Empirically Investigating Extraneous Influences on the “APCO” Model—Childhood Brand Nostalgia and the Positivity Bias
Abstract
:1. Introduction
What influence has a positivity bias induced by childhood brand nostalgia for Pokémon on the privacy calculus of individuals related to the use behavior of Pokémon Go?
2. Related Work and Research Model
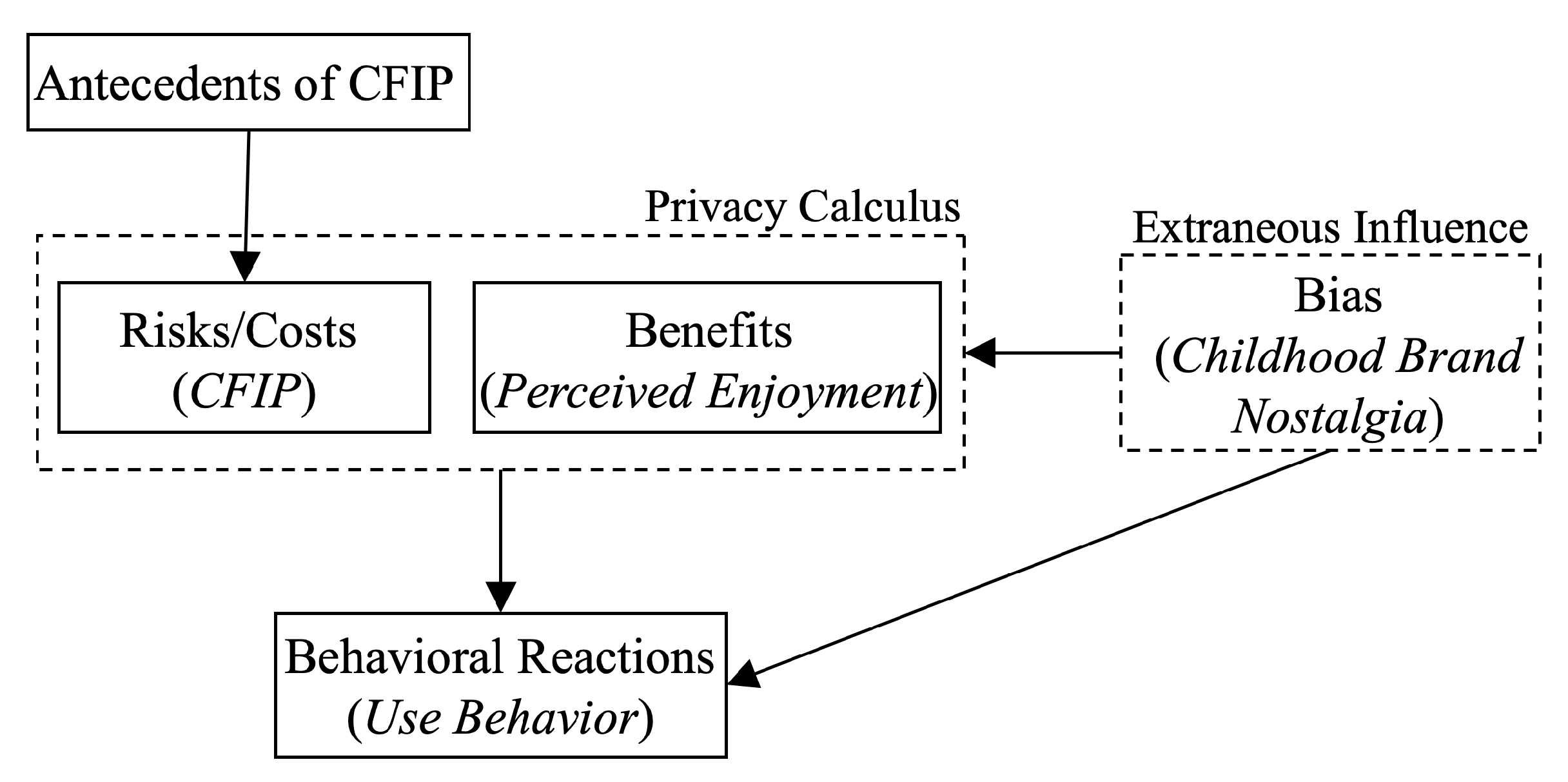
2.1. Model Development
2.2. Antecedents of Cfip in Prior Research
2.3. Nostalgia Induces a Positivity Bias
3. Methodology
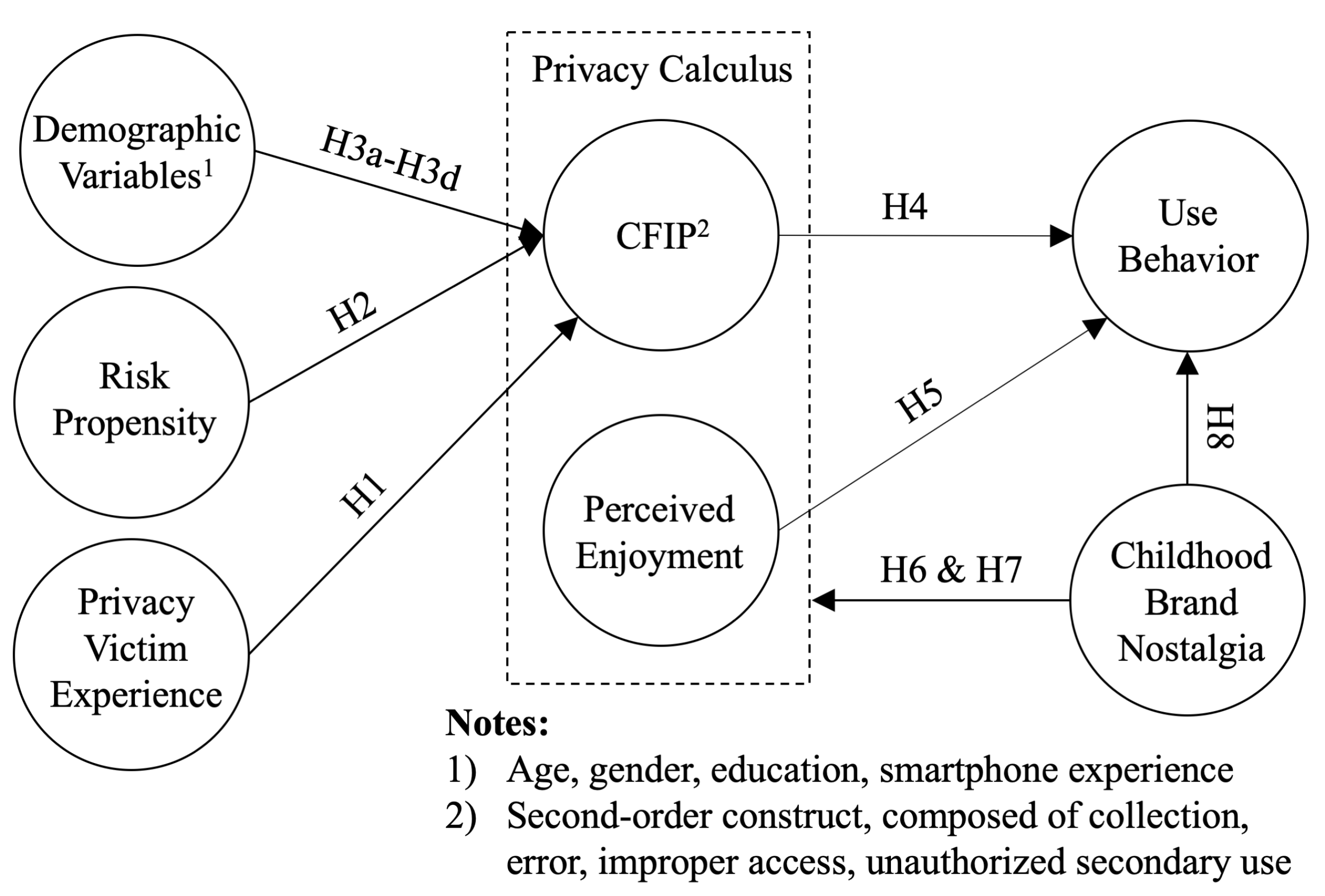
3.1. Research Hypotheses and Model
- 1.
- Prior privacy victim experiences (VIC) have a positive effect on CFIP.
- 2.
- Risk propensity (RP) has a positive effect on CFIP.
- 3.
- (a)
- Age has a positive effect on CFIP.
- (b)
- Female players of Pokémon Go show higher levels of CFIP.
- (c)
- Education has a positive effect on CFIP.
- (d)
- Smartphone experience has a positive effect on CFIP.
- 4.
- CFIP have a negative effect on the use behavior of Pokémon Go (USE).
- 5.
- Perceived enjoyment (PE) has a positive effect on the use behavior of Pokémon Go (USE).
- 6.
- CBN has a negative effect on CFIP.
- 7.
- CBN has a positive effect on players’ perceived enjoyment of playing Pokémon Go (PE).
- 8.
- CBN has a positive effect on the use behavior of Pokémon Go (USE).
3.2. Questionnaire and Data
4. Results
4.1. Assessment of the Measurement Model
4.2. Assessment of the Structural Model
5. Discussion
5.1. Limitations
5.2. Future Work
6. Contributions
Author Contributions
Funding
Conflicts of Interest
Appendix A. Questionnaire
- I have fond memories of this brand from my childhood.
- This brand features in happy memories of when I was younger.
- I still feel positive about this brand today because it reminds me of my childhood.
- This brand is one of my favorite brands from my childhood.
- Playing Pokémon Go is fun.
- Playing Pokémon Go is enjoyable.
- Playing Pokémon Go is very entertaining.
| 1. Never | 6. Once a day |
| 2. Once a month | 7. Several times a day |
| 3. Several times a month | 8. Once an hour |
| 4. Once a week | 9. Several times an hour |
| 5. Several times a week | 10. All the time |
- Age: How old are you?
- Gender: What is your gender? (1 = female, 0 = male)
- Education: What is the highest degree or level of school you have completed? In case you are currently enrolled, please provide the highest degree received. (ranging from no qualification (1) to doctorate (7))
- Smartphone experience: How many years of experience do you have with smartphones? (0 years (1) to >10 years (11))
Appendix B. Descriptive Statistics and Measurement Model Assessment
| Variable | Median | Mean | Std. Dev. | Min. | Max. |
|---|---|---|---|---|---|
| AGE | 27 | 26.766 | 4.626 | 18 | 35 |
| GDR | 1 | 0.612 | 0.488 | 0 | 1 |
| EDU | 4 | 4.091 | 1.117 | 2 | 7 |
| EXP | 6 | 6.007 | 2.209 | 0 | 10 |
| VIC | 3 | 2.694 | 1.375 | 1 | 7 |
| RP | 4.667 | 4.499 | 1.238 | 1 | 7 |
| COLL | 5.25 | 5.257 | 1.139 | 1.25 | 7 |
| ERR | 5.25 | 5.151 | 1.126 | 1 | 7 |
| IA | 6 | 5.872 | 1.097 | 2.333 | 7 |
| USU | 6.25 | 5.958 | 1.050 | 3.25 | 7 |
| CBN | 5.5 | 5.138 | 1.486 | 1 | 7 |
| PE | 6 | 5.649 | 0.979 | 1 | 7 |
| USE | 6 | 5.617 | 1.622 | 2 | 10 |
| Construct | Item | Cr.’s | CR | FL | AVE |
|---|---|---|---|---|---|
| Collection | COLL1 | 0.834 | 0.890 | 0.833 | 0.668 |
| COLL2 | 0.792 | ||||
| COLL3 | 0.827 | ||||
| COLL4 | 0.817 | ||||
| Error | ERR1 | 0.857 | 0.903 | 0.806 | 0.700 |
| ERR2 | 0.865 | ||||
| ERR3 | 0.826 | ||||
| ERR4 | 0.847 | ||||
| Improper Access | IA1 | 0.871 | 0.921 | 0.903 | 0.795 |
| IA2 | 0.876 | ||||
| IA3 | 0.895 | ||||
| Unauthorized Secondary Use | USU1 | 0.892 | 0.925 | 0.864 | 0.755 |
| USU2 | 0.874 | ||||
| USU3 | 0.867 | ||||
| USU4 | 0.871 | ||||
| Risk Propensity | RP1 | 0.800 | 0.873 | 0.936 | 0.700 |
| RP2 | 0.692 | ||||
| RP3 | 0.863 | ||||
| Perceived Enjoyment | PE1 | 0.927 | 0.954 | 0.942 | 0.873 |
| PE2 | 0.940 | ||||
| PE3 | 0.921 | ||||
| Childhood Brand Nostalgia | CBN1 | 0.950 | 0.964 | 0.948 | 0.870 |
| CBN2 | 0.937 | ||||
| CBN3 | 0.942 | ||||
| CBN4 | 0.904 |
| Const. | CBN | COLL | ERR | IA | PE | RP | USU |
|---|---|---|---|---|---|---|---|
| CBN | 0.933 | ||||||
| COLL | 0.043 | 0.817 | |||||
| ERR | 0.131 | 0.435 | 0.836 | ||||
| IA | 0.124 | 0.591 | 0.461 | 0.892 | |||
| PE | 0.343 | 0.139 | 0.106 | 0.291 | 0.934 | ||
| RP | 0.040 | 0.259 | 0.152 | 0.135 | 0.110 | 0.837 | |
| USU | 0.127 | 0.539 | 0.386 | 0.836 | 0.309 | 0.111 | 0.869 |
References
- Dinev, T.; Hart, P. An extended privacy calculus model for e-commerce transactions. Inf. Syst. Res. 2006, 17, 61–80. [Google Scholar] [CrossRef]
- Dinev, T.; Mcconnell, A.R.; Smith, H.J. Informing Privacy Research through Information Systems, Psychology, and Behavioral Economics: Thinking Outside the “APCO” Box. Inf. Syst. Res. 2015, 26, 639–655. [Google Scholar] [CrossRef] [Green Version]
- Orth, U.R.; Gal, S. Nostalgic brands as mood boosters. J. Brand Manag. 2012, 19, 666–679. [Google Scholar] [CrossRef]
- Braun-LaTour, K.A.; LaTour, M.S.; Zinkhan, G.M. Using childhood memories to gain insight into brand meaning. J. Mark. 2007, 71, 45–60. [Google Scholar] [CrossRef]
- Harborth, D.; Pape, S. How nostalgic feelings impact Pokémon Go players—Integrating childhood brand nostalgia into the technology acceptance theory. Behav. Inf. Technol. 2020, 39, 1276–1296. [Google Scholar] [CrossRef]
- Merriam-Webster. Definition of “Rose-Colored Glasses”. 2019. Available online: https://www.merriam-webster.com/dictionary/rose-coloredglasses (accessed on 6 November 2020).
- Peterson, A. Pokémon Go Had ’Full Access’ to the Google Accounts of Some iPhone Players. 2016. Available online: https://www.washingtonpost.com/news/the-switch/wp/2016/07/12/pokemon-go-had-full-access-to-the-google-accounts-of-some-iphone-players/ (accessed on 6 November 2020).
- Harborth, D.; Pape, S. Privacy Concerns and Behavior of Pokémon Go Players in Germany. In Privacy and Identity Management. The Smart Revolution. Privacy and Identity 2017. IFIP Advances in Information and Communication Technology; Hansen, M., Kosta, E., Nai-Fovino, I., Fischer-Hübner, S., Eds.; Springer: Cham, Switzerland, 2018; Volume 526, pp. 314–329. [Google Scholar] [CrossRef]
- de Guzman, J.A.; Thilakarathna, K.; Seneviratne, A. Security and Privacy Approaches in Mixed Reality: A Literature Survey. arXiv 2018, arXiv:1802.05797v2. [Google Scholar] [CrossRef] [Green Version]
- Harborth, D.; Hatamian, M.; Tesfay, W.B.; Rannenberg, K. A Two-Pillar Approach to Analyze the Privacy Policies and Resource Access Behaviors of Mobile Augmented Reality Applications. In Proceedings of the Hawaii International Conference on System Sciences (HICSS), Maui, HI, USA, 8–11 January 2019; pp. 5029–5038. [Google Scholar]
- Dacko, S.G. Enabling smart retail settings via mobile augmented reality shopping apps. Technol. Forecast. Soc. Chang. 2017, 124, 243–256. [Google Scholar] [CrossRef] [Green Version]
- Harborth, D. Unfolding Concerns about Augmented Reality Technologies: A Qualitative Analysis of User Perceptions. In Proceedings of the 14th International Conference on Wirtschaftsinformatik (WI 2019), Siegen, Germany, 24–27 February 2019; pp. 1262–1276. [Google Scholar]
- Harborth, D.; Pape, S. Investigating Privacy Concerns related to Mobile Augmented Reality Applications. In Proceedings of the International Conference on Information Systems (ICIS), Munich, Germany, 15–18 December 2019. [Google Scholar]
- Smith, H.J.; Milberg, S.J.; Burke, S.J. Information privacy: Measuring individuals concerns about organizational practices. MIS Q. 1996, 20, 167–196. [Google Scholar] [CrossRef]
- Stewart, K.A.; Segars, A.H. An Empirical Examination of the Concern for Information Privacy Instrument. Inf. Syst. Res. 2002, 13, 36–49. [Google Scholar] [CrossRef]
- Smith, H.J.; Dinev, T.; Xu, H. Theory and Review Information Privacy Research: An Interdisciplinary Review. MIS Q. 2011, 35, 989–1015. [Google Scholar] [CrossRef] [Green Version]
- Phelan, C.; Lampe, C.; Resnick, P. It’s Creepy, But It Doesn’t Bother Me. In Proceedings of the 2016 CHI Conference on Human Factors in Computing Systems, San Jose, CA, USA, 7–12 May 2016; pp. 5372–5384. [Google Scholar] [CrossRef] [Green Version]
- Kahneman, D. Thinking, Fast and Slow; Macmillan: New York, NY, USA, 2011. [Google Scholar]
- Cooper, H.M. Organizing Knowledge Synthesis: A Taxonomy of Literature Reviews. Knowl. Soc. 1988, 1, 104–126. [Google Scholar]
- Odeyinde, O.B. Information Privacy Concerns of undergraduate Students in a Nigerian University and Their Willingness to Provide Personal Information to Transact on the Internet. Ph.D. Thesis, Wilmington University, New Castle, DE, USA, 2013. [Google Scholar]
- Kansal, P. Online privacy concerns and consumer reactions: Insights for future strategies. J. Indian Bus. Res. 2014, 6, 190–212. [Google Scholar] [CrossRef]
- Powell, A.L. Computer anxiety: Comparison of research from the 1990s and 2000s. Comput. Hum. Behav. 2013, 29, 2337–2381. [Google Scholar] [CrossRef]
- Zukowski, T.; Brown, I. Examining the influence of demographic factors on internet users’ information privacy concerns. In Proceedings of the 2007 Annual Research Conference of the South African Institute of Computer Scientists and Information Technologists on IT Research in Developing Countries, Port Elizabeth, South Africa, 2–3 October 2007; ACM: New York, NY, USA, 2007; pp. 197–204. [Google Scholar]
- Lee, H.; Wong, S.F.; Chang, Y. Confirming the effect of Demographic characteristics on Information Privacy Concerns. In Proceedings of the Pacific Asia Conference on Information Systems (PACIS 2016), Chiayi, Taiwan, 27 June–1 July 2016; p. 70. [Google Scholar]
- Cockcroft, S. Information privacy: Culture, legislation and user attitudes. Australas. J. Inf. Syst. 2006, 14. [Google Scholar] [CrossRef]
- Huang, Y.; Liu, W. The impact of privacy concern on users’ usage intention of mobile payment. In Proceedings of the International Conference on Innovation Management and Industrial Engineering (ICIII), Sanya, China, 20–21 October 2012; Volume 3, pp. 90–93. [Google Scholar]
- Yang, H.C. Young Chinese consumers’ social media use, online privacy concerns, and behavioral intents of privacy protection. Int. J. China Mark. 2013, 4, 82–101. [Google Scholar]
- Bellman, S.; Johnson, E.J.; Kobrin, S.J.; Lohse, G.L. International differences in information privacy concerns: A global survey of consumers. Inf. Soc. 2004, 20, 313–324. [Google Scholar] [CrossRef]
- Dinev, T.; Hart, P. Internet privacy concerns and social awareness as determinants of intention to transact. Int. J. Electron. Commer. 2005, 10, 7–29. [Google Scholar] [CrossRef]
- Donthu, N.; Gilliland, D. Observations: The infomercial shopper. J. Advert. Res. 1996, 36, 69–76. [Google Scholar]
- Korzaan, M.; Brooks, N.; Greer, T. Demystifying personality and privacy: An empirical investigation into antecedents of concerns for information privacy. J. Behav. Stud. Bus. 2009, 1, 1–17. [Google Scholar]
- Malhotra, N.K.; Kim, S.S.; Agarwal, J. Internet users’ information privacy concerns (IUIPC): The construct, the scale, and a causal model. Inf. Syst. Res. 2004, 15, 336–355. [Google Scholar] [CrossRef]
- Berhanu, B. Information Privacy Concerns and Social Network Sites in a Low-Income Country: An Empirical Study in Ethiopia. Ph.D. Thesis, Addis Ababa University, Addis Ababa, Ethiopia, 2015. [Google Scholar]
- Yang, H.; Liu, H. Prior negative experience of online disclosure, privacy concerns, and regulatory support in Chinese social media. Chin. J. Commun. 2014, 7, 40–59. [Google Scholar] [CrossRef]
- Yang, H. Young American consumers’ prior negative experience of online disclosure, online privacy concerns, and privacy protection behavioral intent. J. Consum. Satisf. Dissatisfaction Complain. Behav. 2012, 25, 179–202. [Google Scholar]
- Benamati, J.H.; Ozdemir, Z.D.; Smith, H.J. An empirical test of an Antecedents–Privacy Concerns–Outcomes model. J. Inf. Sci. 2016. [Google Scholar] [CrossRef]
- Okazaki, S.; Li, H.; Hirose, M. Consumer privacy concerns and preference for degree of regulatory control. J. Advert. 2009, 38, 63–77. [Google Scholar] [CrossRef] [Green Version]
- Cheung, W.Y.; Wildschut, T.; Sedikides, C.; Hepper, E.G.; Arndt, J.; Vingerhoets, A. Back to the Future: Nostalgia Increases Optimism. Personal. Soc. Psychol. Bull. 2013, 39, 1484–1496. [Google Scholar] [CrossRef] [Green Version]
- Wildschut, T.; Sedikides, C.; Arndt, J.; Routledge, C. Nostalgia: Content, Triggers, Functions. J. Personal. Soc. Psychol. 2006, 91, 975–993. [Google Scholar] [CrossRef] [Green Version]
- Holak, S.L.; Havlena, W.J. Feelings, Fantasies, and Memories: An Examination of the Emotional Components of Nostalgia. J. Bus. Res. 1998, 42, 217–226. [Google Scholar] [CrossRef]
- Shields, A.B.; Johnson, J.W. Childhood brand nostalgia: A new conceptualization and scale development. J. Consum. Behav. 2016, 15, 359–369. [Google Scholar] [CrossRef]
- Holbrook, M.B.; Schindler, R.M. Nostalgic bonding: Exploring the role of nostalgia in the consumption experience. J. Consum. Behav. 2003, 3, 107–127. [Google Scholar] [CrossRef]
- Bainbridge, J. “It is a Pokémon world”: The Pokémon franchise and the environment. Int. J. Cult. Stud. 2014, 17, 399–414. [Google Scholar] [CrossRef]
- Solove, D.J. ‘I’ve Got Nothing To Hide’ and Other Misunderstandings of Privacy. San Diego Law Rev. 2007, 44, 745–773. [Google Scholar]
- Crossler, R.E.; Johnston, A.C.; Lowry, P.B.; Hu, Q.; Warkentin, M.; Baskerville, R. Future directions for behavioral information security research. Comput. Secur. 2013, 32, 90–101. [Google Scholar] [CrossRef]
- Norberg, P.A.; Horne, D.R.; Horne, D.A. The Privacy Paradox: Personal Information Disclosure Intentions versus Behaviors. J. Consum. Aff. 2007, 41, 100–126. [Google Scholar] [CrossRef]
- Harborth, D.; Pape, S. Exploring the Hype: Investigating Technology Acceptance Factors of Pokémon Go. In Proceedings of the 2017 IEEE International Symposium on Mixed and Augmented Reality (ISMAR), Nantes, France, 9–13 October 2017; pp. 155–168. [Google Scholar] [CrossRef]
- Tversky, A.; Kahneman, D. Judgment under Uncertainty: Heuristics and Biases. Science 1974, 185, 1124–1131. [Google Scholar] [CrossRef]
- Petty, R.E.; Cacioppo, J.T. Communication and Persuasion: Central and Peripheral Routes to Attitude Change; Springer: New York, NY, USA, 1986. [Google Scholar]
- Venkatesh, V.; Thong, J.; Xu, X. Consumer Acceptance and User of Information Technology: Extending the Unified Theory of Acceptance and Use of Technology. MIS Q. 2012, 36, 157–178. [Google Scholar] [CrossRef] [Green Version]
- Hair, J.; Hult, G.T.M.; Ringle, C.M.; Sarstedt, M. A Primer on Partial Least Squares Structural Equation Modeling (PLS-SEM); SAGE Publications: Southend Oaks, CA, USA, 2017; p. 384. [Google Scholar]
- Ringle, C.M.; Wende, S.; Becker, J.M. SmartPLS 3. 2015. Available online: www.smartpls.com (accessed on 30 November 2020).
- Podsakoff, P.M.; MacKenzie, S.B.; Lee, J.Y.; Podsakoff, N.P. Common method biases in behavioral research: A critical review of the literature and recommended remedies. J. Appl. Psychol. 2003, 88, 879–903. [Google Scholar] [CrossRef]
- Xu, H.; Teo, H.H.; Tan, B.C.Y.; Agarwal, R. Research Note-Effects of Individual Self-Protection, Industry Self-Regulation, and Government Regulation on Privacy Concerns: A Study of Location-Based Services. Inf. Syst. Res. 2012, 23, 1342–1363. [Google Scholar] [CrossRef]
- Nissenbaum, H. Privacy in Context: Technology, Policy and the Integrity of Social Life; Stanford University Press: Palo Alto, CA, USA, 2010. [Google Scholar]
- Harborth, D.; Pape, S. German Translation of the Unified Theory of Acceptance and Use of Technology 2 (UTAUT2) Questionnaire. 2018, pp. 1–12. Available online: https://ssrn.com/abstract=3147708 (accessed on 6 November 2020).
- Rosen, L.; Whaling, K.; Carrier, L.; Cheever, N.; Rokkum, J. The Media and Technology Usage and Attitudes Scale: An empirical investigation. Comput. Hum. Behav. 2013, 29, 2501–2511. [Google Scholar] [CrossRef] [Green Version]
- Harborth, D.; Pape, S. German Translation of the Concerns for Information Privacy (CFIP) Construct. 2018, pp. 1–12. Available online: https://ssrn.com/abstract=3112207 (accessed on 6 November 2020).
Sample Availability: The used data set is available from the authors. |
| Independent Var. | Path Coeff. |
|---|---|
| H1: VIC | 0.071 |
| H2: RP | 0.182 *** |
| H3a: AGE | 0.094 |
| H3b: GDR | 0.106 * |
| H3c: EDU | −0.020 |
| H3d: EXP | 0.105 * |
| H6: CBN | 0.159 ** |
| (a) Dependent Variable: CFIP | |
| Independent Var. | Path Coeff. |
| H7: CBN | 0.343 *** |
| (b) Dependent Variable: PE | |
| Independent Var. | Path Coeff. |
| H4: CFIP | −0.013 |
| H5: PE | 0.254 *** |
| H8: CBN | −0.024 |
| (c) Dependent Variable: USE | |
| Dependent Var. | Adj. R2 |
| CFIP | 0.073 |
| PE | 0.116 |
| USE | 0.053 |
| (d) Adj. R2 Values | |
| Hypothesis | Result | |
|---|---|---|
| H1: | VIC has a positive effect on CFIP | ✗ |
| H2: | RP has a positive effect on CFIP | ✔ |
| H3a: | Age has a positive effect on CFIP | ✗ |
| H3b: | Females are more concerned about their privacy (CFIP) | ✔ |
| H3c: | EDU has a positive effect on CFIP | ✗ |
| H3d: | EXP has a positive effect on CFIP | ✔ |
| H4: | CFIP have a negative effect on the use behavior of Pokémon Go | ✗ |
| H5: | PE has a positive effect on the use behavior of Pokémon Go | ✔ |
| H6: | CBN has a negative effect on CFIP | ✗ |
| H7: | CBN has a positive effect on PE | ✔ |
| H8: | CBN has a positive effect on the use behavior of Pokémon Go | ✗ |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Harborth, D.; Pape, S. Empirically Investigating Extraneous Influences on the “APCO” Model—Childhood Brand Nostalgia and the Positivity Bias. Future Internet 2020, 12, 220. https://doi.org/10.3390/fi12120220
Harborth D, Pape S. Empirically Investigating Extraneous Influences on the “APCO” Model—Childhood Brand Nostalgia and the Positivity Bias. Future Internet. 2020; 12(12):220. https://doi.org/10.3390/fi12120220
Chicago/Turabian StyleHarborth, David, and Sebastian Pape. 2020. "Empirically Investigating Extraneous Influences on the “APCO” Model—Childhood Brand Nostalgia and the Positivity Bias" Future Internet 12, no. 12: 220. https://doi.org/10.3390/fi12120220
APA StyleHarborth, D., & Pape, S. (2020). Empirically Investigating Extraneous Influences on the “APCO” Model—Childhood Brand Nostalgia and the Positivity Bias. Future Internet, 12(12), 220. https://doi.org/10.3390/fi12120220






