Big Data Collection in Large-Scale Wireless Sensor Networks
Abstract
1. Introduction
1.1. Background
1.2. Author’s Contributions
1.3. Organization of the Paper
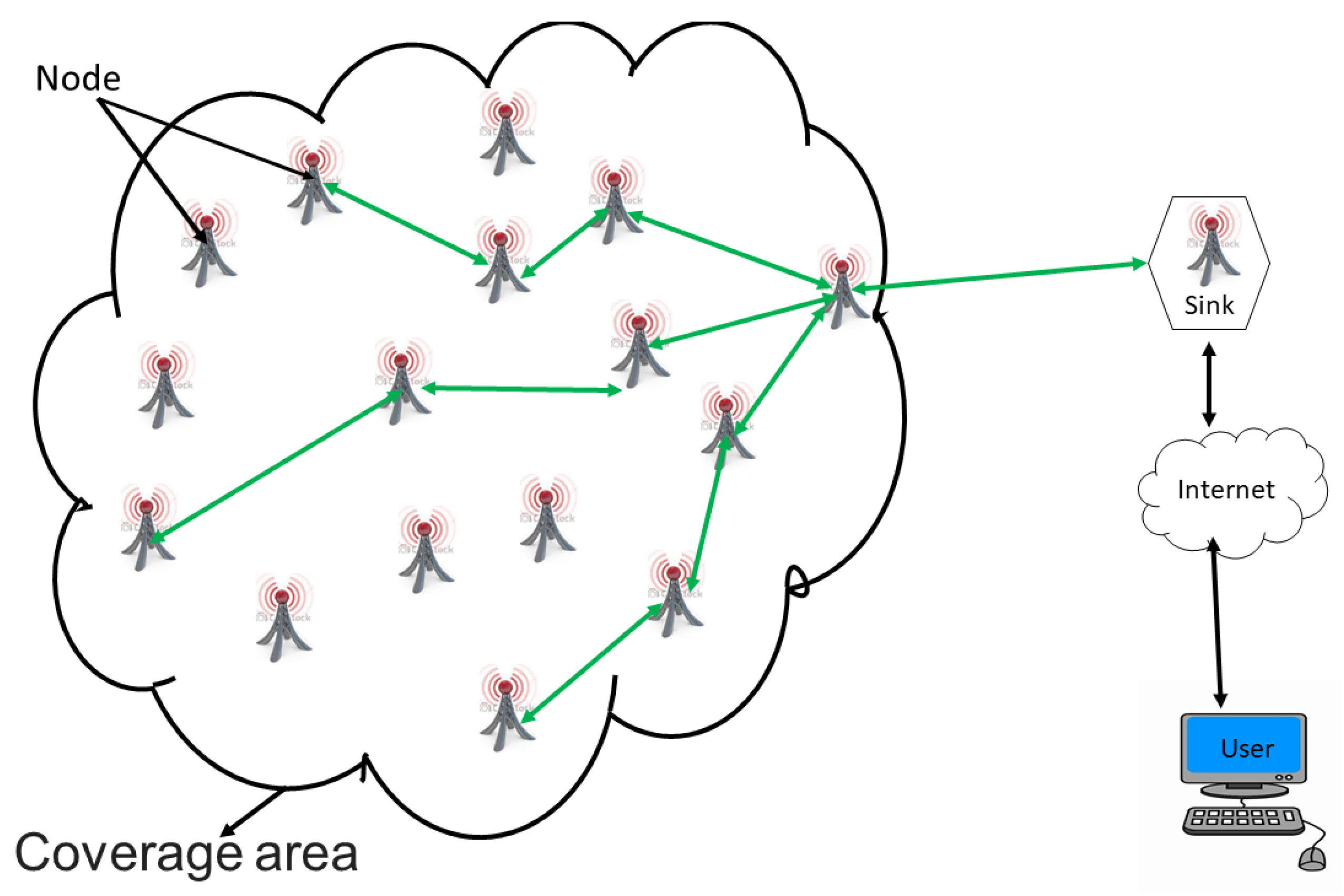
2. Overview of WSNs
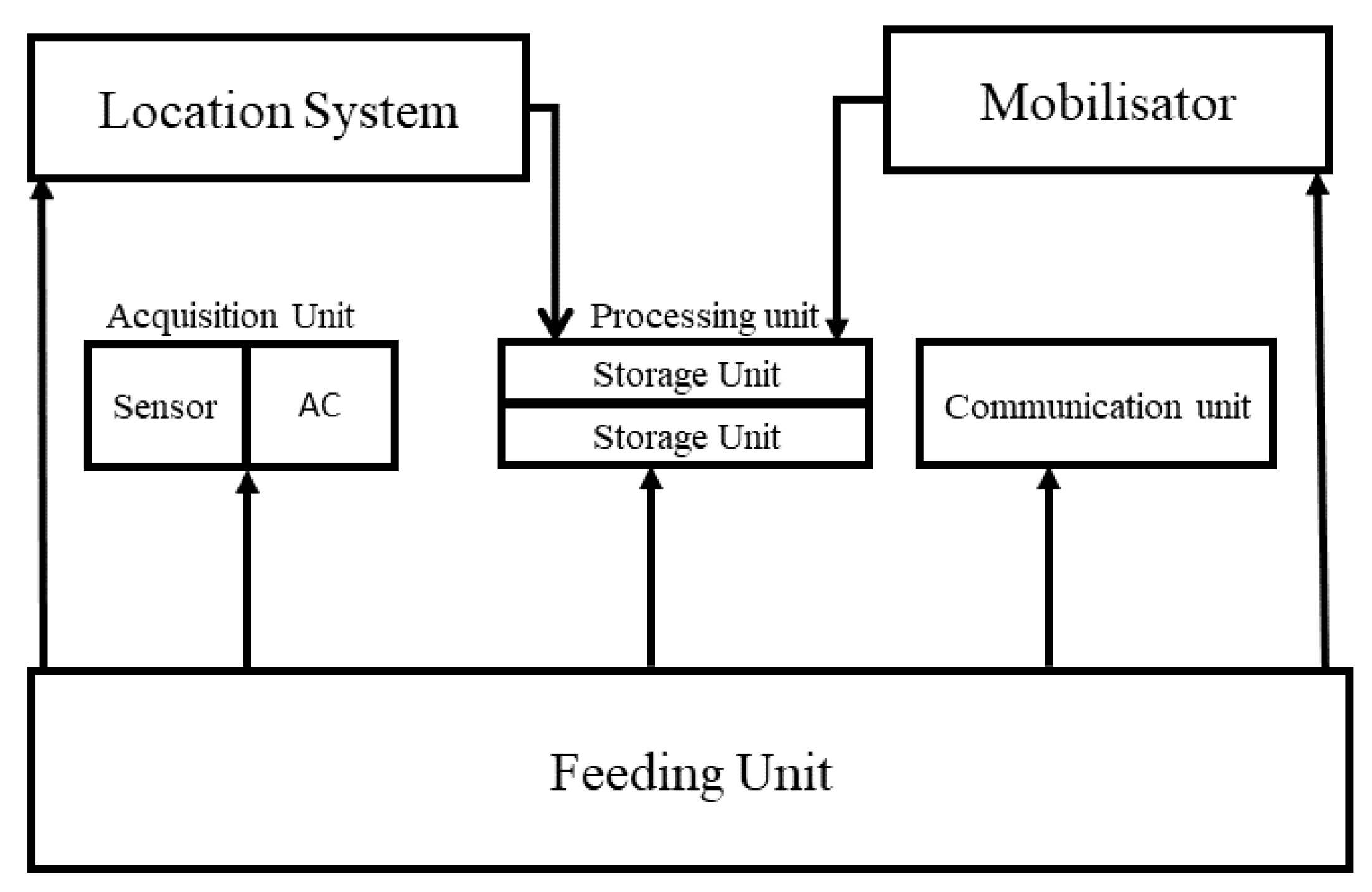
2.1. Hardware Architecture of a Wireless Sensor
- Acquisition unit. This consists of two subunits: a sensor and an analog-to-digital converter (ADC). The sensor collects digital measurements on environmental parameters and transforms them into analog signals. The ADC converts analog signals into digital signals.
- Processing unit. This is also composed of two units: a data-storage unit, and a processor responsible for data-processing and control procedures allowing the collaboration of the sensor with the others in order to carry out acquisition tasks.
- Communication unit. Its function is information transmission and reception. It is equipped with a transmitter/receiver pair. It allows communication within the network, in our case, by radio frequency (radio waves). However, there are other transmission possibilities (e.g., optical and infra red)
- Power unit. Power supply is a critical element of sensor architecture. It is responsible for supplying energy to all other units. It most often corresponds to a battery, feeding the sensor, whose limited resources make it a problem specific to this type of network. However the recent realization of solar-panel power unit is trying to provide a solution for extending sensor life [33].
- Mobilizer. Optionally, this is used to move the node to complete the task to be processed.
- Location-Finding System. Optionally, this provides information on the location required by the application and/or routing.
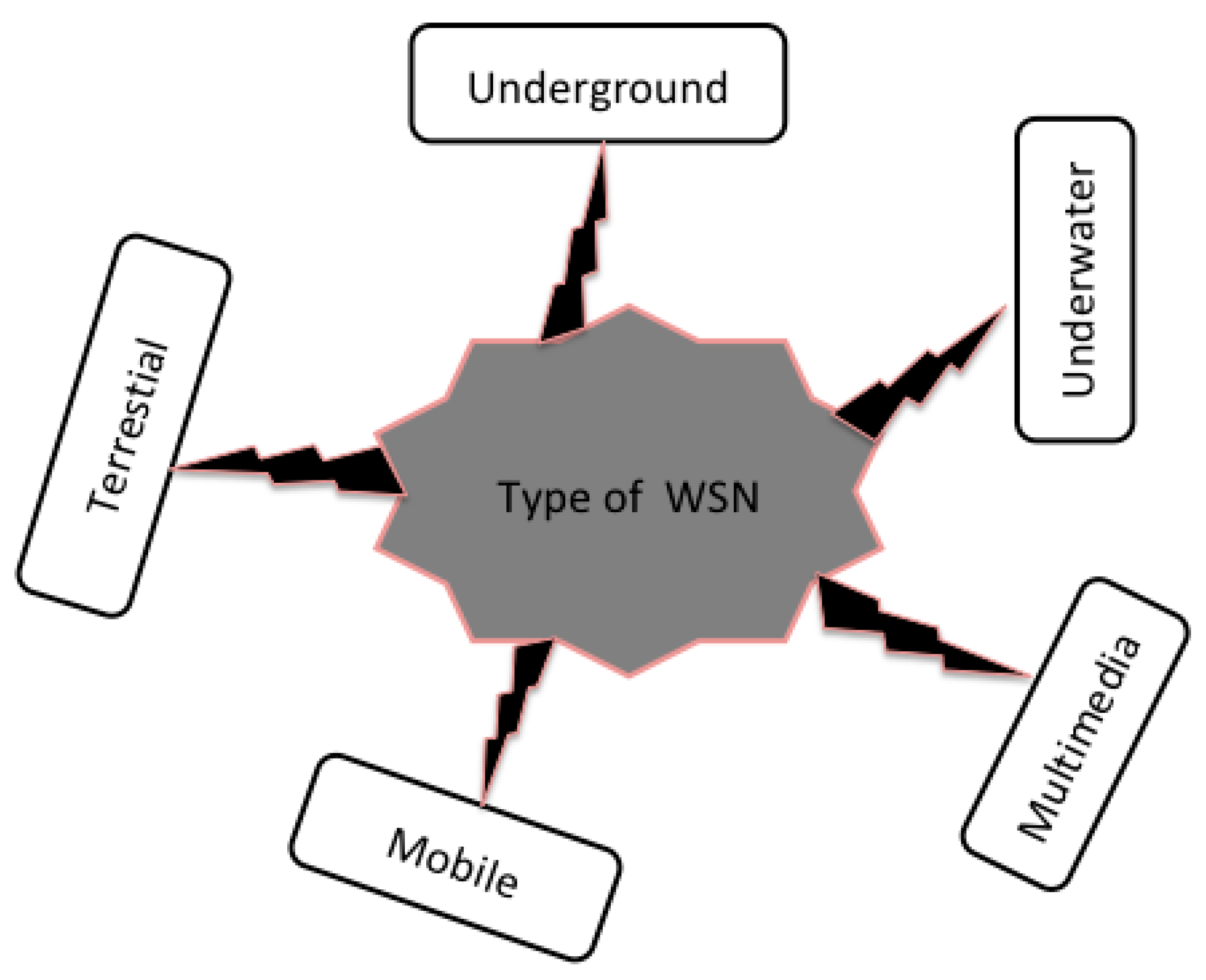
2.2. Types of WSNs
- Terrestrial. This kind of WSNs is intended to be deployed in a terrestrial space. In these networks, hundreds of thousands of sensors are deployed randomly or deterministically over a given area. This type of WSN is much more useful in the field of environmental monitoring and natural phenomena; however, it represents a challenge for the sustainability of the network in terms of energy management [34].
- Underground. These networks consist of very special sensor nodes known for their high cost and the logistics necessary for their implementation and maintenance. In this type of network, the sensor nodes are installed in the ground. They find their application in agriculture or in minefields, where they are used to monitor conditions in the soil. However, in this type of network, there is a ground node that has a role in transmitting the information detected by the underground nodes to the base station [35].
- Underwater. This particular type of WSNs is networks hidden under the sea. Because of the hostility represented by the environment of their deployment, this type of network remains an interesting research challenge. These nodes are more expensive than terrestrial sensors, wireless communication is acoustic, bandwidth is limited, signal loss is recurrent, and propagation delays and synchronization problems are frequent [36,37].
- Multimedia. These WSNs are designed to monitor and trace data such as images, videos, and sound. These sensors are equipped with cameras and microphones. This type of network requires good bandwidth and good quality of service, which implies high power consumption for data processing and compression. Preplanning is required for the deployment of these sensors [38].
- Mobile. This is the most recent type of WSN, and it uses mobile nodes that can autonomously reposition and reorganize the network. After initial deployment, the nodes disperse to gather information. There is also a hybrid network consisting of a combination of mobile and fixed sensors [12,25,26,37,39,40,41,42].
2.3. Topologies of WSNs
2.3.1. Star Topology
2.3.2. Mesh Topology
2.3.3. Hybrid Topology
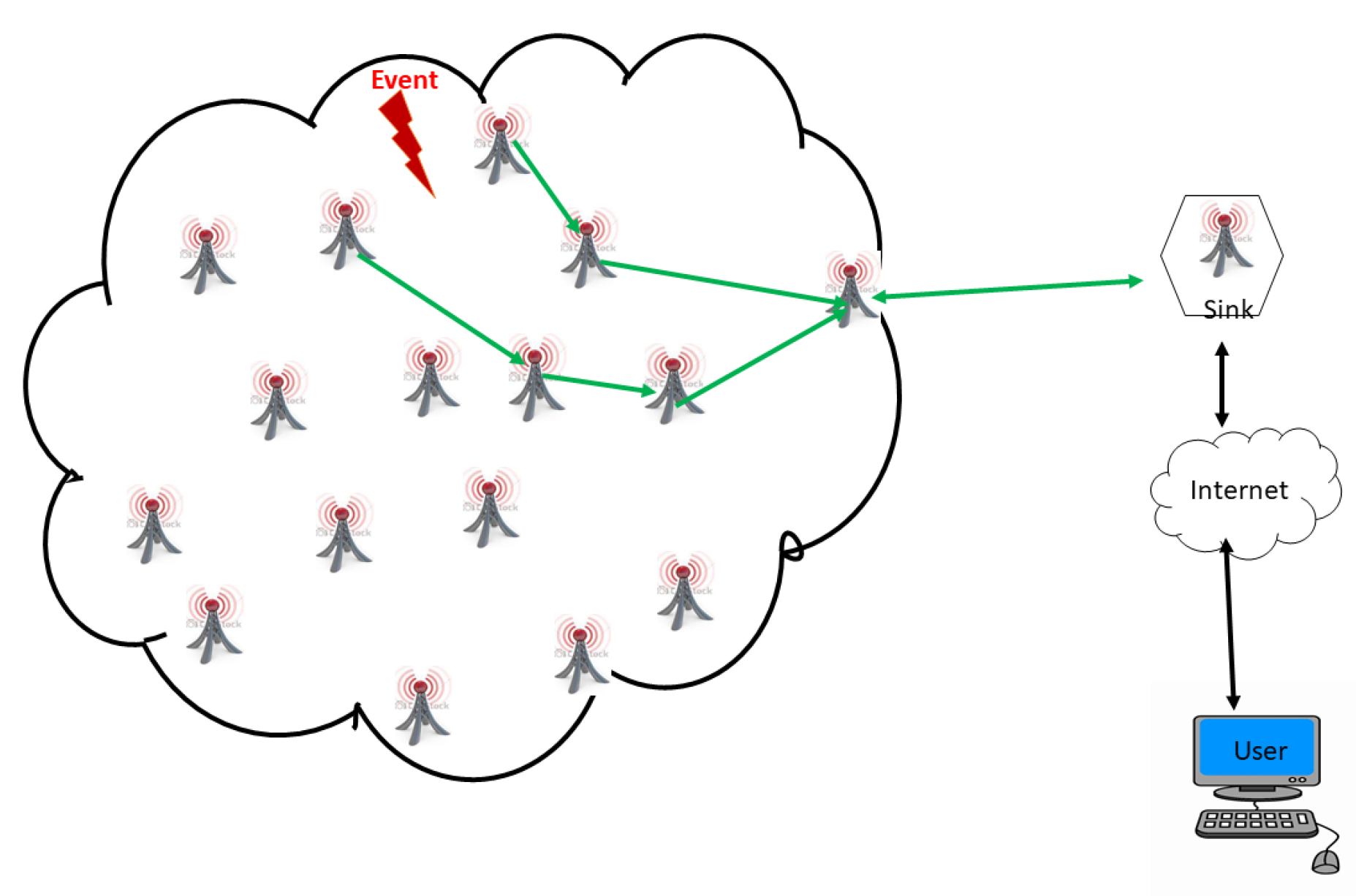
2.4. WSN Communication
2.4.1. One-Hop Communication
2.4.2. Multihop Communication
2.5. Specific Characteristics of Sensor Networks
2.5.1. Sensor-Node Features
- Energy consumption. Sensors have energy autonomy, and they usually use tiny batteries as energy resources. In most cases, WSNs are deployed in hard-to-reach areas. This makes it difficult or almost impossible to recharge or replace the batteries. This difficulty leads us to deduce that the life of a sensor is essentially dependent on the life of the battery. Therefore, energy-consumption management is a major constraint in this type of network.
- Transmission scope. This is an important criterion for the deployment of a WSN. It is limited by the radiation capacity of the antennas used and the signal strength involved. For example, the communication between two sensor nodes can only take place if the distance between them is not too great, i.e., a few tens of meters in practice. The longer the distance is, the higher the energy cost. This is especially true if there are physical obstacles between the two nodes that may prevent communication.
- Storage and processing power. An intrinsic characteristic of these sensors is their low storage capacity. Although they also have a processor, the sensors cannot perform very large operations due to their relatively low processing power. For example, “mote”-type sensor nodes are composed of an 8-bit 4 MHz microcontroller, 40 KB of memory, and a radio with a bit rate of about 10 Kbps. This remains true even for midrange nodes, such as “UCLA/ROCKWELL’S WINS”, which have a strong ARM 1100 processor with 1 MB flash memory, 128 KB of RAM, and a 100 Kbps radio.
2.5.2. WSN Features
- Sensor autoconfiguration. In a WSN, sensors are deployed either in a random manner by a missile, drone, or airplane, or manually deployed by a human or a robot, inside or around an observed phenomenon such as a field of war, volcanic surface, or sick patient [46]. Thus, each sensor node has the ability, on the one hand, to self-configure in the network, and, on the other hand, to collaborate with other nodes in order to dynamically reconfigure the network in case of network-topology changes [41]. As a reminder, each sensor in a WSN has a transmitting/receiving unit that allows it to communicate with the sensors that are close to it. By exchanging information with them, the sensor can then discover its neighbors and thus know the routing method that it will adopt according to the needs of the application. Autoconfiguration appears to be a necessary feature in the case of WSNs since, on the one hand, their deployment is done randomly in the majority of applications, and, on the other hand, the number of sensors is very high.
- Scalability. Unlike traditional wireless networks (personal, local, or extended), a WSN consists of a very large number of sensors (hundreds or thousands) [33]. The sensor network is scalable in that it has the ability to accept a large number of sensors that work together to achieve a common goal.
- Fault tolerance. In case of a sensor malfunction (lack of energy, interference with observation environment) or if new sensors are added to the network, the existing sensor nodes in the WSN must continue to normally operate without interruption [33]. This explains the fact that a WSN does not adopt a fixed but rather dynamic topology.
- Communication ability. It can take one of two aspects, multihop or one-hop. Multihop communication is less energy-intensive, and it remains the most sought-after type of communication for WSN applications that require low energy consumption. Finally, it should be noted that WSNs use a nonstandardized protocol stack. However, the majority of scientific work that deals with the WSN issue is based on the protocol stack proposed in 2002 by Akyildiz et al. [33], which is presented in Section 2.6.
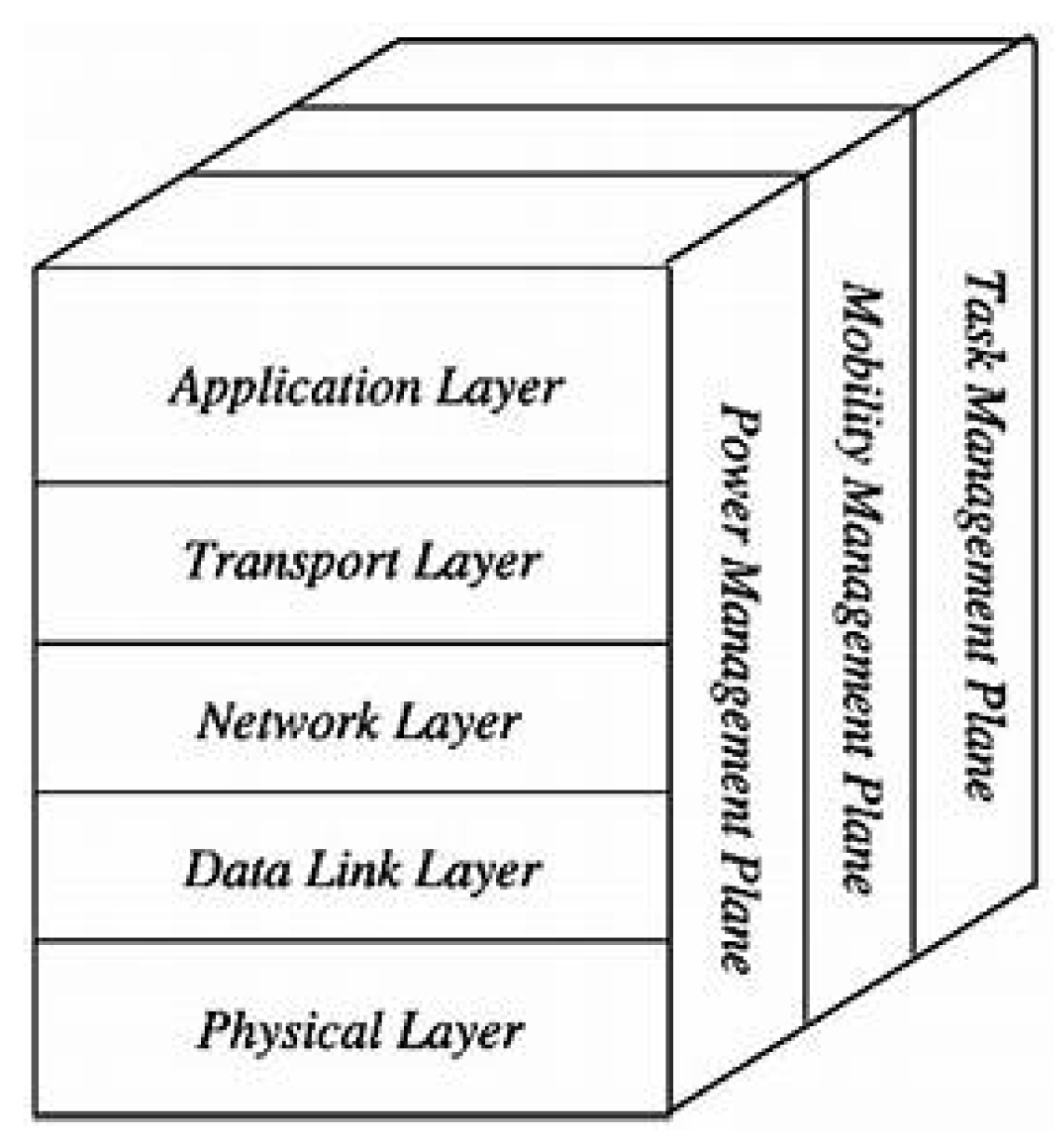
2.6. Protocol Architecture
- Application layer. Depending on the functionality of the sensors, different applications can be used and built on this layer.
- Transport layer. It is used to maintain the flow of data when needed in the applications used, especially when connected to the Internet.
- Network layer. This deals with the routing of data provided by the transport layer.
- Data-link layer. As the sensor network environment is noisy and nodes can be mobile, the MAC layer must ensure low power consumption in the data broadcast of neighboring nodes.
- Physical layer. This deals with data-transmission, -reception, -modulation, and -encryption techniques.
- Energy-, mobility-, and task-management levels are responsible for controlling the consumed energy, node movements, and task distribution across the entire protocol stacks. These levels allow sensors to co-ordinate their tasks and minimize energy consumption.
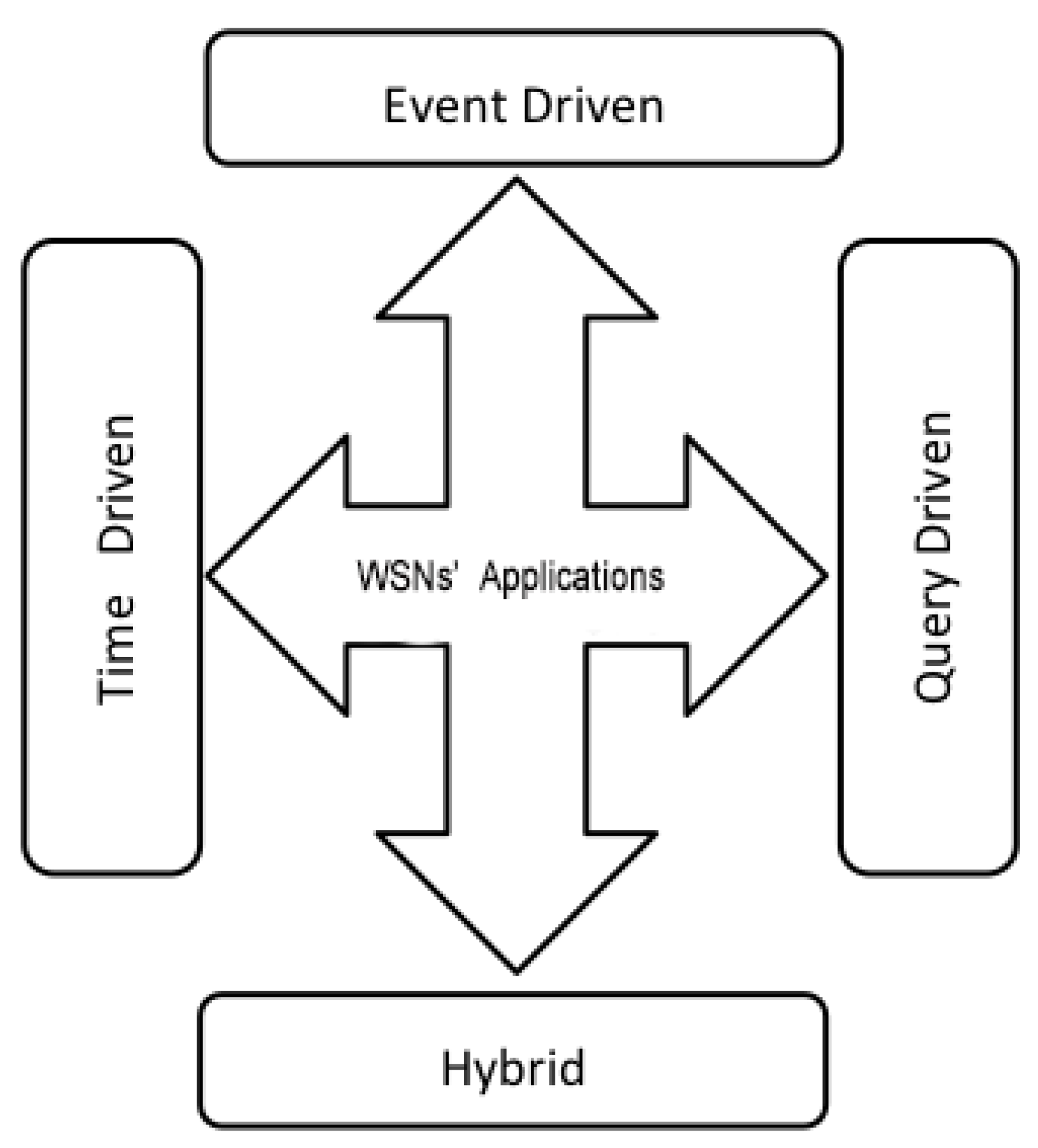
2.7. Dedicated Applications
2.7.1. Event-Driven
- A high density of sensor nodes is required to ensure high probability of event detection. This implies that the network must have very good coverage.
- Good coverage of sensor nodes that usually depends on the type of event to be detected.
- An exact location of all sensor nodes in the network is required. This is to locate the event through the sensor node in which the event occurs. Note that distributed location algorithms could be used for this purpose.
- Good network connectivity linked to transmission coverage so that communication protocols allow the alarm sent by sensor nodes to arrive at the sink with high probability and in the shortest time.
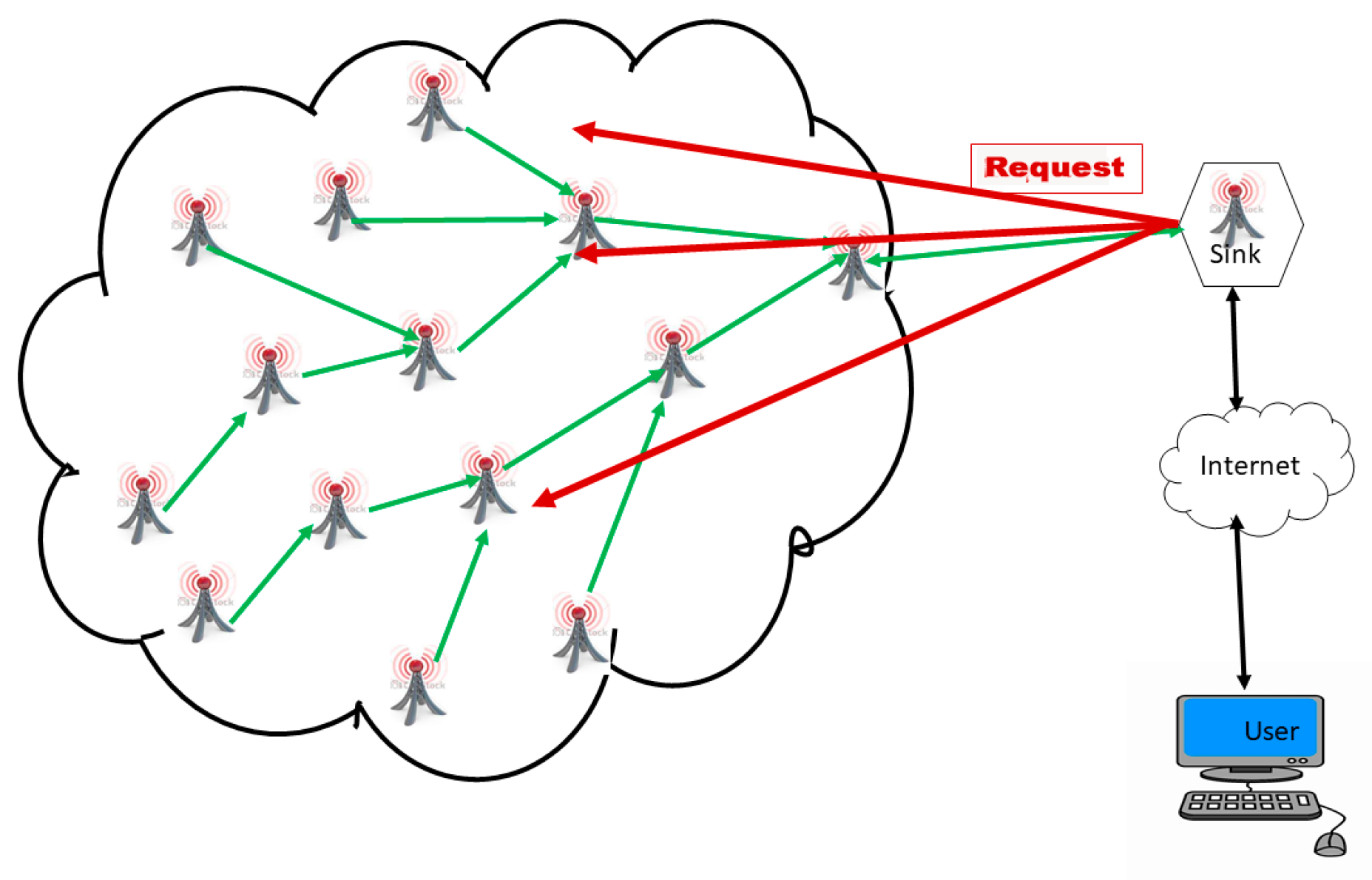
2.7.2. Query-Driven
2.7.3. Time-Driven
2.7.4. Hybrid
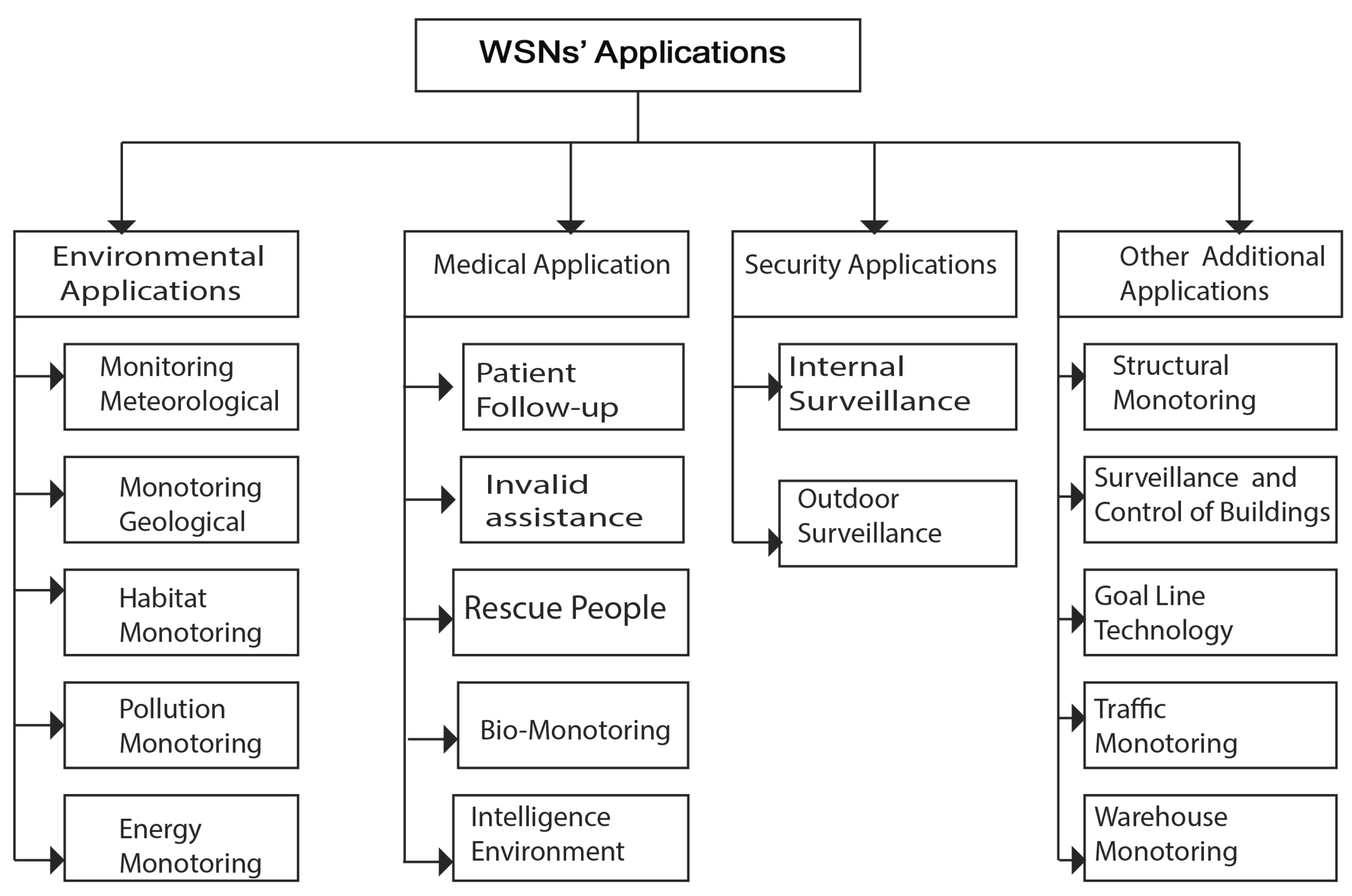
2.8. WSN Application Areas
2.8.1. Environmental Applications
2.8.2. Medical Applications
2.8.3. Security Applications
2.8.4. Other Applications
2.9. Challenges of WSN Design and Deployment
- Energy. A sensor node, by its size, is limited in energy resources, storage capacity, and processing. One of the most serious concerns is the lifespan of the sensor node, which is entirely determined by the amount of energy available and the rate of energy consumption (that is, the average energy consumption). Since improving the energy capacity of small batteries still requires a lot of effort, the goal of a long service life is difficult to achieve by increasing the amount of available energy. As a result, the design of energy-efficient MAC protocols, communication strategies, operating systems, and energy-efficient routing mechanisms provides effective ways to extend the life of the node [36]. The use of energy-recovery technologies for sensor-node power supplies has also been an alternative in recent years.
- Quality of Service (QoS). Quality is defined by the ability to interpret the information collected by the sink. In spite of the fact that the QoS requirements vary according to the different WSN applications, the two main measures of QoS are data reliability and latency [33]. Usually, a successful data-exchange rate between the sensor nodes and the sink must be above a certain threshold to ensure network reliability and functionality. Reliability can be further maximized, but this could be at the cost of increased energy consumption. Therefore, a compromise is necessary. In case of latency, for certain types of applications, the reception of the data detected on the sink is strictly timed, so that latency data can cause delay problems and lead to bad decisions, particularly in industrial-surveillance applications.
- Security and privacy. WSNs find their applications in various areas of life. Some applications manipulate private data. Moreover, WSNs are networks whose topology is very frequently subject to change. The deployment of sensor nodes is sometimes done in accessible areas; they may encounter technical interference or human intrusion, which can lead to confidentiality issues. Thus, the network should allow the detection of intrusions. It is therefore necessary to design robust and lightweight algorithms for data encryption, authentication mechanisms for privacy protection, and secure routing for data relays to protect the entire network against passive and active attacks, and denials of external service providers [55,56,57].
- Adaptability. The design of a WSN must be sufficiently flexible and adaptable to be deployable across a wide range of application scenarios. The entire network should be kept functional regardless if the number of sensor nodes is hundreds, thousands, or very small. Due to the mobility of sensor nodes and observed events, as well as the possibility that a sensor node can fail in the network, the overall topology of the network may be subject to frequent change. Therefore, the design of a WSN must be sufficiently intelligent and robust to deal with these dynamic topology scenarios [10,31].
- Localization. WSNs play an important role in the problem of locating elements in a given deployment area. Certainly, GPS is a well-known tracking system and the most used location system. However, it is not satisfactory for this use, because it accumulates handicaps. It is only available outdoors and if no obstacle obstructs the field of view of the receivers. In addition, an operation under dense foliage or in cities with narrow streets is not possible, which are very bad conditions. Moreover, it is particularly expensive, both in terms of hardware, multiplied to many copies in a network with high sensor density. Moreover, signal reception is very energy-greedy, which is not compatible with management problems of battery service life. Location is done in two steps: distance estimation to the other nodes, and triangulation. The development of new localization techniques has become a major concern for WSNs [33,58].
3. Overview of Big Data
3.1. Characterization of Big Data
3.1.1. Volume
3.1.2. Velocity
3.1.3. Variety
3.2. Toward Smart Data
3.2.1. Veracity
3.2.2. Value
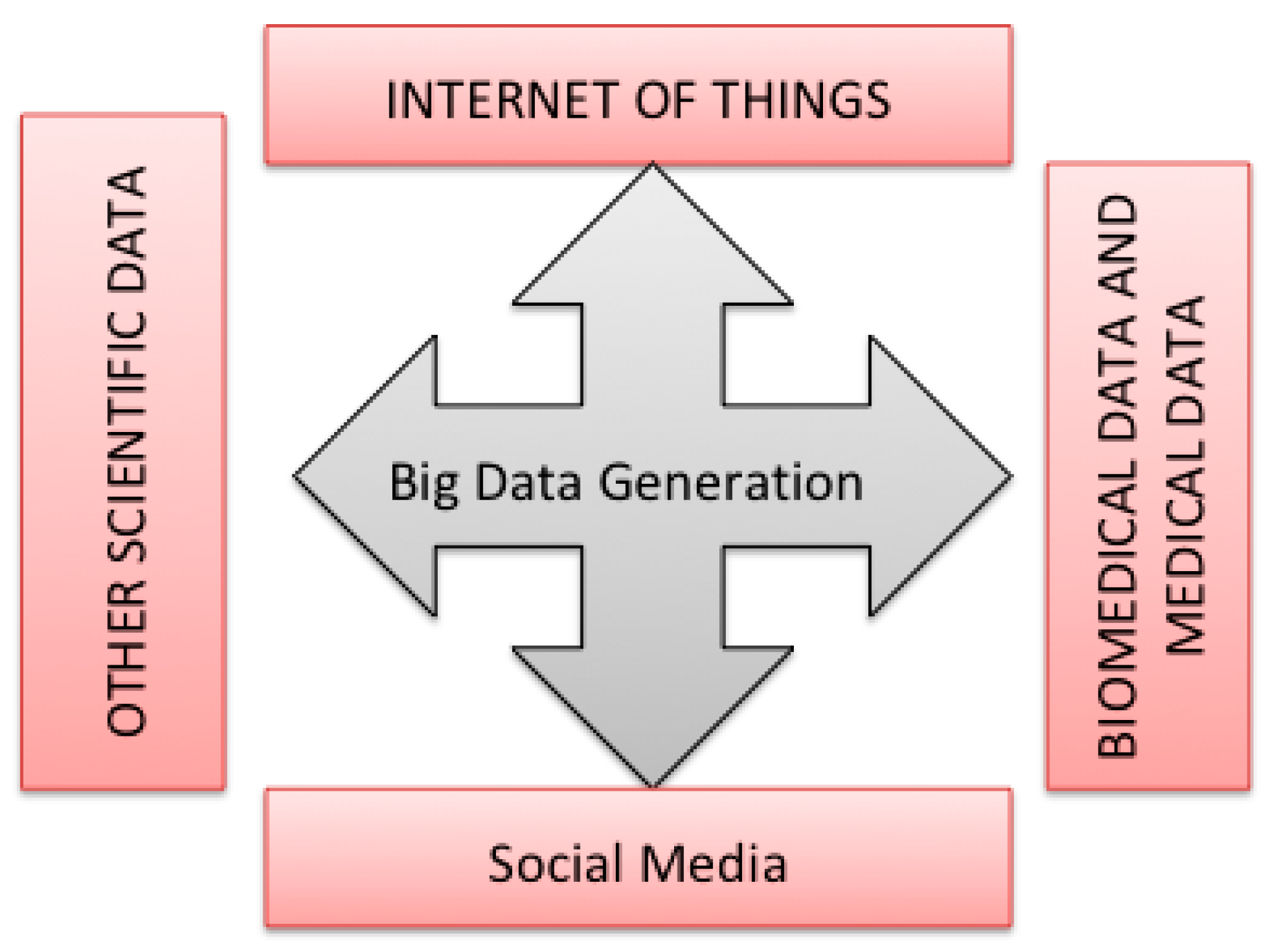
3.3. Big Data Generation
3.3.1. Medical and Biomedical Data
3.3.2. Internet of Things
3.3.3. Social Media
3.3.4. Scientific Data
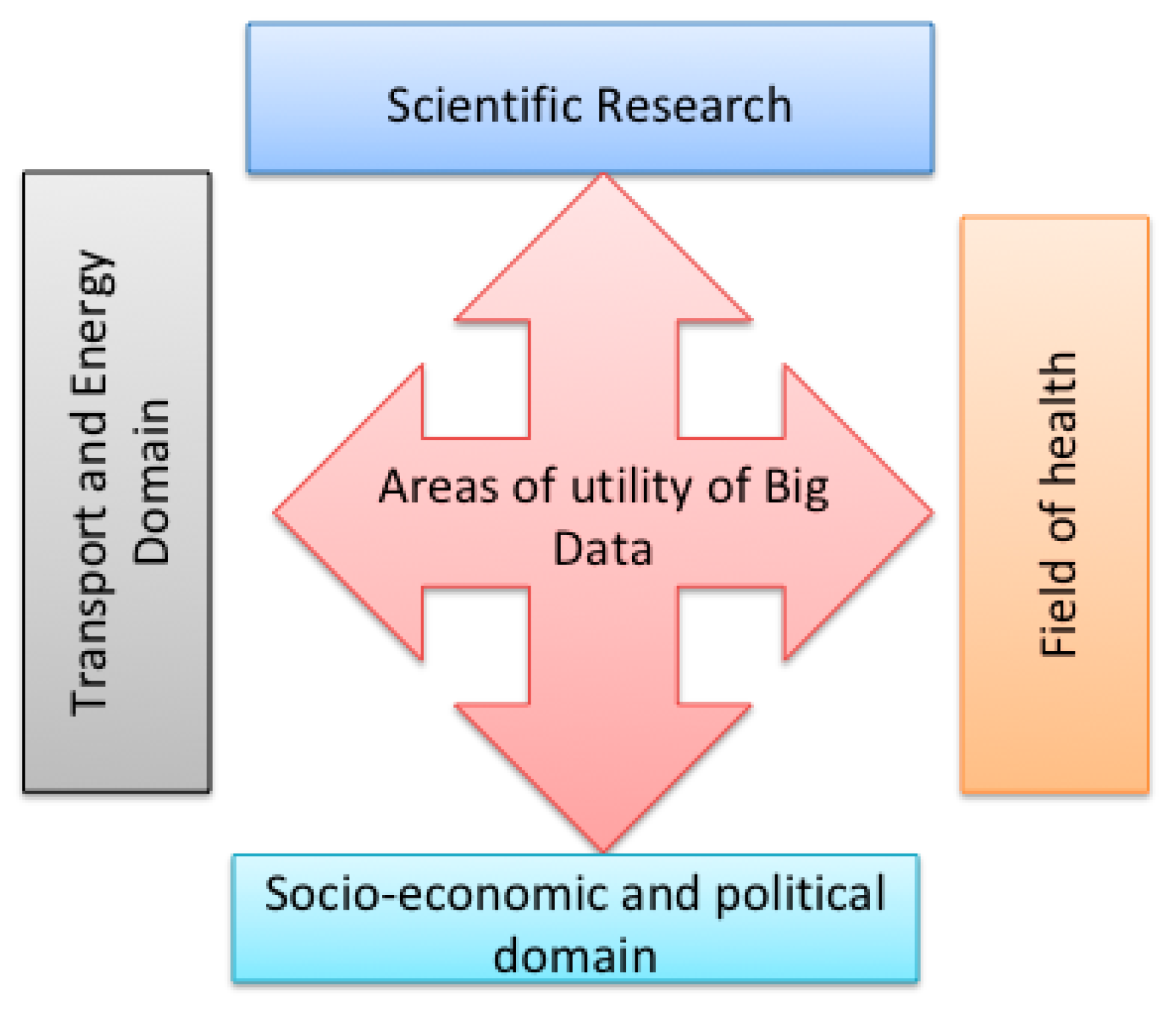
3.4. Areas of Utility of Big Data
3.4.1. Scientific Research
3.4.2. Health
3.4.3. Socioeconomic and Political Domain
3.4.4. Transport and Energy Domain
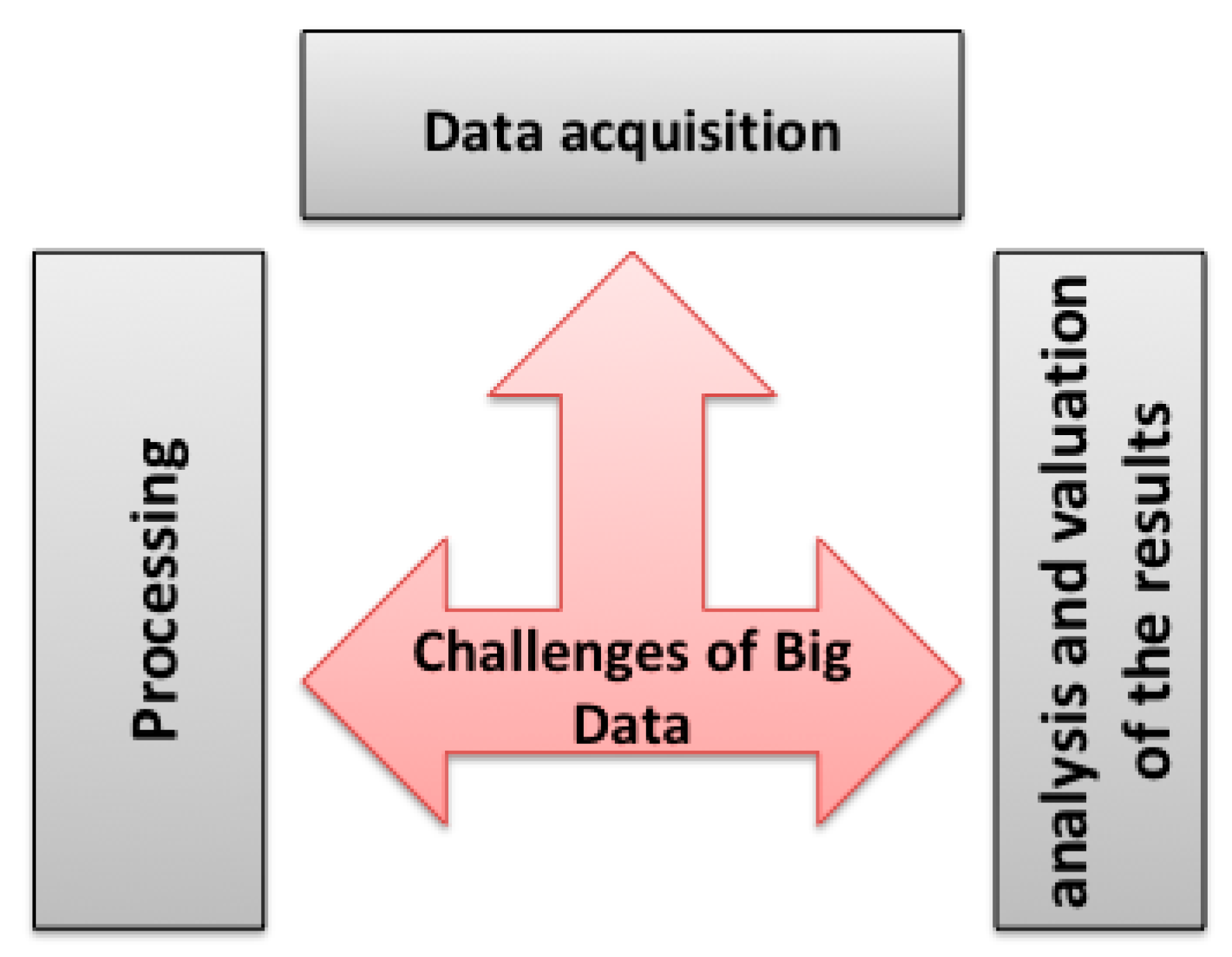
3.5. Big Data Challenges
3.5.1. Data Acquisition and Storage
- Heterogeneity. In general, data-mining algorithms and machine learning expect homogeneous data, and cannot understand the fine distinction between them. IT systems work the fastest if they can store multiple items that are the same size and structure. Thus, Big Data must be carefully structured as a first step in their acquisition process [74].
- Scale. The first thing everyone thinks about Big Data is size. The management of large volumes of data and high growth has been a major problem for many decades. The volume of data is increasing faster than IT resources. Unfortunately, parallel data-processing techniques that were useful in the past for processing data between nodes do not apply directly to intranode parallelism, since the architecture is very different.
- Delay. The larger the dataset to be processed is, the longer it takes to analyze it. Designing a system that effectively treats size is also likely to result in a system capable to more quickly process a given dataset size. However, it is not only this speed that is generally heard when we talk about Velocity in the context of Big Data [75]. There are many situations in which the result of the analysis is immediately required. Given a broad dataset, it is often essential to find elements that meet a specific criterion. The analysis of all the data to find the appropriate elements is obviously impracticable [76].
- Privacy and Security. One of the key value propositions of Big Data is access to data from multiple and diverse domains. Security and privacy play a very important role in Big Data research and technology. In areas such as social media and health information, more data are collected on individuals. It is therefore feared that some organizations will know too much about individuals, developing algorithms that randomize personal data into a large dataset problem [77].
3.5.2. Data Processing
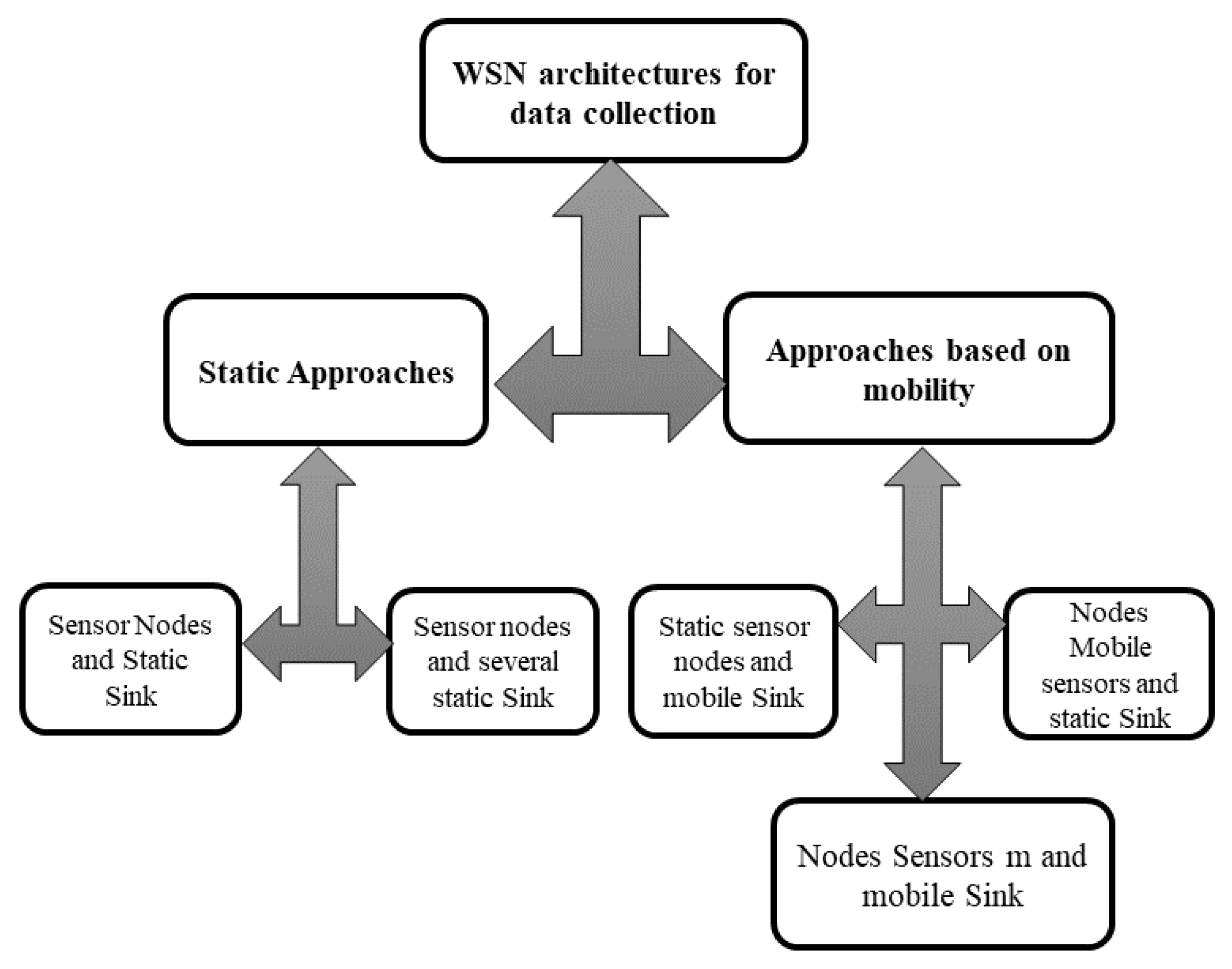
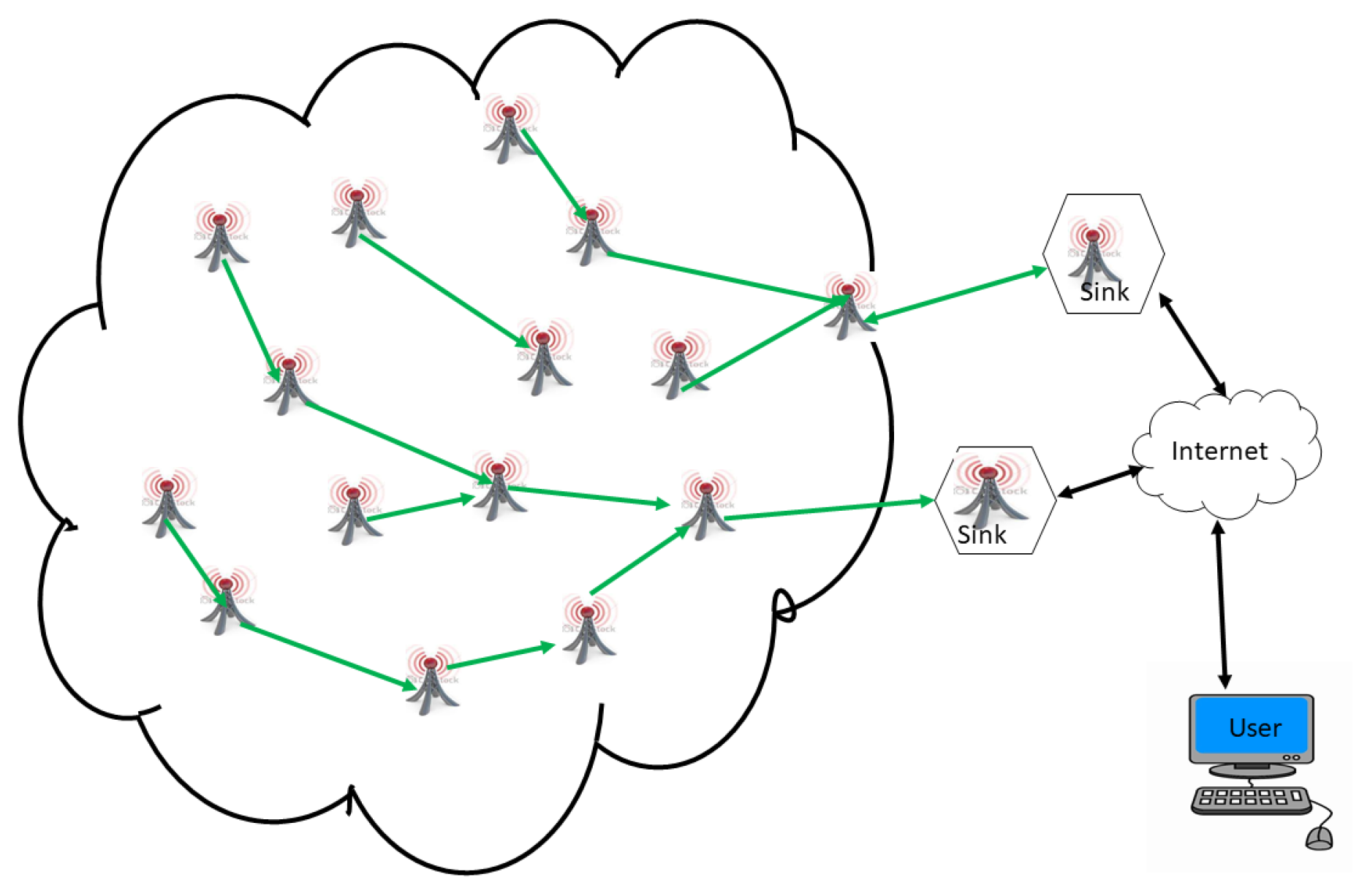
4. Big Data Collection in LS-WSNs
4.1. Static Architectures
4.1.1. Static-Sink and Static-Sensor Architecture
4.1.2. Architecture with Sensor Nodes and Several Static Sinks
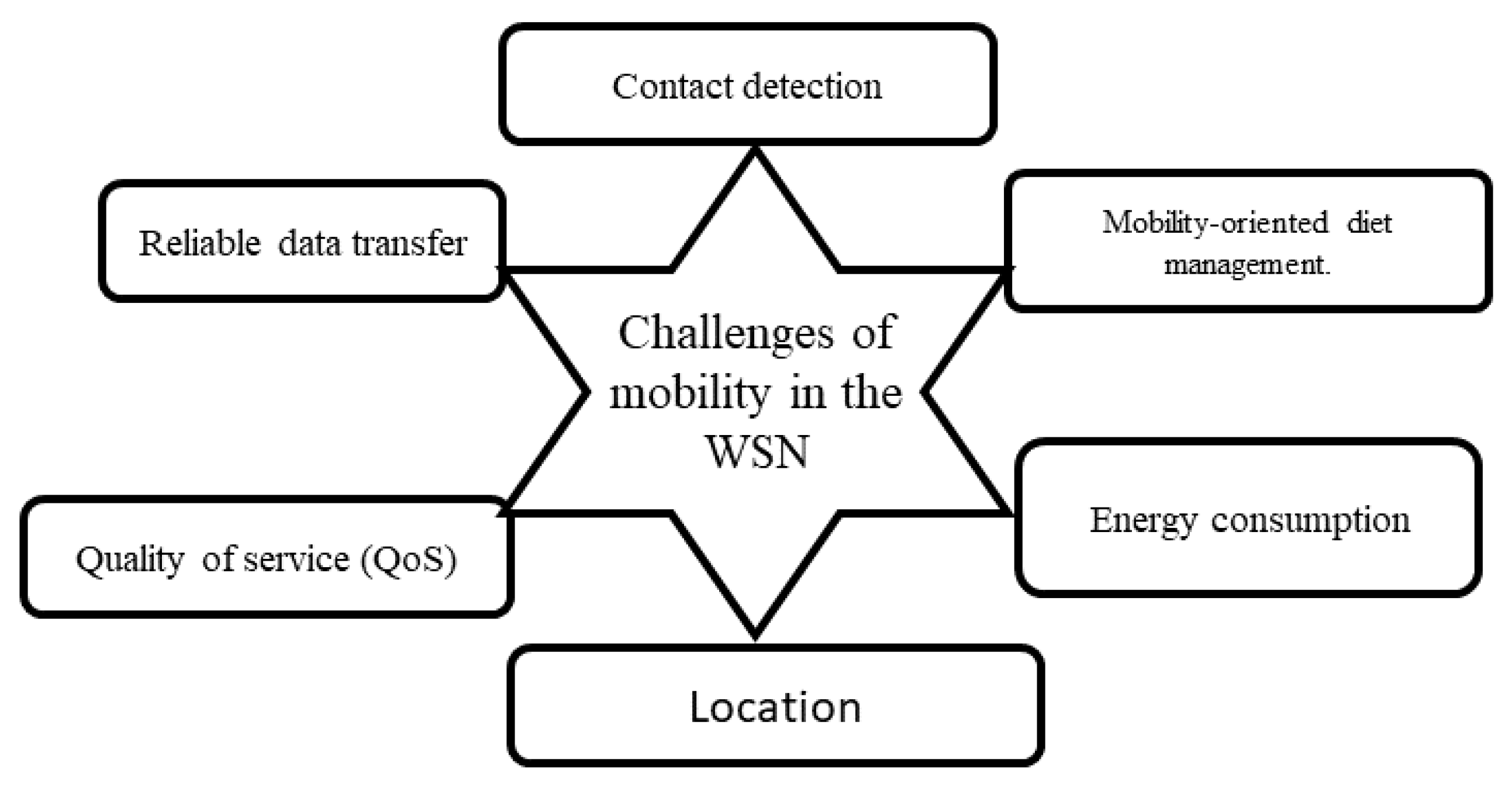
4.2. Architecture Based on Mobility
4.2.1. Static Sink Architecture and Moving Sensor Nodes
4.2.2. Architecture with a Mobile Sink and Static Sensor Nodes
4.2.3. Architecture with a Mobile Sink and Mobile Sensor Nodes
4.2.4. Architecture with Sensors and Multiple Static Sinks
4.2.5. Architecture with Sensors and Multiple Mobile Sinks
4.2.6. Hybrid Architectures
4.3. Comparison of Data-Collection Architectures in the Context of LS-WSNs
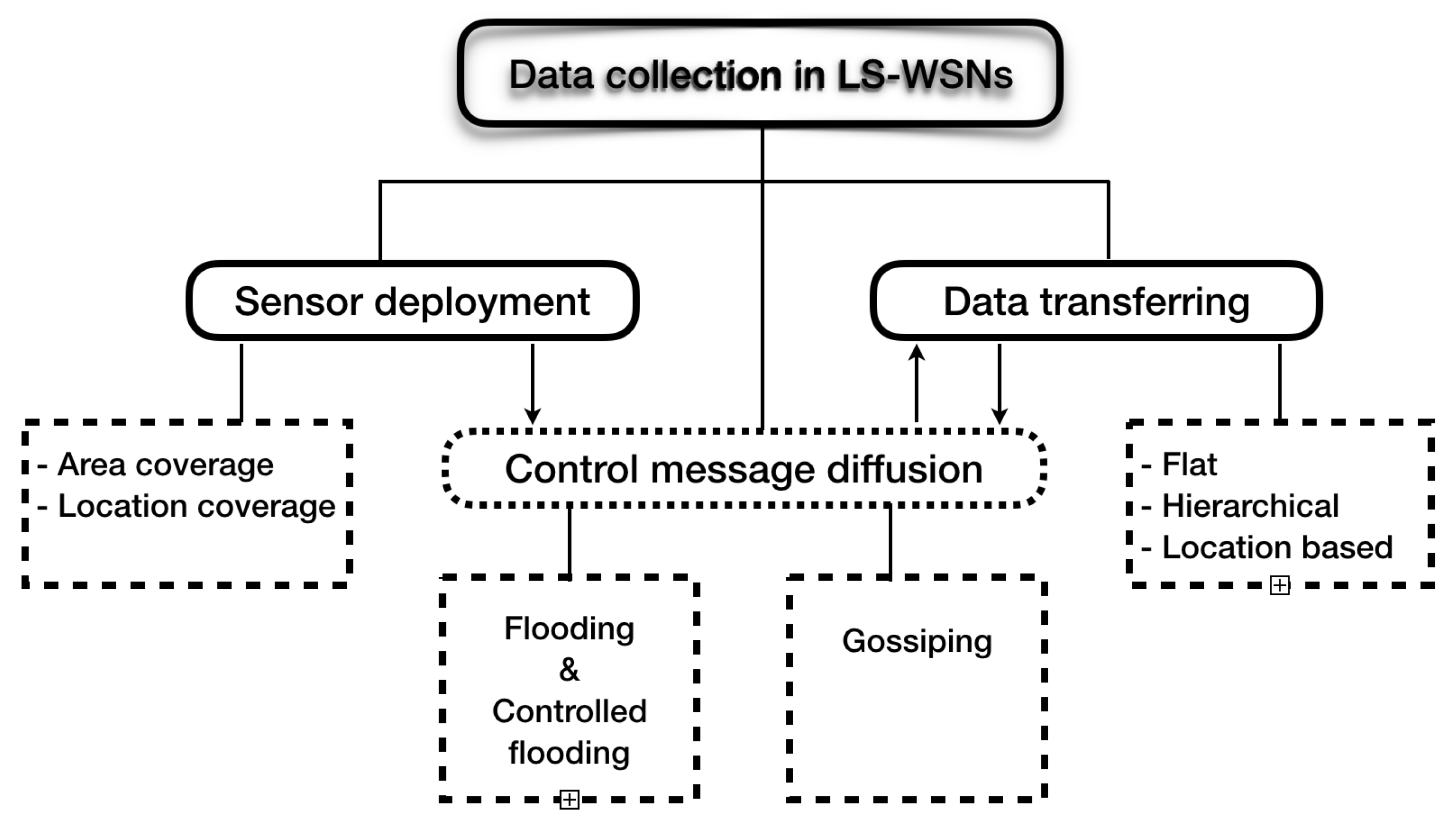
5. Data Transferring in LS-WSNs
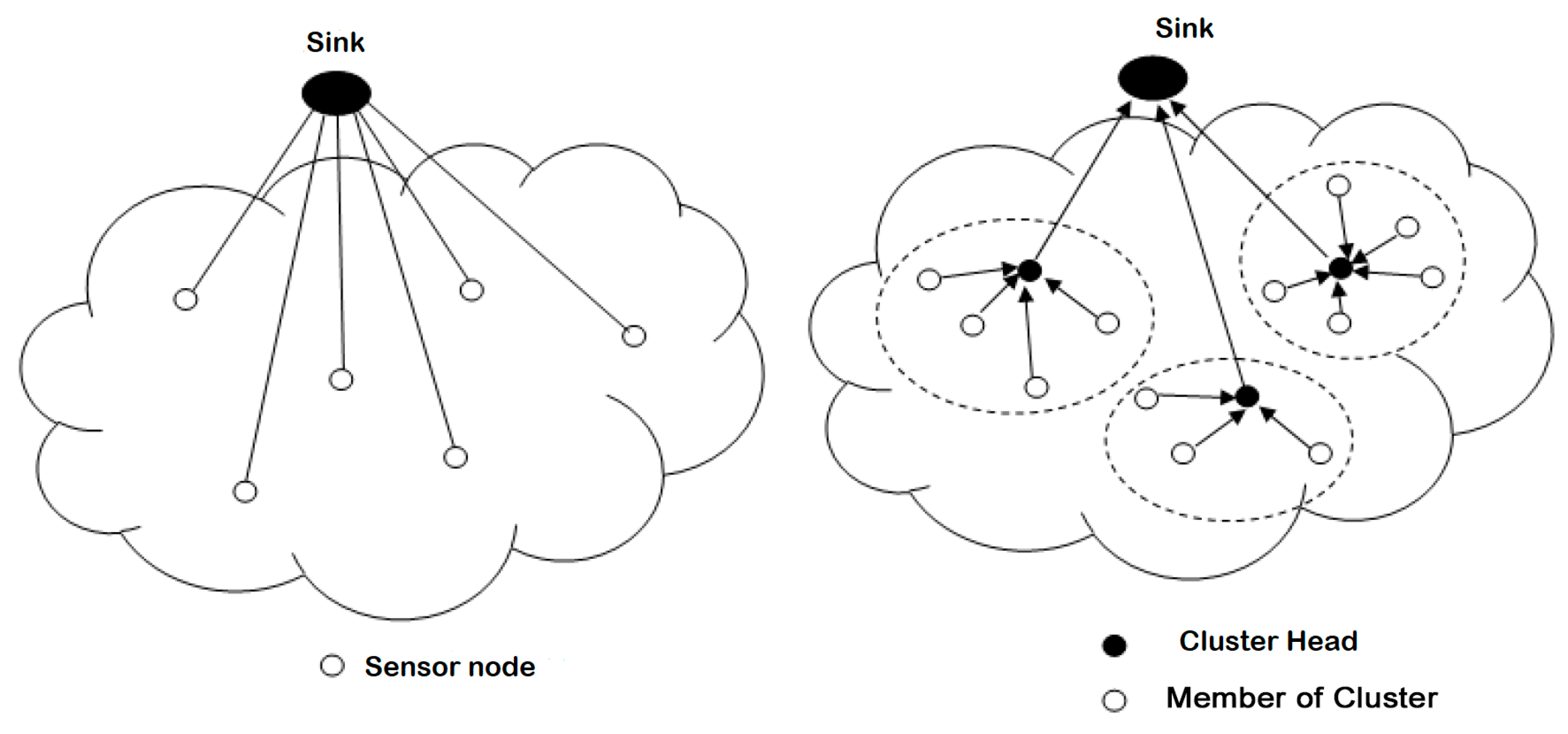
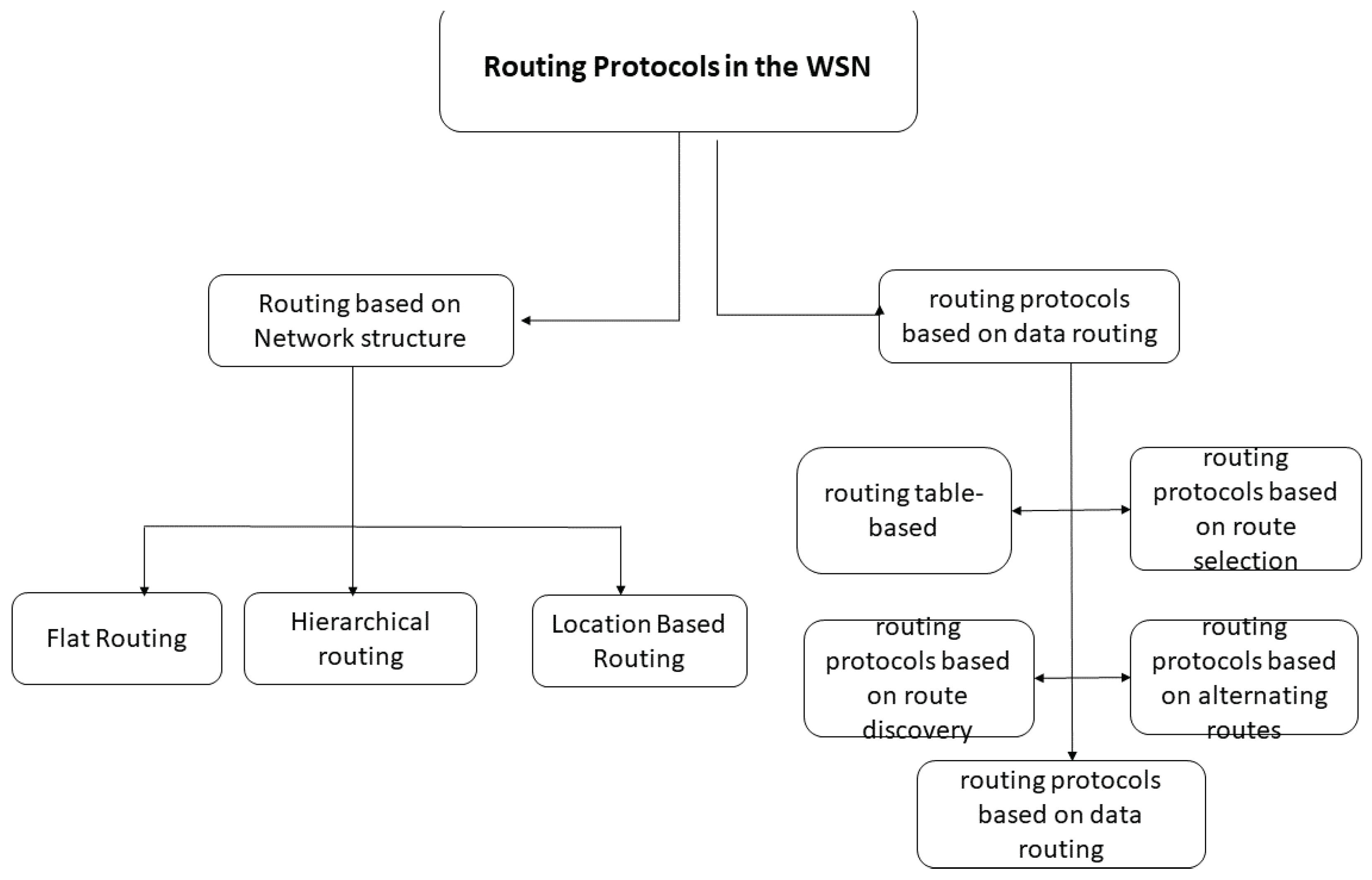
5.1. Network Structure-Based Routing Protocols
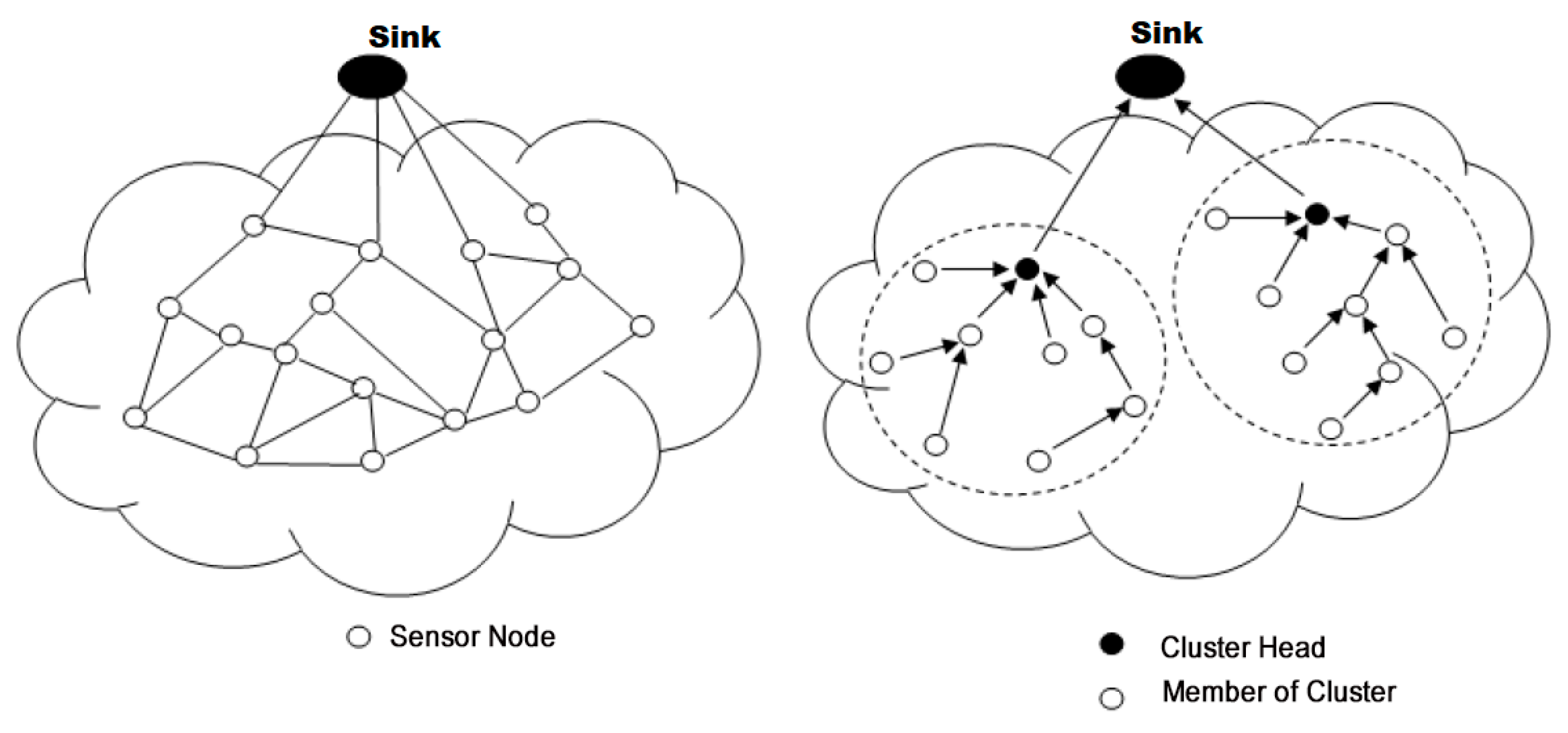
- Flat routing. Called ‘data centric’ as well, all sensor nodes here have the same tasks to perform. This is the first approach used in the routing of data in the WSN. It is based on the collaboration of all the nodes of the network. Data properties are specified by a naming system by attribute (attribute, value) because of the difficulty of assigning a global identifier to each node given their large number. Among their advantages is their simplicity, hence the possibility of establishing communications at no additional cost where each node would only need information from its direct neighbors. The disadvantage is the depletion of the energy resources of the nodes close to the base station because all traffic toward the latter obligatorily passes by them.
- Hierarchical routing. This approach is based on the formation of clusters (common areas) [36,85,100]. The principle is to route the data collected by each node of the cluster to its head of area, the Cluster Head (CH), which, after processing their common parts, forwards them to the next destination (If the CH cannot directly reach the station, basic information is routed to the next zone leader). The advantage is the reduction of communication and energy costs by minimizing the number of messages circulating on the network, since CHs apply aggregate functions on the data of the cluster, which makes it possible to combine them. The disadvantage concerns the size of the network. In addition, as network size increases, the CH election process becomes critical and greedy in resources.
- Location-Based Routing. The identification of the geographic locations of the sensor nodes on the gathering area is of paramount importance for the data-routing mechanisms in the WSN. This location information allows the calculation of sensor positions and the distances between them to build the shortest paths between a source node and its destination. This routing approach is more energy-efficient because it dispenses sensor nodes from using random or probabilistic methods to search for routes [109,110]. In addition, the location of the nodes (and consequently of their regions) makes it possible to only broadcast requests to these regions and to avoid their diffusion in broadcast mode (global diffusion to all the nodes), thus significantly reducing the number of transmissions. The disadvantage is the need to equip sensor nodes with a satellite tracking system, such as GPS, which consumes a lot of energy.
5.2. Feature-Based Routing Protocols
- Routing protocols based on data routing. In this kind of protocol, each sensor node must choose a node of its neighborhood to deliver it the task of conveying these data. This decision is made using different techniques, including table-based routing, broadcasting, and filtering by neighbors, or flooding.
- Routing protocols based on route selection. Route selection is the process of choosing the best route to a sink from the potential routes depending on the constraints of the network and the sensor nodes. Although most protocols only choose a better route (single-path routing), multipath protocols select and save more than one path for different purposes, such as energy, traffic balance, reliability, and robustness. The entities involved in the selection process may include the source sensor node, the intermediate nodes, or the sink node.
- Routing protocols based on route discovery. Each sensor node of a WSN acts as a router and participates in the routing of data to the sink. Many debates and works have discussed when and how many routes each node must maintain in its routing table. Indeed, a node must memorize the roads to reach a sink, or only search and keep track of roads when it has an interest in reaching the sink. As a result, three types of routing protocols are distinguished depending on how routes are maintained in the routing tables. Route discovery is categorized into proactive, reactive, and hybrid routing protocols.
- Routing protocols based on alternating routes. In a WSN, from a sensor node, a routing protocol can maintain a single path that allows it to reach a sink. It can also maintain multiple paths to reach a single destination. We distinguish two classes of protocols: single path and multiple paths.
5.3. Data-Collection Steps in LS-WSNs
6. Challenges of Big Data Collection in LS-WSNs
7. Conclusions
Funding
Acknowledgments
Conflicts of Interest
References
- Networking, C.V. Cisco Global Cloud Index: Forecast and Methodology, 2016–2021 White Paper; Cisco Public: San Jose, CA, USA, 2018. [Google Scholar]
- Collotta, M.; Pau, G.; Talty, T.; Tonguz, O.K. Bluetooth 5: A Concrete Step Forward toward the IoT. IEEE Commun. Mag. 2018, 56, 125–131. [Google Scholar] [CrossRef]
- Puccinelli, D.; Haenggi, M. Wireless sensor networks: Applications and challenges of ubiquitous sensing. IEEE Circuits Syst. Mag. 2005, 5, 19–31. [Google Scholar] [CrossRef]
- Barka, E.; Kerrache, C.; Hussain, R.; Lagraa, N.; Lakas, A.; Bouk, S. A Trusted Lightweight Communication Strategy for Flying Named Data Networking. Sensors 2018, 18, 2683. [Google Scholar] [CrossRef] [PubMed]
- Bello, O.M.; Taiwe, K.D. Mesh node placement in wireless mesh network based on multiobjective evolutionary metaheuristic. Int. J. Auton. Comput. 2017, 2, 231–254. [Google Scholar] [CrossRef]
- Samo, S.D.; Fendji, J.L.E. Evaluation of Energy Consumption of Proactive, Reactive, and Hybrid Routing Protocols in Wireless Mesh Networks Using 802.11 Standards. J. Comput. Commun. 2018, 6, 1. [Google Scholar] [CrossRef]
- Abas, K.; Obraczka, K.; Miller, L. Solar-powered, wireless smart camera network: An IoT solution for outdoor video monitoring. Comput. Commun. 2018, 118, 217–233. [Google Scholar] [CrossRef]
- Dupont, C.; Wussah, A.; Malo, S.; Thiare, O.; Niass, F.; Pham, C.; Dupont, S.; Le Gall, F.; Cousin, P. Low-Cost IoT Solutions for Fish Farmers in Africa. In Proceedings of the IEEE 2018 IST-Africa Week Conference (IST-Africa), Gaborone, Botswana, 9–11 May 2018. [Google Scholar]
- Dieng, O.; Diop, B.; Thiare, O.; Pham, C. A study on IoT solutions for preventing cattle rustling in african context. In Proceedings of the Second International Conference on Internet of things and Cloud Computing, Cambridge, UK, 22–23 March 2017; p. 153. [Google Scholar]
- Ari, A.A.A.; Gueroui, A.; Labraoui, N.; Yenke, B.O. Concepts and evolution of research in the field of wireless sensor networks. Int. J. Comput. Netw. Commun. 2015, 7, 81–98. [Google Scholar]
- Hu, H.; Wen, Y.; Chua, T.S.; Li, X. Toward scalable systems for big data analytics: A technology tutorial. IEEE Access 2014, 2, 652–687. [Google Scholar]
- Ang, K.L.M.; Seng, J.K.P.; Zungeru, A.M. Optimizing energy consumption for big data collection in large-scale wireless sensor networks with mobile collectors. IEEE Syst. J. 2018, 12, 616–626. [Google Scholar] [CrossRef]
- Chen, M.; Mao, S.; Liu, Y. Big data: A survey. Mob. Netw. Appl. 2014, 19, 171–209. [Google Scholar] [CrossRef]
- Hamidouche, R.; Aliouat, Z.; Gueroui, A.M.; Ari, A.A.A.; Louail, L. Classical and bio-inspired mobility in sensor networks for IoT applications. J. Netw. Comput. Appl. 2018, 121, 70–88. [Google Scholar] [CrossRef]
- Hamidouche, R.; Aliouat, Z.; Gueroui, A.M. Genetic Algorithm for Improving the Lifetime and QoS of Wireless Sensor Networks. Wirel. Pers. Commun. 2018, 101, 2313–2348. [Google Scholar] [CrossRef]
- Titouna, C.; Ari, A.A.A.; Moumen, H. FDRA: Fault Detection and Recovery Algorithm for Wireless Sensor Networks. In International Conference on Mobile Web and Intelligent Information Systems; Springer: Cham, Switzerland, 2018; pp. 72–85. [Google Scholar]
- Njoya, A.N.; Thron, C.; Barry, J.; Abdou, W.; Tonye, E.; Konje, N.S.L.; Dipanda, A. Efficient scalable sensor node placement algorithm for fixed target coverage applications of wireless sensor networks. IET Wirel. Sens. Syst. 2017, 7, 44–54. [Google Scholar] [CrossRef]
- Njoya, A.N.; Abdou, W.; Dipanda, A.; Tonye, E. Optimization of sensor deployment using multi-objective evolutionary algorithms. J. Reliab. Intell. Environ. 2016, 2, 209–220. [Google Scholar] [CrossRef]
- Wang, F.; Liu, J. Networked wireless sensor data collection: Issues, challenges, and approaches. IEEE Commun. Surv. Tutor. 2011, 13, 673–687. [Google Scholar] [CrossRef]
- Wu, H.; Li, Y.; Bi, X.; Zhang, L.; Bie, R.; Wang, Y. Joint entropy based learning model for image retrieval. J. Vis. Commun. Image Represent. 2018, 55, 415–423. [Google Scholar] [CrossRef]
- Takaishi, D.; Nishiyama, H.; Kato, N.; Miura, R. Toward energy efficient big data gathering in densely distributed sensor networks. IEEE Trans. Emerg. Top. Comput. 2014, 2, 388–397. [Google Scholar] [CrossRef]
- Rawat, P.; Singh, K.D.; Chaouchi, H.; Bonnin, J.M. Wireless sensor networks: A survey on recent developments and potential synergies. J. Supercomput. 2014, 68, 1–48. [Google Scholar] [CrossRef]
- Bouaziz, M.; Rachedi, A. A survey on mobility management protocols in Wireless Sensor Networks based on 6LoWPAN technology. Comput. Commun. 2016, 74, 3–15. [Google Scholar] [CrossRef]
- Sánchez-García, J.; García-Campos, J.; Arzamendia, M.; Reina, D.; Toral, S.; Gregor, D. A survey on unmanned aerial and aquatic vehicle multi-hop networks: Wireless communications, evaluation tools and applications. Comput. Commun. 2018, 119, 43–65. [Google Scholar] [CrossRef]
- Di Francesco, M.; Das, S.K.; Anastasi, G. Data collection in wireless sensor networks with mobile elements: A survey. ACM Trans. Sens. Netw. (TOSN) 2011, 8, 7. [Google Scholar] [CrossRef]
- Ari, A.A.A.; Damakoa, I.; Gueroui, A.; Titouna, C.; Labraoui, N.; Kaladzavi, G.; Yenké, B.O. Bacterial foraging optimization scheme for mobile sensing in wireless sensor networks. Int. J. Wirel. Inf. Netw. 2017, 24, 254–267. [Google Scholar] [CrossRef]
- Hamidouche, R.; Khentout, M.; Aliouat, Z.; Gueroui, A.M.; Abba Ari, A.A. Sink Mobility Based on Bacterial Foraging Optimization Algorithm. In Proceedings of the Computational Intelligence and Its Applications: 6th IFIP TC 5 International Conference, CIIA 2018, Oran, Algeria, 8–10 May 2018; Springer: Cham, Switzerland, 2018; pp. 352–363. [Google Scholar]
- Wu, M.; Tan, L.; Xiong, N. A structure fidelity approach for big data collection in wireless sensor networks. Sensors 2014, 15, 248–273. [Google Scholar] [CrossRef] [PubMed]
- Ang, L.M.; Seng, K.P.; Zungeru, A.M.; Ijemaru, G.K. Big sensor data systems for smart cities. IEEE Internet Things J. 2017, 4, 1259–1271. [Google Scholar] [CrossRef]
- Mann, P.S.; Singh, S. Improved metaheuristic based energy-efficient clustering protocol for wireless sensor networks. Eng. Appl. Artif. Intell. 2017, 57, 142–152. [Google Scholar] [CrossRef]
- Diongue, D.; Thiare, O. ALARM: An energy aware sleep scheduling algorithm for lifetime maximization in wireless sensor networks. In Proceedings of the 2013 IEEE Symposium on Wireless Technology and Applications (ISWTA), Kuching, Malaysia, 22–25 September 2013; pp. 74–79. [Google Scholar]
- Stankovic, J.; Cao, Q.; Doan, T.; Fang, L.; He, Z.; Kiran, R.; Lin, S.; Son, S.; Stoleru, R.; Wood, A. Wireless sensor networks for in-home healthcare: Potential and challenges. In Proceedings of the High Confidence Medical Device Software and Systems (HCMDSS) Workshop, Philadelphia, PA, USA, 2–3 June 2005; Volume 2005, pp. 1–4. [Google Scholar]
- Akyildiz, I.F.; Su, W.; Sankarasubramaniam, Y.; Cayirci, E. Wireless sensor networks: A survey. Comput. Netw. 2002, 38, 393–422. [Google Scholar] [CrossRef]
- Jiang, F.; Frater, M.; Ling, S.S. A distributed smart routing scheme for terrestrial sensor networks with hybrid Neural Rough Sets. In Proceedings of the 2011 IEEE International Conference on Fuzzy Systems (FUZZ), Taipei, Taiwan, 27–30 June 2011; pp. 2238–2244. [Google Scholar]
- Yu, X.; Wu, P.; Han, W.; Zhang, Z. Overview of wireless underground sensor networks for agriculture. Afr. J. Biotechnol. 2012, 11, 3942–3948. [Google Scholar]
- Ari, A.A.A.; Yenke, B.O.; Labraoui, N.; Damakoa, I.; Gueroui, A. A power efficient cluster-based routing algorithm for wireless sensor networks: Honeybees swarm intelligence based approach. J. Netw. Comput. Appl. 2016, 69, 77–97. [Google Scholar] [CrossRef]
- Fute, E.T.; Tonye, E.; Lauri, F.; Koukam, A. Multi-agent Patrolling: Multi-Objective Approach of the Event Detection by a Mobile Wireless Sensors Network. Int. J. Comput. Appl. 2014, 88, 1–8. [Google Scholar]
- Misra, S.; Reisslein, M.; Xue, G. A survey of multimedia streaming in wireless sensor networks. IEEE Commun. Surv. Tutor. 2008, 10, 18–39. [Google Scholar] [CrossRef]
- Fute, E.T.; Tonye, E. Modelling and self-organizing in mobile wireless sensor networks: Application to fire detection. In International Journal of Applied Information Systems; IJAIS: New York, NY, USA, 2013; Volume 5. [Google Scholar]
- Upadhyay, H.; Mehta, M. Improved APAC algorithm for minimizing delay in wireless sensor network with mobile sink. Int. J. Adv. Comput. Res. 2017, 7, 23. [Google Scholar] [CrossRef]
- Mukherjee, R.; Roy, S.; Das, A. Survey on Data Collection protocols in Wireless Sensor Networks using mobile data collectors. In Proceedings of the IEEE 2015 2nd International Conference on Computing for Sustainable Global Development (INDIACom), New Delhi, India, 11–13 March 2015; pp. 632–636. [Google Scholar]
- Jain, S.; Shah, R.C.; Brunette, W.; Borriello, G.; Roy, S. Exploiting mobility for energy efficient data collection in wireless sensor networks. Mob. Netw. Appl. 2006, 11, 327–339. [Google Scholar] [CrossRef]
- Madden, S.; Franklin, M.J.; Hellerstein, J.M.; Hong, W. TAG: A tiny aggregation service for ad-hoc sensor networks. ACM SIGOPS Oper. Syst. Rev. 2002, 36, 131–146. [Google Scholar] [CrossRef]
- Kaur, G.; Garg, R.M. Energy efficient topologies for wireless sensor networks. Int. J. Distrib. Parallel Syst. 2012, 3, 179. [Google Scholar] [CrossRef]
- Matin, M.A.; Islam, M. Overview of wireless sensor network. In Wireless Sensor Networks-Technology and Protocols; InTech: London, UK, 2012; pp. 1–22. [Google Scholar]
- Akkaya, K.; Younis, M. A survey on routing protocols for wireless sensor networks. Ad Hoc Netw. 2005, 3, 325–349. [Google Scholar] [CrossRef]
- Werner-Allen, G.; Lorincz, K.; Ruiz, M.; Marcillo, O.; Johnson, J.; Lees, J.; Welsh, M. Deploying a wireless sensor network on an active volcano. IEEE Internet Comput. 2006, 10, 18–25. [Google Scholar] [CrossRef]
- Ekici, E.; Gu, Y.; Bozdag, D. Mobility-based communication in wireless sensor networks. IEEE Commun. Mag. 2006, 44, 56–62. [Google Scholar] [CrossRef]
- Ngossaha, J.M.; Ngouna, R.H.; Archimède, B.; Ndjodo, M.F. A simulation model for risk assessment in a smart mobility ecosystem based on the inoperability input-output theory. In Proceedings of the 50th Computer Simulation Conference, Society for Computer Simulation International, Bordeaux, France, 9–12 July 2018; pp. 1–10. [Google Scholar]
- Mfenjou, M.L.; Ari, A.A.A.; Abdou, W.; Spies, F.; Kolyang. Methodology and trends for an intelligent transport system in developing countries. Sustain. Comput. Inform. Syst. 2018, 19, 96–111. [Google Scholar] [CrossRef]
- Tran, D.H.; Yang, J.; Sattler, K.U. Decentralized change detection in wireless sensor network using dft-based synopsis. In Proceedings of the 2011 12th IEEE International Conference on Mobile Data Management (MDM), Lulea, Sweden, 6–9 June 2011; Volume 1, pp. 226–235. [Google Scholar]
- Neves, R.; Della Luna, S.; Marandin, D.; Timm, A.; Gil, V. Report on WSN Applications, Their Requirements, Application-Specific WSN Issues and Evaluation Metrics; European IST NoE CRUISE deliverable IST–User-friendly information society—European Commission: Brussels, Belgium, 2006. [Google Scholar]
- Yick, J.; Mukherjee, B.; Ghosal, D. Wireless sensor network survey. Comput. Netw. 2008, 52, 2292–2330. [Google Scholar] [CrossRef]
- Mainwaring, A.; Culler, D.; Polastre, J.; Szewczyk, R.; Anderson, J. Wireless sensor networks for habitat monitoring. In Proceedings of the 1st ACM international workshop on Wireless sensor Networks and Applications, Atlanta, GA, USA, 28 September 2002; pp. 88–97. [Google Scholar]
- Khedim, F.; Labraoui, N.; Lehsaini, M. Dishonest recommendation attacks in wireless sensor networks: A survey. In Proceedings of the 2015 IEEE 12th International Symposium on Programming and Systems (ISPS), Algiers, Algeria, 28–30 April 2015; pp. 1–10. [Google Scholar]
- Labraoui, N.; Gueroui, M.; Sekhri, L. On-off attacks mitigation against trust systems in wireless sensor networks. In Computer Science and Its Applications; Springer: Cham, Switzerland, 2015; pp. 406–415. [Google Scholar]
- Labraoui, N.; Gueroui, M.; Sekhri, L. A risk-aware reputation-based trust management in wireless sensor networks. Wirel. Pers. Commun. 2016, 87, 1037–1055. [Google Scholar] [CrossRef]
- Labraoui, N.; Gueroui, M.; Aliouat, M. Secure DV?Hop localization scheme against wormhole attacks in wireless sensor networks. Trans. Emerg. Telecommun. Technol. 2012, 23, 303–316. [Google Scholar] [CrossRef]
- Delort, P. Les technologies du Big Data. In Que Sais-je? Presses Universitaires de France: Paris, France, 2015; pp. 48–72. [Google Scholar]
- Agrahari, A.; Rao, D.D. A Review Paper on Big Data: Technologies, Tools and Trends; IRJET: Tamilnadu, India, 2017. [Google Scholar]
- Reimer, A.P.; Madigan, E.A. Veracity in big data: How good is good enough. Health Inform. J. 2018. [Google Scholar] [CrossRef] [PubMed]
- Deloitte. Big Data: Challenges and Success Factors; Deloitte: New York, NY, USA, 2013. [Google Scholar]
- Yin, S.; Kaynak, O. Big data for modern industry: Challenges and trends [point of view]. Proc. IEEE 2015, 103, 143–146. [Google Scholar] [CrossRef]
- Mahrt, M.; Scharkow, M. The value of big data in digital media research. J. Broadcast. Electron. Media 2013, 57, 20–33. [Google Scholar] [CrossRef]
- Wang, Y.; Kung, L.; Byrd, T.A. Big data analytics: Understanding its capabilities and potential benefits for healthcare organizations. Technol. Forecast. Soc. Chang. 2018, 126, 3–13. [Google Scholar] [CrossRef]
- Luo, J.; Wu, M.; Gopukumar, D.; Zhao, Y. Big data application in biomedical research and health care: A literature review. Biomed. Inform. Insights 2016, 8, BII–S31559. [Google Scholar] [CrossRef] [PubMed]
- Madakam, S.; Ramaswamy, R.; Tripathi, S. Internet of Things (IoT): A literature review. J. Comput.Commun. 2015, 3, 164. [Google Scholar] [CrossRef]
- Khan, N.; Yaqoob, I.; Hashem, I.A.T.; Inayat, Z.; Ali, M.; Kamaleldin, W.; Alam, M.; Shiraz, M.; Gani, A. Big data: Survey, technologies, opportunities, and challenges. Sci. World J. 2014, 2014, 712826. [Google Scholar] [CrossRef] [PubMed]
- Raghupathi, W.; Raghupathi, V. Big data analytics in healthcare: Promise and potential. Health Inf. Sci. Syst. 2014, 2, 3. [Google Scholar] [CrossRef] [PubMed]
- Burrows, R.; Savage, M. After the crisis? Big Data and the methodological challenges of empirical sociology. Big Data Soc. 2014, 1. [Google Scholar] [CrossRef]
- Zhou, K.; Fu, C.; Yang, S. Big data driven smart energy management: From big data to big insights. Renew. Sustain. Energy Rev. 2016, 56, 215–225. [Google Scholar] [CrossRef]
- Waller, M.A.; Fawcett, S.E. Data science, predictive analytics, and big data: A revolution that will transform supply chain design and management. J. Bus. Logist. 2013, 34, 77–84. [Google Scholar] [CrossRef]
- Gandhi, K.I.; Sreedhar, S.C. Survey on Big Data: Management and Challenges. Int. J. Comput. Trends Technol. 2015, 20, 33–36. [Google Scholar] [CrossRef]
- Kaisler, S.; Armour, F.; Espinosa, J.A.; Money, W. Big data: Issues and challenges moving forward. In Proceedings of the 2013 46th Hawaii international conference on System sciences (HICSS), Maui, HI, USA, 7–10 January 2013; pp. 995–1004. [Google Scholar]
- Labrinidis, A.; Jagadish, H.V. Challenges and opportunities with big data. Proc. VLDB Endow. 2012, 5, 2032–2033. [Google Scholar] [CrossRef]
- Zhang, Y.; Callan, J.; Minka, T. Novelty and redundancy detection in adaptive filtering. In Proceedings of the 25th Annual International ACM SIGIR Conference on Research and Development in Information Retrieval, Tampere, Finland, 11–15 August 2002; pp. 81–88. [Google Scholar]
- Madden, S. From databases to big data. IEEE Internet Comput. 2012, 16, 4–6. [Google Scholar] [CrossRef]
- Ramírez-Gallego, S.; Fernández, A.; García, S.; Chen, M.; Herrera, F. Big data: Tutorial and guidelines on information and process fusion for analytics algorithms with MapReduce. Inf. Fusion 2018, 42, 51–61. [Google Scholar] [CrossRef]
- Luong, N.C.; Hoang, D.T.; Wang, P.; Niyato, D.; Kim, D.I.; Han, Z. Data collection and wireless communication in Internet of Things (IoT) using economic analysis and pricing models: A survey. IEEE Commun. Surv. Tutor. 2016, 18, 2546–2590. [Google Scholar] [CrossRef]
- Gu, Y.; Ren, F.; Ji, Y.; Li, J. The evolution of sink mobility management in wireless sensor networks: A survey. IEEE Commun. Surv. Tutor. 2016, 18, 507–524. [Google Scholar] [CrossRef]
- Chen, S.; Coolbeth, M.; Dinh, H.; Kim, Y.A.; Wang, B. Data collection with multiple sinks in wireless sensor networks. In International Conference on Wireless Algorithms, Systems, and Applications; Springer: Cham, Switzerland, 2009; pp. 284–294. [Google Scholar]
- Wang, Q.; Guo, S.; Hu, J.; Yang, Y. Spectral partitioning and fuzzy C-means based clustering algorithm for big data wireless sensor networks. EURASIP J. Wirel. Commun. Netw. 2018, 2018, 54. [Google Scholar] [CrossRef]
- Padhy, P.; Martinez, K.; Riddoch, A.; Ong, H.; Hart, J.K. Glacial environment monitoring using sensor networks. In Proceedings of the REALWSN’05 Workshop on Real-World Wireless Sensor Networks, Stockholm, Sweden, 20–21 June 2005; pp. 1–5. [Google Scholar]
- Juang, P.; Oki, H.; Wang, Y.; Martonosi, M.; Peh, L.S.; Rubenstein, D. Energy-efficient computing for wildlife tracking: Design tradeoffs and early experiences with ZebraNet. ACM SIGARCH Comput. Archit. News 2002, 30, 96–107. [Google Scholar] [CrossRef]
- Li, G.; Chen, H.; Peng, S.; Li, X.; Wang, C.; Yu, S.; Yin, P. A Collaborative Data Collection Scheme Based on Optimal Clustering for Wireless Sensor Networks. Sensors 2018, 18, 2487. [Google Scholar] [CrossRef] [PubMed]
- Chakrabarti, A.; Sabharwal, A.; Aazhang, B. Using predictable observer mobility for power efficient design of sensor networks. In Information Processing in Sensor Networks; Springer: Berlin/Heidelberg, Germany, 2003; pp. 129–145. [Google Scholar]
- Kansal, A.; Somasundara, A.A.; Jea, D.D.; Srivastava, M.B.; Estrin, D. Intelligent fluid infrastructure for embedded networks. In Proceedings of the 2nd International Conference on Mobile Systems, Applications, and Services, Boston, MA, USA, 6–9 June 2004; pp. 111–124. [Google Scholar]
- Gao, S.; Zhang, H.; Das, S.K. Efficient data collection in wireless sensor networks with path-constrained mobile sinks. IEEE Trans. Mob. Comput. 2011, 10, 592–608. [Google Scholar] [CrossRef]
- Li, J.; Mohapatra, P. Analytical modeling and mitigation techniques for the energy hole problem in sensor networks. Pervasive Mob. Comput. 2007, 3, 233–254. [Google Scholar] [CrossRef]
- Wang, G.; Cao, G.; La Porta, T.; Zhang, W. Sensor relocation in mobile sensor networks. In Proceedings of the IEEE 24th Annual Joint Conference of the IEEE Computer and Communications Societies, Miami, FL, USA, 13–17 March 2005; Volume 4, pp. 2302–2312. [Google Scholar]
- Sabor, N.; Ahmed, S.M.; Abo-Zahhad, M.; Sasaki, S. ARBIC: An Adjustable Range Based Immune hierarchy Clustering protocol supporting mobility of Wireless Sensor Networks. Pervasive Mob. Comput. 2018, 43, 27–48. [Google Scholar] [CrossRef]
- Sharma, S.; Bansal, R.K.; Bansal, S. Issues and challenges in wireless sensor networks. In Proceedings of the 2013 International Conference on Machine Intelligence and Research Advancement (ICMIRA), Katra, India, 21–23 December 2013; pp. 58–62. [Google Scholar]
- Bendjeddou, A.; Ghoualmi, N.; Pham, C. A new method for prolonging network lifetime and maintaining the connectivity in wireless sensor network through controlling the transmission power. Int. J. Embed. Real-Time Commun. Syst. (IJERTCS) 2014, 5, 1–14. [Google Scholar] [CrossRef]
- Derdour, Y.; Kechar, B.; Khelfi, F. The Impact of the Mobile Element on Performance Improvement in Wireless Sensor Network. Procedia Comput. Sci. 2014, 32, 261–268. [Google Scholar] [CrossRef]
- Handcock, R.N.; Swain, D.L.; Bishop-Hurley, G.J.; Patison, K.P.; Wark, T.; Valencia, P.; Corke, P.; O’Neill, C.J. Monitoring animal behaviour and environmental interactions using wireless sensor networks, GPS collars and satellite remote sensing. Sensors 2009, 9, 3586–3603. [Google Scholar] [CrossRef] [PubMed]
- Huang, J.H.; Amjad, S.; Mishra, S. Cenwits: A sensor-based loosely coupled search and rescue system using witnesses. In Proceedings of the 3rd International Conference on Embedded Networked Sensor Systems, San Diego, CA, USA, 2–4 November 2005; pp. 180–191. [Google Scholar]
- Irish, A.E.; Terence, S.; Immaculate, J. Efficient Data Collection Using Dynamic Mobile Sink in Wireless Sensor Network. In Wireless Communication Networks and Internet of Things; Springer: Singapore, 2019; pp. 141–149. [Google Scholar]
- Zhong, P.; Ruan, F. An energy efficient multiple mobile sinks based routing algorithm for wireless sensor networks. In IOP Conference Series: Materials Science and Engineering; IOP Publishing: Bristol, UK, 2018; Volume 323, p. 012029. [Google Scholar]
- Kumar, P.; Amgoth, T.; Annavarapu, C.S.R. ACO-based mobile sink path determination for wireless sensor networks under non-uniform data constraints. Appl. Soft Comput. 2018, 69, 528–540. [Google Scholar]
- Ari, A.A.A.; Labraoui, N.; Yenké, B.O.; Gueroui, A. Clustering algorithm for wireless sensor networks: The honeybee swarms nest-sites selection process based approach. Int. J. Sens. Netw. 2018, 27, 1–13. [Google Scholar] [CrossRef]
- Zhang, L.; Ye, Q.; Cheng, J.; Jiang, H.; Wang, Y.; Zhou, R.; Zhao, P. Fault-tolerant scheduling for data collection in wireless sensor networks. In Proceedings of the 2012 IEEE Global Communications Conference (GLOBECOM), Anaheim, CA, USA, 3–7 December 2012; pp. 5345–5349. [Google Scholar]
- Khan, M.I.; Gansterer, W.N.; Haring, G. Static vs. mobile sink: The influence of basic parameters on energy efficiency in wireless sensor networks. Comput. Commun. 2013, 36, 965–978. [Google Scholar] [CrossRef] [PubMed]
- Zungeru, A.M.; Ang, L.M.; Seng, K.P. Termite-hill: Performance optimized swarm intelligence based routing algorithm for wireless sensor networks. J. Netw. Comput. Appl. 2012, 35, 1901–1917. [Google Scholar] [CrossRef]
- Jea, D.; Somasundara, A.; Srivastava, M. Multiple controlled mobile elements (data mules) for data collection in sensor networks. In International Conference on Distributed Computing in Sensor Systems; Springer: Berlin/Heidelberg, Germany, 2005; pp. 244–257. [Google Scholar]
- Khedim, F.; Labraoui, N.; Ari, A.A.A. A cognitive chronometry strategy associated with a revised cloud model to deal with the dishonest recommendations attacks in wireless sensor networks. J. Netw. Comput. Appl. 2018, 123, 42–56. [Google Scholar] [CrossRef]
- Ye, F.; Luo, H.; Cheng, J.; Lu, S.; Zhang, L. A two-tier data dissemination model for large-scale wireless sensor networks. In Proceedings of the 8th Annual International Conference on Mobile Computing and Networking, Atlanta, GA, USA, 23–28 September 2002; pp. 148–159. [Google Scholar]
- Zungeru, A.M.; Ang, L.M.; Seng, K.P. Classical and swarm intelligence based routing protocols for wireless sensor networks: A survey and comparison. J. Netw. Comput. Appl. 2012, 35, 1508–1536. [Google Scholar] [CrossRef]
- Bhushan, B.; Sahoo, G. Routing Protocols in Wireless Sensor Networks. In Computational Intelligence in Sensor Networks; Springer: Berlin, Germany, 2019; pp. 215–248. [Google Scholar]
- Li, C.; Zhang, H.; Hao, B.; Li, J. A survey on routing protocols for large-scale wireless sensor networks. Sensors 2011, 11, 3498–3526. [Google Scholar] [CrossRef] [PubMed]
- Maqbool, B.B.; Peer, M. Classification of current routing protocols for ad hoc networks—A review. Int. J. Comput. Appl. 2010, 7, 26–32. [Google Scholar] [CrossRef]
- Diop, B.; Diongue, D.; Thiaré, O. Greedy algorithms for target coverage lifetime management problem in wireless sensor networks. Int. J. Control Autom. 2015, 8, 232–250. [Google Scholar] [CrossRef]
- Cao, B.; Zhao, J.; Yang, P.; Lv, Z.G.; Liu, X.; Min, G. 3D Multi-Objective Deployment of an Industrial Wireless Sensor Network for Maritime Applications Utilizing a Distributed Parallel Algorithm. IEEE Trans. Ind. Inform. 2018. [Google Scholar] [CrossRef]
- Gao, S.; Dai, X.; Hang, Y.; Guo, Y.; Ji, Q. Airborne Wireless Sensor Networks for Airplane Monitoring System. Wirel. Commun. Mob. Comput. 2018, 2018, 6025825. [Google Scholar] [CrossRef]
- Zhan, C.; Zeng, Y.; Zhang, R. Energy-efficient data collection in UAV enabled wireless sensor network. IEEE Wirel. Commun. Lett. 2018, 7, 328–331. [Google Scholar] [CrossRef]
- Zhang, P.; Wang, S.; Guo, K.; Wang, J. A secure data collection scheme based on compressive sensing in wireless sensor networks. Ad Hoc Netw. 2018, 70, 73–84. [Google Scholar] [CrossRef]
- Chatzigiannakis, I.; Kinalis, A.; Nikoletseas, S. Efficient data propagation strategies in wireless sensor networks using a single mobile sink. Comput. Commun. 2008, 31, 896–914. [Google Scholar] [CrossRef]
- Basagni, S.; Carosi, A.; Melachrinoudis, E.; Petrioli, C.; Wang, Z.M. Controlled sink mobility for prolonging wireless sensor networks lifetime. Wirel. Netw. 2008, 14, 831–858. [Google Scholar] [CrossRef]
- Bagaa, M.; Challal, Y.; Ksentini, A.; Derhab, A.; Badache, N. Data aggregation scheduling algorithms in wireless sensor networks: Solutions and challenges. IEEE Commun. Surv. Tutor. 2014, 16, 1339–1368. [Google Scholar] [CrossRef]
- Yogeswari, R.; Subathra, V. A survey on efficient data collection in wireless sensor networks. Int. J. Innov. Res. Comput. Commun. Eng. 2013, 1, 2181. [Google Scholar]
- Taleb, A.A.; Alhmiedat, T.; Hassan, O.A.H.; Turab, N.M. A survey of sink mobility models for wireless sensor networks. J. Emerg. Trends Comput. Inf. Sci. 2013, 4, 679–687. [Google Scholar]
- Hsu, T.C.; Hong, Y.W.P.; Wang, T.Y. Optimized random deployment of energy harvesting sensors for field reconstruction in analog and digital forwarding systems. IEEE Trans. Signal Process. 2015, 63, 5194–5209. [Google Scholar] [CrossRef]
- Liang, W.; Luo, J.; Xu, X. Prolonging network lifetime via a controlled mobile sink in wireless sensor networks. In Proceedings of the 2010 IEEE Global Telecommunications Conference GLOBECOM 2010, Miami, FL, USA, 6–10 December 2010; pp. 1–6. [Google Scholar]
| Source | Production |
|---|---|
| YouTube | - Users upload 400 h of new videos each minute of every day. |
| - Each month, more than 1 billion unique users have access to YouTube. | |
| - Users watch more than 4 million videos every minute. | |
| - Users watch 5.97 billion hours of videos each day. | |
| - Users click the Like button on more than 4 million posts every minute. | |
| - Every day, 5.75 billion likes are registered. | |
| - Every day, 4.3 billion messages are posted. | |
| - 100 terabytes of data are uploaded daily. | |
| - Over 2 billion monthly active users in 2017. | |
| - The site has been translated into 70 languages. | |
| - 656 million tweets every day. | |
| - The site has over 355 million of active users per month. | |
| - 7.1 million active users per month. | |
| - 34.7 billion shares of active photos per month. | |
| - 3.25 billion hours of video are watched in one month. | |
| Foursquare | - This site is used by 45 million of people worldwide. |
| - This site receives over 5 billion check-ins per day. | |
| - Every minute, 571 new websites are launched. | |
| Google+ | - 1 billion accounts have been created. |
| - The site had over 5.2 billion daily searches in 2017. | |
| - Every day, 25 petabytes are processed. | |
| Apple | - Approximately 47,000 applications are downloaded per minute. |
| Amazon | - USD373 million in sales every day in 2017. |
| Linkedln | - 2.1 million groups have been created. |
| - Every day in 2017, 269 billion emails have been sent. | |
| Mobile Device Data | - In 2017, 8 exabytes of data have been created on mobile devices. |
| - In 2017, there were 3.394 billion mobile Internet users. | |
| Data created by the Internet of Things (IoT) | - 2.5 quintillion bytes of data are created every day by mobile devices, WSNs, Smart TVs, cars, etc. |
| Architecture | Reliability | Number of Sinks | Energy Consumption | Latency | Lifespan | Scalability |
|---|---|---|---|---|---|---|
| Static sensors and sinks | ||||||
| Li et al. (2018) [85] | high | many | low | medium | low | yes |
| Ari et al. (2018) [100] | high | 1 | low | medium | medium | yes |
| Wang et al. (2018) [82] | medium | 1 | medium | high | medium | yes |
| Ari et al. (2016) [36] | high | many | low | medium | low | yes |
| Zhang et al. (2012) [101] | low | 1 | strong | high | low | difficult |
| Di Francesco et al. (2011) [25] | medium | many | medium | low | medium | yes |
| Chen et al. (2009) [81] | high | many | medium | low | high | yes |
| Werner et al. (2006) [47] | low | 1 | strong | high | low | difficult |
| Mobile sensors and static sink | ||||||
| Irish et al. (2019) [97] | medium | many | low | medium | no | |
| Handcock et al. (2009) [95] | medium | many | low | medium | no | |
| Huang et al. (2005) [96] | medium | 1 | medium | high | medium | no |
| Mobile sink and static sensor nodes | ||||||
| Sabor et al. (2018) [91] | medium | many | medium | medium | high | yes |
| Kumar et al. (2018) [99] | medium | 1 | medium | high | medium | yes |
| Zhong and Ruan (2018) [98] | low | many | medium | medium | medium | no |
| Ari et al. (2017) [26] | high | 1 | medium | medium | high | yes |
| Khan et al. (2013) [102] | high | 1 | medium | medium | medium | yes |
| Zungeru et al. (2012) [103] | high | many | medium | low | medium | yes |
| Jea et al. (2005) [104] | low | 1 | medium | medium | high | no |
| Juang et al. (2002) [84] | low | 1 | medium | low | medium | no |
| Hybrid | ||||||
| Juang et al. (2002) [84] | depends | weak | no |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Djedouboum, A.C.; Abba Ari, A.A.; Gueroui, A.M.; Mohamadou, A.; Aliouat, Z. Big Data Collection in Large-Scale Wireless Sensor Networks. Sensors 2018, 18, 4474. https://doi.org/10.3390/s18124474
Djedouboum AC, Abba Ari AA, Gueroui AM, Mohamadou A, Aliouat Z. Big Data Collection in Large-Scale Wireless Sensor Networks. Sensors. 2018; 18(12):4474. https://doi.org/10.3390/s18124474
Chicago/Turabian StyleDjedouboum, Asside Christian, Ado Adamou Abba Ari, Abdelhak Mourad Gueroui, Alidou Mohamadou, and Zibouda Aliouat. 2018. "Big Data Collection in Large-Scale Wireless Sensor Networks" Sensors 18, no. 12: 4474. https://doi.org/10.3390/s18124474
APA StyleDjedouboum, A. C., Abba Ari, A. A., Gueroui, A. M., Mohamadou, A., & Aliouat, Z. (2018). Big Data Collection in Large-Scale Wireless Sensor Networks. Sensors, 18(12), 4474. https://doi.org/10.3390/s18124474





