Identity Leakage in Encrypted IM Call Services: An Empirical Study of Metadata Correlation
Abstract
1. Introduction
- This paper formulates a realistic ISP-level threat model to assess privacy risks in IM call services, explicitly accounting for adversary capabilities alongside practical real-world challenges, including encrypted communication, massive user scale, and cross-network synchronization.
- A systematic analysis framework is proposed that synergistically integrates six analysis dimensions, including endpoint identifiability, common server connectivity, service type characteristics, and symmetries in call duration and traffic volume, and signaling artifacts to effectively correlate encrypted call sessions.
- Robust empirical evidence, derived from extensive experiments analyzing bilateral traffic records across heterogeneous network architectures, diverse usage scenarios involving role-swapping, and multiple major IM applications, demonstrates that metadata analysis can reliably reveal communication relationships and edges in user social networks, highlighting a persistent privacy vulnerability under current data retention regimes.
2. Related Works
2.1. Network Traffic Analysis and Classification
2.2. Data Retention Practices
2.3. Encrypted Traffic Analysis and Privacy Leakage
2.4. Threat Model
2.4.1. Adversary Capabilities
- 5-tuple information: The adversary observes the source and destination IP addresses, source and destination ports, and the transport protocol.
- Timing and volume: The adversary records precise timestamps for flow start and end times, flow durations, and volumetric statistics, including packet or byte counts.
- User-IP mapping logs: CG-NAT generally obscures user identities behind shared public IP addresses [52], ISPs maintain internal mapping logs linking subscribers to transient IP addresses for commercial and operational purposes, specifically for data usage billing. Law enforcement agencies can request these records through legal processes to resolve the subscriber identity associated with a specific public IP and port combination.
- Unencrypted packet content: While application payloads are generally encrypted, the adversary can inspect any unencrypted packet content using ISP-deployed DPI tools or lawful interception infrastructures [53,54,55]. This capability is not limited to basic headers but includes any unencrypted artifacts, such as DNS queries, Server Name Indication (SNI), or Session Traversal Utilities for NAT (STUN) attributes, that may reveal service types or assist in identifying communication endpoints.
2.4.2. Practical Challenges for the Adversary
- Encrypted signaling and payload: Consistent with Section 2.1, communication content is end-to-end encrypted. Consequently, IM call signaling is also encrypted, preventing the adversary from retrieving call party information directly from packet payloads.
- Massive user base and traffic volume: As detailed in Section 2.2, platforms such as WhatsApp have an estimated 100 million monthly active users in the United States alone. The immense volume of users and their generated traffic poses a formidable challenge for re-identification. This massive scale of concurrent events makes isolating specific caller-callee pairs akin to finding a needle in a haystack.
- Cross-network time alignment: Callers and callees frequently traverse different ISP networks or are recorded by different logging nodes. Clock skews, network jitter, and imperfect synchronization introduce timestamp discrepancies between vantage points. Because perfect alignment of flow start and end times cannot be assumed, the adversary must tolerate temporal uncertainty when attempting to match caller and callee sessions.
- Targeted retention regime: Reflecting the privacy perspectives in Section 2.3, the adversary may operate under targeted retention rather than indiscriminate bulk retention. In such settings, high-granularity logging is activated only for specific subscribers, IP ranges, time windows, or services, rather than stored for all users indefinitely. A central question addressed by this study is whether significant privacy leakage still persists under these constrained observation conditions.
2.4.3. Attack Goal
3. Methodology
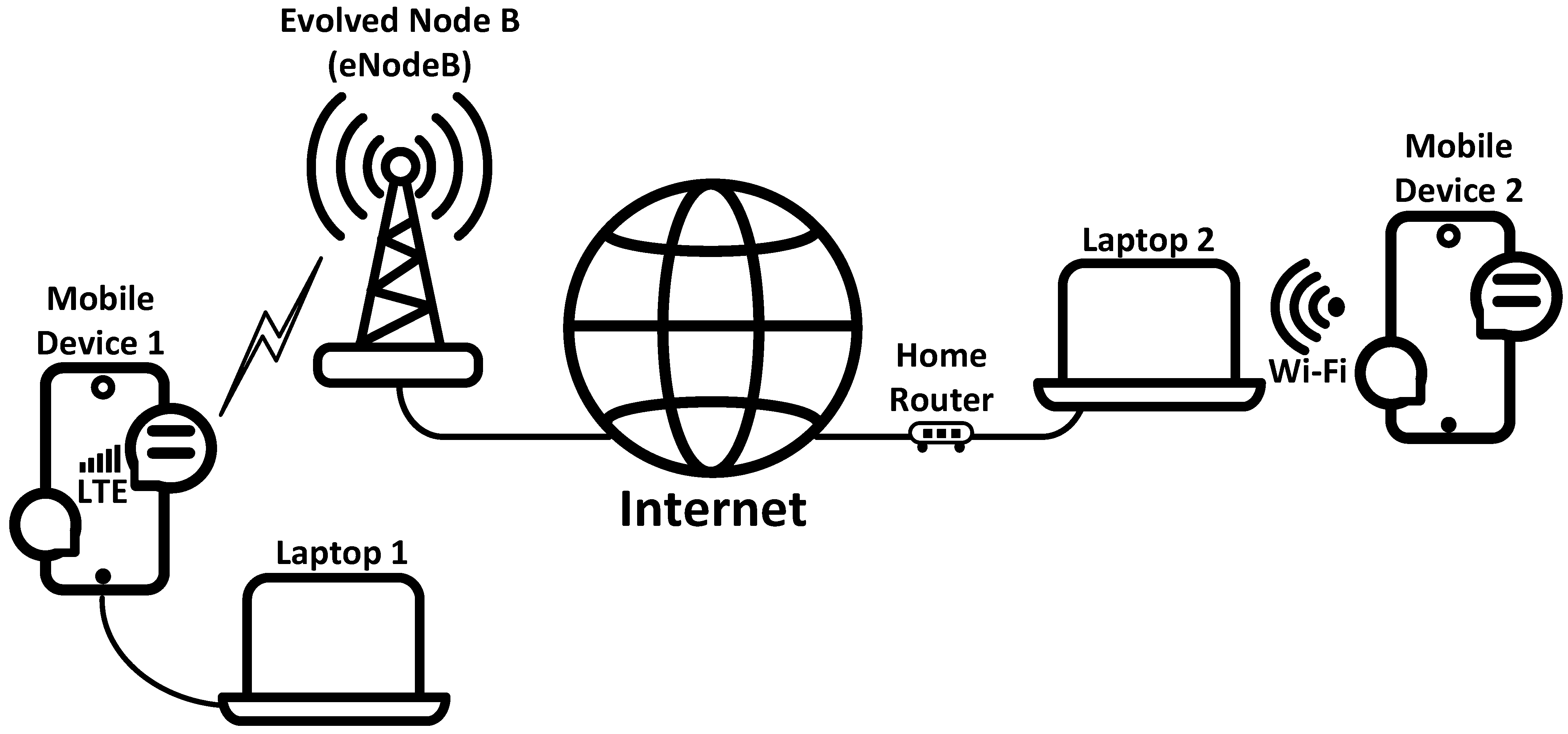
3.1. Experimental Setup
3.2. Call Behavior Scenarios and Experimental Procedure
- Caller-initiated cancellation: The callee does not answer, and the caller manually cancels the call.
- Callee-initiated rejection: The callee does not answer and manually rejects the incoming call.
- System timeout termination: The callee does not respond, and the system automatically terminates the call after a timeout period.
- Caller-terminated conversation: The callee answers the call, and the caller terminates the call.
- Callee-terminated conversation: The callee answers the call, and the callee terminates the call.
- Launch the IM application on caller device and open the chat interface.
- Maintain both devices in an idle state for several seconds to minimize background traffic.
- Initiate synchronized traffic capture on both the caller and callee devices. If excessive background traffic is detected, restart the capture to ensure data integrity.
- Execute the designated behavioral scenario according to the experimental plan.
- Stop the traffic capture and store the traffic for subsequent analysis.
3.3. Multi-Dimensional Correlation Framework
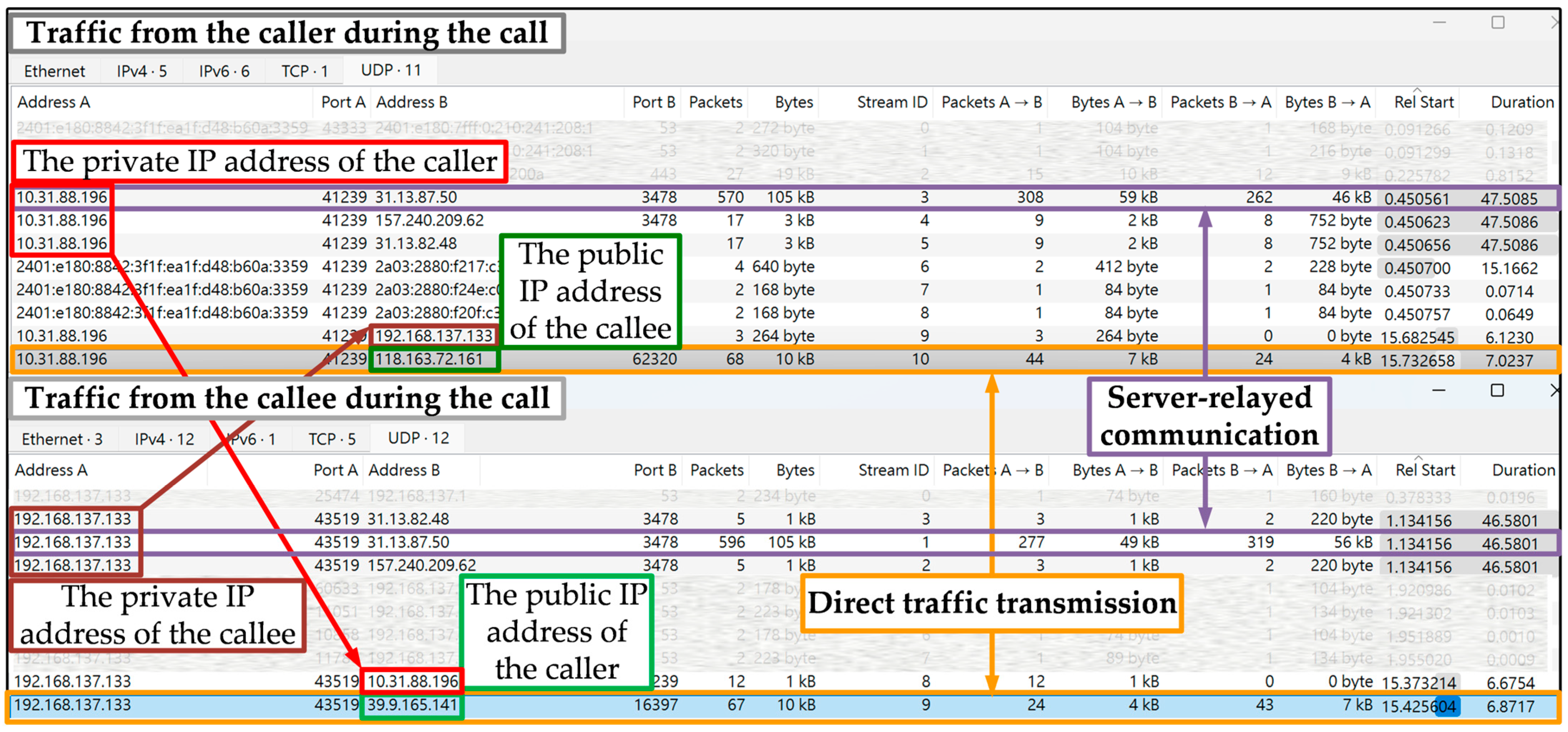
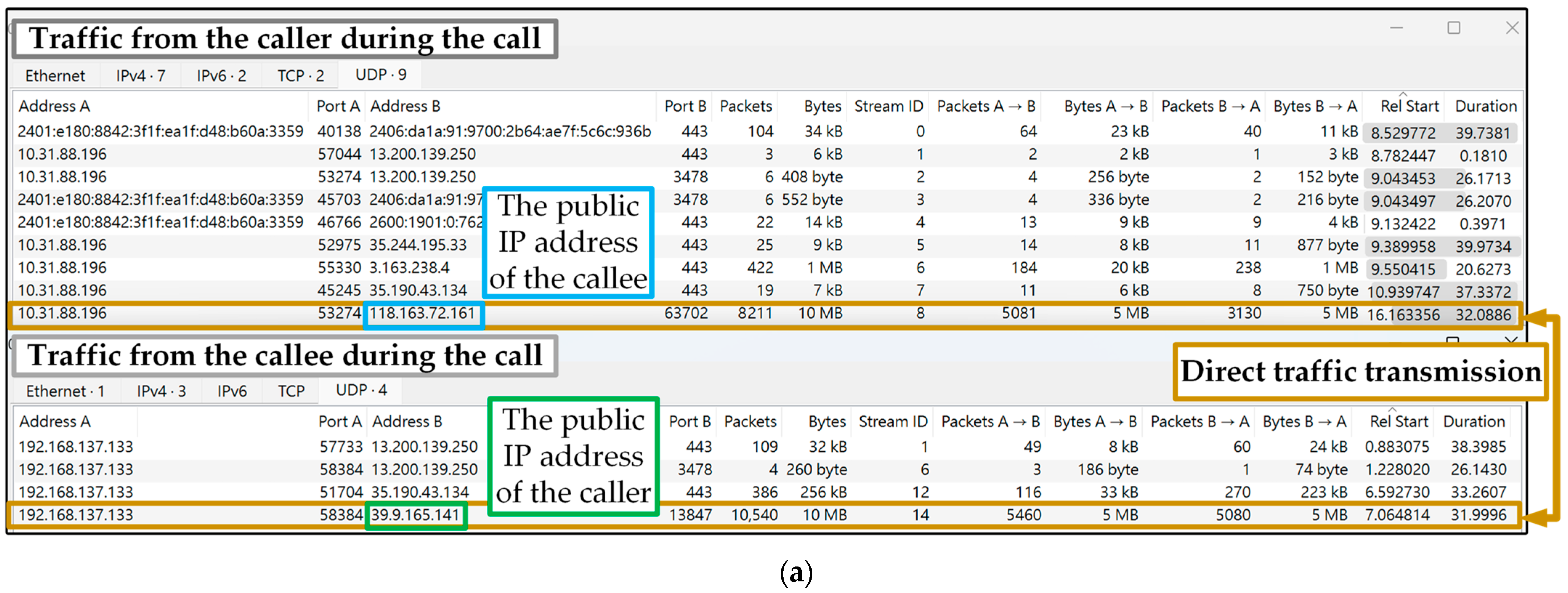
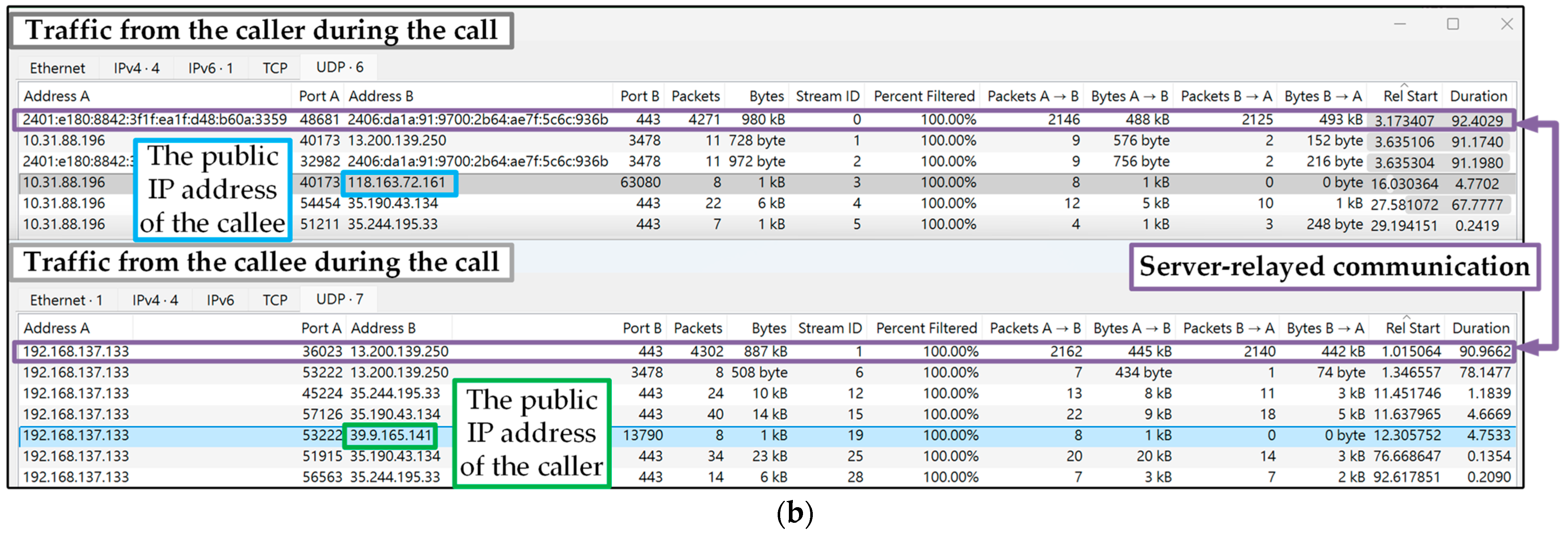
- Endpoint Identifiability: This dimension investigates the visibility of legitimate endpoint IP addresses exposed during connection establishment. Since communicating endpoints often reside behind restrictive network environments, such as mobile networks employing CG-NAT or Wi-Fi networks behind standard NAT, IM applications must employ protocol negotiation to establish connectivity. The analysis assesses whether identifiers are disclosed during this negotiation process, which serves as a primary vector for leakage, or within the resulting traffic topologies. Disclosure, whether inherent in peer-to-peer sessions or inadvertent in server-relayed traffic, enables the direct mapping of network identifiers to physical subscriber identities.
- Server Connectivity: This dimension analyzes concurrent connections to shared relay infrastructure, serving as a critical alternative when direct endpoint identification is unattainable. Since call initiation mandates simultaneous signaling and media sessions from both the caller and callee to specific application servers, monitoring these synchronized connections enables the detection of active call status. By correlating subscribers who establish concurrent sessions to the same server IP address, this metric significantly reduces the anonymity set, thereby isolating potential communicating pairs from the vast background traffic pool.
- Call Duration Symmetry: This dimension quantifies the temporal alignment of flow start and end times between the caller and callee. This metric serves as a vital filter to resolve the ambiguity presented by concurrent connections to shared relay servers. Given the synchronized nature of signaling and media exchanges inherent to real-time communication, the start and end timestamps of the paired flows exhibit high correlation. Despite minor temporal variations introduced by network jitter or signaling delays, this strong temporal consistency is crucial for isolating the true communication pair from a large anonymity set.
- Traffic Volume Symmetry: This dimension evaluates the volumetric consistency between the traffic transmitted by the caller and received by the callee, and vice versa. This analysis provides a critical second filter to further refine the ambiguity remaining after temporal correlation. Given the bidirectional exchange of media, packet counts and byte volumes between the paired flows are expected to be approximately equivalent. Although network factors such as MTU differences, fragmentation, or packet loss introduce minor discrepancies, the overall volumetric balance provides a robust signature for confirming bilateral flow correlation.
- Service Type Characteristics: This dimension differentiates the traffic patterns associated with voice versus video modalities. Distinctions in traffic volume and behavioral signatures between service types allow for more granular fingerprinting and assessment of privacy risks.
- Signaling Artifacts: This dimension extracts supplementary protocol-specific patterns, such as variations in user behavior or application-specific signaling features (e.g., STUN usernames), found in unencrypted phases. These artifacts provide irrefutable evidence that further strengthens potential privacy implications.
4. Experiment Results
4.1. Endpoint Identifiability
4.2. Server Connectivity
4.3. Call Duration Symmetry
4.4. Traffic Symmetry
4.5. Service Type
4.6. Signaling Artifacts
- WhatsApp
- 2.
- Facebook Messenger
- 3.
- Snapchat
4.7. Discussion
5. Conclusions
Funding
Data Availability Statement
Conflicts of Interest
References
- David Curry Messaging App Revenue and Usage Statistics (2025)-Business of Apps. Available online: https://www.businessofapps.com/data/messaging-app-market/ (accessed on 27 September 2025).
- Laura Ceci Mobile Messenger and Communication Apps-Statistics & Facts. Available online: https://www.statista.com/topics/1523/mobile-messenger-apps/?srsltid=AfmBOoryHFFyL16fq6uj4CCHLhvPmSbHBVe7O8DWe-7_xygcZk0CVy8I#topicOverview (accessed on 29 September 2025).
- Karpisek, F.; Baggili, I.; Breitinger, F. WhatsApp Network Forensics: Decrypting and Understanding the WhatsApp Call Signaling Messages. Digit. Investig. 2015, 15, 110–118. [Google Scholar] [CrossRef]
- Tsai, F.-C.; Chang, E.-C.; Kao, D.-Y. WhatsApp Network Forensics: Discovering the Communication Payloads behind Cybercriminals. In Proceedings of the 2018 20th International Conference on Advanced Communication Technology (ICACT), Chuncheon, Republic of Korea, 11–14 February 2018; IEEE: New York, NY, USA, 2018; pp. 679–684. [Google Scholar]
- Ahmed, W.; Shahzad, F.; Javed, A.R.; Iqbal, F.; Ali, L. WhatsApp Network Forensics: Discovering the IP Addresses of Suspects. In Proceedings of the 2021 11th IFIP International Conference on New Technologies, Mobility and Security, NTMS 2021, Paris, France, 19–21 April 2021. [Google Scholar] [CrossRef]
- Afzal, A.; Hussain, M.; Saleem, S.; Shahzad, M.K.; Ho, A.T.S.; Jung, K.H. Encrypted Network Traffic Analysis of Secure Instant Messaging Application: A Case Study of Signal Messenger App. Appl. Sci. 2021, 11, 7789. [Google Scholar] [CrossRef]
- Rathi, K.; Karabiyik, U.; Aderibigbe, T.; Chi, H. Forensic Analysis of Encrypted Instant Messaging Applications on Android. In Proceedings of the 6th International Symposium on Digital Forensic and Security, ISDFS 2018-Proceeding, Antalya, Turkey, 22–25 March 2018; Institute of Electrical and Electronics Engineers Inc.: New York, NY, USA, 2018; Volume 2018, pp. 1–6. [Google Scholar]
- Zhang, H.; Chen, L.; Liu, Q. Digital Forensic Analysis of Instant Messaging Applications on Android Smartphones. In Proceedings of the 2018 International Conference on Computing, Networking and Communications (ICNC), Maui, HI, USA, 5–8 March 2018; IEEE: New York, NY, USA, 2018; pp. 647–651. [Google Scholar]
- Choi, J.; Yu, J.; Hyun, S.; Kim, H. Digital Forensic Analysis of Encrypted Database Files in Instant Messaging Applications on Windows Operating Systems: Case Study with KakaoTalk, NateOn and QQ Messenger. Digit Investig. 2019, 28, S50–S59. [Google Scholar] [CrossRef]
- Keshvadi, S.; Karamollahi, M.; Williamson, C. Traffic Characterization of Instant Messaging Apps: A Campus-Level View. In Proceedings of the Conference on Local Computer Networks, LCN, Sydney, Australia, 16–19 November 2020; IEEE Computer Society: Sydney, Australia, 2020; Volume 2020, pp. 225–232. [Google Scholar]
- Coull, S.E.; Dyer, K.P. Traffic Analysis of Encrypted Messaging Services. ACM SIGCOMM Comput. Commun. Rev. 2014, 44, 5–11. [Google Scholar] [CrossRef]
- IT-Political Association of Denmark Published Written Evidence (IPB0051) of Investigatory Powers Bill. Available online: http://data.parliament.uk/WrittenEvidence/CommitteeEvidence.svc/EvidenceDocument/Science and Technology/Investigatory Powers Bill Technology issues/written/25190.html (accessed on 25 June 2025).
- Sandvine Must Make Good on Its Commitments and Stop Harming Human Rights. Available online: https://www.accessnow.org/press-release/joint-letter-to-sandvine-on-announced-reforms/ (accessed on 30 November 2025).
- Bill, M.; Jakub, D.; Sarah, M.; Adam, S.; John, S.-R.; Ron, D. BAD TRAFFIC: Sandvine’s PacketLogic Devices Used to Deploy Government Spyware in Turkey and Redirect Egyptian Users to Affiliate Ads? Available online: https://citizenlab.ca/2018/03/bad-traffic-sandvines-packetlogic-devices-deploy-government-spyware-turkey-syria/ (accessed on 30 November 2025).
- U.S. Blocklists Sandvine for Enabling Digital Repression in Egypt. Available online: https://www.accessnow.org/press-release/us-blocklists-sandvine-for-digital-repression-in-egypt/ (accessed on 30 November 2025).
- Global Deep Packet Inspection (DPI) Industry Report 2024-2030: DPI Deployments Soar amid Growing Emphasis on Network Security. Available online: https://finance.yahoo.com/news/global-deep-packet-inspection-dpi-083600291.html (accessed on 30 November 2025).
- A Massive Database of 8 Billion Thai Internet Records Leaks. Available online: https://techcrunch.com/2020/05/24/thai-billions-internet-records-leak/ (accessed on 27 September 2025).
- The UK Home Office Home Office Report on the Operation of the Investigatory Powers Act 2016 (Accessible Version). Available online: https://www.gov.uk/government/publications/report-on-the-operation-of-the-investigatory-powers-act-2016/home-office-report-on-the-operation-of-the-investigatory-powers-act-2016-accessible-version#chapter-2-review-outcomes (accessed on 19 February 2025).
- Joined Cases C-793/19 and C-794/19 SpaceNet and Telekom Deutschland ECLI:EU:C:2022:702 (‘SpaceNet’). Available online: https://curia.europa.eu/juris/document/document.jsf?text=&docid=265881&pageIndex=0&doclang=EN&mode=req&dir=&occ=first&part=1&cid=623107#Footnote* (accessed on 25 June 2025).
- Hofstede, R.; Čeleda, P.; Trammell, B.; Drago, I.; Sadre, R.; Sperotto, A.; Pras, A. Flow Monitoring Explained: From Packet Capture to Data Analysis with NetFlow and IPFIX. IEEE Commun. Surv. Tutor. 2014, 16, 2037–2064. [Google Scholar] [CrossRef]
- Cherukuri, A.K.; Ikram, S.T.; Li, G.; Liu, X. Encrypted Network Traffic Analysis; Springer: Berlin/Heidelberg, Germany, 2024. [Google Scholar]
- Naboulsi, D.; Fiore, M.; Ribot, S.; Stanica, R. Large-Scale Mobile Traffic Analysis: A Survey. IEEE Comm. Surv. Tutor. 2016, 18, 124–161. [Google Scholar] [CrossRef]
- Lin, P.; Ye, K.; Hu, Y.; Lin, Y.; Xu, C.Z. A Novel Multimodal Deep Learning Framework for Encrypted Traffic Classification. IEEE/ACM Trans. on Netw. 2023, 31, 1369–1384. [Google Scholar] [CrossRef]
- Pathmaperuma, M.H.; Rahulamathavan, Y.; Dogan, S.; Kondoz, A.M. Deep Learning for Encrypted Traffic Classification and Unknown Data Detection. Sensors 2022, 22, 7643. [Google Scholar] [CrossRef]
- Shen, M.; Ye, K.; Liu, X.; Zhu, L.; Kang, J.; Yu, S.; Li, Q.; Xu, K. Machine Learning-Powered Encrypted Network Traffic Analysis: A Comprehensive Survey. IEEE Commun. Surv. Tutor. 2023, 25, 791–824. [Google Scholar] [CrossRef]
- Papadogiannaki, E.; Ioannidis, S. A Survey on Encrypted Network Traffic Analysis Applications, Techniques, and Countermeasures. ACM Comput. Surv. (CSUR) 2021, 54, 1–35. [Google Scholar] [CrossRef]
- Alblooshi, A.; Aljneibi, N.; Iqbal, F.; Ikuesan, R.; Badra, M.; Khalid, Z. Smartphone Forensics: A Comparative Study of Common Mobile Phone Models. In Proceedings of the 12th International Symposium on Digital Forensics and Security, San Antonio, TX, USA, 29–30 April 2024. [Google Scholar] [CrossRef]
- Sarhan, S.A.E.; Youness, H.A.; Bahaa-Eldin, A.M.; Taha, A.E. VoIP Network Forensics of Instant Messaging Calls. IEEE Access 2024, 12, 9012–9024. [Google Scholar] [CrossRef]
- Prabowo, W.A.; Mohsen, F.; Selamat, S.R. WhatsApp Mobile Applications in the Lens of Digital Forensics: Deciphering the Msgstore.Db.Crypt14 File. J. Cyber Secur. Mobil. 2025, 14, 823–848. [Google Scholar] [CrossRef]
- Trammell, B.; Boschi, E. An Introduction to IP Flow Information Export (IPFIX). IEEE Commun. Mag. 2011, 49, 89–95. [Google Scholar] [CrossRef]
- Finsterbusch, M.; Richter, C.; Rocha, E.; Müller, J.A.; Hänßgen, K. A Survey of Payload-Based Traffic Classification Approaches. IEEE Commun. Surv. Tutor. 2014, 16, 1135–1156. [Google Scholar] [CrossRef]
- Sherry, J.; Lan, C.; Ada Popa ETH Zürich, R.; Berkeley Sylvia Ratnasamy, U. BlindBox: Deep Packet Inspection over Encrypted Traffic. In Proceedings of the ACM SIGCOMM Computer Communication Review 45, Coimbra, Portugal, 8–11 September 2025. [Google Scholar] [CrossRef]
- WhatsApp User Statistics 2025: How Many People Use WhatsApp? Available online: https://backlinko.com/whatsapp-users (accessed on 28 September 2025).
- Danish Administrative Order for Data Retention (Logningsbekendtgørelsen). Available online: https://www.retsinformation.dk/eli/lta/2006/988 (accessed on 25 June 2025).
- Comparison of Internet Connection Records in the Investigatory Powers Bill with Danish Internet Session Logging Legislation. 2016. Available online: https://assets.publishing.service.gov.uk/media/5a81b29840f0b62302698b3c/Comparison_of_ICRs_with_Danish_Session_Logging.pdf (accessed on 25 June 2025).
- Investigatory Powers Act 2016. 2016. Available online: https://www.legislation.gov.uk/ukpga/2016/25/contents (accessed on 25 June 2025).
- Operational Case for the Retention of Internet Connection Records. 2015. Available online: https://assets.publishing.service.gov.uk/media/5a751224e5274a3cb28696be/Operational_Case_for_the_Retention_of_Internet_Connection_Records_-_IP_Bill_introduction.pdf (accessed on 25 June 2025).
- Annual Report of the Investigatory Powers Commissioner 2019. 2020. Available online: https://ipco-wpmedia-prod-s3.s3.eu-west-2.amazonaws.com/IPC-Annual-Report-2019_Web-Accessible-version_final.pdf (accessed on 25 June 2025).
- Investigatory Powers Bill Factsheet–Internet Connection Records; The UK Government: London, UK, 2015.
- Wang, Q.; Yahyavi, A.; Kemme, B.; He, W. I Know What You Did on Your Smartphone: Inferring App Usage over Encrypted Data Traffic. In Proceedings of the 2015 IEEE Conference on Communications and Network Security, Florence, Italy, 28–30 September 2015; pp. 433–441. [Google Scholar] [CrossRef]
- Taylor, V.F.; Spolaor, R.; Conti, M.; Martinovic, I. Robust Smartphone App Identification via Encrypted Network Traffic Analysis. IEEE Trans. on Infor. Foren. Secur. 2018, 13, 63–78. [Google Scholar] [CrossRef]
- Aceto, G.; Ciuonzo, D.; Montieri, A.; Pescapé, A. Multi-Classification Approaches for Classifying Mobile App Traffic. J. Netw. Comput. Appl. 2018, 103, 131–145. [Google Scholar] [CrossRef]
- Wang, S.; Chen, Z.; Zhang, L.; Yan, Q.; Yang, B.; Peng, L.; Jia, Z. TrafficAV: An Effective and Explainable Detection of Mobile Malware Behavior Using Network Traffic. In Proceedings of the 2016 IEEE/ACM 24th International Symposium on Quality of Service, Beijing, China, 20-21 June 2016. [Google Scholar] [CrossRef]
- Wijesekera, P.; Baokar, A.; Hosseini, A.; Egelman, S.; Wagner, D.; Beznosov, K. Android Permissions Remystified: A Field Study on Contextual Integrity. In Proceedings of the 24th USENIX Security Symposium 2015, Washington, DC, USA, 12–14 August 2015; pp. 499–514. [Google Scholar]
- Xu, S.; Sen, S.; Morley Mao, Z. CSI: Inferring Mobile ABR Video Adaptation Behavior under HTTPS and QUIC. In Proceedings of the 15th European Conference on Computer Systems, EuroSys 2020, Heraklion, Greece, 27–30 April 2020; p. 16. [Google Scholar] [CrossRef]
- Lopez-Martin, M.; Carro, B.; Sanchez-Esguevillas, A.; Lloret, J. Network Traffic Classifier with Convolutional and Recurrent Neural Networks for Internet of Things. IEEE Access 2017, 5, 18042–18050. [Google Scholar] [CrossRef]
- He, Q.; Moayyedi, A.; Dan, G.; Koudouridis, G.P.; Tengkvist, P. A Meta-Learning Scheme for Adaptive Short-Term Network Traffic Prediction. IEEE J. Sel. Areas Commun. 2020, 38, 2271–2283. [Google Scholar] [CrossRef]
- Yang, C.; Xiong, G.; Zhang, Q.; Shi, J.; Gou, G.; Li, Z.; Liu, C. Few-Shot Encrypted Traffic Classification via Multi-Task Representation Enhanced Meta-Learning. Comput. Netw. 2023, 228, 109731. [Google Scholar] [CrossRef]
- Hu, Y.; Wu, J.; Li, G.; Li, J.; Cheng, J. Privacy-Preserving Few-Shot Traffic Detection Against Advanced Persistent Threats via Federated Meta Learning. IEEE Trans. Netw. Sci. Eng. 2024, 11, 2549–2560. [Google Scholar] [CrossRef]
- Zhao, J.; Li, Q.; Hong, Y.; Shen, M. MetaRockETC: Adaptive Encrypted Traffic Classification in Complex Network Environments via Time Series Analysis and Meta-Learning. IEEE Trans. Netw. Serv. Man. 2024, 21, 2460–2476. [Google Scholar] [CrossRef]
- Feng, Y.; Li, J.; Mirkovic, J.; Wu, C.; Wang, C.; Ren, H.; Xu, J.; Liu, Y. Unmasking the Internet: A Survey of Fine-Grained Network Traffic Analysis. IEEE Commun. Surv. Tutor. 2025, 27, 3672–3709. [Google Scholar] [CrossRef]
- ETSITR 103 829-V1.1.1; Lawful Interception (LI); IP Address Retention and Traceability. ETSI: Sophia Antipolis, France, 2022.
- Lawful Interception. Available online: https://netquestcorp.com/lawful-intercept/ (accessed on 6 December 2025).
- Lawful Interception Solutions. Available online: https://www.ips-intelligence.com/en/lawful-interception (accessed on 6 December 2025).
- Bąkowski, P. Access to Data for Law Enforcement: Lawful Interception; European Parliament: Brussels, Belgium, July 2025. [Google Scholar]








| Experimental Devices/Tools | Description | Specification/Versions |
|---|---|---|
| Mobile Device 1 | Generate IM network traffic and capture from the mobile network directly | Google Pixel 6 Android 16 Magisk v29.0 (for root access) Android tcpdump 4.99.5 Network Analyzer 4.1 Connectivity: Commercial LTE Network (Operator A) |
| Mobile Device 2 | Generate IM network traffic | Google Pixel 6 Pro Android 16 Network Analyzer 4.1 |
| Laptop 1 | Control Android tcpdump on Mobile Device 1 and analyze the captured traffic | Dell Inspiron 16 Plus 7610 Microsoft Windows 11 Pro Android Debug Bridge 1.0.41 Wireshark 4.4.6 |
| Laptop 2 | Provide Wi-Fi hotspot to Mobile Device 2 and capture traffic; analyze captured traffic | HP ZBook Power G10 Microsoft Windows 11 Pro Wireshark 4.4.6 |
| Home Router | Provide Internet connectivity for Laptop 2 | TP-Link Deco X10 Connectivity: Fixed Broadband Network (Operator B) |
| Application | Version | Supported Call Services |
|---|---|---|
| 2.25.26.74 | Voice, Video | |
| Facebook Messenger | 526.0.0.52.108 | Voice, Video |
| Snapchat | 13.60.0.57 | Voice, Video |
| Scenarios | Facebook Messenger | Snapchat | |
|---|---|---|---|
| Caller-initiated cancellation | No disclosure (12/12) | Caller’s public and private IP is visible in callee’s traffic (12/12). | No disclosure (12/12) |
| Callee-initiated rejection | No disclosure (12/12) | Caller’s public and private IP is visible in callee’s traffic (12/12). | No disclosure (12/12) |
| System timeout termination | No disclosure (12/12) | Caller’s public and private IP is visible in callee’s traffic (12/12). | No disclosure (12/12) |
| Caller-terminated conversation |
|
|
|
| Callee-terminated conversation |
|
|
|
| Application | Observed Server Addresses | Observed Ports |
|---|---|---|
| 31.13.87.50 | 3478 | |
| 157.240.209.62 | ||
| 31.13.82.48 | ||
| Facebook Messenger | 31.13.87.2 | 3478, 40003 |
| 31.13.87.54 | ||
| 31.13.87.128 | ||
| 157.240.31.57 | ||
| 157.240.209.57 | ||
| Snapchat | 13.200.139.250 | 443, 3478 |
| 35.190.43.134 | ||
| 35.244.195.33 |
| Host Name | IP Address |
|---|---|
| edge-turnservices6-shv-01-tpe1.facebook.com | 2a03:2880:f217:c0:face:b00c:0:553e |
| edge-turnservices-shv-01-tpe1.facebook.com | 31.13.87.54 |
| edgeray-msgr6-shv-01-tpe1.facebook.com | 2a03:2880:f217:ce:face:b00c:0:74fd |
| edgeray-msgr-shv-01-tpe1.facebook.com | 31.13.87.128 |
| edgeray-msgr6-shv-01-itm1.facebook.com | 2a03:2880:f24e:cd:face:b00c:0:74fd |
| edgeray-msgr-shv-01-itm1.facebook.com | 157.240.209.57 |
| edgeray-msgr6-shv-01-nrt1.facebook.com | 2a03:2880:f20f:1ce:face:b00c:0:74fd |
| edgeray-msgr-shv-01-nrt1.facebook.com | 157.240.31.57 |
| Application | Caller Device | Voice Call | Video Call | ||
|---|---|---|---|---|---|
| Absolute (s) | Normalized | Absolute (s) | Normalized | ||
| Device 1 | 0.894 (1.735) [0.068, 2.519] | 0.020 (0.014) [0, 0.109] | 1.284 (1.479) [0.0588, 2.548] | 0.021 (0.021) [0.001, 0.143] | |
| Device 2 | 1.242 (0.502) [0.294, 1.941] | 0.037 (0.068) [0.003, 0.273] | 1.663 (0.922) [0.725, 2.743] | 0.031 (0.049) [0.008, 0.288] | |
| Facebook Messenger | Device 1 | 1.155 (0.869) [0.038, 2.510] | 0.021 (0.043) [0.004, 0.220] | 1.249 (0.841) [0.388, 2.439] | 0.017 (0.097) [0.006, 0.238] |
| Device 2 | 2.493 (3.578) [0.868, 11.492] | 0.101 (0.096) [0.022, 0.152] | 2.030 (5.038) [0.688, 12.149] | 0.058 (0.102) [0.012, 0.219] | |
| Snapchat | Device 1 | 1.352 (1.01) [0.898, 2.384] | 0.025 (0.039) [0.008, 0.453] | 1.309 (0.693) [0.089, 3.235] | 0.029 (0.038) [0.001, 0.084] |
| Device 2 | 1.184 (0.647) [0.060, 2.468] | 0.024 (0.054) [0.001, 0.195] | 1.096 (1.243) [0.229, 2.254] | 0.019 (0.045) [0.002, 0.161] | |
| Application | Caller Device | Voice Call | Video Call | ||
|---|---|---|---|---|---|
| Absolute (Packets) | Normalized | Absolute (Packets) | Normalized | ||
| Device 1 | 1 (0.25) [1, 2] | 0.004 (0.037) [0.001, 0.056] | 14 (38) [3, 44] | 0.003 (0.004) [0.001, 0.006] | |
| Device 2 | 12 (6) [7, 19] | 0.014 (0.088) [0.006, 0.107] | 21.5 (53) [0, 71] | 0.012 (0.024) [0, 0.042] | |
| Facebook Messenger | Device 1 | 1 (17) [0, 53] | 0.015 (0.039) [0, 0.040] | 20 (312) [1, 621] | 0.016 (0.064) [0, 0.077] |
| Device 2 | 19.5 (13) [5, 27] | 0.008 (0.049) [0.003, 0.083] | 32 (688.5) [12, 2622] | 0.018 (0.143) [0.003, 0.181] | |
| Snapchat | Device 1 | 10 (27.75) [3, 33] | 0.003 (0.013) [0.001, 0.043] | 1021 (1567.75) [42, 2329] | 0.067 (0.040) [0.041, 0.124] |
| Device 2 | 5 (7.75) [1, 11] | 0.003 (0.002) [0.002, 0.005] | 1405 (1856) [16, 2276] | 0.073 (0.065) [0, 0.130] | |
| Application | Caller Device | Voice Call | Video Call | ||
|---|---|---|---|---|---|
| Absolute (KB) | Normalized | Absolute (KB) | Normalized | ||
| Device 1 | 0.05 (1.25) [0, 2] | 0.003 (0.013) [0, 0.037] | 21 (30.75) [3, 42] | 0.004 (0.005) [0.001,0.006] | |
| Device 2 | 1 (2.25) [1, 4] | 0.020 (0.078) [0.003, 0.111] | 13 (10.25) [1, 3] | 0.0038 (0.013) [0.003, 0.025] | |
| Facebook Messenger | Device 1 | 1 (4.8) [0, 20] | 0.007 (0.064) [0, 0.067] | 7 (42) [0, 61] | 0.007 (0.042) [0, 0.222] |
| Device 2 | 7 (6.5) [1, 9] | 0.019 (0.0832) [0.003, 0.189] | 8 (15) [0, 84] | 0.004 (0.159) [0.002, 0.415] | |
| Snapchat | Device 1 | 42 (65.5) [6, 94] | 0.053 (0.013) [0.028, 0.060] | 82 (153) [2, 223] | 0.011 (0.004) [0.004, 0.014] |
| Device 2 | 3 (6.25) [1, 17] | 0.010 (0.064) [0.004, 0.070] | 34 (124.25) [4, 182] | 0.013 (0.036) [0.005, 0.097] | |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Li, C.-Y. Identity Leakage in Encrypted IM Call Services: An Empirical Study of Metadata Correlation. Future Internet 2026, 18, 12. https://doi.org/10.3390/fi18010012
Li C-Y. Identity Leakage in Encrypted IM Call Services: An Empirical Study of Metadata Correlation. Future Internet. 2026; 18(1):12. https://doi.org/10.3390/fi18010012
Chicago/Turabian StyleLi, Chen-Yu. 2026. "Identity Leakage in Encrypted IM Call Services: An Empirical Study of Metadata Correlation" Future Internet 18, no. 1: 12. https://doi.org/10.3390/fi18010012
APA StyleLi, C.-Y. (2026). Identity Leakage in Encrypted IM Call Services: An Empirical Study of Metadata Correlation. Future Internet, 18(1), 12. https://doi.org/10.3390/fi18010012







