Blockchain for Internet of Underwater Things: State-of-the-Art, Applications, Challenges, and Future Directions
Abstract
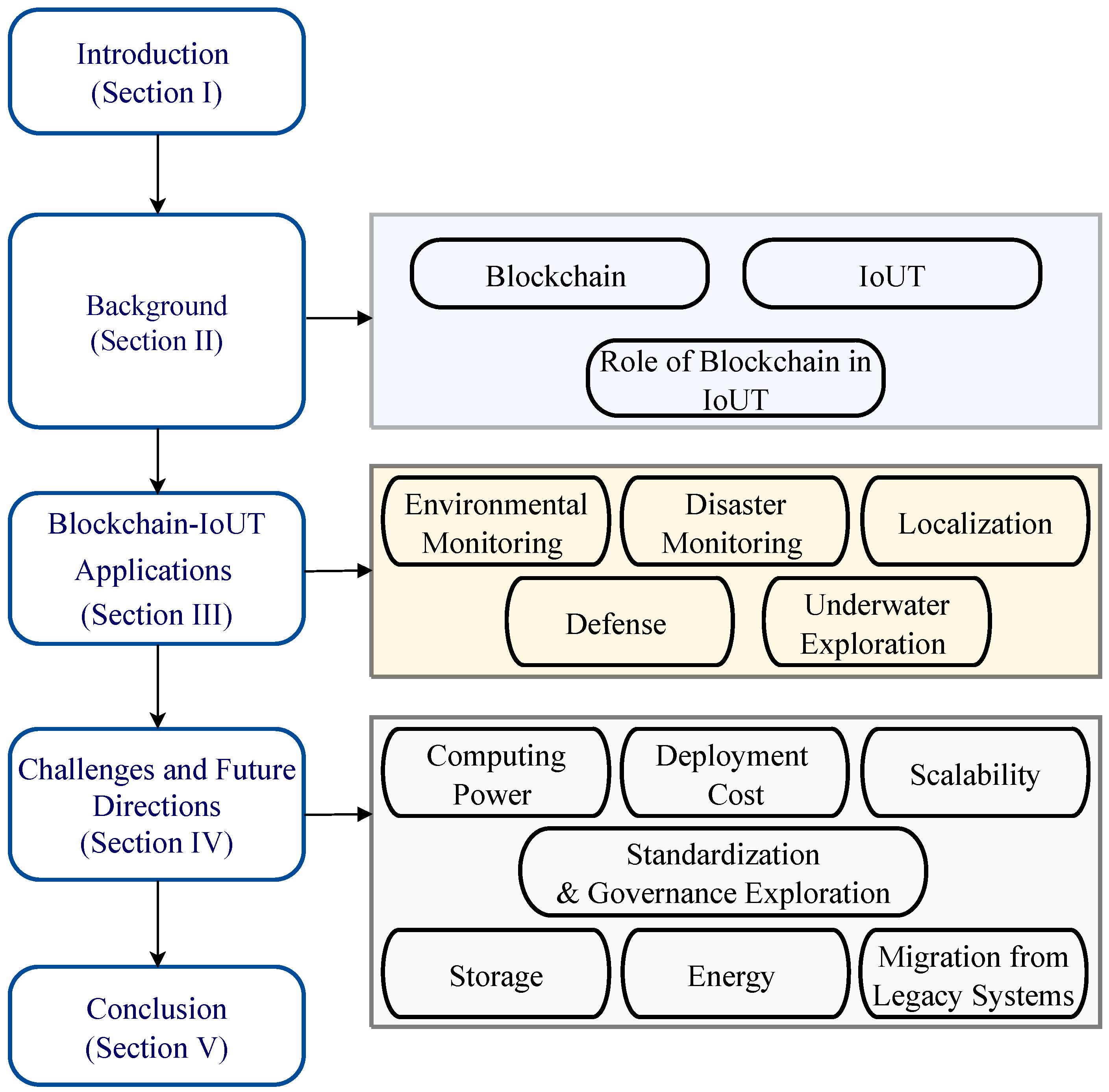
1. Introduction
- A first-of-its-kind survey is presented on applications of blockchain for the IoUT.
- An exhaustive review on the use of blockchain in IoUT applications is presented.
- A discussion on the challenges and future prospects of research relevant to the integration of blockchain in IoUT applications is presented.
2. Background
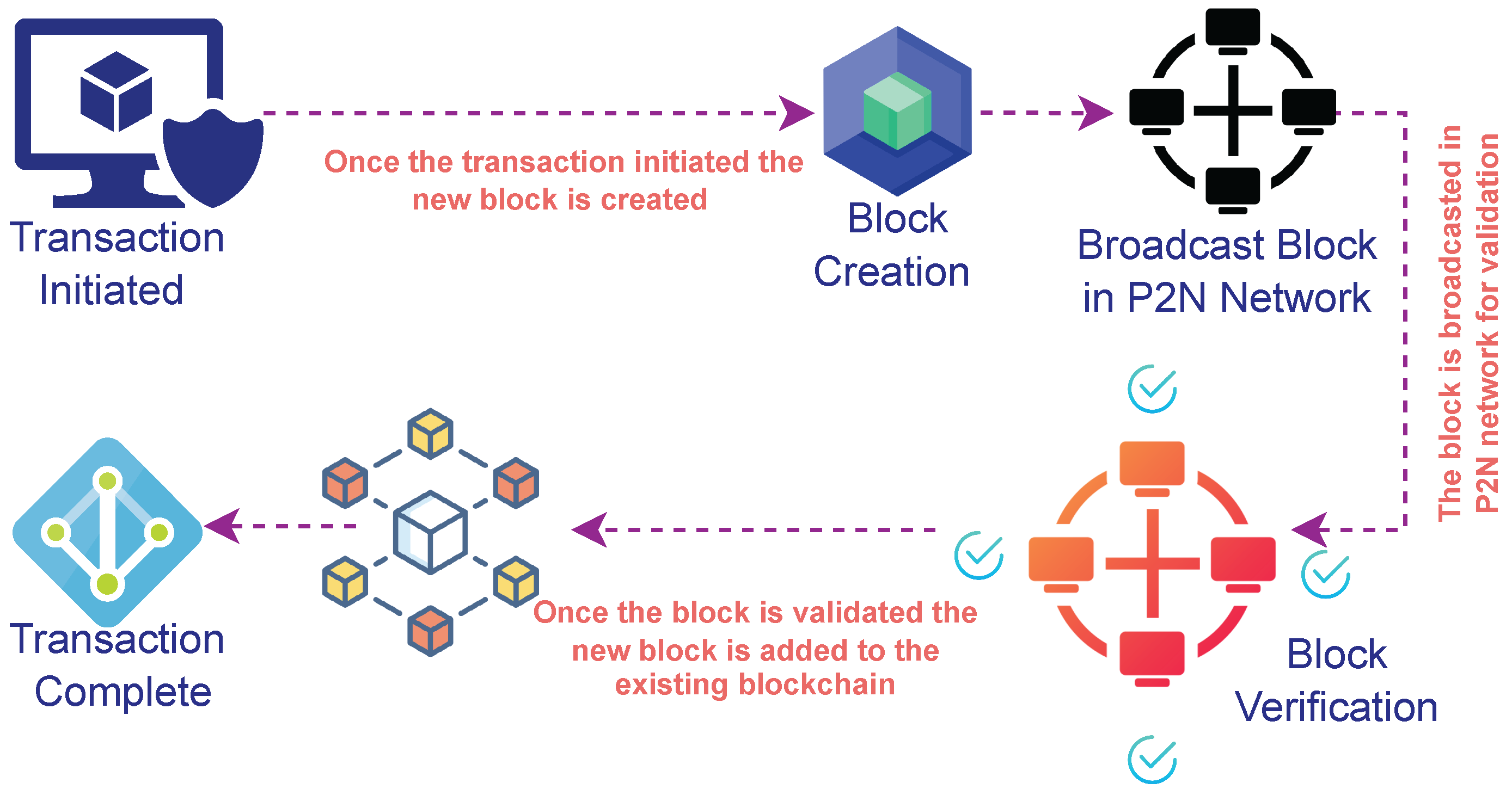
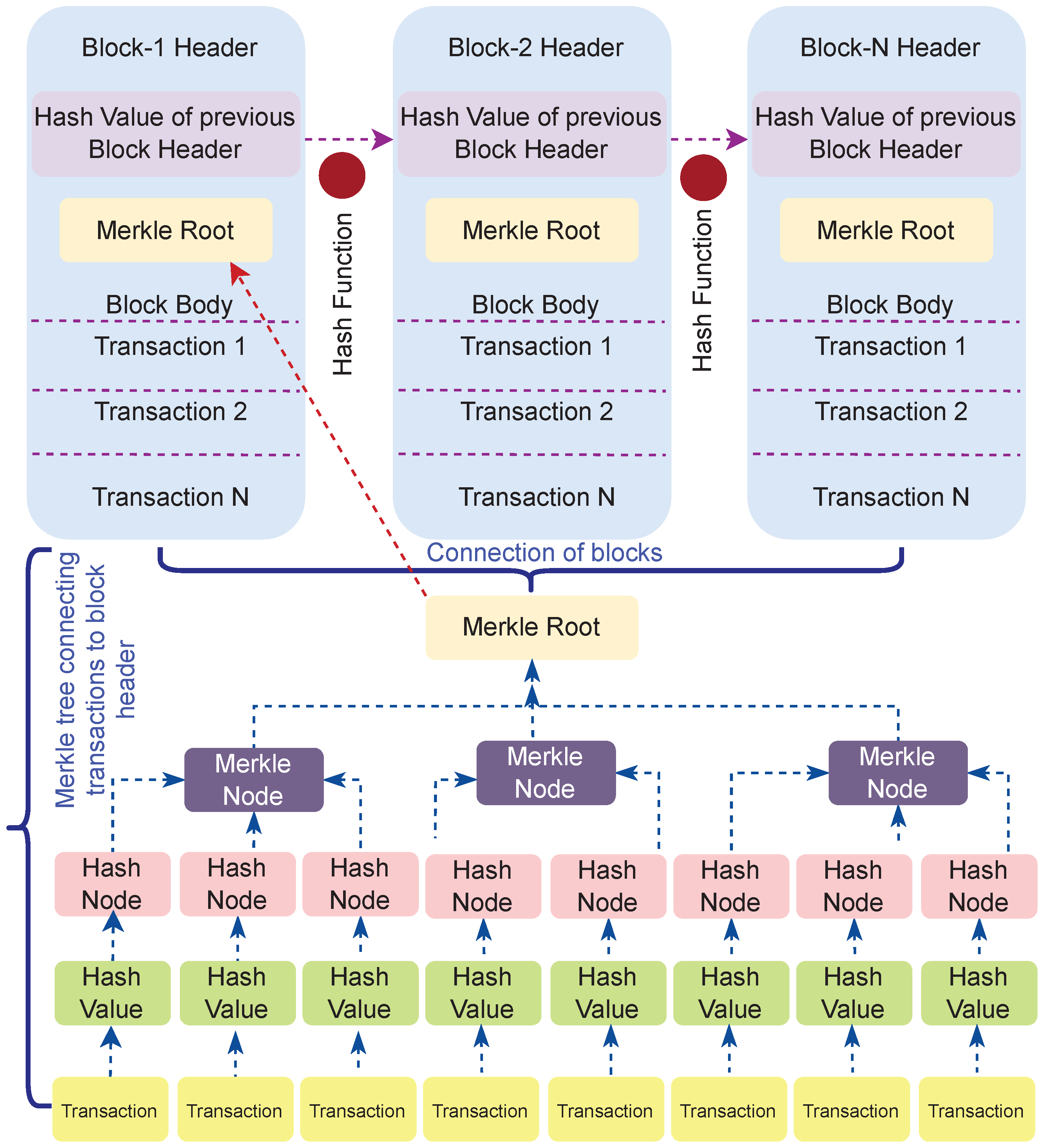
2.1. Blockchain
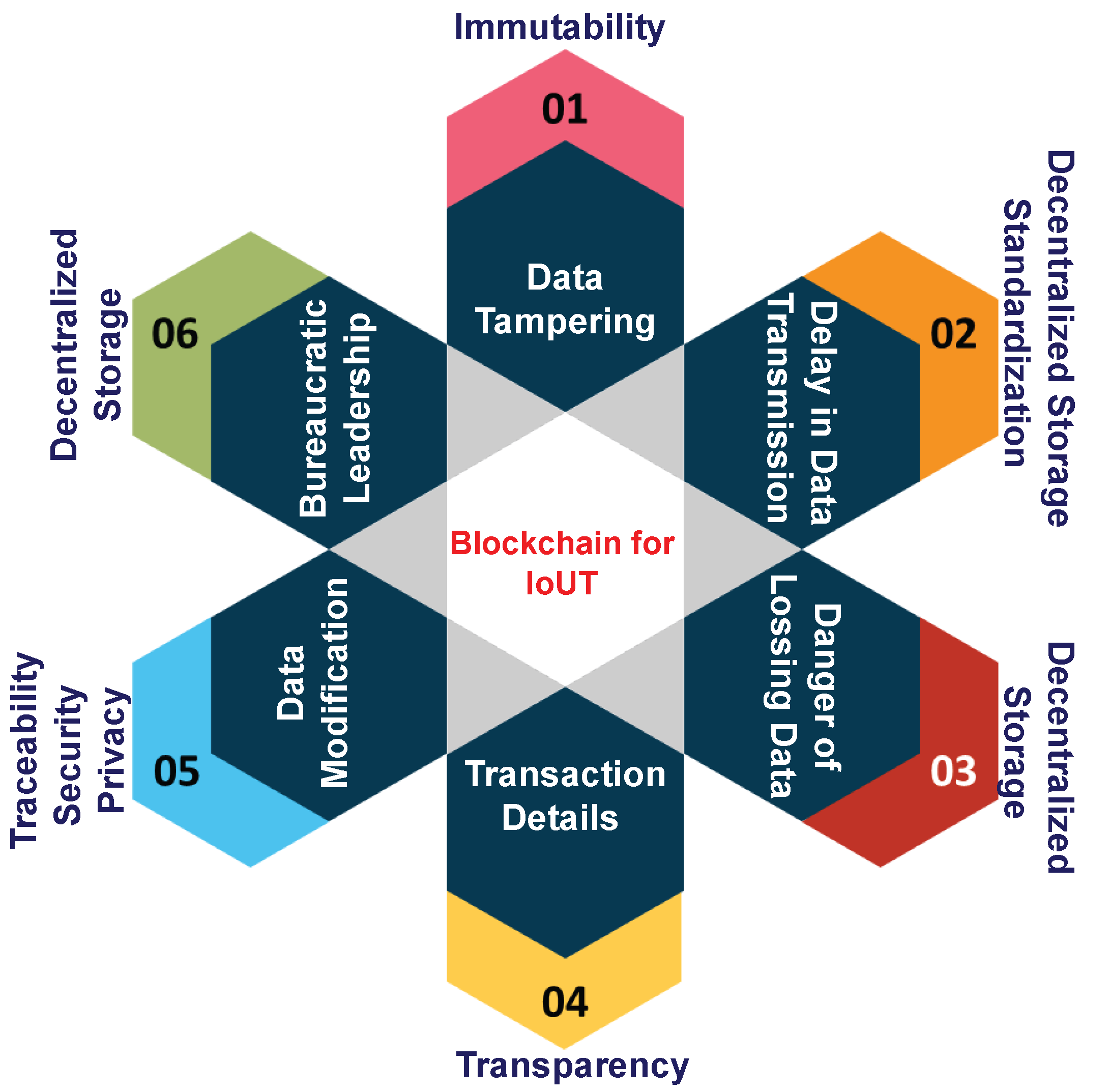
- Immutability—Blockchain is a permanent and unalterable network that promises no chance of changing the nodes in the network. The blockchain network has several nodes chained to each other, and every node maintains a copy of the digital ledger in the network. Hence, any transaction initiated in the network is authenticated and verified to be included in the ledger. As a result, the data stored in any transaction are highly impossible to tamper with, as they are strictly protected by the nodes of the given network. This promotes the network to be highly transparent and secure, creating successful transactions with the consensus of all nodes in the network. Thus, it allows anyone to view the transactions, but does not give access to edit or modify the data in the transactions.
- Decentralization—The framework is not operated under a single authority; rather, a collection of nodes is involved in managing and maintaining the blockchain network. The network is deployed on a peer-to-peer network, enabling each node to have a copy of the digital ledger, unlike the conventional banking system. Hence, the cost to hack such a decentralized network is more expensive, making it one of the most important features of blockchain technology.
- Smart contracts—Blockchain executes the transactions in a faster way by applying the smart contract principle. Smart contracts are self-executing digital contracts that automatically execute the transactions when certain conditions and agreements are satisfied for the current transaction.
- Consensus protocol—The consensus mechanism is the fault-tolerance mechanism in which nodes in the peer-to-peer network accede a common agreement about the current state of transactions in the network. This ensures the data reliability and trustworthiness of transactions among the nodes of blockchain. The Proof-of-Work (PoW) is the robust consensus protocol used widely in banking services and other applications. The PoW ensures that the new block is created by solving extreme and computationally complex puzzles to avoid unreliable transactions [52,53].
- Transparency—The blockchain network renders unparalleled transparency, which ensures advanced data security solutions [54]. Hence, every single transaction taking place within the decentralized network is confirmed by the majority of the nodes in the network. Thus, any updated transaction can be viewed by the user while managing the transparency within the network.
2.2. Internet of Underwater Things
- Different communication technologies;
- Different tracking methodologies;
- Difficulty in recharging the battery;
- Different energy harvesting technologies;
- Different network density;
- Different localization techniques.
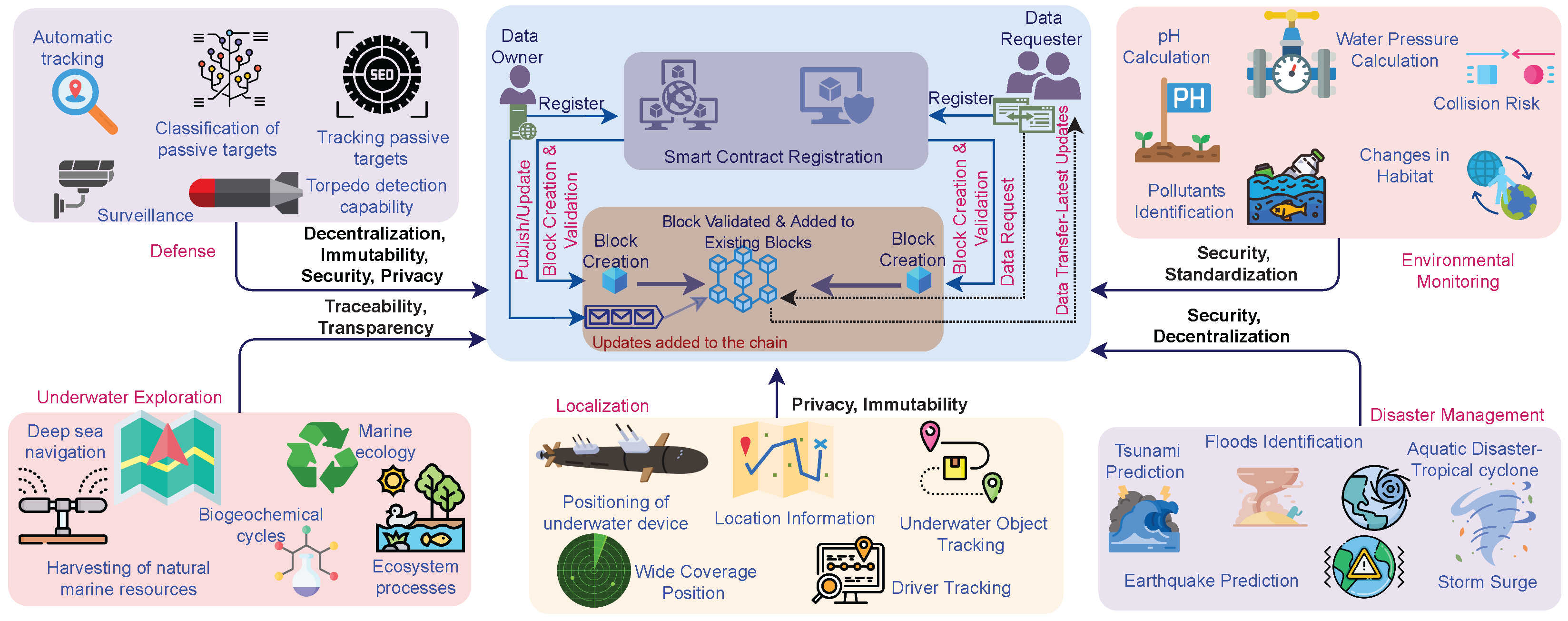
2.3. Integration of Blockchain with the IoUT
- Improving security in underwater communication—The sensors capture the significant information and relay and send the data to the monitoring center present on the land surface. The information transmitted is highly sensitive, which brings several problems such as data stealing, network hacking, and breaking the communication systems [65]. There is also a dire need to provide secured and trusted solutions for the processing and storage of the enormous amount of data being generated from the IoUT devices. The blockchain-based network architectures provide solutions to the aforementioned challenges by providing immutability and trustworthy data sharing and management and also enable efficient monitoring and tracking of the underwater devices, processes, and related resources. Blockchain [66] ensures secured and trusted data sharing in the underwater communications without interventions from humans or third parties. Furthermore, the need for autonomous decision-making in the hostile underwater environment with fickle network connectivity with base stations is supported by blockchain. The smart contract features of blockchain enable such dynamic and autonomous decision-making, ensuring secured data storage and the reliability of such frameworks.
- Trustworthiness of IoUT smart devices—With the substantial growth of IoT technology, more and more sensor devices are introduced, which are used for building the data communication network. Similar to the IoT, the IoUT also has several smart devices embedded with sensors, which are developed and utilized for data communication in the UWSN. The data generated from these UWSN devices may be very sensitive for critical applications such as defense [67]. The consensus algorithm is the decision-making process for the group of active nodes in the communication network while building trustworthy transactions in blockchain.
- Availability of the data in the IoUT—Blockchain [68] uses the fault-tolerant mechanism, building an effective network for the availability of data transmitted through the IoUT devices. The decentralized and distributed structure of blockchain is a very important feature to confirm the availability of data perpetually. This property of blockchain is vital for making the data available to oceanographers to conduct their research analysis and investigations at their convenience [69]. The decentralized system stores the information spread across the globe so that there is no single point of failure. This is achieved by storing the blockchain data over millions of devices on the distributed network of nodes; hence, the data and network are highly resistant to any malicious attack or technical failure in the network. Because of this, the availability of data in the blockchain-enabled IoUT communication network is possible.
- Privacy of the data in the IoUT—Attackers cannot misuse or obtain the data, as the users can control their data with the private and public keys in a blockchain transaction, thereby enabling data ownership. The data owners can control when, how, and to what extent a third party can access the data. The privacy of data generated from IoUT devices can thus be preserved with blockchain technology.
3. Applications
3.1. Environmental Monitoring
3.2. Disaster Management
3.3. Localization
3.4. Defense
3.5. Underwater Exploration
4. Challenges and Future Directions
4.1. Computing Power
4.2. Storage Capacity
4.3. Scalability
4.4. Standardization and Governance
4.5. Migration from Legacy Systems
4.6. Energy Consumption
4.7. Cost
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Cooley, S.W.; Ryan, J.C.; Smith, L.C. Human alteration of global surface water storage variability. Nature 2021, 591, 78–81. [Google Scholar] [CrossRef] [PubMed]
- Yap, W.; Switzer, A.D.; Gouramanis, C.; Marzinelli, E.; Wijaya, W.; Yan, Y.T.; Dominey-Howes, D.; Labbate, M.; Srinivasalu, S.; Jankaew, K.; et al. Environmental DNA signatures distinguish between tsunami and storm deposition in overwash sand. Commun. Earth Environ. 2021, 2, 129. [Google Scholar] [CrossRef]
- Singh, V.K.; Roxy, M. A review of ocean-atmosphere interactions during tropical cyclones in the north Indian Ocean. Earth-Sci. Rev. 2022, 226, 103967. [Google Scholar] [CrossRef]
- Zhou, R.; Meng, Z.; Bai, L. Differences in tornado activities and key tornadic environments between China and the United States. Int. J. Climatol. 2022, 42, 367–384. [Google Scholar] [CrossRef]
- Zhang, Z.; Huang, J.; Cao, S. Marine cold chain transportation monitoring and route scheduling optimization based on IoV-BDS. IEEE Access 2021, 9, 20557–20574. [Google Scholar] [CrossRef]
- Ertör, I. ‘We are the oceans, we are the people!’: Fisher people’s struggles for blue justice. In The Journal of Peasant Studies; Taylor&Francis: Boca Raton, FL, USA, 2021; pp. 1–30. [Google Scholar]
- Kadagi, N.I.; Wambiji, N.; Fennessy, S.T.; Allen, M.S.; Ahrens, R.N. Challenges and opportunities for sustainable development and management of marine recreational and sport fisheries in the Western Indian Ocean. Mar. Policy 2021, 124, 104351. [Google Scholar] [CrossRef]
- Leal Filho, W.; Abubakar, I.R.; Nunes, C.; Platje, J.J.; Ozuyar, P.G.; Will, M.; Nagy, G.J.; Al-Amin, A.Q.; Hunt, J.D.; Li, C. Deep seabed mining: A note on some potentials and risks to the sustainable mineral extraction from the oceans. J. Mar. Sci. Eng. 2021, 9, 521. [Google Scholar] [CrossRef]
- Radeta, M.; Zuniga, A.; Motlagh, N.H.; Liyanage, M.; Freitas, R.; Youssef, M.; Tarkoma, S.; Flores, H.; Nurmi, P. Deep learning and the oceans. Computer 2022, 55, 39–50. [Google Scholar] [CrossRef]
- Samir, M.; Elhattab, M.; Assi, C.; Sharafeddine, S.; Ghrayeb, A. Optimizing age of information through aerial reconfigurable intelligent surfaces: A deep reinforcement learning approach. IEEE Trans. Veh. Technol. 2021, 70, 3978–3983. [Google Scholar] [CrossRef]
- Vo, D.T.; Nguyen, X.P.; Nguyen, T.D.; Hidayat, R.; Huynh, T.T.; Nguyen, D.T. A review on the internet of thing (IoT) technologies in controlling ocean environment. In Energy Sources, Part A: Recovery, Utilization, and Environmental Effects; Taylor&Francis: Boca Raton, FL, USA, 2021; pp. 1–19. [Google Scholar] [CrossRef]
- Reddy, T.; RM, S.P.; Parimala, M.; Chowdhary, C.L.; Hakak, S.; Khan, W.Z. A deep neural networks based model for uninterrupted marine environment monitoring. Comput. Commun. 2020, 157, 64–75. [Google Scholar]
- Reddy Maddikunta, P.K.; Srivastava, G.; Reddy Gadekallu, T.; Deepa, N.; Boopathy, P. Predictive model for battery life in IoT networks. IET Intell. Transp. Syst. 2020, 14, 1388–1395. [Google Scholar] [CrossRef]
- Yazdinejad, A.; Parizi, R.M.; Srivastava, G.; Dehghantanha, A.; Choo, K.K.R. Energy efficient decentralized authentication in internet of underwater things using blockchain. In Proceedings of the 2019 IEEE Globecom Workshops (GC Wkshps), Waikoloa, HI, USA, 9–13 December 2019; pp. 1–6. [Google Scholar]
- Zhou, Z.; Gupta, B.B.; Gaurav, A.; Li, Y.; Lytras, M.D.; Nedjah, N. An Efficient and Secure Identity-Based Signature System for Underwater Green Transport System. IEEE Trans. Intell. Transp. Syst. 2022, 23, 16161–16169. [Google Scholar] [CrossRef]
- Mohsan, S.A.H.; Mazinani, A.; Othman, N.Q.H.; Amjad, H. Towards the internet of underwater things: A comprehensive survey. Earth Sci. Inform. 2022, 15, 735–764. [Google Scholar] [CrossRef]
- Falkowski, P. Ocean science: The power of plankton. Nature 2012, 483, S17–S20. [Google Scholar] [CrossRef]
- Domingo, M.C. An overview of the internet of underwater things. J. Netw. Comput. Appl. 2012, 35, 1879–1890. [Google Scholar] [CrossRef]
- Jahanbakht, M.; Xiang, W.; Hanzo, L.; Azghadi, M.R. Internet of underwater things and big marine data analytics—A comprehensive survey. IEEE Commun. Surv. Tutor. 2021, 23, 904–956. [Google Scholar] [CrossRef]
- Saab, S.; Fu, Y.; Ray, A.; Hauser, M. A Dynamically Stabilized Recurrent Neural Network. Neural Process. Lett. 2022, 54, 1195–1209. [Google Scholar] [CrossRef]
- Kesrai, M.D.R.; Lee, J.; Ko, E.; Shin, S.Y.; Namgung, J.I.; Yum, S.H.; Park, S.H. Underwater network management system in internet of underwater things: Open challenges, benefits, and feasible solution. Electronics 2020, 9, 1142. [Google Scholar]
- Alazab, M.; Tang, M. Deep Learning Applications for Cyber Security; Springer: Berlin/Heidelberg, Germany, 2019. [Google Scholar]
- Yisa, A.G.; Dargahi, T.; Belguith, S.; Hammoudeh, M. Security challenges of internet of underwater things: A systematic literature review. Trans. Emerg. Telecommun. Technol. 2021, 32, e4203. [Google Scholar] [CrossRef]
- Bello, O.; Zeadally, S. Internet of underwater things communication: Architecture, technologies, research challenges and future opportunities. Ad Hoc Netw. 2022, 135, 102933. [Google Scholar] [CrossRef]
- Salami, A.F.; Dogo, E.M.; Makaba, T.; Adedokun, E.A.; Muazu, M.B.; Sadiq, B.O.; Salawudeen, A.T. A decade bibliometric analysis of underwater sensor network research on the Internet of Underwater Things: An African perspective. In Trends Cloud-Based IoT; Springer: Berlin/Heidelberg, Germany, 2020; pp. 147–182. [Google Scholar] [CrossRef]
- Ghafoor, H.; Noh, Y. An overview of next-generation underwater target detection and tracking: An integrated underwater architecture. IEEE Access 2019, 7, 98841–98853. [Google Scholar] [CrossRef]
- Mary, D.R.K.; Ko, E.; Kim, S.G.; Yum, S.H.; Shin, S.Y.; Park, S.H. A Systematic Review on Recent Trends, Challenges, Privacy and Security Issues of Underwater Internet of Things. Sensors 2021, 21, 8262. [Google Scholar] [CrossRef] [PubMed]
- Feng, Q.; He, D.; Zeadally, S.; Khan, M.K.; Kumar, N. A survey on privacy protection in blockchain system. J. Netw. Comput. Appl. 2019, 126, 45–58. [Google Scholar] [CrossRef]
- Arafeh, M.; El Barachi, M.; Mourad, A.; Belqasmi, F. A blockchain based architecture for the detection of fake sensing in mobile crowdsensing. In Proceedings of the 2019 4th International Conference on Smart and Sustainable Technologies (SpliTech), Bol/Split, Croatia, 18–21 June 2019; pp. 1–6. [Google Scholar]
- Murray, M. Tutorial: A descriptive introduction to the Blockchain. Commun. Assoc. Inf. Syst. 2019, 45, 25. [Google Scholar] [CrossRef]
- Dustdar, S.; Fernández, P.; García, J.M.; Ruiz-Cortés, A. Elastic smart contracts in blockchains. IEEE/CAA J. Autom. Sin. 2021, 8, 1901–1912. [Google Scholar] [CrossRef]
- ur Rehman, M.H.; Salah, K.; Damiani, E.; Svetinovic, D. Trust in blockchain cryptocurrency ecosystem. IEEE Trans. Eng. Manag. 2019, 67, 1196–1212. [Google Scholar] [CrossRef]
- Lo, S.K.; Xu, X.; Chiam, Y.K.; Lu, Q. Evaluating Suitability of Applying Blockchain. In Proceedings of the 2017 22nd International Conference on Engineering of Complex Computer Systems (ICECCS), Fukuoka, Japan, 6–8 November 2017; pp. 158–161. [Google Scholar] [CrossRef]
- Cucari, N.; Lagasio, V.; Lia, G.; Torriero, C. The impact of blockchain in banking processes: The Interbank Spunta case study. Technol. Anal. Strateg. Manag. 2022, 34, 138–150. [Google Scholar] [CrossRef]
- Boakye, E.A.; Zhao, H.; Ahia, B.N.K. Emerging research on blockchain technology in finance; a conveyed evidence of bibliometric-based evaluations. J. High Technol. Manag. Res. 2022, 33, 100437. [Google Scholar] [CrossRef]
- Sangari, M.S.; Mashatan, A. A data-driven, comparative review of the academic literature and news media on blockchain-enabled supply chain management: Trends, gaps, and research needs. Comput. Ind. 2022, 143, 103769. [Google Scholar] [CrossRef]
- Keresztes, É.R.; Kovács, I.; Horváth, A.; Zimányi, K. Exploratory analysis of blockchain platforms in supply chain management. Economies 2022, 10, 206. [Google Scholar] [CrossRef]
- Adere, E.M. Blockchain in healthcare and IoT: A systematic literature review. Array 2022, 14, 100139. [Google Scholar] [CrossRef]
- Prybutok, V.R.; Sauser, B. Theoretical and practical applications of blockchain in healthcare information management. Inf. Manag. 2022, 59, 103649. [Google Scholar]
- Abdelmaboud, A.; Ahmed, A.I.A.; Abaker, M.; Eisa, T.A.E.; Albasheer, H.; Ghorashi, S.A.; Karim, F.K. Blockchain for IoT Applications: Taxonomy, Platforms, Recent Advances, Challenges and Future Research Directions. Electronics 2022, 11, 630. [Google Scholar] [CrossRef]
- Pal, S.; Dorri, A.; Jurdak, R. Blockchain for IoT access control: Recent trends and future research directions. J. Netw. Comput. Appl. 2022, 203, 103371. [Google Scholar] [CrossRef]
- Dehury, C.; Srirama, S.N.; Donta, P.K.; Dustdar, S. Securing clustered edge intelligence with blockchain. IEEE Consum. Electron. Mag. 2022, 1. [Google Scholar] [CrossRef]
- Chen, Y.; Lu, Y.; Bulysheva, L.; Kataev, M.Y. Applications of blockchain in industry 4.0: A review. In Information Systems Frontiers; Springer: Berlin/Heidelberg, Germany, 2022; pp. 1–15. [Google Scholar] [CrossRef]
- Bamakan, S.M.H.; Malekinejad, P.; Ziaeian, M. Towards blockchain-based hospital waste management systems; applications and future trends. J. Clean. Prod. 2022, 349, 131440. [Google Scholar] [CrossRef]
- Lemos, C.; Ramos, R.F.; Moro, S.; Oliveira, P.M. Stick or Twist—The Rise of Blockchain Applications in Marketing Management. Sustainability 2022, 14, 4172. [Google Scholar] [CrossRef]
- Mendling, J.; Weber, I.; Aalst, W.V.D.; Brocke, J.V.; Cabanillas, C.; Daniel, F.; Debois, S.; Ciccio, C.D.; Dumas, M.; Dustdar, S.; et al. Blockchains for business process management-challenges and opportunities. ACM Trans. Manag. Inf. Syst. (TMIS) 2018, 9, 1–16. [Google Scholar] [CrossRef]
- Dustdar, S.; Fernández Montes, P.; García Rodríguez, J.M.; Ruiz Cortés, A. Elastic Smart Contracts across Multiple Blockchains. In Proceedings of the FAB 2019: Second International Symposium on Foundations and Applications of Blockchain; University of Southern California: Los Angeles, CA, USA, 2019; pp. 28–34. [Google Scholar]
- Jayabalasamy, G.; Koppu, S. High-performance Edwards curve aggregate signature (HECAS) for nonrepudiation in IoT-based applications built on the blockchain ecosystem. In Journal of King Saud University-Computer and Information Sciences; Elsevier: Amsterdam, The Netherlands, 2021. [Google Scholar] [CrossRef]
- Guo, H.; Yu, X. A Survey on Blockchain Technology and its security. Blockchain Res. Appl. 2022, 3, 100067. [Google Scholar] [CrossRef]
- Xu, X.; Dilum Bandara, H.; Lu, Q.; Weber, I.; Bass, L.; Zhu, L. A Decision Model for Choosing Patterns in Blockchain-Based Applications. In Proceedings of the 2021 IEEE 18th International Conference on Software Architecture (ICSA), Stuttgart, Germany, 22–26 March 2021; pp. 47–57. [Google Scholar] [CrossRef]
- Almeshal, T.A.; Alhogail, A.A. Blockchain for Businesses: A Scoping Review of Suitability Evaluations Frameworks. IEEE Access 2021, 9, 155425–155442. [Google Scholar] [CrossRef]
- Hewa, T.M.; Hu, Y.; Liyanage, M.; Kanhare, S.S.; Ylianttila, M. Survey on blockchain-based smart contracts: Technical aspects and future research. IEEE Access 2021, 9, 87643–87662. [Google Scholar] [CrossRef]
- Manzoor, A.; Braeken, A.; Kanhere, S.S.; Ylianttila, M.; Liyanage, M. Proxy re-encryption enabled secure and anonymous IoT data sharing platform based on blockchain. J. Netw. Comput. Appl. 2021, 176, 102917. [Google Scholar] [CrossRef]
- Xu, L.D.; Lu, Y.; Li, L. Embedding Blockchain Technology Into IoT for Security: A Survey. IEEE Internet Things J. 2021, 8, 10452–10473. [Google Scholar] [CrossRef]
- Al-Turjman, F.; Zahmatkesh, H.; Shahroze, R. An overview of security and privacy in smart cities’ IoT communications. Trans. Emerg. Telecommun. Technol. 2022, 33, e3677. [Google Scholar] [CrossRef]
- Javed, A.R.; Shahzad, F.; ur Rehman, S.; Zikria, Y.B.; Razzak, I.; Jalil, Z.; Xu, G. Future smart cities requirements, emerging technologies, applications, challenges, and future aspects. Cities 2022, 129, 103794. [Google Scholar] [CrossRef]
- Victor, N.; Alazab, M.; Bhattacharya, S.; Magnusson, S.; Maddikunta, P.K.R.; Ramana, K.; Gadekallu, T.R. Federated Learning for IoUT: Concepts, Applications, Challenges and Opportunities. arXiv 2022, arXiv:2207.13976. [Google Scholar]
- Khanfar, A.A.; Iranmanesh, M.; Ghobakhloo, M.; Senali, M.G.; Fathi, M. Applications of blockchain technology in sustainable manufacturing and supply chain management: A systematic review. Sustainability 2021, 13, 7870. [Google Scholar] [CrossRef]
- Wen, J.; Yang, J.; Wang, T. Path planning for autonomous underwater vehicles under the influence of ocean currents based on a fusion heuristic algorithm. IEEE Trans. Veh. Technol. 2021, 70, 8529–8544. [Google Scholar] [CrossRef]
- Rubio-Solis, A.; Martinez-Hernandez, U.; Nava-Balanzar, L.; Garcia-Valdovinos, L.G.; Rodriguez-Olivares, N.A.; Orozco-Muñiz, J.P.; Salgado-Jimenez, T. Online Interval Type-2 Fuzzy Extreme Learning Machine applied to 3D path following for Remotely Operated Underwater Vehicles. Appl. Soft Comput. 2022, 115, 108054. [Google Scholar] [CrossRef]
- Subramani, N.; Mohan, P.; Alotaibi, Y.; Alghamdi, S.; Khalaf, O.I. An efficient metaheuristic-based clustering with routing protocol for underwater wireless sensor networks. Sensors 2022, 22, 415. [Google Scholar] [CrossRef]
- Ismail, A.; Wang, X.; Hawbani, A.; Alsamhi, S.; Abdel Aziz, S. Routing protocols classification for underwater wireless sensor networks based on localization and mobility. Wirel. Netw. 2022, 28, 797–826. [Google Scholar] [CrossRef]
- Reddy, T.S.; Chandra, S.; Arya, R.; Verma, A.K. Malicious anchor node extraction using geodesic search for survivable underwater wireless sensor network. Sci. Rep. 2022, 12, 1–11. [Google Scholar]
- Saleh, M.H.; Takruri, H.; Linge, N. Energy aware routing protocol for sparse underwater acoustic wireless sensor network. In Proceedings of the 2022 13th International Symposium on Communication Systems, Networks and Digital Signal Processing (CSNDSP), Porto, Portugal, 20–22 July 2022; pp. 750–755. [Google Scholar]
- Menaka, D.; Gauni, S.; Manimegalai, C.; Kalimuthu, K. Vision of IoUT: Advances and future trends in optical wireless communication. J. Opt. 2021, 50, 439–452. [Google Scholar] [CrossRef]
- Wazid, M.; Das, A.K.; Shetty, S.; Jo, M. A tutorial and future research for building a blockchain-based secure communication scheme for internet of intelligent things. IEEE Access 2020, 8, 88700–88716. [Google Scholar] [CrossRef]
- Wang, H.; Han, G.; Hou, Y.; Guizani, M.; Peng, Y. A Multi-Channel Interference Based Source Location Privacy Protection Scheme in Underwater Acoustic Sensor Networks. IEEE Trans. Veh. Technol. 2021, 71, 2058–2069. [Google Scholar] [CrossRef]
- Belotti, M.; Božić, N.; Pujolle, G.; Secci, S. A vademecum on blockchain technologies: When, which, and how. IEEE Commun. Surv. Tutor. 2019, 21, 3796–3838. [Google Scholar] [CrossRef]
- Menon, V.G.; Midhunchakkaravarthy, D.; Sujith, A.; John, S.; Li, X.; Khosravi, M.R. Towards Energy-Efficient and Delay-Optimized Opportunistic Routing in Underwater Acoustic Sensor Networks for IoUT Platforms: An Overview and New Suggestions. Comput. Intell. Neurosci. 2022, 2022, 7061617. [Google Scholar] [CrossRef]
- Shen, B.; Dong, C.; Minner, S. Combating Copycats in the Supply Chain with Permissioned Blockchain Technology. Prod. Oper. Manag. 2022, 31, 138–154. [Google Scholar] [CrossRef]
- Huang, L.; Zhen, L.; Wang, J.; Zhang, X. Blockchain implementation for circular supply chain management: Evaluating critical success factors. Ind. Mark. Manag. 2022, 102, 451–464. [Google Scholar] [CrossRef]
- Schinckus, C. A Nuanced perspective on blockchain technology and healthcare. Technol. Soc. 2022, 71, 102082. [Google Scholar] [CrossRef]
- Uddin, M.A.; Stranieri, A.; Gondal, I.; Balasurbramanian, V. A lightweight blockchain based framework for underwater iot. Electronics 2019, 8, 1552. [Google Scholar] [CrossRef]
- Razzaq, A. Blockchain-Based Secure Data Transmission for Internet of Underwater Things; Elsevier: Amsterdam, The Netherlands, 2022; SSRN 4127827. [Google Scholar]
- Qiu, T.; Zhao, Z.; Zhang, T.; Chen, C.; Chen, C.P. Underwater Internet of Things in smart ocean: System architecture and open issues. IEEE Trans. Ind. Inform. 2019, 16, 4297–4307. [Google Scholar] [CrossRef]
- Higuchi, A. Toward more integrated utilizations of geostationary satellite data for disaster management and risk mitigation. Remote Sens. 2021, 13, 1553. [Google Scholar] [CrossRef]
- Esposito, M.; Palma, L.; Belli, A.; Sabbatini, L.; Pierleoni, P. Recent Advances in Internet of Things Solutions for Early Warning Systems: A Review. Sensors 2022, 22, 2124. [Google Scholar] [CrossRef] [PubMed]
- Stojanovic, M.; Preisig, J. Underwater acoustic communication channels: Propagation models and statistical characterization. IEEE Commun. Mag. 2009, 47, 84–89. [Google Scholar] [CrossRef]
- Wang, Q.; Guo, S.; Yiu, K.F.C. Distributed Acoustic Beamforming with Blockchain Protection. IEEE Trans. Ind. Inform. 2020, 16, 7126–7135. [Google Scholar] [CrossRef]
- Nain, M.; Goyal, N. Localization techniques in underwater wireless sensor network. In Proceedings of the 2021 International Conference on Advance Computing and Innovative Technologies in Engineering (ICACITE), Greater Noida, India, 4–5 March 2021; pp. 747–751. [Google Scholar]
- Luo, J.; Yang, Y.; Wang, Z.; Chen, Y. Localization algorithm for underwater sensor network: A review. IEEE Internet Things J. 2021, 8, 13126–13144. [Google Scholar] [CrossRef]
- Sah, D.K.; Nguyen, T.N.; Kandulna, M.; Cengiz, K.; Amgoth, T. 3D Localization and Error Minimization in Underwater Sensor Networks. ACM Trans. Sens. Netw. (TOSN) 2022, 18, 31. [Google Scholar] [CrossRef]
- Li, H.; He, Y.; Cheng, X.; Zhu, H.; Sun, L. Security and privacy in localization for underwater sensor networks. IEEE Commun. Mag. 2015, 53, 56–62. [Google Scholar] [CrossRef]
- Chen, G.; Wu, J.; Yang, W.; Bashir, A.K.; Li, G.; Hammoudeh, M. Leveraging graph convolutional-LSTM for energy-efficient caching in blockchain-based green IoT. IEEE Trans. Green Commun. Netw. 2021, 5, 1154–1164. [Google Scholar] [CrossRef]
- Shen, D.; Huo, N.; Saab, S.S. A Probabilistically Quantized Learning Control Framework for Networked Linear Systems. IEEE Trans. Neural Netw. Learn. Syst. 2021. [Google Scholar] [CrossRef]
- Hammi, M.T.; Bellot, P.; Serhrouchni, A. BCTrust: A decentralized authentication blockchain-based mechanism. In Proceedings of the 2018 IEEE Wireless Communications and Networking Conference (WCNC), Barcelona, Spain, 15–18 April 2018; pp. 1–6. [Google Scholar]
- Hung, N.T.; Rego, F.F.; Pascoal, A.M. Cooperative Distributed Estimation and Control of Multiple Autonomous Vehicles for Range-Based Underwater Target Localization and Pursuit. IEEE Trans. Control Syst. Technol. 2021, 30, 1433–1447. [Google Scholar] [CrossRef]
- Guo, L.; Ma, L.; Zhang, H.; Yang, J.; Cheng, Z.; Jiang, W. An Unmanned Underwater Vehicle Torpedoes Attack Behavior Autonomous Decision-Making Method Based on Model Fusion. Electronics 2022, 11, 3097. [Google Scholar] [CrossRef]
- Islam, A.; Shin, S.Y. Blockchain Based UAV-Assisted Underwater Monitoring in Internet of Underwater Things; Korea Telecommunications Society: Seoul, Korea, 2019. [Google Scholar]
- Zhou, Y.; Li, B.; Wang, J.; Rocco, E.; Meng, Q. Discovering unknowns: Context-enhanced anomaly detection for curiosity-driven autonomous underwater exploration. Pattern Recognit. 2022, 131, 108860. [Google Scholar] [CrossRef]
- Lee, K.H.; Noh, J.; Khim, J.S. The Blue Economy and the United Nations’ sustainable development goals: Challenges and opportunities. Environ. Int. 2020, 137, 105528. [Google Scholar] [CrossRef]
- How Important Is the Ocean to Our Economy? Available online: https://oceanservice.noaa.gov/facts/oceaneconomy.html (accessed on 13 September 2022).
- About NOAA Ocean Exploration. Available online: https://oceanexplorer.noaa.gov/about/welcome.html (accessed on 13 September 2022).
- Ananda, R.G.; Vandavasi, B.N.J.; Raju, R.; Narayanaswamy, V.; Sethuraman, R.; Aravindakshan, A.M. Performance assesment of Navigation Systems Used in Deep-Water Scientific Human-Occupied Vehicle MATSYA 6000. In Proceedings of the OCEANS 2021, San Diego, CA, USA, 20–23 September 2021; pp. 1–9. [Google Scholar]
- Blockchain Firm PO8 Raises Crypto for Bahamas Hurricane Relief. 2019. Available online: https://cointelegraph.com/news/bahama-blockchain-company-raises-crypto-for-hurricane-dorian-relief (accessed on 12 October 2022).
- França, B. Deep Ocean: A blockchain-agnostic dark pool protocol. arXiv 2019, arXiv:1910.02359. [Google Scholar]
- Sun, K.; Cui, W.; Chen, C. Review of Underwater Sensing Technologies and Applications. Sensors 2021, 21, 7849. [Google Scholar] [CrossRef]
- Tsai, C.H.; Elibol, A.; Chong, N.Y. A UAV-UUV Transformative Housing for Minimal Logistics Underwater Exploration. In Proceedings of the 2021 18th International Conference on Ubiquitous Robots (UR), Gangneung, Republic of Korea, 12–14 July 2021. [Google Scholar]
- Nartey, C.; Tchao, E.T.; Gadze, J.D.; Yeboah-Akowuah, B.; Nunoo-Mensah, H.; Welte, D.; Sikora, A. Blockchain-IoT peer device storage optimization using an advanced time-variant multi-objective particle swarm optimization algorithm. EURASIP J. Wirel. Commun. Netw. 2022, 2022, 5. [Google Scholar] [CrossRef]
- Xiao, Y.; Zhang, N.; Lou, W.; Hou, Y.T. A survey of distributed consensus protocols for blockchain networks. IEEE Commun. Surv. Tutor. 2020, 22, 1432–1465. [Google Scholar] [CrossRef]
- Polge, J.; Robert, J.; Le Traon, Y. Permissioned blockchain frameworks in the industry: A comparison. ICT Express 2021, 7, 229–233. [Google Scholar] [CrossRef]
- Haas, B.; Mackay, M.; Novaglio, C.; Fullbrook, L.; Murunga, M.; Sbrocchi, C.; McDonald, J.; McCormack, P.C.; Alexander, K.; Fudge, M.; et al. The future of ocean governance. Rev. Fish Biol. Fish. 2022, 32, 253–270. [Google Scholar] [CrossRef] [PubMed]
- Crosman, K.M.; Allison, E.H.; Ota, Y.; Cisneros-Montemayor, A.M.; Singh, G.G.; Swartz, W.; Bailey, M.; Barclay, K.M.; Blume, G.; Colléter, M.; et al. Social equity is key to sustainable ocean governance. NPJ Ocean. Sustain. 2022, 1, 4. [Google Scholar] [CrossRef]
- Joannou, D.; Kalawsky, R.; Martínez-García, M.; Fowler, C.; Fowler, K. Realizing the role of permissioned blockchains in a systems engineering lifecycle. Systems 2020, 8, 41. [Google Scholar] [CrossRef]
- Kesari Mary, D.R.; Ko, E.; Yoon, D.J.; Shin, S.Y.; Park, S.H. Energy Optimization Techniques in Underwater Internet of Things: Issues, State-of-the-Art, and Future Directions. Water 2022, 14, 3240. [Google Scholar] [CrossRef]
| Ref | Contributions | Limitations |
|---|---|---|
| [18] | -The role of the IoUT in preserving natural water resources is discussed. -The differences of the IoUT and IoT are highlighted. -The architecture and applications of the IoUT are presented. -The potential challenges and solutions are addressed. | -The integration of the IoUT with other advanced technologies are not explored. -The security aspects of the IoUT applications are not explored. |
| [19] | -The concept of BMD is initiated considering the enormous size and variability of marine data collected from harsh and heterogeneous environments using the IoUT. -The traditional challenges of using BMD processing is explored. -The use of ML in handling BMD is presented. -The potential scope of future research in the IoUT and BMD is highlighted. | -More emphasis is given to underwater communication and network protocols and BMD data handling. -Security and privacy aspects of handling BMD are not considered. |
| [21] | -Underwater Network Management Systems (U-NMS) using acoustic communication and the IoUT are discussed. -A prototype implementation of a U-NMS in a library environment is presented. | -The viability of the prototype model in a real-world setup is not justified. |
| [23] | -Emphasizes the security threats related to UWSNs in IoUT implementations. | -Risk mitigation activities include the use of network protocols. -Alternative advanced approaches such as blockchain are not explored. |
| [24] | -Presents a review of existing research relevant to signal processing and routing for developing efficient IoUT systems. -The challenges mostly emphasize exploring various forms of network attacks and possible solutions along with research testbeds. | -The MAC protocol, QoS metrics, and related performance issues are discussed. -Solutions focus on secured transmission of data and not on the storage aspect of the same. |
| [25] | -The use of WSNs and the IoUT in developing underwater vehicles (ROUVs), untethered Autonomous Underwater Vehicles (AUVs), Unmanned Autonomous Surface Vehicles (USVs/ASVs), and various other smart underwater technologies are explored. -Different UWSN-based IoUT implementations in the African region are analyzed. | -The scope of review includes only the African region while missing the security aspect. |
| [16] | -Different network frameworks used in IoUT applications are discussed. -The use of edge computing, data analytics, Optical Wireless Communications (OWCs), machine learning, and Intelligent Reflecting Surfaces (IRSs) in the IoUT is presented. | -The role of a specific technology and its related contributions are not focused on, making the scope generic. |
| [26] | -A survey on various unmanned water vehicles is presented. -The use of cognitive acoustic networks, fog computing, the IoUT, and next-generation underwater networks is discussed. | -Primarily emphasizes the target detection and tracking scheme. -Security and privacy aspects of the collected data through the IoUT are not considered. |
| [27] | -Distinct forms of IoUT attacks in the form of black holes, routing, and Sybil are discussed. | -Focused primarily on IoUT network attacks and their prevention. -Security and privacy aspects of the collected data through the IoUT are not included. |
| The present survey | -The first-of-its-kind survey on the application of blockchain for the IoUT. -Applications of blockchain in the IoUT are discussed. -Challenges and future prospects of the integration of blockchain with the IoUT are highlighted. | - |
| Application | Motivation for Using Blockchain for the IoUT | Challenges of Blockchain–IoUT Integration |
|---|---|---|
| Environmental Monitoring |
|
|
| Disaster Management |
|
|
| Localization |
|
|
| Defense |
|
|
| Underwater Exploration |
|
|
| Sl. No. | Challenge Type | Description | Possible Solutions |
|---|---|---|---|
| 1 | Computing Power | High computational power is required for the consensus algorithms to work | Lightweight mechanisms need to be introduced; devices with high computational power need to be used |
| 2 | Storage Capacity | To handle a larger number of transactions per second and to store ledgers, high storage capacity is required | Use cloud resources |
| 3 | Scalability | Scalable solutions are required to accommodate the huge number of transactions | Transactions to be carried out among subnetworks |
| 4 | Standardization and Governance | To avoid the over-exploitation of resources and non-equitable service distribution, proper standardization is required | Proper standards are to be formulated; ocean governance needs to be considered regionally, nationally, and globally |
| 5 | Migration from legacy systems | Migration from the traditional systems and technologies to adopt blockchain-enabled solutions is expensive and time-consuming | Rigorous training is essential |
| 6 | Energy consumption | Acoustic communication demands more energy. Underwater communication suffers high attenuation, long propagation delays, and high bit rates; in addition, the blockchain adaption consumes high energy for successful transactions. | A lightweight energy-efficient blockchain-based framework for IoUT acoustic communication can be used to solve this |
| 7 | Cost | Installing, managing, and maintaining the communication devices underwater is a challenging task. Frequent maintenance may be required such as battery change, sensor servicing, and so on | (1) Power-saving protocols can be used to reduce power use and also to avoid battery failures; (2) horizontal axis and vertical axis deployment strategies can be used to reduce the complexity of the network |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Bhattacharya, S.; Victor, N.; Chengoden, R.; Ramalingam, M.; Selvi, G.C.; Maddikunta, P.K.R.; Donta, P.K.; Dustdar, S.; Jhaveri, R.H.; Gadekallu, T.R. Blockchain for Internet of Underwater Things: State-of-the-Art, Applications, Challenges, and Future Directions. Sustainability 2022, 14, 15659. https://doi.org/10.3390/su142315659
Bhattacharya S, Victor N, Chengoden R, Ramalingam M, Selvi GC, Maddikunta PKR, Donta PK, Dustdar S, Jhaveri RH, Gadekallu TR. Blockchain for Internet of Underwater Things: State-of-the-Art, Applications, Challenges, and Future Directions. Sustainability. 2022; 14(23):15659. https://doi.org/10.3390/su142315659
Chicago/Turabian StyleBhattacharya, Sweta, Nancy Victor, Rajeswari Chengoden, Murugan Ramalingam, Govardanan Chemmalar Selvi, Praveen Kumar Reddy Maddikunta, Praveen Kumar Donta, Schahram Dustdar, Rutvij H. Jhaveri, and Thippa Reddy Gadekallu. 2022. "Blockchain for Internet of Underwater Things: State-of-the-Art, Applications, Challenges, and Future Directions" Sustainability 14, no. 23: 15659. https://doi.org/10.3390/su142315659
APA StyleBhattacharya, S., Victor, N., Chengoden, R., Ramalingam, M., Selvi, G. C., Maddikunta, P. K. R., Donta, P. K., Dustdar, S., Jhaveri, R. H., & Gadekallu, T. R. (2022). Blockchain for Internet of Underwater Things: State-of-the-Art, Applications, Challenges, and Future Directions. Sustainability, 14(23), 15659. https://doi.org/10.3390/su142315659










