Abstract
Cooperative spectrum sensing (CSS) has been verified as an effective approach to improve the sensing performances of cognitive radio networks (CRNs). Compared with existing works that commonly consider fusion with fixed inputs and neglect the duration of the reporting period in the design, we novelly investigate a fundamental trade-off among three periods of CSS: sensing, reporting, and transmission periods, and evaluate the impact of the fusion rule with a varying number of local sensing results. To be specific, the sensing time could be traded for additional mini-slots to report more local sensing results for fusion, or it could be traded for longer transmission time. In the CRNs with a given durations of sensing/reporting/transmission periods, we, respectively, formulate the throughput and collision probability and optimize the throughput under the collision constraint. The theoretical results show that, in the specific value intervals of the sensing parameters, the collision constraint provides an upper bound of the number of mini-slots in the reporting period or a lower bound of the sensing duration. We provide the approach to the maximum throughput in some cases.Finally, numerical results are presented to validate theoretical results.
1. Introduction
The fast development of wireless communication technologies and the growing number of high-speed wireless devices are expected to create an increasing demand for spectrum resources [1]. This motivates the advent of cognitive radio to tackle the spectrum scarcity problem by allowing opportunistic spectrum access. In cognitive radio networks (CRNs), secondary users (SUs) are allowed to dynamically access the licensed spectrum allocated to primary users (PUs) when the licensed spectrum is temporally available.
To explore the underutilized spectrum resources, SUs need to adopt fast and effective spectrum-sensing techniques to determine spectrum states. Based on the classification of spectrum-sensing approaches in [2], there are a number of works that focused on spectrum-sensing algorithms [3,4,5,6,7]. Liang et al. [3] designed an energy detection sensing scheme to tackle the sensing–the throughput trade-off of the secondary network. In wideband scenarios under noise uncertainty, Dikmese et al. [4] proposed a cyclic prefix auto-correlation-based spectrum sensing system. By exploiting the signal sparsity, El-Alfi et al. [5] proposed a sub-Nyquist cyclo-stationary detection of GFDM. Sedighi et al. [6] studied constant false-alarm-rate eigenvalue-based detectors for multi-antenna spectrum sensing. Tavana et al. [7] considered the energy and correlation of received signals to suppress error detection. Among these spectrum-sensing techniques, energy detection is the most popular spectrum-sensing technique due to its adequate performance, simple practical realization, and low computational complexity.
Based on the energy-detection technique, many efforts have been geared mainly towards non-cooperative spectrum sensing and cooperative spectrum sensing (CSS). Compared with non-cooperative users, cooperation among users has potential benefits for key performances of CRNs, such as the throughput [8,9], connectivity [10], energy efficiency [11], delay [12], and security [13,14]. Since the unreliability in a single SU’s sensing result reduces the accuracy to a certain extent, CSS has been incorporated to overcome the hidden terminal problem and improve the sensing performance, especially in shadowing/multi-path fading environments [15,16]. In CSS, each user first senses the PU independently and then sends its local sensing result to a fusion center (FC). Then, the FC makes a final decision on the spectrum state by combining all the receiving local sensing results [17,18]. The probability of a false alarm and the probability of detection are two important indicators of spectrum-sensing accuracy. The low probability of a false alarm improves the spectrum-access efficiency, while the high probability of detection reduces the interference with the PU [19]. By exploiting the spatial diversity, cooperative SUs obtain better sensing accuracy by CSS than a single SU.
Incorporating various techniques, such as sensing algorithms [3,4,5,6,7], access strategies, fusion rules, and user cooperation, a number of works [16,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34] have focused on the performance improvements of CRNs with CSS. From the perspective of access strategy, Lee et al. [20] proposed an adaptive CSS scheme using random access. Wang et al. [21,22] proposed a principal–agent-based joint spectrum-sensing and -access framework to thwart the malicious behaviors. Alhamad et al. [16] designed a reporting channel scheme based on random access protocols, and Gharib et al. [23,24] proposed multi-band multi-user CSS schemes for opportunistic spectrum access. From the perspective of fusion rule, Liu et al. [25] maximized the spectral efficiency based on the logical OR rule. Yin et al. [26] maximized the secondary the throughput by the optimization of the fusion rule. Ejaz et al. [27] presented a comparison of hard and soft, combining CSS schemes in heterogeneous CRNs. Golvaei et al. [28] proposed a soft decision algorithm to improve CSS performance for hidden PUs in fading and shadowing environments, which showed better performance than the hard decision algorithm. Yuan et al. [29] and Zhang et al. [30], respectively, proposed a secure fusion strategy to defend against malicious users for CSS. Taking the location impact of different SUs into account, Liu et al. [31] proposed a probability-based fusion rule. Based on the soft rule, Perez et al. [32] presented a new algorithm that jointly estimates the instantaneous SNRs and detects the presence of primary signals. From the perspective of coalition formation, Wang et al. [33] considered overlapping coalition formations for distributed cooperative sensing, where SUs form overlapping coalitions to improve sensing accuracy. Then Jiang et al. [34] formulated a classical coalition formation game model for the throughput maximization and cooperation in spectrum sensing.
Among the aforementioned works, [3,26,34,35] study the throughput maximization of SUs with respect to the fusion rule or sensing parameters such as the detection threshold. However, all four works neglect the duration of the reporting period in the slot structure, and [26,35] do not consider the sensing cooperation among SUs. Moreover, we notice that the duration of the reporting period has been analyzed in terms of sensing performance [16,36], energy consumption [36], and channel utilization [37], respectively. In this regard, the duration of the reporting period has a vital impact on the performances of CRNs, while the throughput and sensing performances of the cooperative CRNs with the design of the reporting period have seldom been studied.
Our work differs from previous works from two perspectives. First, from the perspective of a time trade-off, the duration of the sensing period, the duration of the transmission period, and the number of mini-slots in the reporting period, are, respectively, considered as variables in the formulation and optimization of the secondary the throughput. Second, from the perspective of fusion, our work studies the impact of the fusion rule on the throughput and sensing performances of the cooperative CRNs with a varying number of local sensing results for fusion, which has seldom been studied.
To explore the crucial impact of the reporting period on the throughput and sensing performances, this paper studies the throughput maximization of SUs under the collision constraint in cooperative CRNs, where the CSS process consists of three periods: sensing, reporting, and transmission. Autonomous SUs perform spectrum sensing during the sensing period and then send local sensing results to the FC by a reporting channel. The FC makes a final decision about the licensed spectrum using the “k-out-of-n” fusion rule during the reporting period. Obviously, there exists a fundamental time trade-off among the sensing period, reporting period, and transmission period, which results in the sensing–the throughput trade-off in the cooperative CRNs. By tackling the time trade-off, the secondary the throughput is formulated and optimized under the collision constraint, which reflects the accuracy of spectrum sensing. By tackling the sensing–the throughput trade-off, we evaluate the impact of the fusion rule with a varying number of local sensing results on the throughput maximization. Then, we summarize the main contributions as follows.
- We formulate the secondary the throughput and collision probability in three cases of the cooperative CRNs, where each time slot in the CSS process consists of the sensing period, reporting period, and transmission period. In the time trade-off, the sensing time could be traded for additional mini-slots to obtain more local sensing results, and it could also be traded for longer transmission times. The impact of the fusion rule with a varying number of local sensing results is studied in the throughput and collision analysis.
- In three cases of the cooperative CRNs, according to the mathematical relationship between k and n, we, respectively, present a monotonicity analysis of the throughput and collision probability and provide an approach to the maximum the throughput in some cases of the sensing and fusion parameters under the collision constraint.
- The numerical results show that the throughput and the collision probability possess the monotonic property in some value intervals of the sensing and fusion parameters, which is of prime significance for the design of three periods in the slot structure of the CSS process. Moreover, the numerical results demonstrate that, with a given sensing period, the maximal throughput is achieved when the trade-off between the cooperative sensing accuracy, which results from the number of SUs participating in CSS, and transmission time is optimal. With a given reporting period, the maximal throughput is achieved when the trade-off between the local sensing accuracy and transmission time is optimal. With a given transmission period, the maximal throughput is achieved when the cooperative sensing accuracy, which is jointly determined by the local sensing accuracy and the number of SUs participating in CSS, is optimal.
The remainder of this paper is organized as follows. The network model is introduced in Section 2. The the throughput and collision performances of the cooperative CRNs with a given sensing period, reporting period, and transmission period are, respectively, investigated in Section 3, Section 4 and Section 5. The numerical results are given in Section 6, and, finally, this paper is concluded in Section 7.
2. Network Model and Notations
In this section, we introduce the cooperative CRNs from three aspects: the network model, the spectrum-sensing model, and the reporting model. We first specify the network topology and slot structure. Then, we specify how SUs cooperatively and opportunistically access the licensed spectrum.
2.1. Network Model
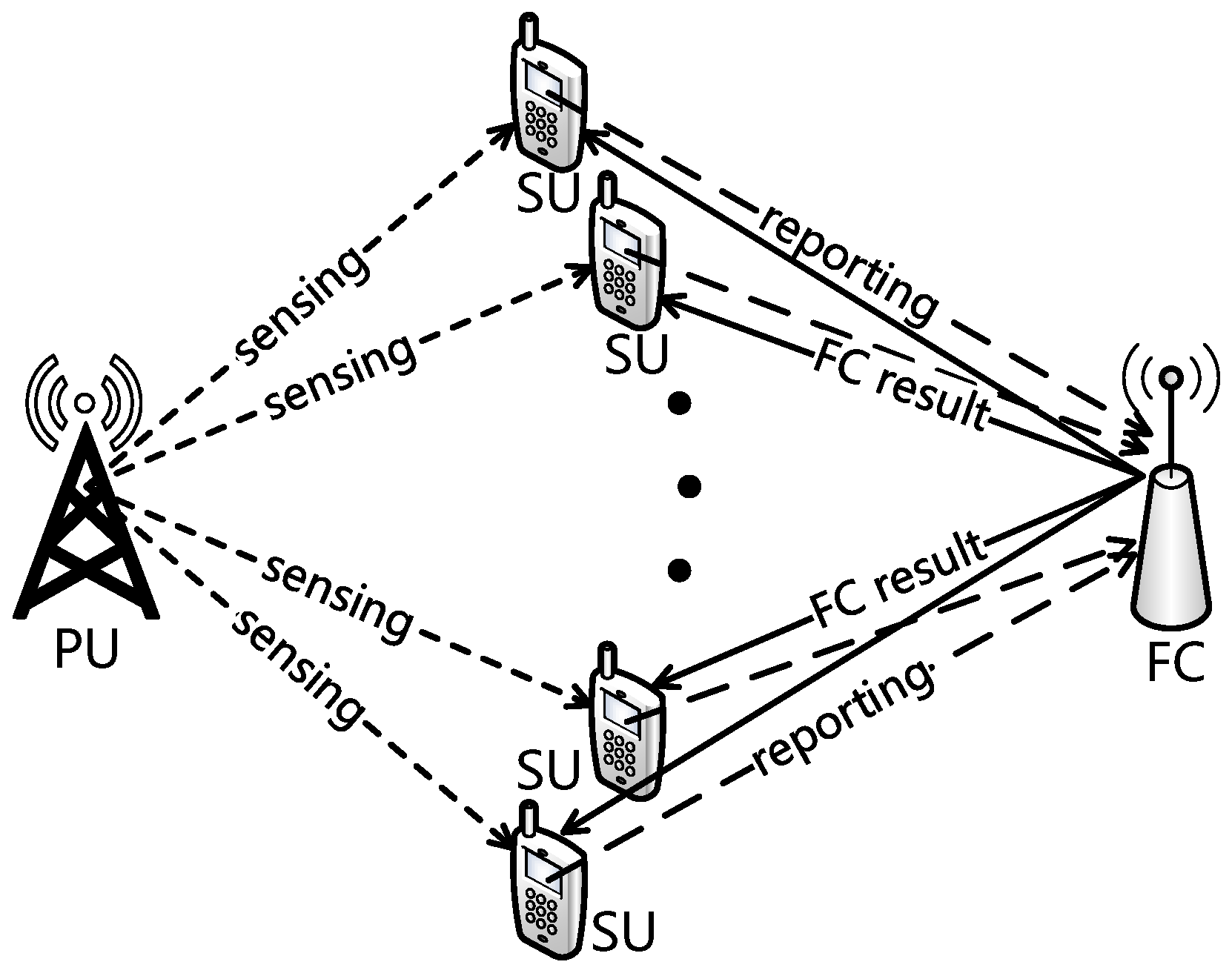
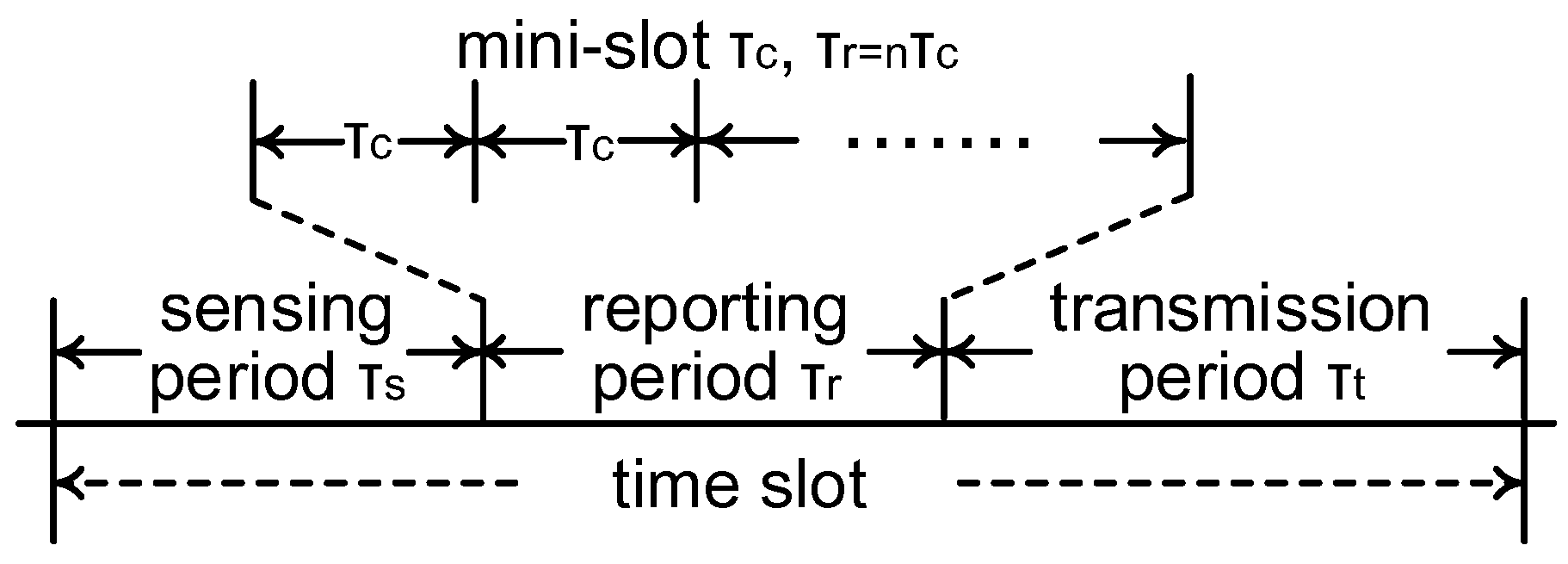
We consider the CRN scenario where one pair of PUs, one FC, and N pairs of SUs coexist. PUs have priorities over SUs to access the licensed spectrum and perform primary packet transmission (the primary receiver is neglected in Figure 1). Spectrum sensing by SUs is essential to avoid excessive interference from SUs to PUs, and the collision probability, which will be defined in the next section, reflects the accuracy of spectrum sensing to a certain extent. When the licensed spectrum is determined is free by the FC, one of the SUs exploits the spectrum and transmits secondary packets to the corresponding secondary receiver (neglected in Figure 1). As shown in Figure 1 and Figure 2, we consider three periods in the slot structure of the cooperative CRNs: a sensing period with duration , a reporting period with duration , and a transmission period with duration . As pointed out by [38], if the SUs have the perfect knowledge of the PU’s communication mechanism, the SUs can be synchronous with the PU’s time slots. Here, we consider that all the SUs and PUs adopt a synchronous slotted protocol with normalized length, where holds for each time slot by normalization.
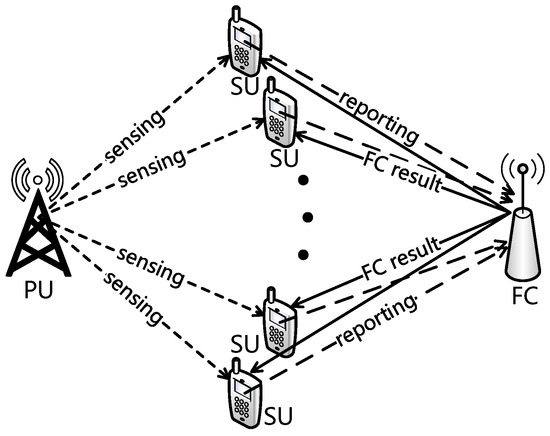
Figure 1.
Network model.
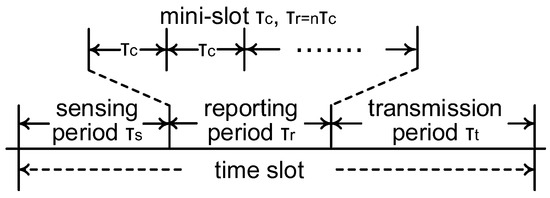
Figure 2.
Slot structure.
During the sensing period, N pairs of SUs independently perform spectrum sensing to detect the primary signal in the licensed spectrum by energy detection, which has relatively low computational and implementation complexities [39]. The details of spectrum sensing will be introduced in Section 2.2. Due to the arrival of primary packets following a time-homogeneous random process, the licensed spectrum randomly switches between the free state and the occupied state at each time slot. We let denote the probability that the licensed spectrum is occupied, and denote the probability that the licensed spectrum is free, where .
During the reporting period, the SUs send local sensing results to the FC; the details of the reporting model will be introduced in Section 2.3. By applying a specific fusion rule, the FC makes a final decision about the spectrum state based on the received local sensing results. Then, the FC broadcasts a message containing the final decision about the spectrum state and the identification of a specified SU to SUs [16]. When the FC determines the licensed spectrum to be occupied, the specified SU for the transmission does not exist and would not be contained in the broadcast message. Due to the limited number of bits in the broadcast message, the time duration of the broadcasting period is neglected in the time slot structure.
During the transmission period, if the received broadcast message indicates that the licensed spectrum is decided is free, the randomly specified SU transmits packets to the corresponding secondary receiver (neglected in Figure 1). Otherwise, the secondary transmission does not occur during the transmission period. To evaluate the secondary the throughput of the CRNs from the perspective of the actual transmission time, we define the throughput as the average time duration of the secondary transmission that does not collide with the primary transmission in the normalized time slot, and this definition is similar to that of the average normalized the throughput in [25].
where denotes the duration of the secondary packet transmission that does not collide with the primary packet transmission at slot i, T represents the observed number of time slots, and holds. If the FC correctly determines the licensed spectrum is free at slot i, the secondary packet transmission occurs during the transmission period, and holds. Otherwise, holds at slot i. Therefore, the average normalized the throughput in (1) represents the ratio of the secondary packet transmission duration without colliding with the primary packet transmission to one time slot from a long-term perspective. According to the slot structure in Figure 2, the sensing period and the number of mini-slots in the reporting period have great impacts on the throughput.
2.2. Spectrum-Sensing Model
Various spectrum-sensing techniques have been proposed to determine the spectrum state, including energy detection [40], matched-filter detection [41], eigenvalue-based detection [42], and cyclostationarity-based detection [43]. Among these four techniques, we employ energy detection to detect the spectrum in the sensing period due to its adequate performance, simple practical realization, and low computational complexity [9,39]. During the sensing period, local sensing is implemented with the energy detector in each SU. The energy detector in the SU conducts spectrum sensing by executing a binary hypothesis test. According to [3], the binary hypothesis test for a given SU is expressed as
where represents the m-th sample of a SU’s energy detector, and m is a positive integer. and represent the PU’s signal and noise, respectively, and they are modeled as independent circularly symmetric complex Gaussian (CSCG) random processes with variances and , respectively [3]. Let denote the sensing result. Let denote the ratio of to , denote the sampling frequency, and denote the detection threshold. According to [3], under hypothesis , the probability of a false alarm, denoted by , can be approximately expressed as
where is the complementary distribution function of the standard Gaussian distribution. The probability of a false alarm represents the probability that the sensing result is occupied while the actual spectrum state is free. Under hypothesis , the probability of detection, denoted by , can be approximately expressed as
The probability of detection represents the probability that the sensing result is occupied while the actual spectrum state is occupied. Each SU is assumed to share the same sampling frequency, signal-to-noise ratio, and detection threshold for local sensing results by energy detection as in [16,26]; thus, the identical probability of detection and that of a false alarm for each SU could be adopted. Based on (2) and (3), we let and for simplicity and have
and
With respect to the definitions of detection probability in (3) and false alarm probability in (2), the cases where and are considered throughout this paper. Otherwise, the probability of correctly determining the spectrum state would be less than a half, and it is meaningless for SUs to perform spectrum sensing with such low accuracy. Based on the formula of and the aforementioned value intervals of and , we could easily obtain that in (4) and in (5).
2.3. Reporting Model
In the reporting model, we consider that the reporting period consists of n mini-slots with equal duration . Actually, denotes the reporting duration for one SU. The number of mini-slots n is considered to be a positive variable in the time trade-off of three periods for the throughput optimization, where n is a positive integer, , and holds. We adopt random access in the reporting period, where the slotted Aloha (S-Aloha) is adopted due to its easy implementation and low complexity [16]. In the S-Aloha protocol, each SU randomly selects one of the n mini-slots to transmit its local sensing result to the FC [16]. Based on the capture effect, we notice that, in the presence of other overlapping or interfering packets, the strongest packet could capture the receiver when the power strength of the strongest packet is at least d times the power strength of the second-strongest packet, where holds for a perfect capture [16,44]. Throughout this paper, we consider the case that the FC receives local sensing results by S-Aloha protocol with perfect capture. Namely, the FC could successfully receive a local sensing result from a non-repeatable SU at each mini-slot.
Without loss of generality, we adopt the “k-out-of-n” fusion rule to make a final decision about the spectrum state. There are n SUs participating in the CSS, and the local sensing result is independently made by each SU. Then, the FC decides the licensed spectrum is free if there are k or more local sensing results being idle. The closed interval of k is , and k is a positive integer. Since the local sensing results obtained by the SUs are independent of each other for CSS, we denote as the overall false-alarm probability and denote as the overall detection probability. According to [9,26], and are, respectively, given by
and
where holds. The “k-out-of-n” fusion rule is reduced to the “Logic-AND” rule when , and it is reduced to the “Logic-OR” rule when [3].
3. Performance Analysis of the CRN with Given Sensing Period
In this section, we tackle the trade-off between the duration of the reporting period and that of the transmission period for the throughput optimization. Namely, the number of mini-slots n in the reporting period could be traded for the transmission time. We start our analysis by formulating the throughput and collision probability and maximizing the secondary the throughput of the cooperative CRN under the collision constraint.
Based on the definition of the throughput in (1), the throughput of the CRN with a given sensing period , denoted by , is given by
where in (2) is simplified as in (8), since is given in this section. Then we introduce the collision probability. A collision occurs when the FC determines that the licensed spectrum is free while the licensed spectrum is actually occupied. Hence, the collision probability represents the probability that the SU accesses the occupied spectrum and collides with the primary signal.
where in (3) is simplified as , since is given in this section. To protect the primary transmission from the access of SUs to some extent, SUs must maintain the collision constraint such that the collision probability remains below the maximum permissible collision probability , which is commonly viewed as a pre-designed value.
3.1. Throughput Analysis
To tackle the trade-off between the duration of the reporting period and that of the transmission period, the number of mini-slots n is considered to be a variable to maximize the throughput . Though n is defined as a positive integer, the following analysis of the continuous function that regards n as a positive continuous variable applies to the throughput analysis of the positive integer n in the closed interval . Then, we differentiate in (8) with respect to n as
where the k in the “k-out-of-n” fusion rule is considered to be independent of n; thus, is
We observe from (15) that , , , , and hold; thus, the first term on the right-hand side of (15) is negative. Only the multiplicator in the second term on the right-hand side of (15) needs to be further discussed as
With the non-negative integer x in the closed interval , we obtain the sufficient condition that the second term on the right-hand side of (15) is positive as
When the value interval of k in (17) holds, the first term on the right-hand side of (15) is negative, while the second term is positive. Due to the definition of and the value comparison between and , we deduce that the throughput increases with the number of mini-slots n when (17) holds. Otherwise, with the increase of k and , the throughput turns to decrease with the number of mini-slots n. Since the k in the “k-out-of-n” fusion rule is independent of n, holds. We summarize the observations from (10)–(17) as follows.
- When , the monotonicity of the throughput depends on and k. On the right-hand side of (15), the first term is negative, the summation of in the second term is positive, while the summation of in the second term is negative. Compared with the second item as follows, is more likely to decrease with the number of mini-slots n due to the larger value of k.
We also deduce from the value interval of k in the above first item that, when , the lower bound of k in the first item is larger than n; thus, the above first item does not exist. With respect to the above value interval of , the interval of k in the second item occupies the majority part. Moreover, with the increase of k, it is easy to observe from (15) and (17) that the throughput is more likely to increase with n.
3.2. Collision Analysis
Since the number of mini-slots n is considered to be a variable in this section, in order to investigate the monotonicity of the collision probability, we differentiate in (9) with respect to n as
We observe from (19) that , , , and hold; thus, only the multiplicator in (19) needs to be further discussed for the monotonicity of the collision probability . Then, we have
As x is a non-negative integer in the closed interval , we obtain the sufficient condition that the right-hand side of (18) is positive as
Based on (18)–(21), we deduce that the collision probability increases with the number of mini-slots n when (21) holds. Then, we summarize the observations from (18)–(21) as follows.
- When , the collision probability increases with the number of mini-slots n. Thus, the collision probability and the maximum permissible collision probability provide an upper bound of n for the throughput optimization.
Moreover, with the increase of or k, we deduce that the collision probability is more likely to decrease with the number of mini-slots n based on (19).
3.3. Throughput Optimization
Based on the monotonicity analysis of and introduced in Section 3.1 and Section 3.2, we formulate the throughput optimization problem as
Equation (22) represents the goal of maximizing the throughput and aims to optimize the time trade-off between the transmission period and the number of mini-slots in the reporting period. Equation (23) represents that the collision probability of the CRN with a given sensing period should not exceed the maximum permissible collision probability , by which the PUs can be sufficiently protected from illegal access by the SUs [9]. The maximum permissible collision probability is a pre-designed value, which is often determined by the network designer and is independent of other variables [3,9]. Since the throughput depends on the duration of the sensing/reporting/transmission period, and the collision probability reflects the accuracy of spectrum sensing to a certain extent, we optimize the secondary the throughput under the collision constraint to tackle the sensing–the throughput trade-off in the cooperative CRNs. In other words, with the constraint of the sensing performance that requires the time of local sensing and reporting, we aim to provide more transmission time for higher the throughput. With respect to the value intervals of and in Section 2.2, we have
Based on the value interval of k in Section 3.1 and Section 3.2, we summarize the throughput optimization under the collision constraint by optimizing the number of mini-slots n as follows.
- When , the monotonicities of the throughput and the collision probability depend on the values of , , and k. Given specified values of the aforementioned parameters, the optimal n could be determined.
- When , the throughput increases with n, while the monotonicity of depends on the values of and k.
- When , the collision probability increases with the number of mini-slots n. Thus, the collision probability and the maximum permissible collision probability provide an upper bound of n. The monotonicity of the throughput is similar to the second item; thus, the provided upper bound of n achieves the maximum the throughput.
4. Performance Analysis of the CRN with a Given Reporting Period
In this section, we tackle the trade-off between the duration of the sensing period and that of the transmission period for the throughput optimization. Namely, the sensing time could be traded for transmission time. We start our analysis by formulating the throughput and the collision probability and maximizing the secondary the throughput of the cooperative CRN under the collision constraint.
Based on the definition of the throughput in (1), the throughput of the CRN with a given reporting period, denoted by , is given by
The collision probability of the CRN with a given reporting period, denoted by , is given by
Given the duration of the reporting period in this section, the number of mini-slots n in the reporting period is viewed as given in (25) and (26).
4.1. Throughput Analysis
To tackle the trade-off between the duration of the sensing period and that of the transmission period, we optimize the duration of the sensing period to maximize the throughput . We differentiate in (25) with respect to as
where n and k are independent of , and we have the first-order partial derivative of with respect to as
Due to , given in Section 2.2, we deduce that in (28) is negative. As the duration of the sensing period holds, we have
and
where represents that tends to 0 from the right of 0, and represents that tends to from the left of . Then, we discuss the multiplicator in (27) as follows.
Since x is a positive integer in the closed interval based on (25), the sufficient condition that the second term on the right-hand side of (27) is positive can be deduced as
- When , the right-hand side of (27) depends on the values of and k. On the right-hand side of (27), the first term is negative, the second term with is negative, while the second term with is positive. Compared with the above first item, the throughput is more likely to decrease with due to the smaller value of k.
Note that the Equations (27)–(32) are derived using differential and integral calculus to analyze the monotonocity of the throughput with respect to the sensing duration . They are the intermediate results in our analysis of the trade-off among the three periods in the CSS,= and do not exist in the existing literature. Moreover, based on (28), the second-order partial derivative of with respect to is
Due to , given in Section 2.2, we deduce that the second-order partial derivative is positive. Comparing the first and second terms on the right-hand side of (27), we infer that the value of in (28)–(30) plays a key role in (27). Moreover, we infer from (27) and (32) that, with the increase of k (or with the decrease of n), the throughput is more likely to increase with .
4.2. Collision Analysis
To analyze the monotonicity of the collision probability, we differentiate with respect to as
where we have
Similar to the analysis of the collision probability (21), (22) in Section 3.2, since , , , and hold in (34), we obtain the sufficient condition that the right-hand side of (34) is negative as
- When , the right-hand side of (34) is negative, and the collision probability decreases with . Thus, the maximum permissible collision probability provides a lower bound of for throughput optimization.
4.3. Throughput Optimization
Based on the monotonicity analysis in Section 4.1 and Section 4.2, we formulate the throughput optimization problem as
The variable of the throughput optimization in (40) is the duration of the sensing period . Equation (40) aims to optimize the time trade-off between the sensing period and the transmission period. With respect to the value intervals of and in Section 2.2, we have
Based on the value interval of k discussed in Section 4.1 and Section 4.2, we summarize the throughput optimization as follows
- When , the collision probability decreases with ; thus, the maximum permissible collision probability provides a lower bound of in the interval . As turns from positive to negative with the increase of in , the optimal depends on the lower bound of and the value of that satisfies .
- When , the collision probability decreases with , and a lower bound of is also provided. The optimal depends on the values of and k.
- When , the monotonicities of the throughput and collision probability depend on the values of , , and k.
4.4. Special Case
In this subsection, we analyze the throughput and collision performances of the CRN with ; thus, holds due to the definition of the “k-out-of-n” fusion rule in Section 2.3. The case corresponds to the CRN scenario with only one pair of SUs. Based on the throughput in (25) and the collision probability in (26), we formulate the optimization problem by specifying and as
Based on (35), it is easy to deduce that decreases with ; thus, the collision constraint (44) provides a lower bound of for the optimization problem. The lower bound of is given by
Then, we analyze the monotonicity of and differentiate with respect to as
We again differentiate with respect to as
Based on (28) and (33), we deduce that the right-hand side of (47) is negative. Moreover, we have
and
Based on (46)–(49), we deduce that there exists a unique that satisfies the first-order partial derivative of with respect to in (46) equaling zero. If satisfies the inequality (45), is the optimal value of that maximizes the throughput . Otherwise, the lower bound of in (45) is the optimal value of due to the monotonicity analysis in (46)–(49).
Therefore, for the CRN with , we have proved the existence of the optimal duration of the sensing period and provided an approach to obtain the explicit value.
5. Performance Analysis of the CRN with a Given Transmission Period
In this section, we tackle the trade-off between the duration of the sensing period and that of the reporting period for the throughput optimization and start our analysis by formulating the throughput and the collision probability.
Based on the definition of the throughput in (1), the throughput of the CRN with a given transmission period , denoted by , is given by
The collision probability of the CRN with a given transmission period, denoted by , is given by
With respect to the given transmission period in this section, the mathematical relationship between and n can be formulated as
5.1. Throughput Analysis
Notice that both and in (50) could be viewed as functions of n, so we derive partial derivatives of positive functions and as follows.
To tackle the trade-off between and , we differentiate with respect to n as
Then, we discuss the first term on the right-hand side of (54) as follows.
As x is a non-negative integer in the closed interval , we obtain the sufficient condition that the first term on the right-hand side of (54) is positive as
We observe from (54) and (57) that , , , and hold; thus, the sufficient condition that the second term on the right-hand side of (54) is negative could be represented as
As x is a non-negative integer in the closed interval , we simplify the sufficient condition as
We infer from (56) and (59) that the upper bound in (56) and that in (59) are approximately equal. Thus, we neglect the difference in the upper bounds to present the following observations concisely. As in (28)–(30) is negative, we summarize the observations from (54)–(59) as follows.
5.2. Collision Analysis
To analyze the monotonicity of the collision probability, we differentiate with respect to n as
For the first term on the right-hand side of (60), we have
Since x is a non-negative integer in the closed interval , and , , and hold, we obtain the sufficient condition that the first term on the right-hand side of (60) is positive as
Then, we discuss the second term on the right-hand side of (60) as
Similarly, we obtain the sufficient condition that the second term on the right-hand side of (60) is positive as
Therefore, when , the right-hand side of (60) depends on and k. When , the analysis of this case is similar to that of the third case as follows. Due to the limited value interval, this case could be neglected. When , both the first and second terms on the right-hand side of (60) are positive; thus, the collision probability increases with . Moreover, we infer from (62) and (65) that, with the increase of k, is more likely to decrease with .
5.3. Throughput Optimization
Based on the monotonicity analysis in Section 5.1 and Section 5.2, we formulate the throughput optimization problem as
The variable of the throughput optimization in (66) is the number of mini-slots n. (66) aims to optimize the time trade-off between the sensing period and the number of mini-slots in the reporting period. Based on the value interval of k discussed in Section 5.1 and Section 5.2, we summarize the throughput optimization as follows.
- When , the monotonicities of the throughput and the collision probability depend on , , and k.
- When , the throughput decreases with the number of mini-slots n when tends to 0. Comparing it with the third item, the collision probability is less likely to increase with the duration of the reporting period due to the larger value of k. The optimal n depends on , and k.
- When , the collision probability increases with the duration of the reporting period , and the maximum permissible collision probability provides an upper bound of n in the interval . As turns from negative to positive with the increase of , the optimal depends on the upper bound of n.
6. Numerical Results
In this section, we evaluate the throughput and collision performances of the CRN with CSS. The numerical results consist of three parts, which correspond to the theoretical results in Section 3, Section 4 and Section 5, respectively. The impact of the “k-out-of-n” fusion rule on the throughput and collision performances is also presented for comparison. The parameters are set as follows unless otherwise specified. Without loss of generality, the length of a time slot is normalized as a unit time. The probability that the licensed spectrum is occupied is set to , and the probability that the licensed spectrum is free is set to . In accordance with the value intervals of and in Section 2.2, the parameter in is set to , and the parameter in is set to .
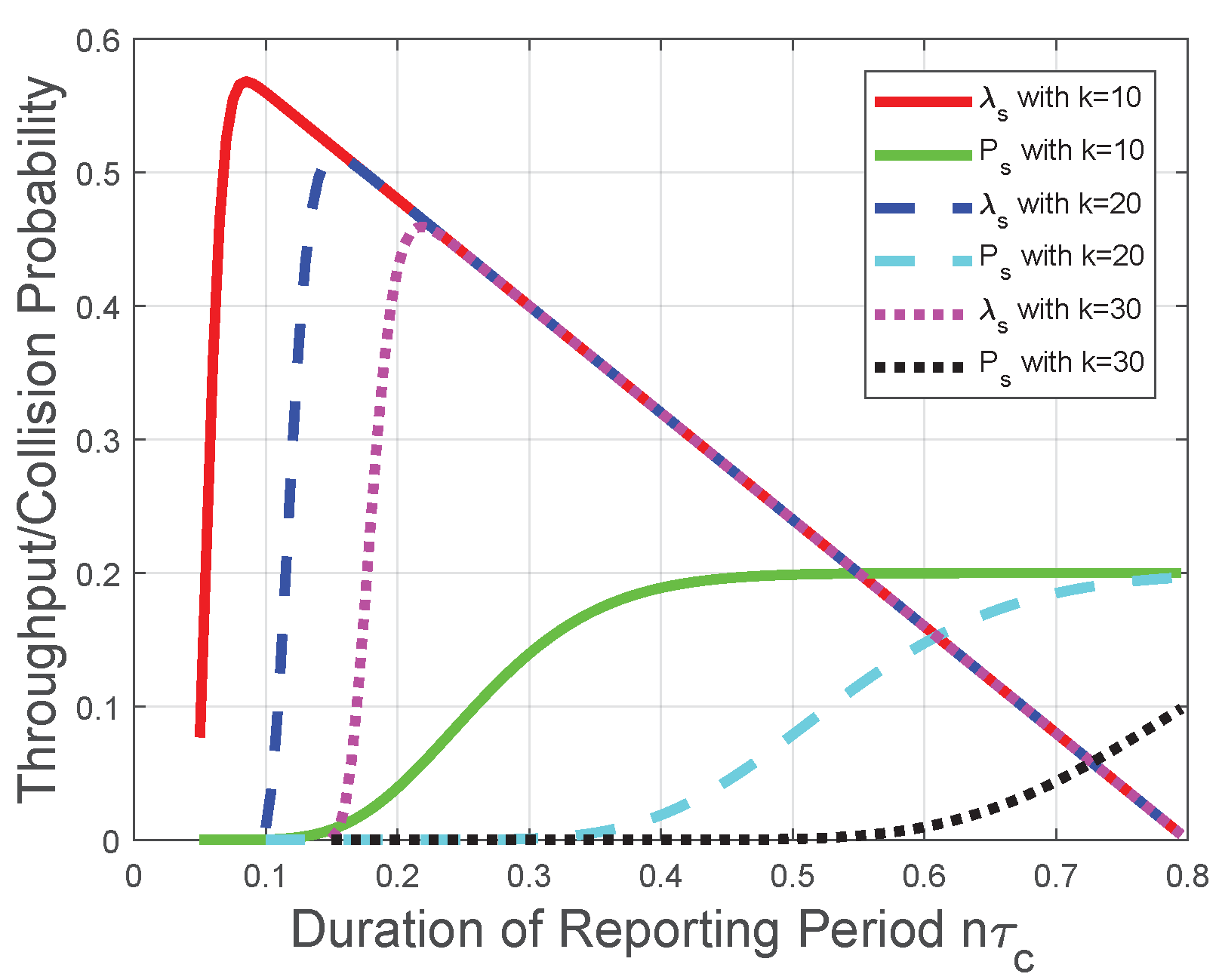
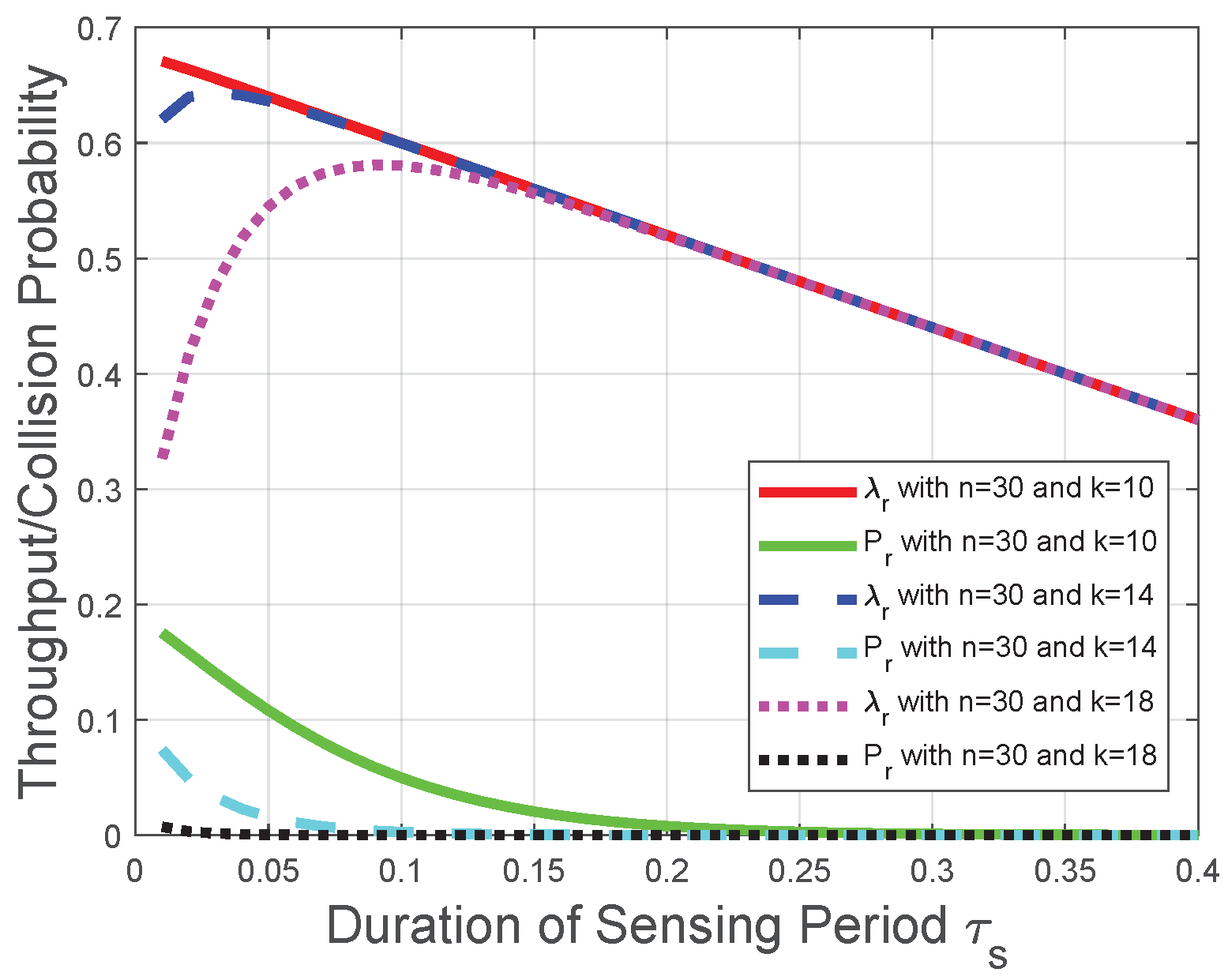
Corresponding to the theoretical analysis in Section 3, Figure 3 plots the throughput and the collision probability of the CRN with a given sensing period. We observe from Figure 3 that the throughput increases with the number of mini-slots n when (17) holds; otherwise, the throughput decreases with the number of mini-slots n. Thus, there is an optimal number of mini-slots for the throughput . When the number of mini-slots is larger than the optimal number of mini-slots, the throughput decreases almost linearly due to the decrease of the duration of the transmission period . Namely, could be viewed as a constant in this scenario, and is represented as a multiplicator in the throughput formula ( in (8)). Moreover, with the increase of k, we observe from Figure 3 that the throughput has a larger value interval where increases with n, which is in accordance with the impact of the “k-out-of-n” fusion rule in Section 3.1. The reason behind this observation is that, based on the definition of the “k-out-of-n” fusion rule and the binomial coefficient in (8), the FC has a higher probability to determine that the licensed spectrum is free when n increases. However, with the increase of n, the increase in the probability that FC determines the licensed spectrum is free could not compensate for the decrease of the transmission time in (8); thus, the throughput decreases with the number of mini-slots n when n is larger than the optimal value. Notice that this result is also in accordance with [16]. We also observe from Figure 3 that the collision probability increases with the number of mini-slots n; thus, provides an upper bound of n in the throughput optimization. This observation is in accordance with the collision analysis in Section 3.2 and the throughput optimization in Section 3.3. The reason is similar as that for the throughput . Based on the definition of the “k-out-of-n” fusion rule, the FC has a higher probability to determine the licensed spectrum is free when n increases. Therefore, the increase of n leads to more opportunities of spectrum access and more collisions with the primary packet transmission.
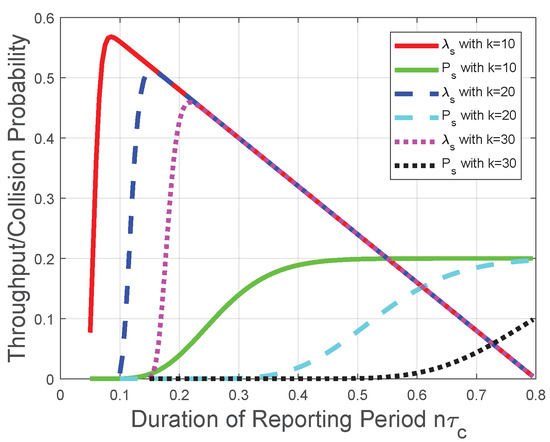
Figure 3.
Throughput and collision performances of the CRN with a given sensing period.
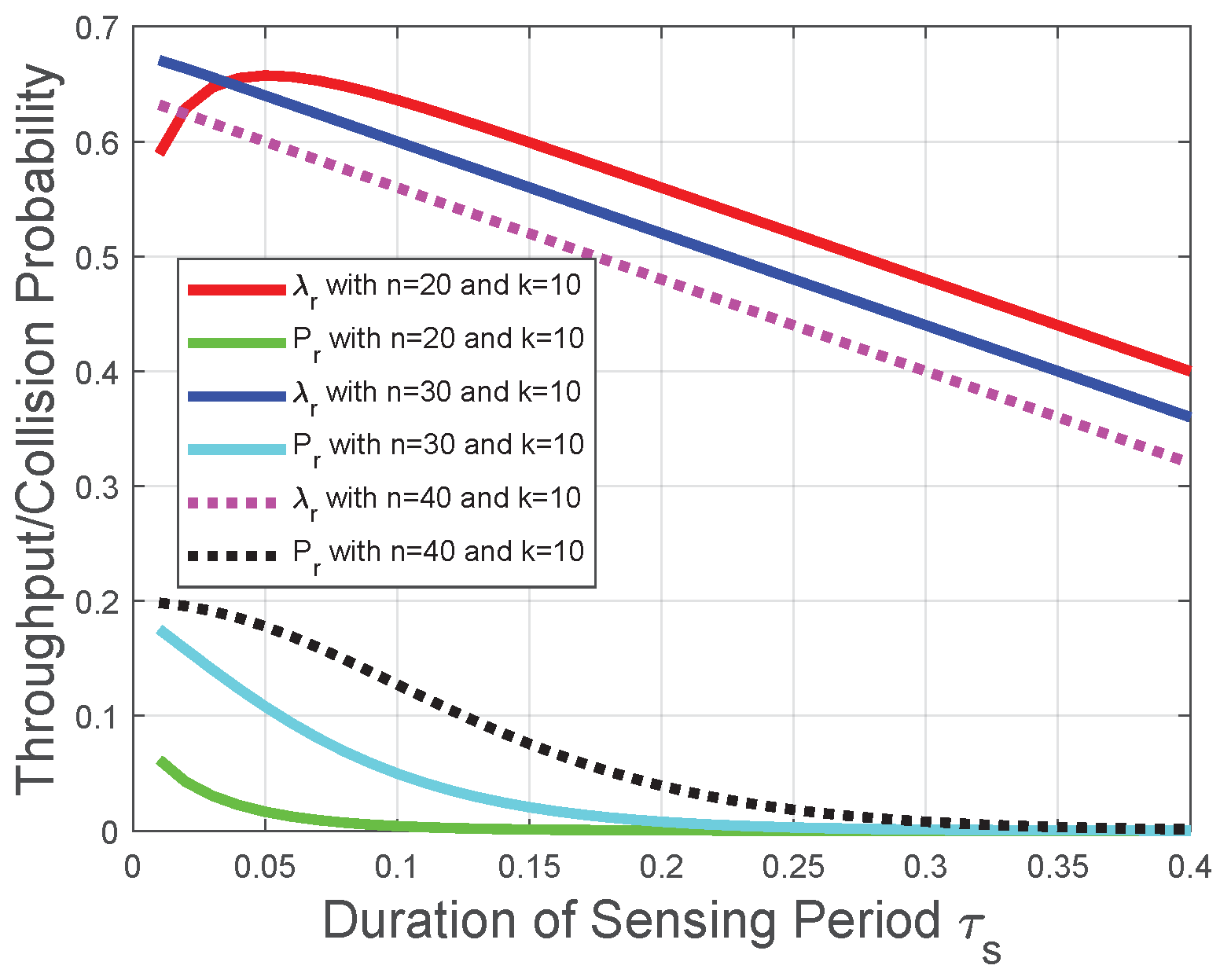
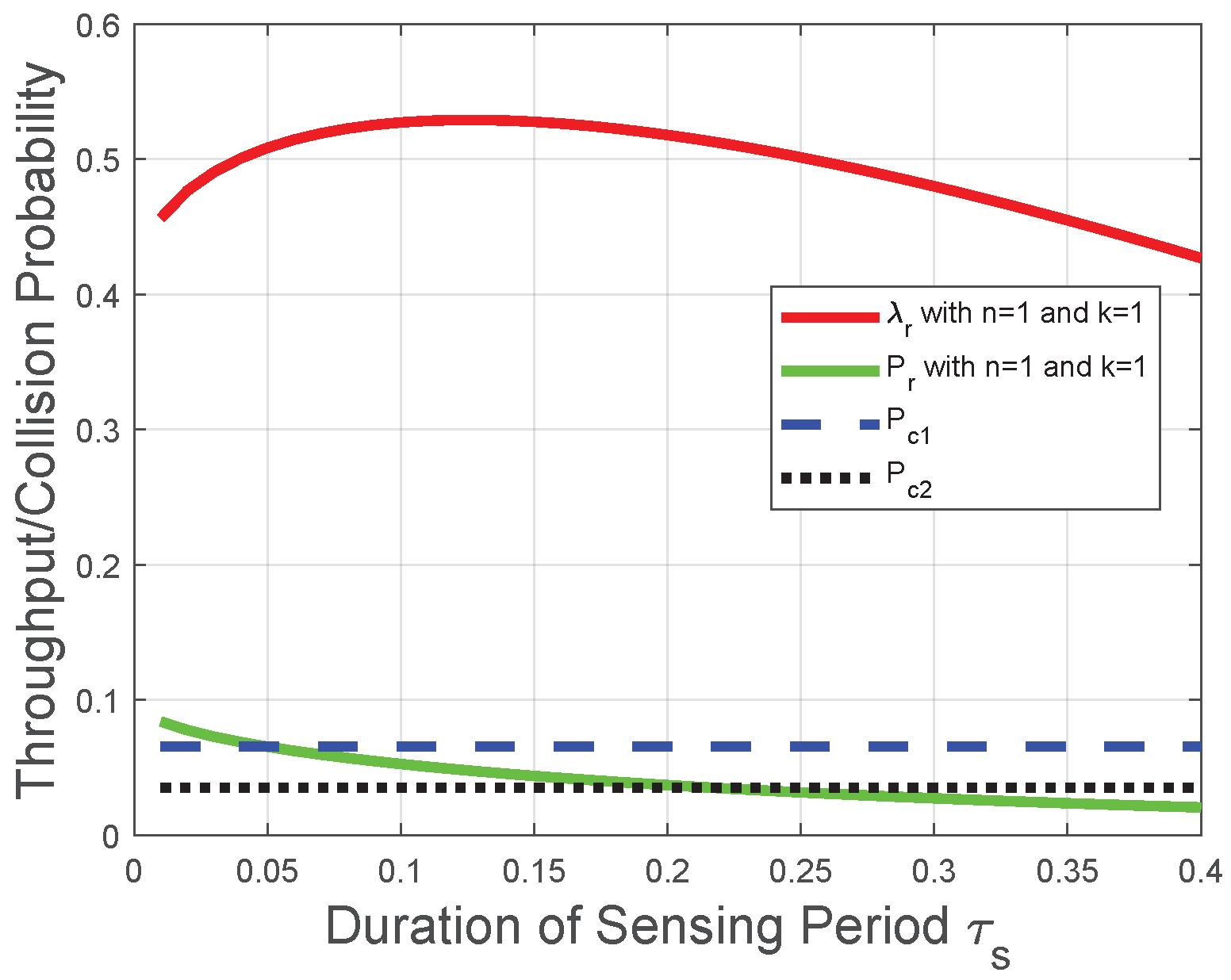
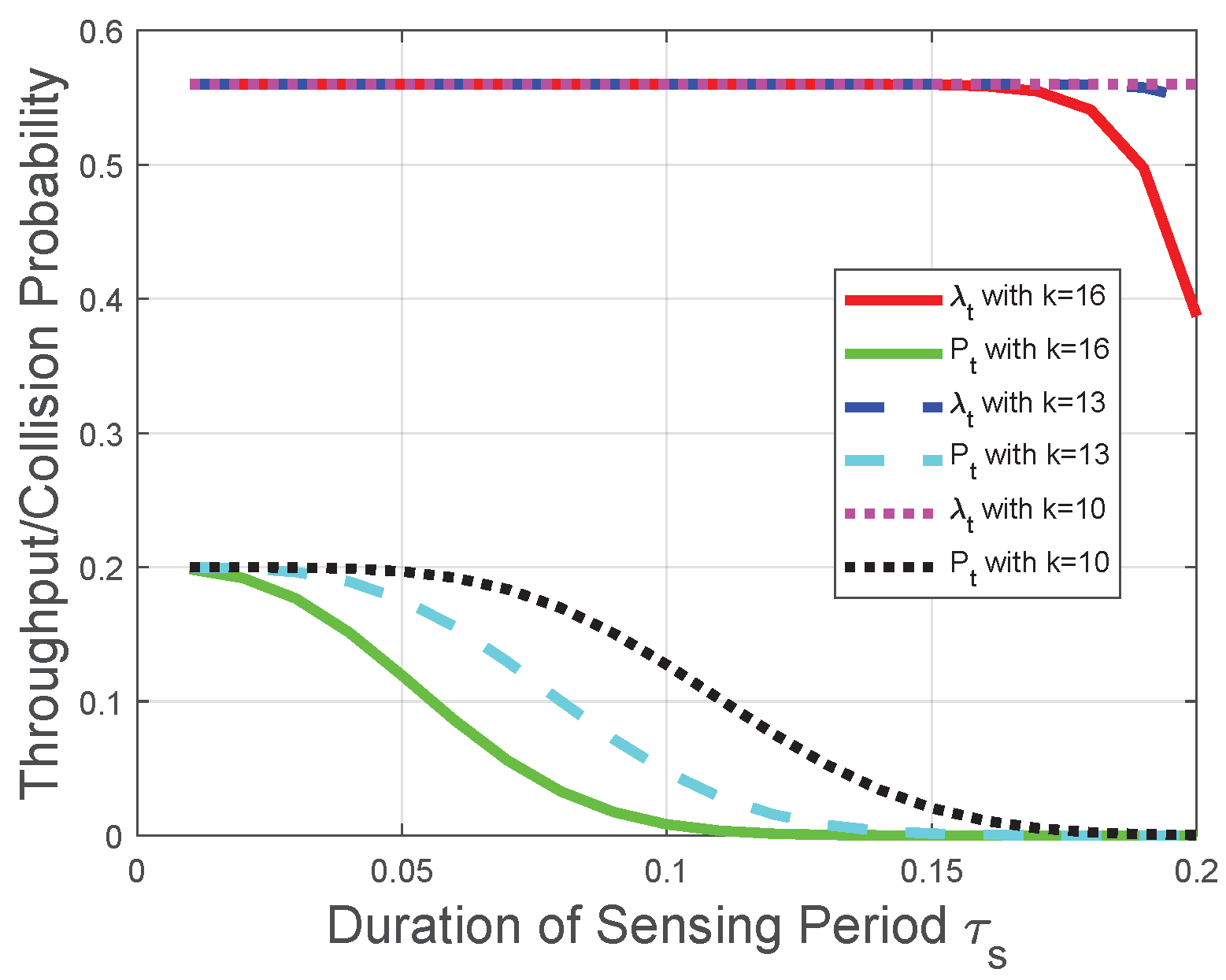
Corresponding to the theoretical analysis in Section 4.1, Section 4.2, Section 4.3, Figure 4 and Figure 5 plot the throughput and the collision probability of the CRN with a given reporting period. In Figure 4, Figure 5 and Figure 6, we tackle the trade-off between the duration of the sensing period and the duration of the transmission period for the optimization problem in the CRN with a given number of mini-slots n in the reporting period and adopt as the variable on the horizontal axis to plot the performances of the throughput and the collision probability. We observe that the throughput increases with the duration of the sensing period when tends to 0, otherwise the throughput decreases with the duration of the sensing period . This observation is in accordance with the throughput analysis in Section 4.1. The reason behind this observation is that, based on the throughput in (25), the increase of leads to the decrease of the transmission time and the increase of the probability, the FC determines the licensed spectrum is free. However, with the increase of , the increase in the probability that FC determines the licensed spectrum is free could not compensate for the reduction of the transmission time in the throughput (25). Thus, there is an optimal duration of the sensing period for the throughput , and the throughput decreases with when the duration of the sensing period is larger than the optimal duration of the sensing period. The throughput decreases almost linearly due to the decrease of the duration of the transmission period in (25). Figure 4 indicates that, with the decrease of n, the throughput is more likely to increase with . Figure 5 indicates that, with the increase of k, the throughput is more likely to increase with . These observations are also in accordance with the throughput analysis and the impact of the “k-out-of-n” fusion rule in Section 4.1. We also observe from Figure 4 and Figure 5 that the collision probability decreases with the duration of the sensing period ; thus, provides a lower bound of in the throughput optimization, which is in accordance with the collision analysis in Section 4.2 and the throughput optimization in Section 4.3. The reason behind this observation is that, based on (35), the probability of detection increases with . Based on the collision probability in (26), the FC has a lower probability to determine the licensed spectrum is free when increases. Therefore, the increase of leads to fewer opportunities of spectrum access and fewer collisions with primary-packet transmission.
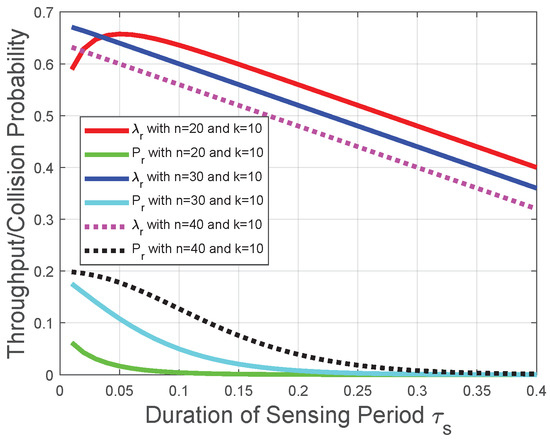
Figure 4.
Throughput and collision performances of the CRN with a given reporting period and k in the “k-out-of-n” fusion rule.
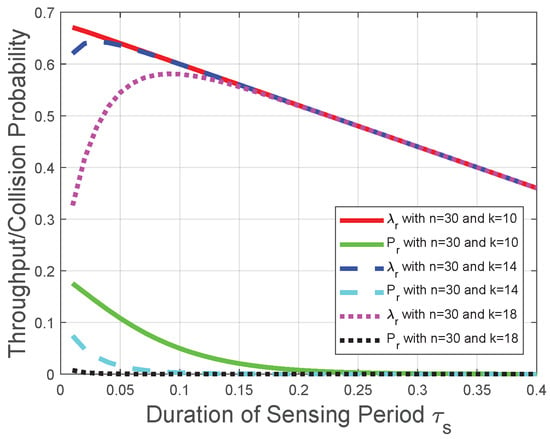
Figure 5.
Throughput and collision performances of the CRN with a given reporting period and n in the “k-out-of-n” fusion rule.
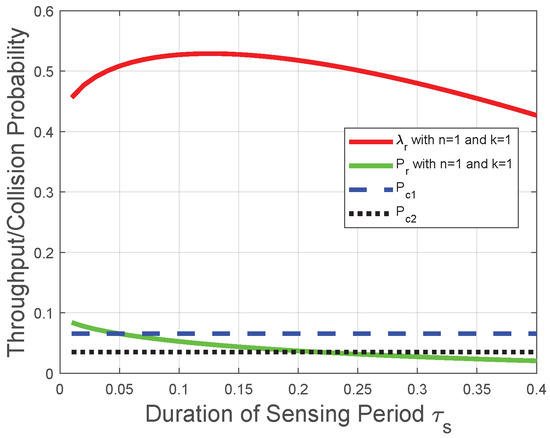
Figure 6.
Throughput and collision performances of the CRN with a given reporting period, , and .
Corresponding to the theoretical analysis in Section 4.4, Figure 6 plots the throughput and collision probability versus the duration of the sensing period. We observe that decreases with the duration of the sensing period ; thus, , and the maximum permissible collision probability provides a lower bound of in the throughput optimization. As for the case of the maximum permissible collision probability with the value , the throughput decreases with the duration of the sensing period under the lower bound of , and this lower bound achieves the maximal throughput. As for the case with value , the throughput first increases with when it is relatively small and decreases with when it is relatively large; thus, the global optimal throughput could be achieved as shown in Figure 6. The above observations are in accordance with the performance analysis in Section 4.4. Moreover, we infer from Figure 3, Figure 4, Figure 5 and Figure 6 that when the duration of the sensing period is relatively large (does not tend to 0), the duration of the transmission period plays a much more important role than that of the reporting period or sensing period. The reason is that, due to the role of the transmission time as a multiplicator in the throughput Formulas (8) and (25), the throughput increases almost linearly with .
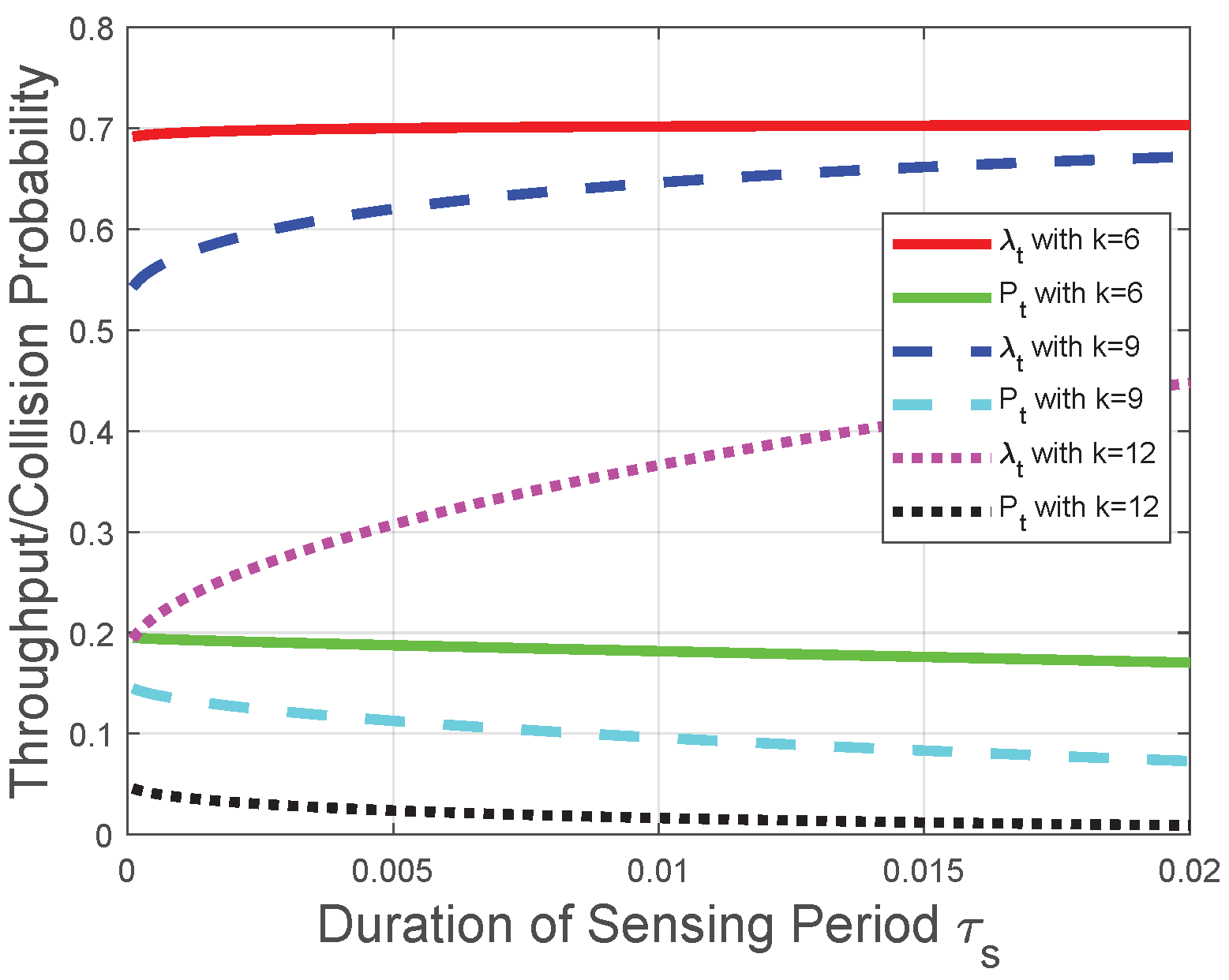
Corresponding to the theoretical analysis in Section 5, Figure 7 and Figure 8 plot the throughput and the collision probability of the CRN with a given transmission period. In Figure 7 and Figure 8, we tackle the trade-off between the duration of the sensing period and the number of mini-slots n in the reporting period for the optimization problem in the CRN with a given duration of the transmission period and adopt as the variable on the horizontal axis to plot the performances of the throughput and the collision probability. We observe that the throughput increases with the duration of the sensing period when tends to 0; otherwise, the throughput decreases with . In the CRN with a given duration of the transmission period , could be viewed as a constant, and this observation is in accordance with the throughput analysis in Section 5.1. Namely, according to the given transmission period, the throughput increasing with is equivalent to the throughput decreasing with , and the observation from Figure 8 that the throughput increases with when tends to 0 is also equivalent to the theoretical result in Section 5.1. The reason behind this observation is that, based on the definition of the “k-out-of-n” fusion rule and the binomial coefficient in (50), the FC has a higher probability to determine the licensed spectrum is free when n or increases. As could be viewed as a constant in this CRN scenario and is considered as a constant, the impact of on the throughput is higher than that of n when tends to 0. The impact relationship between and is due to the monotonicity of in (2) and the binomial coefficient in (50). We also observe from Figure 7 and Figure 8 that the collision probability decreases with , which is in accordance with theoretical result in Section 5.2. Namely, the FC is less likely to determine that the licensed spectrum is free with the increase of (or equivalently, the decrease of n in this CRN scenario). Similarly, Figure 7 indicates that, with the increase of k, the throughput is more likely to decrease with , which is in accordance with the throughput analysis with the fusion rule in Section 5.1. The reason behind this indication is that, with the increase of k, the FC is less likely to determine the licensed spectrum is free according to the received n local sensing results. The increase of is equivalent to the decrease of n in this CRN scenario. Therefore, based on the binomial coefficient in (50), with the increase of k, the throughput is more likely to decrease with .
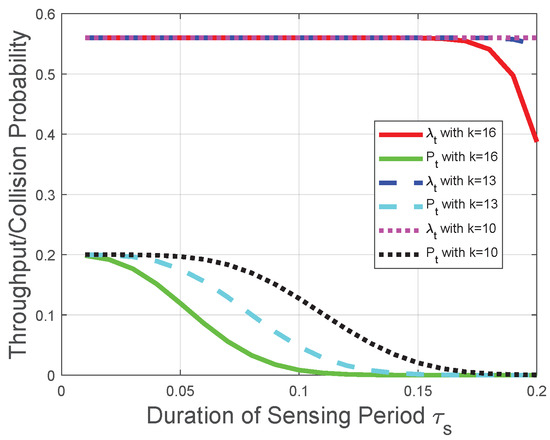
Figure 7.
Throughput and collision performances of the CRN with a given transmission period when is relatively large.
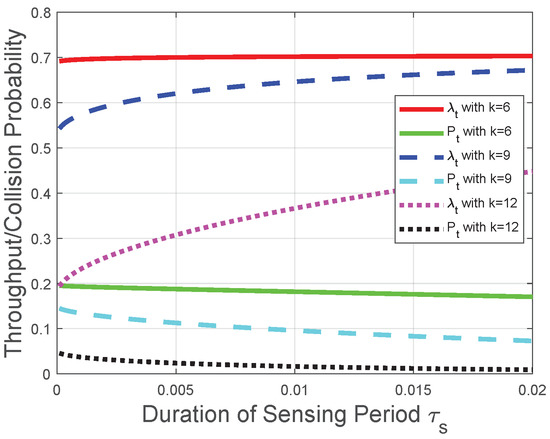
Figure 8.
Throughput and collision performances of the CRN with a given transmission period when tends to 0.
Moreover, we observe from Figure 3, Figure 4, Figure 5, Figure 6, Figure 7 and Figure 8 that both the throughput and the collision probability decrease with the parameter k in the “k-out-of-n” fusion rule, and this observation is in accordance with the definition of the “k-out-of-n” fusion rule. The reason behind this observation is that, with the increase of k, the FC is less likely to determine the licensed spectrum is free according to the received n local sensing results, resulting in a smaller opportunity of secondary-packet transmission and a smaller probability of collision.
7. Conclusions
In this paper, we have studied the throughput and collision performances of the cooperative CRN, where the crucial impact of the reporting design and that of the “k-out-of-n” fusion rule with a varying number of local sensing results are explored. To tackle the time trade-off among sensing, reporting, and transmission, theoretical evaluations and optimizations are performed in the CRNs with a given duration of the sensing/reporting/transmission period, respectively.
We have formulated the throughput and collision probability in the three cases of the CRN. In each case, the monotonicity analysis of the collision constraint and the maximum permissible probability provides an upper bound of n (Section 3.2 and Section 5.2) or a lower bound of (Section 4.2) for throughput maximization in the specific value intervals of sensing parameters. The monotonicity analysis of the throughput with the aforementioned upper/lower bounds provide approaches to the maximal throughput while satisfying the collision constraint. In the other value intervals of sensing parameters, the maximal throughput could be obtained with specified values of sensing and fusion parameters. The derived theoretical results are validated with numerical studies, especially analyzing the effect of the fusion parameters. The derived analytical results can be used to design a cooperative CRN with the required throughput and collision performances. Future works include more complex scenarios, such as the presence of malicious users that may make inappropriate use of the spectrum.
Author Contributions
This research has been carried out via a concerted effort over six months. Each author’s basic role has been summarized in following: conceptualization, X.L.; methodology, X.L.; software, X.L.; validation, X.L.; investigation, X.L.; writing–original draft preparation, X.L.; writing– review and editing, K.Z.; supervision, K.Z.; funding acquisition, K.Z. All authors have read and agreed to the published version of the manuscript.
Funding
Zhejiang Provincial Natural Science Foundation of China, Grant Number: LY21F020022, LY21F020023; National Natural Science Foundation of China, Grant Number: 61902351, 61902353.
Institutional Review Board Statement
Not applicable.
Informed Consent Statement
Not applicable.
Data Availability Statement
Not applicable.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Sani, M.; Tsado, J.; Thomas, S.; Suleiman, H.; Shehu, I.; Shan’una, M. A Survey on Spectrum Sensing Techniques for Cognitive Radio Networks. In Proceedings of the International Conference on Multidisciplinary Engineering and Applied Science (ICMEAS), Abuja, Nigeria, 15–16 July 2021; pp. 1–5. [Google Scholar]
- Al, A.; Hamouda, W. Advances on spectrum sensing for cognitive radio networks: Theory and applications. IEEE Commun. Surveys Tuts. 2017, 19, 1277–1304. [Google Scholar] [CrossRef]
- Liang, Y.-C.; Zeng, Y.; Peh, E.; Hoang, A.T. Sensing-the throughput trade-off for cognitive radio networks. IEEE Trans. Wireless Commun. 2008, 7, 1326–1337. [Google Scholar] [CrossRef]
- Dikmese, S.; Ilyas, Z.; Sofotasios, P.C.; Renfors, M.; Valkama, M. Sparse frequency domain spectrum sensing and sharing based on cyclic prefix autocorrelation. IEEE J. Sel. Areas Commun. 2017, 35, 159–172. [Google Scholar] [CrossRef]
- El-Alfi, N.A.; Abdel-Atty, H.M.; Mohamed, M.A. Sub-Nyquist cyclostationary detection of GFDM for wideband spectrum sensing. IEEE Access 2019, 7, 86403–86411. [Google Scholar] [CrossRef]
- Sedighi, S.; Taherpour, A.; Gazor, S.; Khattab, T. Eigenvalue-based multiple antenna spectrum sensing: Higher order moments. IEEE Trans. Wireless Commun. 2017, 16, 1168–1184. [Google Scholar] [CrossRef]
- Tavana, M.; Rahmati, A.; Shah-Mansouri, V.; Maham, B. Cooperative sensing with joint energy and correlation detection in cognitive radio networks. IEEE Commun. Lett. 2017, 21, 132–135. [Google Scholar] [CrossRef]
- Zheng, K.; Liu, X.; Zhu, Y.; Chi, K.; Liu, K. Total the throughput maximization of cooperative cognitive radio networks with energy harvesting. IEEE Trans. Wireless Commun. 2020, 19, 533–546. [Google Scholar] [CrossRef]
- Liu, X.; Zheng, K.; Chi, K.; Zhu, Y. Cooperative spectrum sensing optimization in energy-harvesting cognitive radio networks. IEEE Trans. Wirel. Commun. 2020, 19, 7663–7676. [Google Scholar] [CrossRef]
- Yuan, X.; Shi, Y.; Qin, X.; Hou, Y.T.; Lou, W.; Sherali, H.D.; Kompella, S.; Midkiff, S.F.; Reed, J.H. Beyond overlay: Reaping mutual benefits for primary and secondary networks through node-level cooperation. IEEE Trans. Mobile Comput. 2017, 16, 2–15. [Google Scholar] [CrossRef]
- Liu, X.; Zheng, K.; Fu, L.; Liu, X.; Wang, X.; Dai, G. Energy efficiency of secure cognitive radio networks with cooperative spectrum sharing. IEEE Trans. Mobile Comput. 2019, 18, 305–318. [Google Scholar] [CrossRef]
- Liu, X.; Zheng, K.; Liu, X.-Y.; Wang, X.; Zhu, Y. Hierarchical cooperation improves delay in cognitive radio networks with heterogeneous mobile secondary nodes. IEEE Trans. Mobile Comput. 2019, 18, 2871–2884. [Google Scholar] [CrossRef]
- Xu, Y.; Liu, J.; Shen, Y.; Liu, J.; Jiang, X.; Taleb, T. Incentive jamming-based secure routing in decentralized Internet of Things. IEEE Internet Things J. 2021, 8, 3000–3013. [Google Scholar] [CrossRef]
- Xu, Y.; Liu, J.; Shen, Y.; Jiang, X.; Ji, Y.; Shiratori, N. QoS-aware secure routing design for wireless networks with selfish jammers. IEEE Trans. Wireless Commun. 2021, 20, 4902–4916. [Google Scholar] [CrossRef]
- Tong, J.; Jin, M.; Guo, Q.; Li, Y. Cooperative spectrum sensing: A blind and soft fusion detector. IEEE Trans. Wireless Commun. 2018, 17, 2726–2737. [Google Scholar] [CrossRef]
- Alhamad, R.; Wang, H.; Yao, Y.D. Cooperative spectrum sensing with random access reporting channels in cognitive radio networks. IEEE Trans. Veh. Technol. 2017, 66, 7249–7261. [Google Scholar] [CrossRef]
- Chaurasiya, R.B.; Shrestha, R. Area-efficient and scalable datafusion based cooperative spectrum sensor for cognitive radio. IEEE Trans. Circuits Syst. Express Briefs 2021, 68, 1198–1202. [Google Scholar] [CrossRef]
- Guimaraes, D.A. Pietra-ricci index detector for centralized data fusion cooperative spectrum sensing. IEEE Trans. Veh. Technol. 2020, 69, 12354–12358. [Google Scholar] [CrossRef]
- Liu, X.; Jia, M.; Zhou, M.; Wang, B.; Durrani, T. Integrated cooperative spectrum sensing and access control for cognitive industrial Internet of Things. IEEE Internet Things J. 2022. [Google Scholar] [CrossRef]
- Lee, D.-J. Adaptive random access for cooperative spectrum sensing in cognitive radio networks. IEEE Trans. Wireless Commun. 2015, 14, 831–840. [Google Scholar] [CrossRef]
- Wang, W.; Chen, L.; Shin, K.G.; Duan, L. Secure cooperative spectrum sensing and access against intelligent malicious behaviors. In Proceedings of the 33rd Annual IEEE International Conference on Computer Communications (INFOCOM’14), Tornoto, ON, Canada, 27 April–2 May 2014; pp. 1267–1275. [Google Scholar]
- Wang, W.; Chen, L.; Shin, K.G.; Duan, L. Thwarting intelligent malicious behaviors in cooperative spectrum sensing. IEEE Trans. Mobile Comput. 2015, 14, 2392–2405. [Google Scholar] [CrossRef]
- Gharib, A.; Ejaz, W.; Ibnkahla, M. Distributed learning-based multi-band multi-user cooperative sensing in cognitive radio networks. In Proceedings of the IEEE Global Communications Conference (GLOBECOM), Abu Dhabi, United Arab Emirates, 9–13 December 2018; pp. 1–6. [Google Scholar]
- Gharib, A.; Ejaz, W.; Ibnkahla, M. Enhanced multiband multiuser cooperative spectrum sensing for distributed CRNs. IEEE Trans. Cogn. Commun. Netw. 2020, 6, 256–270. [Google Scholar] [CrossRef]
- Liu, H.; Chen, J.; Ding, G.; Yan, K.; Cui, L. Optimal cooperative spectrum sensing strategy in cognitive radio networks exploiting RF-energy harvesting. In Proceedings of the International Conference on Wireless Communications Signal Processing (WCSP), Nanjing, China, 17–25 October 2015; pp. 1–5. [Google Scholar]
- Yin, S.; Qu, Z.; Li, S. Achievable the throughput optimization in energy harvesting cognitive radio systems. IEEE J. Sel. Areas Commun. 2015, 33, 407–422. [Google Scholar] [CrossRef]
- Ejaz, W.; Hattab, G.; Cherif, N.; Ibnkahla, M.; Abdelkefi, F.; Siala, M. Cooperative spectrum sensing with heterogeneous devices: Hard combining versus soft combining. IEEE Syst. J. 2018, 12, 981–992. [Google Scholar] [CrossRef]
- Golvaei, M.; Fakharzadeh, M. A fast soft decision algorithm for cooperative spectrum sensing. IEEE Trans. Circuits Syst. Express Briefs 2021, 68, 241–245. [Google Scholar] [CrossRef]
- Yuan, S.; Li, L.; Chigan, C. On MMD-based secure fusion strategy for robust cooperative spectrum sensing. IEEE Trans. Cogn. Commun. Netw. 2019, 5, 504–516. [Google Scholar] [CrossRef]
- Zhang, Y.; Wu, Q.; Shikh-Bahaei, M. On ensemble learning based secure fusion strategy for robust cooperative sensing in full-duplex cognitive radio networks. IEEE Trans. Commun. 2020, 68, 6086–6100. [Google Scholar] [CrossRef]
- Liu, X.; Zheng, K. Probability-based fusion rule in cooperative spectrum sensing with impact of geographic location. IET Commun. 2022, 16, 963–976. [Google Scholar] [CrossRef]
- Perez, J.; Via, J.; Vielva, L.; Ramirez, D. Online detection and SNR estimation in cooperative spectrum sensing. IEEE Trans. Wirel. Commun. 2022, 21, 2521–2533. [Google Scholar] [CrossRef]
- Wang, T.; Song, L.; Han, Z.; Saad, W. Distributed cooperative sensing in cognitive radio networks: An overlapping coalition formation approach. IEEE Trans. Commun. 2014, 62, 3144–3160. [Google Scholar] [CrossRef] [Green Version]
- Jiang, Z.; Yuan, W.; Leung, H.; You, X.; Zheng, Q. Coalition formation and spectrum sharing of cooperative spectrum sensing participants. IEEE Trans. Cybern. 2017, 47, 1133–1146. [Google Scholar] [CrossRef]
- Zheng, K.; Liu, X.-Y.; Liu, X.; Zhu, Y. Hybrid overlay-underlay cognitive radio networks with energy harvesting. IEEE Trans. Commun. 2019, 67, 4669–4682. [Google Scholar] [CrossRef]
- Na, W.; Yoon, J.; Cho, S.; Griffith, D.W.; Golmie, N. Centralized cooperative directional spectrum sensing for cognitive radio networks. IEEE Trans. Mobile Comput. 2018, 17, 1260–1274. [Google Scholar] [CrossRef]
- So, J.; Srikant, R. Improving channel utilization via cooperative spectrum sensing with opportunistic feedback in cognitive radio networks. IEEE Commun. Lett. 2015, 19, 1065–1068. [Google Scholar] [CrossRef]
- Jiang, C.; Chen, Y.; Liu, K.J.; Ren, Y. Renewal-theoretical dynamic spectrum access in cognitive radio network with unknown primary behavior. IEEE J. Sel. Areas Commun. 2013, 31, 406–416. [Google Scholar] [CrossRef]
- Akyildiz, I.F.; Lo, B.F.; Balakrishnan, R. Cooperative spectrum sensing in cognitive radio networks: A survey. Phys. Commun. J. 2011, 4, 40–62. [Google Scholar] [CrossRef]
- Zheng, K.; Liu, X.; Zhu, Y.; Chi, K.; Li, Y. Impact of battery charging on spectrum sensing of CRN with energy harvesting. IEEE Trans. Veh. Technol. 2020, 69, 7545–7557. [Google Scholar] [CrossRef]
- Ma, L.; Li, Y.; Demir, A. Matched filtering assisted energy detection for sensing weak primary user signals. In Proceedings of the IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP), Kyoto, Japan, 25–30 March 2012; pp. 3149–3152. [Google Scholar]
- Zhao, W.; Li, H.; Jin, M.; Liu, Y.; Yoo, S. Eigenvalues-based universal spectrum sensing algorithm in cognitive radio networks. IEEE Syst. J. 2021, 15, 3391–3402. [Google Scholar] [CrossRef]
- Li, Y.; Jayaweera, S.K. Dynamic spectrum tracking using energy and cyclostationarity-based multi-variate non-parametric quickest detection for cognitive radios. IEEE Trans. Wireless Commun. 2013, 12, 3522–3532. [Google Scholar] [CrossRef]
- Sun, X.; Dai, L. To sense or not to sense: A comparative study of CSMA with Aloha. IEEE Trans. Wireless Commun. 2019, 67, 7587–7603. [Google Scholar] [CrossRef]
- Polyanin, A.D.; Manzhrov, A.V. Handbook of Mathematics for Engineers and Scientists, 1st ed.; Chapman & Hall/CRC Press, LCC: New York, NY, USA, 2007. [Google Scholar]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).