An Automated Vulnerability Detection and Remediation Method for Software Security
Abstract
:1. Introduction
2. Related Works
2.1. Automated Vulnerability Detection
2.1.1. Fuzzing
2.1.2. Symbolic Execution
2.1.3. Hybrid Fuzzing
2.2. Automated Vulnerability Remediation
2.2.1. Binary Hardening
2.2.2. Automatic Patch Generation
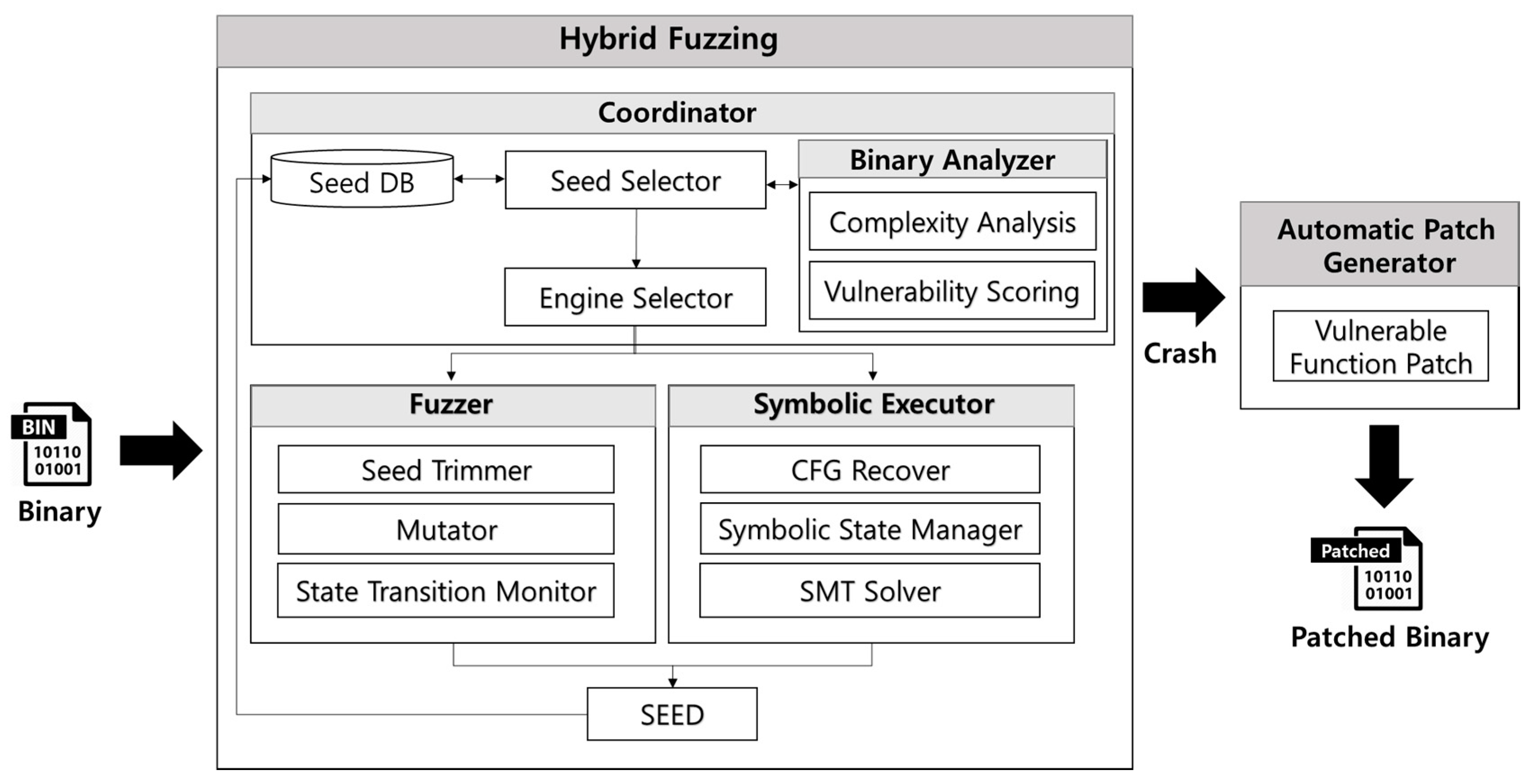
3. Automated Vulnerability Detection and Remediation Method
- Seed Selection: Seed selection is a step to select the input value to be used for vulnerability detection. In a first iteration, a seed scheduler selects a seed defined by the user to detect vulnerability. From a second iteration, a new seed created by the seed generation engine is selected for the next step.
- Binary Analysis: A binary analysis module executes the target binary in an instrumentation environment. As a binary is executed, disassembly code and function call information are extracted through binary instrumentation. Binary complexity and vulnerability scores are analyzed using the extracted information. The results of the complexity analysis determine whether to run a fuzzer or symbolic executor to detect vulnerabilities. The results of the vulnerability score will be used to determine whether a detected crash is exploitable in future research.
- Engine Selection: The engine selection module chooses one of the fuzzing and symbolic execution engines according to the result of the complexity analysis. The symbolic execution engine is executed if the complexity analysis result is smaller than a specific threshold; otherwise, the fuzzing engine is selected.
- Seed Generation: The fuzzer or symbolic executor is executed to generate seeds to be used in the next iteration. The seed generation process is performed until a state transition occurs. When a state transition occurs, the seed value that caused the state transition is stored in the seed DB.
- Repeat.
3.1. Binary Analysis
3.1.1. Instrumentation
3.1.2. Complexity Analysis
3.1.3. Vulnerability Scoring
3.2. Engine Selection
| Algorithm: Selection of Vulnerability Detection Engine |
| Input: Threshold T Data: Difficulty D, , , , Result: Seed S function Engine Selection(T); begin D ← Complexity (, , , ); if D < T then S ← Symbolic Executor(); else S ← Fuzzer(); end return S; end |
3.3. Fuzzing
3.4. Symbolic Execution
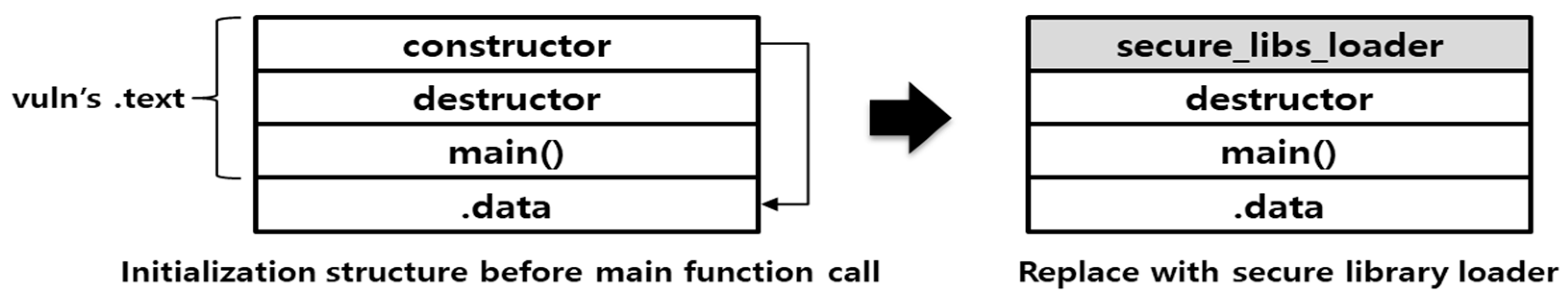
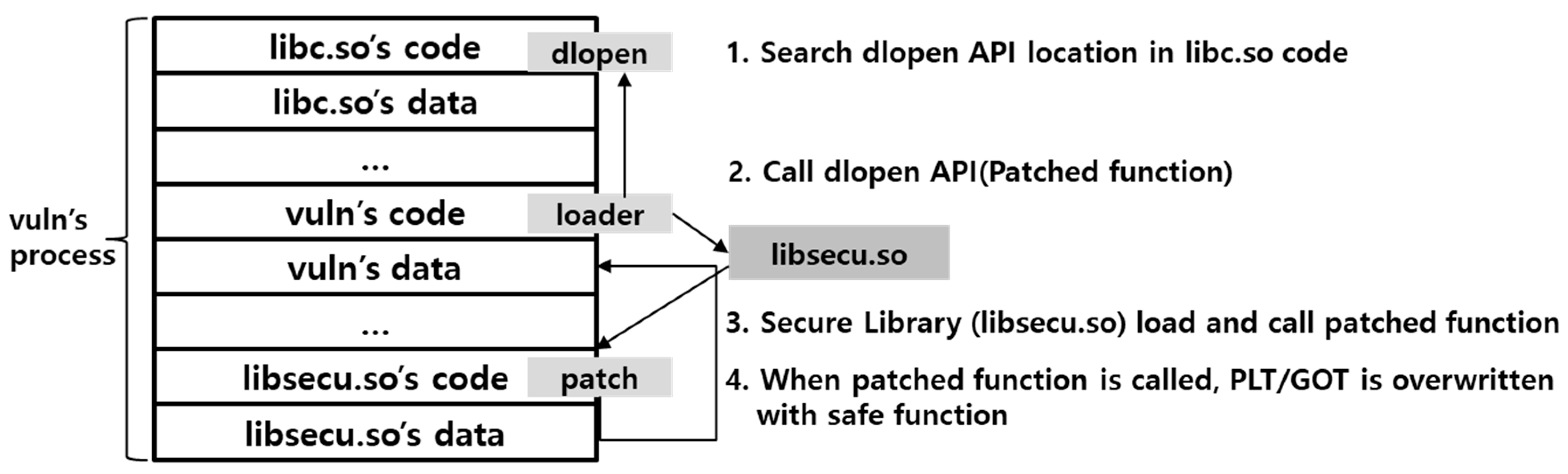
3.5. Automatic Binary Patch
4. Experimental Results
4.1. CFG Recovery Analysis
4.2. Binary Patch Result
5. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
References
- U.S. National Vulnerability Database. Available online: http://cve.mitre.org/cve/ (accessed on 4 April 2018).
- Kang, W.M.; Moon, S.Y.; Park, J.H. An enhanced security framework for home appliances in smart home. Hum.-Centric Comput. Inf. Sci. 2017, 7, 6. [Google Scholar] [CrossRef]
- Keegan, N.; Ji, S.Y.; Chaudhary, A.; Concolato, C.; Yu, B.; Jeong, D.H. A survey of cloud-based network intrusion detection analysis. Hum.-Centric Comput. Inf. Sci. 2016, 6, 19. [Google Scholar] [CrossRef]
- Miller, B.P.; Fredriksen, L.; So, B. An empirical study of the reliability of UNIX utilities. Commun. ACM 1990, 33, 32–44. [Google Scholar] [CrossRef]
- Zzuf—Caca Labs. Available online: http://caca.zoy.org/wiki/zzuf (accessed on 4 April 2018).
- Peach Fuzzer. Available online: https://www.peach.tech/ (accessed on 4 April 2018).
- Sulley. Available online: https://github.com/OpenRCE/sulley (accessed on 4 April 2018).
- Aitel, D. An introduction to SPIKE, the fuzzer creation kit. In Proceedings of the BlackHat USA Conference, Las Vegas, NV, USA, 29 July–1 August 2002. [Google Scholar]
- Bekrar, S.; Bekrar, C.; Groz, R.; Mounier, L. A taint based approach for smart fuzzing. In Proceedings of the IEEE Fifth International Conference on Software Testing, Verification and Validation, Montreal, QC, Canada, 17–21 April 2012; pp. 818–825. [Google Scholar]
- American Fuzzy Lop. Available online: http://lcamtuf.coredump.cx/afl/ (accessed on 4 April 2018).
- Honggfuzz. Available online: https://github.com/google/honggfuzz (accessed on 4 April 2018).
- King, J.C. Symbolic execution and program testing. Commun. ACM 1976, 19, 385–394. [Google Scholar] [CrossRef]
- Godefroid, P.; Levin, M.Y.; Molnar, D.A. Automated whitebox fuzz testing. NDSS 2008, 8, 151–166. [Google Scholar]
- Cadar, C.; Dunbar, D.; Engler, D.R. KLEE: Unassisted and Automatic Generation of High-Coverage Tests for Complex Systems Programs. OSDI 2008, 8, 209–224. [Google Scholar]
- Ciortea, L.; Zamfir, C.; Bucur, S.; Chipounov, V.; Candea, G. Cloud9: A software testing service. ACM SIGOPS Oper. Syst. Rev. 2010, 43, 5–10. [Google Scholar] [CrossRef]
- Cha, S.K.; Avgerinos, T.; Rebert, A.; Brumley, D. Unleashing mayhem on binary code. In Proceedings of the IEEE Symposium on Security and Privacy, San Francisco, CA, USA, 20–23 May 2012; pp. 380–394. [Google Scholar]
- Stephens, N.; Grosen, J.; Salls, C.; Dutcher, A.; Wang, R.; Corbetta, J.; Shoshitaishvili, Y.; Kruegel, C.; Vigna, G. Driller: Augmenting Fuzzing through Selective Symbolic Execution. NDSS 2016, 16, 1–16. [Google Scholar]
- Shoshitaishvili, Y.; Wang, R.; Salls, C.; Stephens, N.; Polino, M.; Dutcher, A.; Grosen, J.; Feng, S.; Hauser, C.; Kruegel, C. Sok: (State of) the art of war: Offensive techniques in binary analysis. In Proceedings of the IEEE Symposium on Security and Privacy, San Jose, CA, USA, 22–26 May 2016; pp. 138–157. [Google Scholar]
- Chipounov, V.; Kuznetsov, V.; Candea, G. S2E: A Platform for In-Vivo Multi-Path Analysis of Software Systems. In Proceedings of the Architectural Support for Programming Langugaes and Operating Systems, Newport Beach, CA, USA, 5–11 March 2011; pp. 265–278. [Google Scholar]
- Stephanie, F.; Thanh, V.N.; Westley, W.; Claire, L.G. A Genetic Programming Approach to, Automated Software Repair. In Proceedings of the 11th Annual Conference on Genetic and Evolutionary Computationm, Montreal, QC, Canada, 8–12 July 2009; pp. 947–954. [Google Scholar]
- Liu, C.; Yang, J.; Tan, L.; Hafiz, M. R2Fix: Automatically generating bug fixes from bug reports. In Proceedings of the International Conference on Software Testing, Verification and Validation, Luxembourg, 18–22 March 2013; pp. 282–291. [Google Scholar]
- Kim, D.; Nam, J.; Song, J.; Kim, S. Automatic patch generation learned from human-written patches. In Proceedings of the International Conference on Software Engineering, San Francisco, CA, USA, 18–26 May 2013; pp. 802–811. [Google Scholar]
- QEMU. Available online: https://www.qemu.org/ (accessed on 4 April 2018).
- Halstead, M.H. Elements of Software Science; Elsevier North-Holland: New York, NY, USA, 1977; p. 128. [Google Scholar]
- DARPA Cyber Grand Challenge. Available online: http://archive.darpa.mil/cybergrandchallenge/ (accessed on 4 April 2018).
- Shudrak, M.O.; Zolotarev, V.V. Improving fuzzing using software complexity metrics. In Proceedings of the International Conference on Information Security and Cryptology, Seoul, Korea, 25–27 November 2015; pp. 246–261. [Google Scholar]
- Mohamed, B.; Smaine, M. A Chi-Square-Based Decision for Real-Time Malware Detection Using PE-File Features. J. Inf. Process. Syst. 2016, 12, 644–660. [Google Scholar]
- Choi, J.H.; Shin, H.S.; Nasridinov, A. A Comparative Study on Data Mining Classification Techniques for Military Applications. J. Converg. 2016, 7, 1–7. [Google Scholar]
- Yamaguchi, F.; Lindner, F.; Rieck, K. Vulnerability extrapolation: Assisted discovery of vulnerabilities using machine learning. In Proceedings of the 5th USENIX conference on Offensive Technologies, San Francisco, CA, USA, 8 August 2011. [Google Scholar]
- Gustavo, G.; Guilermo, L.G.; Lucas, U.; Sanjay, R.; Josselin, F.; Laurent, M. Toward Large-Scale Vulnerability Discovery using Machine Learning. In Proceedings of the Sixth ACM conference on Data and Application Security and Privacy, New Orleans, LA, USA, 9–11 March 2016; pp. 85–96. [Google Scholar]
| Technique | Tool | Testing | Input Generation Strategy |
|---|---|---|---|
| Fuzzing | Zzuf | Blackbox | Mutation Algorithm |
| AFL | Blackbox | Genetic Algorithm | |
| Peach | Blackbox | Format Modeling | |
| Symbolic Execution | Angr | Whitebox | Stepping |
| KLEE | Whitebox | Random Path | |
| S2E | Whitebox | Search Heuristics | |
| Mayhem | Whitebox | Hybrid | |
| Hybrid Fuzzing | Driller | Greybox | Selective |
| Hardening Level | Hardening Technique | Protected Area | Hardening Method |
|---|---|---|---|
| OS-Level Hardening | ASLR | Stack, Heap, Library | Randomize image base |
| DEP | Stack, Heap | Prevent code execution | |
| ASCII-Armor | Library | Insert Null byte | |
| Compiler-Level Hardening | PIE | All | Randomize logical address |
| SSP | Stack | Insert value detecting overflow | |
| RELRO | GOT | Create read-only data area |
| Vulnerability Type | Vulnerable Functions |
|---|---|
| Buffer Overflow | strcpy, wcscpy, stpcpy, wcpcpy, strecpy, memcpy, strcat, wcscat, streadd, strtrns, sprintf, vsprintf, vprintf, vfprintf, gets, scanf, fscanf, vscanf, vsscanf, sscanf, vfscanf, getwd, realpath |
| Format String | syslog, vsyslog, fprintf, printf, sprintf, vfprintf, vprintf, vsprintf, snprintf, vsnprintf, vasprintf, asprintf, vdprintf, dprintf |
| Race Condition | tmpnam, tmpnam_r, mktemp |
| Multiple Command Execution | system, popen, execve, fexecve, execv, execle, execl, execvp, execlp, execvpe |
| Classification | Variable | Description |
|---|---|---|
| Variable | Number of Operators | |
| Number of Operands | ||
| Total Operators | ||
| Total Operands | ||
| Complexity Formula | Program Volume | |
| Program Difficulty | ||
| Effort | ||
| Estimated Bugs |
| Vulnerability Score | Functions |
|---|---|
| 0.5 (Dangerous) | scanf, fscanf, vscanf, vsscanf, sscanf, vfscanf, snprintf, vsnprintf, strtok, wcstok, itoa |
| 1.0 (Banned) | strcpy, wcscpy, stpcpy, wcpcpy, strecpy, memcpy, strcat, wcscat, streadd, strtrns, sprintf, vsprintf, vprintf, vfprintf, gets, getwd, realpath, syslog, vsyslog, fprintf, printf, sprintf, vfprintf, vprintf, vsprintf, vasprintf, asprintf, vdprintf, dprintf |
| Tool | CFG Size (kb) | Min. Binary (s) | Max. Binary (s) | Average Speed (s) |
|---|---|---|---|---|
| Angr (Backward Slicing) | 14,641 | 10.39 | 93.74 | 79.46 |
| Angr (CFG Fast) | 105,007 | 0.87 | 12.037 | 5.12 |
| IDA | 104,779 | 0.18 | 2.33 | 1.82 |
| BARF | 7,367,244 | 1.60 | 192.23 | 63.08 |
| BAP | 323,891 | 0.56 | 36.50 | 1.63 |
| Binary | Test Cases | Crash (Before Patch) | Crash (After Patch) | Removal Rate |
|---|---|---|---|---|
| Lighthttpd | 300 | 13 | 0 | 100% |
| Libhttpd | 420 | 39 | 6 | 85% |
| Abyss | 300 | 18 | 0 | 100% |
| Wsmp3d (low) | 400 | 223 | 30 | 87% |
| Shttpd | 500 | 18 | 15 | 17% |
| Pserv | 300 | 0 | 0 | - |
| Wsmp3d (high) | 400 | 119 | 113 | 6% |
| kritton | 300 | 38 | 31 | 19% |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Jurn, J.; Kim, T.; Kim, H. An Automated Vulnerability Detection and Remediation Method for Software Security. Sustainability 2018, 10, 1652. https://doi.org/10.3390/su10051652
Jurn J, Kim T, Kim H. An Automated Vulnerability Detection and Remediation Method for Software Security. Sustainability. 2018; 10(5):1652. https://doi.org/10.3390/su10051652
Chicago/Turabian StyleJurn, Jeesoo, Taeeun Kim, and Hwankuk Kim. 2018. "An Automated Vulnerability Detection and Remediation Method for Software Security" Sustainability 10, no. 5: 1652. https://doi.org/10.3390/su10051652
APA StyleJurn, J., Kim, T., & Kim, H. (2018). An Automated Vulnerability Detection and Remediation Method for Software Security. Sustainability, 10(5), 1652. https://doi.org/10.3390/su10051652





