Blockchain Technology: Benefits, Challenges, Applications, and Integration of Blockchain Technology with Cloud Computing
Abstract
1. General Introduction to Blockchain Technology
Blockchain Evolution
2. Main Highlights of the Work
- 1.
- The paper reviews blockchain technology in detail, including applications of blockchain technology and evolution.
- 2.
- The paper highlights blockchain technology’s critical challenges, and this study suggests a few solutions.
- 3.
- The paper describes blockchain technology in the transaction system and its cryptocurrencies.
- 4.
- The study integrates blockchain technology with cloud computing, and broadly discusses the application of blockchain in cloud computing.
- 5.
- Scalability and hardware issues of blockchain technology are explained in detail, and a few solutions are suggested to combat the major challenges.
- 6.
- Finally, the paper criticizes the detailed study of the paper and suggests some future directions for the study.
3. Introduction to Various Platforms of Blockchain Technology
- Consensus:
- All participating nodes in the network must agree on the validity of a transaction.
- Provenance:
- All the participants in the network can know the lineage of an asset recorded on the blockchain.
- Immutability:
- It is impossible to tamper with any transaction on the blockchain. If any transaction is wrongly executed, a new transaction must be issued to right the wrongs of the previous transaction.
- Distributed:
- The blockchain network is a peer-to-peer distributed network. There is no single point of failure. If some of the nodes fail to work, that will not affect the functioning of the network. No single authority can control the whole network.
- Security:
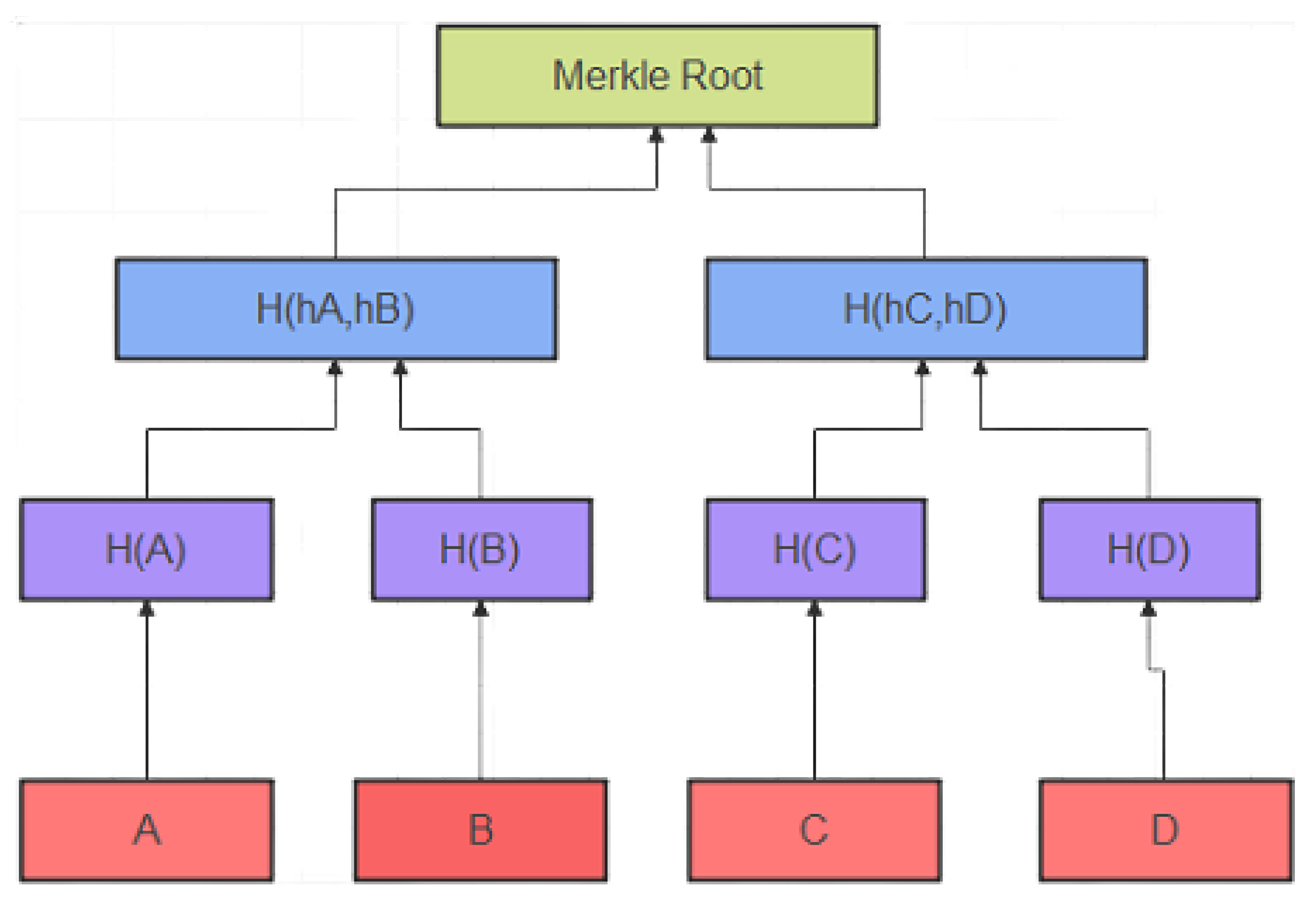
- The security of the transactions is achieved through public key cryptography. Every network participant has public and private keys to encrypt the data and issue digital signatures.
- Coherence:
- There will always exist a single value of truth in the blockchain. Every participant in the network sees the same copy of the distributed ledger.
- Decentralization:
- A conventional centralized transaction structure requires transactions to be approved by a trusted entity (e.g., the National Bank), causing cost and execution bottlenecks on central servers. The blockchain eliminates the need for outsiders, contrary to the previously introduced centralized mode. In blockchain networks, agreement calculations are used to preserve details.
- Persistency:
- There is a quick way to check transactions, and fair miners will not admit to fraudulent transactions. As soon as a transaction is recorded in the blockchain, it is hard to reverse or erase. It is possible to instantly identify blocks that contain invalid transactions.
- Anonymity:
- There is a possibility that a client can sign up for a blockchain and use a generated address that does not reveal the client’s real identity. We should be aware of blockchain technology.
- Auditability:
- A Bitcoin blockchain stores information about client adjustments based on the UTXO (Unused Transaction Performance): Every transaction applies to previously unused exchanges. If the present transaction is registered in the blockchain, the unspent transactions are changed from unspent to spent when the transaction is registered. There is also the possibility of effortlessly confirming transactions.
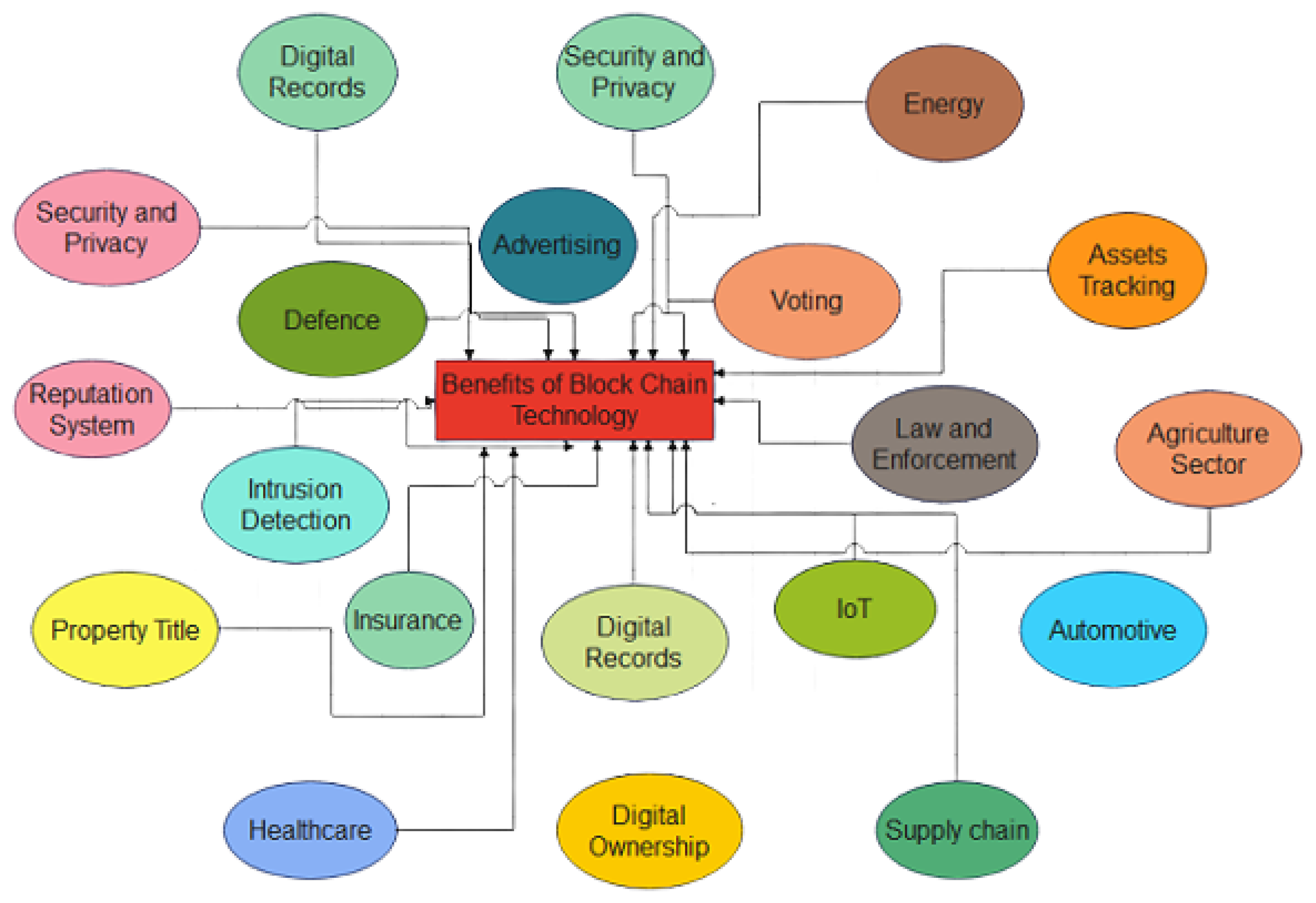
4. Demanding Applications of Blockchain Technology and the Motivation behind Them
4.1. The Cost of the Reduction of Data Breaches
4.2. Increasing Cross-Border Remittances and Reducing Trans-Border Transaction Costs
4.3. Inefficient Supply Chains Can Be Eliminated, and Costs Can Be Reduced
4.4. Data on National Identity Is Being Protected Using Blockchain by Governments
4.5. Protection of Copyright through Blockchain Technology
4.6. A Blockchain-Based Solution for Tracking Drugs throughout Supply Chains and Securing Data in Healthcare
4.7. Blockchain Technology in Cybersecurity
4.8. Blockchain Technology in Smart Contracts
4.9. Blockchain in Business Data Privacy and Threats
5. Major Challenges
5.1. Hardware and Energy Consumption for Blockchain Applications Are a Major Challenge
5.2. Scalability
6. Concept of Cloud Computing
7. Traditional Techniques for Cloud Computing
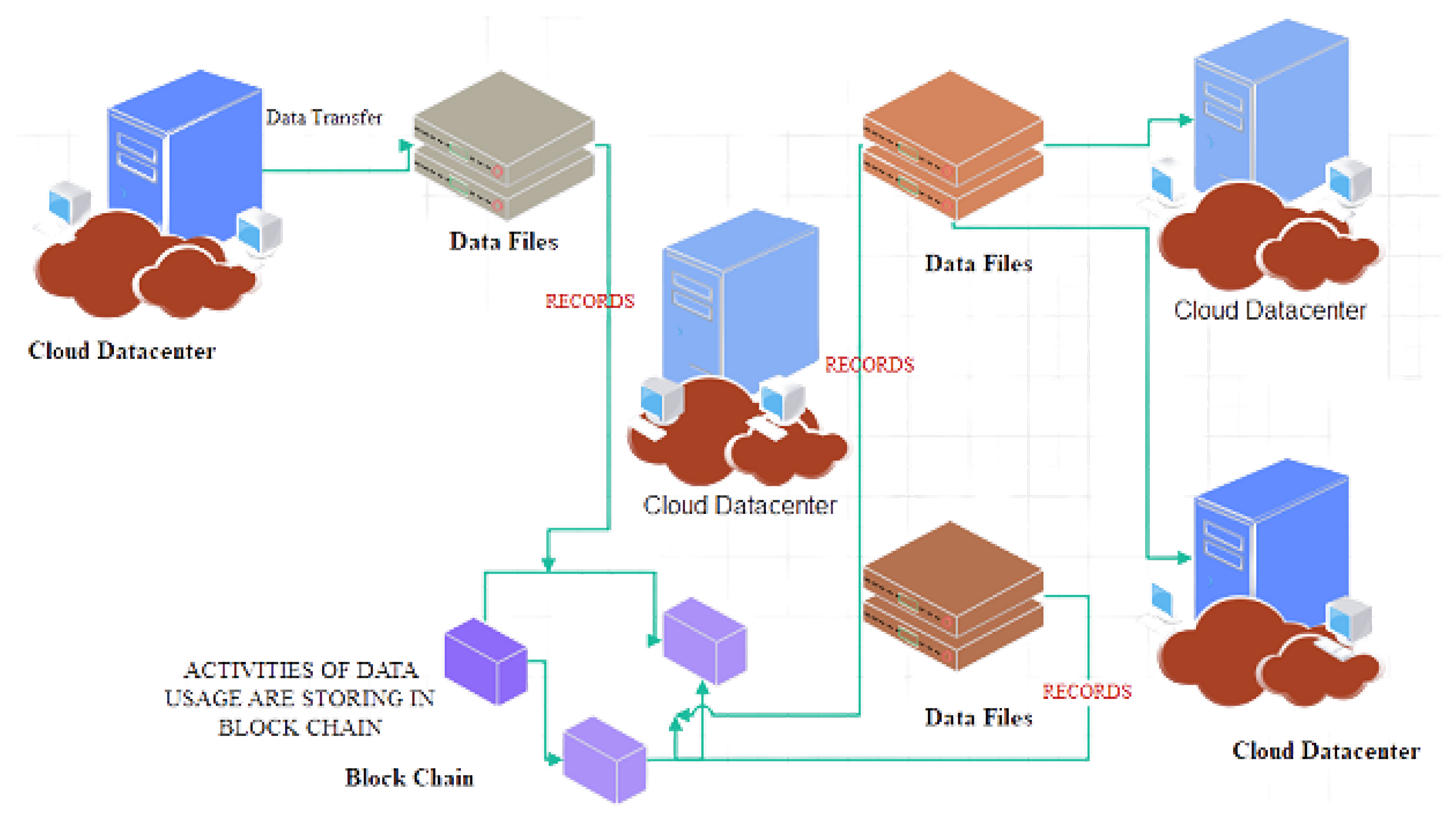
8. Integration of Blockchain Technology and Cloud Computing
Open Research Challenges
9. Benefits of Blockchain in Cloud Computing
9.1. Decentralization
9.2. Enhanced Data Protection
9.3. Improved Goods and Service Ownership Tracking
- 1.
- Consistently monitoring all of the cars in a network.
- 2.
- Determining their current locations.
- 3.
- Determining the time that each car spends in a certain region.
- 4.
- Establishing communication between many vehicles.
9.4. Tolerance for Errors
10. Blockchain in Cloud Computing and the Reasons for Its Popularity
11. Applications of the Integration of Blockchain and Cloud Computing
11.1. A Healthcare Industry That Is Becoming More Knowledgeable
11.2. Smart Home Automation Using Blockchain Technology
11.3. Autonomous Transportation Powered by the Blockchain
11.4. Smart Manufacturing
11.4.1. Data De-Duplication Scheme Using Blockchain Technology for Cloud Storage Services
11.4.2. Blockchain-Based Cloud Storage Access Control Systems
11.4.3. Blockchain as a Driver of Digital Business Transformation
12. Conclusions, Limitations, and Future Work
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Krdzalic, Y. Blockchain Explained: The Complete Guide [2018 Update—Part 2]. 2021. Available online: https://www.trentonsystems.com/blog/blockchain-explained-the-complete-guide-part-2 (accessed on 17 October 2022).
- Harvey, C.R. Bitcoin Myths and Facts. Available at SSRN 2479670. 2014. Available online: https://www.semanticscholar.org/paper/Bitcoin-Myths-and-Facts-Harvey/992342c42002b5952df16f8236b1c80072135496 (accessed on 17 October 2022).
- Hayes, A. The socio-technological lives of bitcoin. Theory Cult. Soc. 2019, 36, 49–72. [Google Scholar] [CrossRef]
- Rose, C. The evolution of digital currencies: Bitcoin, a cryptocurrency causing a monetary revolution. Int. Bus. Econ. Res. J. 2015, 14, 617–622. [Google Scholar] [CrossRef]
- Jeong, S. The Bitcoin Protocol as Law, and the Politics of a Stateless Currency. Available at SSRN 2294124. 2013. Available online: https://papers.ssrn.com/sol3/papers.cfm?abstract_id=2294124 (accessed on 17 October 2022).
- DuPont, Q. Cryptocurrencies and Blockchains; John Wiley & Sons: Hoboken, NJ, USA, 2019. [Google Scholar]
- French, L.A. The Effects of Blockchain on Supply Chain Trust: A Thesis Presented in Partial of the Requirements for the Master of Supply Chain Management at Massey University, Palmerston North, New Zealand. Ph.D. Thesis, Massey University, Palmerston North, New Zealand, 2022. [Google Scholar]
- Burniske, C.; White, A. Bitcoin: Ringing the Bell for a New Asset Class. Ark Invest (January 2017). 2017. Available online: https://research.ark-invest.com/hubfs/1_Download_Files_ARK-Invest/White_Papers/Bitcoin-Ringing-The-Bell-For-A-New-Asset-Class.pdf (accessed on 17 October 2022).
- Mougayar, W. The Business Blockchain: Promise, Practice, and Application of the Next Internet Technology; John Wiley & Sons: Hoboken, NJ, USA, 2016. [Google Scholar]
- Notaro, A. All that is solid melts in the Ethereum: The brave new (art) world of NFTs. J. Vis. Art Pract. 2022, 1–24. [Google Scholar] [CrossRef]
- KiliÇarslan, S.K. Bitcoin Özelİnde Kripto paralarin Edinilmiş mallara katilma rejiminde tasfiyesi sorunu. Kırıkkale Hukuk Mecmuası 2023, 3, 1–27. [Google Scholar]
- Strilets, B. Current state and prospects for the legal regulation of cryptocurrencies in the European Union. Actual Probl. Law 2022, 70–76. [Google Scholar] [CrossRef]
- Ramadoss, R. Blockchain technology: An overview. IEEE Potentials 2022, 41, 6–12. [Google Scholar] [CrossRef]
- Hocaoğlu, M.; Habbal, A. NFT-Based Model to Manage Educational Assets in Metaverse. Avrupa Bilim Teknol. Derg. 2022, 20–25. Available online: https://dergipark.org.tr/tr/download/article-file/2709574 (accessed on 17 October 2022).
- Trimborn, S.; Peng, H.; Chen, Y. Influencer Detection Meets Network AutoRegression–Influential Regions in the Bitcoin Blockchain. Available at SSRN. 2022. Available online: https://www.ml-quant.com/42546603-d6fd-493a-8736-5130928e127b (accessed on 17 October 2022).
- Kaur, H.; Alam, M.A.; Jameel, R.; Mourya, A.K.; Chang, V. A proposed solution and future direction for blockchain-based heterogeneous medicare data in cloud environment. J. Med. Syst. 2018, 42, 156. [Google Scholar] [CrossRef]
- Murthy, C.V.B.; Shri, M.L. A survey on integrating cloud computing with blockchain. In Proceedings of the 2020 International Conference on Emerging Trends in Information Technology and Engineering (ic-ETITE), Vellore, India, 24–25 February 2020; pp. 1–6. [Google Scholar]
- Niranjanamurthy, M.; Nithya, B.; Jagannatha, S. Analysis of Blockchain technology: Pros, cons and SWOT. Clust. Comput. 2019, 22, 14743–14757. [Google Scholar] [CrossRef]
- Baboshkin, P.; Mikhaylov, A.; Shaikh, Z.A. Sustainable Cryptocurrency Growth Impossible? Impact of Network Power Demand on Bitcoin Price. Finans. Žhurnal Financ. J. 2022, 116–130. Available online: https://ideas.repec.org/a/fru/finjrn/220308p116-130.html (accessed on 17 October 2022).
- Jabbar, R.; Dhib, E.; ben Said, A.; Krichen, M.; Fetais, N.; Zaidan, E.; Barkaoui, K. Blockchain Technology for Intelligent Transportation Systems: A Systematic Literature Review. IEEE Access 2022, 10, 20995–21031. [Google Scholar] [CrossRef]
- Pagnotta, E.S. Decentralizing money: Bitcoin prices and blockchain security. Rev. Financ. Stud. 2022, 35, 866–907. [Google Scholar] [CrossRef]
- Salem, H.; Mazzara, M.; Saleh, H.; Husami, R.; Hattab, S.M. Development of a Blockchain-Based Ad Listing Application. In Proceedings of the International Conference on Advanced Information Networking and Applications, Sydney, NSW, Australia, 13–15 April 2022; Springer: Berlin/Heidelberg, Germany, 2022; pp. 37–45. [Google Scholar]
- Rajashekar, M.; Sundaram, S. Dynamic Attribute Tree for the Data Encryption and Third Party Auditing for Cloud Storage. Indian J. Sci. Technol. 2022, 15, 798–805. [Google Scholar] [CrossRef]
- Wang, J.; Chen, J.; Xiong, N.; Alfarraj, O.; Tolba, A.; Ren, Y. S-BDS: An effective blockchain-based data storage scheme in zero-trust IoT. ACM Trans. Internet Technol. 2022. [Google Scholar] [CrossRef]
- Maalla, M.A.; Bezzateev, S.V. Efficient incremental hash chain with probabilistic filter-based method to update blockchain light nodes. Sci. Tech. J. Inf. Technol. Mech. Opt. 2022, 22, 538–546. [Google Scholar] [CrossRef]
- Agrawal, D.; Minocha, S.; Namasudra, S.; Gandomi, A.H. A robust drug recall supply chain management system using hyperledger blockchain ecosystem. Comput. Biol. Med. 2022, 140, 105100. [Google Scholar] [CrossRef] [PubMed]
- Sammeta, N.; Parthiban, L. Hyperledger blockchain-enabled secure medical record management with deep learning-based diagnosis model. Complex Intell. Syst. 2022, 8, 625–640. [Google Scholar] [CrossRef]
- Mirtskhulava, L.; Iavich, M.; Razmadze, M.; Gulua, N. Securing Medical Data in 5G and 6G via Multichain Blockchain Technology using Post-Quantum Signatures. In Proceedings of the 2021 IEEE International Conference on Information and Telecommunication Technologies and Radio Electronics (UkrMiCo), Odesa, Ukraine, 29 November–3 December 2021; pp. 72–75. [Google Scholar]
- Bouachir, O.; Aloqaily, M.; Tseng, L.; Boukerche, A. Blockchain and fog computing for cyberphysical systems: The case of smart industry. Computer 2020, 53, 36–45. [Google Scholar] [CrossRef]
- Sedlmeir, J.; Buhl, H.U.; Fridgen, G.; Keller, R. The energy consumption of blockchain technology: Beyond myth. Bus. Inf. Syst. Eng. 2020, 62, 599–608. [Google Scholar] [CrossRef]
- Gill, S.S.; Tuli, S.; Xu, M.; Singh, I.; Singh, K.V.; Lindsay, D.; Tuli, S.; Smirnova, D.; Singh, M.; Jain, U.; et al. Transformative effects of IoT, Blockchain and Artificial Intelligence on cloud computing: Evolution, vision, trends and open challenges. Internet Things 2019, 8, 100118. [Google Scholar] [CrossRef]
- Nguyen, D.C.; Pathirana, P.N.; Ding, M.; Seneviratne, A. Integration of blockchain and cloud of things: Architecture, applications and challenges. IEEE Commun. Surv. Tutor. 2020, 22, 2521–2549. [Google Scholar] [CrossRef]
- Reyna, A.; Martín, C.; Chen, J.; Soler, E.; Díaz, M. On blockchain and its integration with IoT. Challenges and opportunities. Future Gener. Comput. Syst. 2018, 88, 173–190. [Google Scholar] [CrossRef]
- Al-Jaroodi, J.; Mohamed, N. Blockchain in industries: A survey. IEEE Access 2019, 7, 36500–36515. [Google Scholar] [CrossRef]
- Xie, S.; Zheng, Z.; Chen, W.; Wu, J.; Dai, H.N.; Imran, M. Blockchain for cloud exchange: A survey. Comput. Electr. Eng. 2020, 81, 106–526. [Google Scholar] [CrossRef]
- Gai, K.; Guo, J.; Zhu, L.; Yu, S. Blockchain meets cloud computing: A survey. IEEE Commun. Surv. Tutor. 2020, 22, 2009–2030. [Google Scholar] [CrossRef]
- Wamba, S.F.; Queiroz, M.M. Blockchain in the operations and supply chain management: Benefits, challenges and future research opportunities. Int. J. Inf. Manag. 2020, 52, 102064. [Google Scholar] [CrossRef]
- Atlam, H.F.; Alenezi, A.; Alassafi, M.O.; Wills, G. Blockchain with internet of things: Benefits, challenges, and future directions. Int. J. Intell. Syst. Appl. 2018, 10, 40–48. [Google Scholar] [CrossRef]
- Dorsala, M.R.; Sastry, V.; Chapram, S. Blockchain-based solutions for cloud computing: A survey. J. Netw. Comput. Appl. 2021, 196, 103246. [Google Scholar] [CrossRef]
- Guo, H.; Yu, X. A Survey on Blockchain Technology and its security. Blockchain Res. Appl. 2022, 3, 100067. [Google Scholar] [CrossRef]
- Zheng, Z.; Xie, S.; Dai, H.N.; Chen, X.; Wang, H. Blockchain challenges and opportunities: A survey. Int. J. Web Grid Serv. 2018, 14, 352–375. [Google Scholar] [CrossRef]
- Joshi, A.P.; Han, M.; Wang, Y. A survey on security and privacy issues of blockchain technology. Math. Found. Comput. 2018, 1, 121. [Google Scholar] [CrossRef]
- Chen, W.; Xu, Z.; Shi, S.; Zhao, Y.; Zhao, J. A survey of blockchain applications in different domains. In Proceedings of the 2018 International Conference on Blockchain Technology and Application, Seoul, Republic of Korea, 20–22 June 2018; pp. 17–21. [Google Scholar]
- Dave, D.; Parikh, S.; Patel, R.; Doshi, N. A survey on blockchain technology and its proposed solutions. Procedia Comput. Sci. 2019, 160, 740–745. [Google Scholar] [CrossRef]
- Monrat, A.A.; Schelén, O.; Andersson, K. A survey of blockchain from the perspectives of applications, challenges, and opportunities. IEEE Access 2019, 7, 117134–117151. [Google Scholar] [CrossRef]
- Esposito, C.; De Santis, A.; Tortora, G.; Chang, H.; Choo, K.K.R. Blockchain: A Panacea for Healthcare Cloud-Based Data Security and Privacy? IEEE Cloud Comput. 2018, 5, 31–37. [Google Scholar] [CrossRef]
- Shobanadevi, A.; Tharewal, S.; Soni, M.; Kumar, D.D.; Khan, I.R.; Kumar, P. Novel identity management system using smart blockchain technology. Int. J. Syst. Assur. Eng. Manag. 2022, 13, 496–505. [Google Scholar] [CrossRef]
- Draper, A.; Familrouhani, A.; Cao, D.; Heng, T.; Han, W. Security applications and challenges in blockchain. In Proceedings of the 2019 IEEE International Conference on Consumer Electronics (ICCE), Las Vegas, NV, USA, 11–13 January 2019; pp. 1–4. [Google Scholar]
- Jiang, S.; Li, X.; Wu, J. Hierarchical edge-cloud computing for mobile blockchain mining game. In Proceedings of the 2019 IEEE 39th international conference on distributed computing systems (ICDCS), Dallas, TX, USA, 7–10 July 2019; pp. 1327–1336. [Google Scholar]
- Hazra, A.; Alkhayyat, A.; Adhikari, M. Blockchain-aided Integrated Edge Framework of Cybersecurity for Internet of Things. IEEE Consum. Electron. Mag. 2022. Available online: https://ieeexplore.ieee.org/document/9672722/ (accessed on 17 October 2022).
- Yu, Y.; Liu, S.; Yeoh, P.L.; Vucetic, B.; Li, Y. LayerChain: A hierarchical edge-cloud blockchain for large-scale low-delay industrial Internet of Things applications. IEEE Trans. Ind. Inform. 2020, 17, 5077–5086. [Google Scholar] [CrossRef]
- Rathod, T.; Jadav, N.K.; Alshehri, M.D.; Tanwar, S.; Sharma, R.; Felseghi, R.A.; Raboaca, M.S. Blockchain for Future Wireless Networks: A Decade Survey. Sensors 2022, 22, 4182. [Google Scholar] [CrossRef] [PubMed]
- Alevizos, L.; Ta, V.T.; Hashem Eiza, M. Augmenting zero trust architecture to endpoints using blockchain: A state-of-the-art review. Secur. Priv. 2022, 5, e191. [Google Scholar] [CrossRef]
- Bhuyan, M.; Kashihara, S.; Fall, D.; Taenaka, Y.; Kadobayashi, Y. A survey on blockchain, SDN and NFV for the smart-home security. Internet Things 2022, 20, 100588. [Google Scholar]
- Abdel Ouahab, I.B.; Bouhorma, M.; El Aachak, L.; Boudhir, A.A. Towards a new cyberdefense generation: Proposition of an intelligent cybersecurity framework for malware attacks. Recent Patents Comput. Sci. 2022, 15, 1026–1042. [Google Scholar] [CrossRef]
- Lakhan, A.; Mohammed, M.A.; Elhoseny, M.; Alshehri, M.D.; Abdulkareem, K.H. Blockchain multi-objective optimization approach-enabled secure and cost-efficient scheduling for the Internet of Medical Things (IoMT) in fog-cloud system. Soft Comput. 2022, 26, 6429–6442. [Google Scholar] [CrossRef]
- Jyoti, A.; Chauhan, R. A blockchain and smart contract-based data provenance collection and storing in cloud environment. Wirel. Netw. 2022, 28, 1541–1562. [Google Scholar] [CrossRef]
- Nguyen, T.M.; Prentice, C. Reverse relationship between reward, knowledge sharing and performance. Knowl. Manag. Res. Pract. 2022, 20, 516–527. [Google Scholar] [CrossRef]
- Azariah, W.; Bimo, F.A.; Lin, C.W.; Cheng, R.G.; Jana, R.; Nikaein, N. A Survey on Open Radio Access Networks: Challenges, Research Directions, and Open Source Approaches. arXiv 2022, arXiv:2208.09125. [Google Scholar]
- Li, S.; Zhang, Y.; Xu, C.; Cheng, N.; Liu, Z.; Du, Y.; Shen, X. HealthFort: A Cloud-Based Ehealth System With Conditional Forward Transparency and Secure Provenance Via Blockchain. IEEE Trans. Mob. Comput. 2022, 1–18. Available online: https://ieeexplore.ieee.org/document/9858023 (accessed on 17 October 2022).
- Xiong, H.; Chen, M.; Wu, C.; Zhao, Y.; Yi, W. Research on Progress of Blockchain Consensus Algorithm: A Review on Recent Progress of Blockchain Consensus Algorithms. Future Internet 2022, 14, 47. [Google Scholar] [CrossRef]
- Zhang, X.; Xue, M.; Miao, X. A Consensus Algorithm Based on Risk Assessment Model for Permissioned Blockchain. Wirel. Commun. Mob. Comput. 2022, 2022, 8698009. [Google Scholar] [CrossRef]

| S. No. | Year of Publishing | Description | References |
|---|---|---|---|
| 1 | 2008 | A pseudonymous person or group with the name Satoshi Nakamoto published “Bitcoin: A Peer-to-Peer Electronic Cash System”. | [2] |
| 2 | 2009 | Founder Satoshi Nakamoto and computer scientist Hal Finney execute the first successful Bitcoin transaction. | [3] |
| 3 | 2010 | Laszlo Hanycez, a Florida-based programmer, purchases two Papa John’s pizzas with Bitcoin. A transfer of 10,000 BTCs, worth $60 at the time, was made by Hanycez. Bitcoin’s market cap is now over $1 million. | [4] |
| 04 | 2011 | Bitcoin equals 1 USD, making it the world’s most valuable cryptocurrency. Several organizations, including Wikileaks and the Electronic Frontier Foundation, have started accepting Bitcoin donations. | [5] |
| 05 | 2012 | There is widespread media coverage of blockchain and cryptocurrency, including in television shows such as The Good Wife, bringing blockchain into the mainstream. The Bitcoin Magazine was launched by Vitalik Buterin, a pioneering Bitcoin developer. | [6] |
| 06 | 2013 | The Bitcoin market cap has exceeded $1 billion. There was a first-time rise in Bitcoin’s price to $100/BTC. The Ethereum Project paper is published, suggesting blockchain has other uses besides Bitcoin (such as smart contracts). | [7] |
| 07 | 2014 | A variety of companies accept Bitcoin as a payment method, including Zynga, The D Las Vegas Hotel, and Overstock.com. In an Initial Coin Offering (ICO), Buterin’s Ethereum Project raises over $18 million in Bitcoin and opens up new avenues for blockchain development. Over 200 blockchain firms form the R3 group to explore new uses of blockchain. PayPal announces a Bitcoin integration. The first-ever NFT is minted. | [7] |
| 08 | 2015 | It is estimated that more than 100,000 merchants accept Bitcoin. A partnership between NASDAQ and San Francisco-based blockchain company Chain is intended to test the technology for trading shares in private companies. | [8] |
| 09 | 2016 | IBM announced a blockchain strategy for cloud-based business solutions. Several government agencies recognize the legitimacy of blockchain and cryptocurrencies in Japan. | [9] |
| 10 | 2017 | The price of Bitcoin reaches $1000/BTC for the first time. Cryptocurrencies have a market cap of $150 billion. Despite Wall Street’s distrust of blockchain, JP Morgan CEO Jamie Dimon said he believes in this technology. As of 19,783.21/BTC, Bitcoin has reached its all-time high. A blockchain-powered government has been announced for Dubai by 2020. | [10] |
| 11 | 2018 | Facebook committed to creating a blockchain group and hinted at creating a cryptocurrency itself. Large banks such as Citi and Barclays have signed up to use IBM’s blockchain-based banking platform. | [11] |
| 12 | 2019 | President Ji Xinping embraces blockchain as the Chinese central bank announces its cryptocurrency. Twitter CEO Jack Dorsey announced Square would hire blockchain engineers as part of its cryptocurrency plans. Bakkt is a digital wallet company that offers crypto trading on the New York Stock Exchange (NYSE). | [12] |
| 13 | 2020 | It is estimated that BTC will reach $30,000 by the end of 2020. From now on, Bitcoin and other cryptocurrencies will be bought, sold, and held by PayPal users. Having launched its central bank digital currency aptly called the Sand Dollar, the Bahamas became the first country in the world to do so. As part of the fight against COVID-19, blockchain technology plays a key role in securely storing the data of medical researchers and patients. | [13] |
| 14 | 2021 | For the first time, Bitcoin has reached a market value of more than $1 trillion. Increasing popularity for Web3 implementation. The El Salvadorian government has adopted Bitcoin as a legal tender for the first time. The first car manufacturer to accept Bitcoin as a method of payment for automobiles, Tesla buys $1.5 billion in BTC. As blockchain technology advances, mainstream interest is drawn to the Metaverse, a virtual environment incorporating blockchain technology. | [14] |
| 15 | 2022 | A $2 trillion market value loss occurs due to economic inflation and rising interest rates. Google forms an Enterprise Digital Assets Team to serve customers on blockchain-based platforms. In the UK, the government has proposed safeguards for stablecoin holders. Blockchain technologies and NFTs are banned in the popular video game Minecraft. | [15] |
| Size | Field | Description |
|---|---|---|
| 4 bytes | Version | The version of rules followed |
| 1–9 bytes (Var-Int) | Input Counter | Number of transaction inputs |
| Variable | Inputs | Transaction inputs |
| 1–9 bytes (Var-Int) | Output Counter | Number of transaction outputs |
| Variable | Outputs | Transaction outputs |
| 4 bytes | Lock time | Timestamp of block number |
| Blockchain Technology | Bitcoin | Ethereum | Hyperledger Fabric |
|---|---|---|---|
| Main Purpose | Used for cryptocurrency | Employed for smart contracts | Deploys block chain technology for fabric industries |
| Data storage type | Transactions of cryptocurrencies | Transactions of cryptocurrencies, smart contract history | Chain coding and smart contract transactions |
| Languages used | Script | Solidity Serpent | Go |
| Choice of ecosystem | Open | Open | Restricted |
| Participation choice | Open-source code from GitHub | Open-source code from GitHub | Needs network membership for user source code |
| Naïve currency | Bitcoin (BTC) | Ether (ETC) or (ETH) | N/A |
| Decision-making | Yes | Yes | Unknown |
| Block release timing | 10 min | 12 s | Configurable |
| Size of transaction | 250 B | No upper bound | Configurable |
| Rate of transaction | 3TXN/s | No upper bound | >10,000 TNX/s |
| Mining | Needs proof of work | Needs proof of work using Ethash algorithm | N/A |
| S. No. | Application Methodology | Description | Research Challenges | Reference |
|---|---|---|---|---|
| 01. | ProvChain | An enhanced privacy and availability blockchain-based data provenance architecture for cloud environments. They suggested a decentralized and trusted cloud data provenance architecture based on blockchain technology. The ProvChain architecture was developed for collecting and verifying the provenance of data. | Although data transparency, security, and accountability were improved, it failed to create a trustworthy environment. In the case of large files, overhead increases the complexity of computation. | [48] |
| 02. | Mobile Blockchain Mining Game with Hierarchical Edge-Cloud Computing | This model combines edge computing with cloud computing to offload computations. Two case studies were examined, a fixed miner number and a dynamic miner number. | Although profitable, use of limited resources. Different communication delays alter the security model of an environment. | [49] |
| 03. | Layer Chain | This architecture establishes hierarchies for maintaining IIoT transaction records using an edge-cloud blockchain. To support large-scale IIoT environments, the critical objective was to reduce the long-term resource consumption of blockchain technology. | Low-delay data storage solutions based on secure blockchain networks are crucial in real-time IIoT applications. Unfortunately, there is limited research on block propagation delays in blockchain applications. To address the above issues, pervasive edge computing is widely adopted as a promising solution, which can be used to develop an efficient peer-to-peer network for blockchain. | [50,51] |
| 04. | Blockchain Technology and Cloud Computing in Intelligent Information Security | To achieve intelligent campuses, blockchain can integrate the technical expertise of cloud computing, the Internet of Things, artificial intelligence, and other technologies as the underlying architecture. Typical applications include building a firewall for network infrastructure, providing a certificate for evaluating teaching systems, tracking intelligent property protection, etc. | With the continued enrichment of blockchain technology ecology, its role as the underlying infrastructure of trusted information environments will become more prominent. As a result, future data sharing and value transmission will be greatly enhanced, and original data barriers will be broken. | [52,53,54,55] |
| 05. | Fog Bus | We are developing a lightweight framework for computing edge and fog based on blockchains. IoT fog–cloud integration is enabled through Fog Bus, a mechanism developed to facilitate end-to-end IoT fog–cloud integration. It ensures the sensitive nature of the data by using blockchain technology. | As a result of this simplified process, the data were more scalable, and costs were reduced. Based on the situation, a decision is made on how the data will be communicated. In addition to failing to support users, it also failed to support providers. Even though a centralized programming module is incorporated, the task of applying security features is disliked due to the diversity of the applications. | [56] |
| 06. | Smart Provenance | Uses blockchain technology to prove the provenance of distributed data. Their paper suggested using blockchain technology to collect, verify, and manage data provenance. Additionally, smart contracts and open provenance models were studied to interpret the data trails. | A higher computation cost is associated with allocating each updated document, as it maintains the old memory for each document. Process identity is revealed through the use of a public address system. | [57] |
| 07. | Share | A cloud-based blockchain for sharing knowledge about injection mould redesign in a secure manner. For private and blockchain technologies, cloud-based knowledge is recommended. The platform was redesigned to meet privacy and data format requirements. Similarly, the K-nearest neighbor algorithm was developed to retrieve information. | Due to blockchain’s immutability, labeling is essential. It will help reduce the risks associated with fake knowledge. | [58] |
| 08. | B-RAN stands for blockchain Radio Access Network | Using blockchain radio access networks (B-RANs), they developed decentralized, fast, and efficient methods to manage network access and authentication among inherently distrusting networks. | It can enable secure multi-party computations to avoid unauthorized access to sensitive data without compromising distributed computing. | [59] |
| 09. | Using blockchain to tamper-proof EHRs via the cloud. | Using cloud-based technology, they designed secure e-health systems that eliminate illegal modifications. They analyzed communication overhead as well as computational overhead with reduced computation time. | A blockchain is created by colluding between the data server and its corresponding transactions. In the absence of a central authority, multiple tokens need to be requested, which creates an environment of non-trust. | [60] |
| 10. | Consensus Bookkeeping using blockchain | A cloud–network collaboration scenario can break the monopoly of Internet companies on network data by using blockchain token authorization and the right confirmation mechanism in the ledger, in conjunction with blockchain data encryption, immutability, and traceability characteristics. It is confirmed that the data belongs to each user. A company that needs personal behavior data will use Token to process payments to individual users and provide credible authorization at the data layer to protect the legitimate interests of consumers. In this article, consensus accounting and blockchain technology are used when users purchase cloud services and network services to protect users’ privacy and avoid uploading their local data to cloud servers. Blockchain technology is also used to ensure transaction security in cloud–network collaborations. | The article explains why DBFT consensus is superior to other consensus mechanisms for cloud-based collaboration with network delays, transmission errors, security holes, hacking, and malicious nodes, which are some of the major issues bookkeeping systems face using blockchain technology. | [61,62] |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Habib, G.; Sharma, S.; Ibrahim, S.; Ahmad, I.; Qureshi, S.; Ishfaq, M. Blockchain Technology: Benefits, Challenges, Applications, and Integration of Blockchain Technology with Cloud Computing. Future Internet 2022, 14, 341. https://doi.org/10.3390/fi14110341
Habib G, Sharma S, Ibrahim S, Ahmad I, Qureshi S, Ishfaq M. Blockchain Technology: Benefits, Challenges, Applications, and Integration of Blockchain Technology with Cloud Computing. Future Internet. 2022; 14(11):341. https://doi.org/10.3390/fi14110341
Chicago/Turabian StyleHabib, Gousia, Sparsh Sharma, Sara Ibrahim, Imtiaz Ahmad, Shaima Qureshi, and Malik Ishfaq. 2022. "Blockchain Technology: Benefits, Challenges, Applications, and Integration of Blockchain Technology with Cloud Computing" Future Internet 14, no. 11: 341. https://doi.org/10.3390/fi14110341
APA StyleHabib, G., Sharma, S., Ibrahim, S., Ahmad, I., Qureshi, S., & Ishfaq, M. (2022). Blockchain Technology: Benefits, Challenges, Applications, and Integration of Blockchain Technology with Cloud Computing. Future Internet, 14(11), 341. https://doi.org/10.3390/fi14110341







