IoT-Forensics Meets Privacy: Towards Cooperative Digital Investigations
Abstract
:1. Introduction
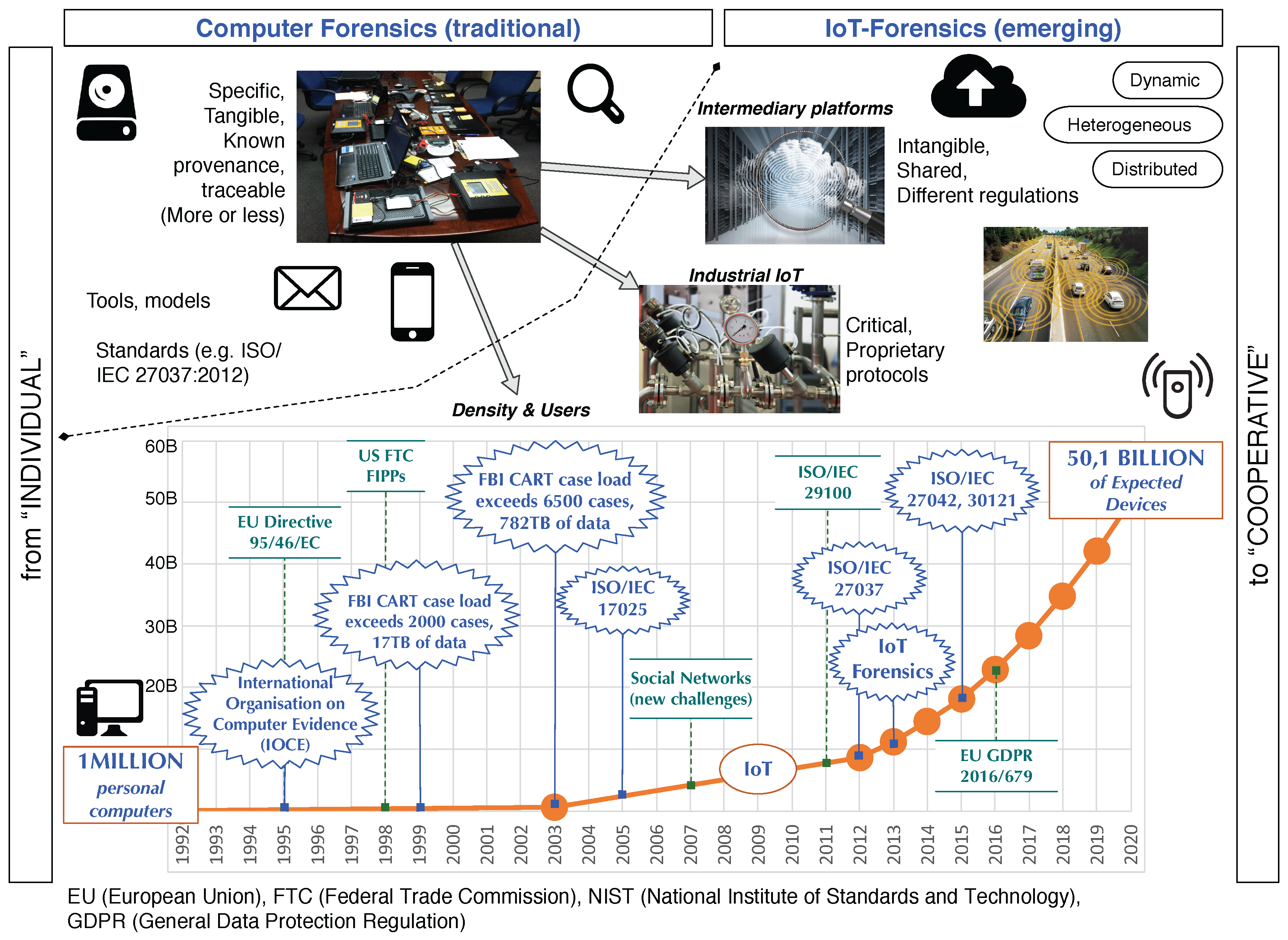
- Increasingly greater numbers of devices (see Figure 1)
- Greater heterogeneity of devices that call for specialized information-retrieval tools
- Widespread implementation of proprietary protocols
- Massive amount and diversity of collected data, complicating the identification of relevant data
- Need for new formats to store digital evidence in IoT devices
- Existence of numerous resource-constrained devices
- Ubiquitous deployment of context-aware devices
2. Background
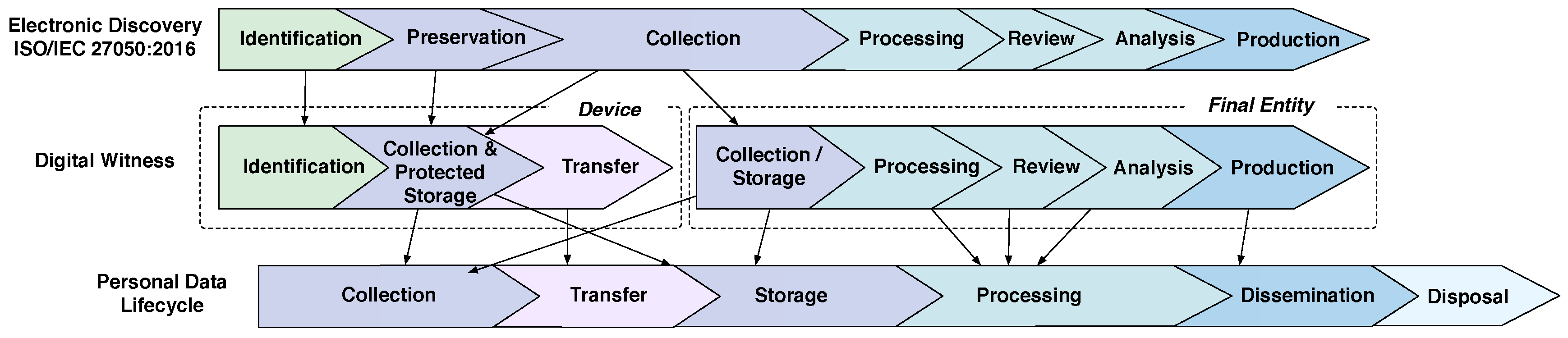
2.1. Digital Witness
- Anti-tampering behavior: a digital witness must integrate some form of Trusted Computing Hardware (e.g., Secure Element, TPM) to provide anti-tampering capabilities to the device. Embedding such hardware inside the device enables not only detecting whether digital evidence has been compromised but also performing periodic integrity checks of the device. If the device is found to have been corrupted it will not be allowed to participate in a DCoC-IoT.
- Binding credentials: a digital witness must be unequivocally bound to the identity of its owner or the entity who is responsible for the device. The ultimate goal of electronically binding digital evidence to a device, which in turn operates on behalf of its owner, is to dissuade people from misusing digital witnesses to report fake evidence, and helps to implement the traceability of the digital evidence during the process of the binding delegation.
- Binding delegation: a digital witness must be allowed to transmit digital evidence to other authorised digital witnesses to enable the deployment of the DCoC-IoT. The way in which the DCoC-IoT is deployed depends on the roles and capabilities of the devices. Some devices may play the role of digital witness but others can also play the role of digital custodian. Digital custodians are owned by agents of the law and are thus usually preferable when deploying the DCoC-IoT.
- Well-defined procedures: a digital witness must behave according to a set of well-defined procedures and standards for compliance with the digital evidence management process. This includes a number of established phases and robust cryptographic mechanisms that guarantees the integrity both of the evidence and the DCoC-IoT.
- The digital witness approach allows other devices in the environment - and not just the OCP and authorised digital witness—to obtain information about users who were not even directly related to the offence. This is because the digital witness collects information from the surroundings of the digital device without asking for third-party consent beforehand.
- The data collected by a digital witness could be used to infer sensitive information which is not relevant to the investigation.
2.2. The PRoFIT Model
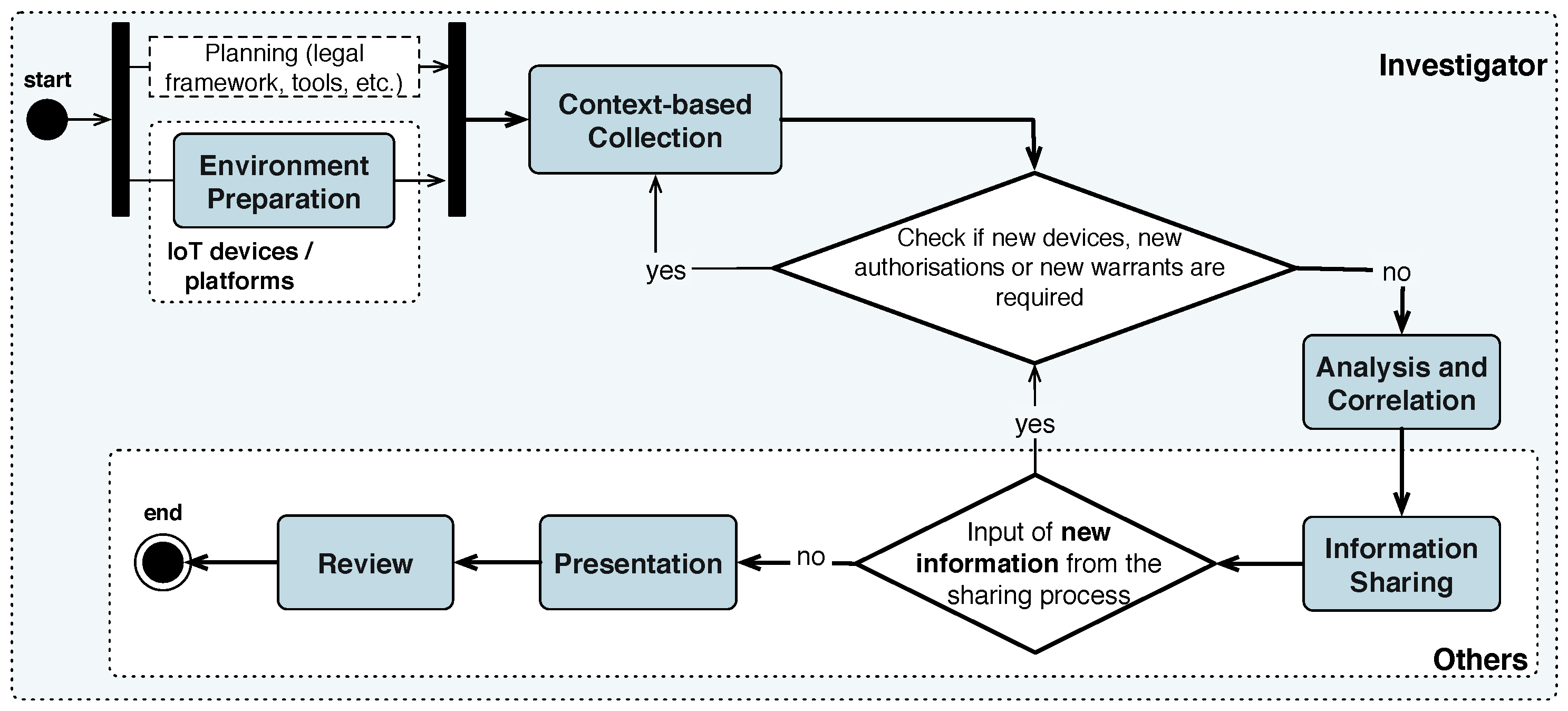
2.2.1. Methodology
- Citizens: the first phase gives citizens the opportunity to prepare their own personal devices. The preparation of devices consists of installing the PRoFIT software to assist citizens in future privacy- and forensics-related decisions. This phase is accomplished before the start of the investigation. Note that citizens are not forced to perform these actions but are encouraged to do so since the installation of this software will aid them in subsequent phases of the investigation.
- Investigator: the involvement of the investigator spans the first three phases of the methodology. In the first phase, the investigator performs all actions necessary for the preparation of a case, namely, the analysis of the legal framework, configuration of data forensic tools, etc. The second phase is devoted to the collection of data from the IoT devices either from citizens willing to collaborate or, in the worst case, obtained through a warrant. In the third phase, the investigator analyses and correlates the data obtained from the previous phase.
- Other actors: the results of the analysis performed in the previous phases are prepared to be presented to non-technical stakeholders involved in the digital investigation (e.g., a client) who requested the investigation, a court of law, etc.). Moreover, this includes the processes related to the release of the digital evidence and the return of artefacts to their corresponding owners.
2.2.2. Privacy Principles
3. PRoFIT-Compliant Digital Witness
3.1. Mitigation of Privacy Risks
- M1.
- Direct Anonymous Attestation. Allows a verifier to check whether a platform uses a certified hardware security module without revealing the identity of the platform’s user.
- M2.
- Blind signatures plus signature chaining. These mechanisms can be used to certify that a given piece of evidence existed at time T without revealing its actual contents to the signer.
- M3.
- Homomorphic encryption or secure computation. The witnesses can collaboratively share and operate on the statements of other participants without learning the contributions of each other.
- M4.
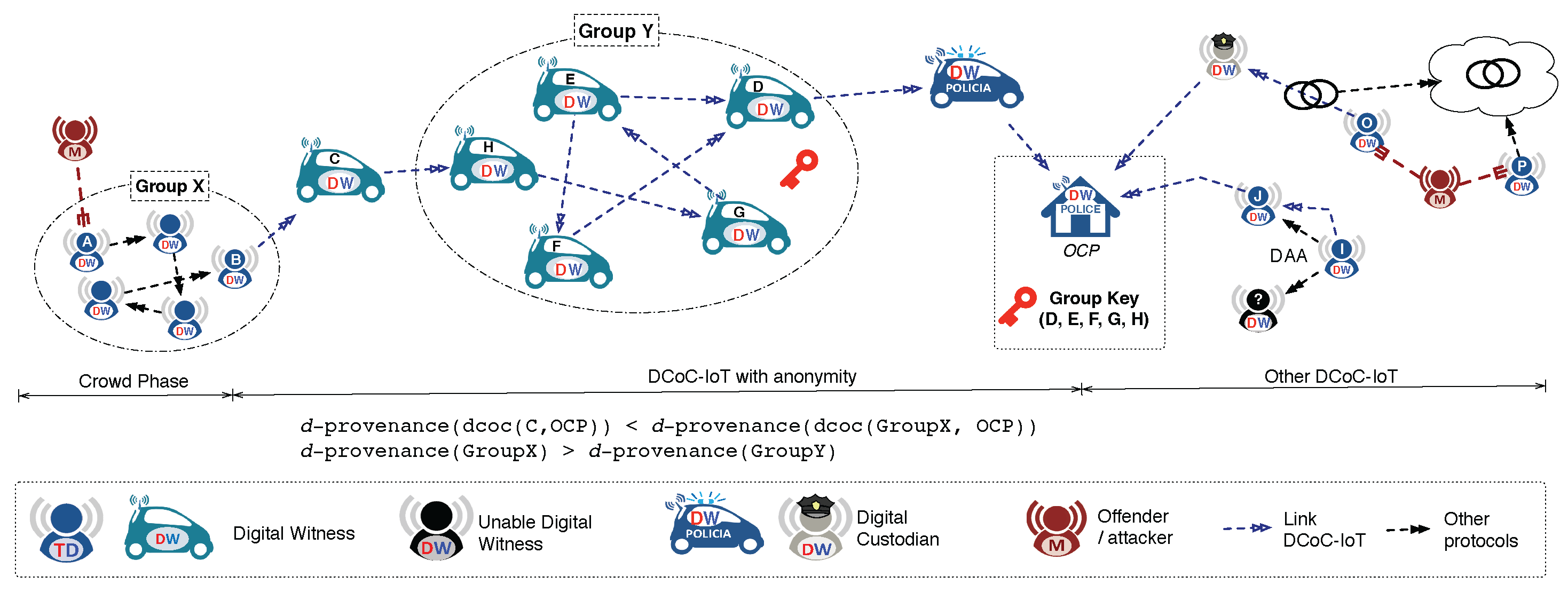
- Anonymous Digital Witnessing. This solution relaxes the definition of digital witness to enable digital evidence to be reported without revealing the real identity of the source. For example, a set of digital witnesses could use a Crowds-like anonymous communication system to report digital evidence without identifying the precise digital witness which requested the investigation. As detailed in [3] and shown in Figure 4, this solution does not provide full anonymity, as this is not allowed because it would affect the traceability requirement (c.f. binding credentials in Section 2.1). Instead, it offers a solution in which i) anonymity is provided at source (defining the concept of d-provenance largely discussed in [3]) but ii) the links in the chain of custody can only opt for the option of anonymity if it is revocable by the OCP.
- M5.
- Anonymous route discovery. Enables the discovery of routes to the OCP without revealing the identity of the initiator. This can be achieved by adapting protocols such as the Authenticated Anonymous Secure Routing (AASR) to the digital witness solution.
- M6.
- Third-party user consents. Not only the user of the digital witness, but all the witnesses involved in a collaboration, accept the policies under a specific context.
- M7.
- Privacy-aware smart contracts. Avoid non-repudiation of transactions while maintaining privacy.
- M8.
- Disposal guarantees. A verifier can check by means of proof of secure erasure whether or not a third party has erased some particular portions of its memory.
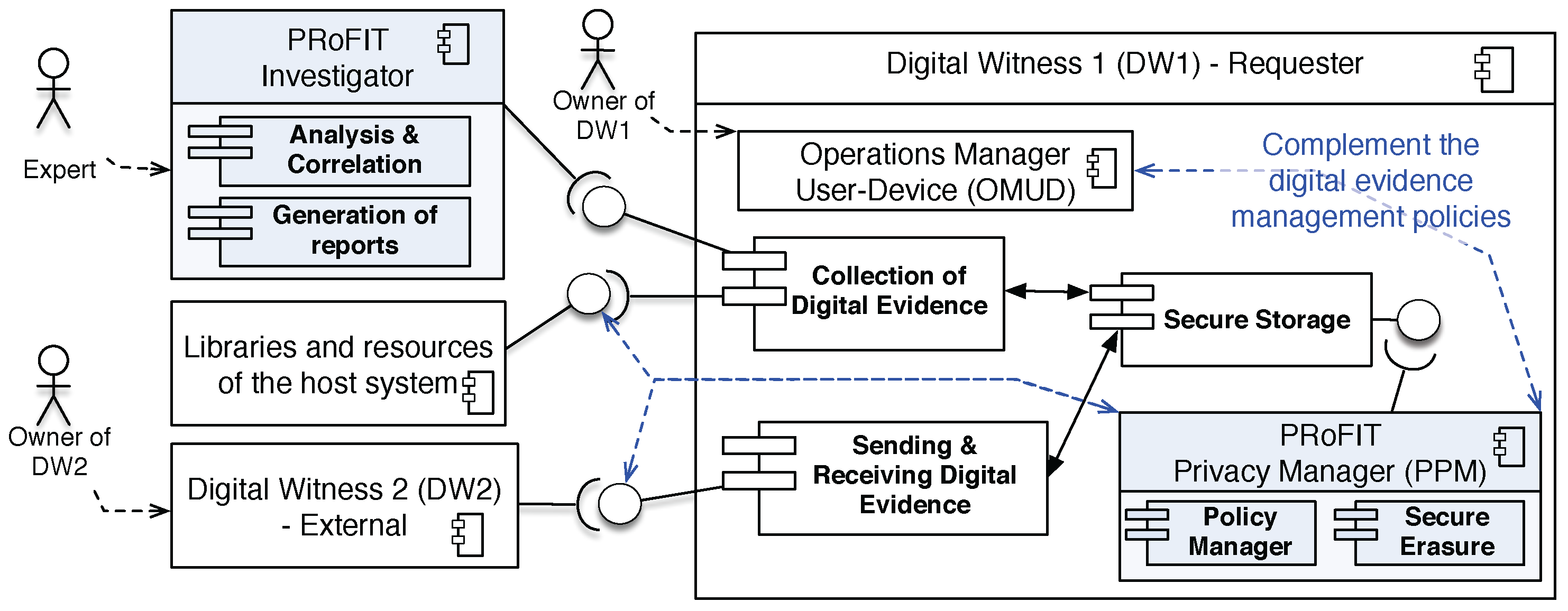
3.2. PRoFIT Privacy Manager Component (PPM) for Digital Witness
- PRoFIT Privacy Manager (PPM). This new component is aimed at enabling the digital witness to follow the PRoFIT methodology [4]. The PPM consists of two subcomponents, the Policy Manager and the Secure Erasure subcomponent. The policy manager handles the group policies defined in [2] plus the new policies to be applied during the PRoFIT phases (c.f. Section 4). The secure erasure module implements the privacy requirement for use, retention and disclosure limitation (c.f. Table 1).
- The privacy policies defined by the owner of the digital witness are used as input to the PPM. Thus, the PRoFIT methodology is followed considering the inputs defined by the user. These privacy policies are defined using the OMUD module but they are handled by the policy manager.
- Fine-grain control in the communication with other digital witness and with other modules of the host system. The PPM acts upon the libraries and resources of the host system to make sure that user policies are satisfied (note that a digital witness is a trusted party within a device [2]), but also in the communication with other digital witnesses, to ensure the inclusion of privacy verification in the PRoFIT phases.
- Direct relationship between two digital witnesses. DW1 requests the cooperation of DW2 to share information. The data received from DW2 is signed by the owner of DW2.
- Relationship between a digital witness and other entities/devices at the crime scene (see Section 4.1). DW1 requests the data from other devices in the crime scene. These objects are handled by a person in charge, and are pre-configured to encrypt and sign the data to be sent together with the conditions to be satisfied, in order to accept the communication with other devices. The signature of data is done using a secret key derived from the key stored in the digital witness (DW2) of the person in charge, following the binding credentials approach (c.f. Section 2.1).
4. Evaluation
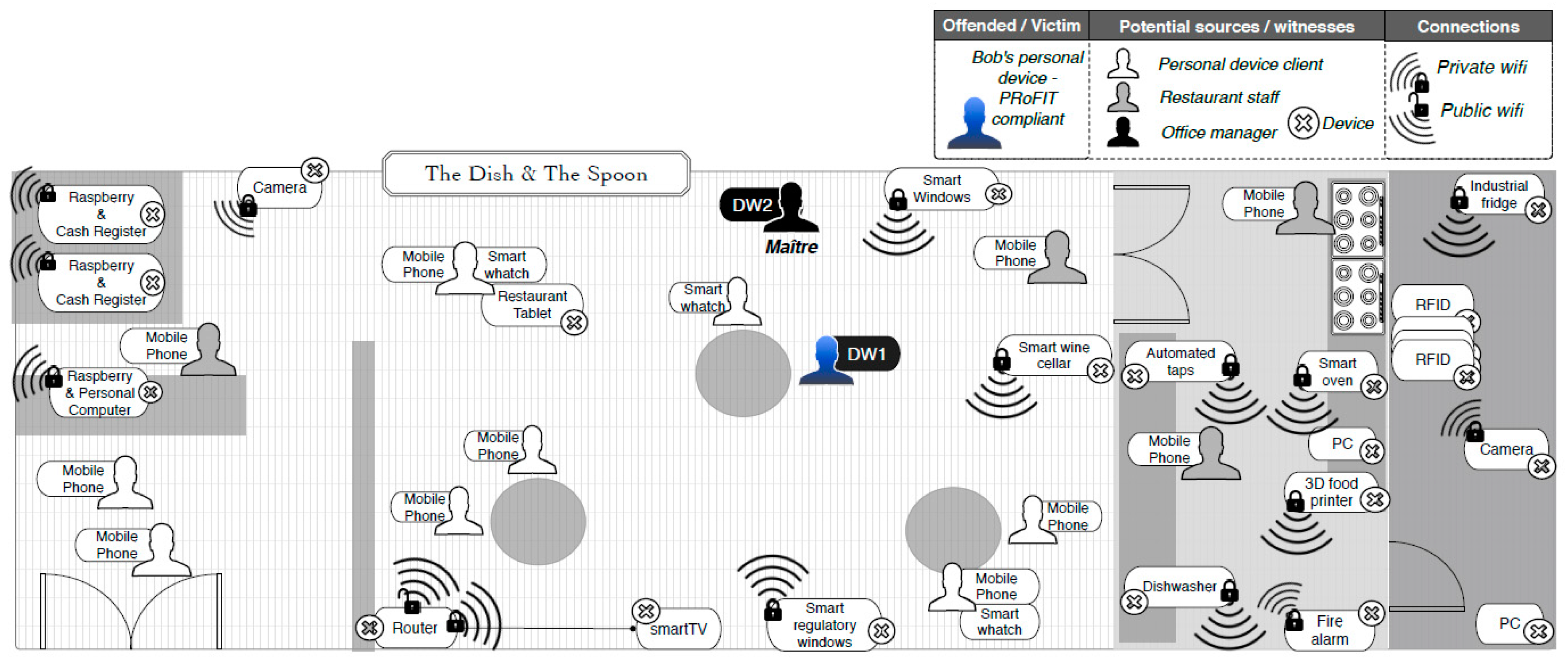
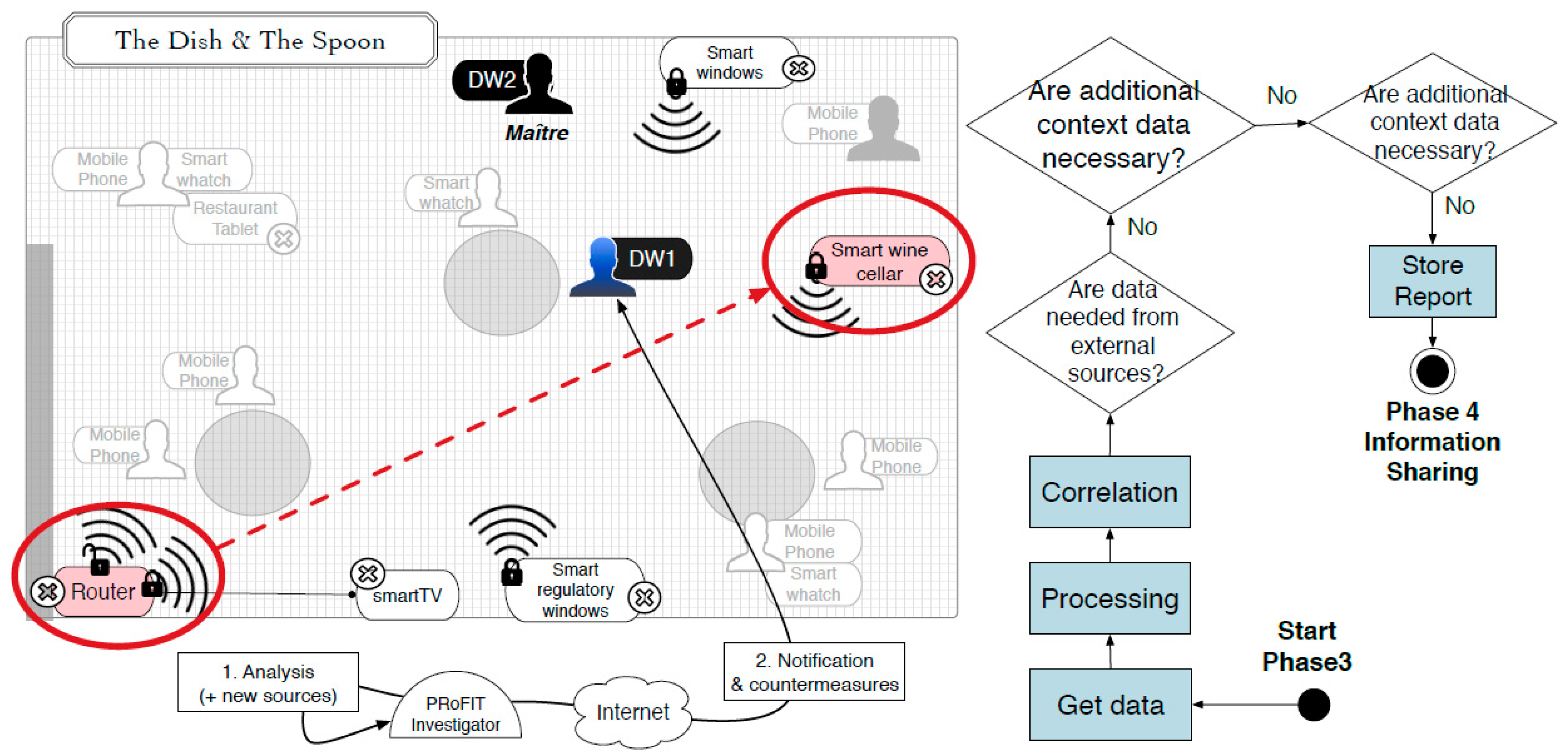
4.1. Social Malware
- Only remote devices within 100 m from Bob (Bluetooth maximum range is around 100 m.) when the incident occurred may share information.
- However, excluding, in any case, those devices that contain personal data or financial information (e.g., cash registers).
- The shared data will only be used for this investigation and once they are eliminated, the restaurant and also the maître (at that time) will be notified.
- The digital evidence collected will be sent using DW1 as intermediary.
4.2. Warehouse Registration
5. Related work
6. Conclusions and Future Work
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Oriwoh, E.; Sant, P. The forensics edge management system: A concept and design. In Proceedings of the 2013 IEEE 10th International Conference on Ubiquitous Intelligence and Computing, 10th International Conference on Autonomic and Trusted Computing (UIC/ATC), Vietri sul Mere, Italy, 18–21 December 2013; pp. 544–550. [Google Scholar]
- Nieto, A.; Roman, R.; Lopez, J. Digital Witness: Safeguarding Digital Evidence by Using Secure Architectures in Personal Devices. IEEE Netw. 2016, 30, 34–41. [Google Scholar] [CrossRef]
- Nieto, A.; Rios, R.; Lopez, J. Digital Witness and Privacy in IoT: Anonymous Witnessing Approach. In Proceedings of the 2017 IEEE Conference on Trustcom/BigDataSE/ICESS, Sydney, NSW, Australia, 1–4 August 2017; pp. 642–649. [Google Scholar]
- Nieto, A.; Rios, R.; Lopez, J. A Methodology for Privacy-Aware IoT-Forensics. In Proceedings of the 2017 IEEE Conference on Trustcom/BigDataSE/ICESS, Sydney, NSW, Australia, 1–4 August 2017; pp. 626–633. [Google Scholar]
- ISO. Information Technology—Security Techniques—Privacy Framework; ISO/IEC 29100:2011 Standard; International Organization for Standardization (ISO): Geneva, Switzerland, 2011. [Google Scholar]
- ISO. Information Technology—Security Techniques—Guidelines for the Analysis and Interpretation of Digital Evidence; ISO/IEC 27042:2015 Standard; International Organization for Standardization (ISO): Geneva, Switzerland, 2015. [Google Scholar]
- Petrocelli, T. Data Protection and Information Lifecycle Management; Prentice Hall PTR: Upper Saddle River, NJ, USA, 2005. [Google Scholar]
- Brickell, E.; Camenisch, J.; Chen, L. Direct Anonymous Attestation. In Proceedings of the 11th ACM Conference on Computer and Communications Security, Washington, DC, USA, 25–29 October 2004; ACM: New York, NY, USA, 2004; pp. 132–145. [Google Scholar]
- Saxena, A.; Soh, B. One-Way Signature Chaining: A new paradigm for group cryptosystems. Int. J. Inf. Comput. Secur. 2008, 2, 268–296. [Google Scholar] [CrossRef]
- Moore, C.; O’Neill, M.; O’Sullivan, E.; Doröz, Y.; Sunar, B. Practical homomorphic encryption: A survey. In Proceedings of the 2014 IEEE International Symposium on Circuits and Systems (ISCAS), Melbourne, VIC, Australia, 1–5 June 2014; pp. 2792–2795. [Google Scholar]
- Liu, W.; Yu, M. AASR: Authenticated Anonymous Secure Routing for MANETs in Adversarial Environments. IEEE Trans. Veh. Technol. 2014, 63, 4585–4593. [Google Scholar] [CrossRef]
- Kosba, A.; Miller, A.; Shi, E.; Wen, Z.; Papamanthou, C. Hawk: The blockchain model of cryptography and privacy-preserving smart contracts. In Proceedings of the 2016 IEEE Symposium on Security and Privacy (SP), San Jose, CA, USA, 22–26 May 2016; pp. 839–858. [Google Scholar]
- Karvelas, N.P.; Kiayias, A. Efficient Proofs of Secure Erasure. In Proceedings of the International Conference on Security and Cryptography for Networks (SCN 2014), Amalfi, Italy, 3–5 September 2014; pp. 520–537. [Google Scholar]
- Peng, S.; Yu, S.; Yang, A. Smartphone malware and its propagation modeling: A survey. IEEE Commun. Surv. Tutor. 2014, 16, 925–941. [Google Scholar] [CrossRef]
- Afanasyev, M.; Kohno, T.; Ma, J.; Murphy, N.; Savage, S.; Snoeren, A.C.; Voelker, G.M. Privacy-preserving network forensics. Commun. ACM 2011, 54, 78–87. [Google Scholar] [CrossRef]
- Stirparo, P.; Kounelis, I. The mobileak project: Forensics methodology for mobile application privacy assessment. In Proceedings of the 2012 International Conference for Internet Technology And Secured Transactions, London, UK, 10–12 December 2012; pp. 297–303. [Google Scholar]
- Daniel, L.E. Digital Forensics for Legal Professionals: Understanding Digital Evidence From the Warrant to the Courtroom; Elsevier: Boston, MA, USA, 2012; 368p. [Google Scholar]
- Antoniou, G.; Sterling, L.; Gritzalis, S.; Udaya, P. Privacy and forensics investigation process: The ERPINA protocol. Comput. Stand. Interfaces 2008, 30, 229–236. [Google Scholar] [CrossRef]
- Law, F.Y.; Chan, P.P.; Yiu, S.M.; Chow, K.P.; Kwan, M.Y.; Hayson, K.; Lai, P.K. Protecting digital data privacy in computer forensic examination. In Proceedings of the 2011 IEEE Sixth International Workshop on Systematic Approaches to Digital Forensic Engineering (SADFE), Oakland, CA, USA, 26 May 2011; pp. 1–6. [Google Scholar]
- Mylonas, A.; Meletiadis, V.; Mitrou, L.; Gritzalis, D. Smartphone sensor data as digital evidence. Comput. Secur. 2013, 38, 51–75. [Google Scholar] [CrossRef]
- Grover, J. Android forensics: Automated data collection and reporting from a mobile device. Digit. Investig. 2013, 10, S12–S20. [Google Scholar] [CrossRef]
- De Fuentes, J.M.; González-Manzano, L.; Gonzalez-Tablas, A.I.; Blasco, J. WEVAN—A mechanism for evidence creation and verification in VANETs. J. Syst. Archit. 2013, 59, 985–995. [Google Scholar] [CrossRef]



| ISO/IEC 29100 | PRoFIT Phases | |||||
|---|---|---|---|---|---|---|
| PP | CC | AC | IS | PT | RV | |
| 1. Consent and choice | ✓ | ✓ | ✓ | |||
| 2. Purpose legitimacy and specification | ✓ | ✓ | ✓ | |||
| 3. Collection limitation | ✓ | |||||
| 4. Data Minimisation | ✓ | ✓ | ||||
| 5. Use, rentention and disclosure limitation | ✓ | |||||
| 6. Accuracy and quality | ✓ | ✓ | ||||
| 7. Openness, transparency and notice | ✓ | ✓ | ||||
| 8. Individual participation and access | ✓ | |||||
| 9. Accountability | ✓ | |||||
| 10. Information security controls | ✓ | ✓ | ||||
| 11. Compliance | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| Privacy Risk for DW | Mitigation Mechanisms | PRoFIT Phases | |||||
|---|---|---|---|---|---|---|---|
| PP | CC | AC | IS | PT | RV | ||
| Devices nearby may know when a DW has been disabled from its duties | Direct Anonymous Attestation [8] | ✓ | ✓ | ||||
| Acknowledge the acquisition of digital evidence without the signer accessing the contents | Blind signatures + signature chaining [9] | ✓ | ✓ | ||||
| Witnesses may be reluctant to share their own version of the incident with other participants | Homomorphic encryption or secure computation [10] | ✓ | ✓ | ||||
| The identity of a witness is known | Anonymous digital witnessing [3] | ✓ | ✓ | ✓ | |||
| The identity of those involved in the discovery process is exposed | Anonymous route discovery [11] | ✓ | ✓ | ||||
| The system could expose other users as being part of the environment | Third-party user consents | ✓ | ✓ | ✓ | ✓ | ✓ | |
| Transactions could show private information | Privacy-aware smart contracts [12] | ✓ | ✓ | ✓ | |||
| The data shared with an investigator could be used for additional purposes without consent | Disposal Guarantees [13] | ✓ | ✓ | ||||
| Example | Privacy | Computer Forensics |
|---|---|---|
| Onion routing | Privacy in communications (e.g., Tor) | Affects traceability |
| Anonymity | Hides the identity of the individual | Affects liability and traceability |
| Data encryption | Confidentiality, data privacy | Makes data analysis difficult/impossible. |
| Aggregation | Data minimisation | Relevant data can be lost and traceability affected |
| Secure erasure | Data privacy | Lost of digital evidence |
| Report incidence | Affects location privacy and anonymity if the subject’s identity is indicated | Adds value to data correlation and verification. |
| Data collection | Can provide sensitive information about the environment | Allows to obtain more verifiable information |
| Data correlation | Affects linkability; can help to get information about the identity of third parties (and other data) | Can help to deduce new relevant information for the case |
| Node discovery | Affects location privacy | Potential sources of data |
| Legal procedures | Privacy as humans right | Admissibility of digital evidence |
| ISO/IEC 29100:2011 | Proactive IoT-Forensic Solutions | |||
|---|---|---|---|---|
| Themis | DroidWatch | DW | PRoFIT-Compliant DW | |
| 1. Consent and choice | ✓(user) | ✓(user) | ✓(user) | ✓(user & third party) |
| 2. Purpose legitimacy and specification | ✓(user) | ✓(user & third party) | ||
| 3. Collection limitation | ✓ | |||
| 4. Data Minimisation | ✓ | |||
| 5. Use, rentention and disclosure limitation | ✓ | |||
| 6. Accuracy and quality | ✓ | ✓ | ||
| 7. Openness, transparency and notice | ✓ | |||
| 8. Individual participation and access | ✓ | |||
| 9. Accountability | ✓ | |||
| 10. Information security controls | ✓ | ✓ | ✓ | |
| 11. Compliance | ✓ | |||
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Nieto, A.; Rios, R.; Lopez, J. IoT-Forensics Meets Privacy: Towards Cooperative Digital Investigations. Sensors 2018, 18, 492. https://doi.org/10.3390/s18020492
Nieto A, Rios R, Lopez J. IoT-Forensics Meets Privacy: Towards Cooperative Digital Investigations. Sensors. 2018; 18(2):492. https://doi.org/10.3390/s18020492
Chicago/Turabian StyleNieto, Ana, Ruben Rios, and Javier Lopez. 2018. "IoT-Forensics Meets Privacy: Towards Cooperative Digital Investigations" Sensors 18, no. 2: 492. https://doi.org/10.3390/s18020492
APA StyleNieto, A., Rios, R., & Lopez, J. (2018). IoT-Forensics Meets Privacy: Towards Cooperative Digital Investigations. Sensors, 18(2), 492. https://doi.org/10.3390/s18020492






