Networking-Aware IoT Application Development
Abstract
1. Introduction
2. Background and Related Work
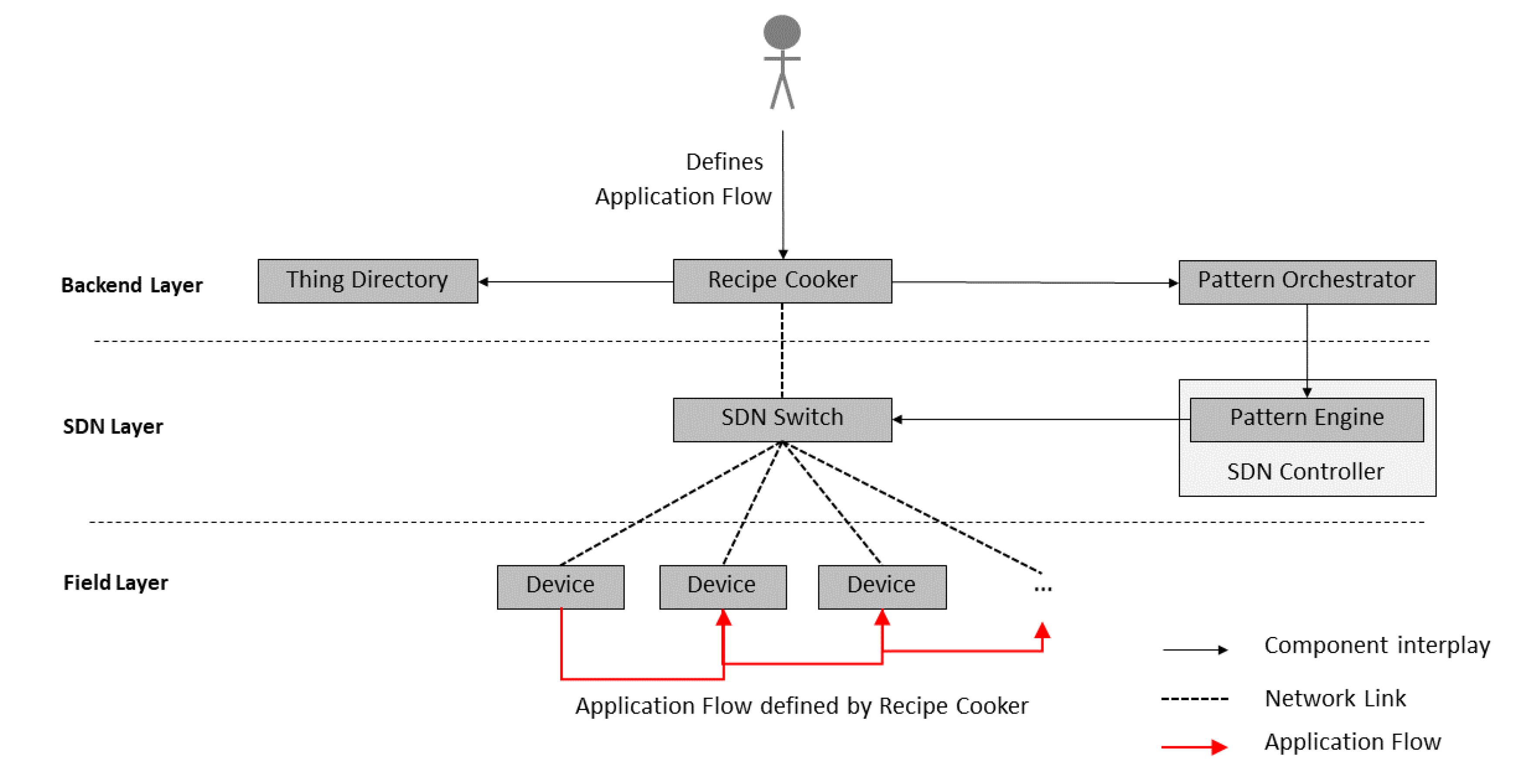
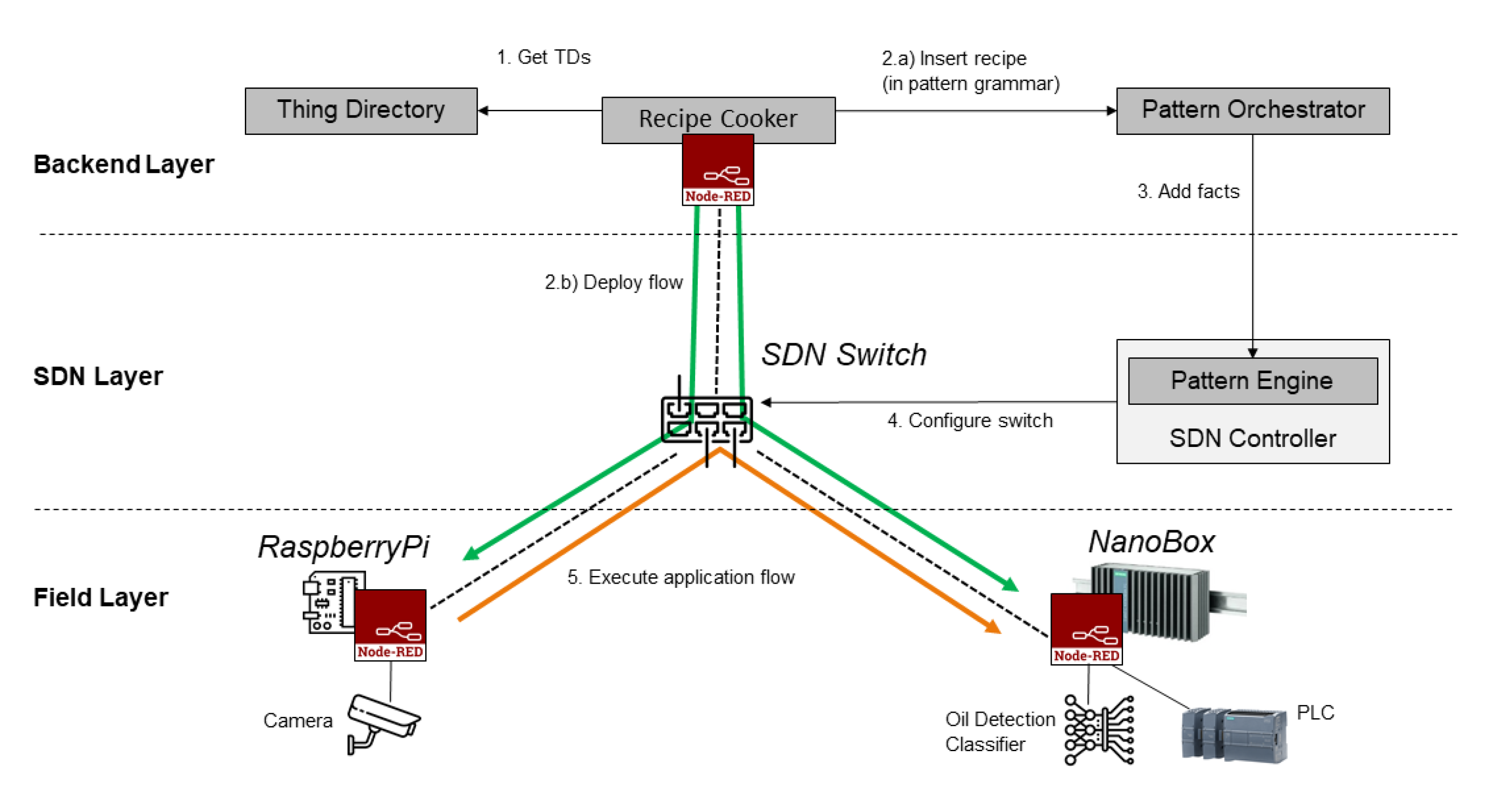
3. An Architecture for Network-Aware IoT Applications
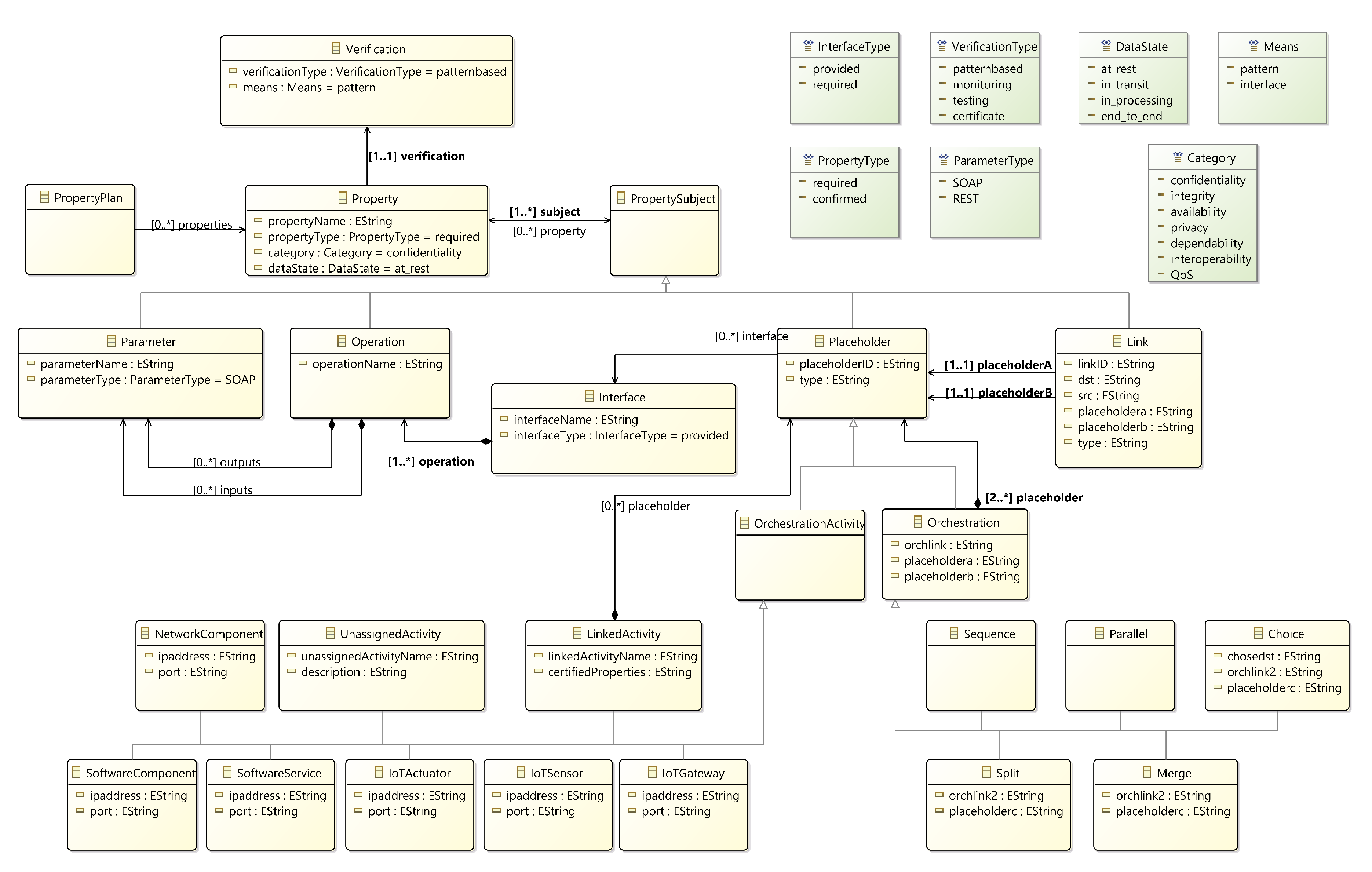
4. Models for IoT Application Flows and Network Patterns
4.1. Model for IoT Application Flows with QoS Constraints
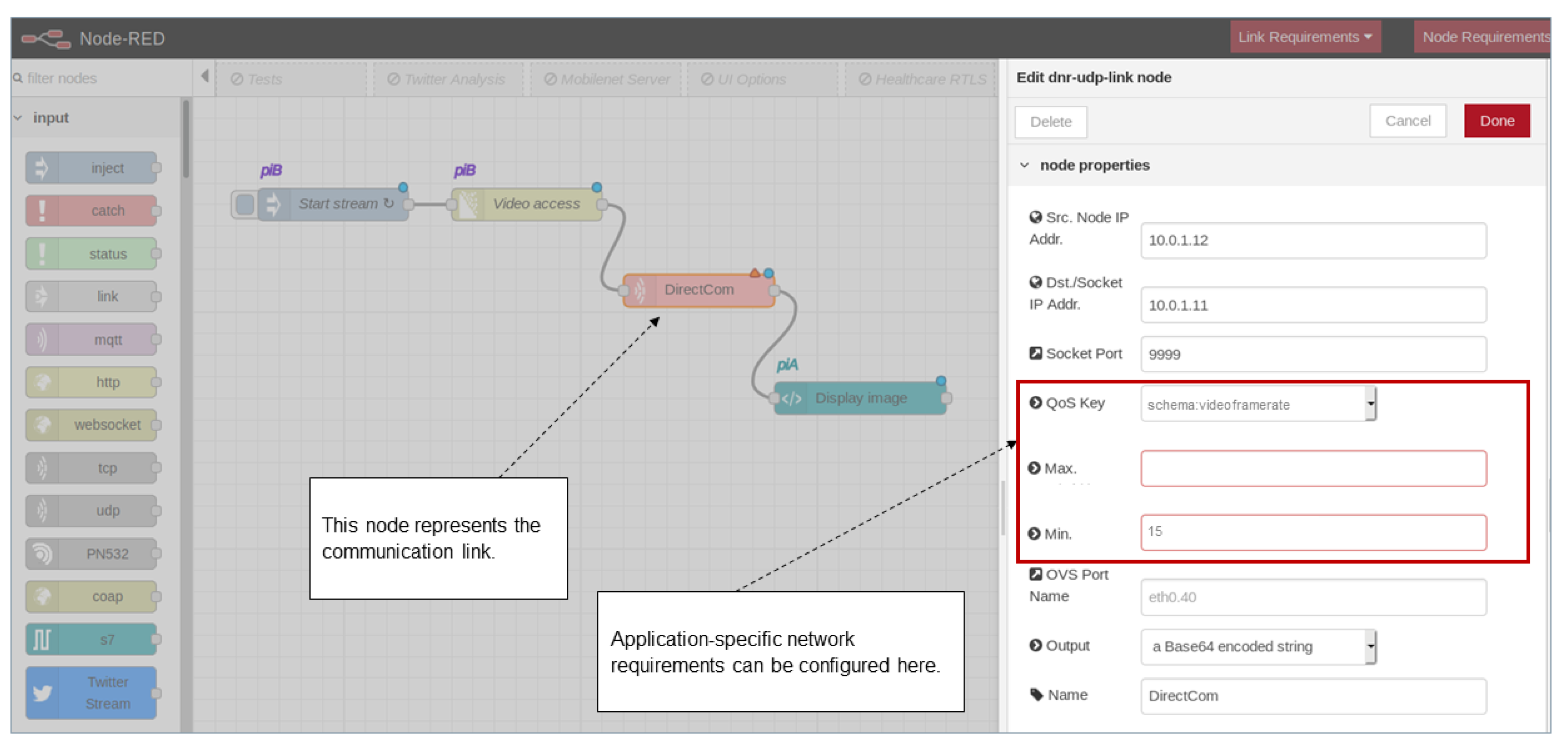
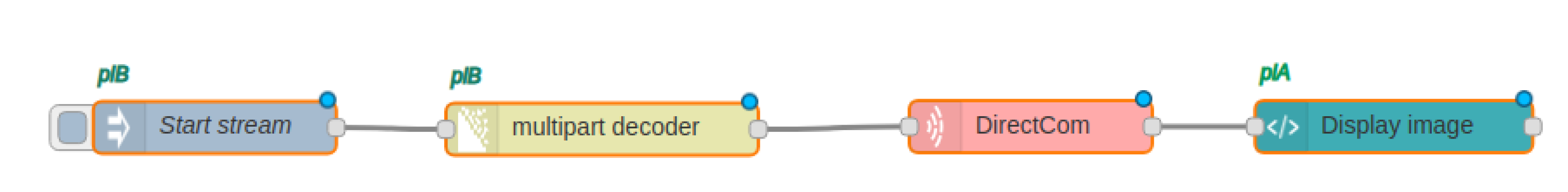
4.2. Defining IoT Application Flows with QoS Constraints
4.3. Pattern-Driven Property Modeling and Management
5. Implementation
| Listing 1: Pattern Language Grammar Snippet |
placeholder
: placeholdertitle OPEN_PAREN placeholderid COMMA interfacename (COMMA interfacename)*
COMMA propertyname (COMMA propertyname)* CLOSE_PAREN
| orchestration
| orchestrationactivity
;
|
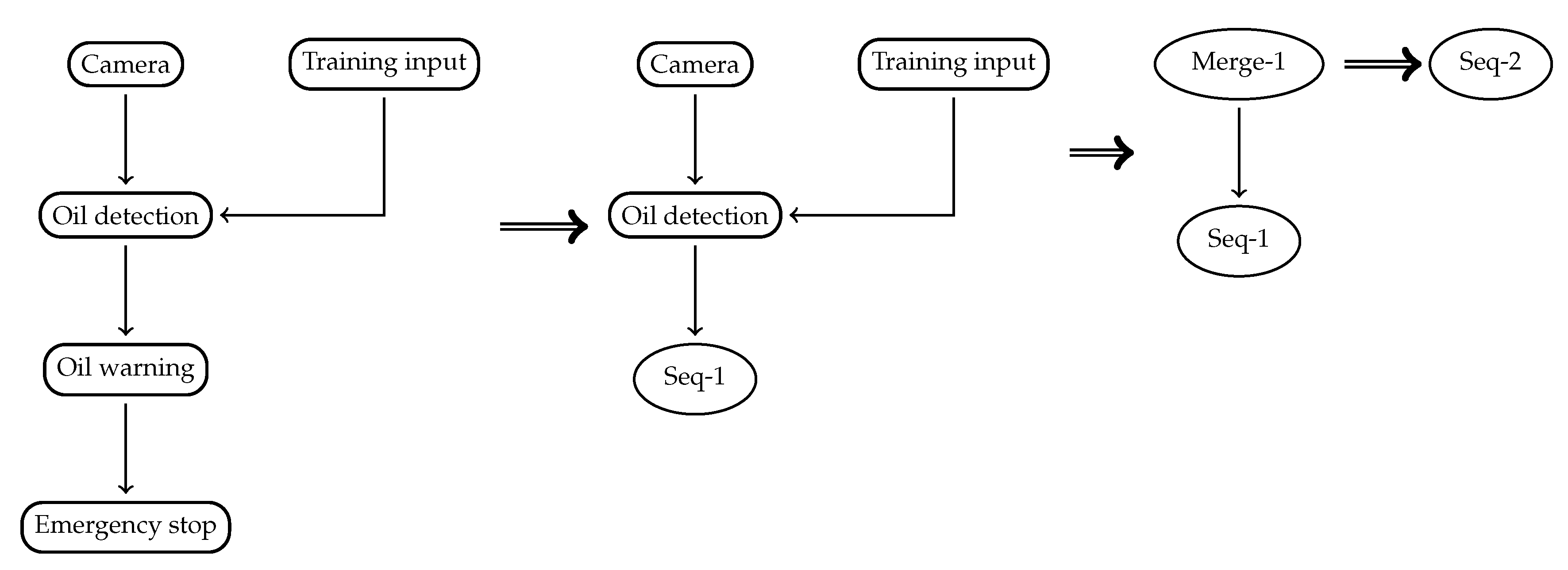
5.1. Translation of Application Flows into Network Configuration
- Emit placeholders and their static properties.
- Merging two nodes and one link into a Sequence.
- Merging three nodes where two nodes are connected to one node into a Merge.
- Merging three nodes where one node is connected to two nodes into a Choice.
- Emit properties that need to be proven.
Placeholder("Camera"),
Placeholder("Oil detection"),
Placeholder("Training Input"),
Placeholder("Oil warning"),
Placeholder("Emergency stop"),
Link("Link1", "Camera", "Oil detection"),
Link("Link2", "Oil detection", "Oil warning"),
Link("Link3", "Oil warning", "Emergency stop"),
Link("Link4", "Training input", "Oil detection"),
Sequence("Seq-1", "Oil warning", "Emergency stop", "Link3"),
Merge("Merge-1", "Camera", "Training input", "Oil detection", "Link1", "Link4"),
Sequence("Seq-2", "Merge-1", "Seq-1", "Link2")
# Static properties
Property("Prop0", required, qosbandwidth, "11400000.0", "Camera", true),
Property("Prop1", required, qosbandwidth, "11400000.0", "Oil detection", true),
# To-be-proven properties
Property("Prop2", required, qosbandwidth, "4000000",..., false)
# Added by monitoring system
Property("Prop3", required, qosbandwidth, "11400000.0", "Link1", true)
|
5.2. Automated Processing of Network Configurations
rule name <attributes>* when <conditional element>* then <action>* end |
5.3. Configuring the SDN
| Listing 2: Specification of QoS (Bandwidth) Property via Drools |
rule "Sequence Bandwidth Verification"
when
Placeholder(pA:=placeholderid)
PR1: Property (pA:=subject, category=="qosbandwidth", prvalue1:=value, satisfied==true)
Placeholder(pB:=placeholderid)
PR2: Property (pB:=subject, category=="qosbandwidth", prvalue2:=value, satisfied==true)
Link (rId:=recipeID, orchLink:=linkid)
PR3: Property (rId:=recipeID, orchLink:=subject, category=="qosbandwidth", prvalue3:=value,
satisfied==true)
SEQ: Sequence(rId:=recipeID, sId:=placeholderid, pA:=placeholdera, pB:=placeholderb,
orchLink:=orchlink)
PR4: Property (rId:=recipeID, sId:=subject, category=="qosbandwidth", prvalue4:=value,
prvalue4<=prvalue1, prvalue4<=prvalue2, prvalue4<=prvalue3, satisfied==false)
then
modify(PR4){satisfied=true};
end
|
| Listing 3: Call to the SDN Controller for configuring the communication with a switch |
curl − XPUT − d’"tcp : OVS_IP_ADDR:TCPListenPORT"’http : //SDN_IP:SDNListenPORT/v1.0/con f /switches/Switch_ID/ ovsdb_addr |
| Listing 4: Call to the SDN Controller for configuring the queues at the switch |
curl − XPOST − d’{”portname” : ”Port_Name", "type": "linux − htb|linux-hfsc", "max_rate": "int”, ”queues” : [{”maxrate” : ”int", "min_rate": "int”}, ...]}’http : //SDN_IP:SDNListenPORT/qos/queue/Switch_ID |
| Listing 5: Call to the SDN Controller for configuring a flow entry |
curl − XPOST − d’”priority” : 1, ”match” : ”ipv4src” : ”10.0.0.1”, ”ipv4dst” : ”10.0.0.2”, ”actions” : [”type” : ”ENQUE”, ”queueid” : 1, ”port” : 1]...’http : // SDN_IP:SDNListenPORT/qos/rules/Switch_ID |
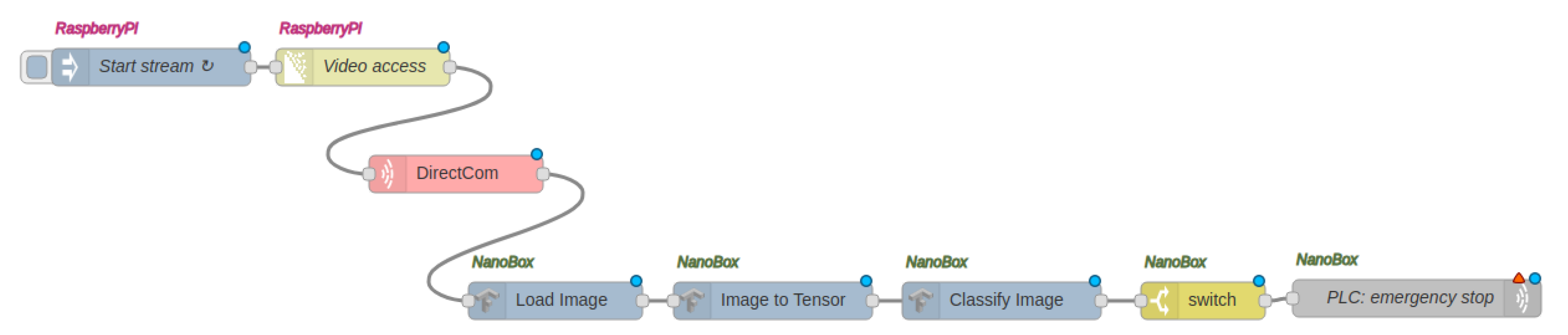
6. Proof of Concept Application and Evaluation
6.1. Oil Detection Application
6.2. Performance Assessment
6.2.1. Evaluation of Network Usage
6.2.2. Evaluation of Pattern Engine
7. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Raggett, D. The web of things: Challenges and opportunities. Computer 2015, 48, 26–32. [Google Scholar] [CrossRef]
- Hannelius, T.; Salmenpera, M.; Kuikka, S. Roadmap to adopting OPC UA. In Proceedings of the 2008 6th IEEE International Conference on Industrial Informatics, Daejeon, Korea, 13–16 July 2008; pp. 756–761. [Google Scholar]
- Swetina, J.; Lu, G.; Jacobs, P.; Ennesser, F.; Song, J. Toward a standardized common M2M service layer platform: Introduction to oneM2M. IEEE Wirel. Commun. 2014, 21, 20–26. [Google Scholar] [CrossRef]
- Pahl, M.O.; Carle, G. Taking Smart Space Users into the Development Loop: An Architecture for Community Based Software Development for Smart Spaces. In Proceedings of the 2013 ACM Conference on Pervasive and Ubiquitous Computing Adjunct Publication, Zurich, Switzerland, 8–12 September 2013; ACM: New York, NY, USA, 2013; pp. 793–800. [Google Scholar]
- Charpenay, V.; Käbisch, S.; Kosch, H. Introducing Thing Descriptions and Interactions: An Ontology for the Web of Things. In SR+ SWIT@ ISWC; Academic Press: Cambridge, MA, USA, 2016; pp. 55–66. [Google Scholar]
- Thuluva, A.S.; Bröring, A.; Medagoda, G.P.; Don, H.; Anicic, D.; Seeger, J. Recipes for IoT Applications. In Proceedings of the IoT ’17 Seventh International Conference on the Internet of Things, Linz, Austria, 22–25 October 2017; ACM: New York, NY, USA, 2017; pp. 10:1–10:8. [Google Scholar] [CrossRef]
- Seeger, J.; Deshmukh, R.A.; Bröring, A. Running Distributed and Dynamic IoT Choreographies. In Proceedings of the 2018 IEEE Global Internet of Things Summit (GIoTS) Proceedings, Bilbao, Spain, 4–7 June 2018; Volume 2, pp. 33–38. [Google Scholar]
- Seeger, J.; Deshmukh, R.A.; Sarafov, V.; Bröring, A. Dynamic IoT Choreographies. IEEE Pervasive Comput. 2019, 18, 19–27. [Google Scholar] [CrossRef]
- Seeger, J.; Bröring, A.; Pahl, M.O.; Sakic, E. Rule-Based Translation of Application-Level QoS Constraints into SDN Configurations for the IoT. In Proceedings of the 2019 European Conference on Networks and Communications (EuCNC), Valencia, Spain, 18–21 June 2019; pp. 432–437. [Google Scholar]
- Sheng, Q.Z.; Qiao, X.; Vasilakos, A.V.; Szabo, C.; Bourne, S.; Xu, X. Web services composition: A decade’s overview. Inf. Sci. 2014, 280, 218–238. [Google Scholar] [CrossRef]
- Lécué, F.; Gorronogoitia, Y.; Gonzalez, R.; Radzimski, M.; Villa, M. SOA4All: An innovative integrated approach to services composition. In Proceedings of the International Conference on Web Services, Miami, FL, USA, 5–10 July 2010; pp. 58–67. [Google Scholar]
- Kopecky, J.; Gomadam, K.; Vitvar, T. hrests: An html microformat for describing restful web services. In Proceedings of the WI-IAT’08 International Conference on Web Intelligence and Intelligent Agent Technology, Sydney, NSW, Australia, 9–12 December 2008; pp. 619–625. [Google Scholar]
- Mayer, S.; Verborgh, R.; Kovatsch, M.; Mattern, F. Smart Configuration of Smart Environments. IEEE Trans. Autom. Sci. Eng. 2016, 13, 1247–1255. [Google Scholar] [CrossRef]
- El Kaed, C.; Khan, I.; Van Den Berg, A.; Hossayni, H.; Saint-Marcel, C. SRE: Semantic rules engine for the industrial Internet-of-Things gateways. IEEE Trans. Ind. Inform. 2017, 14, 715–724. [Google Scholar] [CrossRef]
- Hayyolalam, V.; Pourhaji Kazem, A.A. A systematic literature review on QoS-aware service composition and selection in cloud environment. J. Netw. Comput. Appl. 2018, 110, 52–74. [Google Scholar] [CrossRef]
- Mokhtar, S.B.; Preuveneers, D.; Georgantas, N.; Issarny, V.; Berbers, Y. EASY: Efficient semAntic Service discoverY in pervasive computing environments with QoS and context support. J. Syst. Softw. 2008, 81, 785–808. [Google Scholar] [CrossRef]
- Moustafa, A.; Zhang, M.; Bai, Q. Trustworthy Stigmergic Service Compositionand Adaptation in Decentralized Environments. IEEE Trans. Serv. Comput. 2016, 9, 317–329. [Google Scholar] [CrossRef]
- Liu, C.; Cao, J.; Wang, J. A Reliable and Efficient Distributed Service Composition Approach in Pervasive Environments. IEEE Trans. Mob. Comput. 2017, 16, 1231–1245. [Google Scholar] [CrossRef]
- Nunes, B.A.A.; Mendonca, M.; Nguyen, X.N.; Obraczka, K.; Turletti, T. A Survey of Software-Defined Networking: Past, Present, and Future of Programmable Networks. IEEE Commun. Surv. Tutor. 2014, 16, 1617–1634. [Google Scholar] [CrossRef]
- McKeown, N.; Anderson, T.; Balakrishnan, H.; Parulkar, G.; Peterson, L.; Rexford, J.; Shenker, S.; Turner, J. OpenFlow: Enabling innovation in campus networks. ACM SIGCOMM Comput. Commun. Rev. 2008, 38, 69–74. [Google Scholar] [CrossRef]
- Blake, S.; Black, D.; Carlson, M.; Davies, E.; Wang, Z.; Weiss, W. RFC 2475—An Architecture for Differentiated Services; Technical Report. Available online: https://dl.acm.org/doi/pdf/10.17487/RFC2475 (accessed on 31 January 2020).
- Braden, R.; Clark, D.; Shenker, S. RFC 1633—Integrated Services in the Internet Architecture: An Overview. Technical Report. Available online: https://dl.acm.org/doi/pdf/10.17487/RFC1633 (accessed on 31 January 2020).
- Mekikis, P.V.; Ramantas, K.; Sanabria-Russo, L.; Serra, J.; Antonopoulos, A.; Pubill, D.; Kartsakli, E.; Verikoukis, C. NFV-enabled experimental platform for 5G Tactile Internet support in industrial environments. IEEE Trans. Industrial Inform. 2019, 16, 1895–1903. [Google Scholar] [CrossRef]
- Sarrigiannis, I.; Ramantas, K.; Kartsakli, E.; Mekikis, P.V.; Antonopoulos, A.; Verikoukis, C. Online VNF Lifecycle Management in a MEC-enabled 5G IoT Architecture. IEEE Internet Things J. 2019. [Google Scholar] [CrossRef]
- Seeger, J.; Bröring, A.; Carle, G. Optimally Self-Healing IoT Choreographies. arXiv 2020, arXiv:1907.04611. under review. [Google Scholar]
- Naman, A.T.; Wang, Y.; Gharakheili, H.H.; Sivaraman, V.; Taubman, D. Responsive high throughput congestion control for interactive applications over SDN-enabled networks. Comput. Netw. 2018, 134, 152–166. [Google Scholar] [CrossRef]
- Akella, A.V.; Xiong, K. Quality of Service (QoS)-Guaranteed Network Resource Allocation via Software Defined Networking (SDN). In Proceedings of the 2014 IEEE 12th International Conference on Dependable, Autonomic and Secure Computing, Dalian, China, 24–27 August 2014; pp. 7–13. [Google Scholar] [CrossRef]
- Kucminski, A.; Al-Jawad, A.; Shah, P.; Trestian, R. QoS-based routing over software defined networks. In Proceedings of the 2017 IEEE International Symposium on Broadband Multimedia Systems and Broadcasting (BMSB), Cagliari, Italy, 7–9 June 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Li, F.; Cao, J.; Wang, X.; Sun, Y. A QoS Guaranteed Technique for Cloud Applications Based on Software Defined Networking. IEEE Access 2017, 5, 21229–21241. [Google Scholar] [CrossRef]
- Guck, J.W.; Van Bemten, A.; Kellerer, W. DetServ: Network Models for Real-Time QoS Provisioning in SDN-Based Industrial Environments. IEEE Trans. Netw. Serv. Manag. 2017, 14, 1003–1017. [Google Scholar] [CrossRef]
- Gorlatch, S.; Humernbrum, T. Enabling high-level QoS metrics for interactive online applications using SDN. In Proceedings of the 2015 International Conference on Computing, Networking and Communications (ICNC), Garden Grove, CA, USA, 16–19 February 2015; pp. 707–711. [Google Scholar] [CrossRef]
- Ur, B.; Pak Yong Ho, M.; Brawner, S.; Lee, J.; Mennicken, S.; Picard, N.; Schulze, D.; Littman, M.L. Trigger-Action Programming in the Wild: An Analysis of 200,000 IFTTT Recipes. In Proceedings of the 2016 CHI Conference on Human Factors in Computing Systems, San Jose, CA, USA, 7–12 May 2016; ACM: New York, NY, USA, 2016; pp. 3227–3231. [Google Scholar] [CrossRef]
- Giang, N.K.; Blackstock, M.; Lea, R.; Leung, V.C.M. Developing IoT applications in the Fog: A Distributed Dataflow approach. In Proceedings of the 2015 5th International Conference on the Internet of Things (IOT), Seoul, Korea, 26–28 October 2015; pp. 155–162. [Google Scholar] [CrossRef]
- Salatino, M.; De Maio, M.; Aliverti, E. Mastering Jboss Drools 6; Packt Publishing Ltd.: Birmingham, UK, 2016. [Google Scholar]
- Forgy, C.L. Rete: A fast algorithm for the many pattern/many object pattern match problem. In Readings in Artificial Intelligence and Databases; Elsevier: Amsterdam, The Netherlands, 1989; pp. 547–559. [Google Scholar]
- Bröring, A.; Schmid, S.; Schindhelm, C.K.; Khelil, A.; Käbisch, S.; Kramer, D.; Phuoc, D.L.; Mitic, J.; Anicic, D.; Teniente, E. Enabling IoT Ecosystems through Platform Interoperability. IEEE Softw. 2017, 34, 54–61. [Google Scholar] [CrossRef]
- Guha, R.; Brickley, D.; Macbeth, S. Schema. org: Evolution of structured data on the web. Commun. ACM 2016, 59, 44–51. [Google Scholar] [CrossRef]
- Hodgson, R.; Keller, P.J. QUDT-Quantities, Units, Dimensions and Data Types in OWL and XML. 2011. Available online: http://www.qudt.org (accessed on 6 February 2020).
- Shi, W.; Cao, J.; Zhang, Q.; Li, Y.; Xu, L. Edge computing: Vision and challenges. IEEE Internet Things J. 2016, 3, 637–646. [Google Scholar] [CrossRef]
- Meusel, R.; Bizer, C.; Paulheim, H. A web-scale study of the adoption and evolution of the schema. org vocabulary over time. In Proceedings of the 5th International Conference on Web Intelligence, Mining and Semantics, Larnaca, Cyprus, 13–15 July 2015; ACM: New York, NY, USA; p. 15. [Google Scholar]
- Fysarakis, K.; Papoutsakis, M.; Petroulakis, N.; Spanoudakis, G. Towards IoT Orchestrations with Security, Privacy, Dependability and Interoperability Guarantees. In Proceedings of the 2019 IEEE Global Communications Conference (GLOBECOM 2019), Waikoloa, HI, USA, 9–13 December 2019. [Google Scholar]
- Soultatos, O.; Papoutsakis, M.; Fysarakis, K.; Hatzivasilis, G.; Michalodimitrakis, M.; Spanoudakis, G.; Ioannidis, S. Pattern-Driven Security, Privacy, Dependability and Interoperability Management of IoT Environments. In Proceedings of the 2019 IEEE 24th International Workshop on Computer Aided Modeling and Design of Communication Links and Networks (CAMAD), Limassol, Cyprus, 11–13 September 2019; pp. 1–6. [Google Scholar]
- Fysarakis, K.; Spanoudakis, G.; Petroulakis, N.; Soultatos, O.; Bröring, A.; Marktscheffel, T. Architectural Patterns for Secure IoT Orchestrations. In Proceedings of the Global IoT Summit 2019 (GIoTS’19), Aarhus, Denmark, 17–21 June 2019. [Google Scholar]
- Pino, L.; Spanoudakis, G.; Fuchs, A.; Gurgens, S. Discovering Secure Service Compositions. In Proceedings of the 4th International Conference on Cloud Computing and Services Sciences (CLOSER 2014), Barcelona, Spain, 3–5 April 2014; Available online: https://openaccess.city.ac.uk/id/eprint/4064/ (accessed on 31 January 2020).
- Pino, L.; Spanoudakis, G.; Krotsiani, M.; Mahbub, K. Pattern Based Design and Verification of Secure Service Compositions. IEEE Trans. Serv. Comput. 2017. [Google Scholar] [CrossRef]
- Maña, A.; Damiani, E.; Guergens, S.; Spanoudakis, G. Extensions to Pattern Formats for Cyber Physical Systems. In Proceedings of the 31st Conference on Pattern Languages of Programs (PLoP’14), Monticello, IL, USA, 14–17 September 2014. [Google Scholar]
- Petroulakis, N.E.; Spanoudakis, G.; Askoxylakis, I.G. Fault tolerance using an sdn pattern framework. In Proceedings of the IEEE Global Communications Conference (GLOBECOM), Singapore, 4–8 December 2017; pp. 1–6. [Google Scholar]
- Extended Backus-Naur Form. Available online: https://tomassetti.me/ebnf (accessed on 6 February 2020).
- ANother Tool for Language Recognition. Available online: https://www.antlr.org (accessed on 6 February 2020).
- Business Rules Management System (BRMS). Available online: https://www.drools.org (accessed on 6 February 2020).
- Howard, A.G.; Zhu, M.; Chen, B.; Kalenichenko, D.; Wang, W.; Weyand, T.; Andreetto, M.; Adam, H. Mobilenets: Efficient convolutional neural networks for mobile vision applications. arXiv 2017, arXiv:1704.04861. [Google Scholar]
- Abadi, M.; Agarwal, A.; Barham, P.; Brevdo, E.; Chen, Z.; Citro, C.; Corrado, G.S.; Davis, A.; Dean, J.; Devin, M.; et al. Tensorflow: Large-scale machine learning on heterogeneous distributed systems. arXiv 2016, arXiv:1603.04467. [Google Scholar]
- Berger, H. Automating with SIMATIC: Controllers, Software, Programming, Data; John Wiley & Sons: Hoboken, NJ, USA, 2012. [Google Scholar]
- Siemens. SIMATIC Box IPC. Available online: https://new.siemens.com/global/en/products/automation/pc-based/simatic-box-ipc.html#SIMATICIPC227E (accessed on 29 November 2019).
- Park, J.; Samarakoon, S.; Bennis, M.; Debbah, M. Wireless network intelligence at the edge. Proc. IEEE 2019, 107, 2204–2239. [Google Scholar] [CrossRef]


| Name | Description | Valid Value Example |
|---|---|---|
| recipeID | The ID of the recipe the fact belongs to | “WF1” |
| factID | The identifier of the fact object itself | “WF1-1” |
| from | Originator of the message | “Orchestrator” |
| factMessage | The fact itself | “DisplayImage, 80801, PiB” |
| type | The object type of the fact | “Softwarecomponent” |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Bröring, A.; Seeger, J.; Papoutsakis, M.; Fysarakis, K.; Caracalli, A. Networking-Aware IoT Application Development. Sensors 2020, 20, 897. https://doi.org/10.3390/s20030897
Bröring A, Seeger J, Papoutsakis M, Fysarakis K, Caracalli A. Networking-Aware IoT Application Development. Sensors. 2020; 20(3):897. https://doi.org/10.3390/s20030897
Chicago/Turabian StyleBröring, Arne, Jan Seeger, Manos Papoutsakis, Konstantinos Fysarakis, and Ahmad Caracalli. 2020. "Networking-Aware IoT Application Development" Sensors 20, no. 3: 897. https://doi.org/10.3390/s20030897
APA StyleBröring, A., Seeger, J., Papoutsakis, M., Fysarakis, K., & Caracalli, A. (2020). Networking-Aware IoT Application Development. Sensors, 20(3), 897. https://doi.org/10.3390/s20030897







