A Novel Hyperchaotic 2D-SFCF with Simple Structure and Its Application in Image Encryption
Abstract
:1. Introduction
2. 2D-SFCF
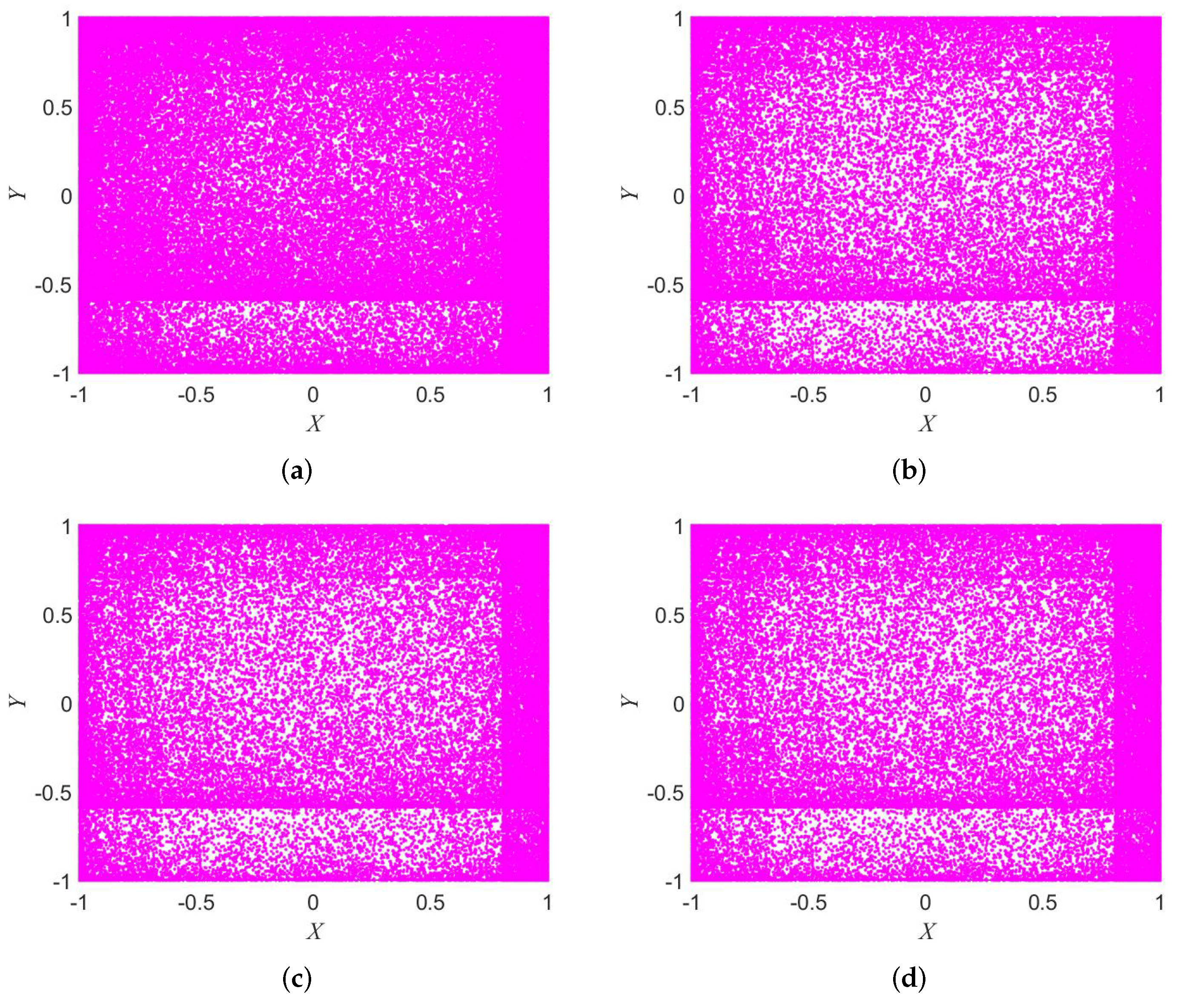
2.1. Attractor
2.2. NIST Statistical Test Suite
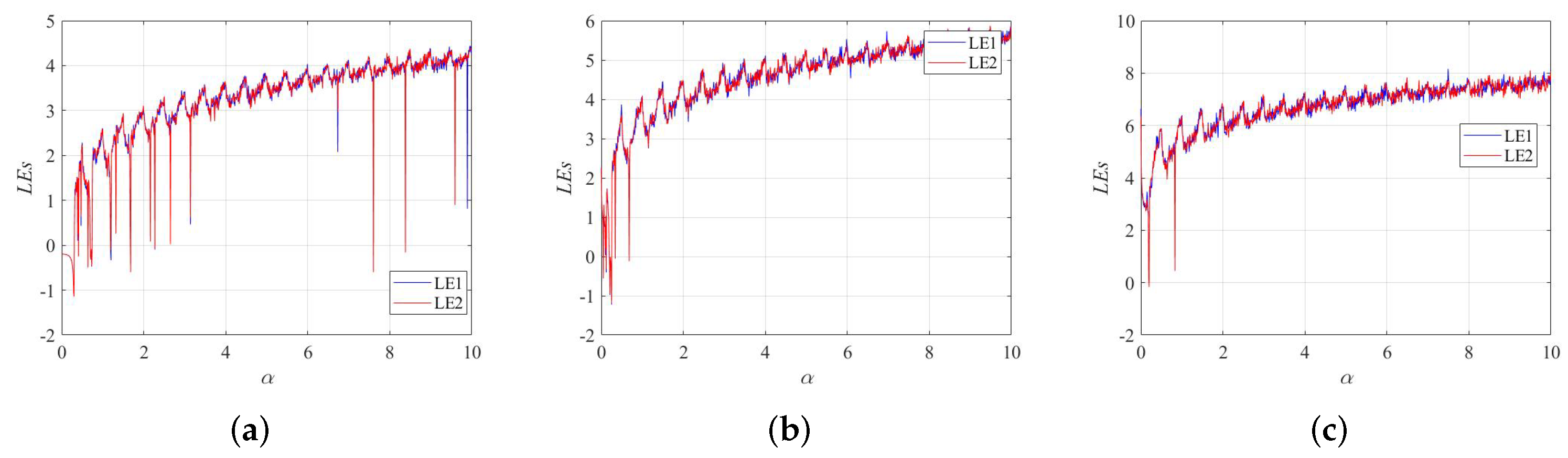
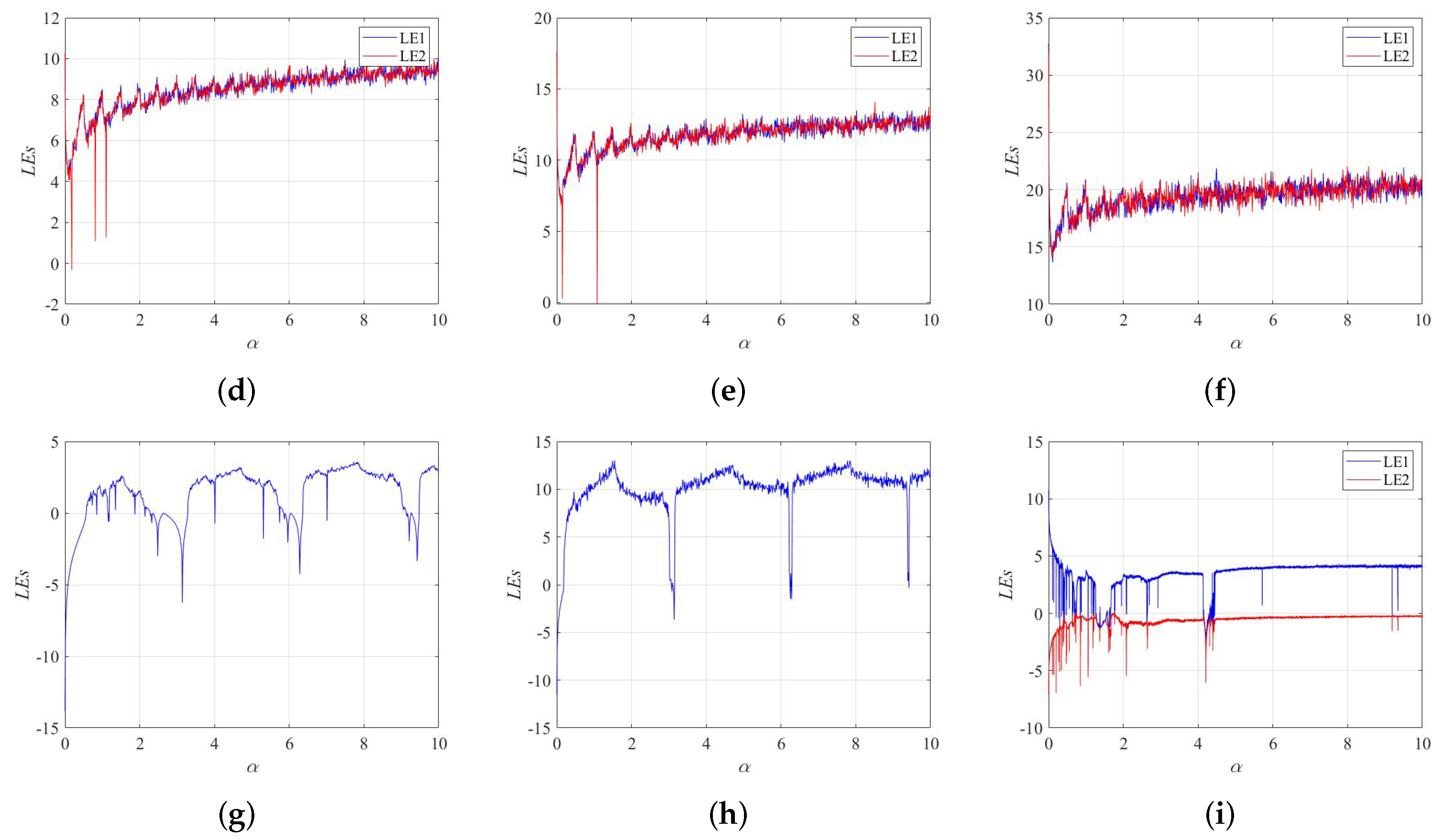
2.3. Lyapunov Exponents
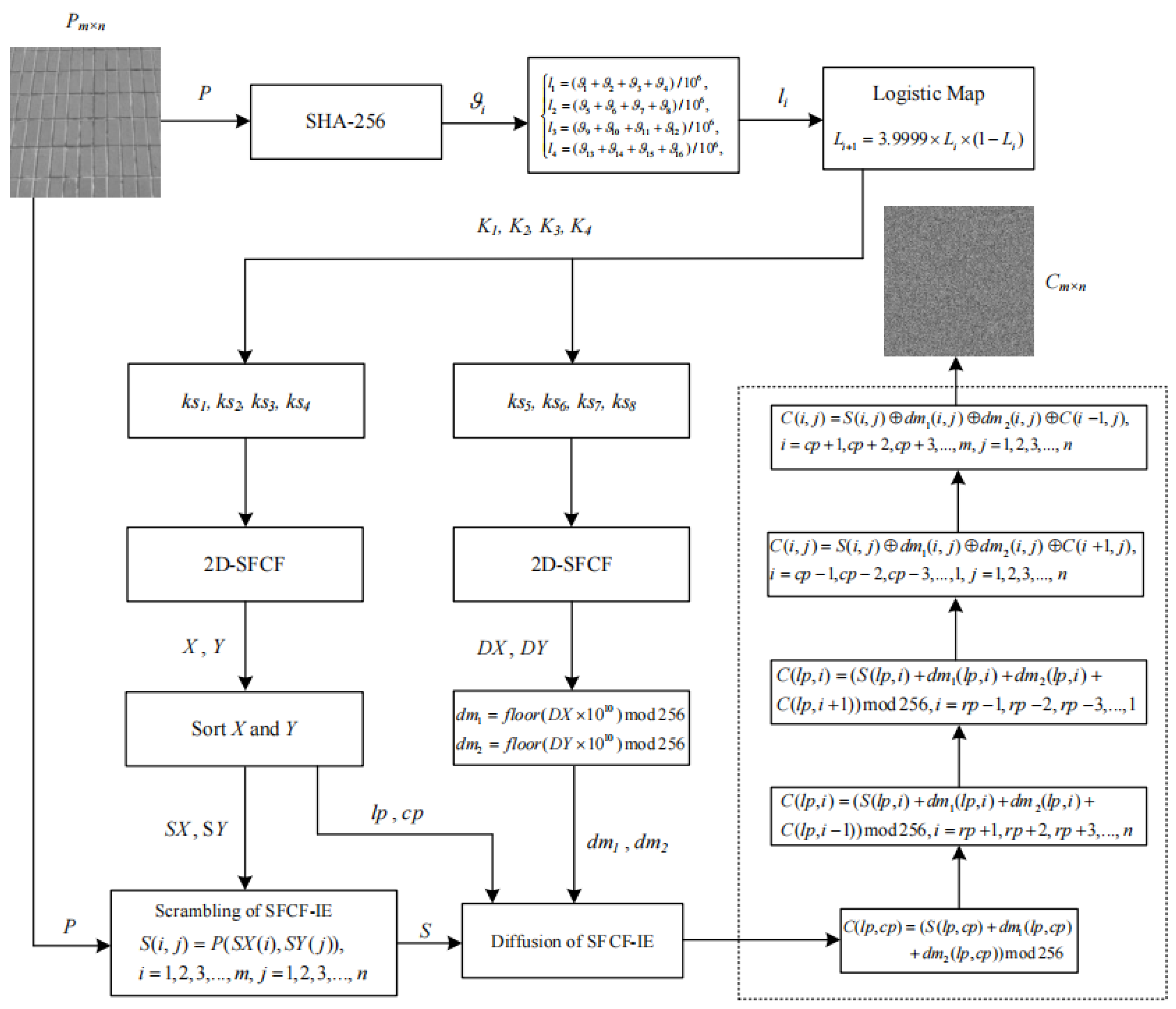
3. SFCF-IE Algorithm
3.1. Function Declaration
- (1)
- (2)
- Set to a keystream generation function , where a is the parameter of the 2D-SFCF, b is the parameter of the 2D-SFCF, c is the initial value of the 2D-SFCF, d is the initial value of the 2D-SFCF, and N is the number of iterations. Output sequences are and . Note that when generating a chaotic sequence, some initial values of iterations need to be discarded, so that the generated sequence is sufficiently chaotic. Here, the first 100 iteration values are set to be discarded.
- (3)
- Set a sorting function , which can sort the one-dimensional vector a and find the position of the sorted vector in the vector a, and the return value is B. An example of a sorting function. If , and then .
3.2. Key Generation of SFCF-IE
3.3. Scrambling of SFCF-IE
3.4. Diffusion of SFCF-IE
4. Performance Analysis
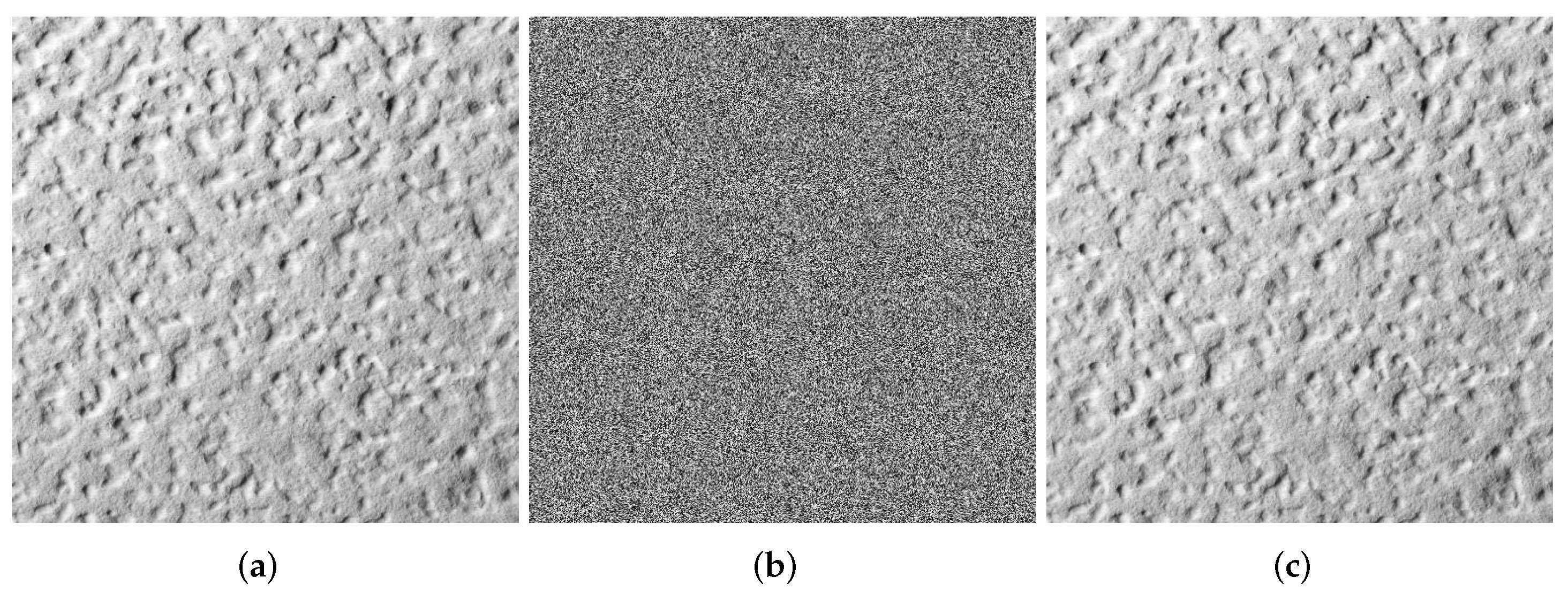
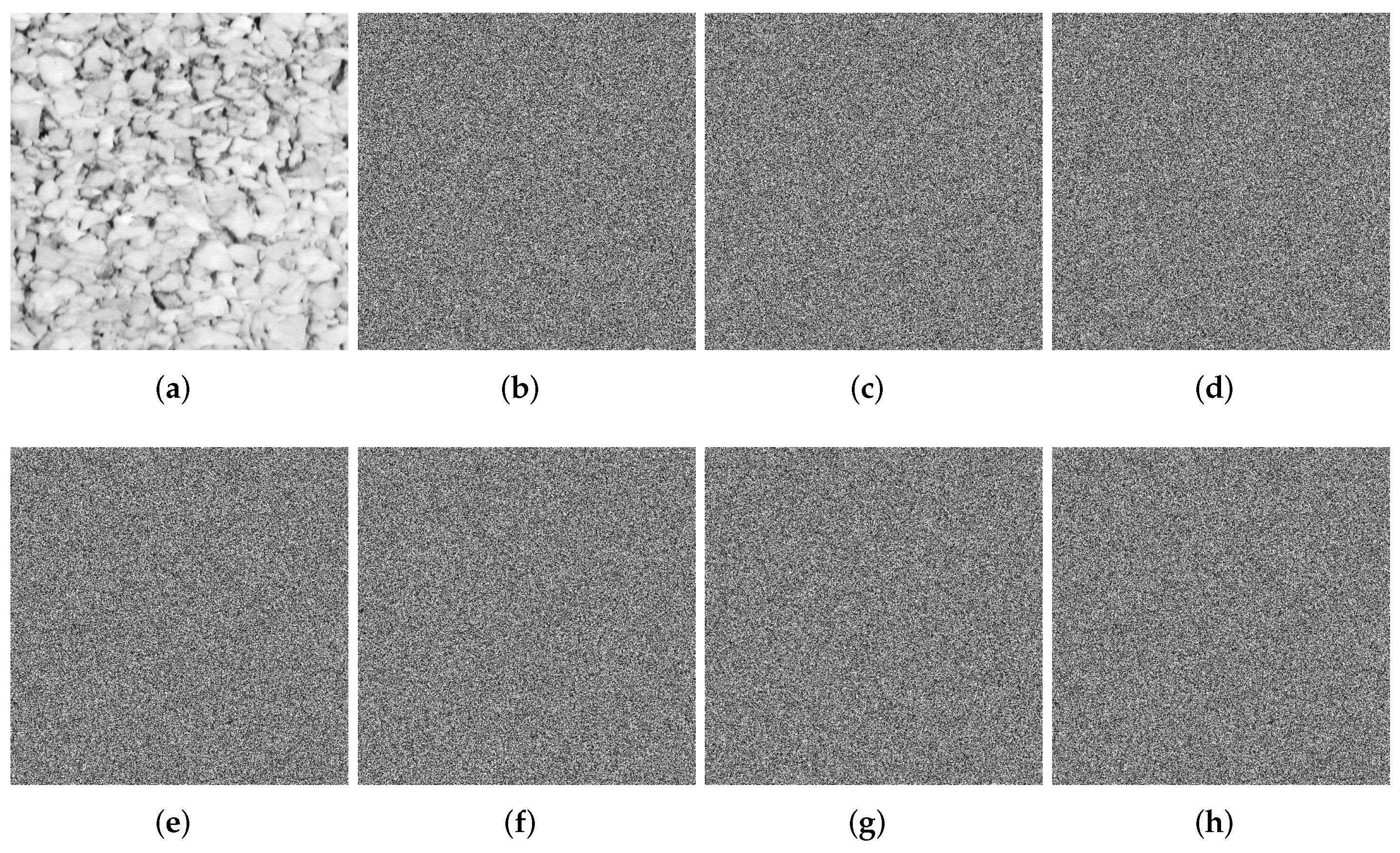
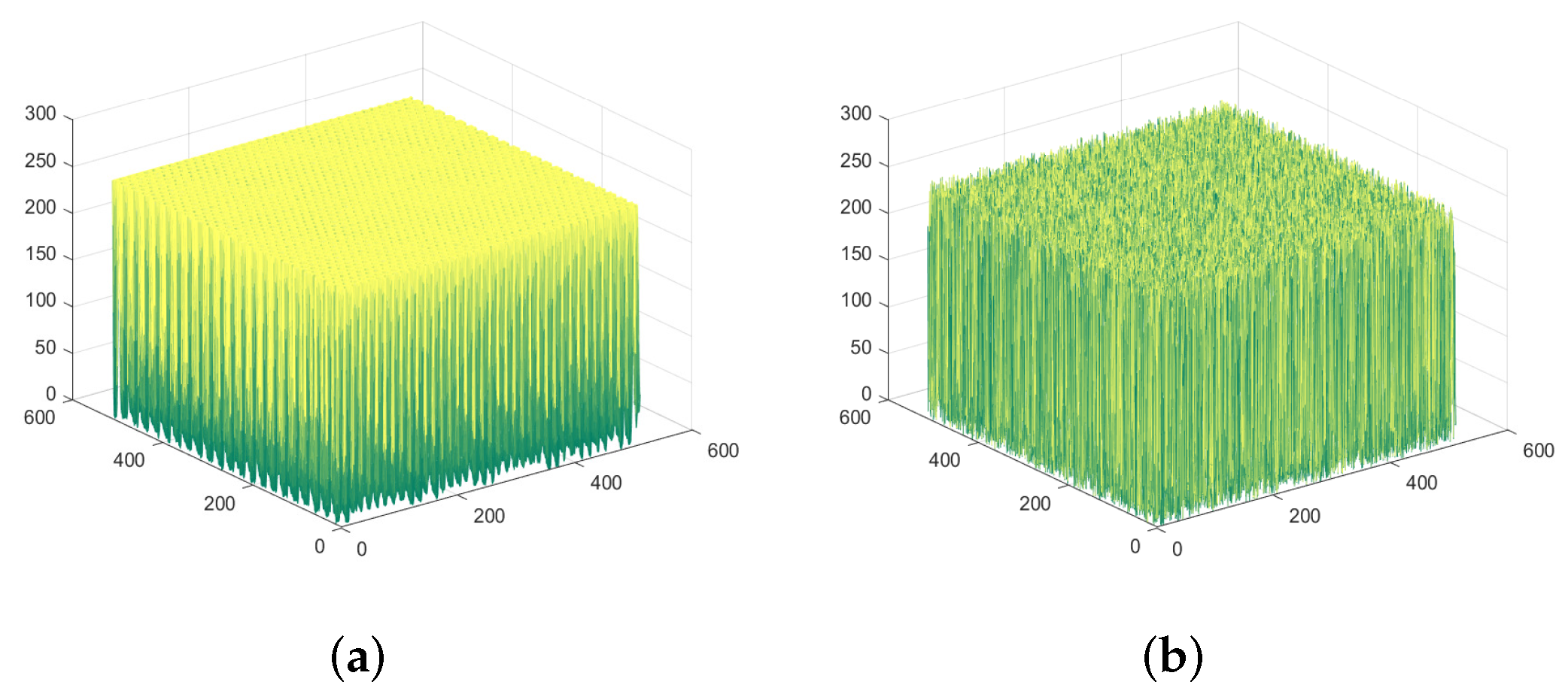
4.1. Visualization
4.2. Key Analysis
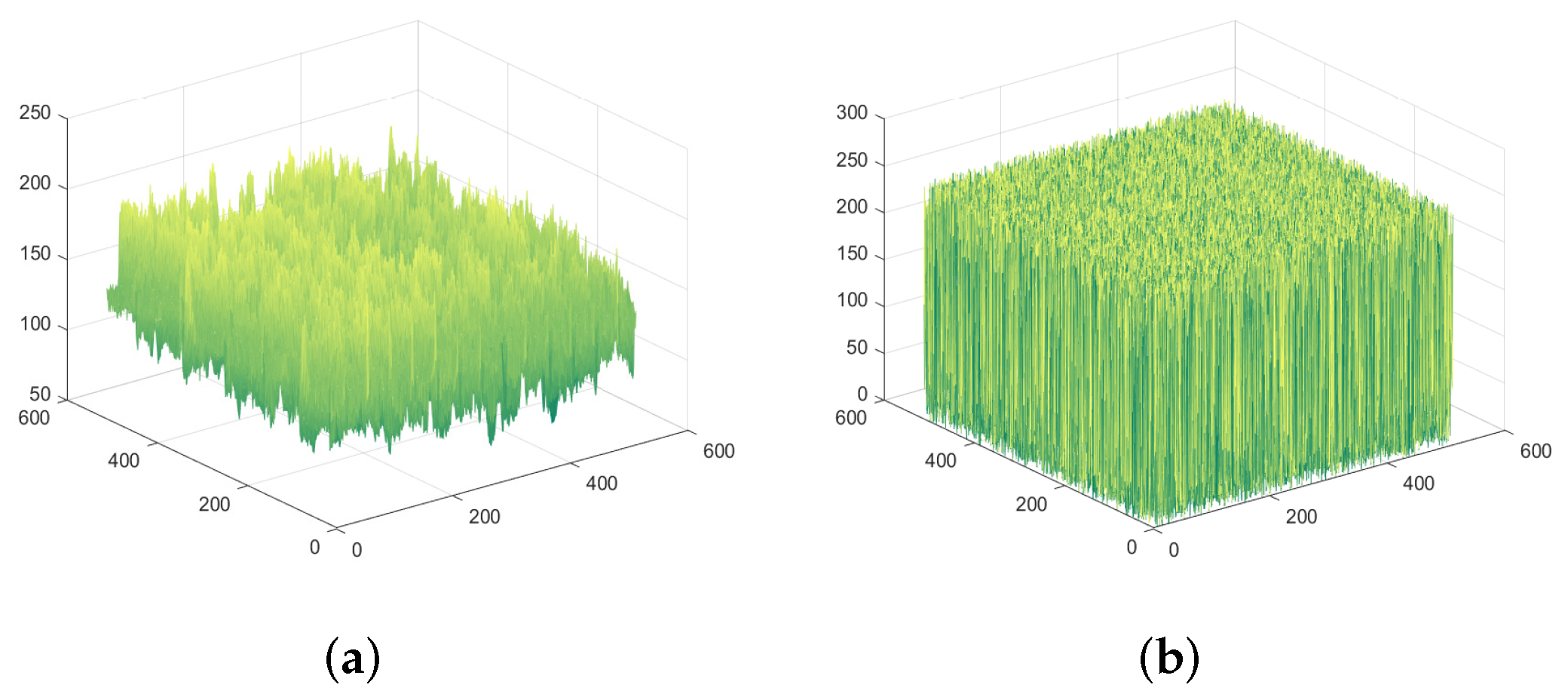
4.3. Histogram Analysis
4.4. Information Entropy Analysis
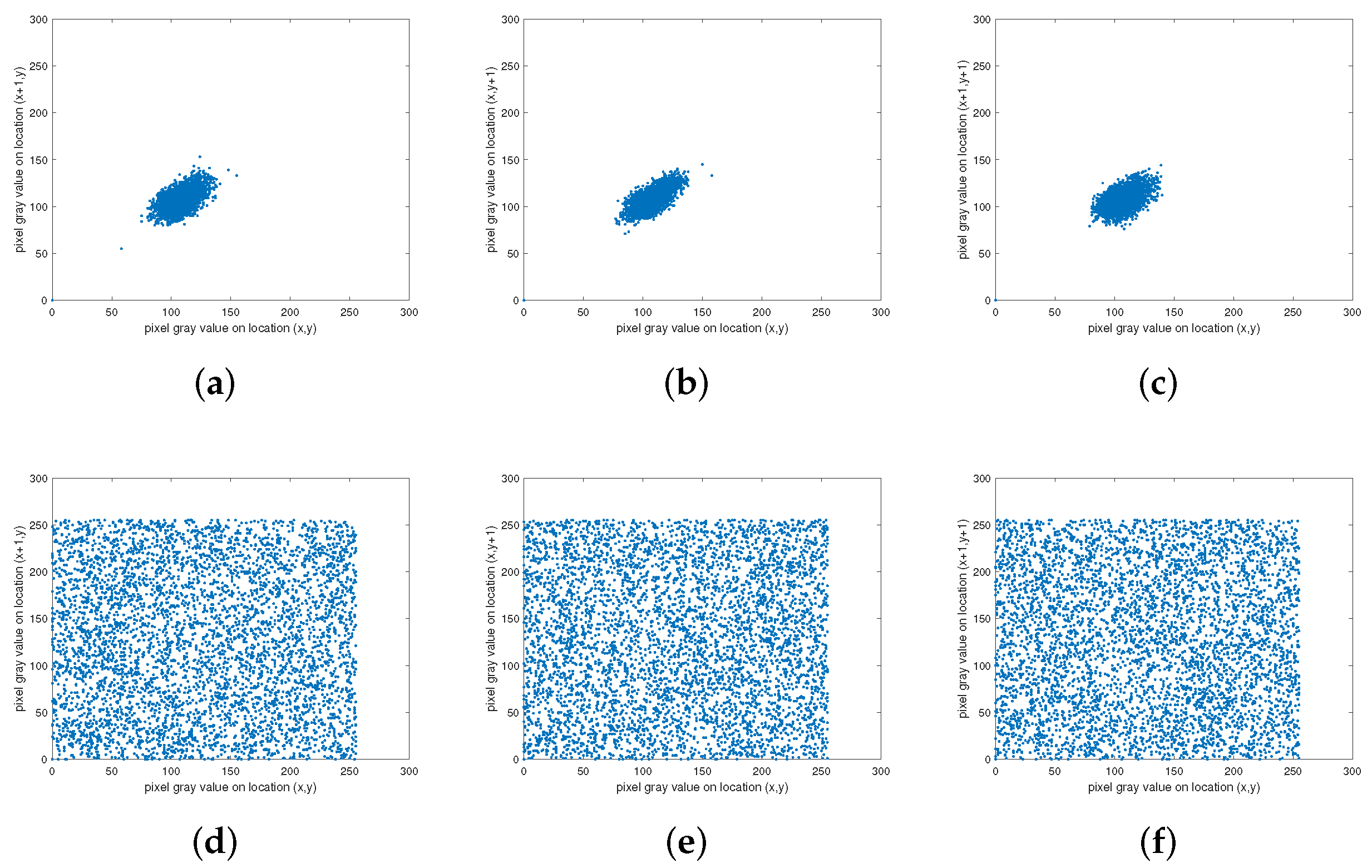
4.5. Correlation Analysis
4.6. NIST for Ciphertexts
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Data Availability Statement
Conflicts of Interest
References
- Shi, G.; Yu, S.; Wang, Q. Security Analysis of the Image Encryption Algorithm Based on a Two-Dimensional Infinite Collapse Map. Entropy 2022, 24, 1023. [Google Scholar] [CrossRef] [PubMed]
- Hua, Z.; Yi, S.; Zhou, Y. Medical image encryption using high-speed scrambling and pixel adaptive diffusion. Signal Process. 2018, 144, 134–144. [Google Scholar] [CrossRef]
- Chai, X.; Wu, H.; Gan, Z.; Han, D.; Zhang, Y.; Chen, Y. An efficient approach for encrypting double color images into a visually meaningful cipher image using 2D compressive sensing. Inf. Sci. 2021, 556, 305–340. [Google Scholar] [CrossRef]
- Toktas, A.; Erkan, U.; Toktas, F.; Yetgın, Z. Chaotic map optimization for image encryption using triple objective differential evolution algorithm. IEEE Access 2021, 9, 127814–127832. [Google Scholar] [CrossRef]
- Fu, X.Q.; Liu, B.C.; Xie, Y.Y.; Li, W.; Liu, Y. Image encryption-then-transmission using DNA encryption algorithm and the double chaos. IEEE Photonics J. 2018, 10, 1–15. [Google Scholar] [CrossRef]
- Hsiao, F.H. Applying 3DES to Chaotic Synchronization Cryptosystems. IEEE Access 2021, 10, 1036–1050. [Google Scholar] [CrossRef]
- Wang, C.; Ma, B.; Xia, Z.; Li, J.; Li, Q.; Shi, Y.Q. Stereoscopic image description with trinion fractional-order continuous orthogonal moments. IEEE Trans. Circuits Syst. Video Technol. 2021, 32, 1998–2012. [Google Scholar] [CrossRef]
- Wang, X.; Wang, X.; Ma, B.; Li, Q.; Shi, Y.-Q. High precision error prediction algorithm based on ridge regression predictor for reversible data hiding. IEEE Signal Process. Lett. 2021, 28, 1125–1129. [Google Scholar] [CrossRef]
- Ma, B.; Shi, Y.Q. A reversible data hiding scheme based on code division multiplexing. IEEE Trans. Inf. Forensics Secur. 2016, 11, 1914–1927. [Google Scholar] [CrossRef]
- Li, Q.; Wang, X.; Ma, B.; Wang, X.; Wang, C.; Gao, S.; Shi, Y. Concealed attack for robust watermarking based on generative model and perceptual loss. IEEE Trans. Circuits Syst. Video Technol. 2021, 32, 5695–5706. [Google Scholar] [CrossRef]
- Erkan, U.; Toktas, A.; Toktas, F.; Alenezi, F. 2D epimap for image encryption. Inf. Sci. 2022, 589, 770–789. [Google Scholar] [CrossRef]
- Wang, X.; Gao, S. A chaotic image encryption algorithm based on a counting system and the semi-tensor product. Multimed. Tools Appl. 2021, 80, 10301–10322. [Google Scholar] [CrossRef]
- Li, T.; Shi, J.; Li, X.; Wu, J.; Pan, F. Image encryption based on pixel-level diffusion with dynamic filtering and DNA-level permutation with 3D Latin cubes. Entropy 2019, 21, 319. [Google Scholar] [CrossRef]
- Yang, F.; Mou, J.; Luo, C.; Cao, Y. An improved color image encryption scheme and cryptanalysis based on a hyperchaotic sequence. Phys. Scr. 2019, 94, 085206. [Google Scholar] [CrossRef]
- Ding, L.; Ding, Q. A novel image encryption scheme based on 2D fractional chaotic map, DWT and 4D hyper-chaos. Electronics 2020, 9, 1280. [Google Scholar] [CrossRef]
- Masood, F.; Ahmad, J.; Shah, S.A.; Jamal, S.S.; Hussain, I. A novel hybrid secure image encryption based on julia set of fractals and 3D Lorenz chaotic map. Entropy 2020, 22, 274. [Google Scholar] [CrossRef] [PubMed]
- Li, X.; Mou, J.; Xiong, L.; Wang, Z.; Xu, J. Fractional-order double-ring erbium-doped fiber laser chaotic system and its application on image encryption. Opt. Laser Technol. 2021, 140, 107074. [Google Scholar] [CrossRef]
- Wang, T.; Ge, B.; Xia, C.; Dai, G. Multi-Image Encryption Algorithm Based on Cascaded Modulation Chaotic System and Block-Scrambling-Diffusion. Entropy 2022, 24, 1053. [Google Scholar] [CrossRef]
- Gao, S.; Wu, R.; Wang, X.; Wang, J.; Li, Q.; Wang, C.; Tang, X. A 3D model encryption scheme based on a cascaded chaotic system. Signal Process. 2022, 202, 108745. [Google Scholar] [CrossRef]
- Chai, X.; Wu, H.; Gan, Z.; Zhang, Y.; Chen, Y.; Nixon, K.W. An efficient visually meaningful image compression and encryption scheme based on compressive sensing and dynamic LSB embedding. Opt. Lasers Eng. 2020, 124, 105837. [Google Scholar] [CrossRef]
- Hua, Z.; Zhu, Z.; Yi, S.; Zhang, Z.; Huang, H. Cross-plane colour image encryption using a two-dimensional logistic tent modular map. Inf. Sci. 2021, 546, 1063–1083. [Google Scholar] [CrossRef]
- Wang, X.; Gao, S.; Yu, L.; Sun, Y.; Sun, H. Chaotic image encryption algorithm based on bit-combination scrambling in decimal system and dynamic diffusion. IEEE Access 2019, 7, 103662–103677. [Google Scholar] [CrossRef]
- Zhu, S.; Wang, G.; Zhu, C. A secure and fast image encryption scheme based on double chaotic S-boxes. Entropy 2019, 21, 790. [Google Scholar] [CrossRef] [PubMed]
- Pak, C.; An, K.; Jang, P.; Kim, J.; Kim, S. A novel bit-level color image encryption using improved 1D chaotic map. Multimed. Tools Appl. 2019, 78, 12027–12042. [Google Scholar] [CrossRef]
- Pak, C.; Huang, L. A new color image encryption using combination of the 1D chaotic map. Signal Process. 2017, 138, 129–137. [Google Scholar] [CrossRef]
- Zhu, C.; Wang, G.; Sun, K. Improved cryptanalysis and enhancements of an image encryption scheme using combined 1D chaotic maps. Entropy 2018, 20, 843. [Google Scholar] [CrossRef]
- Chen, Z.; Yuan, X.; Yuan, Y.; Iu, H.H.-C.; Fernando, T. Parameter identification of chaotic and hyper-chaotic systems using synchronization-based parameter observer. IEEE Trans. Circuits Syst. I Regul. Pap. 2016, 63, 1464–1475. [Google Scholar] [CrossRef]
- Hua, Z.; Zhou, B.; Zhou, Y. Sine-transform-based chaotic system with FPGA implementation. IEEE Trans. Ind. Electron. 2017, 65, 2557–2566. [Google Scholar] [CrossRef]
- Al-Hazaimeh, O.M.; Al-Jamal, M.F.; Alhindawi, N.; Omari, A. Image encryption algorithm based on Lorenz chaotic map with dynamic secret keys. Neural Comput. Appl. 2019, 31, 2395–2405. [Google Scholar] [CrossRef]
- Pourasad, Y.; Ranjbarzadeh, R.; Mardani, A. A new algorithm for digital image encryption based on chaos theory. Entropy 2021, 23, 341. [Google Scholar] [CrossRef]
- Wang, X.; Gao, S.; Ye, X.; Shuang, Z.; Mingxu, W. A new image encryption algorithm with cantor diagonal scrambling based on the PUMCML system. Int. J. Bifurc. Chaos 2021, 31, 2150003. [Google Scholar]
- Talhaoui, M.Z.; Wang, X.; Talhaoui, A. A new one-dimensional chaotic map and its application in a novel permutation-less image encryption scheme. Vis. Comput. 2021, 37, 1757–1768. [Google Scholar] [CrossRef]
- Sun, J. 2D-SCMCI hyperchaotic map for image encryption algorithm. IEEE Access 2021, 9, 59313–59327. [Google Scholar] [CrossRef]
- Ibrahim, S.; Abbas, A.M. Efficient key-dependent dynamic S-boxes based on permutated elliptic curves. Inf. Sci. 2021, 558, 246–264. [Google Scholar] [CrossRef]
- Tsafack, N.; Kengne, J.; Abd-El-Atty, B.; Iliyasu, A.M.; Hirota, K.; Abd EL-Latif, A.A. Design and implementation of a simple dynamical 4-D chaotic circuit with applications in image encryption. Inf. Sci. 2020, 515, 191–217. [Google Scholar] [CrossRef]
- Wang, X.; Feng, L.; Zhao, H. Fast image encryption algorithm based on parallel computing system. Inf. Sci. 2019, 486, 340–358. [Google Scholar] [CrossRef]
- Ravichandran, D.; Praveenkumar, P.; Rayappan, J.B.B.; Amirtharajan, R. Chaos based crossover and mutation for securing DICOM image. Comput. Biol. Med. 2016, 72, 170–184. [Google Scholar] [CrossRef]
- Ravichandran, D.; Praveenkumar, P.; Rayappan, J.B.B.; Amirtharajan, R. DNA chaos blend to secure medical privacy. IEEE Trans. Nanobioscience 2017, 16, 850–858. [Google Scholar] [CrossRef]


| Statistical Test | a = 9.7, b = 8 | a = 2.8, b = 10 | ||||||
|---|---|---|---|---|---|---|---|---|
| X | Y | X | Y | |||||
| p-Value | Result | p-Value | Result | p-Value | Result | p-Value | Result | |
| Longest run of ones | 0.419021 | Success | 0.096578 | Success | 0.236810 | Success | 0.534146 | Success |
| Overlapping template matching | 0.616305 | Success | 0.383827 | Success | 0.534146 | Success | 0.574903 | Success |
| Random excursions variant | 0.671779 | Success | 0.350485 | Success | 0.976060 | Success | 0.888137 | Success |
| Rank | 0.657933 | Success | 0.350485 | Success | 0.816537 | Success | 0.911413 | Success |
| Frequency | 0.066882 | Success | 0.350485 | Success | 0.494392 | Success | 0.108791 | Success |
| Universal | 0.657933 | Success | 0.494392 | Success | 0.350485 | Success | 0.883171 | Success |
| Random excursions | 0.602458 | Success | 0.275709 | Success | 0.862344 | Success | 0.995711 | Success |
| Block frequency | 0.289667 | Success | 0.911413 | Success | 0.006661 | Success | 0.779188 | Success |
| Cumulative sums | 0.191687 | Success | 0.289667 | Success | 0.574903 | Success | 0.236810 | Success |
| Runs | 0.213309 | Success | 0.816537 | Success | 0.816537 | Success | 0.085587 | Success |
| Serial | 0.779188 | Success | 0.616305 | Success | 0.883171 | Success | 0.289667 | Success |
| Spectral | 0.045675 | Success | 0.816537 | Success | 0.883171 | Success | 0.851383 | Success |
| Approximate entropy | 0.955835 | Success | 0.455937 | Success | 0.816537 | Success | 0.383827 | Success |
| Nonoverlapping template matching | 0.971699 | Success | 0.383827 | Success | 0.534146 | Success | 0.739918 | Success |
| Linear complexity | 0.574903 | Success | 0.534146 | Success | 0.455937 | Success | 0.455937 | Success |
| Image | Plaintext | Ciphertext |
|---|---|---|
| 1.4.01 | 6.3291 | 7.9998 |
| 1.4.02 | 7.1882 | 7.9998 |
| 1.4.03 | 6.6188 | 7.9998 |
| 1.4.04 | 6.1911 | 7.9998 |
| 1.4.05 | 7.1177 | 7.9998 |
| 1.5.01 | 5.6826 | 7.9993 |
| 1.5.02 | 5.8145 | 7.9993 |
| 1.5.03 | 6.9857 | 7.9993 |
| 1.5.04 | 6.4154 | 7.9993 |
| 1.5.05 | 6.8087 | 7.9993 |
| 1.5.06 | 5.1332 | 7.9993 |
| 1.5.07 | 6.7359 | 7.9993 |
| Black | 0 | 7.9993 |
| White | 0 | 7.9992 |
| Average | 5.5015 | 7.9995 |
| Algorithms | SFACF-IE | Ref. [34] | Ref. [35] | Ref. [36] | Ref. [37] | Ref. [38] |
|---|---|---|---|---|---|---|
| Information entropy | 7.9995 | 7.993 | 7.9995 | 7.9993 | 7.9992 | 7.9972 |
| Image | Size | Plaintext | Ciphertext | ||||
|---|---|---|---|---|---|---|---|
| Horizontal | Vertical | Diagonal | Horizontal | Vertical | Diagonal | ||
| 1.4.01 | 1024 × 1024 | 0.9468 | 0.9172 | 0.9175 | −0.0002 | −0.0005 | 0.0011 |
| 1.4.02 | 0.9749 | 0.9347 | 0.9209 | −0.0002 | −0.00002 | 0.0005 | |
| 1.4.03 | 0.9700 | 0.9557 | 0.9503 | −0.0010 | −0.0009 | 0.0005 | |
| 1.4.04 | 0.9739 | 0.9691 | 0.9633 | 0.0006 | 0.0007 | 0.0006 | |
| 1.4.05 | 0.9894 | 0.9734 | 0.9670 | 0.0012 | 0.0010 | −0.0011 | |
| 1.5.01 | 0.8383 | 0.8956 | 0.7945 | −0.0003 | −0.0053 | −0.0009 | |
| 1.5.02 | 0.8893 | 0.8940 | 0.8043 | 0.0009 | 0.0030 | −0.0003 | |
| 1.5.03 | 0.8821 | 0.9214 | 0.8119 | 0.0006 | 0.0019 | −0.0004 | |
| 1.5.04 | 0.7553 | 0.7146 | 0.5593 | −0.0006 | −0.0014 | 0.0001 | |
| 1.5.05 | 0.9510 | 0.9582 | 0.9206 | −0.0015 | 0.0039 | −0.0006 | |
| 1.5.06 | 0.6165 | 0.5006 | 0.4633 | 0.0020 | 0.0017 | −0.0017 | |
| 1.5.07 | 0.7163 | 0.8144 | 0.5950 | 0.0007 | 0.0003 | −0.0024 | |
| Black | 1 | 1 | 1 | 0.00003 | −0.0022 | 0.0031 | |
| White | 1 | 1 | 1 | 0.0012 | −0.0019 | −0.0016 | |
| Average | 0.8931 | 0.8892 | 0.8334 | 0.0002 | 0.00005 | −0.0002 | |
| Algorithms | SFCF-IE | Ref. [34] | Ref. [35] | Ref. [36] | Ref. [37] | Ref. [38] |
|---|---|---|---|---|---|---|
| Horizontal | 0.0002 | 0.0048 | −0.0042 | 0.0022 | −0.0519 | −0.0016 |
| Vertical | 0.00005 | −0.0025 | −0.0049 | 0.0017 | −0.0385 | −0.0026 |
| Diagonal | −0.0002 | −0.0072 | −0.0045 | 0.0019 | 0.0046 | 0.0116 |
| Number | Statistical Test | Plaintext | Ciphertext | ||
|---|---|---|---|---|---|
| p-Value | Result | p-Value | Result | ||
| 1 | Longest run of ones | 0 | Fail | 0.151616 | Success |
| 2 | Overlapping template matching | 0 | Fail | 0.611108 | Success |
| 3 | Random excursions variant | 0 | Fail | 0.949602 | Success |
| 4 | Rank | 0 | Fail | 0.016431 | Success |
| 5 | Frequency | 0 | Fail | 0.258961 | Success |
| 6 | Universal | 0 | Fail | 0.559523 | Success |
| 7 | Random excursions | 0 | Fail | 0.602458 | Success |
| 8 | Block frequency | 0 | Fail | 0.199580 | Success |
| 9 | Cumulative sums | 0 | Fail | 0.855534 | Success |
| 10 | Runs | 0 | Fail | 0.113706 | Success |
| 11 | Serial | 0 | Fail | 0.714660 | Success |
| 12 | Spectral | 0 | Fail | 0.509162 | Success |
| 13 | Approximate entropy | 0 | Fail | 0.258961 | Success |
| 14 | Non-overlapping template matching | 0 | Fail | 0.953553 | Success |
| 15 | Linear complexity | 0 | Success | Fail | Success |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hu, Y.; Wu, H.; Zhou, L. A Novel Hyperchaotic 2D-SFCF with Simple Structure and Its Application in Image Encryption. Entropy 2022, 24, 1266. https://doi.org/10.3390/e24091266
Hu Y, Wu H, Zhou L. A Novel Hyperchaotic 2D-SFCF with Simple Structure and Its Application in Image Encryption. Entropy. 2022; 24(9):1266. https://doi.org/10.3390/e24091266
Chicago/Turabian StyleHu, Yongsheng, Han Wu, and Luoyu Zhou. 2022. "A Novel Hyperchaotic 2D-SFCF with Simple Structure and Its Application in Image Encryption" Entropy 24, no. 9: 1266. https://doi.org/10.3390/e24091266
APA StyleHu, Y., Wu, H., & Zhou, L. (2022). A Novel Hyperchaotic 2D-SFCF with Simple Structure and Its Application in Image Encryption. Entropy, 24(9), 1266. https://doi.org/10.3390/e24091266







