A Lightweight Authentication and Key Agreement Protocol for IoT-Enabled Smart Grid System
Abstract
1. Introduction
1.1. Related Work
1.2. Motivation
1.3. Contribution
- We introduce an insider attack and take Zhang et al.’s protocol [22] as an example to improve the security. We first analyze the security of Zhang et al.’s protocol [22] and point out the reasons why their protocol cannot resist insider attack. Then, we describe the detailed steps of an insider attack, and show the potential threats of insider attack. In addition, we have made improvements to Zhang et al.’s protocol to resist insider attack.
- We analyze the security and performance of our proposed protocol and the results show that the protocol has strong security and efficiency. We analyze the security of the improved protocol in detail and prove the security of the protocol under the real-or-random oracle model. Through informal analysis, it has been shown that this protocol can resist common attacks, including insider attack. After that, we compare the proposed protocol with other schemes, indicating that the improved protocol is still lightweight.
2. Preliminaries
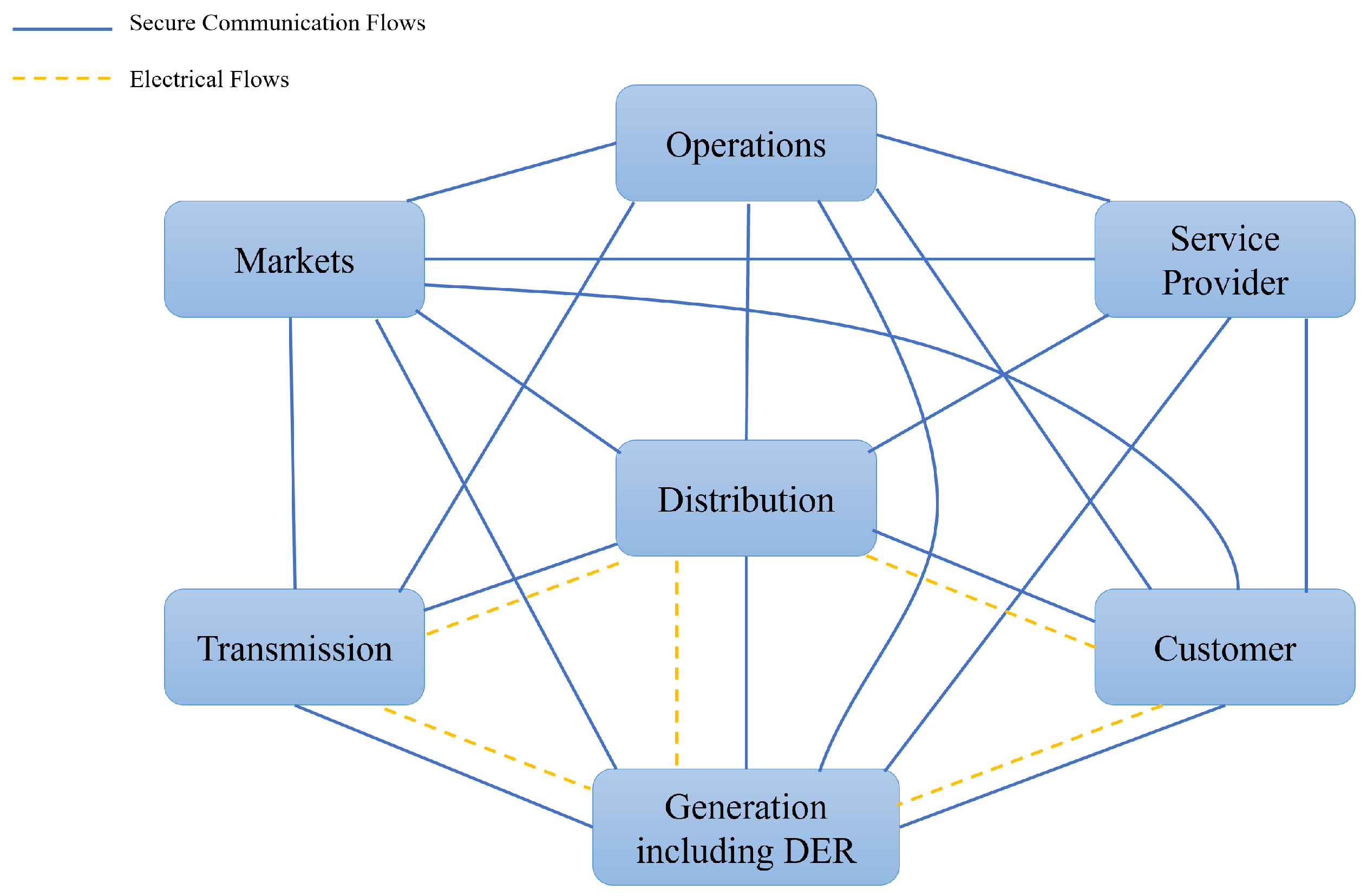
2.1. Communication Model
2.2. Threat Model
2.3. Security Goals
- Mutual authentication: Each session between the smart meter and service provider requires complete mutual authentication. This is to ensure that both sides of the communication are credible.
- Generate security session key: The security scheme should generate a temporary session key, which is confidential and unpredictable to any third party.
- Resist known security attacks: The security scheme should resist common attacks, such as man in the middle attack, replay attack, and so on.
- Provide SM’s anonymity: The scheme usually only needs to ensure that the third party cannot obtain the identity information of the smart meter. However, a good security protocol should make the service provider unable to figure out whether two sessions are possessed by the same SM or not.
3. Some Flaws of Zhang et al.’s Scheme
3.1. Review of Zhang et al.’s Scheme
3.1.1. Registration Phase
- The smart meter firstly chooses a random value with high entropy . Then, sends its identification and to the service provider securely.
- After receiving the messages from , computes , where means the identification of and s means the master key of . Then, calculates where means the secure symmetric encryption with secret key s. Finally, stores into its dynamic verification table and returns to via a secure channel.
- receives from , and stores into its own tamper-resistant device.
3.1.2. Authentication and Key Agreement Phase
- When the smart meter attempts to start the communication with the service provider , produces a random value with high entropy temporarily. After that, calculates and sends to through a public channel.
- decrypts with its master key s where . Then, calculates , and , and checks whether is in its dynamic verification table or not. There are two columns, and , in the table, and the values of both columns are blank at the beginning. When is successfully registered, the generated would be stored in column . If is found in , fills in the value of to . Once the value of can be found in the table, obtains and computes . Next, chooses a random value with high entropy and generates a temporary key . After this, gets the session key . To authenticate , calculates with the secret key k and returns to .
- calculates and uses to decrypt that . Then, checks whether or not. If this verification is valid, computes . Next, computes and sends to .
- After receiving from , checks whether matches with . If it holds, displaces with where . Then, calculates and returns to .
- checks whether . If this verification is valid, replaces with . After that, and apply the session key into the communication.
3.2. Security Flaws of Zhang et al.’s Scheme
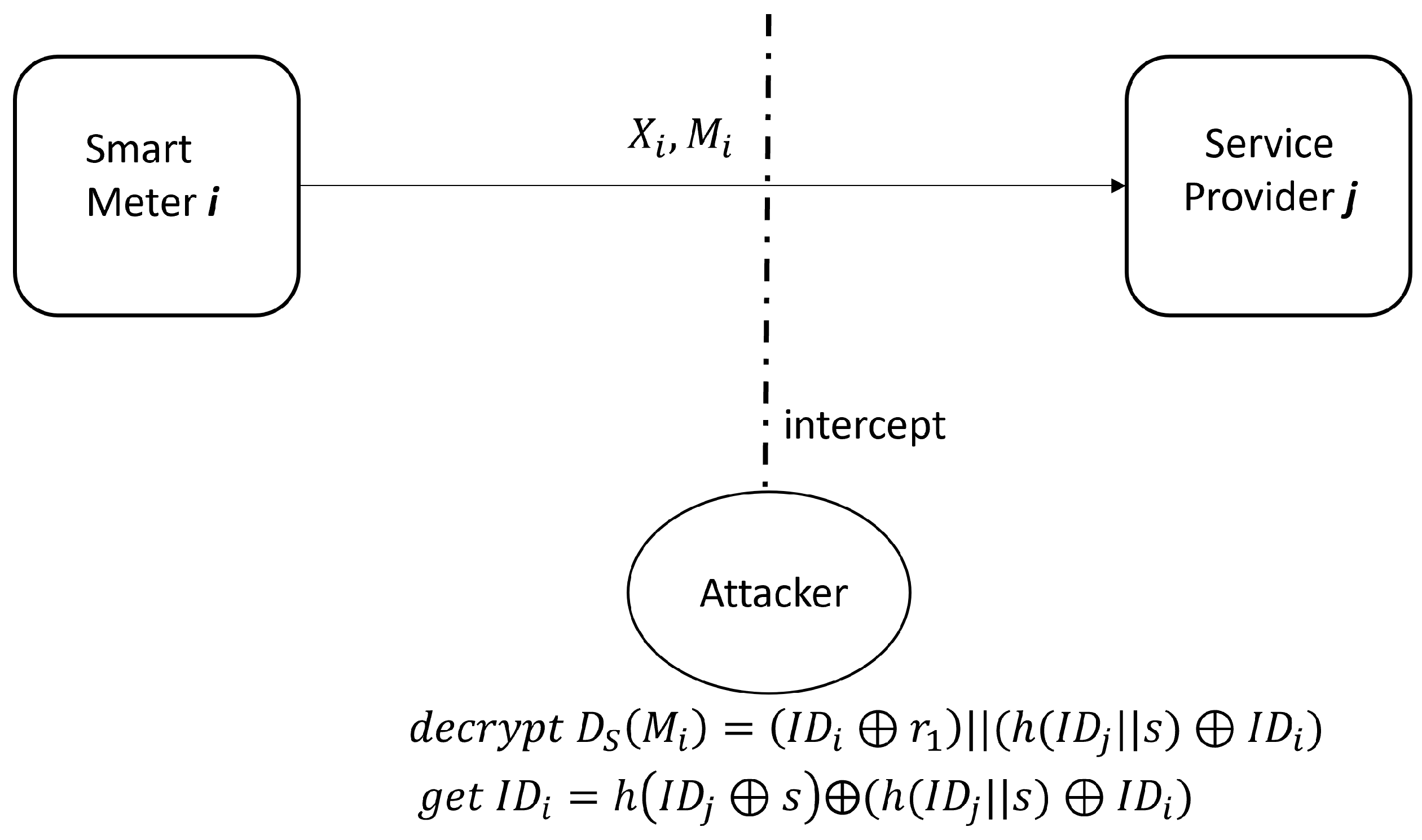
- Step 1. The attacker firstly registers to as a legitimate user, and obtains his identity information , and after successful registration. He/she can decrypt with key s to obtain , where . The phase is shown in Figure 3.
- Step 2. During the protocol process between a registered smart meter and , the attacker intercepts sent by to . Then, he/she decrypts the information with key s to obtain and , where generally.
- Step 3. The attacker computes , where comes from step 2 and comes from step 1. This phase is shown in Figure 4.
- The loss of smart meter anonymity: Through Step 3 above, the attacker obtains of legitimate , which directly leads to the loss of the user’s anonymity.
- Impersonate attack: The attacker can also obtain stored in by calculating and from the intercepted message. This means that all information stored by is obtained by the attacker. The attacker can impersonate and communicate with .
- Session key compromise attack: If the attacker knows the information , he/she can compute and fake by sending to . After receiving the message from , the attacker is able to execute all operations performed by step by step, and gets the correct and returns correct to .
- Permanent denial of service attack: Because the scheme uses a dynamic authentication table to verify ’s identity, will lose the ability of communication with permanently when the attacker disguises twice in succession. In abstract, this scheme only retains the current and last session credentials of in the verification table of . Once the attacker successfully disguises more than two times, the session credentials of will expire, and this process is irreversible.
3.3. Reasons for the Weakness
4. The Improved Scheme
4.1. Registration Phase
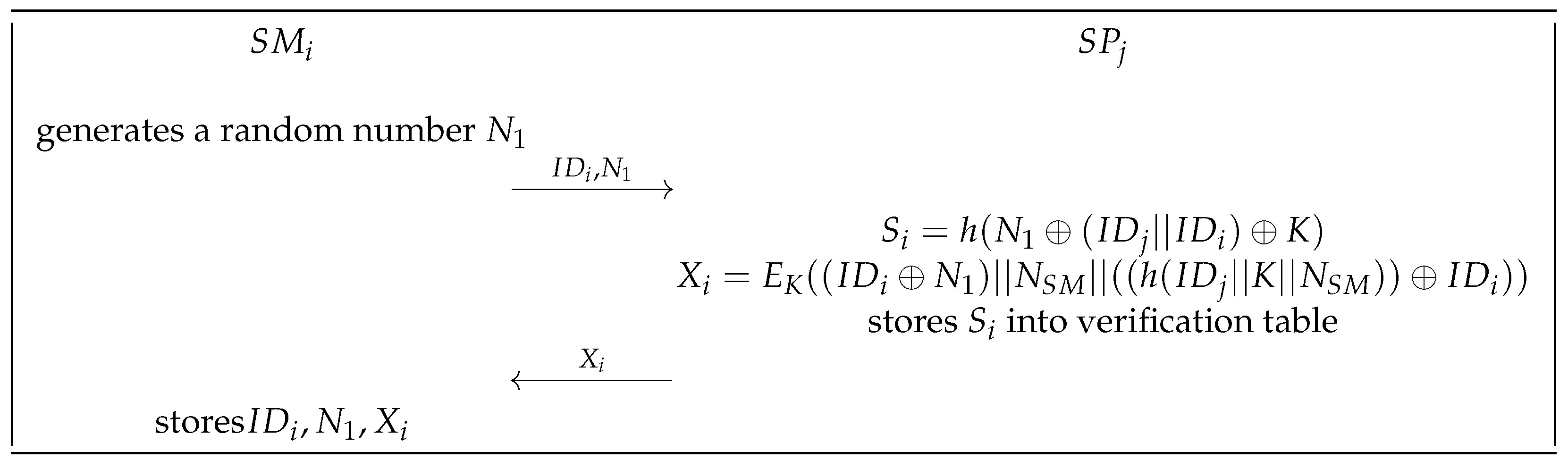
- The smart meter firstly generates a random integer . Then, sends its identification and to via a secure channel.
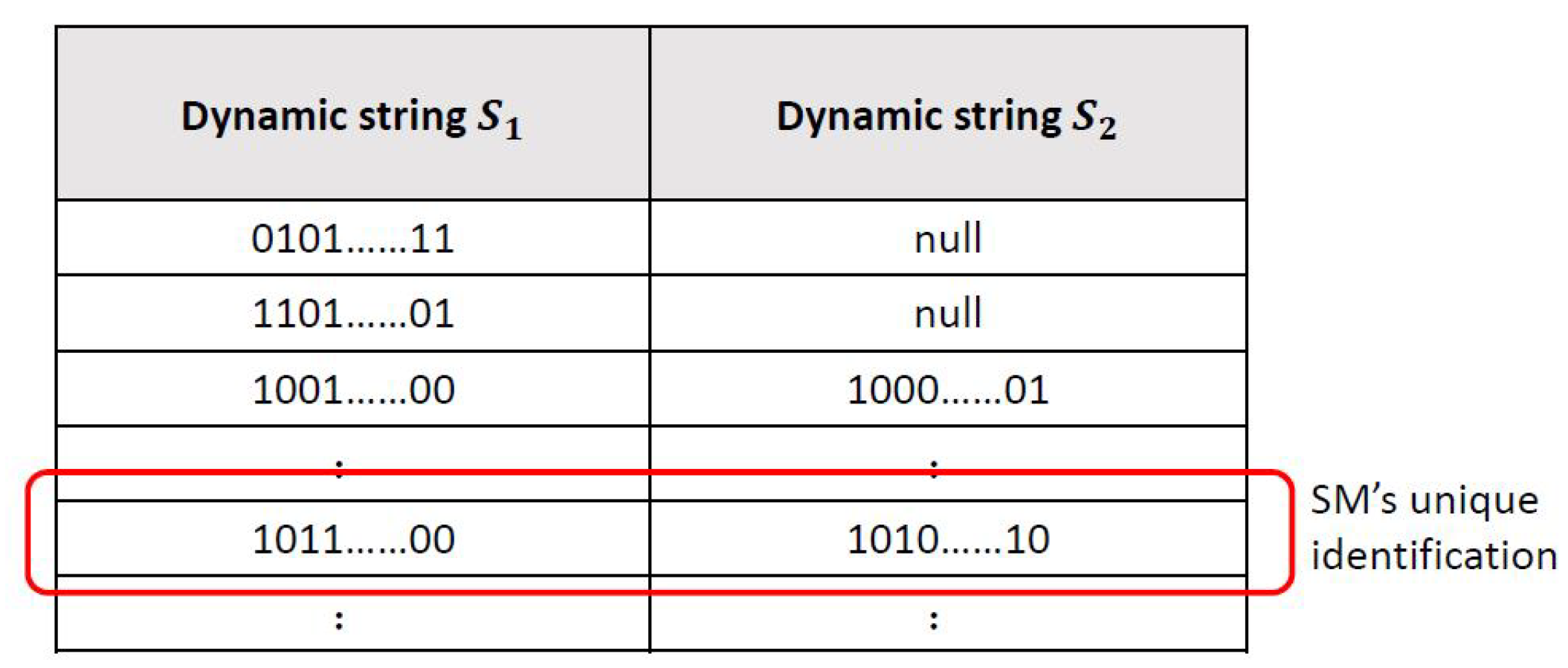
- After receiving the message from , computes , where K means the master key of the service providers. Next, calculates , where is a high entropy random number generated for . Then, stores into its dynamic verification table. The dynamic verification table is shown in Figure 6. There are two columns and in the table, and the values of both columns are blank at the beginning. When is successfully registered, the generated will be stored in a new blank of column . Each row in the table represents a registered smart meter. Finally, returns to securely.
- receives from , and stores into its own tamper-resistant device.
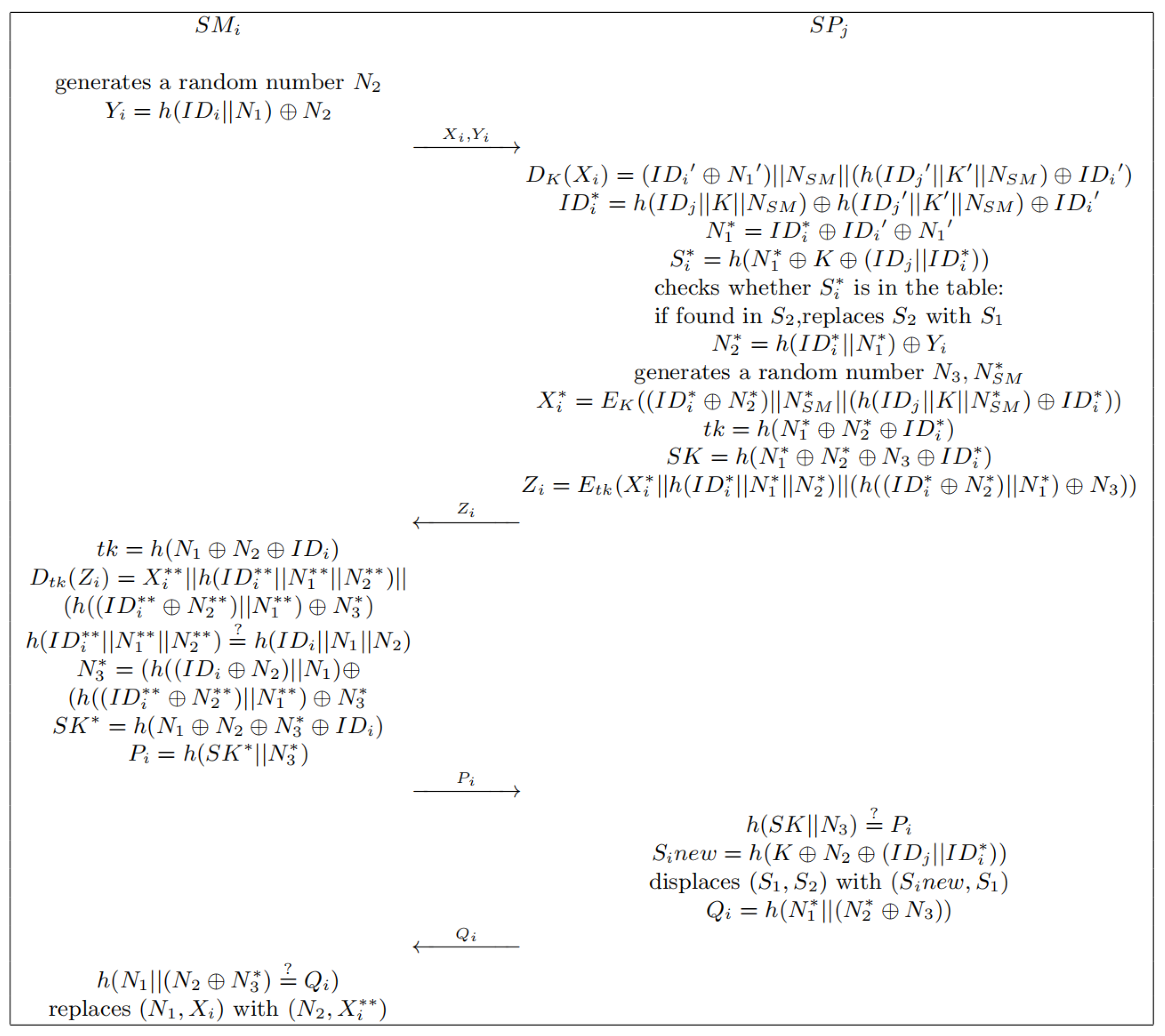
4.2. Authentication and Key Agreement Phase
- When is willing to build the communication with the , needs to produce a high entropy random number temporarily. After that, calculates and sends to through a public channel.
- decrypts with its master key K where . Then, can calculate , and , and checks whether can be found in its dynamic verification table or not. If is found in , fills in the value of to . Once the value of can be found in the table, can obtain . Next, chooses high entropy random numbers and . It can compute and generate a temporary key . After this, can obtain the session key . To authenticate , calculates with secret key and returns to .
- calculates and uses to decrypt that . Then, checks whether or not. If this verification is valid, can compute . Next, computes and sends to .
- After receiving message from , makes a check on whether matches with . If it holds, displaces with where . Then, calculates and returns to .
- checks whether . If this verification is valid, replaces with . After that, and apply the session key in the communication.
5. Security Analysis of the Improved Scheme
5.1. Formal Security Analysis
Security Model
- Execute (, ): This module is built to simulate a passive attack. An attacker can obtain all messages sent by and through this operation.
- Send (E, M): This operation aims at simulating an active attack. An attacker can send message M to any or , and or would perform corresponding steps according to the protocol. The corresponding information would also be returned to the attacker.
- Corrupt (E): This operation is applied to simulate the forward security. The attacker can obtain the leaked long-term secret information, such as ’s master key or ’s identity (but not both).
- Test (E): This operation is used to return the session key or a randomly generated key. This response depends on a random bit b. If b is equal to 1, the query returns the session key; if b equals 0, the query returns a random key.
5.2. Informal Security Analysis
5.2.1. Insider Attack
5.2.2. De-Synchronization Attack
5.2.3. Replay Attack
5.2.4. Man-in-the-Middle Attack
5.2.5. Impersonation Attack
- SM impersonation attack. If adversary wants to impersonate the SM, he must forge the message to have the SP believe that the message is legal. However, must know secret parameters such as in order to produce the messages as legal. Due to the lack of knowledge of these parameters, the adversary cannot implement the SM impersonation attack.
- SP impersonation attack. If the adversary wants to impersonate SP, it needs to forge the message . The generation of the message requires SP’s long-term secret as auxiliary material which the adversary cannot learn. Therefore, the improved scheme can resist the impersonation attack.
5.2.6. Anonymity and Untraceability
5.2.7. Perfect Forward Secrecy
6. Performance Analysis
6.1. Security and Functionality Analysis
6.2. Computation Overhead Analysis
6.3. Communication Overhead Analysis
7. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Ehsani, M.; Gao, Y.; Longo, S.; Ebrahimi, K. Modern Electric, Hybrid Electric, and Fuel Cell Vehicles; CRC Press: Boca Raton, FL, USA, 2018. [Google Scholar]
- Rehmani, M.H.; Reisslein, M.; Rachedi, A.; Erol-Kantarci, M.; Radenkovic, M. Integrating renewable energy resources into the smart grid: Recent developments in information and communication technologies. IEEE Trans. Ind. Inform. 2018, 14, 2814–2825. [Google Scholar] [CrossRef]
- Hamedani, K.; Liu, L.; Atat, R.; Wu, J.; Yi, Y. Reservoir computing meets smart grids: Attack detection using delayed feedback networks. IEEE Trans. Ind. Inform. 2018, 14, 734–743. [Google Scholar] [CrossRef]
- Kumar, P.; Lin, Y.; Bai, G.; Paverd, A.; Dong, J.S.; Martin, A. Smart Grid Metering Networks: A Survey on Security, Privacy and Open Research Issues. IEEE Commun. Surv. Tutor. 2019, 21, 2886–2927. [Google Scholar] [CrossRef]
- NIST. Framework and Roadmap for Smart Grid Interoperability Standards, Release 4.0; Smart Grid Interoperability Panel (SGIP): Washington, DC, USA, 2021. [Google Scholar]
- Wu, J.; Guo, S.; Huang, H.; Liu, W.; Xiang, Y. Information and communications technologies for sustainable development goals: Stateof-the-art, needs and perspectives. IEEE Commun. Surv. Tutor. 2018, 20, 2389–2406. [Google Scholar] [CrossRef]
- McDaniel, P.; McLaughlin, S. Security and privacy challenges in the smart grid. IEEE Secur. Priv. 2009, 7, 75–77. [Google Scholar] [CrossRef]
- Yan, Y.; Qian, Y.; Sharif, H.; Tipper, D. A survey on smart grid communication infrastructures: Motivations, requirements and challenges. IEEE Commun. Surv. Tutor. 2013, 15, 5–20. [Google Scholar] [CrossRef]
- Analysis of the Cyber Attack on the Ukrainian Power Grid. Available online: https://africautc.org/wp-content/uploads/2018/05/E-ISAC_SANS_Ukraine_DUC_5.pdf (accessed on 12 April 2023).
- Wu, D.; Zhou, C. Fault-Tolerant and Scalable Key Management for Smart Grid. IEEE Trans. Smart Grid 2011, 2, 375–381. [Google Scholar] [CrossRef]
- Xia, J.; Wang, Y. Secure key distribution for the smart grid. IEEE Trans. Smart Grid 2012, 3, 1437–1443. [Google Scholar] [CrossRef]
- Park, J.H.; Kim, M.; Kwon, D. Security Weakness in the Smart Grid Key Distribution Scheme Proposed by Xia and Wang. IEEE Trans. Smart Grid 2013, 4, 1613–1614. [Google Scholar] [CrossRef]
- Wang, Y. Password protected smart card and memory stick authentication against off-line dictionary attacks. In Information Security and Privacy Research; Springer: Heidelberg, Germany, 2012; pp. 489–500. [Google Scholar]
- Tsai, J.-L.; Lo, N.-W. Secure anonymous key distribution scheme for smart grid. IEEE Trans. Smart Grid 2016, 7, 906–914. [Google Scholar] [CrossRef]
- Odelu, V.; Das, A.K.; Wazid, M.; Conti, M. Provably Secure Authenticated Key Agreement Scheme for Smart Grid. IEEE Trans. Smart Grid 2016, 9, 1900–1910. [Google Scholar] [CrossRef]
- Odelu, V.; Das, A.K.; Goswami, A. A secure biometrics-based multi-server authentication protocol using smart cards. IEEE Trans. Inf. Forensics Secur. 2015, 10, 1953–1966. [Google Scholar] [CrossRef]
- Canetti, R.; Krawczyk, H. Analysis of key-exchange protocols andtheir use for building secure channels. In Advances in Cryptology Eurocrypt 2001; Springer: Heidelberg, Germany, 2001; pp. 453–474. [Google Scholar]
- Nicanfar, H.; Jokar, P.; Beznosov, K.; Leung, V. Efficient authentication and key management mechanisms for smart grid communications. Syst. J. IEEE 2014, 8, 629–640. [Google Scholar] [CrossRef]
- Mohammadali, A.; Haghighi, M.S.; Tadayon, M.H.; Mohammadi-Nodooshan, A. A novel identity-based key establishment method for advanced metering infrastructure in smart grid. IEEE Trans. Smart Grid 2016, 9, 2834–2842. [Google Scholar] [CrossRef]
- Mahmood, K.; Chaudhry, S.A.; Naqvi, H.; Kumari, S.; Li, X.; Sangaiah, A.K. An elliptic curve cryptography based lightweight authentication scheme for smart grid communication. Future Gener. Comput. Syst. 2018, 81, 557–565. [Google Scholar] [CrossRef]
- Kumar, P.; Gurtov, A.; Sain, M.; Martin, A.; Ha, P. Lightweight authentication and key agreement for smart metering in smart energy networks. IEEE Trans. Smart Grid 2018, 10, 4349–4359. [Google Scholar] [CrossRef]
- Zhang, L.; Zhao, L.; Yin, S.; Chi, C.H.; Liu, R.; Zhang, Y. A lightweight authentication scheme with privacy protection for smart grid communications. Future Gener. Comput. Syst. 2019, 100, 770–778. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Babaghayou, M.; Yazici, M.A. Cyber security for fog-based smart grid SCADA systems: Solutions and challenges. J. Inf. Secur. Appl. 2020, 52, 102500. [Google Scholar] [CrossRef]
- Sadhukhan, D.; Ray, S.; Obaidat, M.S.; Dasgupta, M. A secure and privacy preserving lightweight authentication scheme for smart-grid communication using elliptic curve cryptography. J. Syst. Archit. 2021, 114, 101938. [Google Scholar] [CrossRef]
- Abbasinezhad-Mood, D.; Nikooghadam, M. An anonymous ECC-based self-certified key distribution scheme for the smart grid. IEEE Trans. Ind. Electron. 2018, 65, 7996–8004. [Google Scholar] [CrossRef]
- Khan, A.A.; Kumar, V.; Ahmad, M.; Rana, S.; Mishra, D. PALK: Password-based anonymous lightweight key agreement framework for smart grid. Int. J. Electr. Power Energy Syst. 2020, 121, 106121. [Google Scholar] [CrossRef]
- Taqi, S.A.M.; Jalili, S. LSPA-SGs: A lightweight and secure protocol for authentication and key agreement based Elliptic Curve Cryptography in smart grids. Energy Rep. 2022, 8, 153–164. [Google Scholar] [CrossRef]
- Deebak, B.D.; Memon, F.H.; Cheng, X.; Dev, K.; Hu, J.; Khowaja, S.A.; Qureshi, N.M.F.; Choi, K.H. Seamless privacy-preservation and authentication framework for IoT-enabled smart eHealth systems. Sustain. Cities Soc. 2022, 80, 103661. [Google Scholar] [CrossRef]
- Tanveer, M.; Ahmad, M.; Khalifa, H.S.; Alkhayyat, A.; Abd El-Latif, A.A. A new anonymous authentication framework for secure smart grids applications. J. Inf. Secur. Appl. 2022, 71, 103336. [Google Scholar] [CrossRef]
- Khan, A.A.; Kumar, V.; Ahmad, M. An elliptic curve cryptography based mutual authentication scheme for smart grid communications using biometric approach. J. King Saud Univ.-Comput. Inf. Sci. 2022, 3, 698–705. [Google Scholar] [CrossRef]
- Chaudhry, S.A.; Nebhan, J.; Yahya, K.; Al-Turjman, F. A privacy enhanced authentication scheme for securing smart grid infrastructure. IEEE Trans. Ind. Inform. 2021, 18, 5000–5006. [Google Scholar] [CrossRef]
- Chen, M.; Miao, Y.; Hao, Y.; Hwang, K. Narrow band internet of things. IEEE Access 2017, 5, 20557. [Google Scholar] [CrossRef]
- Chen, M.; Li, W.; Hao, Y.; Qian, Y.; Humar, I. Edge cognitive computing based smart healthcare system. Future Gener. Comput. Syst. 2018, 86, 403–411. [Google Scholar] [CrossRef]
- Wang, Y.; Chen, Q.; Hong, T.; Kang, C. Review of smart meter data analytics: Applications, methodologies, and challenges. IEEE Trans. Smart Grid 2018, 10, 3125–3148. [Google Scholar] [CrossRef]
- Su, W.; Eichi, H.; Zeng, W.; Chow, M.-Y. A survey on the electrification of transportation in a smart grid environment. IEEE Trans. Ind. Informat. 2012, 8, 1–10. [Google Scholar] [CrossRef]
- Fang, X.; Misra, S.; Xue, G.; Yang, D. Smart grid-The new and improved power grid: A survey. IEEE Commun. Surv. Tuts. 2012, 14, 944–980. [Google Scholar] [CrossRef]
- Boroyevich, D.; Cvetkovic, I.; Burgos, R.; Dong, D. Intergrid: A future electronic energy network? IEEE J. Emerg. Sel. Top. Power Electron. 2013, 1, 127–138. [Google Scholar] [CrossRef]
- Shoup, V. Sequences of Games: A Tool for Taming Complexity in Security Proofs. IACR Cryptology ePrint Archive. 2004. Available online: https://eprint.iacr.org/2004/332 (accessed on 12 April 2023).
- Abbasinezhad-Mood, D.; Nikooghadam, M.; Mazinani, S.M.; Babamohammadi, A.; Ostad-Sharif, A. More efficient key establishment protocol for smart grid communications: Design and experimental evaluation on ARM-based hardware. Ad Hoc Netw. 2019, 89, 119–131. [Google Scholar] [CrossRef]


| Scheme | Limitations | Primitive Used | Year |
|---|---|---|---|
| [19] | Cannot resist replay attack, SK compromised attack, SM impersonation attack, and MINM attacks, cannot ensure anonymity, does not consider internal attackers | ECC, XOR, and Hash | 2018 |
| [20] | Cannot ensure the anonymity of SM, does not consider internal attackers | ECC, XOR, and Hash | 2018 |
| [21] | Cannot ensure the anonymity of SM, does not consider internal attackers | ECC, XOR, and Hash | 2018 |
| [22] | Cannot resist insider attacks, impersonation attack, SK compromise attack, loss the anonymity of SM | AES, XOR, and Hash | 2019 |
| [27] | Does not consider internal attackers | ECC, XOR, and Hash | 2022 |
| our scheme | Can resist known attacks, considers internal attackers | AES, XOR, and Hash |
| Symbols and Notations | Description |
|---|---|
| the ith smart meter and ’s identity | |
| the jth service provider and ’s identity | |
| K | service providers’ master secret key |
| a temporary key between and | |
| concatenating operation | |
| ⊕ | exclusive OR |
| a one-way hash function | |
| Symmetric encryption using key K | |
| Symmetric decryption using key K | |
| High entropy random numbers | |
| ’s unique identification stored in the table |
| F1 | F2 | F3 | F4 | F5 | F6 | R1 | R2 | R3 | R4 | R5 | R6 | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| [19] | YES | YES | YES | NO | NO | YES | YES | YES | YES | / | / | YES |
| [20] | YES | YES | YES | NO | NO | YES | YES | YES | YES | / | YES | YES |
| [21] | YES | YES | YES | YES | / | YES | YES | YES | NO | / | / | YES |
| [22] | YES | YES | YES | NO | YES | YES | YES | YES | YES | YES | NO | YES |
| [27] | YES | YES | YES | YES | YES | YES | YES | YES | YES | NO | YES | YES |
| our scheme | YES | YES | YES | YES | YES | YES | YES | YES | YES | YES | YES | YES |
| [19] | [20] | [21] | [22] | [27] | Our Scheme | |
|---|---|---|---|---|---|---|
| 3+ 2 = | 3 + 2 = | 3 + 2 + + + | 7 + 1 = | 4 + + + 3 | 7 + 1 = | |
| 4.4589 ms | 4.4589 ms | = 4.4773 ms | 0.0207 ms | = 6.7796 ms | 0.0207 ms | |
| 4 + 3 = | 2 + 3 + | 4 + 3 + + + | 9 + 2 + | 3 + + + 3 | 9 + 2 + | |
| 6.6872 ms | = 6.7114 ms | 2 = 6.7056 ms | = 0.0345 ms | = 6.7772 ms | = 0.0345 ms | |
| 11.1461 ms | 11.1703 ms | 11.1829 ms | 0.0552 ms | 13.5568 ms | 0.0552 ms |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Chen, C.; Guo, H.; Wu, Y.; Shen, B.; Ding, M.; Liu, J. A Lightweight Authentication and Key Agreement Protocol for IoT-Enabled Smart Grid System. Sensors 2023, 23, 3991. https://doi.org/10.3390/s23083991
Chen C, Guo H, Wu Y, Shen B, Ding M, Liu J. A Lightweight Authentication and Key Agreement Protocol for IoT-Enabled Smart Grid System. Sensors. 2023; 23(8):3991. https://doi.org/10.3390/s23083991
Chicago/Turabian StyleChen, Chen, Hua Guo, Yapeng Wu, Bowen Shen, Mingyang Ding, and Jianwei Liu. 2023. "A Lightweight Authentication and Key Agreement Protocol for IoT-Enabled Smart Grid System" Sensors 23, no. 8: 3991. https://doi.org/10.3390/s23083991
APA StyleChen, C., Guo, H., Wu, Y., Shen, B., Ding, M., & Liu, J. (2023). A Lightweight Authentication and Key Agreement Protocol for IoT-Enabled Smart Grid System. Sensors, 23(8), 3991. https://doi.org/10.3390/s23083991






