SAMGRID: Security Authorization and Monitoring Module Based on SealedGRID Platform †
Abstract
:1. Introduction
- providing security and privacy requirements for a module dedicated to delivering security authorization and monitoring the security status of the participating nodes;
- proposing SAMGRID, a novel authorization and security monitoring module tailored to SG needs based on well-established security technologies;
- assessing SAMGRID’s performance: implementation and evaluation were performed in a simulation environment.
2. Authorization in SG
2.1. Definition and Participants
2.2. Motivating Examples
2.3. Security and Functional Requirements
2.3.1. Security Requirements
- S1.
- Data confidentiality: Data exchanged within a SG ecosystem should be available only to SG components with the respective privilege.
- S2.
- Data integrity and authenticity: Data exchanged among the participating SG components should be safeguarded against alteration and replication; thus, these should be capable of verifying the origin of the acquired data.
- S3.
- Accountability: Devices, handlers/employees and end-users should be accountable for their actions.
- S4.
- Non-repudiation: Devices, handlers and end-users should not be able to deny their actions.
- S5.
- Physical protection: All electronic devices that participate in a SG ecosystem should contain protection mechanisms to prevent being tampered by adversaries with physical access.
2.3.2. Functional Requirements
- F1.
- Time consuming: As it is well known, the SG concept aims to support real-time services to its end-user. Thus, the implemented application for authentication, authorization, policy updating should not consume much time and deplete the available sources.
- F2.
- Scalability: A SG ecosystem should consist of applications that are capable of handling the numerous fluctuations of grid’s size (e.g., nodes can join and leave a grid) without negatively affecting their performance.
- F3.
- Delegated access control: Any application access must be authenticated and authorized by a security policy, and the granting decisions must be made relying on a trusted party.
- F4.
- Authorization: Any access to applications must be authorized according to a security policy.
- F5.
- Authentication: Requesters should be authenticated before accessing any application.
3. Related Work
3.1. Security Authorization Approaches
3.2. Opinion Dynamics Approaches
4. SAMGRID Concept
4.1. SAMGRID
4.2. SAMGRID Authorization
4.3. SAMGRID Opinion Dynamics (ODyn)
5. Performance Evaluation
5.1. Authorization
5.2. ODyn
6. Security Analysis
7. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Khan, M.W.; Wang, J.; Ma, M.; Xiong, L.; Li, P.; Wu, F. Optimal energy management and control aspects of distributed microgrid using multi-agent systems. Sustain. Cities Soc. 2019, 44, 855–870. [Google Scholar] [CrossRef]
- Ghosal, A.; Conti, M. Key management systems for smart grid advanced metering infrastructure: A survey. IEEE Commun. Surv. Tutor. 2019, 21, 2831–2848. [Google Scholar] [CrossRef]
- Rendroyoko, I.; Setiawan, A.D. Development of Meter Data Management System Based-on Event-Driven Streaming Architecture for IoT-based AMI Implementation. In Proceedings of the 2021 3rd International Conference on High Voltage Engineering and Power Systems (ICHVEPS), Bandung, Indonesia, 5 October 2021; IEEE: Piscataway, NJ, USA, 2021; pp. 403–407. [Google Scholar] [CrossRef]
- Gopstein, A.; Nguyen, C.; O’Fallon, C.; Hastings, N.; Wollman, D. NIST Framework and Roadmap for Smart Grid Interoperability Standards, Release 4.0; NIST Special Publication; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2021. [CrossRef]
- Alcaraz, C.; Lopez, J. Secure interoperability in cyber-physical systems. In Cyber Warfare and Terrorism: Concepts, Methodologies, Tools, and Applications; IGI Global: Hershey, PA, USA, 2020; pp. 521–542. [Google Scholar] [CrossRef]
- Hasankhani, A.; Hakimi, S.M.; Bisheh-Niasar, M.; Shafie-khah, M.; Asadolahi, H. Blockchain technology in the future smart grids: A comprehensive review and frameworks. Int. J. Electr. Power Energy Syst. 2021, 129, 106811. [Google Scholar] [CrossRef]
- Javaid, N.; Gul, H.; Baig, S.; Shehzad, F.; Xia, C.; Guan, L.; Sultana, T. Using GANCNN and ERNET for Detection of Non-Technical Losses to Secure Smart Grids. IEEE Access 2021, 9, 98679–98700. [Google Scholar] [CrossRef]
- Yang, H.; Liu, S.; Fang, C. Model-based secure load frequency control of smart grids against data integrity attack. IEEE Access 2020, 8, 159672–159682. [Google Scholar] [CrossRef]
- Boudko, S.; Aursand, P.; Abie, H. Evolutionary Game for Confidentiality in IoT-enabled Smart Grids. Information 2020, 11, 582. [Google Scholar] [CrossRef]
- Veichtlbauer, A.; Engel, D.; Knirsch, F.; Langthaler, O.; Moser, F. Advanced metering and data access infrastructures in smart grid environments. In Proceedings of the Seventh International Conference on Sensor Technologies and Applications (SENSORCOMM) 2013, Barcelona, Spain, 25–31 August 2013; pp. 63–68, ISBN 978-1-61208-296-7. [Google Scholar]
- Alcaraz, C.; Lopez, J.; Wolthusen, S. Policy enforcement system for secure interoperable control in distributed smart grid systems. J. Netw. Comput. Appl. 2016, 59, 301–314. [Google Scholar] [CrossRef]
- Duan, L.; Liu, D.; Zhang, Y.; Chen, S.; Liu, R.P.; Cheng, B.; Chen, J. Secure data-centric access control for smart grid services based on publish/subscribe systems. ACM Trans. Internet Technol. (TOIT) 2016, 16, 1–7. [Google Scholar] [CrossRef]
- Alcarria, R.; Bordel, B.; Robles, T.; Martín, D.; Manso-Callejo, M.Á. A blockchain-based authorization system for trustworthy resource monitoring and trading in smart communities. Sensors 2018, 18, 3561. [Google Scholar] [CrossRef]
- Bolgouras, V.; Ntantogian, C.; Panaousis, E.; Xenakis, C. Distributed key management in microgrids. IEEE Trans. Ind. Inform. 2019, 16, 2125–2133. [Google Scholar] [CrossRef]
- Karopoulos, G.; Ntantogian, C.; Xenakis, C. MASKER: Masking for privacy-preserving aggregation in the smart grid ecosystem. Comput. Secur. 2018, 73, 307–325. [Google Scholar] [CrossRef]
- Farao, A.; Veroni, E.; Ntantogian, C.; Xenakis, C. P4G2Go: A Privacy-Preserving Scheme for Roaming Energy Consumers of the Smart Grid-to-Go. Sensors 2021, 21, 2686. [Google Scholar] [CrossRef] [PubMed]
- Suciu, G.; Istrate, C.I.; Vulpe, A.; Sachian, M.A.; Vochin, M.; Farao, A.; Xenakis, C. Attribute-based access control for secure and resilient smart grids. In Proceedings of the 6th International Symposium for ICS & SCADA Cyber Security Research 2019, Athens, Greece, 10–12 September 2019; pp. 67–73. [Google Scholar] [CrossRef]
- Suciu, G.; Istrate, C.; Sachian, M.A.; Vulpe, A.; Vochin, M.; Farao, A.; Xenakis, C. FI-WARE authorization in a Smart Grid scenario. In Proceedings of the 2020 Global Internet of Things Summit (GIoTS), Dublin, Ireland, 3 June 2020; IEEE: Piscataway, NJ, USA; pp. 1–5. [Google Scholar] [CrossRef]
- Langner, R. Stuxnet: Dissecting a cyberwarfare weapon. IEEE Secur. Priv. 2011, 9, 49–51. [Google Scholar] [CrossRef]
- FireEye. Cyber Attacks on the Ukrainian Grid: What You Should Know. 2015. Available online: https://www.fireeye.com/content/dam/fireeye-www/global/en/solutions/pdfs/fe-cyber-attacks-ukrainian-grid.pdf (accessed on 17 May 2022).
- Kaspersky. BlackEnergy APT Attack in Ukraine. Available online: https://www.kaspersky.com/resource-center/threats/blackenergy (accessed on 17 March 2022).
- Wired. The Untold Story of a Cyberattack, a Hospital and a Dying Woman. Available online: https://www.wired.co.uk/article/ransomware-hospital-death-germany (accessed on 17 March 2022).
- Nbc News. Colonial Announces Pipeline Restart, Says Normal Service Will Take ‘Several Days’. Available online: https://www.nbcnews.com/tech/security/colonial-announces-pipeline-restart-says-normal-service-will-take-seve-rcna917 (accessed on 17 March 2022).
- Hackers Breached Colonial Pipeline Using Compromised Password. Available online: https://www.bloomberg.com/news/articles/2021-06-04/hackers-breached-colonial-pipeline-using-compromised-password (accessed on 17 March 2022).
- Farao, A.; Panda, S.; Menesidou, S.A.; Veliou, E.; Episkopos, N.; Kalatzantonakis, G.; Mohammadi, F.; Georgopoulos, N.; Sirivianos, M.; Salamanos, N.; et al. SECONDO: A platform for cybersecurity investments and cyber insurance decisions. In Proceedings of the International Conference on Trust and Privacy in Digital Business, Bratislava, Slovakia, 14–17 September 2020; Springer: Cham, Switzerland, 2020; pp. 65–74. [Google Scholar] [CrossRef]
- The Cyber Kill Chain. Available online: https://www.lockheedmartin.com/en-us/capabilities/cyber/cyber-kill-chain.html (accessed on 17 March 2022).
- Yadav, T.; Rao, A.M. Technical aspects of cyber kill chain. In Proceedings of the International Symposium on Security in Computing and Communication, Kochi, India, 10 August 2015; Springer: Cham, Switzerland, 2015; pp. 438–452. [Google Scholar] [CrossRef] [Green Version]
- Rubio, J.E.; Alcaraz, C.; Lopez, J. Preventing advanced persistent threats in complex control networks. In Proceedings of the European Symposium on Research in Computer Security, Oslo, Norway, 11–15 September 2017; Volume 10493, pp. 402–418. [Google Scholar] [CrossRef]
- Mitre Att&Ck. Available online: https://attack.mitre.org/ (accessed on 17 March 2022).
- Nisioti, A.; Loukas, G.; Laszka, A.; Panaousis, E. Data-driven decision support for optimizing cyber forensic investigations. IEEE Trans. Inf. Forensics Secur. 2021, 16, 2397–2412. [Google Scholar] [CrossRef]
- Rubio, J.E.; Roman, R.; Alcaraz, C.; Zhang, Y. Tracking apts in industrial ecosystems: A proof of concept. J. Comput. Secur. 2019, 27, 521–546. [Google Scholar] [CrossRef]
- Rubio, J.E.; Roman, R.; Lopez, J. Integration of a threat traceability solution in the industrial internet of things. IEEE Trans. Ind. Inform. 2020, 16, 6575–6583. [Google Scholar] [CrossRef]
- “OpenWay Riva”, Itron. Available online: https://blogs.itron.com/tag/openway-riva/ (accessed on 17 March 2022).
- French, J.R., Jr. A formal theory of social power. Psychol. Rev. 1956, 63, 181. [Google Scholar] [CrossRef]
- DeGroot, M.H. Reaching a consensus. J. Am. Stat. Assoc. 1974, 69, 118–121. [Google Scholar] [CrossRef]
- Dong, Y.; Zhan, M.; Kou, G.; Ding, Z.; Liang, H. A survey on the fusion process in opinion dynamics. Inf. Fusion 2018, 43, 57–65. [Google Scholar] [CrossRef]
- Noorazar, H. Recent advances in opinion propagation dynamics: A 2020 survey. Eur. Phys. J. Plus 2020, 135, 1–20. [Google Scholar] [CrossRef]
- Grabisch, M.; Rusinowska, A. A Survey on Nonstrategic Models of Opinion Dynamics. Games 2020, 11, 65. [Google Scholar] [CrossRef]
- Lopez, J.; Rubio, J.E.; Alcaraz, C. A resilient architecture for the smart grid. IEEE Trans. Ind. Inform. 2018, 14, 3745–3753. [Google Scholar] [CrossRef]
- Gunduz, M.Z.; Das, R. Cyber-security on smart grid: Threats and potential solutions. Comput. Netw. 2020, 169, 107094. [Google Scholar] [CrossRef]
- Suciu, G.; Sachian, M.-A.; Vulpe, A.; Vochin, M.; Farao, A.; Koutroumpouchos, N.; Xenakis, C. SealedGRID: Secure and Interoperable Platform for Smart GRID Applications. Sensors 2021, 21, 5448. [Google Scholar] [CrossRef]
- Muñoz, A.; Farao, A.; Correia, J.R.C.; Xenakis, C. P2ISE: Preserving Project Integrity in CI/CD Based on Secure Elements. Information 2021, 12, 357. [Google Scholar] [CrossRef]


| Related Work/Features | Blockchain | Access Control | Opinion Dynamics | Machine Learning | Data Integrity | Interoperability |
|---|---|---|---|---|---|---|
| Smart Grid Interoperability Standards [4] | ✓ | |||||
| Interconnection between heterogeneous cyber-physical systems [5] | ✓ | |||||
| Blockchain technology for smart grids [6] | ✓ | ✓ | ||||
| ML models for Electricity Theft Detection [7] | ✓ | ✓ | ||||
| Load frequency control of smart grids [8] | ||||||
| Confidentiality in Smart Grids [9] | ✓ | ✓ | ||||
| Metering and data access infrastructures in smart grid [10] | ✓ | ✓ | ||||
| Policy enforcement in smart grid [11] | ✓ | |||||
| Access control for smart grid services based on publish/subscribe [12] | ✓ | ✓ | ||||
| Blockchain-based authorization system [13] | ✓ | ✓ | ||||
| Proposed work | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| Entity | Description |
|---|---|
| Smart Meter (SM) | Collect the readings of the electricity consumption. |
| Aggregator | Sum all the SMs’ readings and transmit the result to the Utility. |
| Utility | Compute the total consumption of a customer. |
| Role | Description |
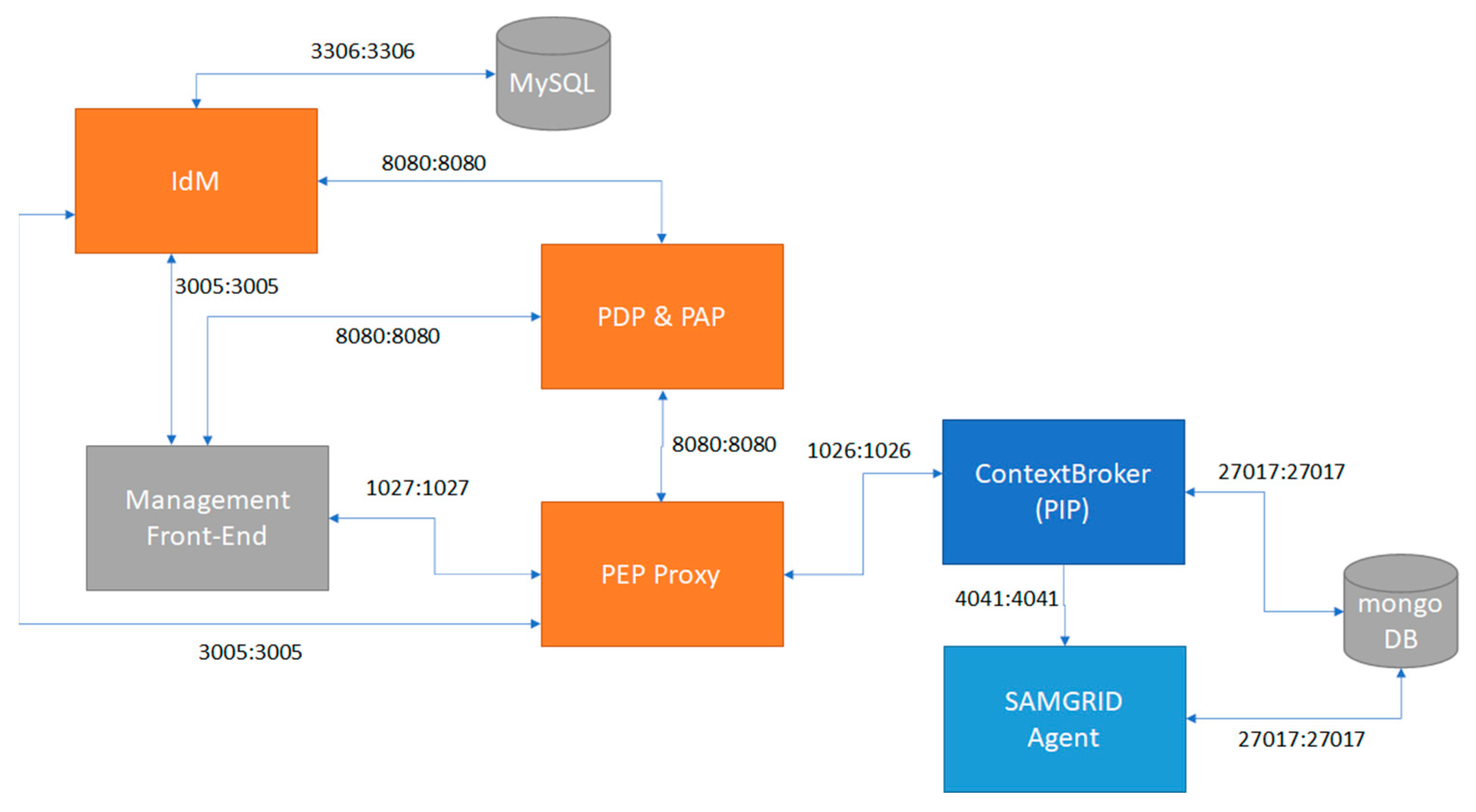
| PAP | Authors and maintains a set of policies. |
| PDP | Assesses a policy against other relevant policies and attributes. |
| PIP | Is a source of attribute values. |
| PEP | Performs decision requests, receives policy updates and accordingly translates them, and enforces policies’ decisions. |
| Entity | Setup |
|---|---|
| Smart Meter |
|
| Aggregator |
|
| Utility |
|
| # of Nodes | Average CPU Utilization (Percentage) | Average Memory Consumption (MB) | API Response Time (ms) | ||||||
|---|---|---|---|---|---|---|---|---|---|
| Smart Meter | Aggregator | Utility | Smart Meter | Aggregator | Utility | Smart Meter | Aggregator | Utility | |
| 10 | 6.86 | 1.39 | 0.8 | 154.57 | 315.69 | 1455.42 | 162.85 | 71 | 38.62 |
| 50 | 6.68 | 6.87 | 3.43 | 154.71 | 327.29 | 1464.28 | 868.83 | 357.41 | 137.96 |
| 100 | 6.58 | 12.82 | 6.59 | 132.28 | 261.78 | 1481.81 | 4041.98 | 460.3 | 189.1 |
| 500 | 7.86 | 19.3 | 34.3 | 137.40 | 304.12 | 2033.95 | 6670.35 | 2529 | 1545.4 |
| Entity | Setup |
|---|---|
| Smart Meter, Aggregator | -ARM Device single-core CPU at 700 MHz, 512 MB RAM (Download: 9.6 Mbps; Upload: 9 Mbps) |
| Utility | -Intel Core i5-6500 CPU at 3.2 GHz 4 cores, 8 GB RAM (Download: 98 Mbps; Upload: 92 Mbps) |
| # of Nodes | CPU Utilization (Percentage) | Memory Consumption (Percentage) | Network Usage | |||
|---|---|---|---|---|---|---|
| Smart Meter, Aggregator | Utility | Smart Meter, Aggregator | Utility | Smart Meter, Aggregator | Utility | |
| 100 | 1.47 | 0.26 | 51 MB | |||
| 500 | 18.07 | 0.9 | 255 MB | |||
| 1000 | 1.44 | 25 | 0.1 | 1.1 | 514 Kb | 500 MB |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Suciu, G.; Farao, A.; Bernardinetti, G.; Palamà, I.; Sachian, M.-A.; Vulpe, A.; Vochin, M.-C.; Muresan, P.; Bampatsikos, M.; Muñoz, A.; et al. SAMGRID: Security Authorization and Monitoring Module Based on SealedGRID Platform. Sensors 2022, 22, 6527. https://doi.org/10.3390/s22176527
Suciu G, Farao A, Bernardinetti G, Palamà I, Sachian M-A, Vulpe A, Vochin M-C, Muresan P, Bampatsikos M, Muñoz A, et al. SAMGRID: Security Authorization and Monitoring Module Based on SealedGRID Platform. Sensors. 2022; 22(17):6527. https://doi.org/10.3390/s22176527
Chicago/Turabian StyleSuciu, George, Aristeidis Farao, Giorgio Bernardinetti, Ivan Palamà, Mari-Anais Sachian, Alexandru Vulpe, Marius-Constantin Vochin, Pavel Muresan, Michail Bampatsikos, Antonio Muñoz, and et al. 2022. "SAMGRID: Security Authorization and Monitoring Module Based on SealedGRID Platform" Sensors 22, no. 17: 6527. https://doi.org/10.3390/s22176527
APA StyleSuciu, G., Farao, A., Bernardinetti, G., Palamà, I., Sachian, M.-A., Vulpe, A., Vochin, M.-C., Muresan, P., Bampatsikos, M., Muñoz, A., & Xenakis, C. (2022). SAMGRID: Security Authorization and Monitoring Module Based on SealedGRID Platform. Sensors, 22(17), 6527. https://doi.org/10.3390/s22176527









