Estimation of Distribution Algorithm for Resource Allocation in Green Cooperative Cognitive Radio Sensor Networks
Abstract
: Due to the rapid increase in the usage and demand of wireless sensor networks (WSN), the limited frequency spectrum available for WSN applications will be extremely crowded in the near future. More sensor devices also mean more recharging/replacement of batteries, which will cause significant impact on the global carbon footprint. In this paper, we propose a relay-assisted cognitive radio sensor network (CRSN) that allocates communication resources in an environmentally friendly manner. We use shared band amplify and forward relaying for cooperative communication in the proposed CRSN. We present a multi-objective optimization architecture for resource allocation in a green cooperative cognitive radio sensor network (GC-CRSN). The proposed multi-objective framework jointly performs relay assignment and power allocation in GC-CRSN, while optimizing two conflicting objectives. The first objective is to maximize the total throughput, and the second objective is to minimize the total transmission power of CRSN. The proposed relay assignment and power allocation problem is a non-convex mixed-integer non-linear optimization problem (NC-MINLP), which is generally non-deterministic polynomial-time (NP)-hard. We introduce a hybrid heuristic algorithm for this problem. The hybrid heuristic includes an estimation-of-distribution algorithm (EDA) for performing power allocation and iterative greedy schemes for constraint satisfaction and relay assignment. We analyze the throughput and power consumption tradeoff in GC-CRSN. A detailed analysis of the performance of the proposed algorithm is presented with the simulation results.1. Introduction
Wireless sensor networks (WSN) play an important role in many industrial [1], health [2] and body monitoring systems [3,4], seismic vibration sensing [5], ad-hoc systems [6] and spectrum sensing [7] applications. Almost all modern applications and services require some form of sensors. Due to the rapid increase in WSN applications and services, in the future, the limited frequency spectrum available for WSN applications will be extremely crowded [8]. With the rapid growth and dense deployment of WSN, in the field of information and communication technologies (ICTs) they play a significant role on the global environment [9]. According to the International Telecommunication Union report [10], the primary sources of greenhouse gases are electricity generation, transport vehicles, buildings, electronic waste (e.g., batteries, small electric cells, etc.) and agricultural by-products. A vast portion of electricity is generated with thermal- or coal-operated turbines. The process of electricity generation is a major contributor to the emissions of green house gases. With the rapid growth and demand of WSN, future WSNs' will face three major challenges: (1) the wireless spectrum availability, (2) the demand for high data rate transmission and (3) the reduction in greenhouse gases to cope with global warming.
A large portion of green house gases is composed of carbon dioxide (CO2) emissions. For WSN, the term green refers to an energy-efficient and a low carbon deployment and operation. For reducing green house gases, particularly carbon dioxide emissions, an energy-efficient resource allocation plays a significant role and has a direct impact on the lifecycle of WSN. The lifecycle of WSN is shown in Figure 1. WSN are composed of the following phases: sensor network design, manufacturing, transportation, deployment and recycling. Each phase has its role in global warming—e.g., sensor network design and the manufacturing phase require highly sophisticated computing machines that not only use ample amounts of electricity, but also produce electronic waste. Both the generation of electricity and electronic waste has a direct impact on global warming. The sensor network application, e.g., multiple tracking, traffic monitoring, spectrum sensing or any other commercial/military application, requires a dense deployment of sensors. In the deployment, maintenance and recycling phases, the use of transportation is the major source of global warming.
An energy efficient-design of WSN can reduce its contribution towards global warming. Research in green ICTs will enable the wireless system designers to develop and design cellular, ad-hoc and WSN systems that will achieve user data rate demands with minimum power usage and, thus, contribute to reduction of green houses gases [11]. A combination of the intelligent design of future WSN with emerging wireless technologies, such as cooperative communication and cognitive radio, can help in coping with the crowded spectrum, the demand for a high data rate and global warming issues. Cognitive radio is an interesting concept for solving the problem of spectrum availability by reusing the under-utilized licensed frequency bands [12]. Formally, a cognitive radio is defined as [12], “a radio that changes its transmitter parameters based on the interaction with its environment”. The cognitive radio has been mainly proposed to improve the spectrum utilization by allowing (unlicensed) secondary users (SUs) to use under-utilized licensed frequency bands. The IEEE 802.22 standard for Wireless Regional Area Network (WRAN) addresses the cognitive radio technology by allowing access to white spaces in the licensed TV band. In North America, the frequency range for the IEEE 802.22 standard will be 54–862 MHz, while the 41–910 MHz band will be used in the international standard. In cognitive radio networks, licensed users and unlicensed users are known as primary and secondary users, respectively. In [13–20], the authors use cognitive radio technology for wireless sensor networks. A detailed architecture, topologies and potential applications of cognitive radio sensor networks (CRSNs) are presented in [17]. The potential applications include indoor sensing, multimedia, multi-class heterogeneous sensing, body area networks and real-time surveillance.
In the context of environmentally friendly cognitive radio sensor network, cooperative communication can help in reducing the total transmission power and, thus, reducing the CO2 emissions. The relays play an important role in many real-life wireless sensor network applications [21–26]. Experimental results and WSN testbeds for cooperative communication also provide insight into the effect of relays on the WSN lifetime. In [21], the authors experimentally show the performance of the amplify and forward scheme in an orthogonal frequency-division multiplexing (OFDM)-based system. The results show that the amplify and forward scheme is highly beneficial for power-aware wireless sensor networks. In [22,23], the authors investigate the effect of relays in terrestrial and underground WSN. In a terrestrial WSN, reliable communication in a dense environment is very important. Terrestrial sensor nodes must be able to effectively communicate data back to the base station. Underground WSNs consist of a number of sensor nodes buried underground or in a cave or mine used to monitor underground conditions. Additional sink nodes are located above ground to relay information from the sensor nodes to the base station. The authors show that with limited battery power (which cannot be recharged, due to geographical constraint) in terrestrial and underground sensor nodes, energy (battery life) can be conserved with the use of relays, a short transmission range, in-network data aggregation, eliminating data redundancy, minimizing delays and using low duty-cycle operations. A dual-hop energy-efficient cooperative spectrum sensing scheme with amplify-and-forward relaying in CRSN is proposed in [7]. In [4], the authors presented a relay-assisted human monitoring system in a body area network that uses 802.15.3/802.15.4 for its monitoring application. The performance analysis of dual-hop relaying in CRSN is described in [27]. In [28], the authors presented spectrum sensing and communication protocols for a dual-hop sensor relay network operating in the VHF-UHF band. Information theoretic data gathering and the effect of relaying in CRSN are described in [29]. In [30], a cognitive dual-hop relaying base sensing-transmission protocol is proposed. In [31], the authors presented an optimal solution for source-sum-power minimization in multi-sensor single-relay networks. Subspace-based cooperative spectrum sensing and correlation-based sensing for CRSN were proposed in [18] and [32], respectively.
A relay-assisted WSN for volcanic monitoring is investigated in [24]. The challenges of a WSN application for volcanic data collection include reliable event detection, efficient data collection, high data rates and sparse deployment of nodes. In the proposed WSN, each sensor node is a T-mote sky device equipped with an external omni-directional antenna, a seismometer, a microphone and a custom hardware interface board. Some of the sensor nodes are equipped with a single axis Geospace Industrial GS-11 Geophone with a corner frequency of 4.5 Hz, while the other two sensor nodes carried triaxial Geospace Industries GS-1 seismometers with corner frequencies of 1 Hz. The custom hardware interface board was designed with four Texas Instruments AD7710 analog to digital converters to integrate with the T-mote sky devices. Each sensor node draws power from a pair of alkaline D-cell batteries. Sensor nodes are placed approximately 200 to 400 meters apart from each other. Sensor nodes relay data to a gateway node. The gateway node, connected to a long-distance Free- Wave radio modem, transmits the collected data to the base station. The authors inspected the data for three weeks and observed that the network sensed 230 eruptions and other volcanic events. The authors also investigated the performance of relays in volcanic events. A three-level wireless sensor network for oil well health monitoring is proposed in [26]. Relays are used to transfer the data from one level to the other levels. An amplify and forward base linear WSN to increase the coverage is proposed in [25]. In [33], the authors present relay scheduling in a time-slotted source relay destination system, where a sensor (the source) has the option to have another sensor (the relay) help transmit its data to the destination. From an energy efficiency perspective, it is shown by the authors that the source may achieve the same bit error rate (BER) for a lower transmission power if it uses a relay, as compared to a direct transmission.
In sensor networks, the transmission power dissipated by a sender node to transmit each bit of data to a receiver node is directly dependent on the distance between them. This use of multi-hop communication may reduce overall energy consumption; some nodes can be overloaded and drain out their energy more quickly (and die), as compared to some other nodes in the network. This may produce an undesirable effect on the functionality of the networks, even causing the network to become inoperable. The use of multiple relays that convey the same data with low power can reduce the chances of WSN failure. The major challenge is how to assign multiple relays efficiently that will increase the throughput of WSN and reduce the power consumption. One open research question of CRSN is the per-hop throughput optimization. Increasing the number of hops will increase the delay, complexity, deployment and transportation cost [34].
1.1. Contributions and Organization
In this paper, we investigate dual-hop CRSN that jointly maximizes the throughput and minimizes the total transmission power by assigning multiple relays to the users. In the future, we will investigate the optimal number of hops in CRSN to jointly maximize the throughput and minimize the total transmission power (or minimize the CO2 emissions). We use a combination of shared-band non-regenerative amplify and forward relaying and cognitive radio to solve the problem of the crowded spectrum, the demand for a high data rate and global warming.
Data rate maximization and power minimization are two conflicting objectives. Determining the optimal set of decision variables for a single objective, e.g., CO2 emissions minimization, can result in a non-optimal set with respect to other objectives, e.g., sum-capacity (throughput) maximization. In our formulation, we use the normalized weighted sum method (WSM) to combine these conflicting objectives. In WSM, the weight of each objective is proportional to its importance, placed for decision-making. A WSM [35] without normalization would result in a biased fitness function—e.g., if the value of one objective function is in the range [0, 1] and the value of second objective is in the range [0, x] (where 1 < x ≤ ∞), then the second objective produces bias in the weighted fitness function. In this work, we normalize all the objective values within the range [0, 1]. We formulate our problem in a way that the range of the combined objective function is always within 0 and 1.
According to the best knowledge of the authors, there is no joint multiple relay assignment and power allocation scheme in the literature that deals with the analysis and optimization of the energy efficiency in a shared band multi-user cognitive radio system. The motivation of this work is to fill the gap, especially important for future green radio communications, with the aim of analyzing the shared-band multiple relay assignment and power allocation problem that maximizes the data rate and minimizes the CO2 emissions. The main contributions of this paper are summarized as follows:
We propose a multi-objective optimization framework that jointly exploits the crowded spectrum, the demand for a high data rate and global warming with the help of relay-assisted GC-CRSN. The proposed multi-objective framework jointly performs multiple relay assignment and power allocation in GC-CRSN, while optimizing two conflicting objectives. The first objective is to maximize the total throughput, and the second objective is to minimize the total transmission power of GC-CRSN.
For multiple relay assignment, we use a shared-band amplify and forward protocol. We also drive an upper bound on the data rate of the shared band amplify and forward protocol. This upper bound is useful for normalization in multi-objective optimization.
The proposed joint multiple relay assignment and power allocation problem is a non-convex mixed-integer non-linear optimization problem (NC-MINLP), which is generally NP-hard. We introduce a hybrid heuristic algorithm for this problem. The hybrid heuristic is a combination of the estimation-of-distribution algorithm (EDA) for performing power allocation and an iterative greedy algorithm for constraint satisfaction and relay assignment.
In addition to applying the EDA to the constrained multi-objective optimization problem for GC-CRSN, we also propose a modification in the EDA that greatly improves its performance.
A detailed analysis of the performance of the proposed algorithm is presented with the simulation results.
We use A, a and a to represent matrix, vector and an element of a vector, respectively. When ai ≥ 0 for all components, i, of a vector, a, we use a ≥ 0. Table 1 presents the summary of notations and symbols used in this paper. The rest of the paper is organized as follows. The system model is presented in Section 2. In Section 3, we present our EDA and its improved version. Simulation results are presented in Section 4.
2. System Model and Problem Formulation
We consider a two-hop wireless sensor network with one transmitter node (source), K receiver nodes (also known as secondary users/nodes), L relay nodes and M primary users/nodes. Each relay, transmitter, and receiver is equipped with a single antenna. We denote by , the channel from the source to the lth relay, , the channel from the lth relay to the kth secondary user, , the channel from the source to the mth primary user, and , the channel from the lth relay to the mth primary user. We denote by pl, the lth relay's transmission power; is the maximum power of the lth relay, , the source power in the kth user band, and Ps, the maximum source power, i.e., . In our system model, each user will receive the data on a separate frequency band. Each relay will transmit and receive in the same frequency band.
We consider a half-duplex shared band amplify and forward (AF) protocol in which each symbol is transmitted in two time slots; in the first time slot, by the source, and in the second time slot, by the relays. In the first time slot, the signal received by the lth relay (after listening to the kth SU's band) can be written as , where complex-valued s represents the transmitted symbol and Zl represents the complex-valued white Gaussian noise at the lth relay. The symbol value, s, E(|s|2) = 1 and are the power spectral density of the noise Zl. The noise power, N, in watts, in each SU band can be written as , where W is the bandwidth of each SU band [36]. In the second time slot, the relays amplify the received signal and re-transmit the amplified signal. The channel capacity of the kth user for shared band, AF, is [37]:
Our first objective is to maximize the sum-rate capacity, . To normalize the first objective between 0 and 1, we will divide the sum-rate capacity with its upper bound, .
Lemma 1. The ecision variable-free upper bound of Equation (1) is .
Proof. It is easy to see that Ck in Equation (1) is an increasing function of the source power. We can set the source power to its maximum transmission power, Ps. We will get an upper bound as:
Applying Cauchy-Schwartz inequality, we will get:
Mathematically, we can write the normalized sum-rate as:
The second objective is to reduce the carbon footprint or CO2 emissions. The CO2 emissions are measured in grams. If P is the power used in the transmission and X is a constant in grams/watt, then the product of P and X (i.e., PX) represents the CO2 emissions in grams. The value of X is different for different types of material (fuel) used for electricity generation. There are three major sources of fuel for electricity generation. These fuels are oil, gas and coal. The value of X for lignite/brown coal, natural gas, crude oil and diesel oil is 940, 370, 640 and 670 grams/watt, respectively [11]. We define by , the CO2 emissions due to the lth relay, and , the CO2 emissions due to the source transmission power in the kth user band. We will normalize the CO2 emissions objective function with , where and . We can write the objective of CO2 emissions as:
The joint objective of the GC-CRSN problem is to maximize the data-rate—i.e., F1—and minimize the CO2 emissions—i.e., F2. For joint optimization, we need to transform the objectives, F1 and F2, into a joint minimization (or maximization) objective. Since both objectives are normalized and bounded between 0 and 1, we can make the joint minimization objective as:
Using Equation (7), we can write the multi-objective optimization for GC-CRSN as:
In OP1, the constraint, C1, assures that a relay can only be assigned to one secondary user; C2 and C3 are the power constraints. The constraints, C3, ensures that if the lth relay is not assigned to any secondary user, then the transmission power of the lth relay should be zero. Constraints, C4 and C5, are the interference constraints. The objective function in OP1 is bounded by zero and one. The formulation in OP1 is a multi-objective non-convex mixed-integer non-linear programming problem, which is generally NP-hard. In the next section, we will present a low-complexity hybrid estimation-of-distribution algorithm (EDA) for the GC-CRSN multi-objective optimization problem.
| Algorithm 1 Pseudo code for a typical EDA. | |
| 1: | Initialize the population with uniform probability distribution |
| 2: | while (true) do |
| 3: | Evaluate the population |
| 4: | Rank the population according to fitness |
| 5: | Select the best individuals |
| 6: | Estimate the probability distribution from best selected individuals |
| 7: | Sample the probability model to generate new population |
| 8: | if Termination Criterion Satisfied then |
| 9: | break |
| 10: | end if |
| 11: | end while |
3. Hybrid EDA Solution for the GC-CRSN Problem
In this section, we will present a hybrid scheme to solve the GC-CRSN multi-objective problem as given in OP1. The proposed scheme is a combination of an evolutionary estimation-of-distribution algorithm for power allocation and an iterative greedy scheme for relay assignment. The iterative scheme also ensures the feasibility of the optimization solution.
Evolutionary algorithms (EAs) in general have been often used to solve multi-objective optimization problems. EAs are inspired by the theory of biological evolution. The candidate solutions to a multi-objective optimization problem are represented as individuals in the population. In EAs, the objective function value of a candidate solution indicates the fitness of the individual, which is associated with the concept of natural selection [38]. Unlike other EAs, such as the genetic algorithm (GA), in EDA, the individuals are generated without the crossover and mutation operators. Instead, in EDA, a new population is generated based on a probability distribution, which is estimated from the best-selected individuals of the previous iterations [39].
Algorithm 1 presents a pseudo code of a typical evolutionary EDA. At the start of the EDA algorithm, the population is generated by sampling the uniform probability distribution. After getting the population, the algorithm evaluates each individual in the population and ranks the population according to the fitness of each individual. Then, the algorithm selects the best individual from the ranked population with the help of the probability of selection. These selected individuals are used to estimate the new probability distribution for the next iteration. The algorithm again samples the probability model to generate the new population. The algorithm continues its execution until some predefined termination criterion is satisfied. In the next section, we will describe EDA for the GC-CRSN problem.
3.1. EDA for GC-CRSN Problem
In the implementation of EDA for the optimization problem in OP1, each individual can be designated by an (L + K)-dimensional real-valued vector. First, L-dimensions are for relay powers, and the next K dimensions are for source power. We denote by Δt, the population at the tth iteration, and |Δt| denotes its cardinality, ηt, the set of best candidate solutions selected from set |Δt| at the tth iteration, and ρs is the selection probability. The EDA selects ρs|Δt | individuals from the set | Δt | to make up the set ηt. In our implementation of EDA, each individual represents the transmission power of the relays and source. We denote by a row vector, P = (p1, p2,⋯, pL, pL+1,⋯, pL+k), as an individual in the population, where pi, i = 1,2,⋯, L is the relay power vector and pi, i = L + 1, L + 2,⋯, L + K is the source power vector. The transmission power of the each relay and source is bounded by WLow and WHigh, where WLow and WHigh are the lower and upper limit of the EDA search window.
In each iteration, the EDA maintains a population of individuals. Population Δt can be specified by the following | Δt| × (L + K) matrix:
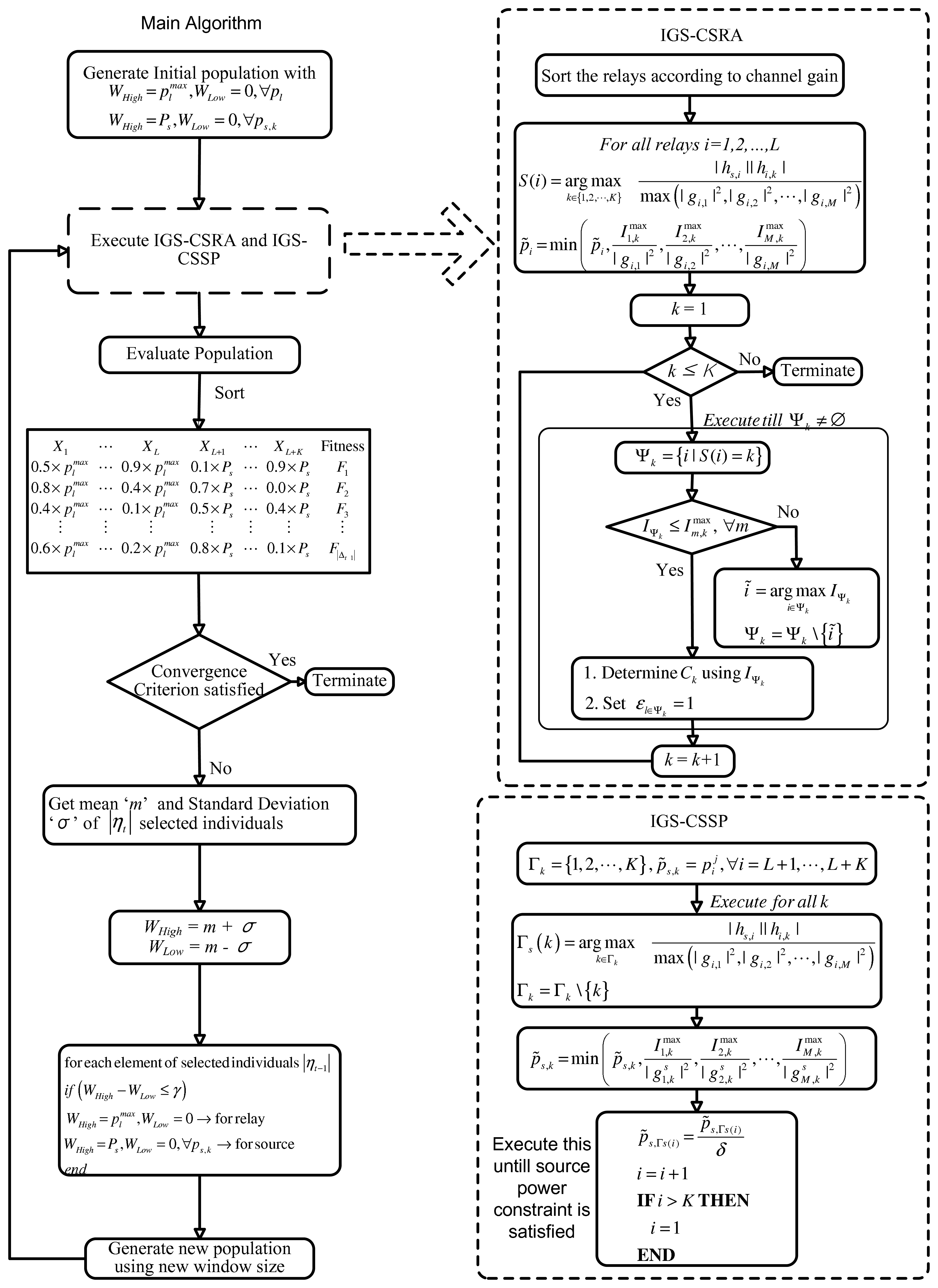
Each row of the matrix, ΛEDA, represent an individual. There are |Δt| individuals in the population, and each individual has L + K elements. A flow diagram of the EDA algorithm is shown in Figure 2. The EDA applied to the OP1 problem can be described in the following steps: Step 0: Generate an initial population, Δ0. Each element of matrix, ΛEDA, is obtained from the following formula:
- Step 1:
Evaluate the individuals in the current population, Δt−1, according to the fitness function, f(). For OP1, we use the function as described in Equation (7) as the fitness function—i.e., F = w1 (1 − F1) + w2F2. The best fitness function in any iteration is the function with the minimum value. Sort the candidate solutions (individuals in the current population) according to their fitness orders.
- Step 2:
Rank the candidate solutions (individuals in the current population) according to their fitness orders.
- Step 3:
In this step, the algorithm determines the assignment variable, , for each individual heuristically. Step 1 does not guarantee a feasible solution. Feasibility check and constraint satisfaction are also performed in step 3.
We propose an iterative greedy scheme for constraint satisfaction and relay assignment (IGS-CSRA). The IGS-CSRA ensures that the constraints C1, C3 and C5 are satisfied. We also propose an iterative algorithm for the source power such that constraints C2 and C4 are satisfied. We call this method the iterative greedy scheme for constraint satisfaction of source power (IGS-CSSP). The IGS-CSRA and IGS-CSSP are shown in Figure 2 and described in Sections 3.2 and 3.3. At the end of this step, the algorithm has a population, which comprises individuals with feasible relay and source power levels and the associated assignment variables ε.
- Step 4:
If the convergence criterion (e.g., number of iterations) is satisfied, then terminate; else, continue.
- Step 5:
Select the best |ηt−1| = ρs |Δt−1| candidate solutions (individuals) from the current population, Δt−1. This selected population is used to compute the mean and standard deviation of the selected individuals.
- Step 6:
Determine the mean, ‘m’, and standard deviation, σ. Based on these estimates of ‘m’ and σ, update the search window bounds, WLow and WHigh, as WLow = m-σ and WHigh = m+σ.
- Step 7:
Generate new |ηt−1| individuals on the basis of this new estimated WLow and WHigh using Equation (10). Combine these newly generated |ηt−1| individuals with members of ηl−1 to form a new population, Δl.
- Step 8:
Go to step 1 and repeat the steps.
From a practical point of view, the following observations and suggestions can help in implementing the proposed EDA for relay assignment and power allocation in a green cooperative cognitive radio sensor network. A good sensing mechanism is inevitable for a cognitive radio that will add robustness to the system. We also need optimal parameter settings of EDA for different geographical regions. A good estimate of the initial population of EDA can also increase its convergence rate towards good solutions. This increase in convergence rate eventually decreases the computational complexity of the central controller. Now, we will explain iterative greedy schemes that jointly assign relays and ensure the feasibility of the solution.
3.2. Iterative Greedy Scheme for Constraint Satisfaction and Relay Assignment (IGS-CSRA)
In this section, we present an iterative greedy scheme for constraint satisfaction and relay (IGS-CSRA). The IGS-CSRA scheme will be executed on each EDA individual in the population. IGS-CSRA illustrates the relay assignment for the EDA individual indexed by . We denote by , i = 1,⋯, L, the ith relay's power level of the jth individual in the population. The proposed algorithm has two stages. In the first stage, based on the channel conditions, relays are assigned to the secondary users without satisfying the interference constraint. In the second stage, the algorithm performs final assignment under the constraint that interference to the primary users is satisfied.
For developing this greedy algorithm, we can view the product of the channel from the ith relay to the kth secondary user and the channel from the source to the ith relay as profit taken from investing one unit of transmission power to relay i. We also view the channel from the ith relay to its primary users as loss. In particular, our algorithm views max(|gi,1|2, |gi,2|2,⋯, |gi,M|2) as loss incurred from investing unit transmission power to relay i.
- Stage 1:
In this stage, the algorithm assigns each relay to the secondary user that gives the maximum profit to loss ratio. The profit is secondary users channel gain—i.e., |hs,i| |hi,k|—and loss is the maximum channel gain from the secondary user to the primary users—i.e., max(|gi,1|2, |gi,2|2,⋯, |gi,M|2).
Mathematically, for each relay i, the algorithm temporarily assigns a secondary user:
where S is an L-dimensional vector that stores this assignment. At the end of Stage 1, relays are assigned to the secondary users with the power pi˜, i = 1,⋯, L.Note that the relays' power levels randomly generated by the EDA algorithm can violate the constraint of limited interference to the primary users. In the next stage, the algorithm refines the relay assignment done in Stage 1 and adjusts the power level of each relay, so that interference to the primary users is satisfied.
- Stage 2:
At the start of the second stage, the algorithm starts adjusting the relays' power levels if there is a violation of the primary users' interference constraint. First, the algorithm examines for each relay i whether its transmission power would still violate any interference constraint, even if all other relays' power level were set to zero. If pi˜ violates any of the interference constraint, , even under the assumption that other relays' transmission power levels are all set to 0, then the algorithm first makes the following adjustment:
With this power adjustment, each user individually guarantees constraint satisfaction of the primary users' interference constraint. After the power adjustment, the algorithm iterates over the secondary users and completes the assignment of relays.
At the kth iteration, the algorithm determines the set of relays, Ψkthat are assigned to the kth secondary user in Stage 1. Then, the algorithm checks whether the relays in the set Ψk satisfy the interference constraint at all the primary users. If the relays in the set, Ψk, violate the interference constraint at any primary user; then the algorithm iteratively removes the relay from the set, Ψk, that causes maximum interference to the primary users. Mathematically, this determines the relay with the highest interference from the set, Ψk, as:
This relay removal process continues until the relays in the set, Ψk, satisfy the interference constraint. When the algorithm has a set of relays that satisfy the interference constraint, then the algorithm determines the capacity of the kth user and it sets εl∈Ψk = 1.
The algorithm executes till all the secondary users get their assigned relays. In the next subsection, we will present the iterative greedy scheme and constraint satisfaction for source power.
3.3. Iterative Greedy Scheme and Constraint Satisfaction for Source Power (IGS-CSSP)
Now, we will describe IGS-CSSP. We denote by , ∀i = L+ 1, L+ 2,⋯, L + K, the source power level at the kth user band in the jth sample drawn by the EDA. We denote by Γs, a vector that will be used for user indices, Γk, a set of users, and δ, a power control factor. The power control factor is used for source power adjustment. This adjustment will be done iteratively until all the interference constraints related to the source power are satisfied. The proposed IGS-CSSP is also a two-stage algorithm.
- Stage 1:
In the first stage, users are ranked according to their channel conditions. Similar to the IGS-CSRA, the maximum profit to loss ratio criterion is used to rank the users. The profit is secondary users channel gain, i.e., |hs,i| |hi,k|, and loss is the maximum channel gain from the secondary user to the primary users, i.e., max(|gi,1|2, |gi,2|2,⋯, |gi,M|2). Mathematically:
In the next stage, the power of each user will adjusted according to their ranks.
- Stage 2:
At the start of the second stage, the algorithm starts adjusting the source power levels if there is a violation of the primary users' interference constraint, using the expression:
After source power adjustment with the interference constraint, the algorithm verifies the power constraint. If the source power constraint is not satisfied, then the algorithm adjusts the source power using power control factor, δ, till the constraint is satisfied. The user with the worst channel condition is reduced first using the power control factor, δ. This process will be executed for all users till we get a feasible solution.
At the end of the algorithm, we shall have a feasible solution. Since, we are using the half-duplex amplify and forward protocol, both IGS-CSRA and IGS-CSSP will execute independently.
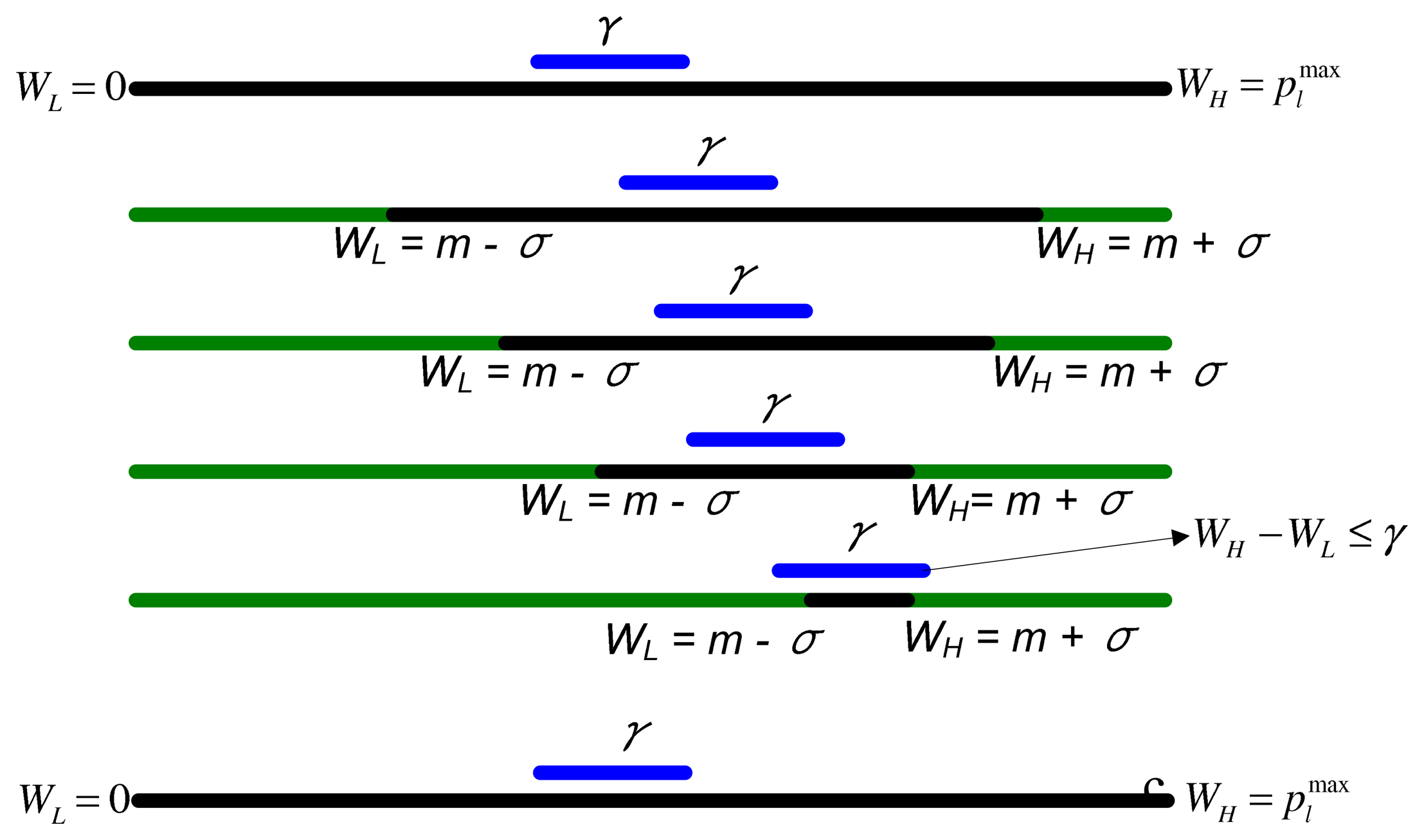
3.4. Modified EDA (MEDA)
During the execution of EDA, the difference between the search window bounds, WLow and WHigh, may diminish as the iterations proceeds. This may cause the EDA to get stuck in a local search space and result in premature convergence. The premature convergence may occur if the difference between WLow and WHigh diminishes to an extremely small value. In that case, at every future iteration, the algorithm will generate nearly the same power levels. In this section, we will propose a modification in the traditional EDA algorithm that can improve the EDA's performance. The modification includes the introduction of thresholds in EDA to avoid premature convergence. We name this algorithm the Modified EDA (MEDA).
We suggest restoring the WLow and WHigh to their initial values ( WLow = 0, for relay powers and WLow = 0, WHigh= Ps for source power) when the difference between WLow and WHigh is less than a pre-specified threshold, γ, i.e.:
| if (WHigh − WLow ≤ γ) then |
| WLow = 0,WHigh = → for relays |
| WLow = 0,WHigh = Ps → for source |
| end if |
The above steps are illustrated in Figure 3. In the next section, we present some experimental results, which show the effect of threshold on the performance of EDA.
4. Numerical Results
In this section, we present simulation results to demonstrate the performance of the proposed EDA and MEDA. The impact of network parameters (e.g., number of SUs, number of relays) is also investigated.
4.1. Simulation Setup and Common Parameters
In all the simulations, the channels between source, relays and destinations have independent complex Gaussian distribution. Some common parameter values for simulation are shown in Table 2. In all simulations, the channel gain, h, is modeled as [40]:
For each PU, there is a PU protection area, wherein the strengths of the cognitive radio signals must be constrained. We define as R, the radius of the protected circular area for each individual PU. Given a distance, dm, between the SU base station and the mth PU and the radius, Rm, of the protected circular area of the mth PU, the channel from the source to the mth PU in the kth SU band is given as:
We compare the results of EDA and MEDA with the standard continuous genetic algorithm (GA) [38]. The EDA, MEDA and GA use IGS-CSSP and IGS-CSRA for constraint satisfaction. We will use the the word “non-green communication” when we set w1 = 1 and w2 = 0. In all the simulation results, we set the (M)EDA/GA parameters as (Δt, ρs, ITer) = (20, 0.5, 1000), where Δt, ρs, ITer are the population, selection probability and maximum iteration, respectively.
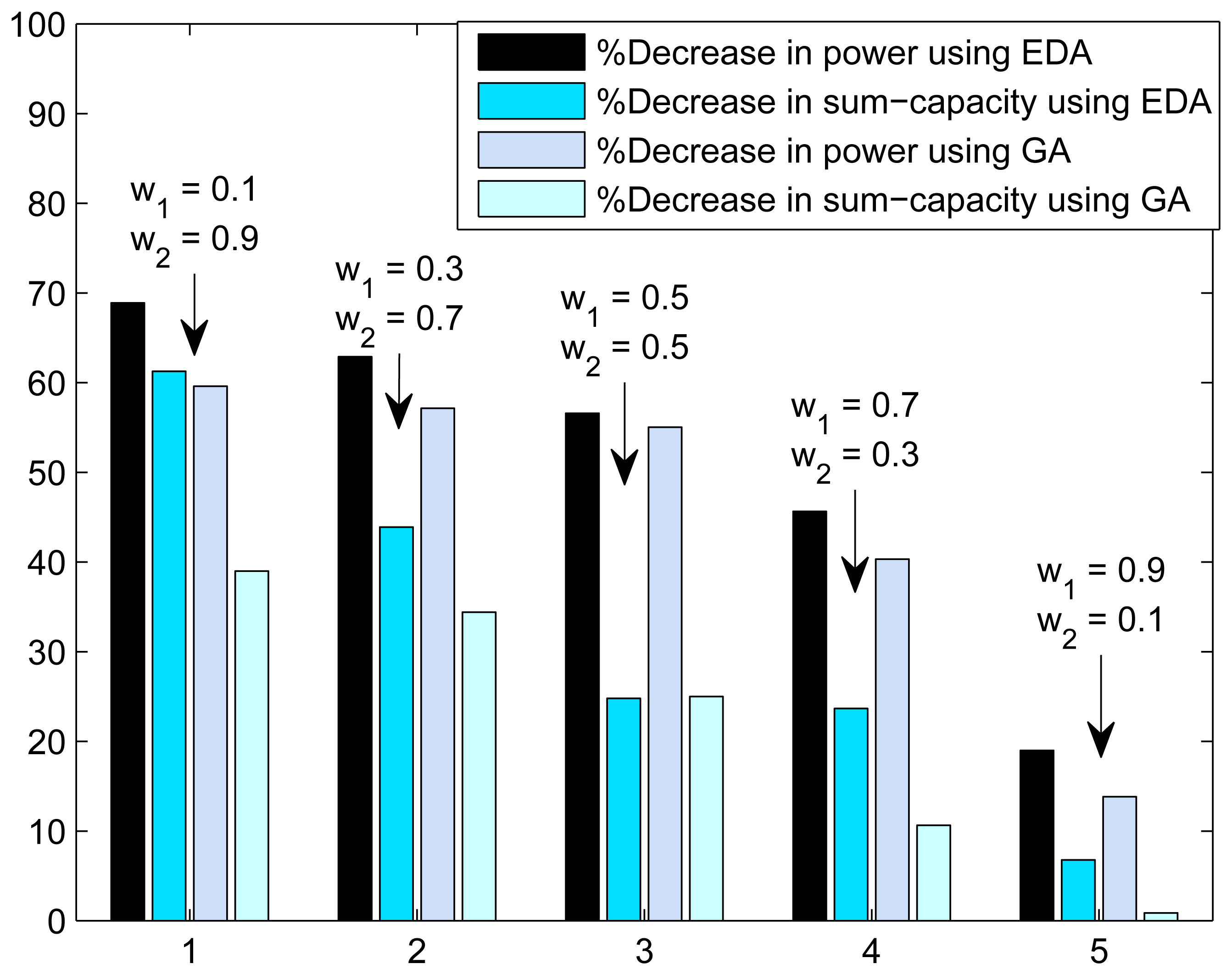
4.2. Throughput and CO2 Emissions Trade-Off
In Figure 4, we present the trade-off plot of sum-capacity and total transmission power(or CO2 emissions). The trade-off is calculated between the green communication and without green communication. Trade-off is presented as the percentage decrease in sum-capacity and percentage decrease in power consumption. The decrease in sum-capacity and decrease in power consumption is calculated using the expressions:
4.3. Performance of Proposed Schemes
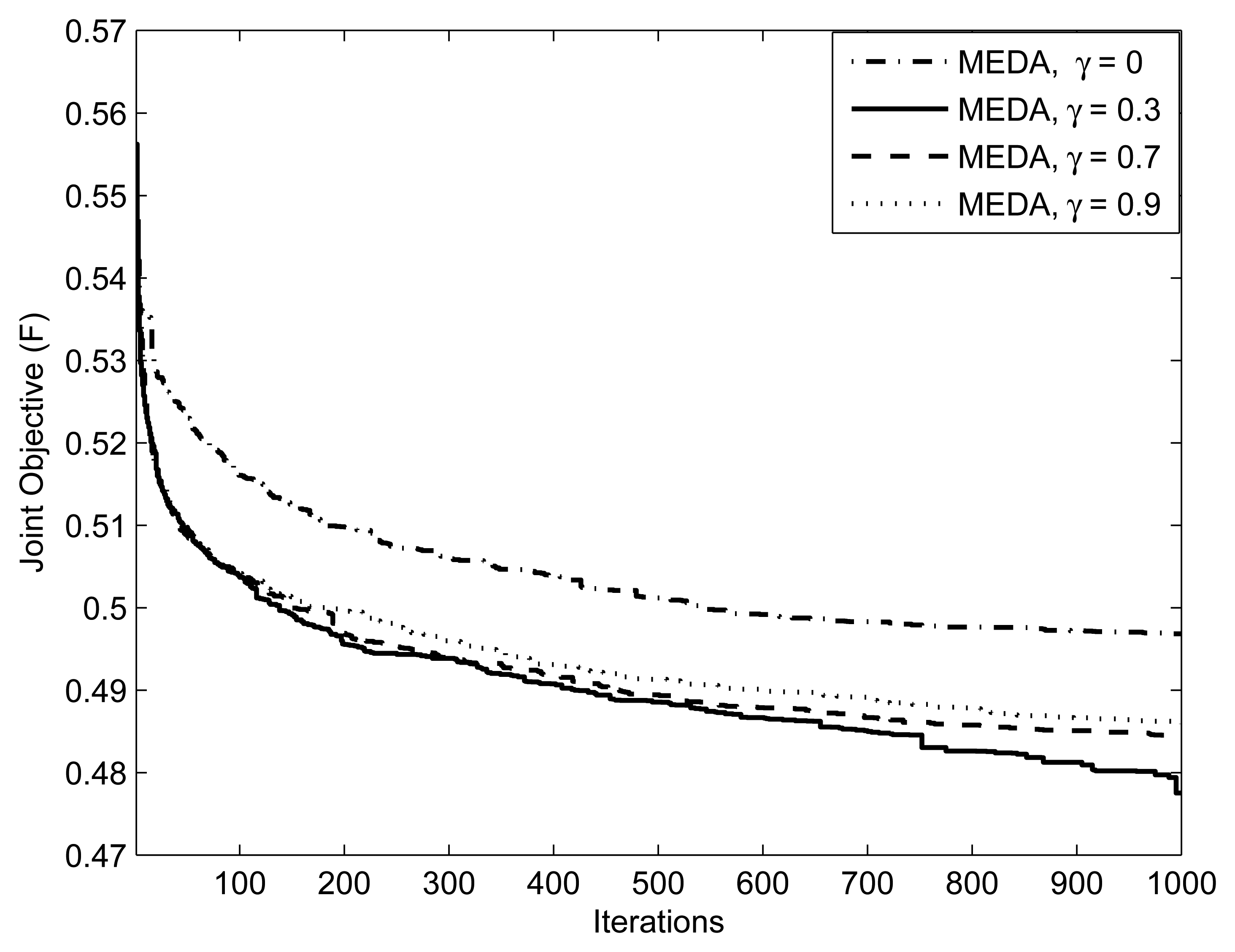
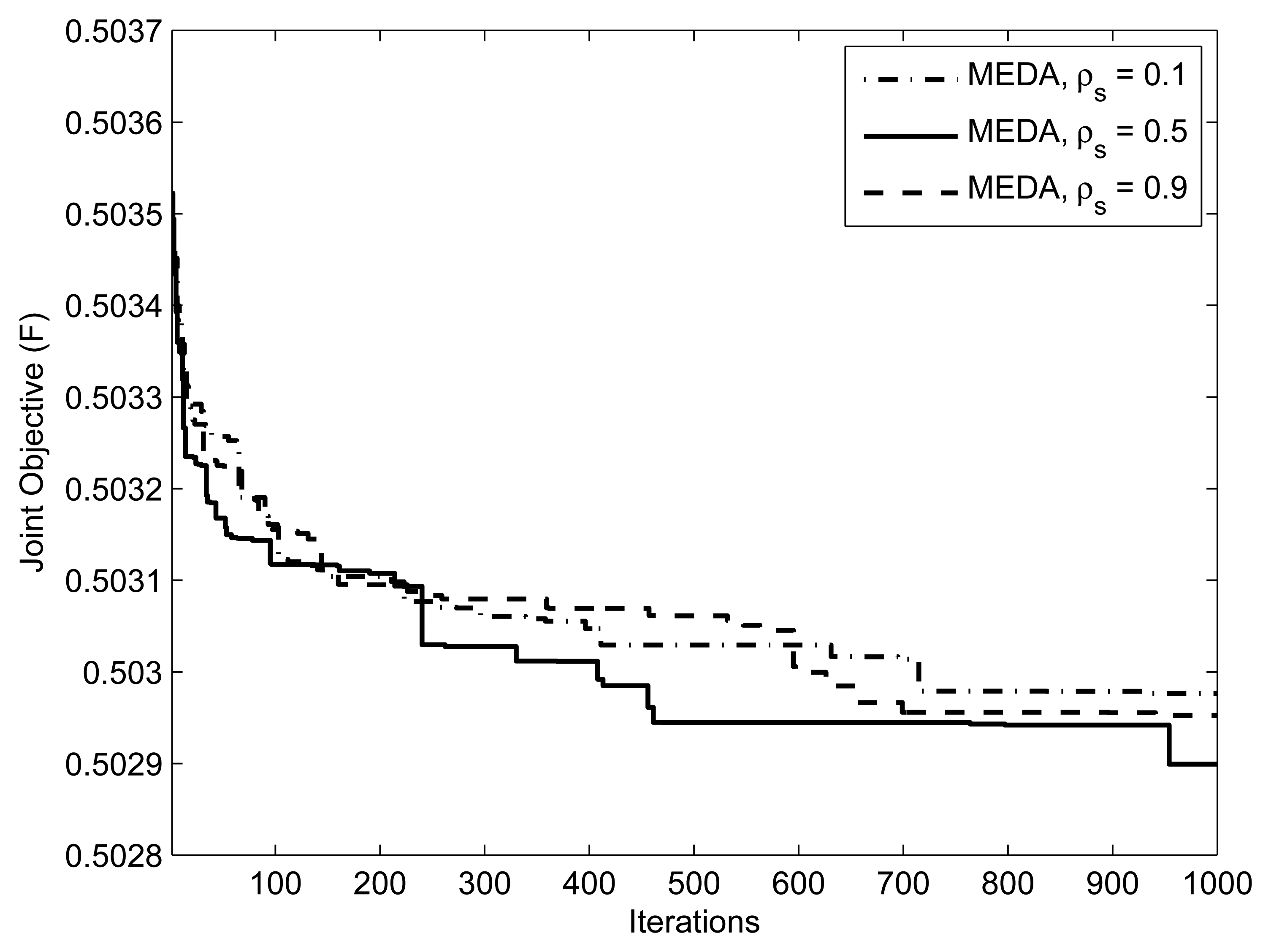
Figure 5 focuses on the method of applying thresholds on EDA, which is described in section 3.4. We ran an EDA with parameters for threshold values = {0.3, 0.7, 0.9}. Note that setting γ= 1 is equivalent to not applying the threshold at all. Setting the threshold closer to 1 means that the algorithm generates the population from an almost identical distribution in each iteration; that is, the algorithm does not take advantage of the natural selection. An interesting issue is what values of the threshold facilitates the computation. From Figure 5, we can observe that the performance of EDA is poor at γ = 0.9 and 0.7. We can interpret this as, at the threshold values of γ = 0.9 and 0.7, which are close to 1.0, the algorithm does not evolve significantly. Figure 6 presents the effect of selection probability, ρs, on the performance of EDA. The parameters are . From Figure 6, we can observe that the performance of EDA is better if selection probability, ρs, is not close to either 0 or 1. There will be no evolution if selection probability, ρs, is close to 1, the EDA will behave like a random algorithm. On the other hand, if selection probability, ρs, is close to 0, the algorithm does not evolve significantly, because it is more likely that EDA will get stuck in the local optimum.
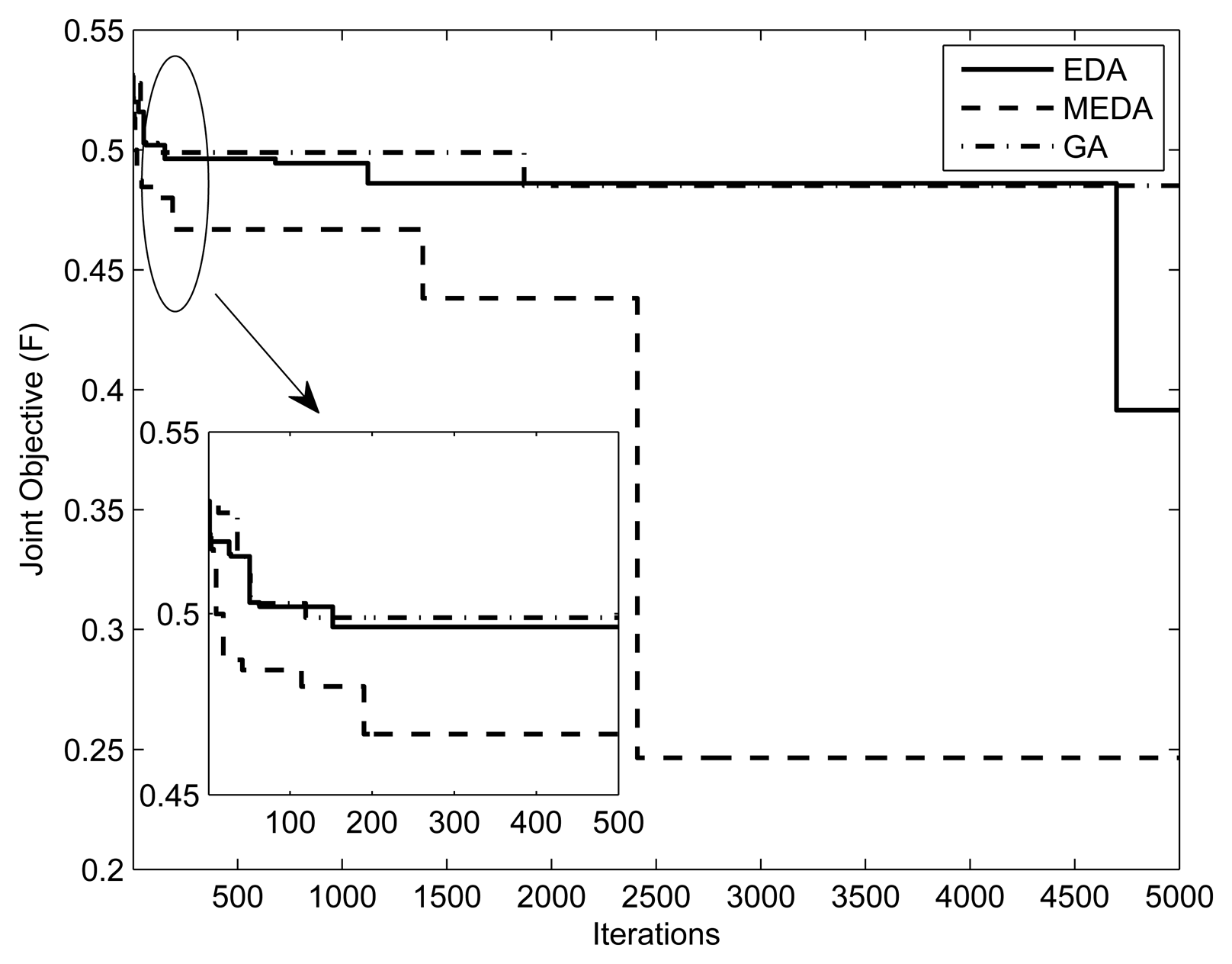
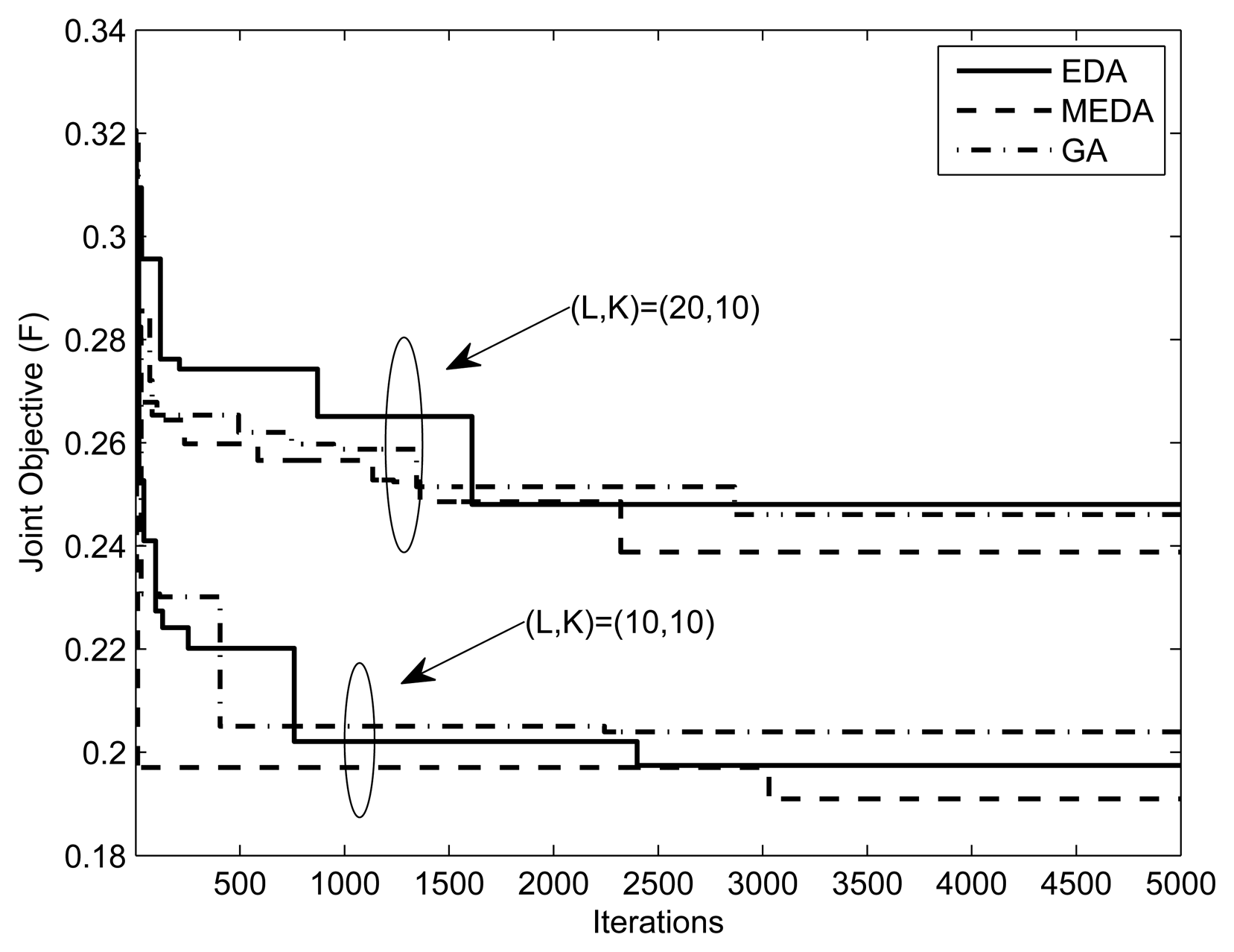
Figures 7 and 8 present the fitness vs. iterations plot for different numbers of relays and users. The fitness function was defined in Equation (7). The parameters are and (1, 10mW, 0.5, 0.5, 5), respectively. The value of threshold γ is set to 0.3. From the results, we can observe that the performance of MEDA is better than EDA and GA. This is because a simple EDA and GA can get stuck in the local optimum after a few iterations. We can also note that fitness values with less relays is better than fitness values with more relays. This is because the assignment takes more iterations for a large number of relays.
Figures 9, 10 and 11 present the impact of SUs, relays and PUs on the performance of the green sensor network. The parameters are , (20, {10.20, 40}, 10mW) and (10,10,{1, 2, 3},10mW), respectively. In all simulations, (, w1, w2, δ) are set to (0.5,0.5, 5). We observe that for a fixed number of secondary users, the fitness of the objective function will always be better with a lesser number of relays. This is because the assignment takes more iterations for a large number of relays. In the simulation results, we also observe that the objective function is better at a low number of PUs. This is because the relay assignment needs to satisfy more interference constraints as the number of PUs increases.
5. Conclusion
In this paper, we presented a multi-objective framework for resource allocation in green cooperative cognitive radio sensor networks. The estimation-of-distribution algorithm with iterative greedy scheme is used to solve the multi-objective optimization problem. The simple underlying concept and ease of implementation of the proposed algorithm make EDA a suitable candidate for green resource allocation.
References
- Akyildiz, I.; Su, W.; Sankarasubramaniam, Y.; Cayirci, E. Wireless sensor networks: A survey. Comput. Netw. 2002, 38, 393–422. [Google Scholar]
- Valenzuela, S.; Chen, M.; Leung, V.C.M. Mobility support for health monitoring at home using wearable sensors. IEEE Trans. Inf. Technol. Biomed. 2011, 15, 539–549. [Google Scholar]
- Gorce, J.-M.; Goursaud, C.; Villemaud, G.; Errico, R.; Ouvry, L. Opportunistic relaying protocols for human monitoring in BAN. Proceedings of IEEE 20th International Symposium on Personal, Indoor and Mobile Radio Communications, Tokyo, Japan, 13–16 September 2009; pp. 732–736.
- Ehyaie, A.; Hashemi, M.; Khadivi, P. Using relay network to increase life time in wireless body area sensor networks. Proceedings of IEEE International Symposium on World of Wireless, Mobile and Multimedia Networks and Workshops, Kos, Greece, 15–19 June 2009; pp. 1–6.
- Weiss, B.; Truong, H.L.; Schott, W.; Munari, A.; Lombriser, C. A power-efficient wireless sensor network for continuously monitoring seismic vibrations. Proceedings of 8th Annual IEEE Communications Society Conference on Sensor, Mesh and Ad Hoc Communications and Networks, Salt Lake City, UT, USA, 27–30 June 2011; pp. 37–45.
- Akatsuka, K.; Nakamura, K.; Hirata, Y.; Hattori, T. A proposal of the co-existence MAC of IEEE 802.11b/g and 802.15.4 used for the wireless sensor network. Proceedings of 5th IEEE Conference on Sensors, Daegu, Korea, 22–25 October 2006; pp. 722–725.
- Huang, S.; Chen, H.; Zhang, Y.; Zhao, F. Energy-Efficient cooperative spectrum sensing with amplify-and-forward relaying. IEEE Commun. Lett. 2012, 16, 450–453. [Google Scholar]
- Zhou, G.; Stankovic, J.A.; Son, S.H. Crowded spectrum in wireless sensor networks. Proceedings of Third Workshop on Embedded Networked Sensors, Cambridge, MA, USA, 30–31 May 2006.
- Herault, L.; Strinati, E.C.; Blume, O.; Zeller, D.; Imran, M.A.; Tafazolli, R.; Jading, Y.; Meyer, M. Green communications: A global environmental challenge. Proceedings of 12th International Symposium on Wireless Personal Multimedia Communications, Sendai, Japan, 7–10 Sepetember 2009.
- ITU and Climate Change; International Telecommunication Union: Geneva, Switzerland, 2008.
- Koutitas, G. Green network planning of single frequency networks. IEEE Trans. Broadcasting 2010, 56, 541–550. [Google Scholar]
- Akyildiz, I.F.; Lee, W.Y.; Vuran, M.C.; Mohanty, S. A Survey on spectrum management in cognitive radio networks. IEEE Commun. Mag. 2008, 46, 40–48. [Google Scholar]
- Yau, K.A.; Komisarczuk, P.; Teal, P.D. Cognitive radio-based wireless sensor networks: Conceptual design and open issues. Proceedings of IEEE 34th Conference on Local Computer Networks, Zurich, Switzerland, 20–23 October 2009; pp. 955–962.
- Vijay, G.; Bdira, E.B.; Ibnkahla, M. Cognition in wireless sensor networks: A perspective. IEEE Sens. J. 2011, 11, 582–592. [Google Scholar]
- Glaropoulos, I.; Fodor, V. Cognitive WSN transmission control for energy efficiency under WLAN coexistence. Proceedings of Sixth International ICST Conference on Cognitive Radio Oriented Wireless Networks and Communications, Osaka, Japan, 1–3 June 2011; pp. 261–265.
- Gao, S.; Qian, L.; Vaman, D.R. Distributed energy efficient spectrum access in wireless cognitive radio sensor networks. 31 March 2008–April 3 2008; pp. 1442–1447.
- Akan, O.B.; Karli, O.; Ergul, O. Cognitive radio sensor networks. IEEE Network 2009, 23, 34–40. [Google Scholar]
- Cheng, Q.; Varshney, P.K. Subspace-Based cooperative spectrum sensing for cognitive radios. IEEE Sens. J. 2011, 11, 611–620. [Google Scholar]
- Zemin, H.; Yongmei, S.; Ji, Y. A Dynamic spectrum access strategy based on real-time usability in cognitive radio sensor networks. Proceedings of IEEE International Conference on Mobile Ad-Hoc and Sensor Networks, Beijing, China, 16–18 December 2011; pp. 318–322.
- Sreesha, A.A.; Somal, S.; Lu, I.-T. Cognitive radio based wireless sensor network architecture for smart grid utility. Proceedings of EEE Long Island Systems, Applications and Technology Conference, Farmingdale, NY, USA, 6 May 2011; pp. 1–7.
- Murphy, P.; Sabharwal, A.; Aazhang, B. On building a cooperative communication system: Testbed implementation and first results. EURASIP J. Wirel. Commun. Netw. 2009. [Google Scholar] [CrossRef]
- Akyildiz, I.F.; Stuntebeck, E.P. Wireless underground sensor networks: research challenges. Ad Hoc Netw. 2006, 4, 669–686. [Google Scholar]
- Li, M.; Liu, Y. Underground structure monitoring with wireless sensor networks. Proceedings of 6th International Symposium on Information Processing in Sensor Networks, Cambridge, MA, USA, 25–27 April 2007; pp. 69–78.
- Werner-Allen, G.; Lorincz, K.; Welsh, M.; Marcillo, O.; Johnson, J.; Ruiz, M.; Lees, J. Deploying a wireless sensor network on an active volcano. IEEE Internet Comput. 2006, 10, 18–25. [Google Scholar]
- Darymli, K.E. Amplify-And-Forward cooperative relaying for a linear wireless sensor network. Proceedings of IEEE International Conference on Systems Man and Cybernetics, Istanbul, Turkey, 10–13 October 2010; pp. 106–112.
- Wang, D.; He, R.; Han, J.; Fattouche, M.; Ghannouchi, F.M. Sensor network based oilwell health monitoring and intelligent control. IEEE Sens. J. 2012, 12, 1326–1339. [Google Scholar]
- Elsaadany, M.; Abdallah, M.; Khattab, T.; Khairy, M.; Hasna, M. Cognitive relaying in wireless sensor networks: Performance analysis and optimization. Proceedings of IEEE Global Telecommunications Conference, Miami, FL, USA, 6–10 December 2010; pp. 1–6.
- Pandharipande, A.; Han, Y.; Wang, Y. Sensing and communication protocols in cognitive sensor relay networks. Proceedings of IEEE Sensors, Lecce, Italy, 26–29 October 2008; pp. 617–620.
- Gulbahar, B.; Akan, O. Information theoretical optimization gains in energy adaptive data gathering and relaying in cognitive radio sensor networks. IEEE Trans. Wirel. Commun. 2012, 11, 1788–1796. [Google Scholar]
- Han, Y.; Ting, S.H.; Pandharipande, A. Spectrally efficient sensing protocol in cognitive relay systems. IET Commun. 2011, 5, 709–718. [Google Scholar]
- Kim, I.; Kim, D. Source-Sum-Power minimization in multi-sensor single-relay networks with direct links. IEEE Commun. Lett. 2013. accepted. [Google Scholar]
- Sharma, R.K.; Wallace, J.W. Correlation-Based sensing for cognitive radio networks: Bounds and experimental assessment. IEEE Sens. J. 2011, 11, 657–666. [Google Scholar]
- Li, H.; Jaggi, N.; Sikdar, B. Relay scheduling for cooperative communications in sensor networks with energy harvesting. IEEE Trans. Wirel. Commun. 2011, 10, 2918–2928. [Google Scholar]
- Schwieger, K.; Fettweis, G. Multi-Hop transmission: Benefits and deficits. Proceedings of GI/ITG Fachgespraech Sensornetze, Karlsruhe, Germany, 26–27 February 2004.
- Deb, K. Multi-Objective Optimization Using Evolutionary Algorithms; Wiley: New York, NY, USA, 2001. [Google Scholar]
- Cover, T.; Thomas, J. Elements of Information Theory, 2nd ed.; John Wiley and Sons: New York, NY, USA, 2006. [Google Scholar]
- Maric, I.; Yates, R.D. Bandwidth and power allocation for cooperative strategies in gaussian relay networks. IEEE Trans. Inform. Theory 2010, 56, 1880–1889. [Google Scholar]
- Eiben, A.E.; Smith, J.E. Introduction to Evolutionary Computing; Springer: Berlin, Germany, 2003. [Google Scholar]
- Larranga, P.; Lozano, J.A. Estimation of Distribution Algorithms: A New Tool for Evolutionary Computation; Kluwer Academic Publishers: Alphen aan den Rijn, The Netherlands, 2001. [Google Scholar]
- Goldsmith, A. Wireless Communications; Cambridge University Press: New York, NY, USA, 2005. [Google Scholar]



| Symbol | Definition |
|---|---|
| K | Number of secondary users |
| M | Number of primary users |
| L | Number of relays |
| Im | Interference threshold at mth PU |
| Channel between the source and the lth relay | |
| Channel between the kth SU and the lth relay | |
| pl | Transmission power of the lth relay |
| Maximum power of the lth relay | |
| Transmission power of the source at the kth SU band | |
| Ps | Maximum available power of the source |
| Channel between the source and the mth PU in the k SU band | |
| Channel between the mth PU and the lth relay in the k SU band | |
| ε | binary assignment indicator |
| F() | Fitness function as mentioned in Equation (7) |
| WH | Upper limit of the EDA search window |
| WL | Lower limit of the EDA search window |
| Δt | The population at the tth iteration and |Δt | denotes the cardinality |
| ηt | The set of best candidate solutions selected from set |Δt| at the tth iteration. |
| ρs | The selection probability. The EDA selects ρs|Δt| individuals from the set |Δt| to make up the set ηt. |
| ITer | The maximum number of iterations |
| Parameters | Values |
|---|---|
| 1 Watts | |
| ρs | 10 Watts |
| γ | 0.2 |
| Δt | 20 |
| ηt | 10 |
| ρs | 0.5 |
| ITer | 5000 |
© 2013 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license ( http://creativecommons.org/licenses/by/3.0/).
Share and Cite
Naeem, M.; Pareek, U.; Lee, D.C.; Anpalagan, A. Estimation of Distribution Algorithm for Resource Allocation in Green Cooperative Cognitive Radio Sensor Networks. Sensors 2013, 13, 4884-4905. https://doi.org/10.3390/s130404884
Naeem M, Pareek U, Lee DC, Anpalagan A. Estimation of Distribution Algorithm for Resource Allocation in Green Cooperative Cognitive Radio Sensor Networks. Sensors. 2013; 13(4):4884-4905. https://doi.org/10.3390/s130404884
Chicago/Turabian StyleNaeem, Muhammad, Udit Pareek, Daniel C. Lee, and Alagan Anpalagan. 2013. "Estimation of Distribution Algorithm for Resource Allocation in Green Cooperative Cognitive Radio Sensor Networks" Sensors 13, no. 4: 4884-4905. https://doi.org/10.3390/s130404884
APA StyleNaeem, M., Pareek, U., Lee, D. C., & Anpalagan, A. (2013). Estimation of Distribution Algorithm for Resource Allocation in Green Cooperative Cognitive Radio Sensor Networks. Sensors, 13(4), 4884-4905. https://doi.org/10.3390/s130404884




