
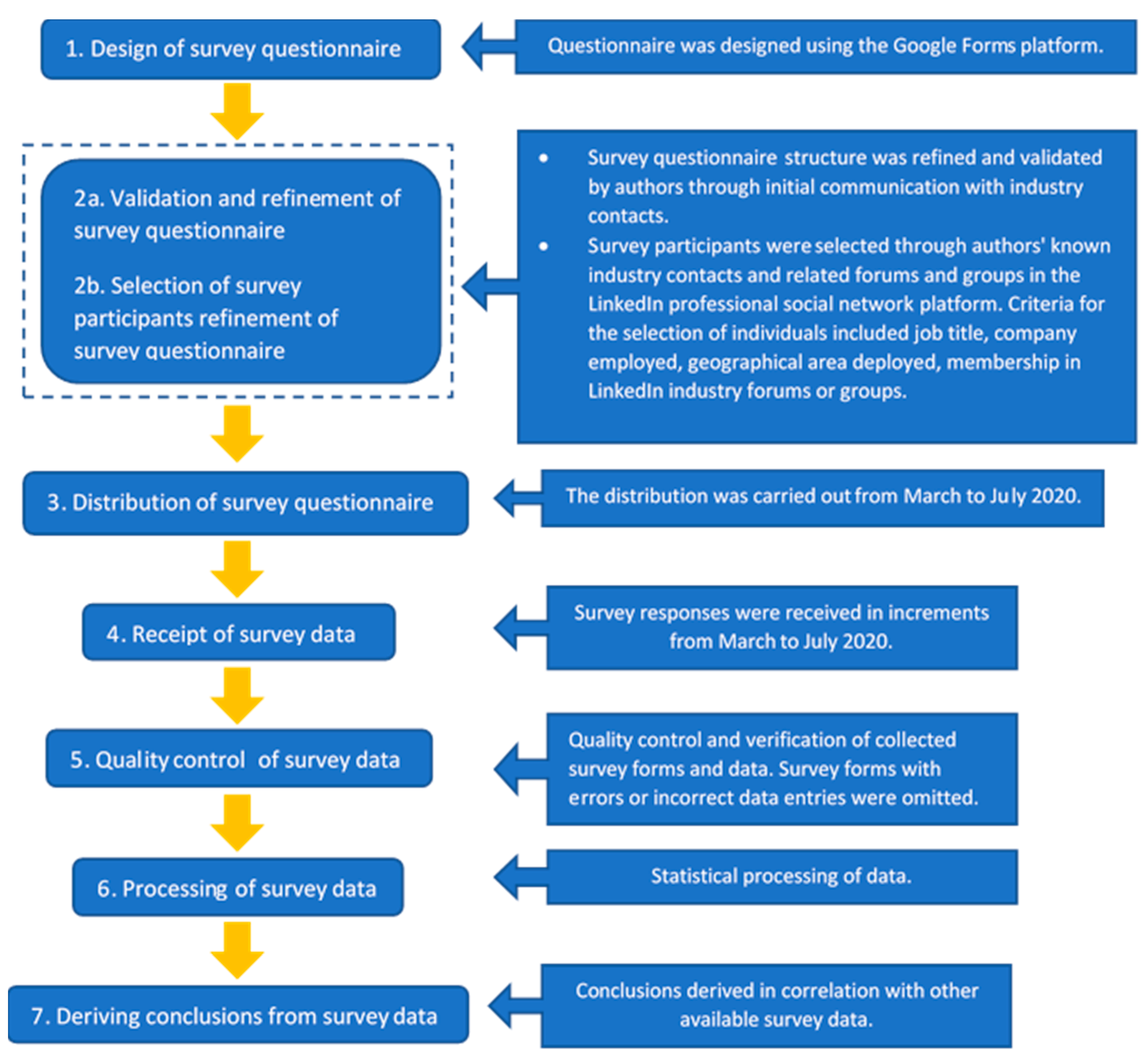
4.1. Survey Methodology and Objectives
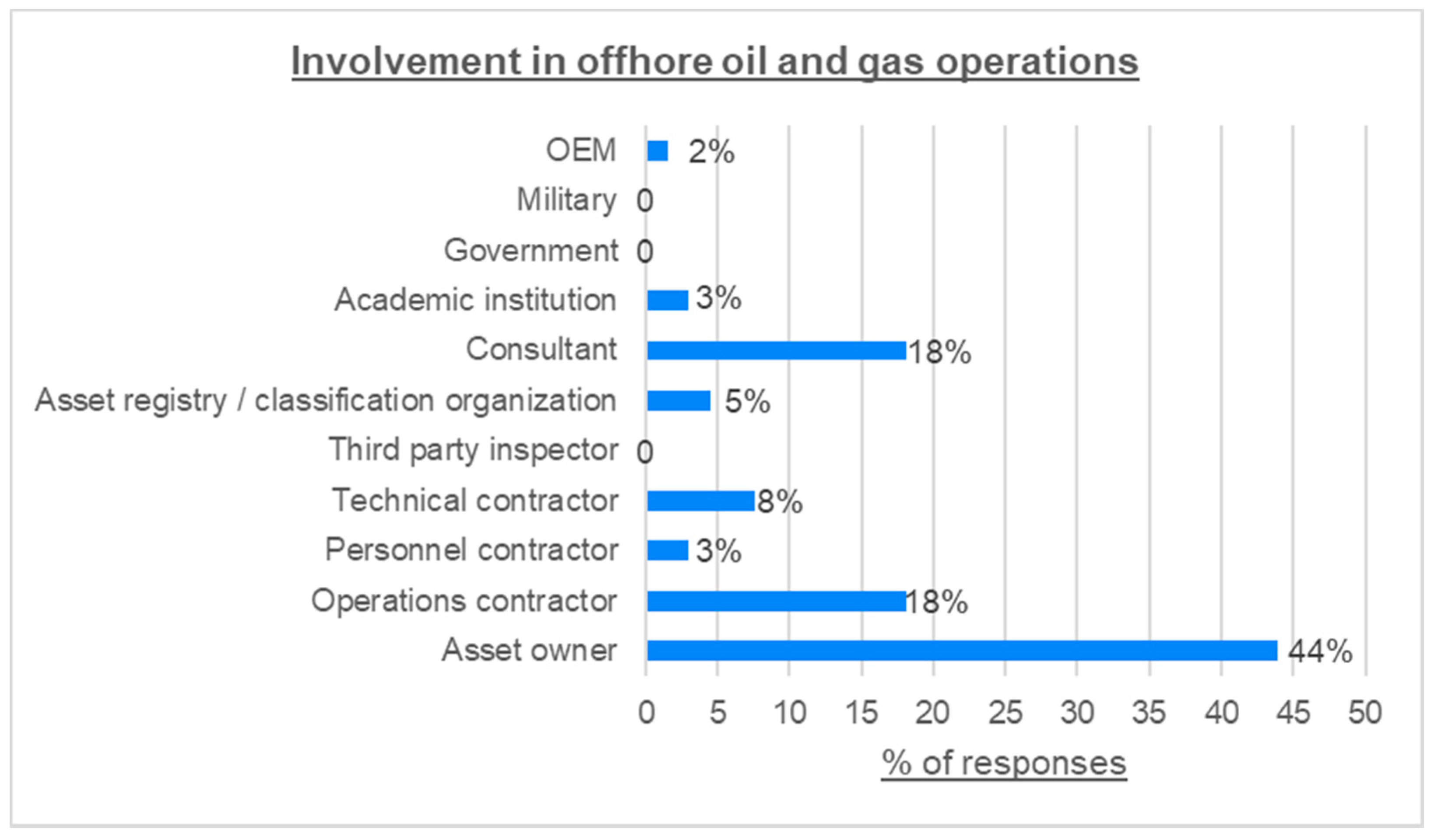
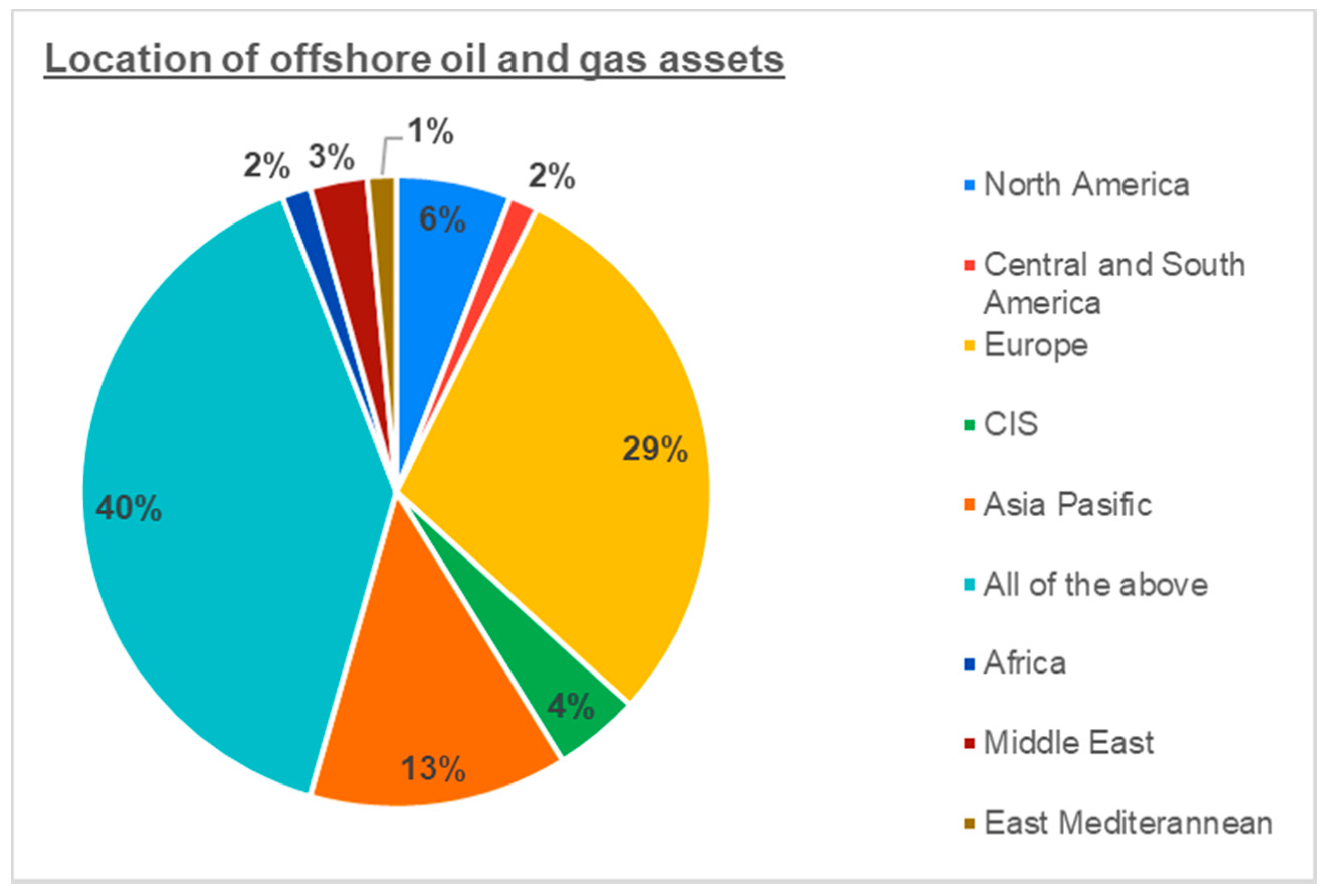
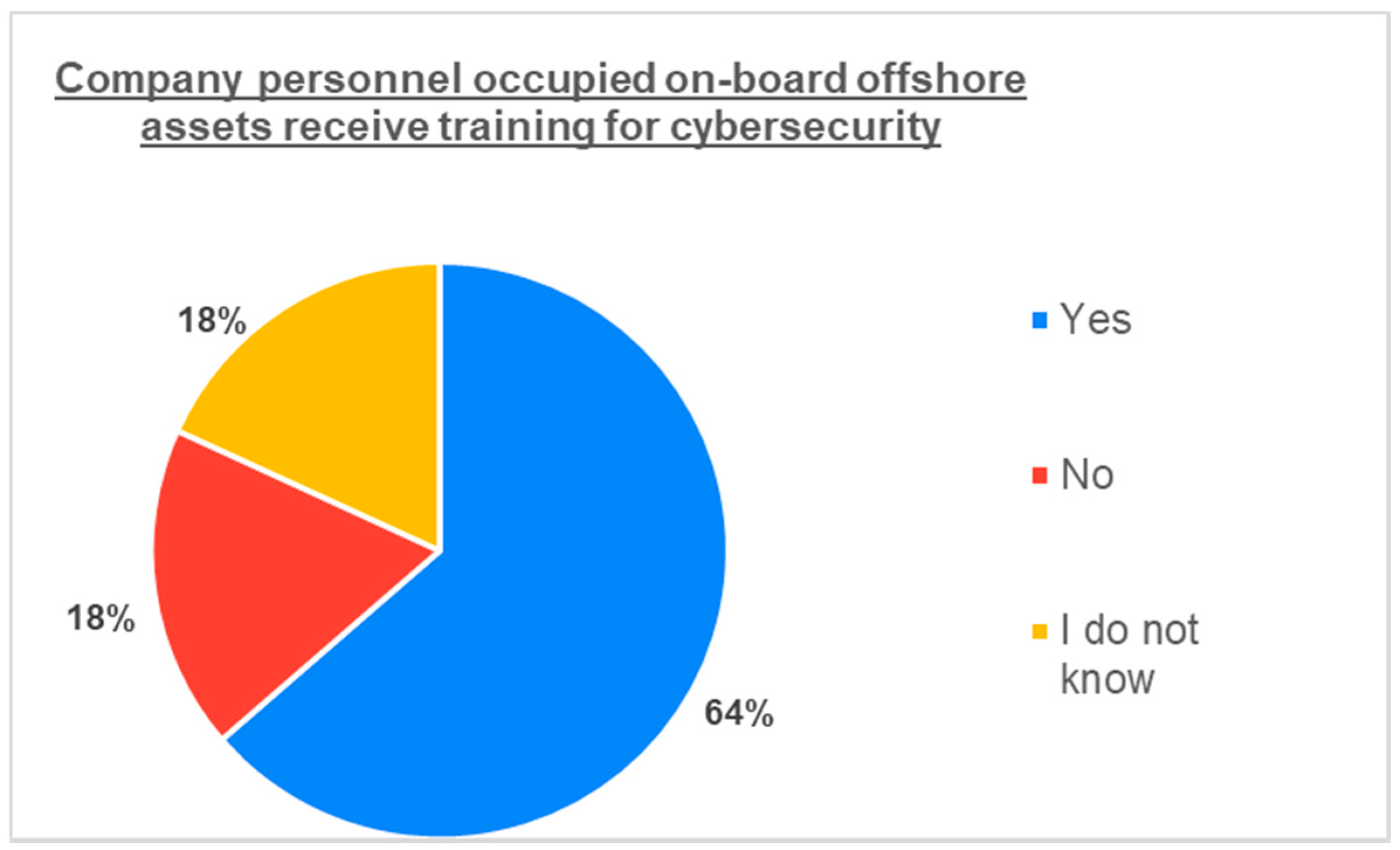
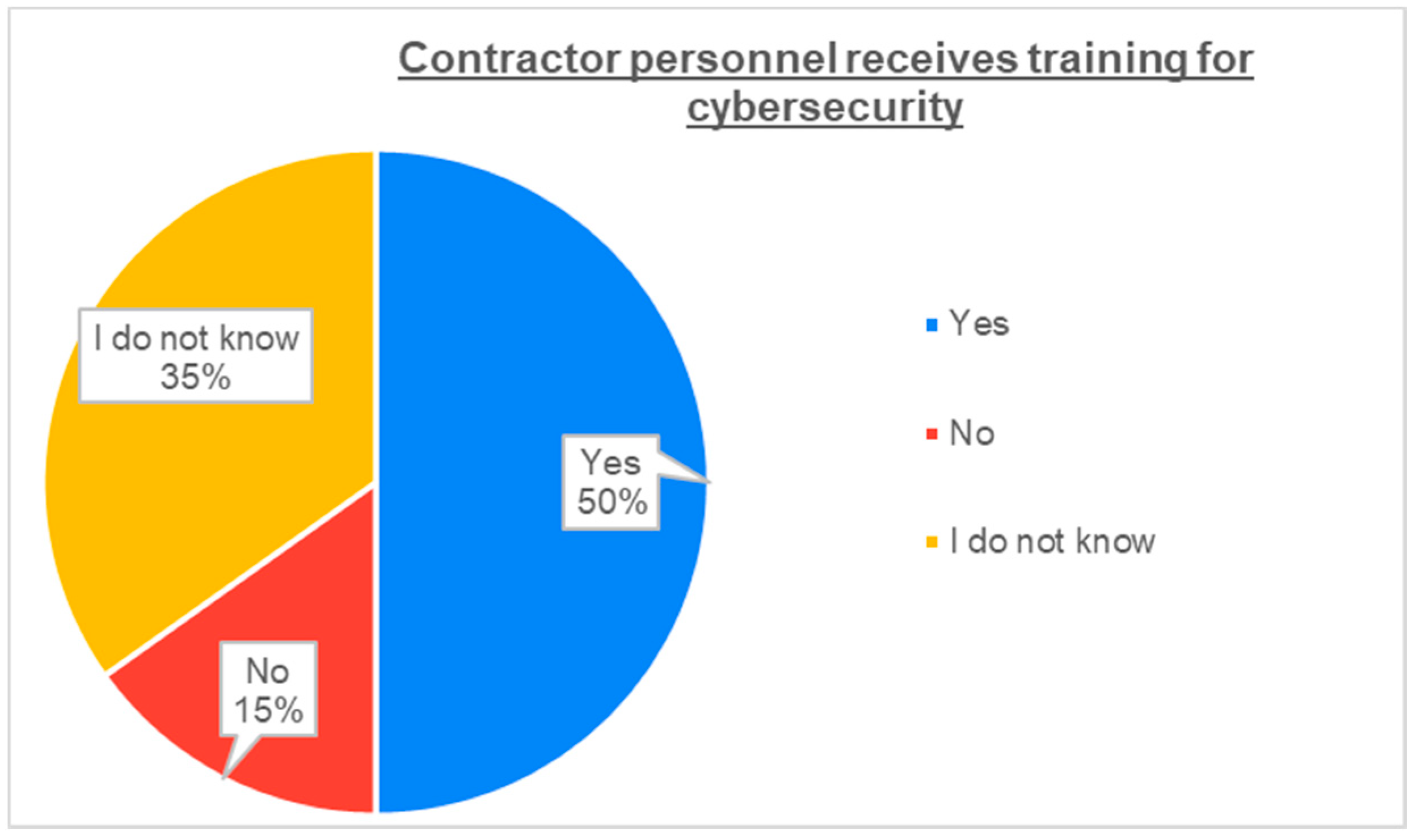
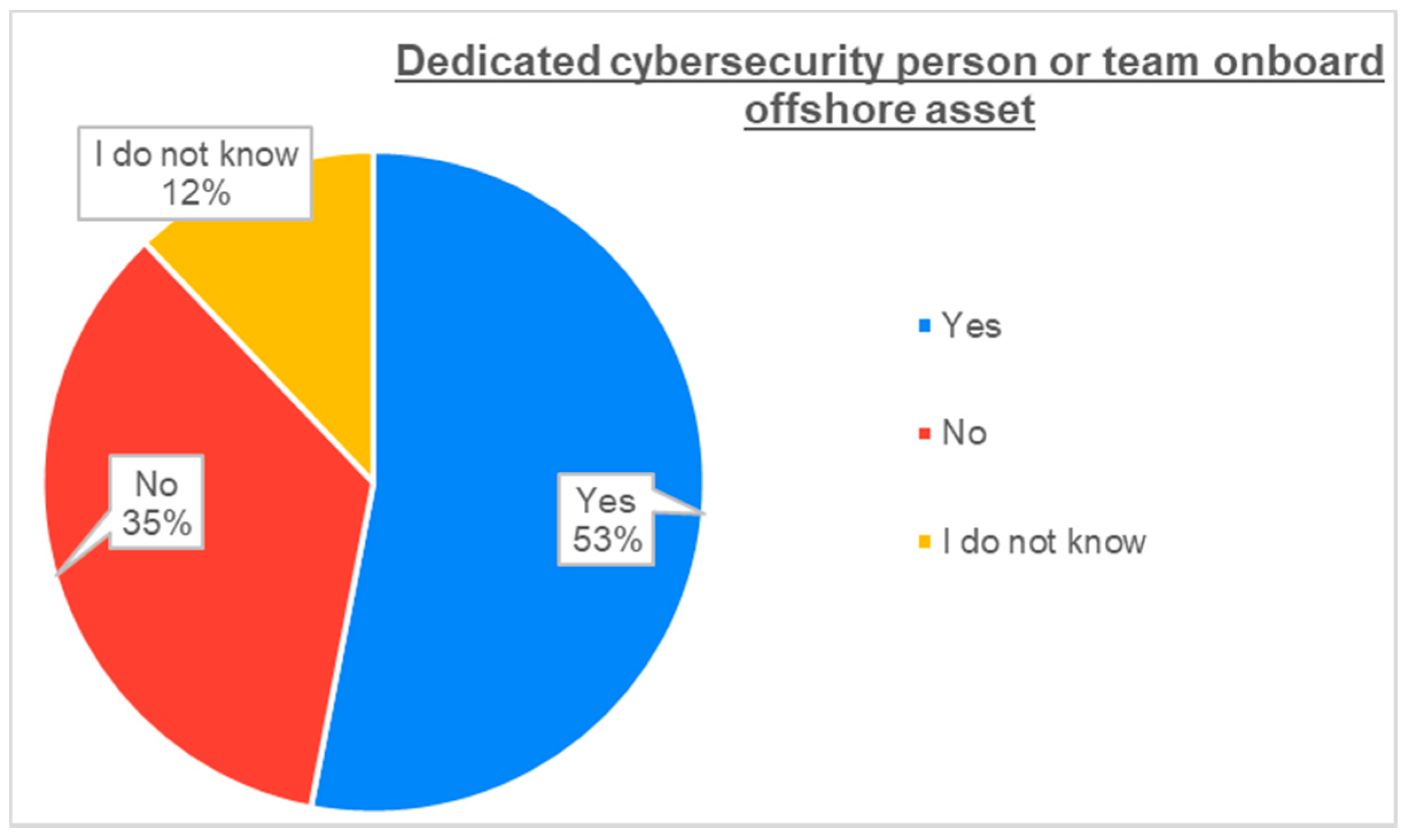
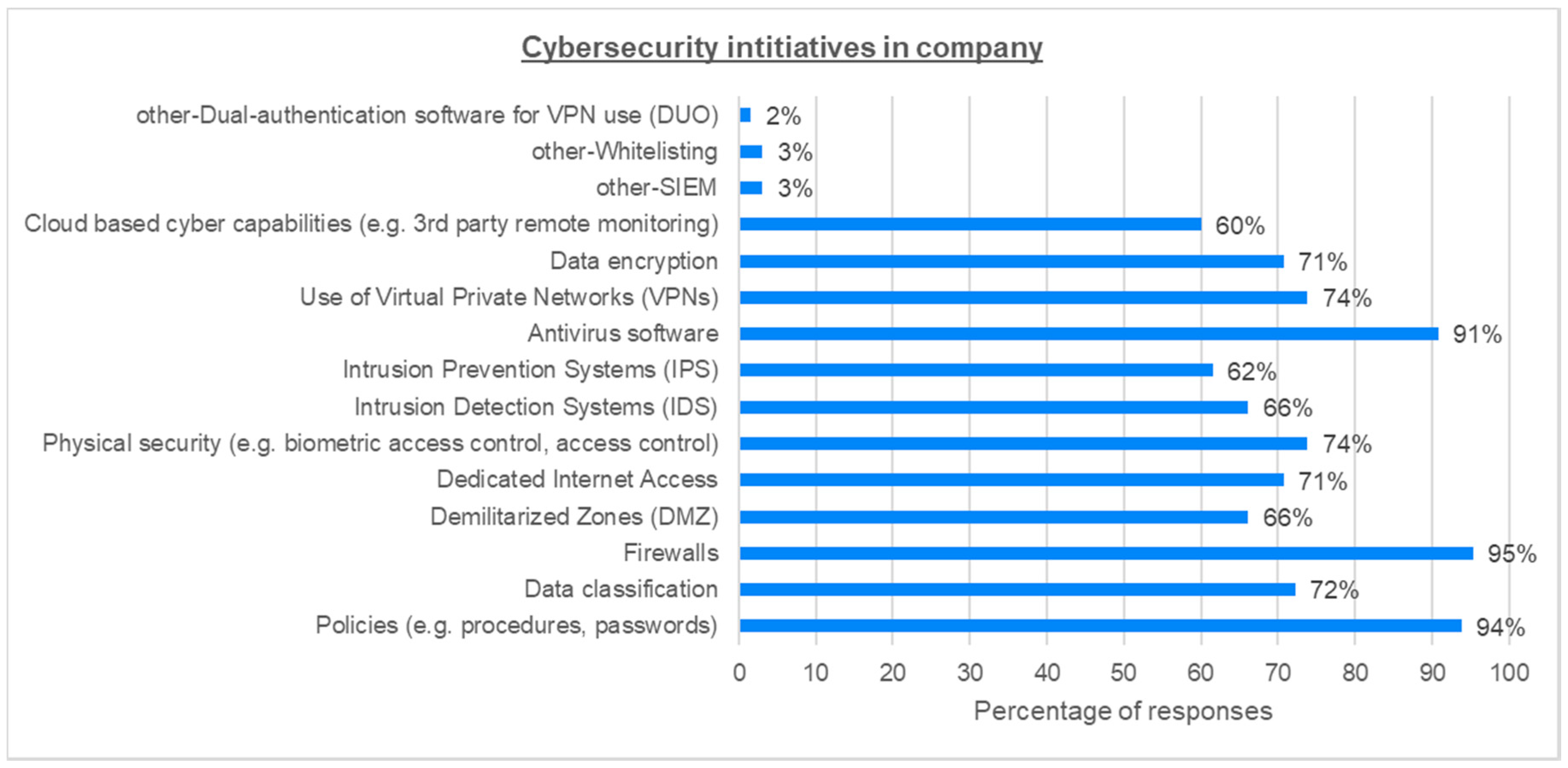
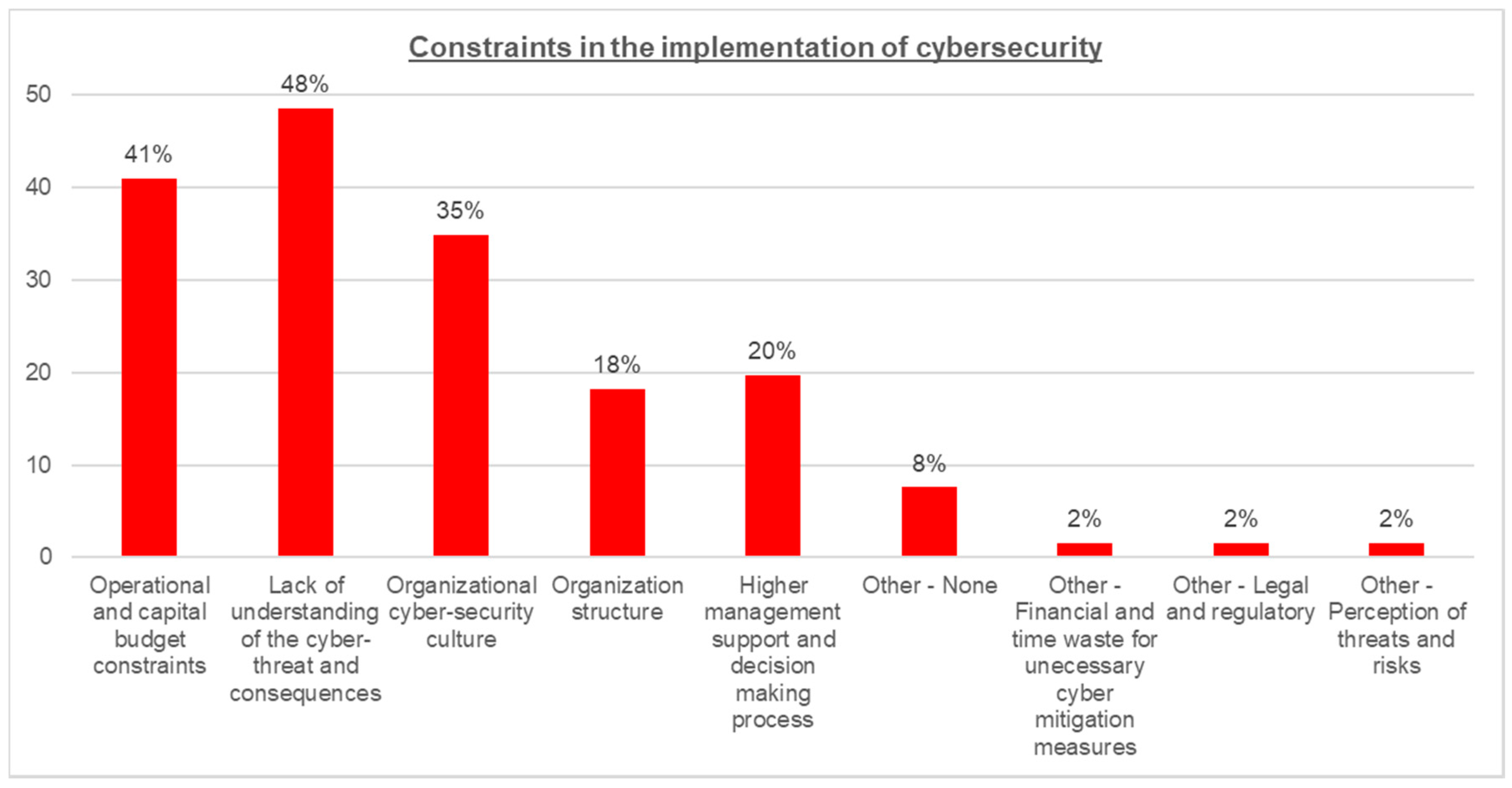
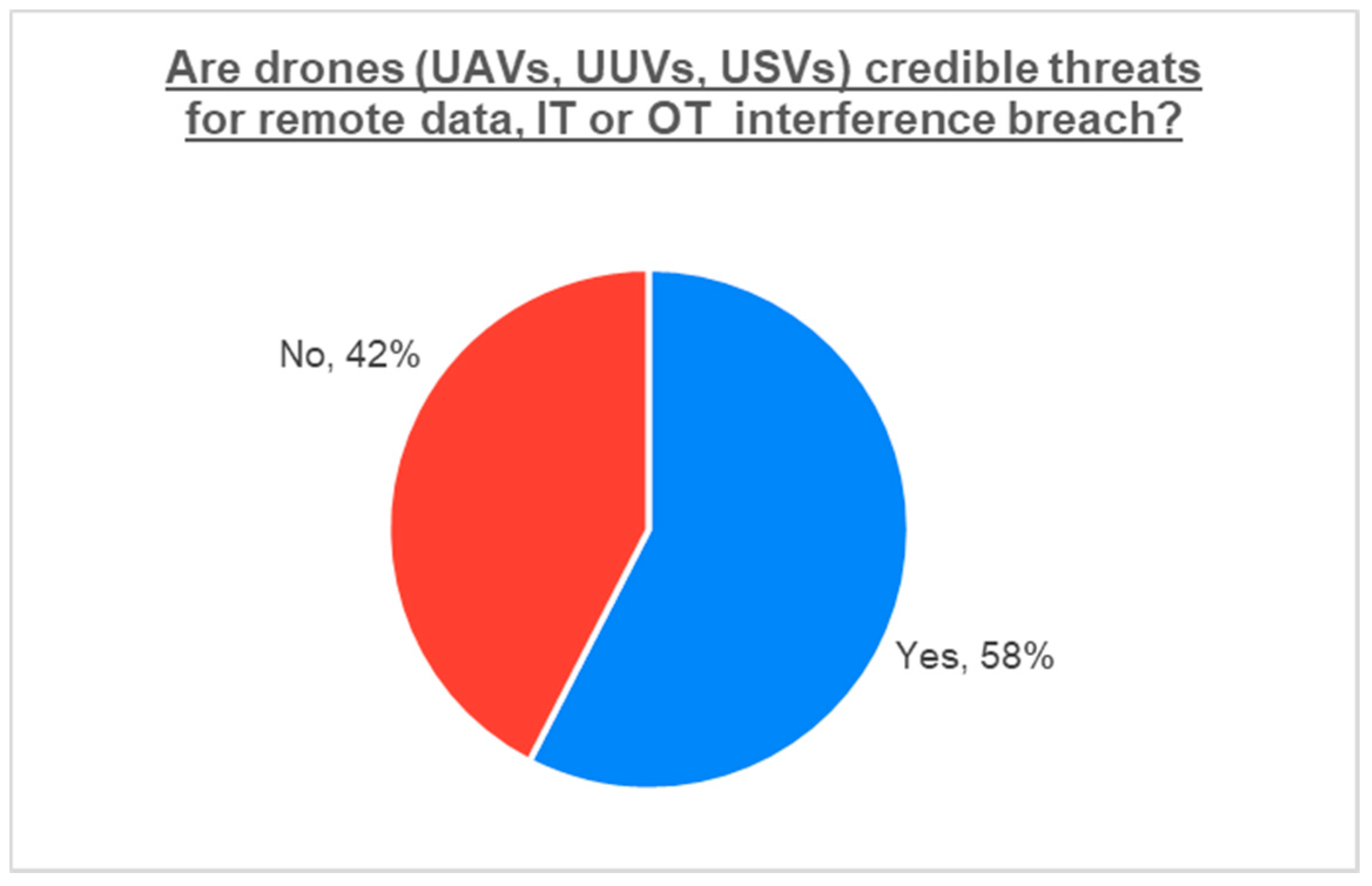
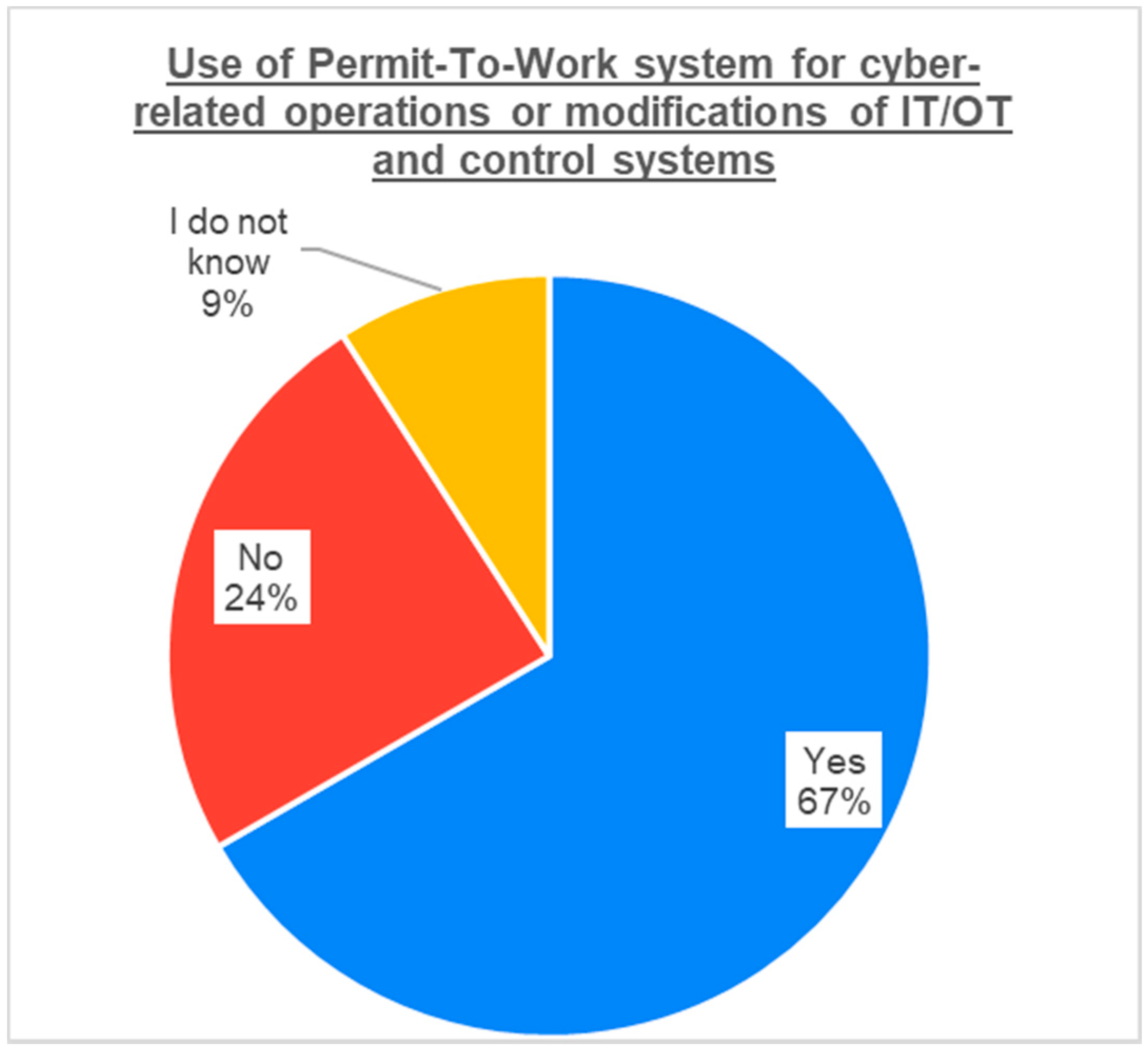
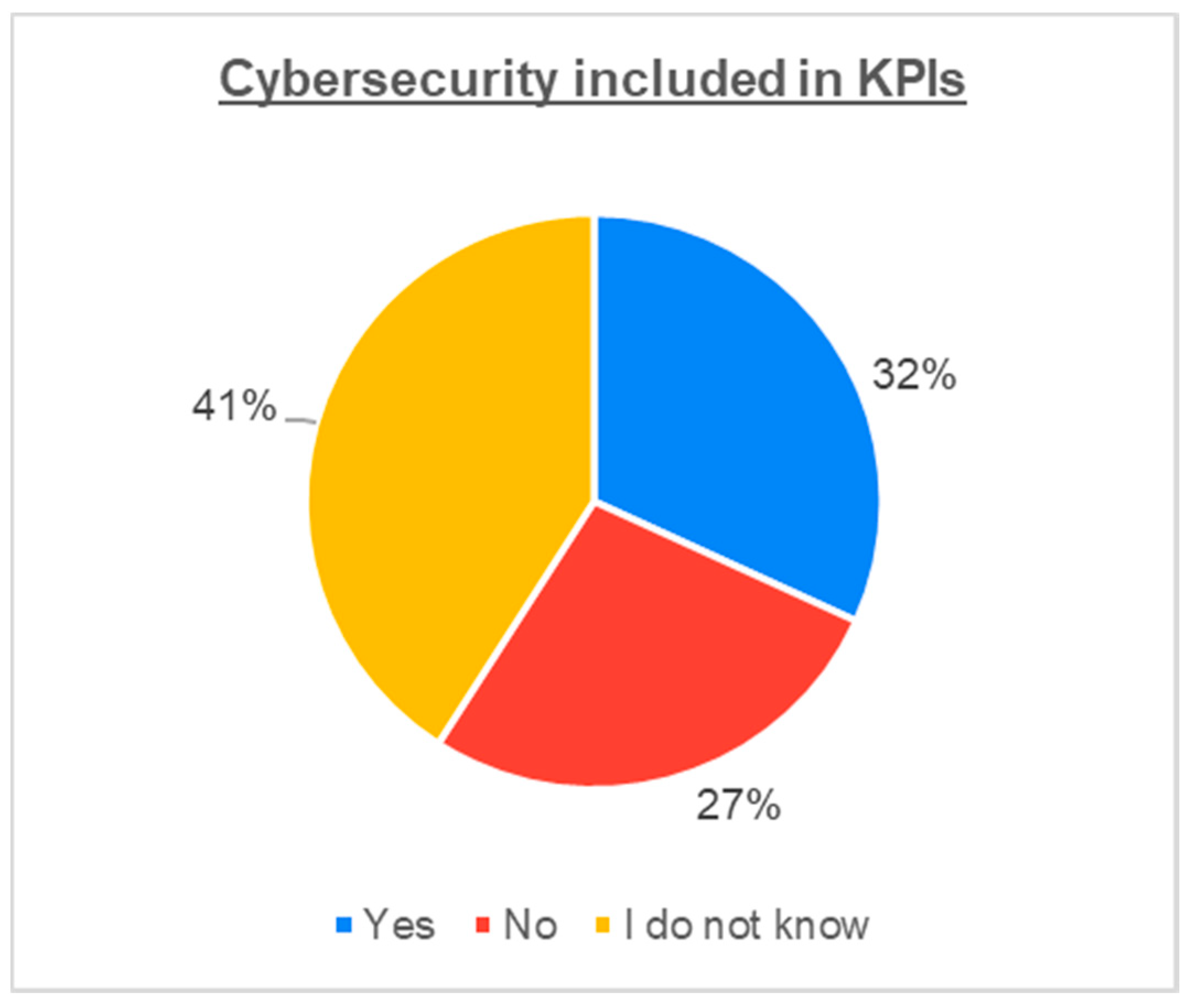
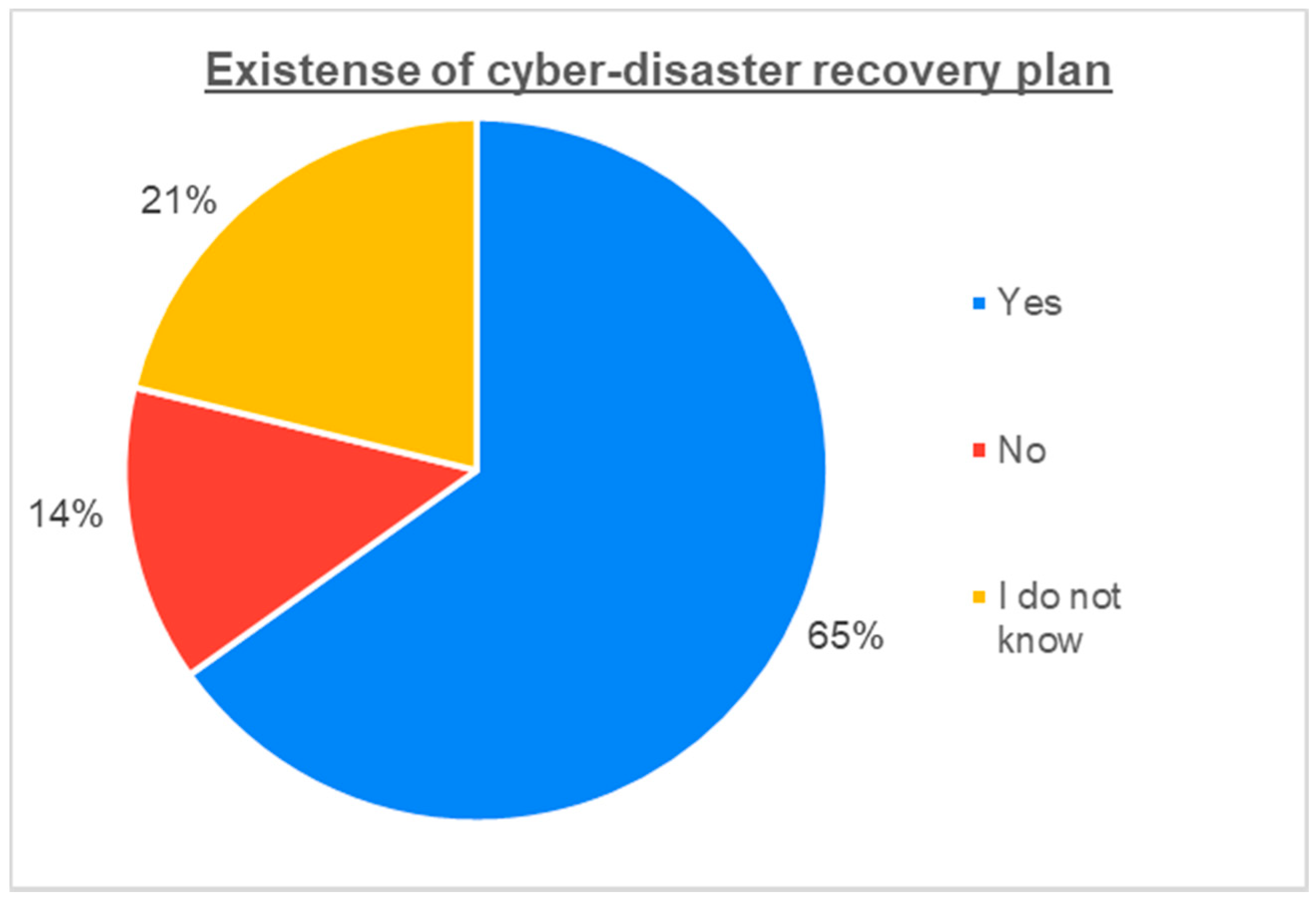
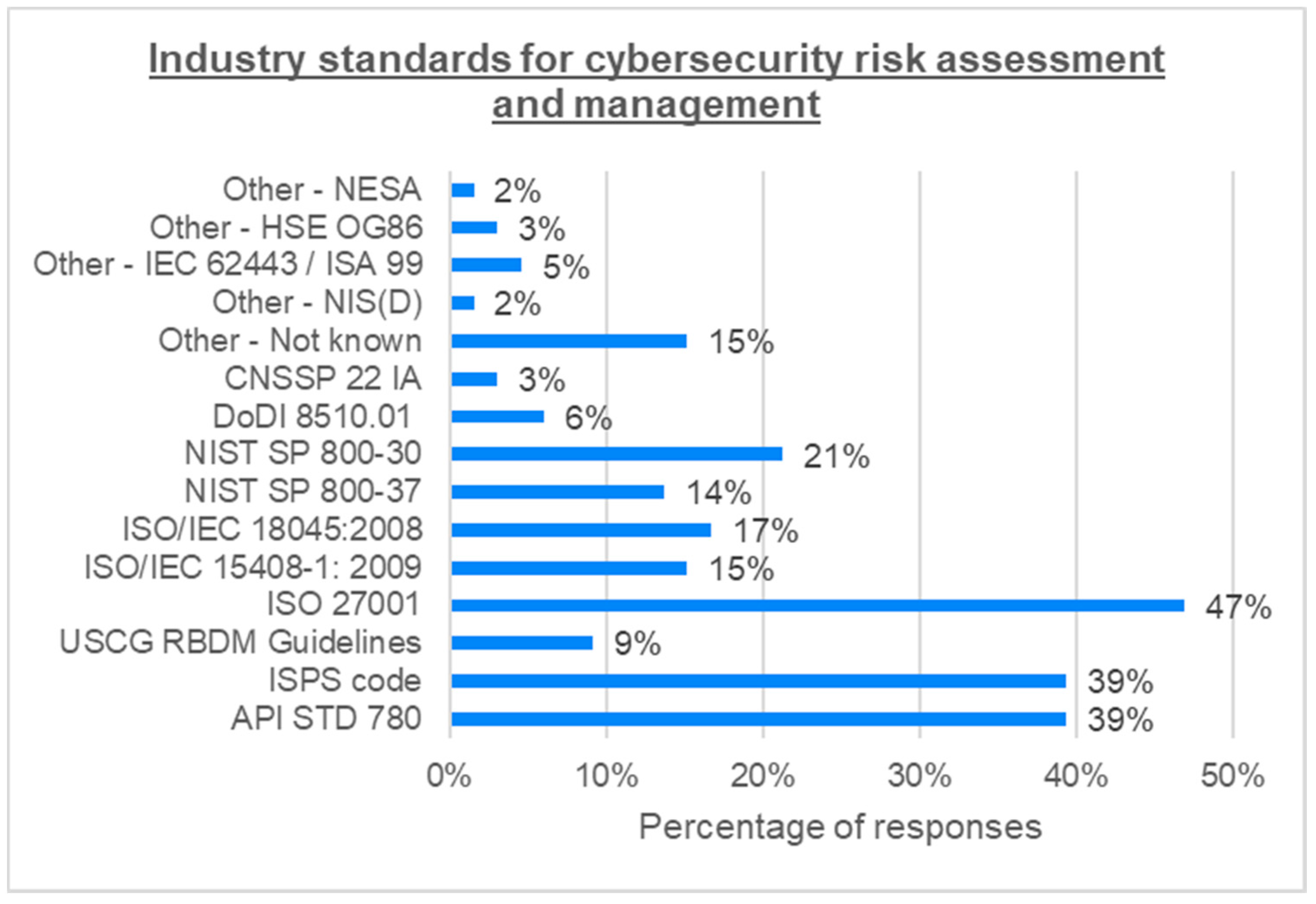
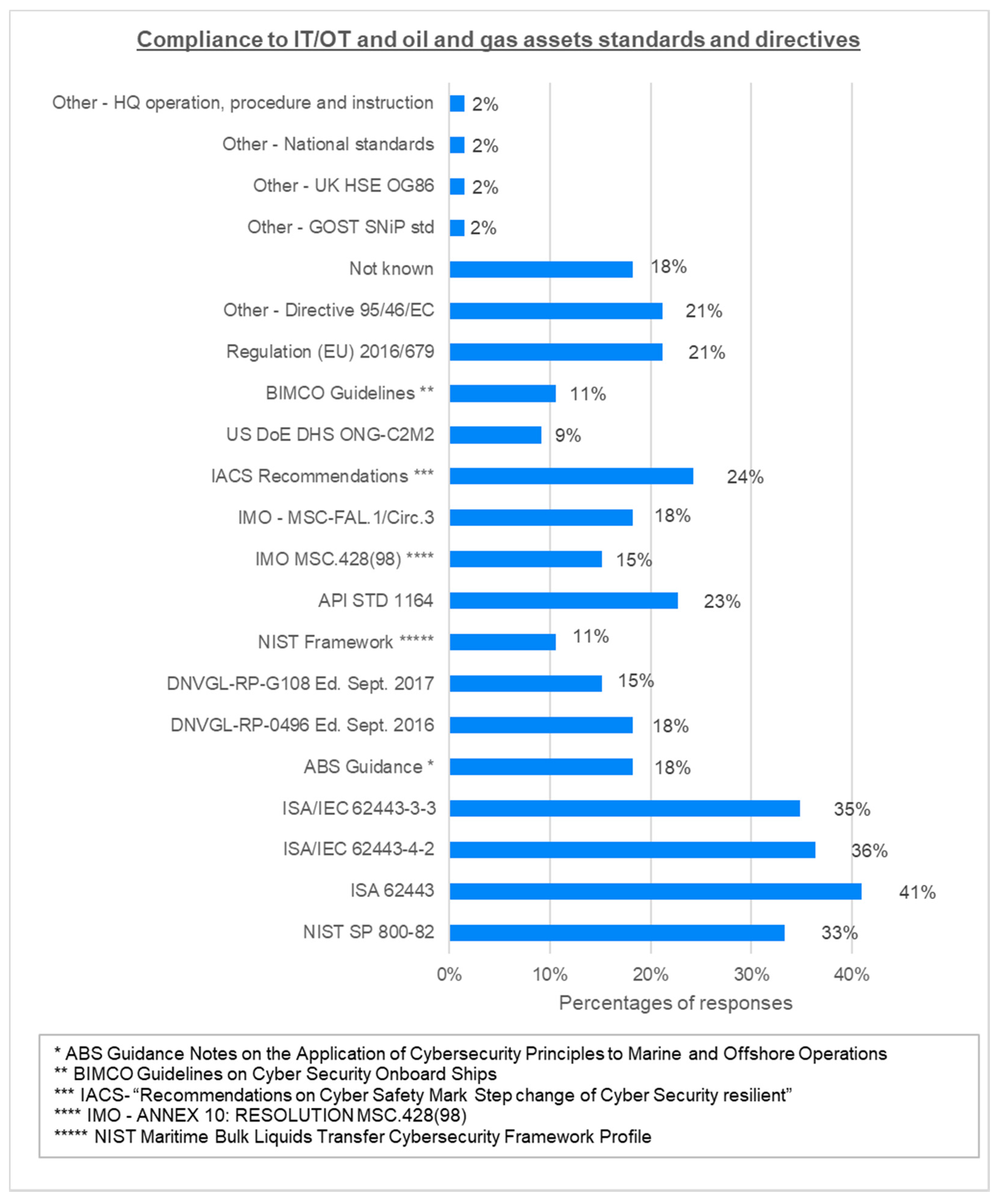
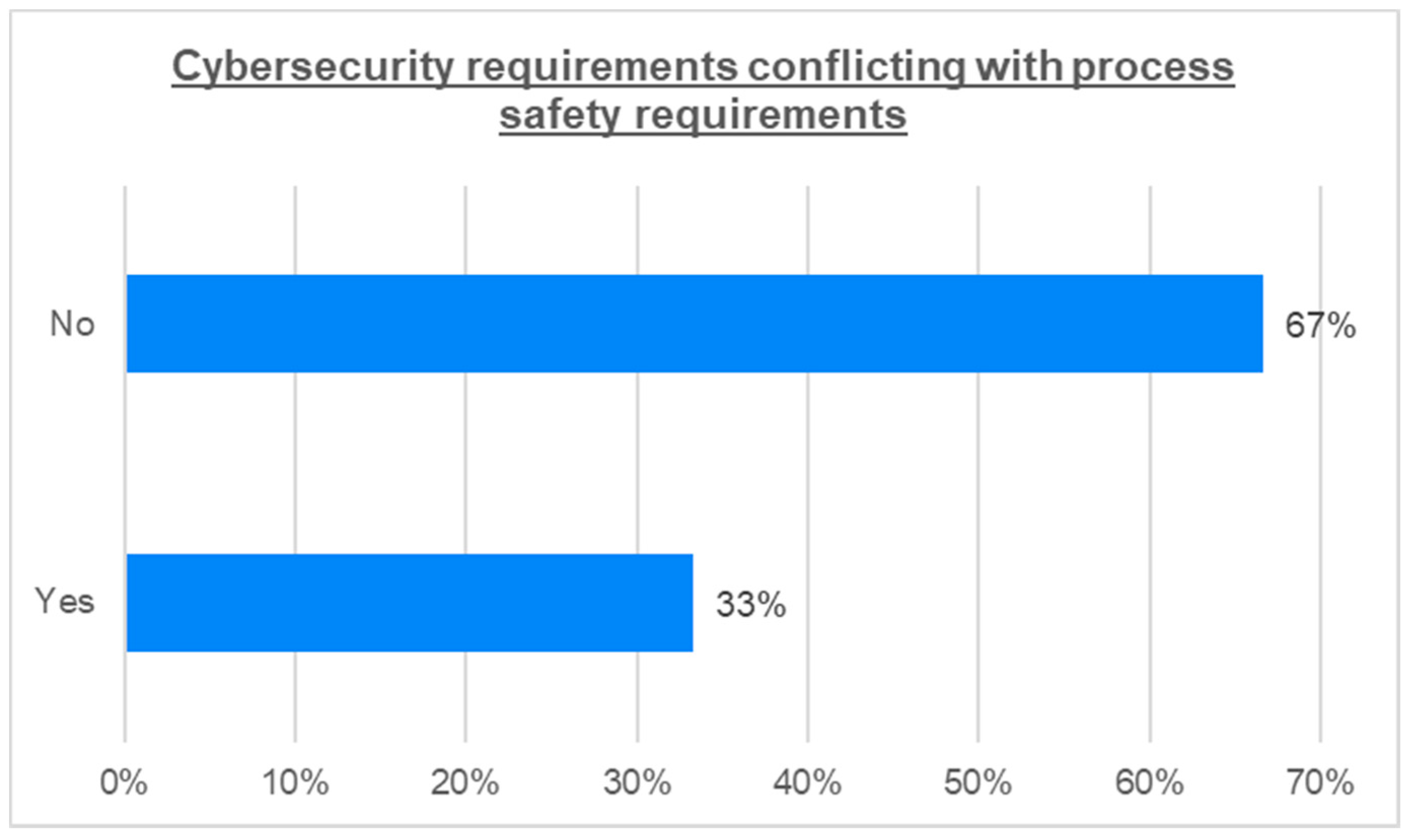
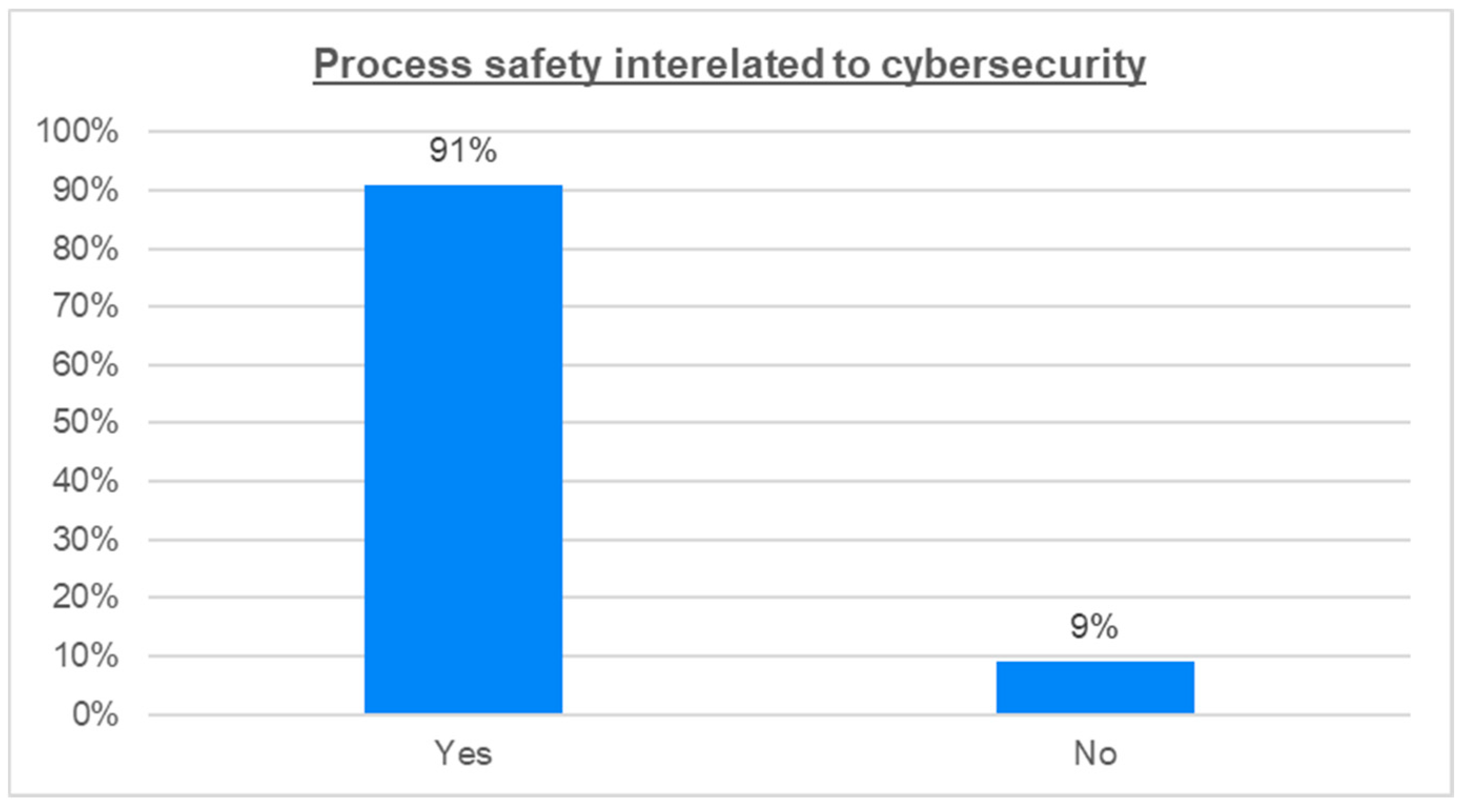
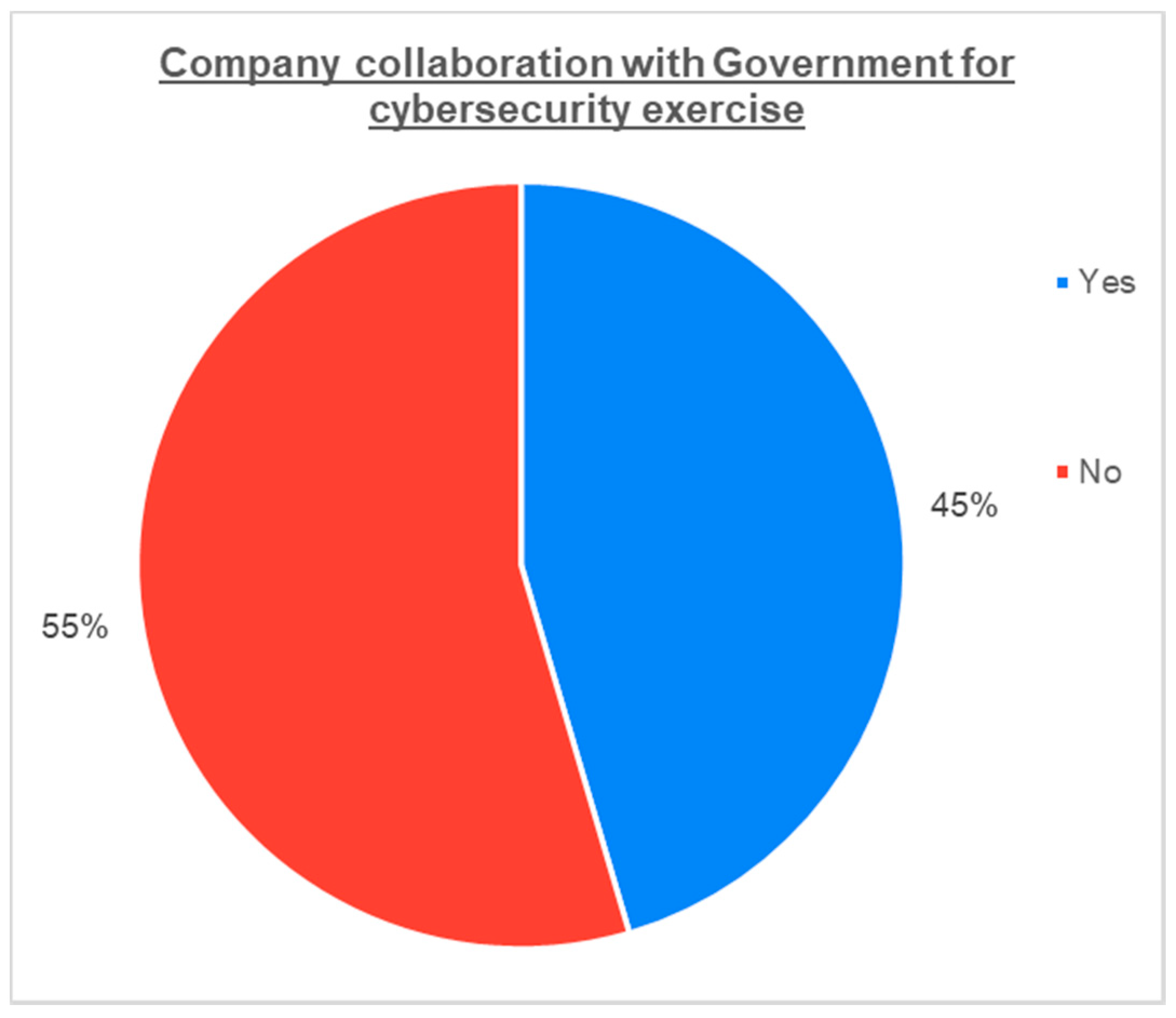
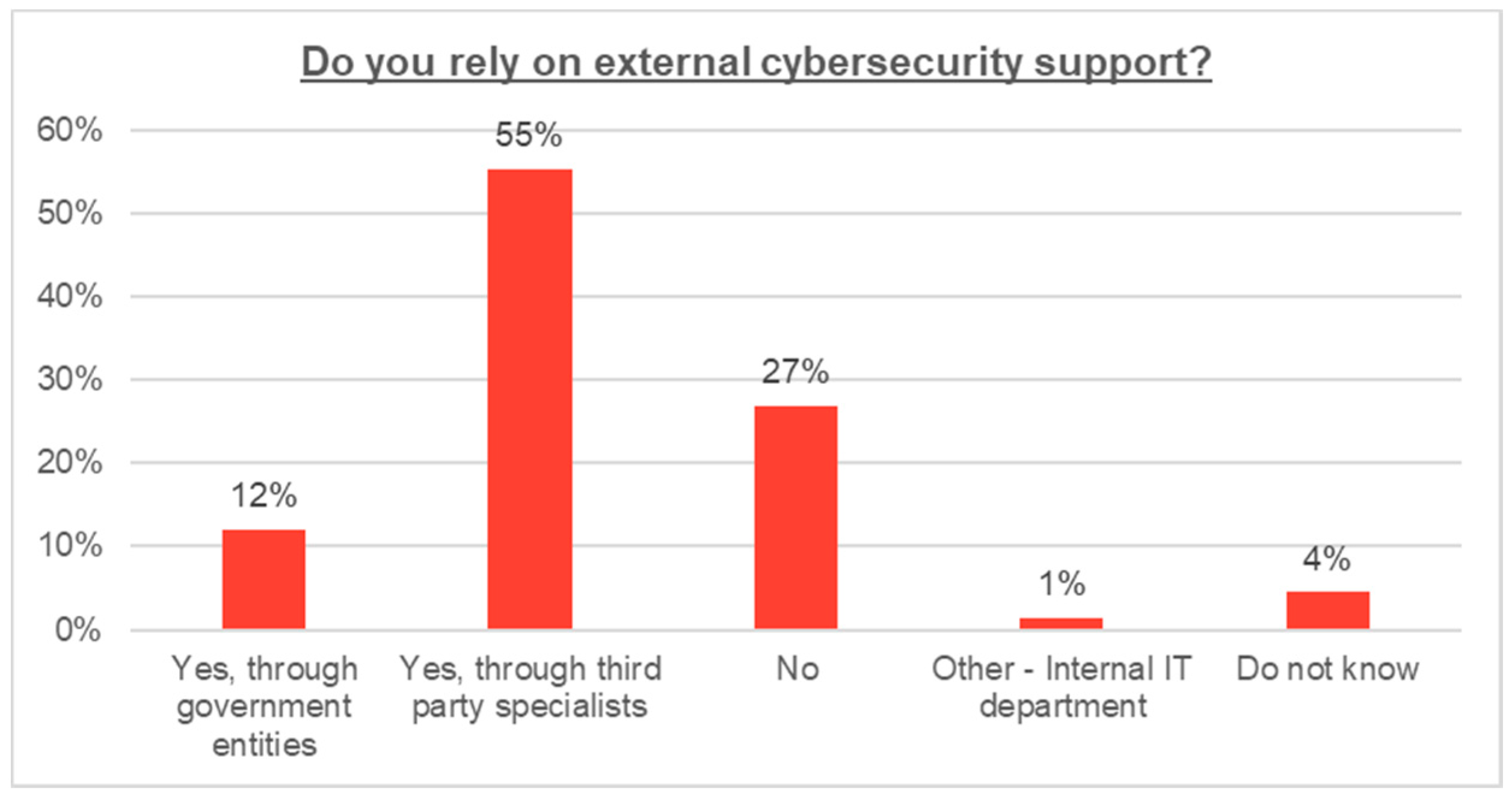
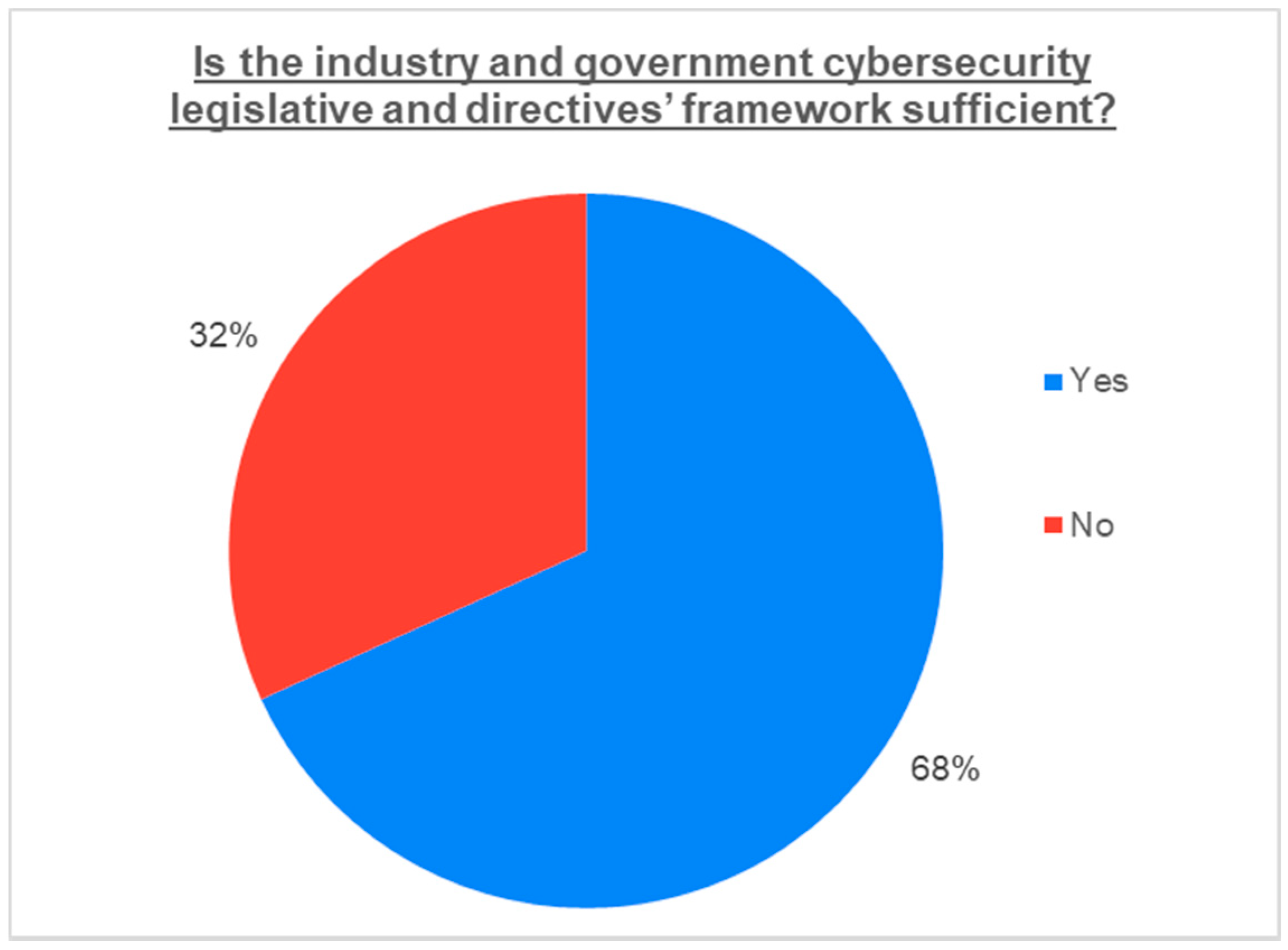
4.2. Survey Results and Analysis
5. Conclusions
- The adaptation of measures for the mitigation of insider threats: As illustrated from the survey results, insider-led malicious acts rank high in their probability to occur. Their mitigation is considered difficult as they constitute a hybrid type of threats that can include criminal intent, unintentional actions, as well as state sponsored espionage. These measures can be methods and tools used by the military and government sectors that could be replicated to the possible extent in order to tackle these threats in a proactive manner.
- The implementation of countermeasures against hostile unmanned platforms (i.e., UAVs, UUVs, USVs): Unmanned platforms or drones are continuously advancing in performance and technological characteristics and pose a significant threat that can cause electronic interference or even attack against network-connected devices [56]. Countermeasures to be implemented should consider the special operational conditions of offshore oil and gas assets and should not impede the safety of infrastructure, systems, or personnel. These countermeasures can be electronic countermeasures or kinetic-type of weapons that neutralize such airborne, surface, or underwater threats, similar to the ones used by the military or government security agencies.
- The improvement of corporate and industry culture on the perception of cyber security: This is a difficult feat that can be achieved through the study of known attacks in the industry, the sharing of information on such attacks through industry organizations, the increased communication between industry sectors and companies’ departments, and the increased and continuous training of individuals on the subject. These are also suggested by government and industry reports from Folga et al. and the Argonne National Laboratory [29].
- The increased monitoring of cyber security performance indicators through the use of corporate KPIs
- The increased collaboration with the government and the military for the training of personnel, simulation of attack scenarios, and general raising of awareness on the subject at a legislative and national security level
- The abolition of USB devices from the available toolkit of the offshore oil and gas domain: This could be achieved by the further integration of IIoT and wireless communication but with their enhanced security features.
- The increased capital and operational expenditure for cyber security measures dictated by industry standards and national legislation: As the offshore oil and gas sector is considered critical for many national economies and supporting numerous others critical infrastructures, it is obvious that funding and resources need to be allocated to increase asset and organizational resiliency.
6. Limitations and Future Work
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Eversheds Sutherland Ltd. Microsoft Report DTUK001917_10/18: Responding to the Evolving Cyber Threat Landscape in the Oil and Gas Sector; Eversheds Sutherland Ltd.: London, UK, 2018. [Google Scholar]
- Coble, S. Attacks Against Oil and Gas Industry on the Rise. Available online: https://www.infosecurity-magazine.com/news/attacks-against-oil-and-gas (accessed on 24 September 2020).
- Ovcina, J. Naval Dome: 400% Increase in Attempted Hacks Since February 2020. Available online: https://www.offshore-energy.biz/naval-dome-400-increase-in-attempted-hacks-since-february-2020/ (accessed on 10 August 2020).
- Lu, H.; Guo, L.; Azimi, M.; Huang, K. Oil and Gas 4.0 era: A systematic review and outlook. Comput. Ind. 2019, 111, 68–90. [Google Scholar] [CrossRef]
- Lamb, K. Challenges of Digitalisation in the Offshore Oil and Gas Sector. In University of Cambridge CMBB Research Bridgehead Report CDBB_REP_001; Center for Digital Build Britain (CDBB): Cambridge, UK, 2018. [Google Scholar]
- Mohammadpoor, M.; Torabi, F. Big Data analytics in oil and gas industry: An emerging trend. J. Pet. 2018. Under Publication. [Google Scholar] [CrossRef]
- Nguyen, T.; Gosine, R.G.; Warrian, P. A Systematic Review of Big Data Analytics for Oil and Gas Industry 4.0. IEEE Access 2020, 8, 61183–61201. [Google Scholar] [CrossRef]
- Gharbi, R.B.C.; Mansoori, G.A. An introduction to artificial intelligence applications in petroleum exploration and production. J. Pet. Sci. Eng. 2005, 49, 93–96. [Google Scholar] [CrossRef]
- Bello, O.; Holzmann, J.; Yaqoob, T.; Teodoriu, C. Application of Artificial Intelligence Methods in Drilling System Design and Operations: A Review of the State Of The Art. J. Artif. Intell. Soft Comput. Res. 2015, 5, 121–139. [Google Scholar] [CrossRef]
- LaGrange, E. Developing a Digital Twin: The Roadmap for Oil and Gas Optimization. In Proceedings of the 2019 SPE Offshore Europe Conference and Exhibition, Aberdeen, UK, 3–6 September 2019. [Google Scholar]
- Holmås, H.; Sjåtil, O.A.; Santamarta, S.; Lindseth, S.H.; Forbes, P.W.; Romanin, P. Creating Value with Digital Twins in Oil and Gas; Boston Consulting Group: Boston, MA, USA, 2019. [Google Scholar]
- Thibaud, M.; Chi, H.; Zhou, W.; Piramuthu, S. Internet of things (IoT) in high-risk Environment, Health and Safety (EHS) industries: A comprehensive review. J. Decis. Support Syst. 2018, 108, 79–95. [Google Scholar] [CrossRef]
- Nikitakos, N.; Progoulakis, I. An introduction to the security assessment for offshore oil and gas installations. NMIOTC MIO J. 2019, 18, 10–18. [Google Scholar]
- Lobo, F. Upstream Oil & Gas Cyber Risk: Insurance Technical Review; Lloyd’s Market Assoc.: London, UK, 2018. [Google Scholar]
- Crandal, J. Cybersecurity and Offshore Oil: The Next Big Threat. 4 Oil & Gas. Nat. Resour. Energy J. 2019, 4, 703–735. [Google Scholar]
- Soares, L.; Souza, R. Cyber Risks in the Oil & Gas Industry. In Proceedings of the Rio Oil and Gas Expo and Conference, Rio de Janeiro, Brazil, 15–18 September 2014. [Google Scholar]
- Hacquebord, F.; Pernet, C. Drilling Deep: A look at Cyberattacks on the Oil and Gas Industry, Trend Micro Research. 2019. Available online: https://www.trendmicro.com/vinfo/us/security/news/internet-of-things/drilling-deep-a-look-at-cyberattacks-on-the-oil-and-gas-industry (accessed on 28 September 2020).
- Ginter, A. Secure Operations Technology; Abterra Technologies Inc.: Calgary, AB, Canada, 2018. [Google Scholar]
- Lawrence Livermore National Laboratory (LLNL). Dragonstone Strategy—State of Cybersecurity in the Oil & Natural Gas Sector. In US Government—Lawrence Livermore National Security LLC Report LLNL-TR-805864; LLNL: Livermore, CA, USA, 2020. [Google Scholar]
- Dragos Inc. Global Oil and Gas Cyber Threat Perspective: Assessing the Threats, Risks, and Activity Groups Affecting the Global Oil and Gas Industry. August 2019. Available online: https://www.dragos.com/wp-content/uploads/Dragos-Oil-and-Gas-Threat-Perspective-2019.pdf (accessed on 1 August 2019).
- Hadjistassou, C.; Bratskas, R.; Koutras, N.; Kyriakides, A.; Charalambous, E.; Hadjiantonis, A.M. Safeguarding critical infrastructures from cyber attacks: A case study for offshore natural gas assets. J. Pol. Saf. Reliab. Assoc. 2015, 6, 115–123. [Google Scholar]
- Stergiopoulos, G.; Gritzalis, D.A.; Limnaios, E. Cyber-Attacks on the Oil & Gas Sector: A Survey on Incident Assessment and Attack Patterns. IEEE Access 2020, 8, 128440–128475. [Google Scholar]
- Moreno, V.C. Analysis of physical and cyber security-related events in the chemical and process industry. Process Saf. Environ. Prot. 2018, 116, 621–631. [Google Scholar] [CrossRef]
- Rohmeyer, P.; Bayuk, J.L. Financial Cybersecurity Risk Management; Springer: Berlin/Heidelberg, Germany, 2019. [Google Scholar]
- Fazzini, K. CNBC Tech News. The Saudi Oil Attacks Could Be a Precursor to Widespread Cyberwarfare—With Collateral Damage for Companies in the Region. 2019. Available online: https://www.cnbc.com/2019/09/21/saudi-aramco-attacks-could-predict-cyber-warfare-from-iran.html (accessed on 9 December 2019).
- Clayton, B.; Segal, A. Council on Foreign Relations Energy Brief: Addressing Cyber Threats to Oil and Gas Suppliers. 2013. Available online: https://www.files.ethz.ch/isn/166056/Energy_Brief_Clayton_Segal.pdf (accessed on 12 September 2020).
- Deloitte University Press. Protecting the Connected Barrels—Cybersecurity for Upstream Oil and Gas, A Report by Deloitte Center for Energy Solutions, Houston, TX, USA. 2017. Available online: https://www2.deloitte.com/tr/en/pages/energy-and-resources/articles/oil-and-gas-cybersecurity.html (accessed on 27 June 2019).
- Lewis, T.G. Critical Infrastructure Protection in Homeland Security, 3rd ed.; Willey: Hoboken, NJ, USA, 2020. [Google Scholar]
- Stephen, F.S.; Talaber, L.; McLamore, M.; Kraucunas, I.; McPherson, T.; Manzanares, T.; Parrott, L. Literature Review and Synthesis for the Natural Gas Infrastructure. In Argonne National Laboratory Report ANL/GSS-15/5; Argonne, IL, USA, 2015. Available online: https://www.osti.gov/biblio/1350046 (accessed on 22 January 2021).
- NTT Security Global Overview: Cybersecurity Expertise in the oil and Gas Sector. In NTT Security—NTT Group Report; NTT Group: Tokyo, Japan, 2019.
- Chevron Says Hit by Stuxnet Virus in 2010. 2012. Available online: https://phys.org/news/2012-11-chevron-stuxnet-virus.html (accessed on 28 September 2020).
- ENISA Report ETL2020. Cyber Espionage: ENISA Threat Landscape from January 2019 to April 2020; ENISA (European Union Agency for Cybersecurity): Athens, Greece, 2020.
- Katharina Rick and Karthik Lyer, BCG Perspectives: Countering the Threat of Cyberattacks in Oil and Gas. 2016. Available online: https://www.bcg.com/publications/2016/upstream-oil-gas-technology-digital-countering-the-threat-of-cyberattacks-in-oil-and-gas (accessed on 3 December 2019).
- DNV GL, Cyber Security Vulnerabilities for the Oil and Gas Industry, Lysne Committee Study—Executive Summary. 2015. Available online: https://www.dnvgl.com/oilgas/download/lysne-committee-study.html (accessed on 9 September 2019).
- Yang, L.; Cao, X.; Li, J. A new cyber security risk evaluation method for oil and gas SCADA based on factor state space. J. Chaos Solitons Fractals 2015, 89, 203–209. [Google Scholar] [CrossRef]
- Vieira, A.C.; Houmb, S.H.; Insua, D.R. A Graphical Adversarial Risk Analysis Model for Oil and Gas Drilling Cybersecurity; GraMSec: Grenoble, France, 2014; pp. 78–93. [Google Scholar]
- Siva Prasad, M.V.V.; Avadhani, P.S. Attack Tree Design and Analysis of Offshore Oil and Gas Process Complex SCADA System. Int. J. Comput. Appl. 2019, 181, 12–18. [Google Scholar]
- Refsdal, A.; Solhaug, B.; Stølen, K. Security risk analysis of system changes exemplified within the oil and gas domain. Int. J. Softw. Tools Technol. Transf. 2015, 17, 251–266. [Google Scholar] [CrossRef]
- Marcin, Ś.; Emilian, P. Procedure based functional safety and information security management of industrial automation and control systems on example of the oil port installations. J. Pol. Saf. Reliab. Assoc. 2017, 8, 129–138. [Google Scholar]
- Kosmowski, K.T.; Gołębiewski, D. Functional safety and cyber security analysis for life cycle management of industrial control systems in hazardous plants and oil port critical infrastructure including insurance. J. Pol. Saf. Reliab. Assoc. 2019, 10, 99–126. [Google Scholar]
- McEvoy, T.R.; Wolthusen, S. An Attack Analysis of Managed Pressure Drilling Systems on Oil Drilling Platforms. In Proceedings of the International Conference on Critical Information Infrastructures Security CRITIS 2014, Berlin, Germany, 2–3 September 2014; pp. 109–121. [Google Scholar]
- Fataliyev, T.K.; Mehdiyev, S.A. Analysis and New Approaches to the Solution of Problems of Operation of Oil and Gas Complex as Cyber-Physical System. Inf. Technol. Comput. Sci. 2018, 11, 67–76. [Google Scholar] [CrossRef]
- Aalsalem, M.Y.; Khan, W.Z.; Gharibi, W.; Khan, M.K.; Arshad, Q. Wireless Sensor Networks in oil and gas industry: Recent advances, taxonomy, requirements, and open challenges. J. Netw. Comput. Appl. 2018, 113, 87–97. [Google Scholar] [CrossRef]
- Radmand, P.; Talevski1, A.; Petersen, S.; Carlsen, S. Taxonomy of Wireless Sensor Network Cyber Security Attacks in the Oil and Gas Industries. In Proceedings of the 2010 24th IEEE International Conference on Advanced Information Networking and Applications, Perth, WA, Australia, 20–23 April 2010; pp. 949–957. [Google Scholar]
- Sveen, F.O.; Qian, Y.; Hillen, S.; Radianti, J.; Gonzalez, J.J.; Dynamic, A. Approach to Vulnerability and Risk Analysis of the Transition to eOperations. In Proceedings of the 24th International Conference of the System Dynamics Society, Nijmegen, The Netherlands, 23–27 July 2006. [Google Scholar]
- Rydzak, F.; Breistrand, L.; Sveen, F.O.; Qian, Y.; Gonzalez, J.J. Exploring resilience towards risks in eOperations in the oil and gas industry. In Proceedings of the 25th international conference on Computer Safety, Reliability, and Security SAFECOMP’06, Gdansk, Poland, 27–29 September 2006; pp. 57–70. [Google Scholar]
- Spandonidis, C.C.; Giordamlis, C. Data-centric Operations in Oil & Gas Industry by the Use of 5G Mobile Networks and Industrial Internet of Things (IIoT). In Proceedings of the Thirteenth International Conference on Digital Telecommunications ICDT, Athens, Greece, 22–26 April 2018. [Google Scholar]
- Erkoyuncu, J.A.; Ononiwu, S.; Roy, R. Mitigating the Risk of Software Obsolescence in the Oil and Gas Sector. In Proceedings of the 3rd International Conference on Through-life Engineering Services, Procedia CIRP 22, Cranfield, UK, 2–4 July 2014; pp. 81–86. [Google Scholar]
- ENISA Report, Report on Cyber Security Information Sharing in the Energy Sector; ENISA (European Union Agency for Cybersecurity): Athens, Greece, 2016.
- Holcomb, J. Definitive Guide to Cybersecurity for the Oil & Gas Industry. In LEIDOS Ebook Report; LEIDOS Holdings Inc.: Reston, VA, USA, 2016; Available online: https://www.ciosummits.com/Online_Assets_Leidos_Definitive_Guide_to_Cyber_for_Oil_and_Gas_eBook.pdf (accessed on 17 January 2021).
- Oil and Natural Gas Subsector Coordinating Council (ONG SCC); Natural Gas Council (NGC). Defense-in-Depth: Cybersecurity in the Natural Gas and Oil Industry. In ONG SCC and NGC Report; Washington, DC, USA, 2018; Available online: http://ongsubsector.com/ (accessed on 22 January 2021).
- Sam Chambers, Number of Shipping Cyber Attacks Leaps 400% Since February. Available online: https://splash247.com/number-of-shipping-cyber-attacks-leaps-400-since-february/ (accessed on 6 July 2020).
- David Paul, Weathering the Storm: The Oil and Gas Sector and COVID-19. Available online: https://digit.fyi/weathering-the-storm-the-oil-and-gas-sector-and-covid-19/ (accessed on 15 June 2020).
- Jeff Williams and Piotr Ciepiela, Six Cybersecurity Issues for Oil and Gas Companies. 2019. Available online: https://www.ey.com/en_gl/oil-gas/six-cybersecurity-issues-for-oil-and-gas-companies (accessed on 12 November 2019).
- Ponemon Institure LLC/SIEMENS, The State of Cybersecurity in the Oil & Gas Industry: United States. 2017. Available online: https://assets.siemens-energy.com/siemens/assets/api/uuid:4ec3d46c-234e-4f48-9bc7-aef5889dcaba/ponemoncyberreadinessinoilgasfinal.pdf (accessed on 23 August 2020).
- Katharina, L.B. How to Analyze the Cyber Threat from Drones. In RAND Report RR2972; RAND Corp.: Santa Monica, CA, USA, 2020. [Google Scholar]
| Category | Originator | Title |
|---|---|---|
| Standards | NIST | NIST Special Publications 800-30, 800-37, 800-82 |
| ASTM | ASTM F3286-17, ASTM F3449-20 | |
| ISO/IEC | ISO/IEC 27001, IEC-62443-4-2, IEC 62443-3-3, ISO/IEC 21827, ISO/IEC 15408-1, ISO/IEC 18045, and ISO/IEC 27032 | |
| API | API RP 70, API RP 70I, API RP 780, API Standard 1164 | |
| Industry organizations | IMO | IMO Resolution MSC.428(98), IMO Guidance MSC-FAL.1/Circ.3 |
| IADC | IADC guideline: “Assessing and Managing Cybersecurity Risks to Drilling Assets (2015)” IADC guideline: “Guidelines for Baseline Cybersecurity for Drilling Assets (2018)” | |
| Government | DHS and DoE | Oil and Natural Gas Subsector Cybersecurity Capability Maturity Model (ONG-C2M2) |
| USCG | NVIC 01-20 | |
| U.S. Congress | Bill S. 4023 “Enhancing Maritime Cybersecurity Act of 2020” | |
| European Union | 2008/114/EC, 2013/30/EU, 2016/1148/EU, 2019/881/EU, EU Cybersecurity strategy JOIN/2013/01, ENISA report 2016 | |
| MPA Singapore | Shipping Circular No. 15 (2020) | |
| Maritime classification societies | ABS | ABS “Guidance Notes on the Application of Cybersecurity Principles to Marine and Offshore Operations—ABS CyberSafety Vol. 1”, September 2016 ABS “Guide for Cybersecurity Implementation for the Marine and Offshore Industries—ABS CyberSafety Vol. 2”, June 2018 (revised) ABS “Guidance Notes on Data Integrity for Marine and Offshore Operations—ABS CyberSafety Vo. 3”, September 2016 ABS “Guide for Software Systems Verification—ABS CyberSafety Vol. 4”, September 2016 ABS “Guidance Notes on Software Provider Conformity Program—ABS CyberSafety Vol. 5”, September 2016 |
| DNV GL | DNVGL-RP-G108 (2017), DNVGL-RP-G 496 (2016), DNVGL-CP-0231 (2018) | |
| Lloyd’s Register | Lloyd’s Register Guidance Note: Cyber-enabled ships—Deploying information and communications technology in shipping—Lloyd’s Register’s approach to assurance, 2016. Lloyd’s Register Guidance Note: Cyber-enabled ships—ShipRight procedure—autonomous ships, 2016. Lloyd’s Register Guidance Note: Cyber-enabled ships—Type Approval of Cyber Enabled Systems Components, 2016. | |
| Class NK | Class NK, “Guidelines for Designing Cyber Security Onboard Ships”, 2nd Ed., July 2020. Class NK, “Cyber Security Management Systems for Ships”, 1st Ed., April 2019. |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Progoulakis, I.; Nikitakos, N.; Rohmeyer, P.; Bunin, B.; Dalaklis, D.; Karamperidis, S. Perspectives on Cyber Security for Offshore Oil and Gas Assets. J. Mar. Sci. Eng. 2021, 9, 112. https://doi.org/10.3390/jmse9020112
Progoulakis I, Nikitakos N, Rohmeyer P, Bunin B, Dalaklis D, Karamperidis S. Perspectives on Cyber Security for Offshore Oil and Gas Assets. Journal of Marine Science and Engineering. 2021; 9(2):112. https://doi.org/10.3390/jmse9020112
Chicago/Turabian StyleProgoulakis, Iosif, Nikitas Nikitakos, Paul Rohmeyer, Barry Bunin, Dimitrios Dalaklis, and Stavros Karamperidis. 2021. "Perspectives on Cyber Security for Offshore Oil and Gas Assets" Journal of Marine Science and Engineering 9, no. 2: 112. https://doi.org/10.3390/jmse9020112
APA StyleProgoulakis, I., Nikitakos, N., Rohmeyer, P., Bunin, B., Dalaklis, D., & Karamperidis, S. (2021). Perspectives on Cyber Security for Offshore Oil and Gas Assets. Journal of Marine Science and Engineering, 9(2), 112. https://doi.org/10.3390/jmse9020112









