1. Introduction
Over the last decades, the spread of information and communication technologies has triggered a pervasive change at all levels of human society. In an era in which information communication technologies (ICT) shape economies and even institutions [
1], new regulatory mechanisms are needed to order a “hybrid” reality in which technologies and social activities melt in an inextricable whole. This scenario raises new challenges to legal systems and public authorities—traditional regulations and policies often look unsuitable to safeguard rights in digital settings. As witnessed by the evolution of privacy enhancing technologies [
2,
3,
4], legal safeguards are increasingly bound to be conceived and developed together with the technological ones.
The issue can be traced back to “techno-regulation,” an emerging regulatory paradigm that can be in the first place defined as “
the effectuation of norms through technical means at various levels such as rule-making, implementation, monitoring and enforcement” [
5]. Taking hold in all the scenarios where social and economic interactions are mediated by ICT, techno-regulation confronts us with a perspective in which technology is at once subject to, and an active part of, the regulatory process. Due to this hybrid nature, techno-regulation raises issues on the legal level and, at the same time, presents challenges for both computer science and computational legal research. The idea of implementing normative strategies through digital technologies, indeed, calls not only for adequate regulatory frames but also for IT solutions that properly support legal safeguards.
This work presents an ongoing project facing the development of techno-regulatory solutions that focuses, in particular, on the gig economy scenario. Stemming from a collaboration between computational legal scholars and computer scientists that draws also from two university classes “Computational Intelligence and Techno-regulation: paradigms, methods, tools”, a Ph.D. course taught at Department of Computer Science of the University of Salerno, and “Law and computational social science”, a class taught at the Department of Law, Economics, Management and Quantitative Methods of the University of Sannio—the initiative explores the possibility of strengthening existing labor law safeguards for Digital Labor Platforms (hereinafter DLPs) workers by integrating legal and technological remedies. The analysis proposed here focuses on the technological component of a broader techno-regulative strategy currently under development, which will require the active involvement of DLPs and Public Administration. Specifically, we introduce GigAdvisor, a cross-platform web application that has a twofold goal: (i) to increase transparency in the DLPs’ market and (ii) to exploit reputational mechanisms to induce fairer practices among the DLP market’s operators. IT can indeed have a profound impact in promoting trust and cooperation among economic agents especially by means of online communities, enabling the creation of low cost reputation networks of global reach.
The paper is structured as follows.
Section 2 introduces the techno-regulation paradigm, sketching its evolution from its inception in the early 2000s to the present day.
Section 3 describes the scenario of our research, that is, the gig and sharing economy, one of the most challenging fields for the development of techno-regulation solutions.
Section 4 is devoted to the presentation of our case study: after a brief outline of a techno-regulation project’s architecture applied to DLPs, it focuses on
GigAdvisor, the underlyining vision inspiring it and the technological solutions adopted for that purpose.
Section 5 concludes with some considerations about both the project’s future steps and challenges.
2. Origins and Perspectives of Techno-Regulation
In the introduction, we touched on the difficulties that traditional legal remedies come across when attempting to uphold the law in digital environments—the need for technological support for legal safeguards is growing.
On closer inspection, human artifacts have always contributed to shaping the law in terms of content, complexity and ways to protect rights. The “offendicula” known since ancient Roman law—gates and shards of glass put on the edge of boundary walls—are an ante-litteram example of this—a way to protect rights relating to physical goods (an orchard, a house) from threats taking place in the physical world, using physical artifacts. In the information society, where the goods to be protected are often intangible just like the threats against them, technology retains its role. Contexts that could be cited in this regard are manifold, just think about the use scenarios of robots and drones.
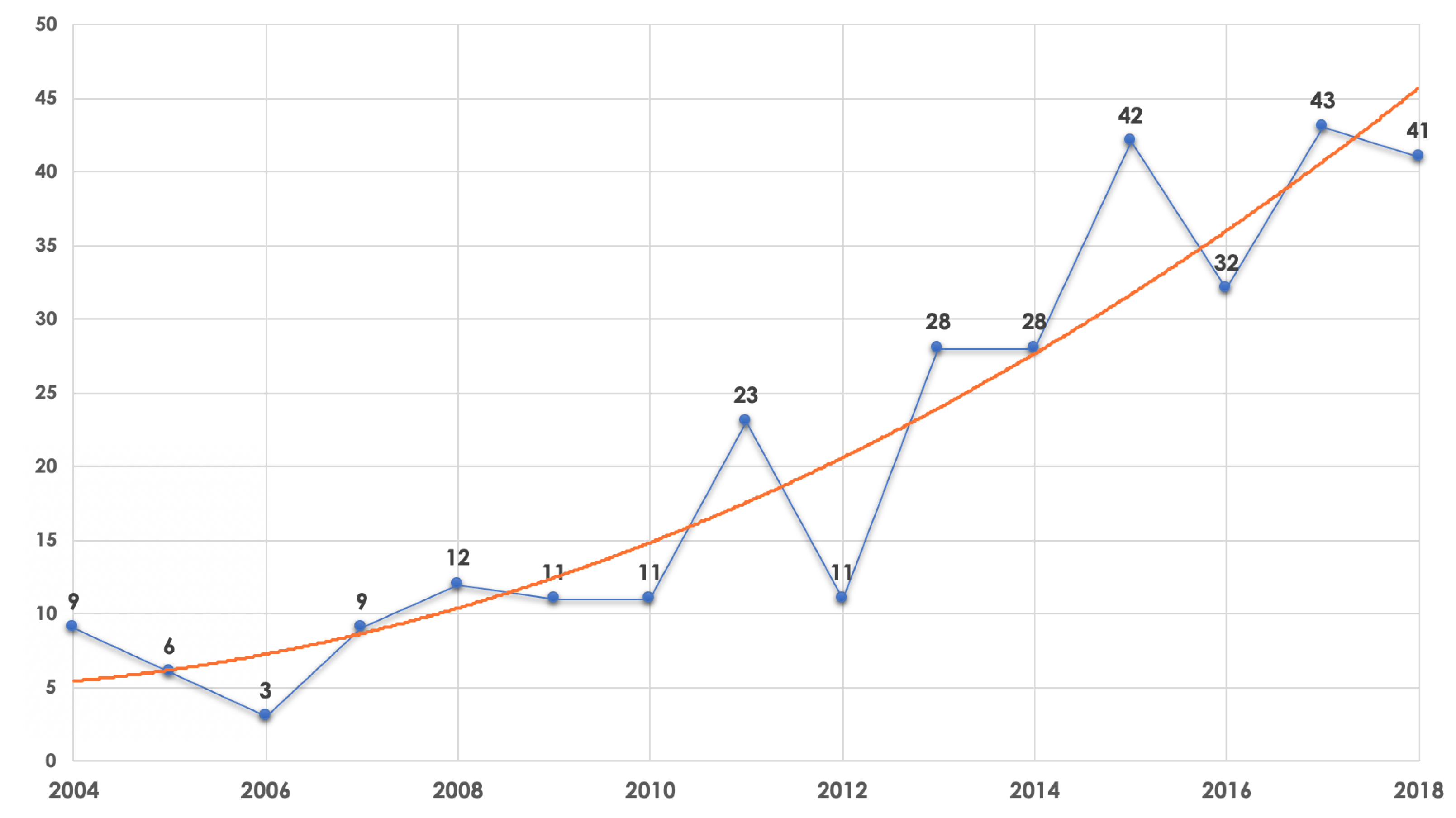
A special place should anyway be acknowledged for the Internet, a universe that is deeply connected with the idea of algorithmic governance. It is no accident that the theoretical reflection on techno-regulation went along with the rise and evolution of the World Wide Web. An indirect confirmation of this relation can be found by analyzing the number of scientific publications dealing with techno-regulation over the years. The trend shows how the development of interest in the regulatory use of technology coincides with the emergence of Web 2.0 (see
Figure 1). The Internet is not only the place where the normative role of code has been identified and discussed for the first time but it has also provided legal scholars with cues about the possibility of purposely using the code, computational tools and web technologies to implement legal safeguards.
In this respect, it makes sense to cast a glance at the contributions coming from those legal scholars that have so far paid more attention to the impact of information technologies on the law and its phenomenology. A cursory review can turn useful to better understand the evolution that led to the emergence of current vision of techno-regulation.
The debate started with a group of scholars that first realized how, throughout the internet, technology plays a regulatory role. Back in 1997, Joel Reidenberg [
6], director of the Fordham Center on Law and Information Policy, highlighted how technical standards and design choices on the web actually impose rules, just like legal rule-making does. Policies—in the narrow sense of protocols but also policies in the broadest sense—are embedded into the design of technological systems, similar to what happens in “privacy by design” [
7]. This vision is taken to the extreme by Lawrence Lessig [
8], from Stanford Center for Internet Society, with his claim that in cyberspace “code is law.”
Over the years, the way of looking at the potential intersection between law and technology has turned into the idea of exploiting technology to regulate economic and social relationships both online and offline. The philosopher of law, Roger Brownsword, was one of the earliest to explicitly state that technological infrastructures supporting our transactions and interactions are set
“to join law, morals and religion” as
“one of the main instruments of social control and order” [
9]. A bolder consideration is that of Primavera De Filippi when claiming that, in some ways, technical rules can be even more effective than traditional legal norms [
10]. While the latter merely stipulates what people shall or shall not do, the former determine what people can or cannot do in the first place [
10]. According to De Filippi, this actually
“eliminates the need for any third party enforcement authority to intervene after the fact, in order to punish those who infringed the law.”The transition we are talking about is somehow accomplished with the concept of “code-driven law” recently sketched to identify “self-executing” statutes and contracts directly written into computer code. In the vision proposed by Mireille Hildebrandt [
11], code-driven law gives rise to a completely new kind of normativity:
“the upcoming integration of computational law into mainstream legal practice” is going to
“transform the very nature of existence of law”.
The definition that best summarizes all the facets of techno-regulation is probably the one proposed in Reference [
12] that describes it as the
“intentional influencing of individuals’ behavior by building norms into technological devices.” In this case, the attention is put not only on automated enforcement of legal norms but also on the possibility to nudge people. The perspective extends the concept of techno-regulation to include the design of technical solutions aimed to affect behaviors by promoting norm compliance through targeted warnings or suggestions [
12,
13]. Ultimately, early forms of ICT-enabled techno-regulation date back to the 2000s with Digital Right Management (DRM), a way to implement copyright law safeguards into technological means by limiting the copy of multimedia contents. Since then, technological development and research at the boundaries between law and computer science has led to more sophisticated ways to integrate regulation and IT.
A review of the most interesting proposals and experiments is offered in Reference [
14]. The authors of Reference [
15] deal with the dangerousness of 3D printing technology for intellectual property because the easy access to 3D printing technology makes it convenient to illegally reproduce physical objects regardless of copyright law. 3D printing threatens traditional intellectual property laws, which were created in an era when copyright infringement of physical objects was yet to come. The researchers have brought forward the legal issues and have attempted to describe a secure-streaming solution partially solving the problem of copyrights in 3D printing. The proposed approach provides the possibility for a copyright owner to limit the number of 3D prints by specifying the maximum number of copies for each manufacturer or end user. Moreover, secured streaming allows to control and detect system compromises and to stop streaming of 3D designs to printers.
Another project deals with online scams, a common risk in modern communications. The authors of Reference [
16] try to tackle the issues by examining whether, in addition to experience and personal skills, technology can help to avoid risks of misuse of personal data, fraud and so on. Researchers show that the elements arousing suspicions in a skeptical and above-average vigilant Internet user can be generalized and instrumentalized through software agents. This allows such agents to help the user and give it warning, even when the user itself may not detect the danger. The authors propose a taxonomy of 18 common scam patterns ranging from the misuse of the online platforms (i.e., the purpose of the online communication platform does not match with the nature of interaction) to geo-localization mismatch (i.e., the IP address from where the scammer is connected conflicts with the declared location.) that might be used to implement an intelligent assistant.
As clearly emerges from the examples just made, the techno-regulation paradigm is already producing tools somehow capable of pursuing the same goals normally pursued by means of traditional legal instruments. We are facing an entirely new dimension of legal regulation showing different interesting aspects. A first one lies in the fact that, instead of having to be entrusted with
ex-post regulations by legal bodies or the police, ‘techno-rules’ can be enforced
ex-ante, making their violation impossible or still very difficult. Moreover, in contrast to traditional legal rules, intrinsically ambiguous and open to interpretation, technorules are highly formalized and leave little room for ambiguity, thus reducing the likelihood of misunderstanding and lawsuits. Based on the current debate (see, among the most recent contributions References [
5,
17,
18,
19]) and from an analysis of experiences made both in private and public contexts, we can sketch a tentative categorization of the directions taken by techno-regulation.
Fact Detection/Classification
Techno-rules and tools are first aimed at identifying facts and individuals to which particular regulatory and/or legal consequences must be linked. Activities of different types can be traced back to this category: (i) detection of breaches of norms (both private regulation and legal provisions); (ii) identification of individuals deserving protection; (iii) identification of individuals responsible for illegal/prohibited conducts.
Enforcement
The second category includes tools aiming to concretely safeguard interests protected by norms and regulations. This first turns into technical solutions materially preventing conducts regarded as harmful or illegal. Alongside these tools, designed to directly
’determine what people can or cannot do in the first place’ [
10], other ‘softer forms’ of (intentional) technological influencing can be mentioned. As already emphasized by scholars in the field of
Law and Technology (see References [
12,
13,
20]), technologies may also be used to persuade or to nudge individuals promoting awareness and the compliance with rules through targeted warnings, messages and suggestions.
3. Techno-Regulation Scenarios: Platform Economy
In
Section 2, we presented techno-regulation as an emergent normative practice, a general perspective in the evolution of legal safeguards meant to be applied potentially in all the scenarios in which economic, social, and personal interactions are mediated by information and communication technology. Within the digital society, there are understandably many contexts that match this description. One of these is undoubtedly represented by
gig-economy, an area of the digital economy in which work is entrusted by organisations operating online platforms to connect customers directly with service-providing workers.
The gig economy is already a significant part of economic life both within the European Union (EU) [
21] and worldwide and it is likely to steadily grow for the foreseeable future: a recent McKinsey report [
22] finds that up to 162 million people in Europe and the United States—20 to 30 percent of the working-age population—engage in some form of independent digital work. It is no coincidence that in recent years an intense and interdisciplinary debate has developed on this topic both at European and international level (see, for example, the interesting analysis proposed in Reference [
23].
Digital labor platforms (DLPs) are the cornerstone of the
gig economy. Over the past decade, they have disrupted both existing business paradigms and employment models the economy relies on. DLPs foster the matching of labor supply and demand by acting as intermediaries. Taking advantage of web technologies, platforms offer new enhanced ways of matching supply and demand of labor minimizing transaction costs with a higher level of efficiency compared to traditional intermediaries. They also provide customer-oriented services and create job opportunities with flexible schedules thanks to a “
pay-as-you-go” workforce [
24]. Platforms are however more than just mere tools for matching labor supply and demand. Using algorithms, they manage many other aspects of labor relations. DLPs give precise instructions about time, place and fulfillment of the service. (
Uber, just to give an example, provide the route and the code of conduct that drivers have to respect [
25]), dynamically determine working conditions [
26] and fix the wage according to criteria embedded in the algorithm parameters such as location, time, and service demand [
27]. Over the years, different types of DLPs have emerged that can be classified according to different criteria—type of services requested; payment and adjudication methods (bid/defined rate); tasks complexity and control over performance. An interesting taxonomy (see
Figure 2) is that proposed in a recent report by the International Labor Organization [
28].
Despite their attractiveness, DLPs are not without critical aspects. A number of controversies have arisen regarding social protection for gig workers—they are not only more vulnerable to fluctuations in the availability of work but, as highlighted in recent research, they face issues with job security, low income and worker status. There are, furthermore, relevant risks resulting from the peculiarity of a remote work relationship taking place online. It is a long list: (i) rating algorithm opacity; (ii) wage-theft via refusal of work done; (iii) unilateral change of terms and conditions and pay (e.g., waivers of cancellation fees, application of discounts); (iv) changes of platforms’ fees; (v) enhanced possibility for monitoring working activities; abusive termination or “deactivation” whilst subject to lock-in effects [
24].
Such a scenario clearly confronts policy makers and legislators with the challenge of drawing up strategies capable of reconciling an effective level of protection for crowd workers and the goal of economic growth. The topic is currently the subject of regulatory and political initiatives at different levels (for an overview about the EU see Reference [
29]). The
European Pillar of Social Rights [
30], to give just a recent example, makes explicit reference to DLPs issues when listing the rights (e.g., health and safety protection, provisions on working time and rest time) to be guaranteed to employees and all workers in non-standard forms of employment.
In general terms, traditional legal remedies threaten to be inadequate to manage ongoing change and this is for several reasons. Some problems are purely legal. For example, the supranational scale of corporate structures and the modularity of technological components—often belonging to different subjects—for example, raise practical problems concerning the identification of a potential counterparty and also of the applicable law itself. In this last respect, as highlighted in Reference [
31], one of the risks connected to the planetary scale of the platforms is the “
choice of law and jurisdiction” that is, the implementation of strategies to choose applicable law according to criteria of convenience (e.g., a lower tax burden).
Other problems are more strictly related to the algorithmic management of crowd work, something that, using the definition proposed in Reference [
32], can be described as the work setting in which “
human jobs are assigned, optimized, and evaluated through algorithms and tracked data”. As highlighted above, in DLPs, algorithmic management reaches beyond directing work and scheduling to control almost all aspects of the job. Möhlmann and Zalmanson [
33] define five characteristics of algorithmic management: (i) continuous tracking of workers’ behavior; (ii) constant performance evaluation of workers from client reviews but also the client’s acceptance or rejection of their work; (iii) automatic implementation of decisions, without human intervention; (iv) workers’ interaction with a “system” rather than humans, depriving them of opportunities for feedback or discussion and negotiation with their supervisor and (v) low transparency stemming from both competitive practices that keep platforms from disclosing how the algorithms work, and from the adaptive nature of the algorithms, whereby the decisions change according to the data being collected.
The development of strategies capable of coping with the complexity of the dynamics mentioned above is a very broad topic that largely transcends the objectives of this paper. What is certain is that, from a computer science point of view, it makes sense to investigate the use of technological tools to support the protection of workers and the management of the DLP market. We will talk about this in the following.
4. Implementing a Techno-Regulation Strategy for Digital Labour Platforms
In this section, we present ongoing research aimed at exploring IT solutions to implement techno-regulatory policies in the DLPs sector. The idea is to experiment with new ways to support, on the technological level, legal policies in the field of gig-economy. The case study presented in the following sections is rooted in a recent paper [
34] speculating about regulatory solutions to achieve higher levels of economic security and social protection for crowd workers and people offering “work on demand via apps” [
24]. To this end, the proposal (to which reference is made for more details) comes up with a “hybrid” strategy integrating different regulatory approaches. On the one hand, as we will see in
Section 4.2, it tries to exploit the power of nudges—more precisely reputational ones—currently at the heart of
Behavioral Law and Economics research. At the same time, far from interpreting nudge as a vehicle for deregulation [
35], it aims to introduce a tighter public scrutiny over the digital labor market so as to enable a more effective control over the compliance with labor law and contracts. In line with the techno-regulation paradigm, authors try to integrate traditional legal safeguards and technological aids going towards the paradigm that Mireille Hildebrandt defines as
“legal protection by design” [
11]. The attempt ends up in what is called
“Integrated Crowdwork System” (hereinafter
ISC), a technological and regulatory public architecture supporting the above mentioned goals.
Legal solutions imagined—we dwell on them just to give an overview of the scenario the case study is placed in—aim, first of all, to favor the intervention of public administrations (national level authority in the proposal) in the crowd work market. Measures envisaged in this vein are of two types—a preemptive authorization mechanism of the DLPs to operate on the market and the mandatory registration in a public record of all the individuals interested in working with DLPs and in being recognized as virtual crowd workers. Other measures are designed for the active protection of workers—tracking and the validity for social security/pension purposes of the work activities carried out in favor of different DLPs; minimum wages; allowances for inactivity periods.
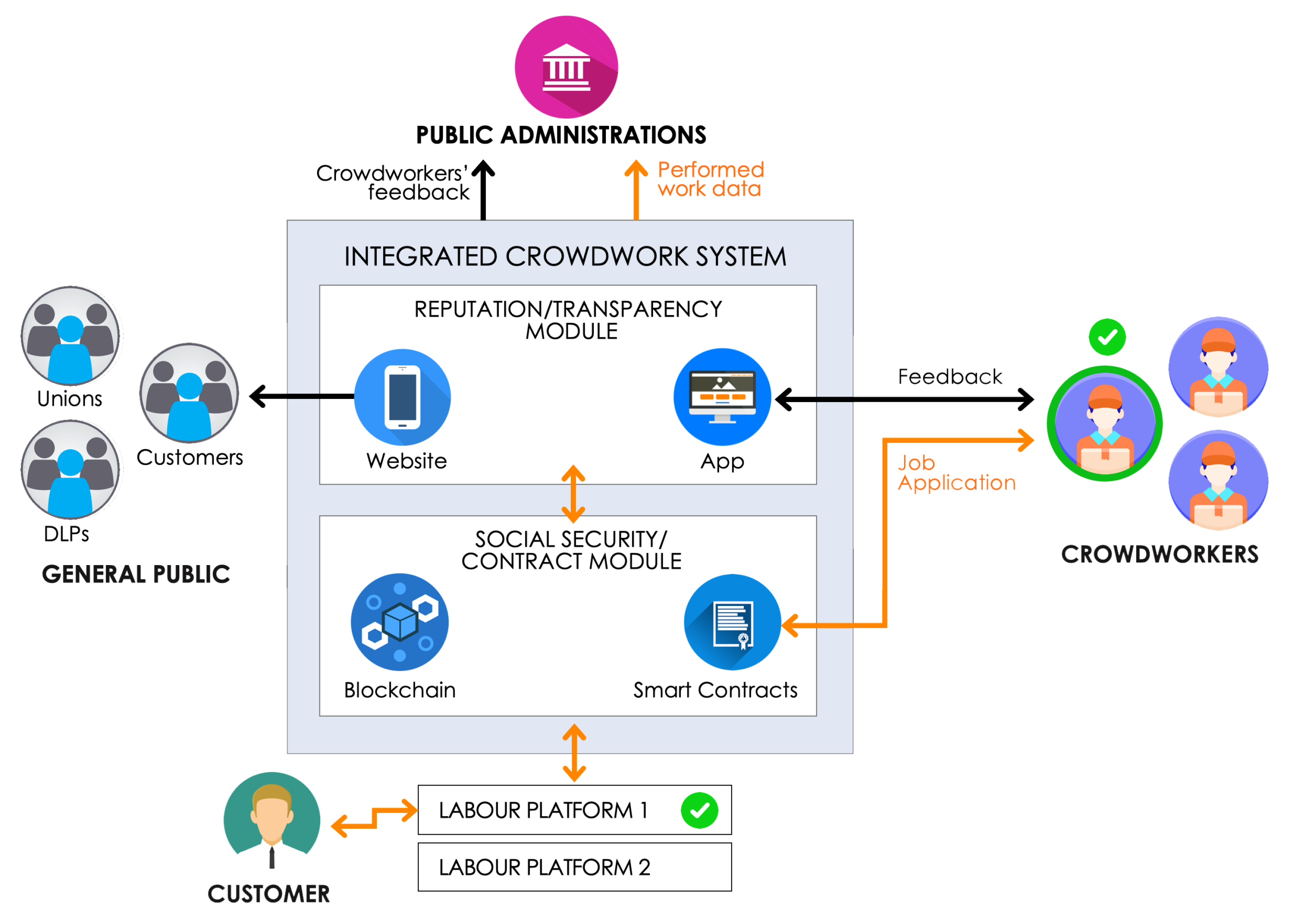
From the technological point of view, the implementation of the ISC should be supported by an integrated architecture conceived as a public intermediate layer, a “trust intermediary” [
36] for the interactions between all the subjects in various ways involved in the market dynamics of the digital work: public administrations (e.g., ministries, labor inspectorates, social security institutions), crowd workers; DLPs; other actors (e.g., labor and industrial associations, potential customers and crowd workers, ordinary citizens).
In general terms, the infrastructure should support the following functions: (i) recording of the labor and financial relations between DLPs and crowd workers; (ii) collecting and exposing to the Public Administrations all data stemming from the interactions between workers and platforms; (iii) guarantee certainty and transparency in transactions; (iv) allowing the stipulation of smart contracts; (v) providing the worker with the possibility to store and have at hand all the financial and social security information of his occasional works; (vi) implementing reputation mechanisms to protect crowd workers.
To implement these functions, authors foresee an architecture based on two modules (see
Figure 3). The
Social Security and Contracts Module should exploit blockchain and smart contracts technology to enable and keep track of any interaction taking place in the digital labor market. The
Reputation/Transparency Module should manage reputation mechanisms as well as public access to crowd work market information using two internal components: a mobile app (allowing workers to enter and interact with the ISC) and a website (allowing public access to data generated by interactions within the digital labor market).
4.1. A Case Study: Techno-Regulation and Reputational Nudge
Drawing on the architecture described above, we started a case study dealing with the development of one of the ISC’s components. We focused, in this vein, on the Reputation/Transparency Module that, for understandable reasons, can be more easily developed and tested. The implementation of a review platform, actually, can be tackled with reasonable technical effort and without necessarily involving all the actors of the architecture. On the other hand, the reputation is capable of playing a significant role in influencing the behavior of subjects operating in the digital market.
As resulting from a literature dating back to the 2000s and despite their undeniable limitations (see, among the others, References [
37,
38,
39] reputation mechanisms can play a significant role in tackling problems related to trust and contracts’ compliance, especially in contexts where transactions take place between people/partners unfamiliar and at a distance [
40]. They seems to be a valuable support to integrate the more established institutions for building trust (such as formal contracts) in electronic environments where such contractual guarantees cannot be efficiently enforced. It is useful to note that reputational systems, usually concerning sellers [
41,
42] rather than buyers [
43], are indeed found to achieve important global effects, that is, keeping prices lower (for a review, see Reference [
44]). The potential applications of online reputation mechanisms go beyond the relatively narrow domain of trust building in electronic marketplaces. The appeal of reputation mechanisms is that, when they work, they facilitate cooperation without the need for costly enforcement institutions. They have, therefore, the potential of providing more economically efficient outcomes in a wide range of moral hazard settings where societies currently rely on the threat of litigation in order to induce cooperation.
Reputation, on the other hand, is an interesting topic also because it represents one of the frontiers in the future developments of technoregulation, identified up to now above all with hard-coded, (almost) unavoidable legal rules that are enabled, or inhibited, through the technology. As highlighted in Reference [
12], by focusing exclusively on regulation through the use of technologies, this domain “
excludes other, “softer”, less “legal” forms of influencing [...] the fact that technologies may also be used to persuade, or to nudge, for example, is left un(der)addressed.” There are indeed scholars in the field of
Law & Technology that mention softer forms of (intentional) technological influencing [
13,
20,
45] but too often nudging, and other forms of more gentle persuasion, largely falls outside the scope of the current debate on techno-regulation. Yet, in recent years, nudge—“
any small feature of the environment that attracts people’s attention and alters their behavior but does so in a way that does not compel” [
46]—has become an inspiring reference point in the current debate about the frontiers of policy design (see, among the others, Reference [
47]).
In the light of the above we decided to explore the integration of techno-regulatory tools with nudge strategies. We focused, in particular, on reputation mechanisms that have proven to be a powerful ally in triggering norm compliance and cooperation in digital environments [
48,
49,
50]. As a matter of fact, recent history of DLPs (see, for instance, the case of
Turkopticon [
51]), which shows how the assignment of ratings can push platforms to modify their behavior to avoid drawbacks deriving from bad reputation.
4.2. The Techno-Regulatory Model: Nudging by Means of Information and Reputation
The development of the
Reputation/Tranparency Module has been preceded by the definition of a regulatory model: a comprehensive definition of the normative goals and of the mechanism devised to accomplish them. Our regulatory model revolves around “
information nudge” [
46,
52,
53], that is, affecting individual and social behaviors by gathering, processing, and sharing different kinds of information. In more detail, the idea is to put together an
information asset encompassing: (i)
raw data (e.g., the amount of smart contracts or transactions for each DLP, spatial distribution of DLP); (ii)
knowledge extracted by applying computational heuristics to raw data (e.g., insights about DLPs behavioral patterns like unfair workers rounding or other misconducts); (iii)
reputational data (e.g., structured feedback provided by crowd workers, public administrations or unions about DLPs activity). In order to get an effective regulatory impact on the digital labor market, our model relies on two main factors—the number and variety of individuals reached by information and the intrinsic qualities of data conveyed by the
Reputation/Tranparency Module. With regard to the first point, the goal is to reach different categories of entities:
Crowd workers: they can get an idea about the fairness of DLPs’ conduct, and thus make more informed decisions when applying for gigs.
Public authorities: administrations (e.g., labor inspectorates) can rely on trustable information highlighting DLP misconduct from an administrative and legal standpoint (e.g., breaches of labor or even criminal law).
DLPs: they find all the feedback on their activity in one place, having the possibility of observing the evaluations reserved for competitors. This increases the regulatory effect of the system because a bad reputation affects the possibility of finding crowd workers; on the “judgment” of public institutions; on public opinion.
General public: DLP’s customers, people potentially interested in gigs, unions can draw relevant information from DLPs ratings.
The quality of the information asset will be pursued, focusing on the following criteria:
4.3. An App for Techno-Nudging: GigAdvisor
GigAdvisor is a cross-platform experimental application aimed at implementing the “techno-nudging” [
57] perspective according to the model described in
Section 4.1. The tool, conceived to be part of the
ISC infrastructure (
Figure 3) should allow crowd workers to send and publish (controlled) feedback about their work experiences. Below, we detail the envisioned architecture and functionalities.
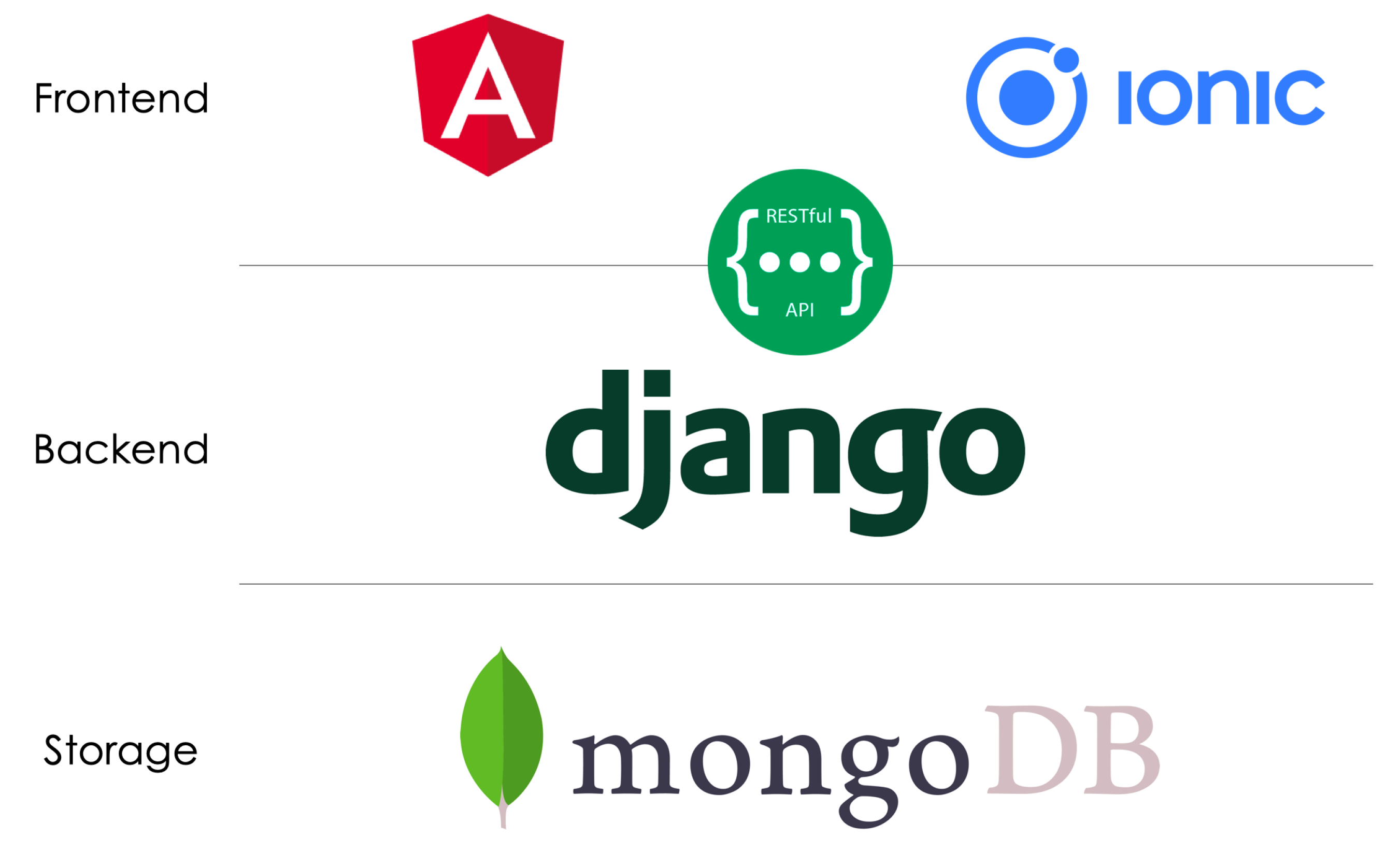
4.3.1. Architecture
GigAdvisor architecture integrates a website and a mobile application. To do that, we built the following 3-layer architecture (see
Figure 4):
Frontend: this layer provides the user interface by using AngularJS [
58] for the website and the Ionic [
59] framework for the mobile app.
Backend: the layer is developed by means of Django [
60], a high-level Python Web framework that encourages rapid development and clean, pragmatic design. Django is free, open source, and provides high scalability and seamless integration with all the powerful libraries Python could offer, such as the Natural Language Toolkit [
61], a leading platform for building Python programs to work with human language data [
62].
Storage: in the Storage layer all data about platforms and crowd workers are stored. We selected MongoDB [
63], an open source NoSQL database which grants flexibility and scalability.
4.3.2. Functionalities
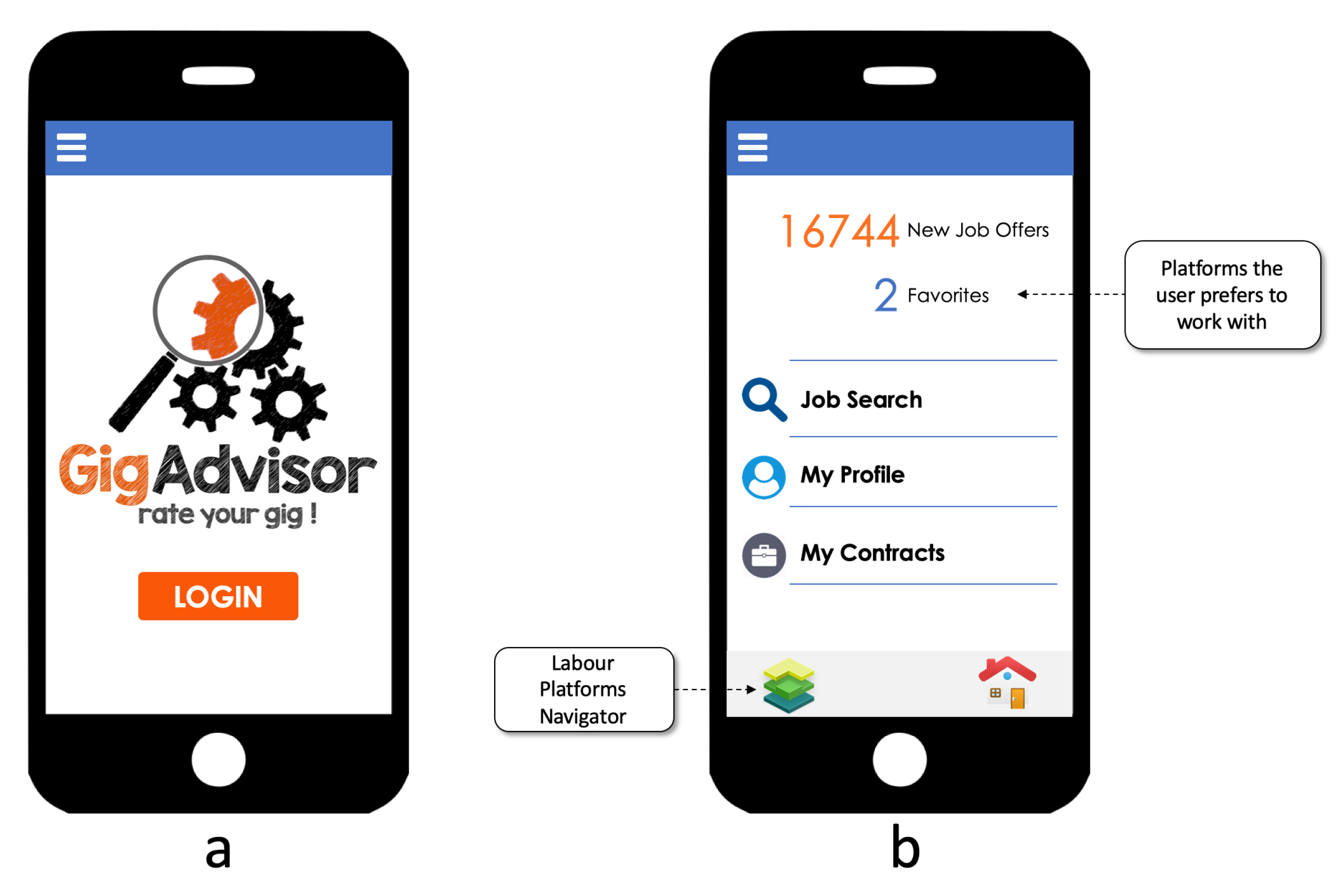
The first release of
GigAdvisor provides a series of functionalities—beyond basic ones such as sign in, login, and logout (
Figure 5a)—to meet the need of visualizing data and providing a reputation mechanism for DLPs. Such functionalities, representing just the starting point of an ongoing project, can be summarized as follows.
Dashboard
The Dashboard (
Figure 5b) shows (top-center) the amount of job offers, the number of favorite platforms which have published a job offer and a list box to browse personal and DLPs information. The list box provides three options: (i)
Job Search which allows the user to search for a job and where appropriate apply for that job; (ii)
My Profile accessing to the user’s personal profile with all its data; (iii)
My Contracts to visualize user’s contracts summary over the time. At bottom-right in the Dashboard the user finds the “Home” button to go back to the Dashboard (always visible) and bottom-left the “Labor Platforms navigator” button to show all the platforms signed into the system.
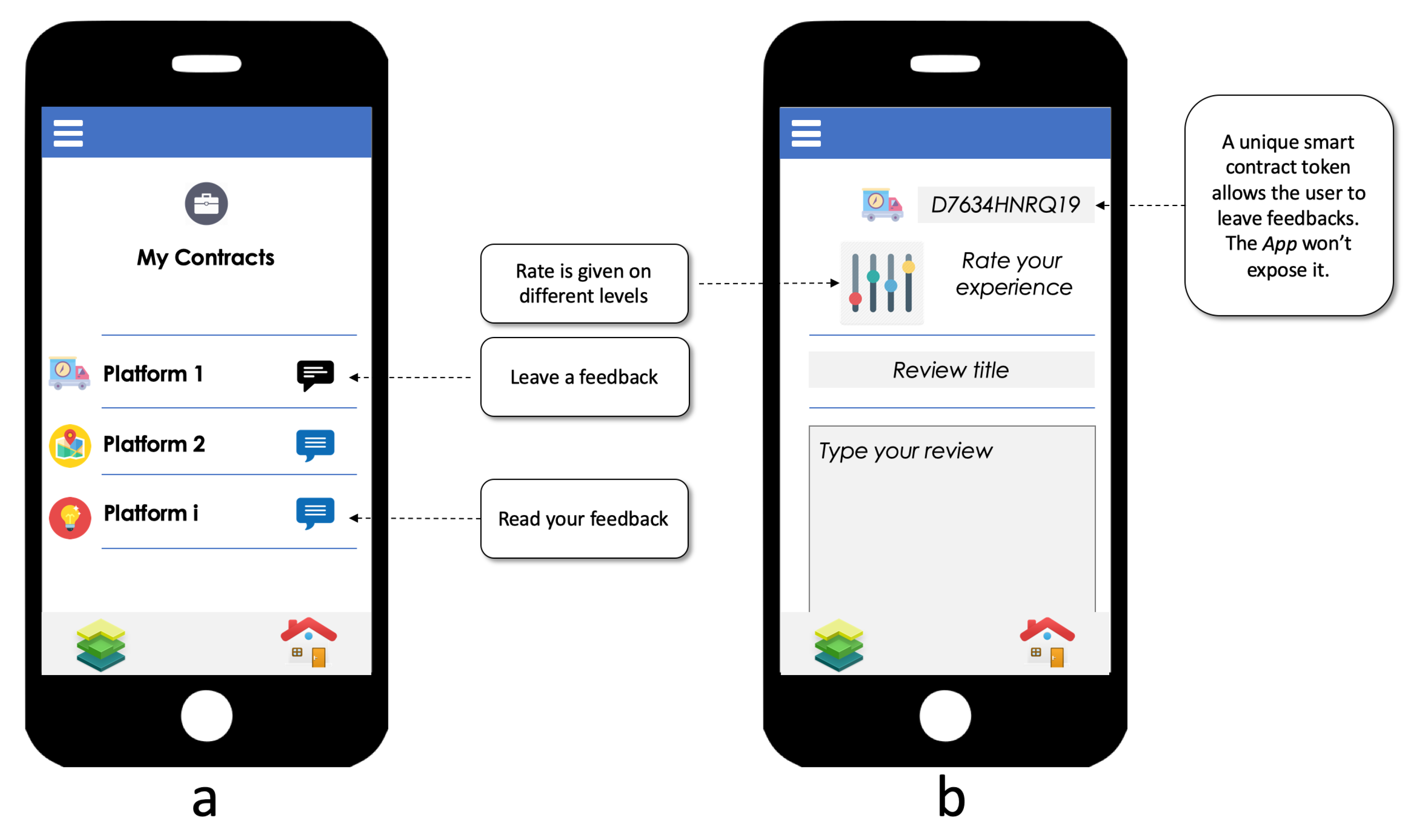
My Contracts
Through “My Contracts” the user visualizes his job history in the gig-economy (see
Figure 6a). A list box includes all the gig-works the user performed over the time (virtually in the blockchain, see
Section 4) showing the (i) DLP logo, (ii) DLP’s name, (iii) a button which indicates—according to the color changing—the chances to insert or read a feedback about that DLP.
By clicking on “leave a feedback” (
Figure 6b) the tool shows the unique token associated with the user’s smart contracts (binding the user, the platform and the job) which is mandatory to perform the task. With this method only true crowd workers can leave a feedback on a DLP. This token in any case will stay private as personal crowd worker data in order to prevent the identification of the user and potentially negative consequences like, for instance, reprisals on the part of the DLP.
The architecture foreseen in
Figure 3 is very complex and requires the involvement of the DLPs and the Public Administration, and it foresees a smart contracts subsystem. Thus, in the Beta version of
GigAdvisor the token linked with the smart contracts concluded will not be exploited. In the absence of smart contracts, crowd workers will still be able to leave feedback to DLPs they worked for, with the same difference there is in main Social Networks (e.g., Twitter, Facebook, Instagram) between a verified and not verified account. In other words, the reviews associated with smart contracts by means of the unique token will be tagged with an
“authenticity mark”.
In the “Leave a feedback” section the user is allowed to (i) evaluate their experience with the DLP on various levels, by means of a “graphic equalizer”, (ii) give a title to his review, and (iii) write a review to tell all the audience their opinion. The equalizer lets the user evaluate the platforms according to a variety of criteria such as fairness, payment timeliness and appropriateness that are full of legal implications. A specific attention has been reserved to other problems frequently faced by crowd workers interacting with DLPs. We have included in the evaluation grid a series of issues identified in recent literature [
64] and detailed in
Table 1. The “graphic equalizer,” in the first release, allows to rate on standard criteria. The evaluation grid developed so far is the same for each DLP category. In the future we aim to draw up customized evaluation grids for each type of DLP—the criteria for a food delivery platform could be slightly different than the ones for evaluating a micro-tasking platform.
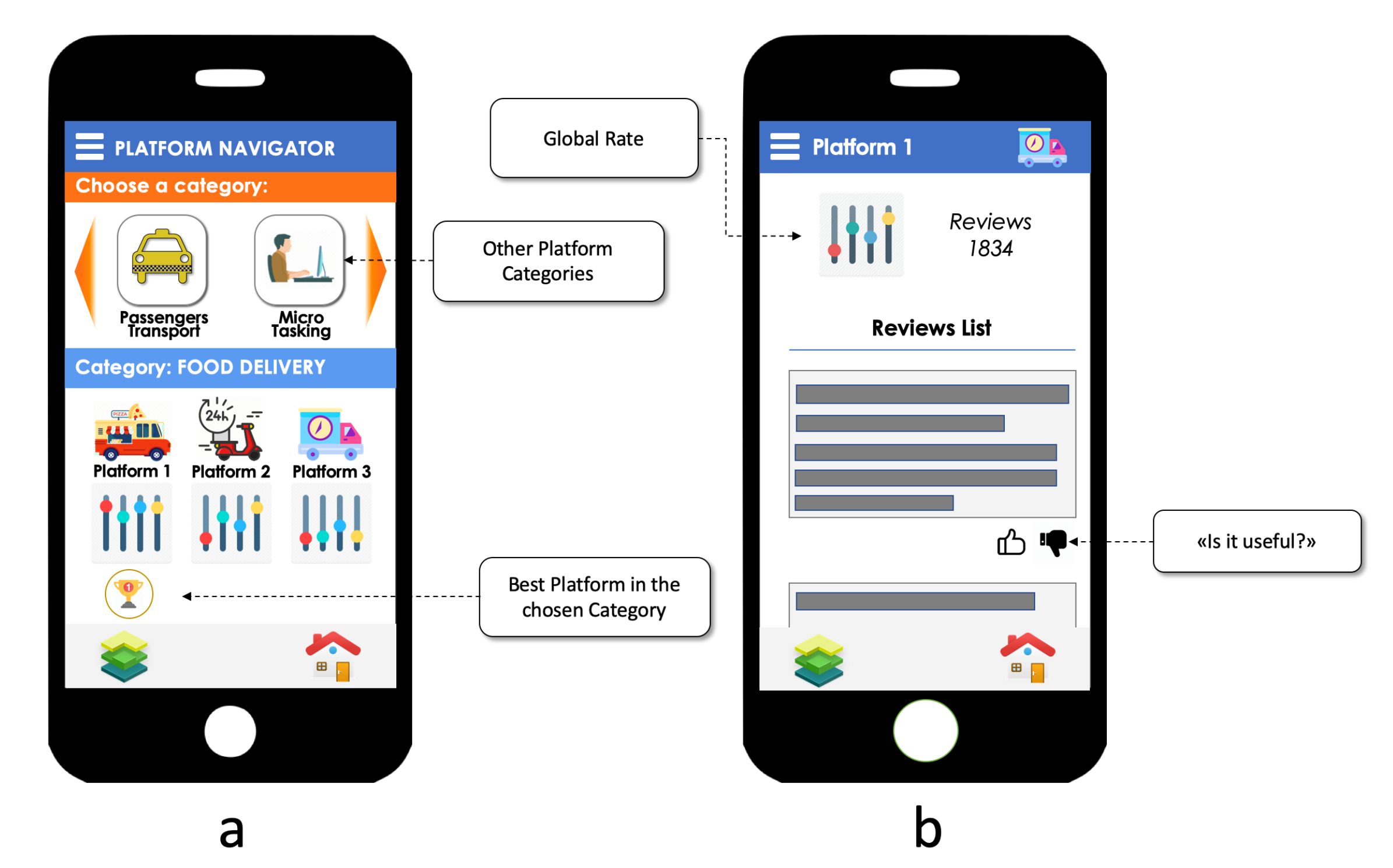
Labour Platforms Navigator
The Labour Platforms Navigator shows a list group of DLPs (
Figure 7a). Once the user selects a DLP of interest (see
Figure 7b)it is possible to visualize: the rating for that platform which is calculated taking into account (i) the amount of feedback received by the DLP, (ii) sentiment of the received feedback [
54,
69], (iii) rating from the “graphic equalizer”, (iv) timing (e.g., a DLP which was high-rated one year before with no other new feedback should be downgraded), and (v) utility of feedback.
In addition, by means “useful/not useful” button, it is possible to rate the feedback by expressing how useful the same has been. According to a dating back literature (see, among the first contribution on the topics, Reference [
70]), the “evaluation of evaluators” is essential to the emergence of social norms and cooperation.
Clearly some of the showed functionalities are just “ready” in GigAdvisor, because the whole projects lacks of the Social Security and Contracts Module. Indeed, for example, in the Beta version of GigAdvisor a part of the DLPs (the most famous) is directly added but in the meantime a user will be allowed to add a new DLP he worked for.
5. Conclusions
The research presented above is still ongoing. The beta version of the GigAdvisor app is close to the release. A series of developments is already foreseen.
We are planning a trial involving crowdworkers associations so to make them available for free GigAdvisor. The trial will have several goals relating both technical aspects and overall project design choices: (i) gathering feedback on system design and functionalities; (ii) getting insights regarding additional functionalities (e.g., is the rating expressed through the right parameters or more are needed?); (iii) identifying possibile scalability and privacy problems; (iv) gaining evidence about the effectivenes of the reputation mechanisms implemented; (v) gathering data for machine learning, knowledge extraction tasks (e.g., where do the feedback come from? From which categories of workers?).
Another part of future efforts will be devoted to the upgrade of the app. As previously said, the application has been conceived in a modular way, so to allow the gradual addition of new functionalities. We have already figured out a couple of interesting developments in this perspective.
A first development will be that of providing GigAdvisor with a social-oriented component. The Social module would act as the virtual community of practice where crowdworkers can share and discuss about their experience. Another part of our efforts will be put towards the application of more advanced knowledge extraction methods to the data generated by users interacting with the app. The idea is that of endowing GigAdvisor with a Knowledge mining module with functionalities like those provided by AirBnB. AirBnB provides, for instance, a booking request’s trend prediction mechanism based upon the past timeline of bookings. Those predictions are shown to the hosts so that they can adjust their prices to the demand trends. Following the same line, in the case of crowdworkers, geo-tagged predictions about time-based patterns in the work demand could help workers in the arranging their time and job.
In more general terms, the project provided food for thought about fundamental issues in technoregulation. Actually, the impact of the techno-regulatory strategies can be more or less positive depending on our ability to intelligently merge principles, rules and priorities defined at the legal level within the technologies gradually available. The risks are many and go from the lack of transparency and controllability produced when norms and values are embedded into software code that remain hidden from view and unfathomable [
17,
20], to the potential sillness of technoregulatory tools unable to adapt to the concrete law enforcement context. In this scenario, research on the borders between AI and law can give an essential contribution to make more transparent, explainable [
71] and therefore open to criticism the functioning of the techniques used and, at the same time, more adaptive and smart the legal enforcement mediated by technology.
Against this backdrop, new and strongly interdisciplinary research approaches are needed. Readapting the words used by Mireille Hildebrandt’s [
72] techno-regulation requires a novel approach to law making addressing the challenges of technology, legitimacy, and political-legal theory, as only a “constructive and collaborative effort to migrate law from books to other technologies can ensure that techno-regulation becomes reality,” safeguarding the fundamental values underlying privacy, identity and democracy in tomorrow’s intelligent world.