A Systemic Review of the Cybersecurity Challenges in Australian Water Infrastructure Management
Abstract
:1. Introduction
2. Methodology
- RQ1: What are the current cybersecurity threats and control systems in the water sector of Australia?
- RQ2: How do the cybersecurity management systems of the water sector in Australia compare to other countries?
- RQ3: What are the existing research developments around cybersecurity management for water infrastructure?
- RQ3.1: How did the number of publications change over the years?
- RQ3.2: What is the geographic distribution of these studies (across countries)?
- RQ3.3: What is the distribution of the relevant research authority (academic, governmental, and industry) in this study area?
- RQ3.4: What are the most globally cited research studies in this area?
- RQ3.5: What are the target venues for publishing these studies?
- RQ3.6: What are the limitations of the existing studies and the directions for future research?
- RQ3.7: What objective functions and evaluation metrics have the existing studies applied to deal with cybersecurity issues in water infrastructure?
3. Results
3.1. Cybersecurity Challenges for Water Infrastructure in Australia
- Remote terminal unit (RTU): The RTU is a wireless telemetry unit specially constructed to maintain distant SCADA stations. RTUs are field instruments often set with radio interconnections to assist isolated places where wire-based connections are absent.
- Programmable logic controller (PLC): The PLC is a small processor constructed to accomplish logical operations through the use of electric hardware (switches, transmitters, and timers). PLCs are involved in managing complex procedures in DCS and SCADA systems.
3.2. Common Cybersecurity Vulnerabilities and Threats in Water Infrastructure Systems
- Always being logged-in to the operator station, even in the absence of an operator at the workstation, limiting the authentication activity;
- It is easy to get access to the security equipment;
- There is insecure access to the security network from distant or isolated locations through dial-up modem lines or digital subscriber lines (DSLs);
- Direct or indirect exposure to the Internet system makes the security networks more vulnerable;
- The absence of a firewall or weak or unverified firewall configurations;
- Unsupervised system event logs;
- The absence of intrusion detection systems;
- The absence of routinely maintained operating and security system software;
- Insecure network and router configurations [31].
3.3. Australian Cybersecurity Management Initiatives and Standards for Water Infrastructure
- Prepare a risk management plan regarding the terrorist act;
- Conduct an audit on this plan on an annual basis;
- Check the plan annually and prepare a crisis simulation exercise.

- Detect key exposures within ICT systems and assess the ability of the systems to withstand exploitation;
- Analyse the safety implications of strategic changes to the infrastructure;
- Evaluate the related physical and personnel safety issues.
- Coordinating GovCERT with foreign governments regarding cybersecurity issues in Australia’s critical infrastructure systems, such as its water infrastructure;
- Incorporating the Australian government’s policies with the private sector’s policies for securing and overcoming cyber-based attacks;
- Providing cash grants to private sector organisations to carry out safety assessments of their systems and networks.
3.4. Overseas Cybersecurity Management Standards for Water Infrastructure
3.5. Existing Research Developments around Cybersecurity Management for Water Infrastructure
3.6. Objective Functions and Evaluation Metrics for Measuring Cybersecurity in Water Infrastructure
4. Discussion
5. Conclusions
- Water infrastructure systems in Australia are frequently facing cyber-attacks due to their complex nature;
- Many attacks remain undetected or unreported, or else undisclosed to safeguard consumers’ trust and the service providers’ reputations;
- Although the Australian government is taking different initiatives (policies or strategies and financial aid) at the federal, state, and local levels to collaborate with the public and private sectors to protect Australia’s critical water infrastructure, there are still some significant gaps in addressing cyber risks and implementing adequate security controls;
- There is an urgent need for expert training and human resource development for individuals who are capable of constantly assessing the system’s security and identifying threats in the commercial network infrastructure, as well as in the SCADA systems used in the water infrastructure.
Supplementary Materials
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Williams, A. Beyond 2000: The Rise of Australian Cyber Warfare Capability. In Proceedings of the International Conference on Cyber Warfare and Security, Towson, MD, USA, 9–10 March 2020; Academic Conferences International Limited: Manchester, UK, 2020; p. 549-XVIII. Available online: https://www.proquest.com/docview/2455894288?pq-origsite=gscholar&fromopenview=true (accessed on 23 October 2022).
- Shamir, U.; Salomons, E. Optimal Real-Time Operation of Urban Water Distribution Systems Using Reduced Models. J. Water Resour. Plan. Manag. 2008, 134, 181–185. [Google Scholar] [CrossRef] [Green Version]
- Addeen, H.H.; Xiao, Y.; Li, J.; Guizani, M. A survey of cyber-physical attacks and detection methods in smart water distribution systems. IEEE Access 2021, 9, 99905–99921. [Google Scholar] [CrossRef]
- Gleick, P.H. Water and terrorism. Water Policy 2006, 8, 481–503. [Google Scholar] [CrossRef] [Green Version]
- Mutchek, M.; Williams, E. Moving towards sustainable and resilient smart water grids. Challenges 2014, 5, 123–137. [Google Scholar] [CrossRef] [Green Version]
- Gonzalez-Vidal, A.; Cuenca-Jara, J.; Skarmeta, A.F. IoT for water management: Towards intelligent anomaly detection. In Proceedings of the 2019 IEEE 5th World Forum on Internet of Things (WF-IoT), Limerick, Ireland, 15–18 April 2019; pp. 858–863. [Google Scholar]
- Hopman, V.; Kruiver, P.; Koelewijn, A.; Peters, T. How to create a smart levee. In Proceedings of the 8th International Symposium on Field Measurements in GeoMechanics 2010, Berlin, Germany, 12–16 September 2011. [Google Scholar]
- Li, J.; Yang, X.; Sitzenfrei, R. Rethinking the framework of smart water system: A review. Water 2020, 12, 412. [Google Scholar] [CrossRef] [Green Version]
- Priya, S.K.S.G.; Revathi, T. Design of smart sensors for real time drinking water quality monitoring and contamination detection in water distributed mains. Int. J. Eng. Technol. 2018, 7, 47–51. [Google Scholar] [CrossRef] [Green Version]
- Skiba, R. Water Industry Cyber Security Human Resources and Training Needs. Int. J. Eng. Manag. 2020, 4, 11–16. [Google Scholar] [CrossRef]
- Sun, B.; Ahmed, F.; Sun, F.; Qian, Q.; Xiao, Y. Water quality monitoring using STORM 3 data loggers and a wireless sensor network. Int. J. Sens. Netw. 2016, 20, 26–36. [Google Scholar] [CrossRef]
- Gleick, P.H. The water conflict chronology. In The World’s Water 2004–2005: The Biennial Report on Freshwater Resources; Gleick, P.H., Ed.; Island Press: Covelo, CA, USA, 2004; pp. 234–255. [Google Scholar]
- Presidential Decision Directive: Critical Infrastructure Security and Resilience; Technical Report PPD-21; The White House: Washington, DC, USA, 2013.
- White House. Presidential Executive Order on Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure; Technical Report; 2017. Available online: https://trumpwhitehouse.archives.gov/presidential-actions/presidential-executive-order-strengthening-cybersecurity-federal-networks-critical-infrastructure/ (accessed on 23 October 2022).
- ICS-CERT. NCCIC/ICS-CERT Year in Review: FY 2015; U.S. Department of Homeland Security Industrial Control Systems-Cyber Emergency Response Team: Washington, DC, USA, 2016. [Google Scholar]
- Hassanzadeh, A.; Rasekh, A.; Galelli, S.; Aghashahi, M.; Taormina, R.; Ostfeld, A.; Banks, K. A review of cybersecurity incidents in the water sector. arXiv 2020, arXiv:2001.11144v2. [Google Scholar] [CrossRef] [Green Version]
- Cava, M.D. Uber to Pay $148 Million over Undisclosed Data Breach that Ex-CEO Paid Hackers to Keep Quiet. USA Today. 2018. Available online: https://www.usatoday.com/story/tech/news/2018/09/26/uber-pay148-million-over-undisclosed-data-breach-ex-ceo-paid-hackers-keepquiet/1432335002. (accessed on 15 August 2019).
- Rubin, G.T. Many Company Hacks Go Undisclosed to SEC Despite Regulator Efforts. The Wall Street Journal. 2019. Available online: https://www.wsj.com/articles/many-company-hacks-go-undisclosedto-sec-despite-regulator-efforts-11551218919 (accessed on 15 October 2022).
- Walton, B. Water Sector Prepares for Cyberattacks. Circle of Blue. 2016. Available online: https://www.circleofblue.org/2016/world/water-sector-preparescyberattacks (accessed on 11 October 2022).
- Australian Government. Strong and Secure: A strategy for Australia’s National Security; Department of Prime Minster and Cabinet: Barton, Australia, 2013.
- Slay, J.; Miller, M. Lessons learned from the Marchoory Water Breach. In Critical Infrastructure Protection; Springer: Boston, MA, USA, 2008; pp. 73–82. [Google Scholar]
- Lehto, M.; Neittaanmäki, P. (Eds.) Cyber Security: Analytics, Technology and Automation; Springer: London, UK, 2015; Volume 78, p. 258. [Google Scholar]
- Saha, H.N.; Auddy, S.; Chatterjee, A.; Pal, S.; Sarkar, S.; Singh, R.; Singh, A.K.; Sharan, P.; Banerjee, S.; Sarkar, R.; et al. IoT solutions for smart cities. In Proceedings of the 2017 8th Annual Industrial Automation and Electromechanical Engineering Conference (IEMECON), Institute of Electrical and Electronics Engineers (IEEE), Bangkok, Thailand, 16–18 August 2017; pp. 74–80. [Google Scholar]
- Taormina, R.; Galelli, S.; Tippenhauer, N.O.; Salomons, E.; Ostfeld, A. Characterizing cyber-physical attacks on water distribution systems. J. Water Resour. Plan. Manag. 2017, 143, 04017009. [Google Scholar] [CrossRef]
- Moher, D.; Liberati, A.; Tetzlaff, J.; Altman, D.; The PRISMA Group. Preferred Reporting Items for Systematic Reviews and Meta-Analyses: The PRISMA Statement. BMJ 2009, 339, b2535. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Tuptuk, N.; Hazell, P.; Watson, J.; Hailes, S. A systematic review of the state of cyber-security in water systems. Water 2021, 13, 81. [Google Scholar] [CrossRef]
- Richards, K. Australian Business Assessment of Computer User Security; Australian Institute of Criminology: Canberra City, Australia, 2009; ISBN 9781921532351. [Google Scholar]
- Krutz, R. Securing SCADA Systems; Wiley: Indianapolis, IN, USA, 2006. [Google Scholar]
- Stouffer, K.; Falco, J.; Scarfone, K. Guide to Industrial Control Systems (ICS) Security: Supervisory Control and Data Acquisition (SCADA) Systems, Distributed Control Systems (DCS), and Other Control System Configurations Such as Programmable Logic Controllers (PLC); NIST Special Publication; National Institute of Standards and Technology (NIST), U.S. Department of Commerce: Washington, DC, USA, 2015.
- Shea, D. Critical Infrastructure: Control Systems and the Terrorist Threat. Congressional Research Services. 2003. Available online: http://www.fas.org/irp/crs/RL31534.pdf (accessed on 1 June 2008).
- Beggs, C. A holistic SCADA security standard for the Australian context. In Proceedings of the 9th Australian Information Warfare and Security Conference, Perth, Australia, 5–7 December 2008. [Google Scholar]
- Khadidos, A.O.; Khadidos, A.O.; Manoharan, H.; Alyoubi, K.H.; Alshareef, A.M.; Selvarajan, S. Integrating Industrial Appliances for Security Enhancement in Data Point Using SCADA Networks with Learning Algorithm. Int. Trans. Electr. Energy Syst. 2022, 2022, 8685235. [Google Scholar] [CrossRef]
- Pollet, J. Developing a Solid SCADA Security Strategy. In Proceedings of the 2nd ISA/IEEE Sensors for Industry Conference, Houston, TX, USA, 19–21 November 2002; pp. 148–156. [Google Scholar]
- Mays, L. Water Supply System Security; McGraw-Hill: New York, NY, USA, 2004. [Google Scholar]
- Fink, R.; Spencer, D.; Wells, R. Lessons Learned from Cyber Security Assessments of SCADA and Energy Management Systems Control; Office of Electricity Delivery and Energy Reliability, U.S. Department of Energy: Washington, DC, USA, 2006.
- Schneider, A. Parliamentary Joint Committee on the Australian Crime Commission-Inquiry into Cybercrime. Attorneys General Department; 2003. Available online: URL http://www.aph.gov.au/Senate/committee/acc_ctte/cybercrime/submissions/sub21.doc (accessed on 24 August 2008).
- TISN. Australia’s Critical Infrastructure Protection Arrangements. Australian Govt; 2007. Available online: http://www.tisn.gov.au/agd/WWW/rwpattach.nsf/VAP/(930C12A9101F61D43493D44C70E84EAA)~TISN+diagram+v.2+Dec+07.pdf/$file/TISN+diagram+v.2+Dec+07.pdf (accessed on 24 August 2008).
- Victorian Government. Terrorism (Community Protection) Act 2003; Parliament of Victoria: Melbourne, Australia, 2003.
- TISN. Diagram of the TISN. Trusted Information Sharing Network (TISN); 2012. Available online: http://www.tisn.gov.au/Pages/the_tisn.aspx. (accessed on 16 June 2012).
- TISN. CIP Newsletter. Volume 3, March 2006. Available online: http://www.tisn.gov.au/agd/WWW/rwpattach.nsf/VAP/(930C12A9101F61D43493D44C70E84EAA)~Newsletter+March+06.pdf/$file/Newsletter+March+06.pdf (accessed on 10 September 2008).
- NIST. Framework for Improving Critical Infrastructure Cybersecurity; Technical Report; NIST: Gaithersburg, MD, USA, 2017. [Google Scholar]
- NISCC Good Practice Guide on Firewall Deployment for SCADA and Process Control Networks. Available online: http://www.niscc.gov.uk/niscc/scada-en.html (accessed on 15 October 2022).
- Australian Cyber Security Centre. ACSC Annual Cyber Threat Report. September 2020. Available online: https://www.cyber.gov.au/sites/default/files/2020-09/ACSC-Annual-CyberThreat-Report2019-20.pdf (accessed on 10 October 2022).
- Sun, N.; Zhang, J.; Rimba, P.; Gao, S.; Xiang, Y.; Zhang, L.Y. Data-driven cybersecurity incident prediction: A survey. IEEE Commun. Surv. Tuts. 2018, 21, 1744–1772. [Google Scholar] [CrossRef]
- Fielding, K.S.; Spinks, A.; Russell, S.; McCrea, R.; Stewart, R.; Gardner, J. An experimental test of voluntary strategies to promote urban water demand management. J. Environ. Manag. 2013, 114, 343–351. [Google Scholar] [CrossRef]
- Stewart, R.A.; Willis, R.; Giurco, D.; Panuwatwanich, K.; Capati, G. Web-based knowledge management system: Linking smart metering to the future of urban water planning. Aust. Plan. 2010, 47, 66–74. [Google Scholar] [CrossRef] [Green Version]
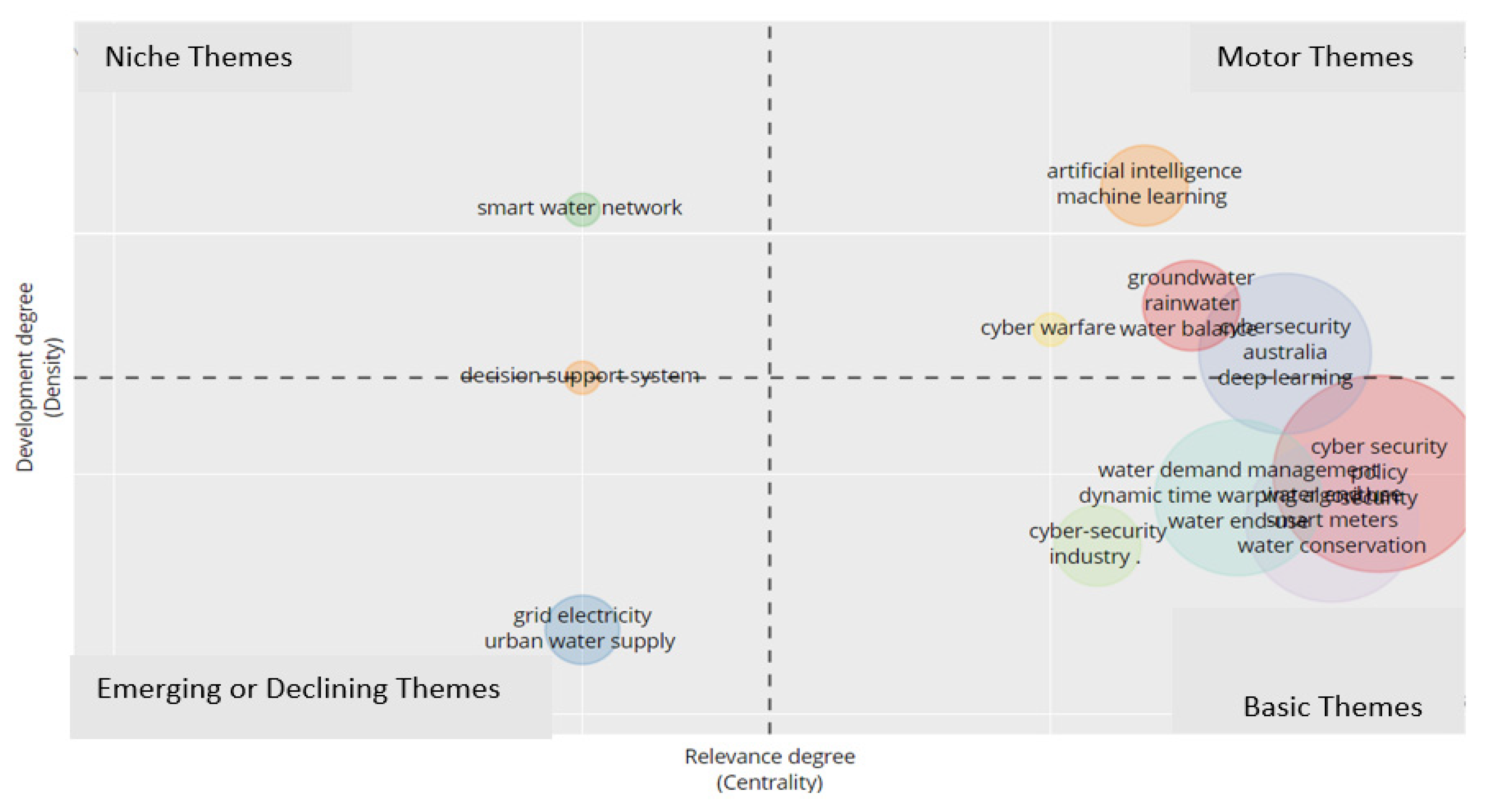
- Cobo, M.J.; López-Herrera, A.G.; Herrera-Viedma, E.; Herrera, F. An approach for detecting, quantifying, and svisualising the evolution of a research field: A practical application to the Fuzzy Sets Theory field. J. Informetr. 2011, 5, 146–166. [Google Scholar] [CrossRef]
- Cobo, M.J.; López-Herrera, A.G.; Herrera-Viedma, E.; Herrera, F. Science mapping software tools: Review, analysis, and cooperative study among tools. J. Am. Soc. Inf. Sci. Technol. 2011, 62, 1382–1402. [Google Scholar] [CrossRef]
- Germano, J.H. Cybersecurity Risk & Responsibility in the Water Sector; AWWA: Denver, CO, USA, 2018. [Google Scholar]
- American Water Works Association. 2019 AWWA State of the Water Industry Report. 2019. Available online: https://www.awwa.org/Portals/0/AWWA/ETS/Resources/2019_STATE%20OF%20THE%20WATER%20INDUSTRY_post.pdf (accessed on 15 October 2022).
- Victorian Auditor-General’s Office. Security of Water Infrastructure Control Systems; Victorian Government Printer: Melbourne, Australia, 2019.





| Category | Description |
|---|---|
| Unencrypted (Clear Text) Communications | Unencrypted communications are usually seen in network traffic, which allows a correctly positioned attacker to see a legal user’s network traffic, record and observe their communications, and uncover any information the legal user supplies. Additionally, an attacker is able to change the traffic and can use the application as a platform for attacks. |
| Account Management | Users’ accounts that uses easily predicted usernames and passwords; sometimes, attackers can code some tough usernames and passwords that have been defined in records or extracted from binary systems or arrangement files. Additionally, the policies related to password protection are weak. |
| Weak or No Authentication | Little authentication or the absence of authentication of communication between hosts increases susceptibility to cyber-attacks. |
| Coding Practices | Dismantling or re-arranging of existing code that causes malicious input of data because of potentially insecure coding styles (specifically due to loop control and buffer management). |
| Unused Services | Services with ordinary susceptibilities were running in the hosts’ system; the need for maintenance was not recommended in the default system. |
| Network Addressing | Network address protocols (DNS, etc.) were vulnerable to scamming or other circumvention systems. |
| Scripting and Interface Programming | Archive and other records (Perl, etc.) could be manipulated with malevolent insert or other methods. |
| Unpatched Components | Old software modules that contained known available vulnerabilities required by the configuration. |
| Web Servers and Clients | Faulty configured web servers may allow directory traversal or file alteration issues. |
| Boundary Protection | Misconfigured access control lists may happen from links originating from outside the SCADA boundary; the firewalls contained excess open ports. |
| Enumeration | Attackers may use the available information revealed from web servers and other networks services. |
| Description | Results | Description | Results |
|---|---|---|---|
| Main Information | Document Contents | ||
| Timespan | 2003–2023 | Keywords Plus (ID) | 2001 |
| Sources (Journals, Books, etc.) | 210 | Author’s Keywords (DE) | 886 |
| Documents | 271 | Authors | |
| Average years from publication | 3.91 | Authors | 916 |
| Average citations per documents | 16.3 | Author Appearances | 1037 |
| Average citations per year per doc | 3.077 | Authors of single-authored documents | 29 |
| References | 10,126 | Authors of multi-authored documents | 887 |
| Document Types | Author Collaborations | ||
| article | 99 | Single-authored documents | 31 |
| book | 2 | Documents per Author | 0.296 |
| book chapter | 29 | Authors per Document | 3.38 |
| conference paper | 128 | Co-Authors per Documents | 3.83 |
| review | 13 | Collaboration Index | 3.7 |
| SL. | Region | Freq | SL. | Region | Freq |
|---|---|---|---|---|---|
| 1 | USA | 178 | 11 | FRANCE | 25 |
| 2 | CHINA | 136 | 12 | SAUDI ARABIA | 23 |
| 3 | INDIA | 111 | 13 | ROMANIA | 17 |
| 4 | SOUTH KOREA | 53 | 14 | MALAYSIA | 16 |
| 5 | UK | 51 | 15 | ISRAEL | 14 |
| 6 | AUSTRALIA | 46 | 16 | MEXICO | 14 |
| 7 | ITALY | 36 | 17 | KENYA | 13 |
| 8 | SPAIN | 35 | 18 | PAKISTAN | 13 |
| 9 | GERMANY | 30 | 19 | SOUTH AFRICA | 11 |
| 10 | SINGAPORE | 30 | 20 | AUSTRIA | 9 |
| R | Author | Articles | Journals | TC | TC/Year | NTC |
|---|---|---|---|---|---|---|
| 1 | Fielding KS, 2013 | An experimental test of voluntary strategies to promote urban water demand management | J. Environ. Manage. | 265 | 26.5 | 4.34 |
| 2 | Stewart RA, 2010 | Web-based knowledge management system: Linking smart metering to the future of urban water planning | Aust Planner | 111 | 8.54 | 1.00 |
| 3 | Cole G, 2013 | Smart meter enabled disaggregation of urban peak water demand: Precursor to effective urban water planning | Urban Water J. | 69 | 6.90 | 1.88 |
| 4 | Gurung TR, 2015 | Smart meter enabled water end-use demand data: Platform for the enhanced infrastructure planning of contemporary urban water supply networks | J. Cleaner Production | 59 | 7.38 | 2.42 |
| 5 | Gurung TR, 2014 | Smart meters for enhanced water supply network modelling and infrastructure planning | Resources, Conservation and Recycling | 59 | 6.56 | 2.46 |
| 6 | Luiijf E, 2013 | Nineteen national cybersecurity strategies | Int. J. of Critical Infrastructure systems | 59 | 5.90 | 1.61 |
| 7 | Liang G, 2019 | A framework for cyber topology attacks: Line-switching and new attack scenarios | IEEE Transactions on Smart Grid | 57 | 14.25 | 3.86 |
| 8 | Nguyen KA, 2015 | Intelligent autonomous system for residential water end use classification: Autoflow | Applied Soft Computing Journal | 50 | 6.25 | 2.05 |
| 9 | Nguyen KA, 2014 | An autonomous and intelligent expert system for residential water end-use classification | Expert Systems with Applications | 43 | 4.78 | 1.79 |
| 10 | Moglia M, 2018 | Promoting water conservation: Where to from here? | Water (Switzerland) | 33 | 6.60 | 3.79 |
| 11 | Andreasson K, 2015 | Digital divides: The new challenges and opportunities of e-inclusion | Digital Divides: The New Challenges and Opportunities of e-Inclusion | 29 | 3.63 | 1.19 |
| 12 | Thiyagarajan K, 2020 | Robust Sensor Suite Combined with Predictive Analytics Enabled Anomaly Detection Model for Smart Monitoring of Concrete Sewer Pipe Surface Moisture Conditions | IEEE Sensors | 27 | 9.00 | 5.10 |
| 13 | Vakilifard N, 2019 | An interactive planning model for sustainable urban water and energy supply | Applied Energy | 26 | 6.50 | 1.76 |
| 14 | Talebpour MR, 2014 | Water and energy nexus of residential rainwater tanks at an end-use level: Case of Australia | Energy and Buildings | 25 | 2.78 | 1.04 |
| 15 | Parvin S, 2013 | Multi-cyber framework for availability enhancement of cyber–physical systems | Computing | 24 | 2.40 | 0.65 |
| SL. | Sources | Articles |
|---|---|---|
| 1 | ACM International Conference Proceeding Series | 6 |
| 2 | IEEE Access | 6 |
| 3 | Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) | 6 |
| 4 | Water (Switzerland) | 6 |
| 5 | Electronics (Switzerland) | 5 |
| 6 | Advances in Intelligent Systems and Computing | 4 |
| 7 | IEEE Internet of Things | 4 |
| 8 | Journal of Water Resources Planning and Management | 4 |
| 9 | Communications in Computer and Information Science | 3 |
| 10 | IET Conference Publications | 3 |
| 11 | International Journal of Critical Infrastructure Protection | 3 |
| 12 | Procedia Engineering | 3 |
| 13 | Sensors | 3 |
| 14 | Sustainable Cities and Society | 3 |
| 15 | Wireless Personal Communications | 3 |
| 16 | Advanced Sciences and Technologies for Security Applications | 2 |
| 17 | Applied Sciences (Switzerland) | 2 |
| 18 | Computers And Security | 2 |
| 19 | IEEE International Conference on Communications | 2 |
| 20 | IEEE Sensors | 2 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Bello, A.; Jahan, S.; Farid, F.; Ahamed, F. A Systemic Review of the Cybersecurity Challenges in Australian Water Infrastructure Management. Water 2023, 15, 168. https://doi.org/10.3390/w15010168
Bello A, Jahan S, Farid F, Ahamed F. A Systemic Review of the Cybersecurity Challenges in Australian Water Infrastructure Management. Water. 2023; 15(1):168. https://doi.org/10.3390/w15010168
Chicago/Turabian StyleBello, Abubakar, Sayka Jahan, Farnaz Farid, and Farhad Ahamed. 2023. "A Systemic Review of the Cybersecurity Challenges in Australian Water Infrastructure Management" Water 15, no. 1: 168. https://doi.org/10.3390/w15010168
APA StyleBello, A., Jahan, S., Farid, F., & Ahamed, F. (2023). A Systemic Review of the Cybersecurity Challenges in Australian Water Infrastructure Management. Water, 15(1), 168. https://doi.org/10.3390/w15010168






