1. Introduction
With the advances in wireless communication technology, the global mobility network (GLOMONET) [
1,
2,
3] has become a popular means of communication. Users can access roaming services through mobile devices; therefore, people’s access to knowledge has been improved significantly. In GLOMONET, each mobile user depends on a specific home agent (HA) where they are registered. If the mobile user is in the domain of a foreign agent (FA), the FA must ensure service after authenticating the mobile user. However, as a mobile device has limited resources available in terms of computing power, memory, and battery capacity [
4,
5], it is not suitable to apply symmetric and asymmetric cryptosystems that generate high computational overheads. In this case, mobile users can face delays during processing and service availing. In addition, a malicious adversary may attempt various attacks using sensitive data transmitted via an insecure channel in GLOMONET. Therefore, secure and efficient mutual authentication has become an essential security requirement to provide secure roaming services for legitimate mobile users. The security requirements for GLOMONET are summarized as follows:
Secure and efficient authentication schemes are required to provide various services in GLOMONET.
Authentication schemes must resist various attacks, including stolen mobile devices, masquerades, and trace attacks.
Authentication schemes must consider the limitations of mobile devices relative to the computing power, memory, and battery capacity [
4,
5].
In the last few years, many authentication schemes have been presented for GLOMONET to ensure the security of users [
6,
7,
8,
9]. In 2004, Zhu et al. [
10] presented an efficient two-factor authentication scheme to provide the roaming facility. However, Lee et al. [
11] indicated that Zhu et al.’s [
10] protocol did not resist impersonation attacks and also could not achieve user authentication. In 2006, Lee et al. [
11] presented an improved protocol for wireless environments to overcome the security flaws of Zhu et al.’s scheme. However, Wu et al. [
12] assessed that Lee et al.’s [
11] scheme did not withstand perfect backward secrecy and did not ensure user anonymity. In 2012, Li et al. [
13] assessed that Wu et al.’s [
12] scheme could not withstand replay and masquerade attacks and also could not provide user anonymity.
To overcome these security flaws, Li et al. [
13] then proposed a novel user authentication scheme based smart-card to provide efficient high computational and communication overheads. However, Das et al. [
14] demonstrated that Li et al.’s protocol [
13] was sensitive to replay attacks and did not achieve proper user password updates in the password change processes. In 2015, Marimuthu and Saravanan [
15] presented a secure authentication protocol in GLOMONET. However, Madhusudhan et al. [
16] proved that their protocol could not withstand offline guessing, insider, stolen-verifier, denial of service, and forgery attacks.
In 2018, Madhusudhan et al. [
16] presented a secure and efficient user authentication scheme for GLOMONET using a mobile device to resolve the security problems of Marimuthu and Saravanan’s scheme. Madhusudhan et al. claimed that their scheme could prevent replay and masquerade attacks and provide secure mutual authentication. Unfortunately, we analyzed that Madhusudhan et al.’s scheme [
16] could not prevent various security threats and could not provide secure mutual authentication. Moreover, Madhusudhan et al.’s scheme [
16] was unsuitable for resource-constrained mobile devices as it uses symmetric key encryption and modular multiplication, which generate high computational overheads. Thus, we proposed a secure and efficient three-factor user authentication scheme for roaming services in GLOMONET to resolve the security flaws of Madhusudhan et al.’s scheme.
1.1. Motivation and Contributions
We have studied numerous user authentication schemes [
6,
8,
15,
16] for roaming services and found that they had the following in common:
- 1.
Many authentication protocols [
6,
8,
15,
16] are exposed to well-known attacks, such as masquerade, replay, mobile device theft, and session key disclosure attacks in global mobility environments.
- 2.
Many authentication schemes must provide secure convenience for mobile users in the GLOMONET and must take into account all the security requirements specified in
Section 1.2.
- 3.
Secure and lightweight authentication schemes are essential, which take into account limitations for resource-constrained mobile devices relative to computing power, memory, and battery capacity.
Recently, Madhusudhan et al. [
16] presented a secure and efficient user authentication scheme for GLOMONET using a mobile device. They claimed that their scheme could resist various attacks and could ensure secure mutual authentication and anonymity. However, our paper presents a brief review of Madhusudhan et al.’s scheme [
16], and we demonstrated that their scheme could not prevent various security threats. To resolve the security threats of Madhusudhan et al.’s scheme, we proposed a secure and efficient three-factor authentication protocol. The proposed scheme demonstrated several advantages compared with previous related authentication schemes.
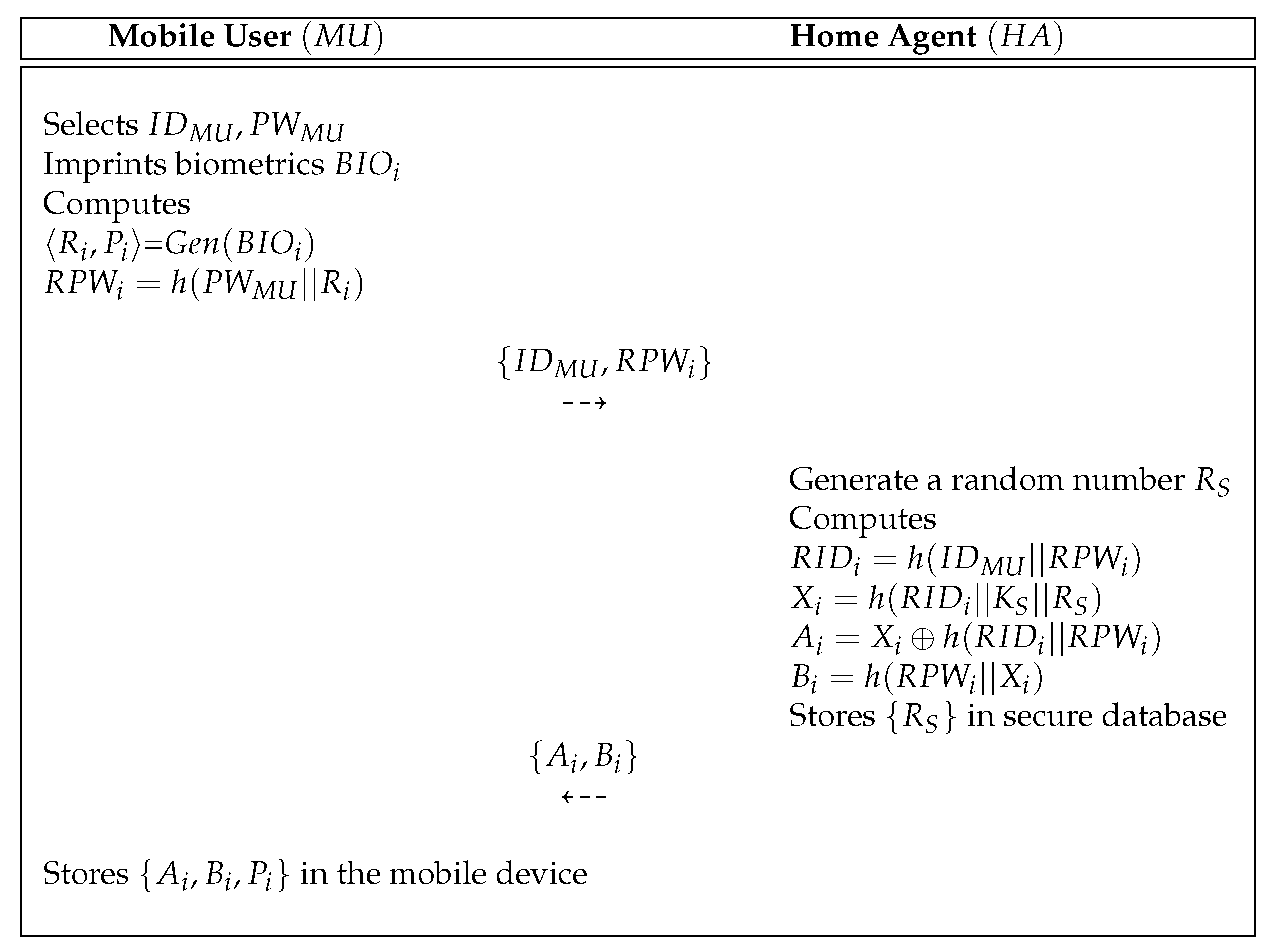
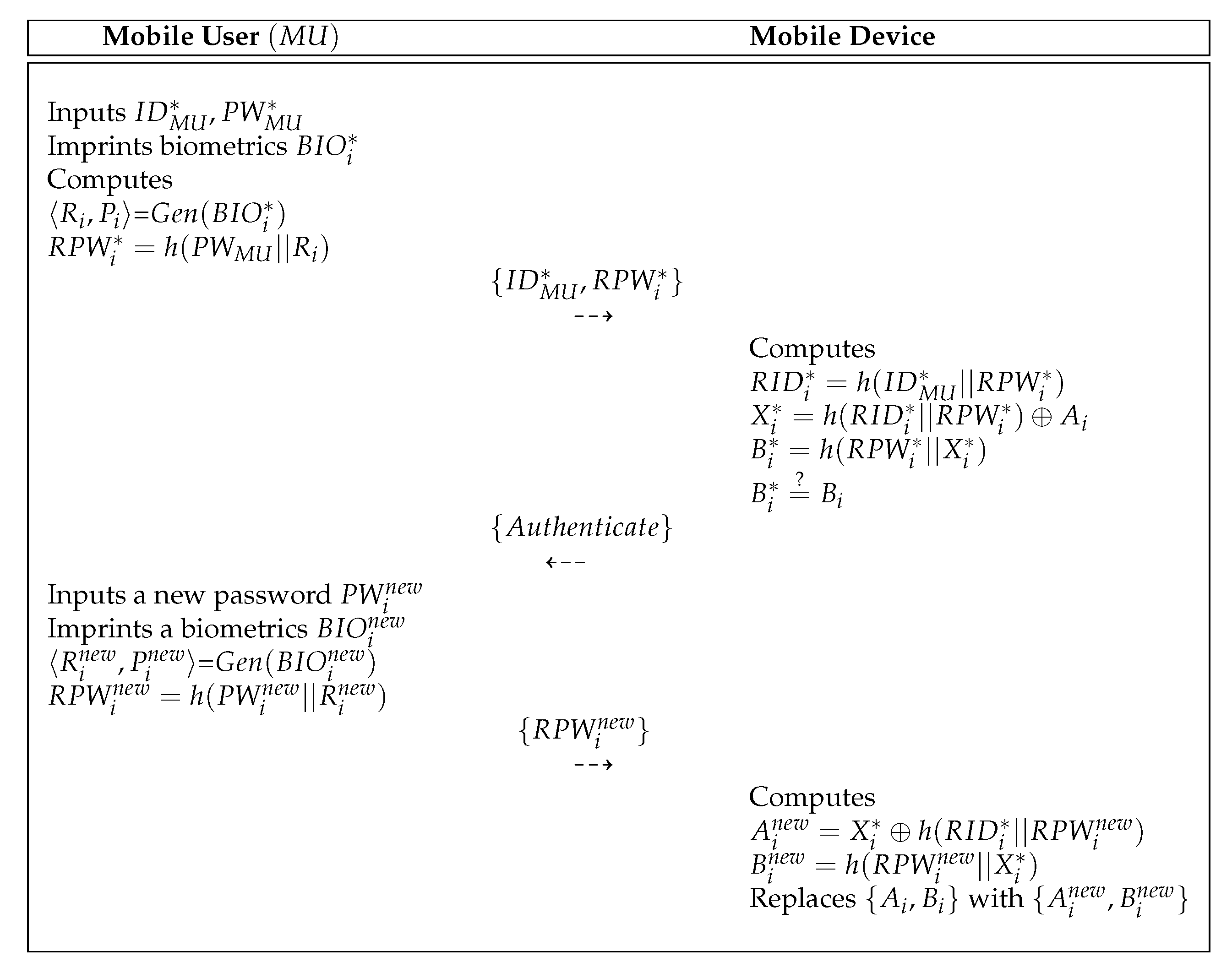
First, the proposed scheme could prevent various attacks, such as mobile device theft, masquerade, session key disclosure, and replay attacks and also provided secure mutual authentication, user anonymity, and user friendliness. Second, the proposed scheme used the fuzzy extractor mechanism to improve the security level of the protocol. Even if two of the three factors were compromised, the proposed scheme was still secure. Finally, the proposed scheme provided better effective computation costs with related schemes as it only utilized the one-way hash function. Therefore, the proposed scheme was secure, efficient, and more suitable for practical mobile and wireless environments.
1.2. Security Requirements
The research on the security of communication for GLOMONET has shown that the security requirements are essential to produce a secure and efficient authentication protocol.
Table 1 shows the security requirements for authenticaiton and key agreement protocol.
1.3. Organization
The remainder of this paper is organized as follows. In
Section 2, we present the preliminaries, and in
Section 3, we review Madhusudhan et al.’s scheme [
16]. In
Section 4 and
Section 5, we assess the security flaws of Madhusudhan et al.’s scheme [
16] and present a secure and efficient authentication scheme for GLOMONET to overcome the security flaws of Madhusudhan et al.’s scheme [
16]. In
Section 6, we demonstrate the security of our scheme using informal security analysis and formal security analysis, including Burrows–Abadi–Needham (BAN) logic and the real-or-random (ROR) model. In
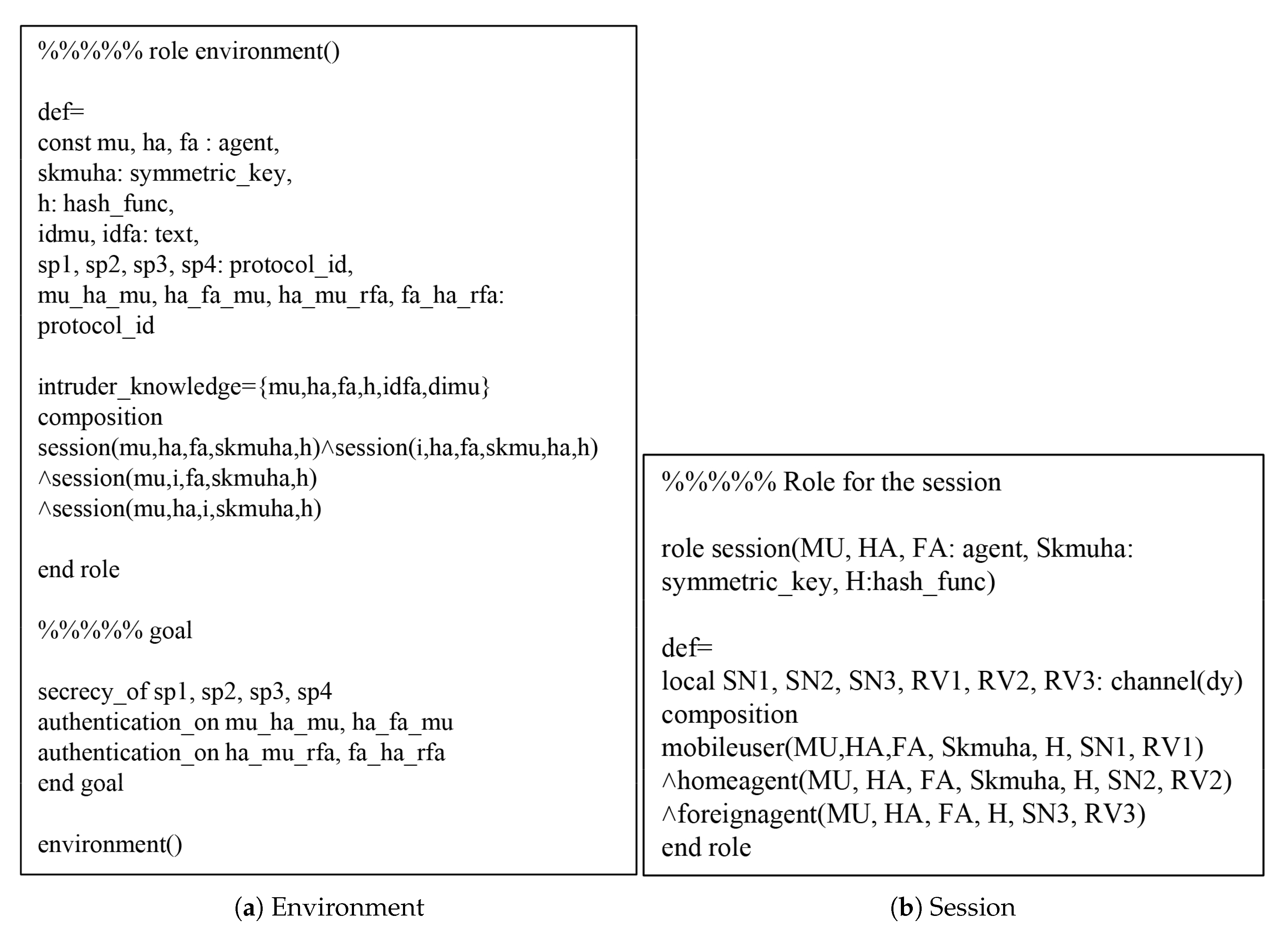
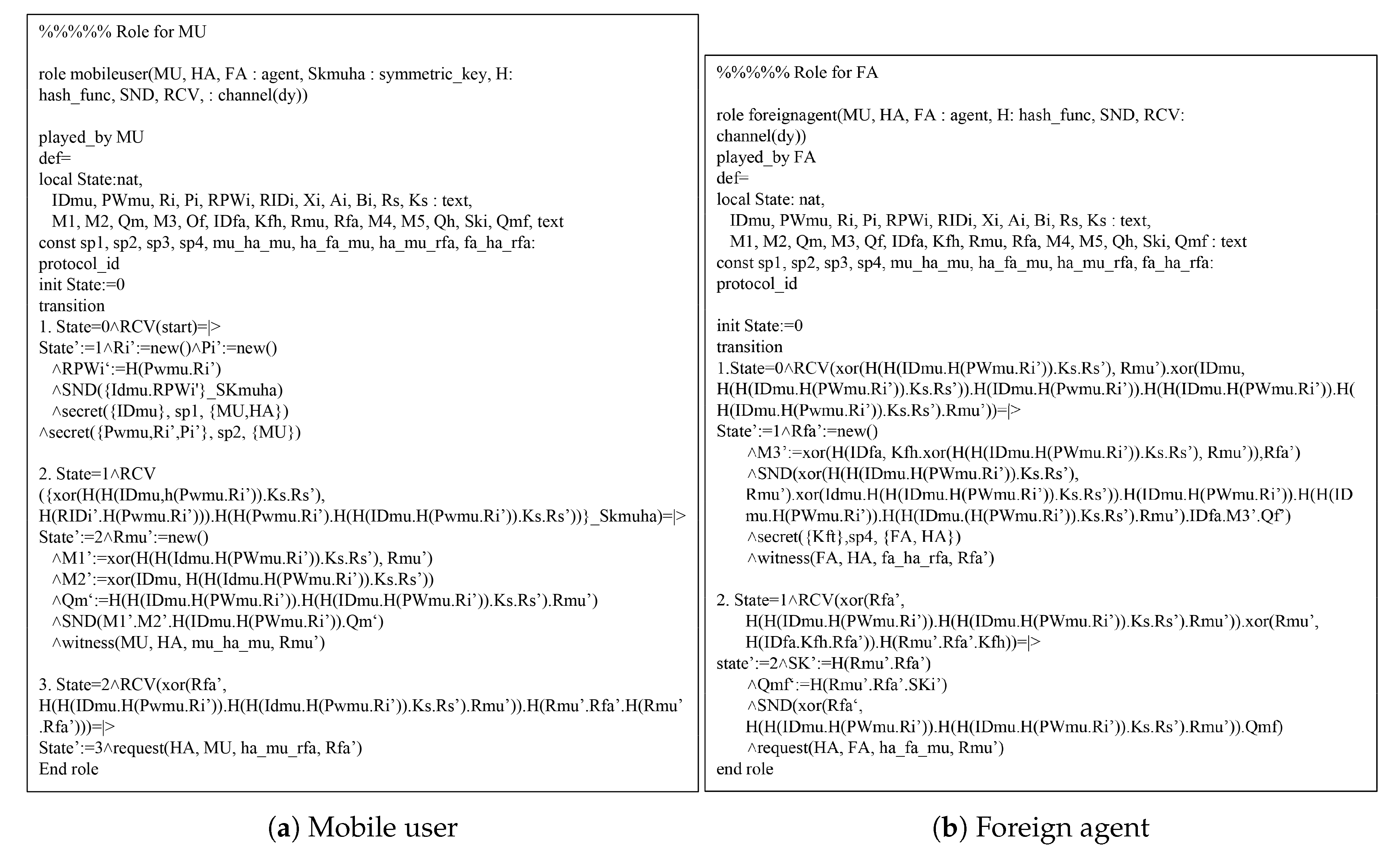
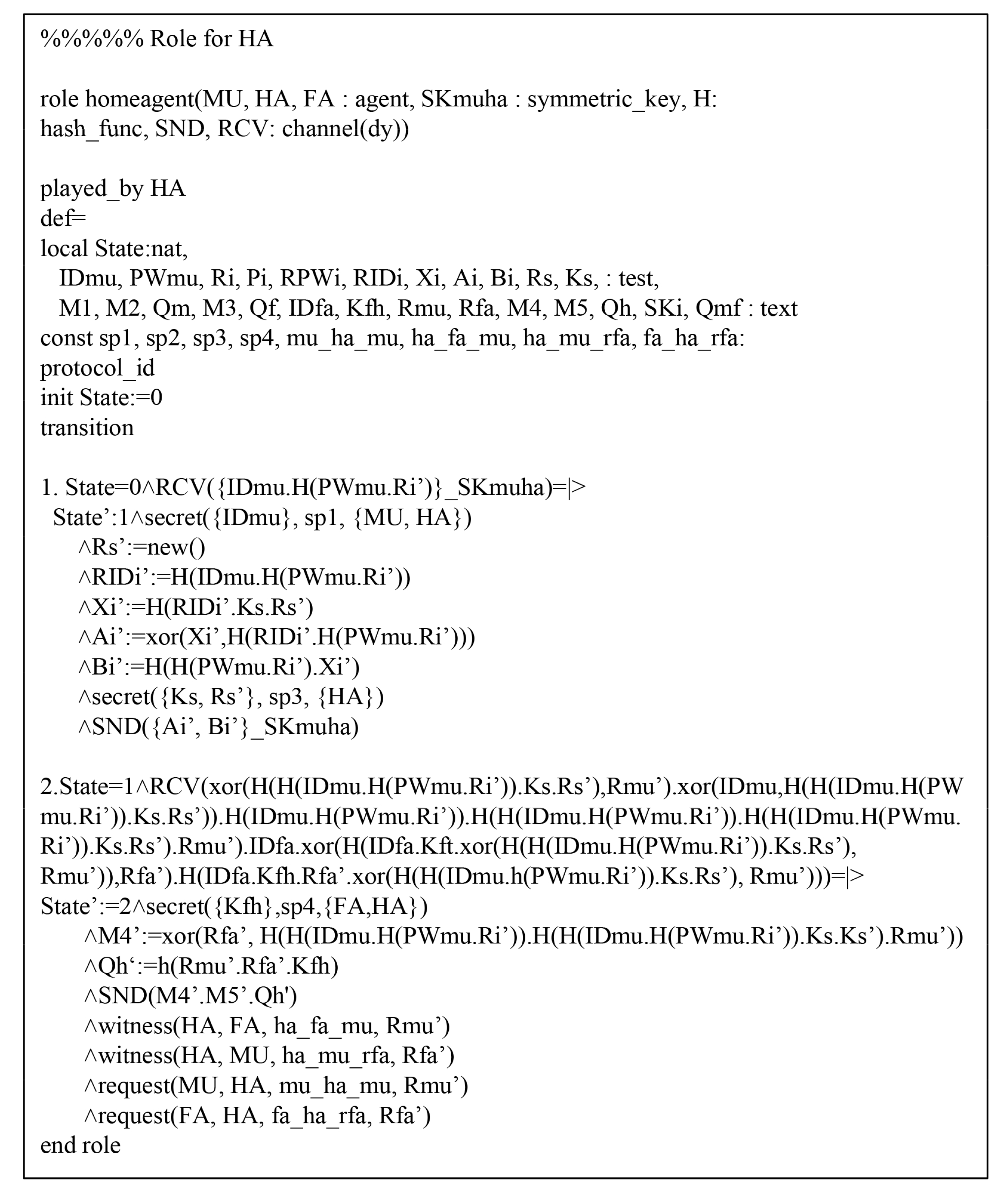
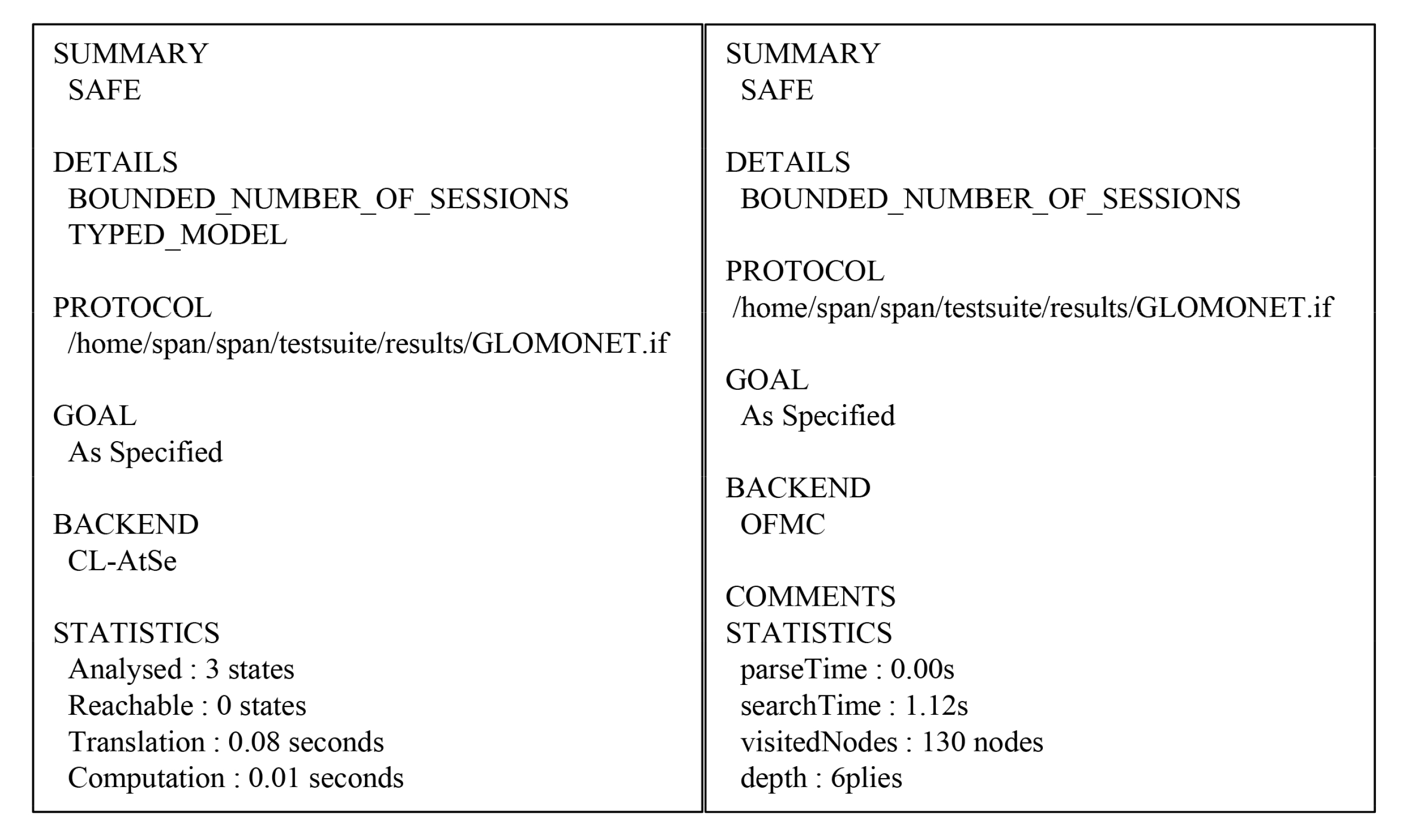
Section 7, we report a formal security validation utilizing the Automated Validation of Internet Security Protocols and Applications (AVISPA) simulation tool. In
Section 8, we compare the performance properties of our protocol to existing protocols. We present our conclusions in the final
Section 9.
3. Review of Madhusudhan et al.’s Protocol
Madhusudhan et al.’s scheme [
16] is comprised of three processes: (1) user registration, (2) authentication, and (3) password update. The notations utilized in this paper are defined in
Table 2 and each process is detailed as follows.
3.1. Initialization Process
The home agent () selects two prime numbers and generator g of a finite field in , of which is a nonsingular elliptic curve (mod p). The calculates and . Then, the chooses an integer e, such that and . After that, the computes the value of an integer d, such that , where d is the secret key of the , and mod n, where y is the public key of the . The keeps securely.
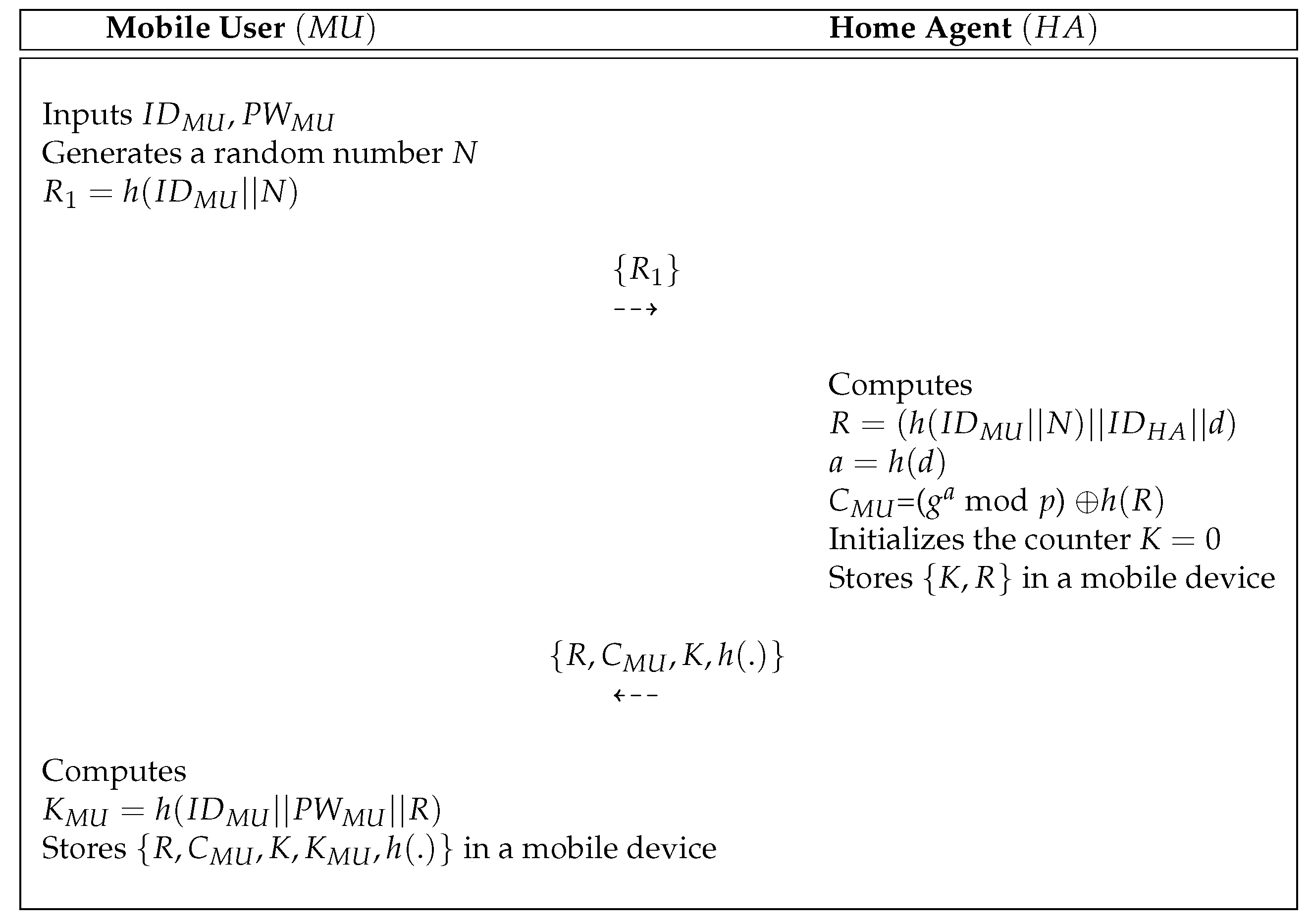
3.2. Registration Process
In Madhusudhan et al.’s protocol, a new
who requests roaming services must register their identity with the
.
Figure 1 indicates the user registration process of Madhusudhan et al.’s protocol [
16] and this process is described in detail as follows.
- Step 1:
A mobile user inputs and selects a random number N. Then, computes and sends a request message to the via a public channel.
- Step 2:
After obtaining messages , the calculates , and = ( mod p) . After that, sets the value of the counter and stores in a secure database. Then, sends to over a secure channel.
- Step 3:
After obtaining messages , the computes and stores it in a mobile device. Finally, the mobile device of the contains .
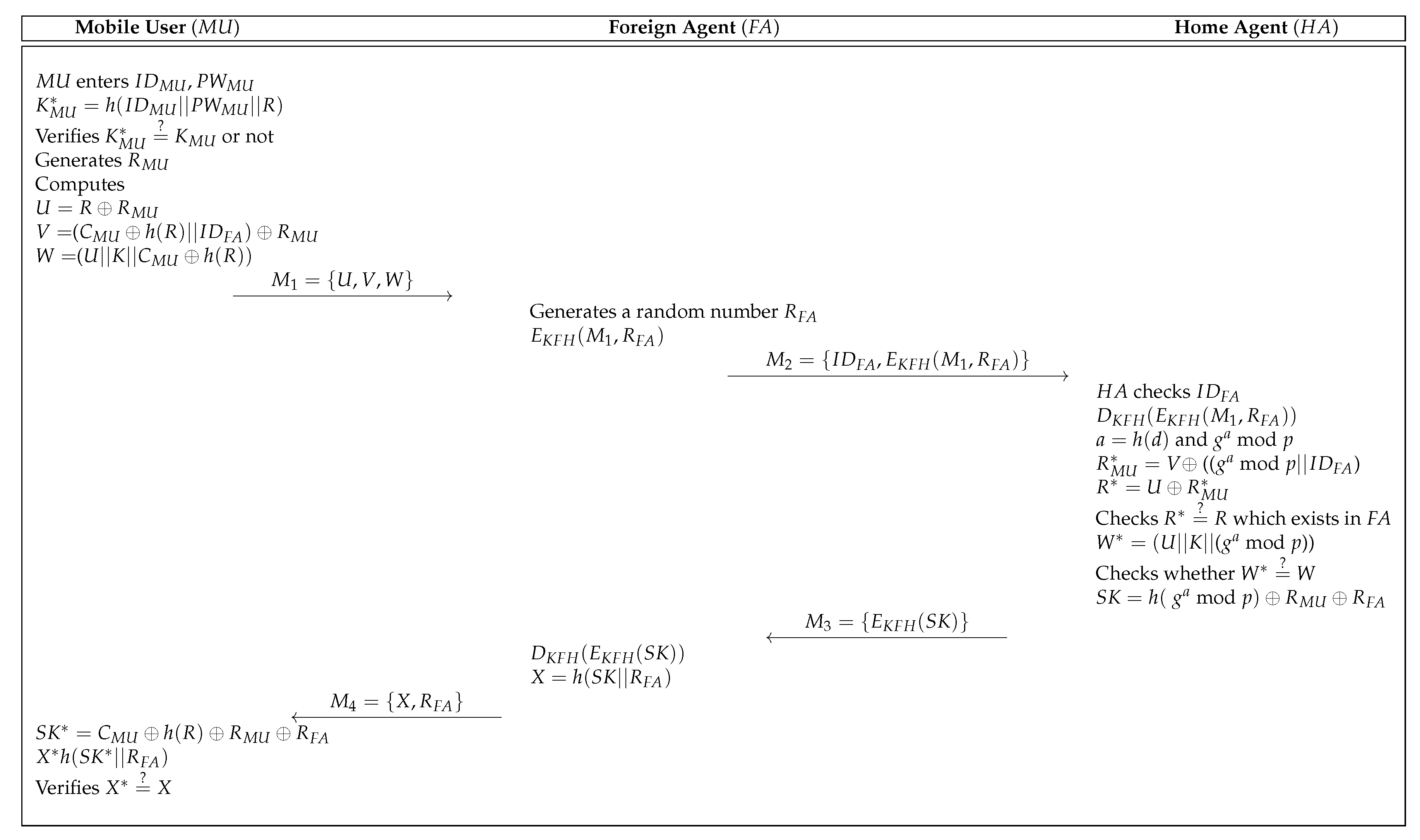
3.3. Login and Authentication Process
In Madhusudhan et al.’s protocol [
16], they considered a scenario in which the
associated with the
visits a foreign network from the foreign agent
and attempts to access the roaming service. A
who requests roaming service must send a login request message to the
. The
,
, and
then perform mutual authentication with each other, then
and
share the session key.
Figure 2 indicates the login and authentication process of Madhusudhan et al.’s protocol [
16]. The process is described in detail as follows.
- Step 1:
The retrieves the authentication data stored in the mobile device and enters and . After that, the mobile device computes and checks whether . If this condition holds, the generates a random number and computes , and . Then, sends the login request message to through an insecure channel.
- Step 2:
After obtaining the , selects a random number and encrypts and using the shared secret key. The sends the to the .
- Step 3:
Upon reception of , the checks the identity of and retrieves the secret key corresponding to . After that, the decrypts and computes , mod p, (( mod p)) and . The then checks whether there exists in a secure database. If the condition is valid, the computes =(( mod p)) and checks whether . If it is correct, the computes = mod and sends to the .
- Step 4:
After obtaining the , the decrypts and computes . Finally, the sends to the .
- Step 5:
Upon reception of , the computes and . After that, the checks whether . If this holds, the and achieve the successfully.
3.4. Password Update Process
In Madhusudhan et al.’s protocol, the can freely update their password. The process is described in detail as follows.
- Step 1:
When a legitimate wants to update the password, the inputs and the request messages are transmitted via a terminal.
- Step 2:
The mobile device of calculates and checks whether . If this holds, the is legitimate user. Otherwise, the mobile device terminates the password change process.
- Step 3:
The selects new password and computes . Finally, the mobile device of replaces with .
6. Security Analysis
We utilized the BAN logic to evaluate the user authentication of our protocol and then we used the ROR model to prove the session key security. In addition, we performed AVISPA simulation to evaluate the security of our protocol to replay and MITM attacks.
6.1. Informal Security Analysis
This section presents an informal security analysis to evaluate the security of the proposed protocol. We proved that our scheme can prevent various attacks and allow user authentication and anonymity.
6.1.1. Masquerade Attack
If a attempts to impersonate a legal mobile user, must calculate a request message and response message successfully. However, cannot compute this because does not know ’s real identity , password , secret parameters , random nonce , and biometrics . Consequently, the proposed protocol can withstand masquerade attacks because cannot generate correct messages successfully.
6.1.2. Replay Attack
Our protocol can resist replay attacks utilizing random nonce that is changed every session. If a may try to impersonate a mobile user by resending messages that were exchanged in a previous session, cannot obtain the previous messages because the checks whether and . Consequently, the proposed protocol can withstand replay attacks because does not know and .
6.1.3. Stolen Mobile Device Attack
We assume that a
can steal the mobile device of a legitimate user and extract the data
from the mobile device by utilizing a power analysis attack [
20]. However,
still cannot obtain a legitimate user’s information because the parameters stored in the mobile device are masked using bitwise XOR operations and hash functions. Thus, the proposed scheme can defend against mobile device theft attacks.
6.1.4. Session Key Disclosure Attack
In our protocol, a cannot compute because a legitimate mobile user generates an authentication request message by using the dynamic random nonce and secret parameter . Consequently, the proposed protocol protects against session key disclosure attacks.
6.1.5. Anonymity
In our protocol, a cannot obtain the identity of a legitimate mobile user because the parameters are masked by using XOR operations and hash functions, such as and . Consequently, our protocol provides anonymity because a cannot obtain without and .
6.1.6. Mutual Authentication
After obtaining the login request messages from , the checks whether . If this holds, authenticates . After obtaining the messages from , the checks whether . If it is valid, authenticates . After obtaining the messages from , checks whether . If this holds, authenticates . Finally, checks whether . If this holds, authenticates . Consequently, our protocol ensures secure mutual authentication among , and because a does not know the secret parameter of and .
6.1.7. User Friendliness
In our protocol, can easily change his/her own and without the assistance of the . In particular, the proposed protocol allows the to change the original password in a short time. Because, the need not go through the entire login process, which saves the time as well as minimizes the computation complexity of the proposed scheme. Consequently, the proposed protocol is user-friendly.
6.2. Security Properties
Table 3 presents the better security properties ensured by the proposed scheme compared to related schemes [
6,
8,
15,
16]. The existing schemes are insecure various attacks and their scheme cannot ensure mutual authentication and user anonymity. In contrast, the proposed scheme can provide essential security properties and can achieve user anonymity and mutual authentication.
6.3. Authentication Proof Using BAN Logic
We present the security analysis utilizing the BAN logic [
25] to prove the secure user authentication of our protocol. In
Table 4, we present the notations used for BAN logic. We present the security rules, the security goals, the idealized forms and the assumptions that are essential to BAN logic. We assessed that our scheme ensured mutual authentication among
,
, and
.
6.3.1. Rules of BAN Logic
The rules of BAN logic are summarized as follows.
- 1.
- 2.
- 3.
- 4.
- 5.
.
6.3.2. Goals
To analyze mutual authentication, we define the goals of our protocol as below.
- Goal 1:
- Goal 2:
- Goal 3:
- Goal 4:
.
6.3.3. Idealized Forms
The idealized form of messages of our protocol are as below.
- :
:
- :
:
- :
:
- :
: .
6.3.4. Assumptions
The following assumptions are applied in the BAN logic analysis.
- :
- :
- :
- :
- :
- :
- :
- :
- :
- :
.
6.3.5. Proof Using BAN Logic
The proof then proceeds as below:
- Step 1:
According to
, we obtain the following
- Step 2:
Utilizing
and
with the “message meaning rule”, the following is obtained
- Step 3:
Now, using
and
with the “freshness rule”, the following is obtained
- Step 4:
Utilizing
and
with the “nonce verification rule”, we obtain
- Step 5:
Utilizing
and the “belief rule”, we obtain
- Step 6:
According to
, we obtain
- Step 7:
Utilizing the
and
with the “message meaning rule”, the following is obtained
- Step 8:
Now, using
and
with the “freshness rule”, we obtain
- Step 9:
Utilizing
and
with the “nonce verification rule”, the following is obtained
- Step 10:
According to
, we obtain
- Step 11:
Utilizing
and
with the “message meaning rule”, the following is obtained
- Step 12:
Now, using
and
with the “freshness rule”, we obtain
- Step 13:
Utilizing
and
with the “nonce verification rule”, the following is obtained
- Step 14:
According to
, we could obtain
- Step 15:
Utilizing
and
with the “message meaning rule”, we obtain
- Step 16:
Now, using
and
with the “freshness rule”, the following is obtained
- Step 17:
Utilizing
and
with the “nonce verification”, we obtain
- Step 18:
Utilizing
and the belief rule, we obtain
- Step 19:
Now, using
and
with the “jurisdiction rule”, the following is obtained
- Step 20:
Because of
, from the
,
,
and
we obtain
- Step 21:
Utilizing
and
with the “jurisdiction rule”, we obtain
Based on goals 1 to 4, we proved that , , and are securely mutually authenticated. We assessed that the proposed scheme ensured mutual authentication between , , and .
6.4. ROR Model Analysis
To evaluate the session key (SK) security of the protocol from the malicious adversary
, the proposed protocol performs the ROR model [
26], which is a widely known formal security analysis. We first introduce the ROR model before doing a SK security proof for the proposed protocol.
Participants: There are three participants: the mobile user , the foreign agent , and the home agent are instances of the , of the , and of the , respectively.
Partnering: The instances and are partners if they satisfy the following conditions: (1) and are in the accept state, (2) and authenticate each other mutually sharing the same , and (3) and are mutually authenticated.
Freshness: If the does not obtain the SK between and by utilizing the reveal query , the instance or is considered fresh.
Adversary: In the ROR model, the can eavesdrop, modify, delete, or insert the exchanged messages during the communication. Furthermore, the will have the access to the following queries.
: It denotes that performs the eavesdropping attack by eavesdropping exchanged messages between , , and over wireless communication.
: It is modeled from the mobile device lost/stolen attack, in which the is able to extract the secret data in the mobile device.
: In this query, the can dispatch a message M to the instance and can also reply accordingly.
: It corresponds to the semantic security of the
between
and
following the indistinguishability style in the ROR model [
26]. In this query, before the experiment starts, an unbiased coin
c is tossed. If the
executes
query and the established
is fresh, then
returns
for the case when
or a random value when
. On the other cases, it returns a null value (⊥).
: With this query, the can reveal the created by its partner to in the current session.
Semantic security of the session key: In this formal security model, the malicious adversary
must distinguish between an instance’s actual
and a random secret key. The
can perform
queries to either
or
, and its output is checked for consistency against the random bit c. If the condition
is valid, the
wins the game. Otherwise, the
loses the game. Let
denote an event that is
winning the game. Therefore, the advantage of
in breaking the semantic security of our protocol
P is shown in Equation (
1). The proposed protocol
P is secure relative to the ROR model when
, for any sufficiently small
.
Random oracle: In this paper, all the participants and the malicious adversary can access a collision-resistant one-way hash function . We model as a random oracle, say .
Security Proof
We utilized Zipf’s law [
27] to assess the SK security of our protocol and the detailed theorems are given as follows:
Theorem 1. If denotes the advantage function of the in violating SK security of our protocol. Then, we obtain the following.where , , and are the number of queries, the number of queries, and the range space of the hash function , respectively; is the number of bits present in the ’s biometric secret key ; and s and C are the Zipf’s parameters [27]. Proof. We follow the proof as presented in [
28,
29]. A sequence of five games denoted by
, where
, are defined to demonstrate the SK security of our protocol.
denotes the probability of
winning the game
. Each game is described in detail as follows.
Game: This game is considered as an actual attack by the
for the proposed protocol
P. Since the bit
c is guessed at the beginning of
. According to this game, we obtain the following:
Game: This game is modeled so that the
performs an eavesdropping attack in which the exchanged messages
,
,
, and
are intercepted during the authentication phase using the
query. Then,
performs the
query to check whether it is the real SK or a random number. In the proposed protocol, the
is calculated as
. To derive
, the
needs secret credentials, such as
,
, and
. Consequently, the
’s probability in winning
by eavesdropping on the exchanged messages does not increase. We can obtain
Game: The difference between
and
is that the
and
queries are included in
. This game can be considered as an active attack in which the
may try to fool a legitimate entity to accept the exchanged messages modified by the
. All exchanged messages are protected by using the collision-resistant one-way hash function
. All exchanged messages are constructed using the random credentials
,
, and
. All exchanged messages are constructed using the random credentials
,
, and
and these messages are protected by using the collision-resistant one-way hash function
. Using birthday paradox, we can obtain the following result:
Game: In the final game, the
query is modeled. In this case, a
can extract the secret parameters
from a mobile device’s memory utilizing the power-analysis attack. Here,
,
and
. It is computationally infeasible for
to derive the real identity
and password
of
correctly via the
query without
’s master key
and secret parameter
. The probability of guessing the biometric key
of
bits by the
is approximately
. Consequently, the
and
are indistinguishable if password/biometrics guessing attacks are not implemented. Therefore, utilizing Zipf’s law [
27], we can obtain the following result:
As all the games are executed, the
must guess the exact bit
c. Thus, we can obtain the following result:
With Equations (1), (2), and (5), we can obtain the result as below:
Using Equations (4)–(6), we can obtain the following result, which uses the triangular inequality.
Finally, multiplying both sides of Equation (
7) by a factor of two, we can obtain the result as belows:
□
9. Conclusions
In this paper, we assessed that Madhusudhan et al.’s authentication scheme did not prevent various attacks. Furthermore, we assessed that their protocol could not achieve user authentication. We proposed a secure and efficient three-factor authentication protocol for roaming services in GLOMONET to improve the security flaws of Madhusudhan et al.’s scheme. Our scheme was able to resist various attacks, such as masquerade, replay, session key disclosure, and mobile device theft attacks and could ensure anonymity and user authentication. We demonstrated that our scheme achieved secure mutual authentication among the mobile user, the foreign agent, and the home agent by performing BAN logic analysis.
Furthermore, we assessed a formal security validation analysis of our protocol utilizing the ROR model and AVISPA simulation. We compared the computation costs and security features with existing schemes. The three-factor based proposed scheme provided a great improvement in terms of the security level compared with two-factor based existing schemes and also preserved the low computation cost. The principal merit of the proposed scheme was resistance against potential attacks in GLOMONET. Therefore, the proposed scheme satisfies the security requirements for roaming service and is suitable for practical mobile environments.