3VSR: Three Valued Secure Routing for Vehicular Ad Hoc Networks using Sensing Logic in Adversarial Environment
Abstract
:1. Introduction
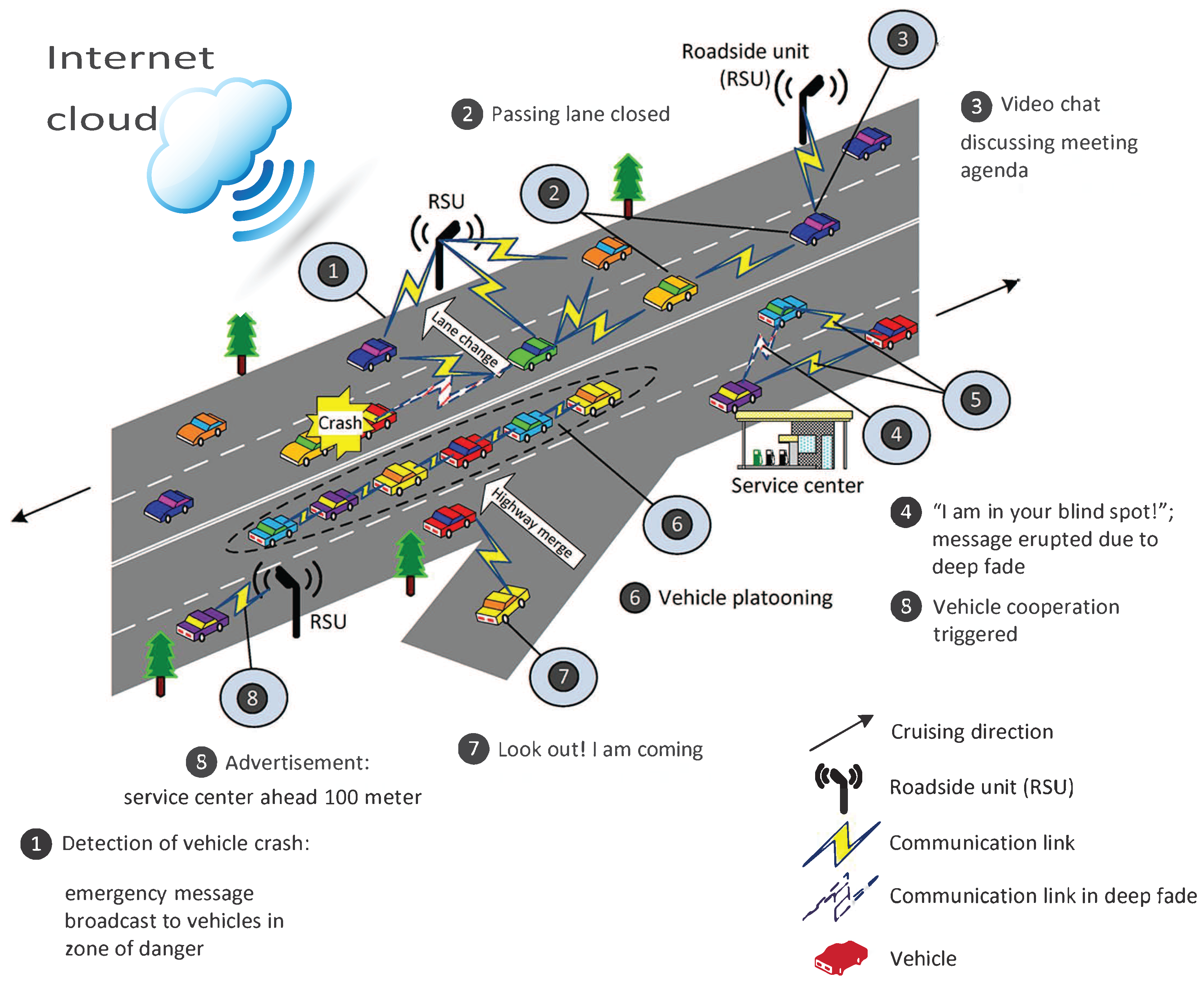
- First, we take advantage of the unique features of VANET [19,20], e.g., high dynamics, hybrid architecture, and vehicle-to-infrastructure (V-2-I) and vehicle-to-vehicle (V-2-V) communications, to propose our 3VSR scheme. Specifically, the high dynamics ensure the real-time update of feedback. The hybrid architecture, i.e., vehicles, roadside units (RSUs), server, and trust authority (TA), enables the storage of feedback and the computation of trust scores.
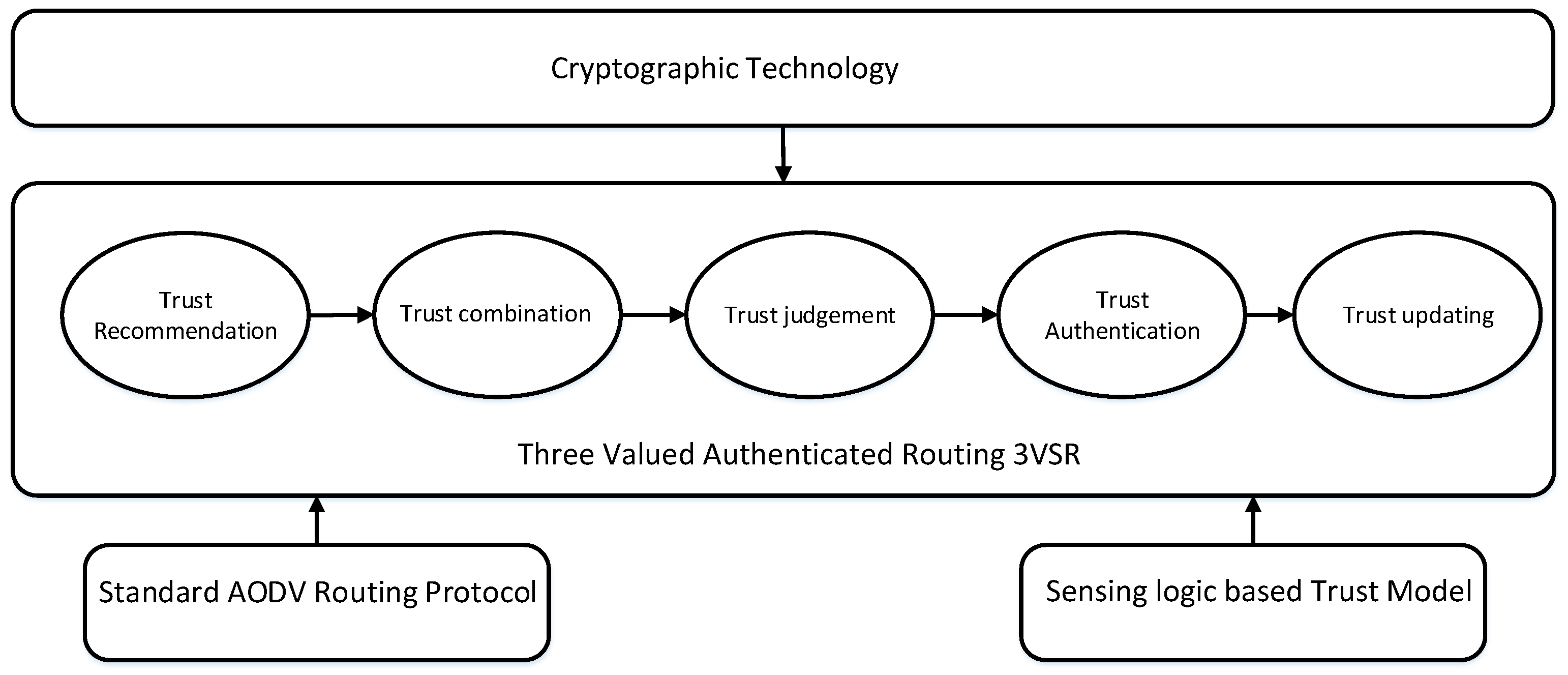
- A secure routing is proposed using sensing logic as trust model to enhance security of VANET, as efficient multi-hop trust assessment technique. This trust model is capable of assessing trust between multi path, arbitrary and bridge topologies.
- In our 3VSR, nodes perform trusted routing behavior mainly according to the trust relationship between them, a node that will behave malicious eventually denied from the network. Also, system performance is improved by means of 3VSR as anonymous routing, that avoid verifying and requesting certificate exchange at each step. This also helps in minimizing computation and routing overhead.
- In this article, we have proposed sensing logic-based trust model, that despite highlighting posterior uncertainty during trust propagation also capable of correctly assess arbitrary topologies.
2. Problem Statement
2.1. System Model
2.2. Adversary Model
- Simple Attack (SA) An attacker may manipulate the compromised nodes not to follow normal network protocols and not to provide necessary services for other nodes, such as forwarding data packets or propagating route discovery requests. However, the compromised node will not provide any fake trust opinions when it is asked about other node’s trustworthiness.
- Black Hole Attack (BH) In this case malicious node doesn’t forward data packet, still remains active as using path initiated by other nodes to save its energy. In these attacks packets can be forged, altered and tend to behave as good nodes. Black Hole attacks are known as the basic byzantine attacks.
- Zigzag Attack (ZA): Sometimes sly attackers can alter their malicious behavior patterns so that it is even harder for the trust management scheme to detect them. For instance, they can conduct malicious behaviors for some time and then stop for a while (in that case the malicious behaviors are conducted in an on-and-off manner). In addition, the sly attackers can also exhibit different behaviors to different audiences, which can lead to inconsistent trust opinions to the same node among different audiences. Due to the insufficient evidence to accuse the adversary, it is generally more difficult to identify such sly attackers.
2.3. Design Goals
- Overhead: To reduce computational and routing overhead by using secure routing protocol and having limited number of RSUs.
- Resilience: How to tackle against adversary attack Modification attacks, Forgery attacks and Black Hole attacks during V-2-V authentication.
- Efficiency: The trust management scheme should be efficient in processing and having less time for convergence.
- Scalability and consistency: The proposed scheme should work fine even with high density of vehicles.
3. Preliminaries
3.1. Beta Distribution
3.2. Dirichlet Distribution
3.3. Subjective Logic
3.4. Sensing Logic Fundamental
3.5. Ad Hoc Routing Protocols
Ad-Hoc on Demand Distance Vector Routing (AODV)
4. Overview of Trusted AODV
4.1. Trusted Assumptions
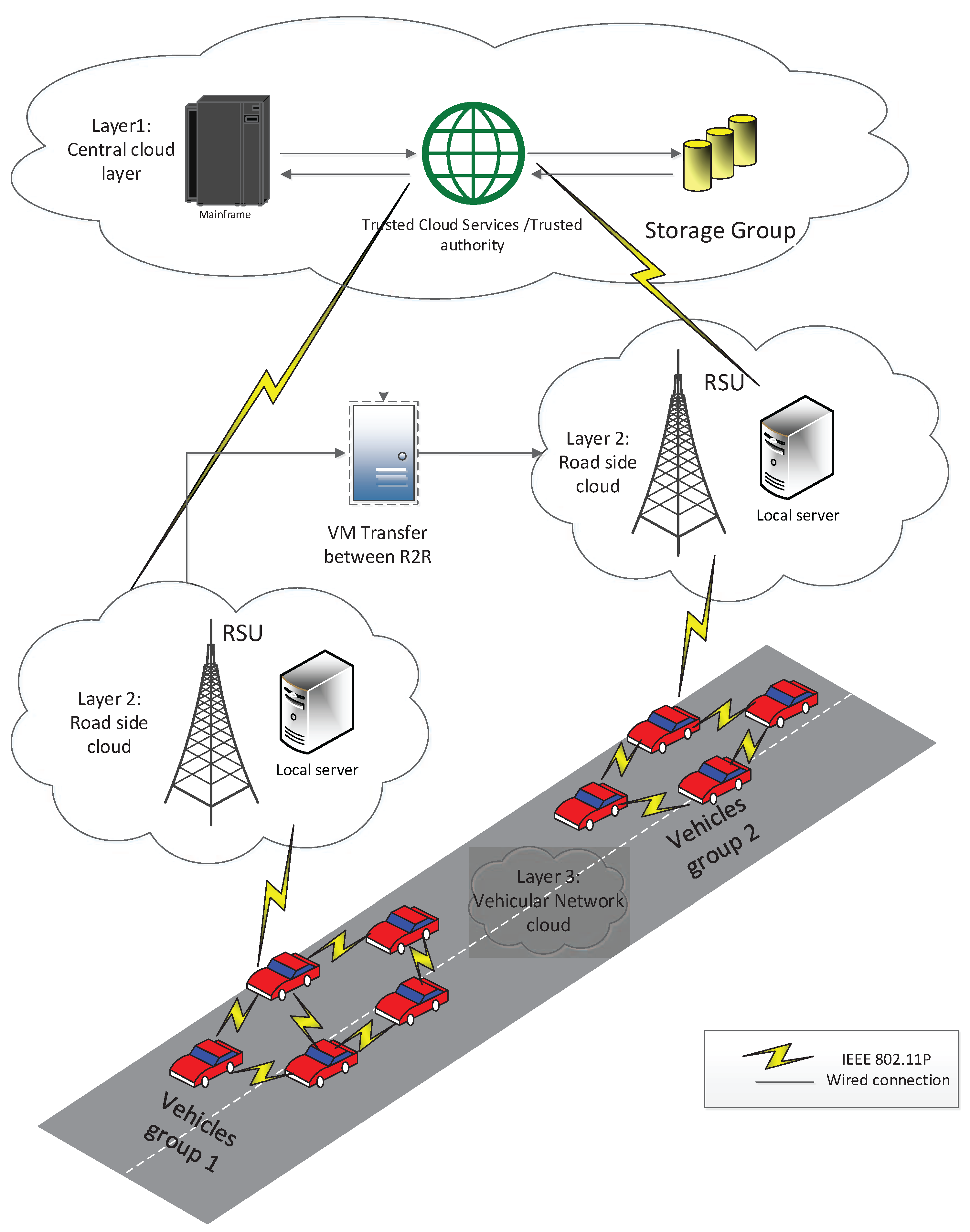
- Server: The server in central cloud layer is capable of having high storage capacity regarding brief history and profile also with vehicle Id and digital certificate that is distributed soon after entering the coverage area via RSU. Further, it is proposed that central server is under strong physical protection and not affected by adversaries.
- Remote Site Unit RSU: Here, we proposed that RSUs act as local trust manager for vehicles on road, but have limited storage capabilities as compared with server in CCL. Here RSU is used to manage the vehicle information e.g., IP address, public or private key etc for short time and update server after one complete trip via V-2-R communication.
- Vehicle: A vehicle can access all its neighbor vehicles and broadcast initial information about itself using V-2-V communication. A user vehicle after interacting provide their feedback about other vehicle. When a new vehicle join the group, the uncertainty towards it is normally high, so its trust value is evaluated after observing its behavior also taking advise from neighbor vehicles. At start, the new incoming vehicle also prove its credibility via exchange of digital certificate, which helps other vehicles to reduce uncertain opinion about it. Once the trust relationship establish vehicles can use our secure routing protocol to reduce extra communication overhead.
4.2. Framework for 3VSR
5. Trust Model
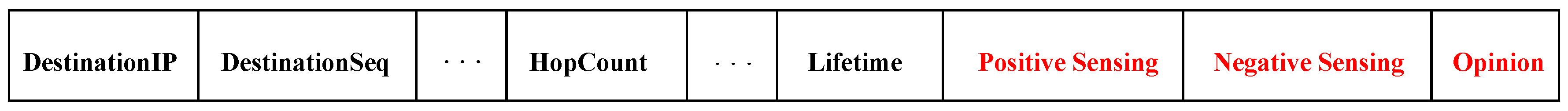
6. Trusted Routing Operation in AODV
6.1. Node Model
6.2. Trust Judging Rules
- If node A want to communicate with node B and if belief of A in B is ≥0.5, then A will trust B and start to route packet to node B.
- If disbelief opinion of A in node B i.e., >0.5, then A will not trust node B and will not route packets unless to verify it by certification or destroy it.
- If uncertainty of node A in node B is >0.5, then A will ask for digital signature for node B and waits for the verifying. If A successfully verifies B’s signature then A will start communication with B and reverse is also true.
6.3. Trust Updating Rule
- If node A had successful communication with node B then its update the trust value by incrementing trust in that node. By successful communication we mean normal packet forward or RREP with in the time interval.
- If node A had failed communication with node B then it degrades trust values by decrementing the update counter.
- Every time field of successful or failed event is changed, opinion space values are recalculated using Equation (5).
- If node B’s routing entry is deleted from node A routing table due to expiry, then new opinion will set as .
6.4. Trusted Information Exchange
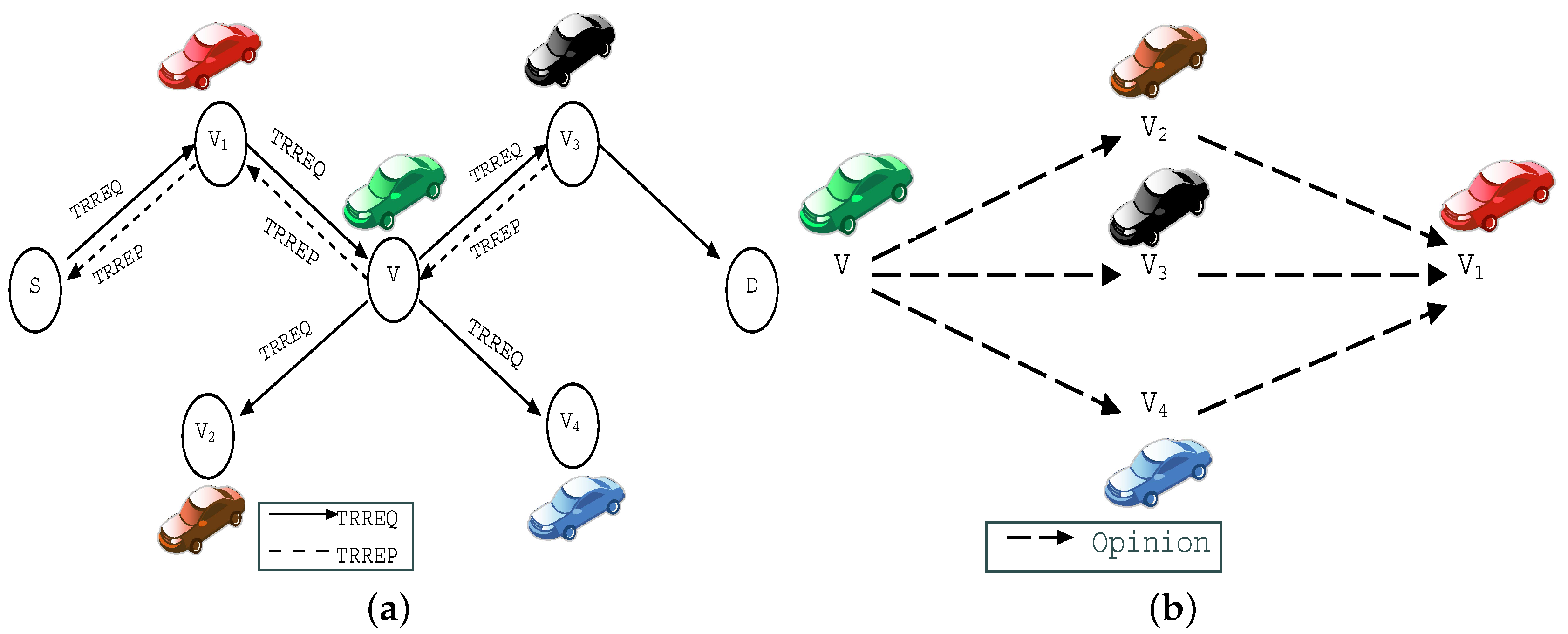
6.5. Trusted Routing Discovery
| Algorithm 1 Trusted Routing Discovery. |
| Receive an or an from V1; |
| /*Verify the trustworthiness of */ |
| Broadcast to request the opinions from neighbors to ; |
| Receive opinions from neighbors: |
| Combine these opinions together and get a latest: |
| Exchange opinions about with its neighbors . |
| /* and Judge the next step using conditions set in Table 1 */ |
| if |
| trust and forward RREQ/RREP |
| elseif |
| distrust for expiry time |
| elseif request and verify digital certificate |
| else |
| /* the confidence about trustworthiness is decreased*/ |
| request and verify certificates, by default |
| endif |
6.6. Initiation of a Secure VANET
- (1)
- broadcast RREQ requesting route path to node and waits for RREP in time t from V.
- (2)
- V receive RREQ packet after that node V will check route to by checking opinion and . As it is network initial stage so uncertainty will be high and currently no route to .
- Node V authenticates both the neighbors to verify certificate if passes, the successful event is increased by 1 and the new opinion is made. V also authenticates and revises the same process. If node fails the authentication, then new opinion will be . V will not forward the packet till the expiry time.
- If has also been authorized and V’s route table will be updated and V will re-broadcast the RREQ to after passed the authentication, V will forward the RREQ. If fails authentication process then opinion will be re-calculated accordingly.
- (3)
- Node will also check and node V’s trustworthiness if V passes authentication, will generate an RREP packet to V and update its route table. If not, will drop the RREQ packet.
6.7. Trusted Route Maintenance
7. Experimental Setup
Evaluation Metrics
- Packet Delivery Ratio (PDR): The ratio of the total number of data packets successfully delivered to the total number of data packets sent out by a source node.
- Packet Loss Ratio: It occurs when certain data packets traveling across a network fail to reach their destination. Packet loss is typically caused by network congestion. Packet loss is measured as a percentage of packets lost with respect to packets sent.
- Throughput: This value is calculated by dividing the overall number of messages received at destination node by the total messages sent from source nodes according to the following equation:
- Delay: It is very important factor to measure the efficiency of any communication system. Delay represents the time period that needs to route a packet from the source to the desired destination which depends on PDR value in the system and can be calculated using the following equation
- Probability of Detection: It is the ratio between number of malicious nodes to the actual nodes present in the network. The malicious nodes are unable to make trust score up to threshold level, therefore 3VSR has high probability to detect these nodes.
8. Results and Discussions
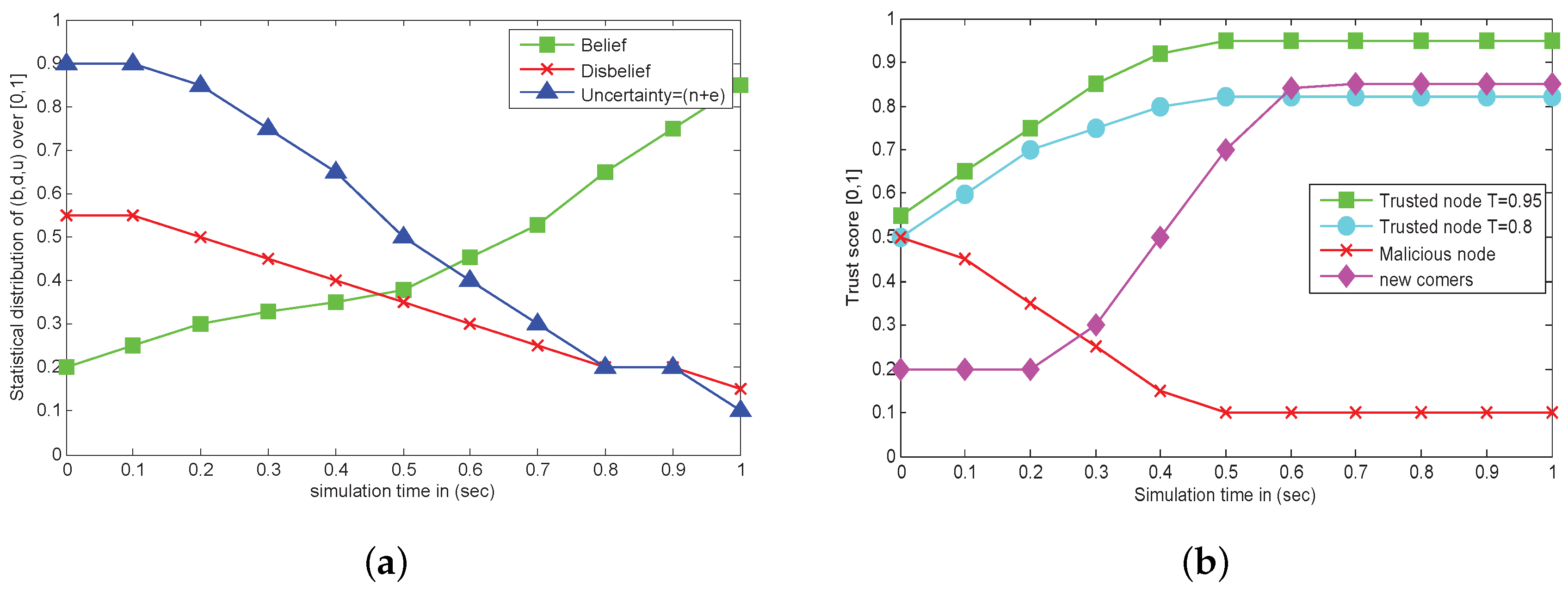
- Test 1: Uncertainty analysis from initial stage to secure VANET.
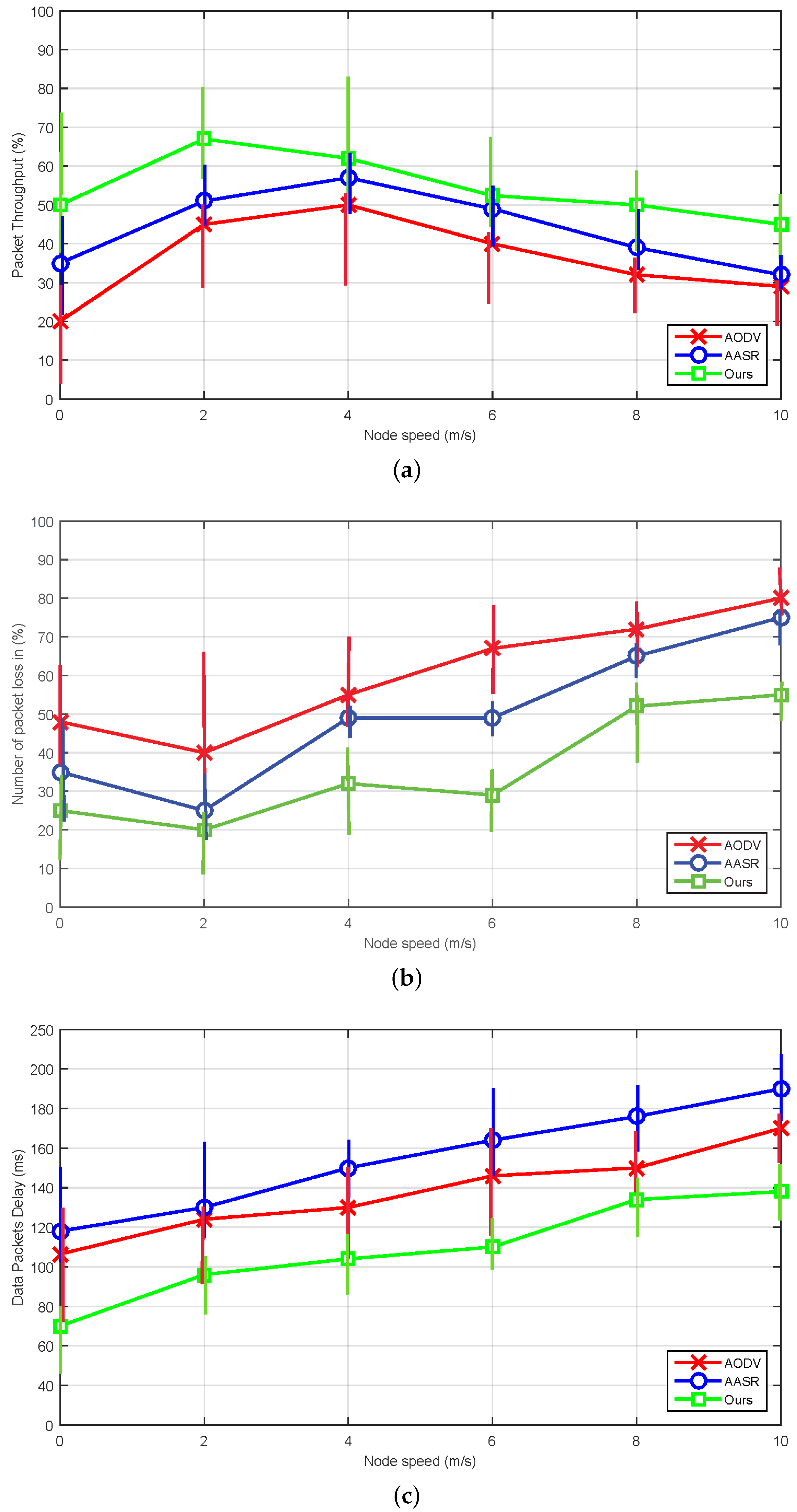
- Test 2: Comparison between standard, AASR and our proposed AODV routing over different metric.
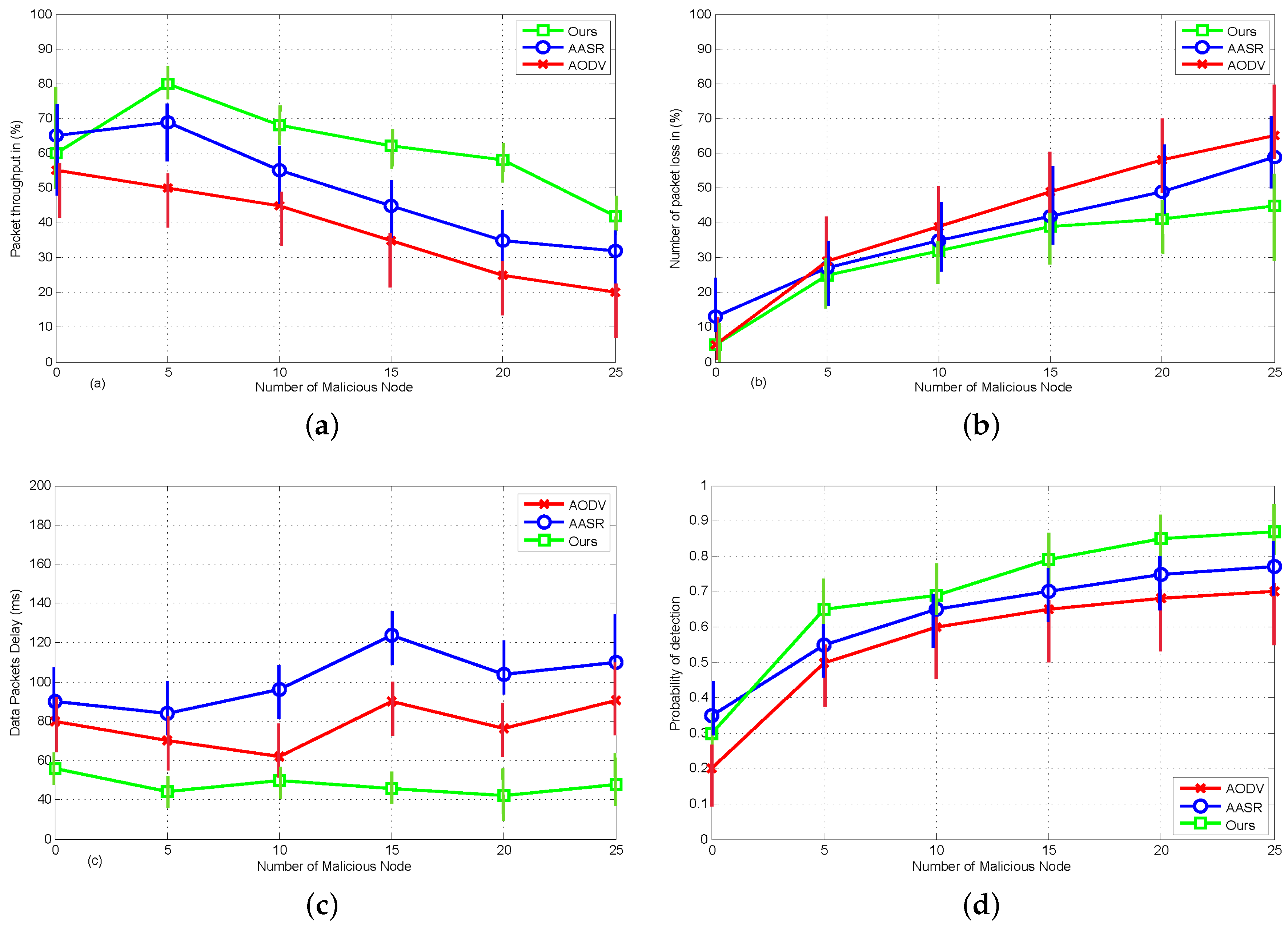
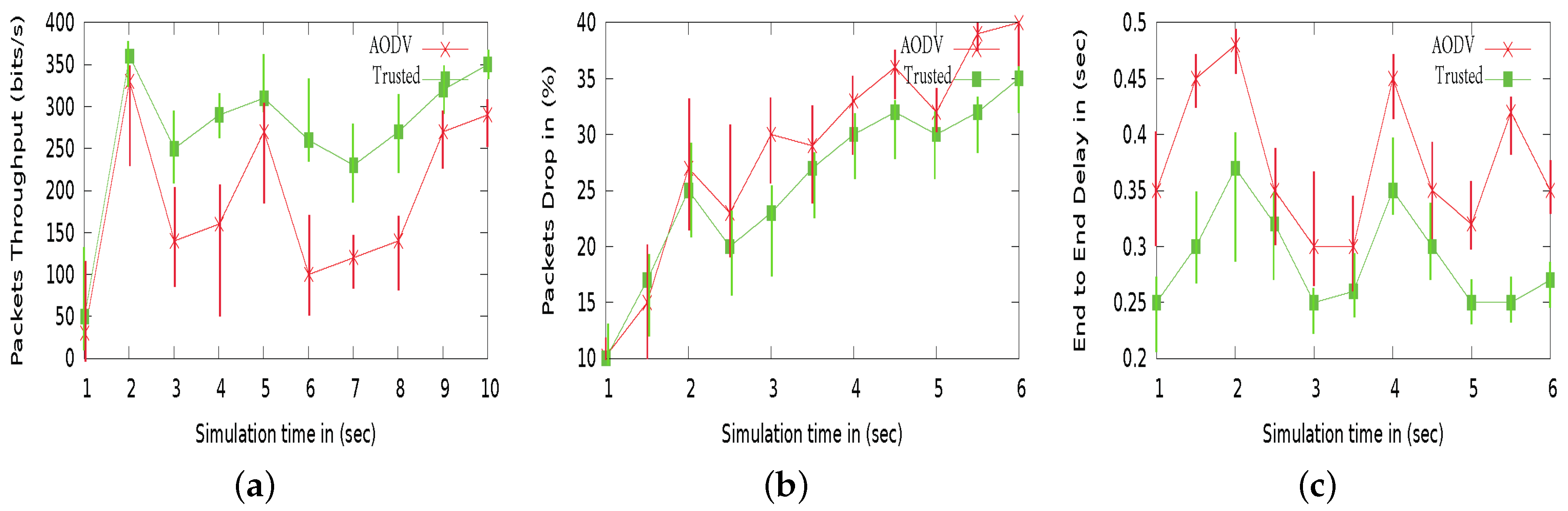
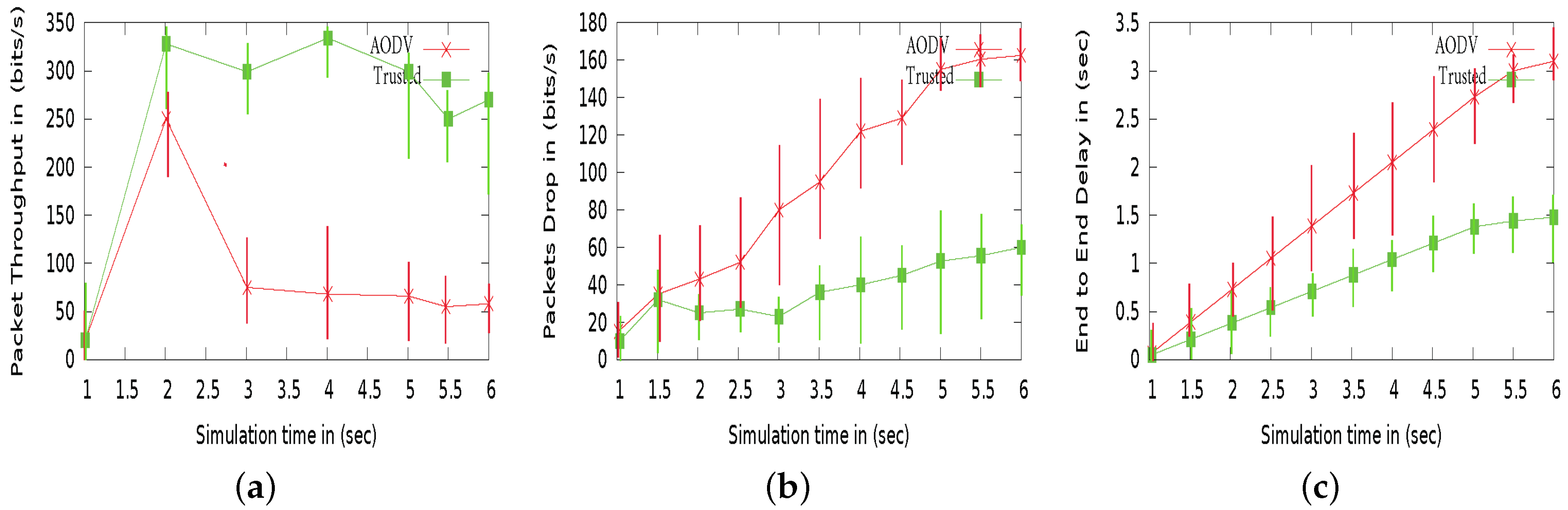
- Test 3: Comparison between Trusted vs standard AODV over different attack pattern.
8.1. Uncertainty Analysis from Initial Stage to Stable VANET
8.2. Performance Comparison between Standard, AASR and Our Proposed 3VSR under Different Mobility and Attack Pattern
8.2.1. The Effect of Mobility Scenario
8.2.2. The Effect of Malicious Attacks
8.3. Performance Comparison between 3VSR vs. Standard AODV under Black Hole and Zigzag Attacks
9. Related Work
9.1. Misbehavior Detection for Ad hoc Networks
9.2. Trust Establishment and Management in Ad Hoc Networks
10. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
Abbreviations
| VANET | Vehicular Ad-Hoc Network |
| 3VSR | Three Valued Secure Routing |
| AODV | Ad-Hoc On-Demand Distance Vector Routing |
| ITS | Intelligent Transportation System |
| RSU | Remote Side Unit |
| OBU | Onboard Unit |
| V-2-V | Vehicle to Vehicle communication |
| V-2-R | Vehicular to RSU |
| V-2-I | Vehicle to Infrastructure |
| CCL | Central Cloud Layer |
| RCL | Remote Cloud Layer |
| VCL | Vehicle Cloud Layer |
References
- Yan, Z.; Zhang, P.; Vasilakos, A.V. A survey on trust management for Internet of things. J. Netw. Comput. Appl. 2014, 42, 120–134. [Google Scholar] [CrossRef]
- Chen, X.; Wang, L. A cloud-based trust management framework for vehicular social networks. IEEE ACCS 2017, 5, 2967–2980. [Google Scholar] [CrossRef]
- Nogueira, M.; Silva, H.; Santos, A.; Pujolle, G. A security management architecture for supporting routing services on Wanets. IEEE. Trans. Netw. Serv. Manag. 2012, 9, 156–168. [Google Scholar] [CrossRef]
- Guo, B.; Yu, Z.; Zhou, X.; Zhang, D. From participatory sensing to mobile crowd sensing. In Proceedings of the IEEE International Conference on Pervasive Computing and Communication Workshops (PerCom 2014 Workshops), Budapest, Hungary, 24–28 March 2014; pp. 593–598. [Google Scholar]
- Huang, K.L.; Kanhere, S.S.; Hu, W. Are you contributing trustworthy data: The case for a reputation system in participatory sensing. In Proceedings of the 13th International Symposium on Modeling Analysis and Simulation of Wireless and Mobile Systems (MSWiM 2010), Bodrum, Turkey, 17–21 October 2010; pp. 14–22. [Google Scholar]
- Karagiannis, G.; Altintas, O.; Ekici, E.; Heijenk, G.; Jarupan, B.; Lin, K.; Weil, T. Vehicular Networking: A Survey and Tutorial on Requirements, Architectures, Challenges, Standards and Solutions. IEEE Commun. Surv. Tutor. 2011, 13, 584–616. [Google Scholar] [CrossRef]
- Wang, X.O.; Cheng, W.; Mohapatra, P.; Abdelzaher, T.F. Artsense: Anonymous reputation and trust in participatory sensing. In Proceedings of the IEEE INFOCOM 2013, Turin, Italy, 14–19 April 2013; pp. 2517–2525. [Google Scholar]
- Jiang, S.; Zhu, X.; Wang, L. An efficient anonymous batch authentication scheme based on hmac for vanets. IEEE Trans. Intell. Transp. Syst. 2016, 17, 2193–2204. [Google Scholar] [CrossRef]
- Zhu, X.; Jiang, S.; Wang, L.; Li, H. Efficient privacy-preserving authentication for vehicular ad hoc networks. IEEE Trans. Veh. Technol. 2014, 63, 907–919. [Google Scholar] [CrossRef]
- Jiejun, K.; Xiaoyan, H. Anodr: Anonymous on demand routing with untraceable routes for mobile ad-hoc networks. In Proceedings of the 4th ACM International Symposium on Mobile Ad hoc Networking and Computing (Mobi-Hoc’03), Annapolis, MD, USA, 1–3 June 2003; pp. 291–302. [Google Scholar]
- Liu, W.; Yu, M. Aasr: Authenticated anonymous secure routing for manets in adversarial environments. IEEE Trans. Veh. Technol. 2014, 63, 4585–4593. [Google Scholar] [CrossRef]
- Xia, H.; Jia, Z.; Sha, E.H. Research of trust model based on fuzzy theory in mobile ad hoc networks. IET Inf. Secur. 2014, 8, 88–103. [Google Scholar] [CrossRef]
- Cho, J.H.; Swami, A.; Chen, I.R. A survey on trust management for mobile ad hoc networks. IEEE Commun. Surv. Tutor. 2011, 13, 562–583. [Google Scholar] [CrossRef]
- Govindan, K.; Mohapatra, P. Trust computations and trust dynamics in mobile adhoc networks: A survey. IEEE Commun. Surv. Tutor. 2012, 14, 279–298. [Google Scholar] [CrossRef]
- Josang, A. A logic for uncertain probabilities. Int. J. Uncertain. Fuzziness Knowl. Syst. 2001, 9, 279–311. [Google Scholar] [CrossRef]
- Josang, A.; Bhuiyan, T. Optimal trust network analysis with subjective logic. In Proceedings of the Second International Conference on Emerging Security Information, Systems and Technologies, Washington, DC, USA, 25–31 August 2008; pp. 179–184. [Google Scholar]
- Liu, G.; Yang, Q.; Wang, H.; Lin, X.; Wittie, M.P. Assessment of multi-hop interpersonal trust in social networks by three-valued subjective logic. In Proceedings of the IEEE INFOCOM 2014—IEEE Conference on Computer Communications, Toronto, ON, Canada, April 27–May 2 2014; pp. 1698–1706. [Google Scholar]
- Liu, G.; Chen, Q.; Yang, Q.; Wang, H.; Zhu, B.; Wang, W. Opinionwalk: An efficient solution to massive trust assessment in online social networks. In Proceedings of the IEEE INFOCOM 2017—IEEE Conference on Computer Communications, Atlanta, GA, USA, 1–4 May 2017; pp. 1–9. [Google Scholar]
- Hao, H.; Lu, R.; Cheng, H.; Zhang, Z. Tripsense: A trust-based vehicular platoon crowdsensing scheme with privacy preservation in vanets. Sensors 2016, 16, E803. [Google Scholar] [CrossRef]
- Hu, H.; Lu, R.; Zhang, Z.; Shao, J. Replace: A reliable trust-based platoon service recommendation scheme in vanet. IEEE Trans. Veh. Technol. 2017, 66, 1786–1797. [Google Scholar] [CrossRef]
- Fung, C.J.; Zhang, J.; Aib, I.; Boutaba, R. Dirichlet-based trust management for effective collaborative intrusion detection networks. IEEE Trans. Netw. Serv. Manag. 2011, 8, 79–91. [Google Scholar] [CrossRef]
- Hafez, A.; Xu, Y. Exploiting the Beta Distribution-Based Reputation Model in Recommender System. In Proceedings of the Australasian Joint Conference on Artificial Intelligence, Canberra, ACT, Australia, 30 November–December 4 2015; Springer: Cham, Switzerland, 2015; pp. 1–13. [Google Scholar]
- Omid, A.; Mahmood, F.; Jamshid, T. Enhancing AODV routing protocol using mobility parameters in VANET. In Proceedings of the IEEE International Conference on Computer Systems and Applications, Doha, Qatar, 31 March–4 April 2008; pp. 229–235. [Google Scholar]
- Zhang, C.; Zhu, X.; Song, Y.; Fang, Y. A formal study of trust-based routing in wireless ad hoc networks. In Proceedings of the IEEE INFOCOM, San Diego, CA, USA, 15–19 March 2010; pp. 1–9. [Google Scholar]
- Perkins, C.E.; Royer, E.M. Ad-Hoc on-demand distance vector routing. In Proceedings of the IEEE Workshop on Mobile Computing Systems and Applications WMCSA ’99, New Orleans, LA, USA, 25–26 Feburay 1999; pp. 90–100. [Google Scholar]
- Panos, C.; Xenakis, C.; Kotzias, P.; Stavrakakis, I. A specification-based intrusion detection engine for infrastructure-less networks. J. Comput. Commun. 2014, 54, 67–83. [Google Scholar] [CrossRef]
- Xia, H.; Jia, Z.; Li, X.; Ju, L.; Sha, E.H. Trust prediction and trust-based source routing in mobile ad hoc networks. Ad Hoc Netw. 2013, 11, 2096–2114. [Google Scholar] [CrossRef]
- Ns: The Network Simulator. Available online: https://www.isi.edu/nsnam/ns/ (accessed on 22 December 2018).
- Issariyakul, T.; Hossain, E. Introduction to Network Simulator 2 (NS2); Springer: Boston, MA, USA, 2012; pp. 21–40. ISBN 978-1-4614-1406-3. [Google Scholar]
- Libert, B.; Peters, T.; Yung, M. Short Group Signatures via Structure-Preserving Signatures: Standard Model Security from Simple Assumptions. In Cryptology Conference; Springer: Berlin, Heidelberg, 2015; pp. 296–316. [Google Scholar]
- Defrawy, K.E.; Tsudik, G. ALARM: Anonymous location-aided routing in suspicious MANETs. IEEE Trans. Mob. Comput. 2011, 10, 1345–1358. [Google Scholar] [CrossRef]
- Zhang, L.; Tan, C.P.; Li, S.; Fang, H.; Rai, R.; Chen, Y.; Luthra, R.; Ng, W.K.; Zhang, J. The Influence of Interaction Attributes on Trust in Virtual Communities. In Proceedings of the International Conference on User Modeling, Adaptation, and Personalization, Girona, Spain, 11–15 July 2011; pp. 268–279. [Google Scholar]
- Wu, D.; Zhang, G.; Lu, J. A Fuzzy Preference Tree-Based Recommender System for Personalized Business-to-Business E-Services. IEEE Trans. Fuzzy Syst. 2014, 23, 29–43. [Google Scholar] [CrossRef]
- He, Q.; Wu, D.; Khosla, P. SORI: A secure and objective reputation based incentive scheme for ad-hoc networks. In Proceedings of the IEEE WCNC, Atlanta, Georgia, USA, 21–25 March 2004; pp. 825–830. [Google Scholar]
- Buchegger, S.; Le Boudec, J.Y. Performance analysis of the confidant protocol. In Proceedings of the IEEE 3rd ACM International Symposium on Mobile Ad Hoc Networking and Computing, Lausanne, Switzerland, 9–11 June 2002; pp. 226–236. [Google Scholar]
- Michiardi, P.; Molva, R. CORE: A collaborative reputation mechanism to enforce node cooperation in mobile ad hoc networks. In Proceedings of the IEEE 6th Joint Working Conference on Communications and Multimedia Security, Portoroz, Slovenia, 26–27 September 2002; pp. 107–121. [Google Scholar]
- Patwardhan, A.; Joshi, A.; Finin, T.; Yesha, Y. A data intensive reputation management scheme for vehicular ad hoc networks. In Proceedings of the IEEE 3rd International Conference on Mobile and Ubiquitous Systems, San Jose, CA, USA, 17–21 July 2006; pp. 1–8. [Google Scholar]
- Eldin, B.; Ayman, M. TARA: Trusted Ant Colony Multi Agent Based Routing Algorithm for Mobile Ad-Hoc Networks. In Bio-inspiring Cyber Security and Cloud Services: Trends and Innovations; Springer: Berlin/Heidelberg, Germany, 2014; pp. 38–72. [Google Scholar]
- Xia, H.; Yu, J.; Pan, Z.K.; Cheng, X.G.; Sha, E.H. Applying trust enhancements to reactive routing protocols in mobile ad hoc networks. Wirel. Netw. 2016, 22, 2239–2257. [Google Scholar] [CrossRef]
- Balakrishnan, V.; Varadharajan, V.; Tupakula, U. Subjective logic based trust model for mobile ad hoc networks. In Proceedings of the 4th International Conference on Security and Privacy in Communication Netowrks (SecureComm ’08), Istanbul, Turkey, 22–25 September 2008; pp. 30:1–30:11. [Google Scholar]
- Ren, Y.; Zadorozhny, V.I.; Oleshchuk, V.A.; Li, F.Y. A novel approach to trust management in unattended wireless sensor networks. IEEE Trans. Mob. Comput. 2014, 13, 1409–1423. [Google Scholar] [CrossRef]
- Li, X.; Lyu, M.R.; Liu, J. A trust model based routing protocol for secure ad hoc networks. In Proceedings of the IEEE Aerospace Conference, Big Sky, MT, USA, 6–13 March 2004; pp. 1286–1295. [Google Scholar]
- Tan, S.; Li, X.; Dong, Q. A trust management system for securing data plane of ad-hoc networks. IEEE. Trans. Veh. Technol. 2016, 65, 7579–7592. [Google Scholar] [CrossRef]

| Action | |||
|---|---|---|---|
| ⩾0.5 | Request to verify digital signature. | ||
| >0.5 | Distrust node till next request. | ||
| >0.5 | Trust a node and share resources. | ||
| ≤0.5 | ≤0.5 | ≤0.5 | Request and verify authentication. |
| Examined Protocol | 3VSR |
|---|---|
| Simulation time | 100 (s) |
| Trust model | Sensing logic |
| Simulation area | 1000 × 1000 (m) |
| Number of nodes | 50 |
| Transmission range | 250 (m) |
| Propagation model | Two way ground reflection |
| Maximum speed | 0–10 m/s |
| Physical link bandwidth | 11 Mb |
| traffic type | CBR |
| Payload size | 512 bytes |
| Packet rate | 4 pkt/s |
| Routing Attacks | Black and Modification |
| Number of malicious nodes | 0–25 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Sohail, M.; Wang, L. 3VSR: Three Valued Secure Routing for Vehicular Ad Hoc Networks using Sensing Logic in Adversarial Environment. Sensors 2018, 18, 856. https://doi.org/10.3390/s18030856
Sohail M, Wang L. 3VSR: Three Valued Secure Routing for Vehicular Ad Hoc Networks using Sensing Logic in Adversarial Environment. Sensors. 2018; 18(3):856. https://doi.org/10.3390/s18030856
Chicago/Turabian StyleSohail, Muhammad, and Liangmin Wang. 2018. "3VSR: Three Valued Secure Routing for Vehicular Ad Hoc Networks using Sensing Logic in Adversarial Environment" Sensors 18, no. 3: 856. https://doi.org/10.3390/s18030856
APA StyleSohail, M., & Wang, L. (2018). 3VSR: Three Valued Secure Routing for Vehicular Ad Hoc Networks using Sensing Logic in Adversarial Environment. Sensors, 18(3), 856. https://doi.org/10.3390/s18030856






