In this section, we apply our game-theoretic, compositional approach to show how a defender can mitigate an attacker’s typical timing side-channel attack, while avoiding the usual burden imposed on the password-checker’s efficiency by measures that make time consumption constant.
The following sections are organized as follows: We first provide a formalization of the trade-off between efficiency and security in password checkers using our framework of leakage games. We then illustrate the approach in a simple instance of the program for 3-bit passwords. Finally, we provide general results for the n-bit case regarding the defender’s optimal strategy in equilibrium.
7.1. Modeling the Trade-Off between Efficiency and Security as a Game
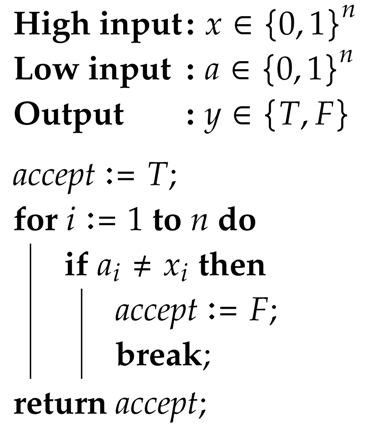
Consider the password-checker PWD1…n of Algorithm 1, which performs a bitwise-check of an n-bit low-input provided by the attacker against an n-bit secret password . The bits are compared in increasing order (1, 2, …, n), with the low-input being rejected as soon as it mismatches the secret, and accepted otherwise.
| Algorithm 1: Password-checker PWD1…n. |
![Entropy 20 00382 i001 Entropy 20 00382 i001]() |
The attacker can choose low-inputs to try to gain information about the password. Obviously, in case PWD1…n accepts the low-input, the attacker learns that the password value is . Yet, even when the low-input is rejected, there is some leakage of information: from the duration of the execution, the attacker can estimate how many iterations have been performed before the low-input was rejected, thus inferring a prefix of the secret password.
To model this scenario, let be the set of all possible n-bit passwords and be the set of observables produced by the system. Each observable is an ordered pair whose first element indicates whether or not the password was accepted (T or F, respectively), and the second element indicates the duration of the computation (1, 2, …, or n iterations).
For instance, consider a scenario with 3-bit passwords. Let
PWD123 be a password checker that performs the bitwise comparison in increasing order (1, 2, 3). Channel
in
Table 4 models
PWD123’s behavior when the attacker provides low-input
. Note that this channel represents the fact that
PWD123 accepts the low-input when the secret is
(the channel outputs
with probability one), and otherwise rejects the low-input in a certain number of steps (e.g., the checker rejects the low-input in two steps when the password is
, so in this case, the channel outputs
with probability one).
To quantify the password checker’s leakage of information, we will adopt Bayes vulnerability, so the prior Bayes vulnerability will correspond to the probability that the attacker guesses correctly the password in one try, whereas the posterior Bayes vulnerability will correspond to the probability that the attacker guesses correctly the password in one try, after he/she observes the output of the channel (i.e., after he/she has measured the time needed for the checker to accept or reject the low-input). For instance, in the 3-bit password scenario, if the prior distribution on all possible 3-bit passwords is , the corresponding prior Bayes vulnerability is . For prior above, the posterior Bayes vulnerability of channel is , which represents an increase in Bayes vulnerability of about ).
A way to mitigate this timing side-channel is to make the checker’s execution time independent of the secret. This can be done by by eliminating the
break command within the loop in
PWD1…n, so no matter when the matching among high and low input happens, the password checker will always need
n iterations to complete. For instance, in the context of our 3-bit password example, we can let
PWDcons be a constant-time 3-bit password checker that applies this counter measure. Channel
from
Table 5 models
PWDcons’s behavior when the attacker’s low-input is
. Note that this channel reveals only whether or not the low-input matches the secret value, but does not allow the attacker to infer a prefix of the password. Indeed, this channel’s posterior Bayes vulnerability is
, which brings the multiplicative Bayes leakage down to an increase of only about
.
However, the original program is substantially more efficient than the modified one. Consider the general case of
n-bit passwords and assume that either the password, or the program’s low input, is chosen uniformly at random. Because of this assumption, each bit being checked in the original program has probability
of being rejected. Hence, the program will finish after one iteration with probability
, after two iterations with probability
, and so on, up to the
n-th iteration. After that, the program always finishes, so with the remaining probability
, the program finishes after
n iterations, giving a total expected time of:
The above derivation is based on the series . Hence, the expected running time of the original program (under the uniform assumption) is constant: always bounded by two, and converging to two as n grows. On the other hand, the running time of the modified constant-time program is n iterations, an -fold increase.
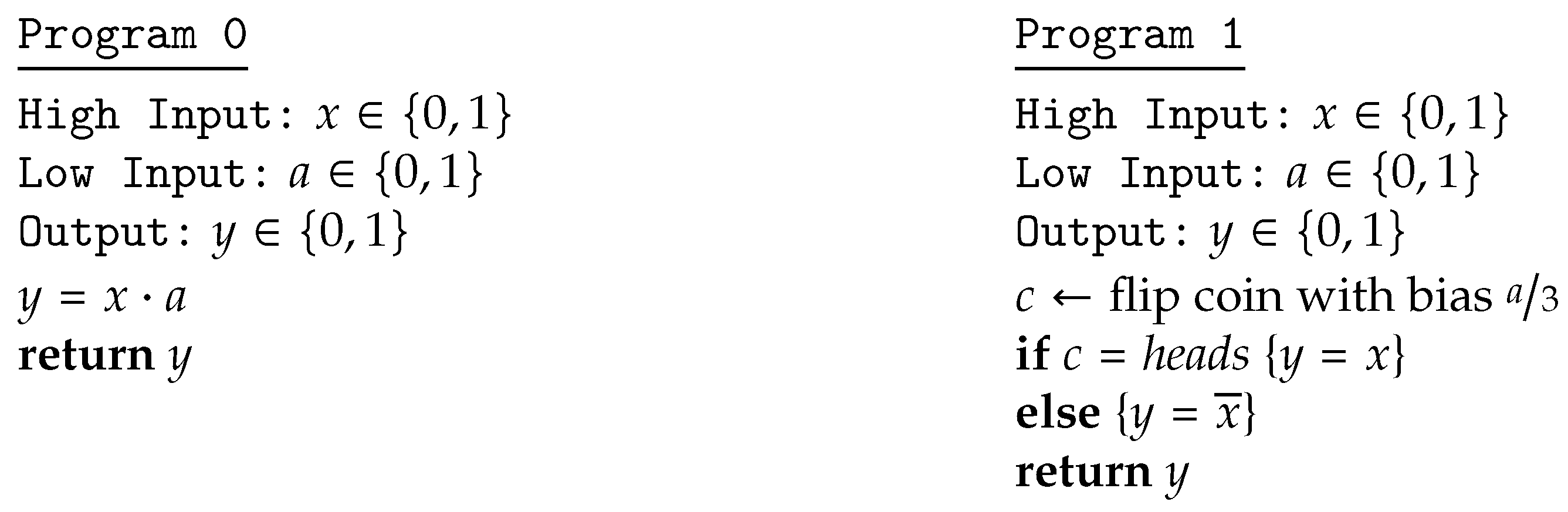
Seeking some compromise between security and efficiency, assume the defender can employ different versions of the password-checker, each performing the bitwise comparison among low-input a and secret password x in a different order. More precisely, there is one version of the checker for every possible order in which the index i ranges in the control of the loop in Algorithm 1.
To determine a defender’s best choice of which versions of the checker to run, we model this problem as a game. The attacker’s set of actions consists of all possible low-inputs to the checker, and the defender’s set of actions consists of all orders in which the checker can perform the bitwise comparison. There is, then, a channel for each possible combination of , . In our framework, the payoff of a mixed strategy profile is given by: For each pure strategy profile , the payoff of the game will be the posterior Bayes vulnerability of the resulting channel (since, if we are measuring the information leakage, the prior vulnerability is the same for every channel once the prior is fixed).
In the 3-bit password scenario, the attacker’s actions
are all possible 3-bit low-inputs, and the defender’s
are all possible versions of the password checker (each action represents the order in which the 3 bits are checked).
Table 6 depicts the corresponding payoffs of all 48 possible resulting channels
with
,
, when the prior is still
. Note that the attacker’s and defender’s actions substantially affect the effectiveness of the attack: vulnerability ranges between 0.4934 and 0.9311 (and so, multiplicative leakage is in the range between an increase of
and one of
). Using techniques from [
6], we can compute the best (mixed) strategy for the defender in this game, which turns out to be:
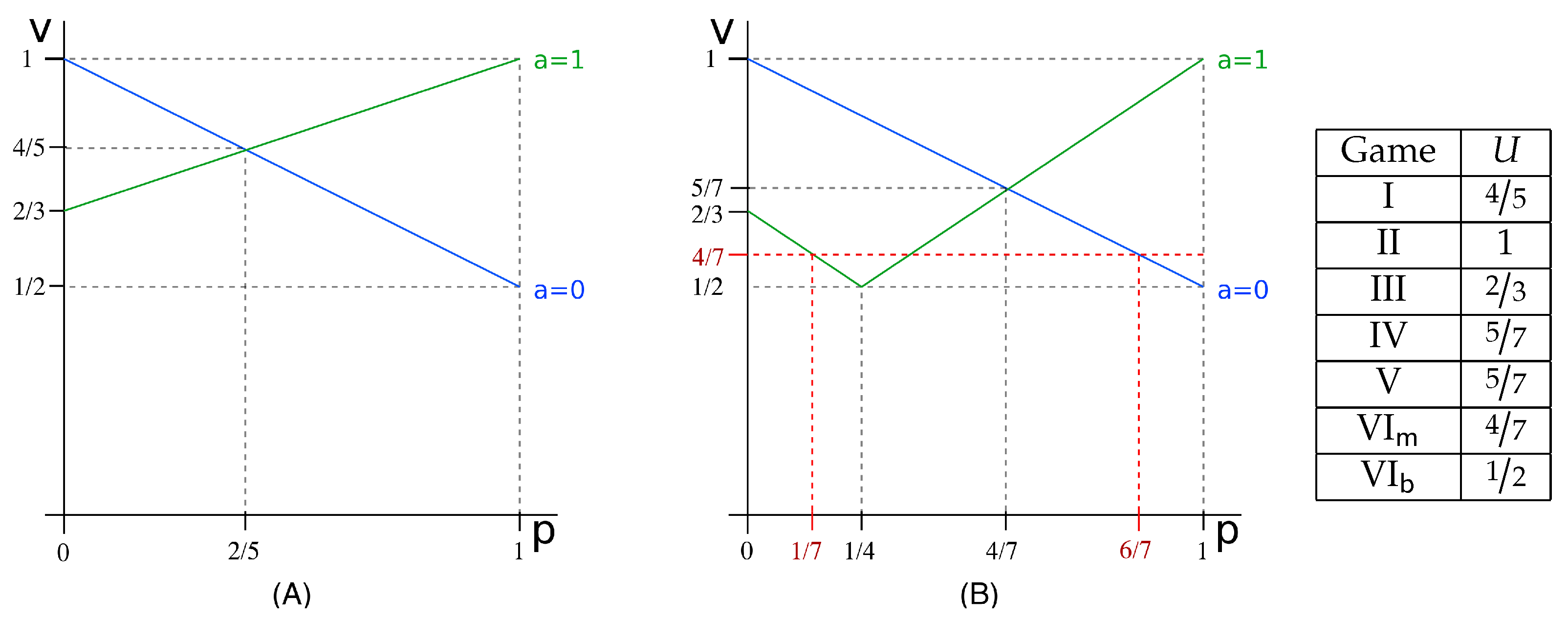
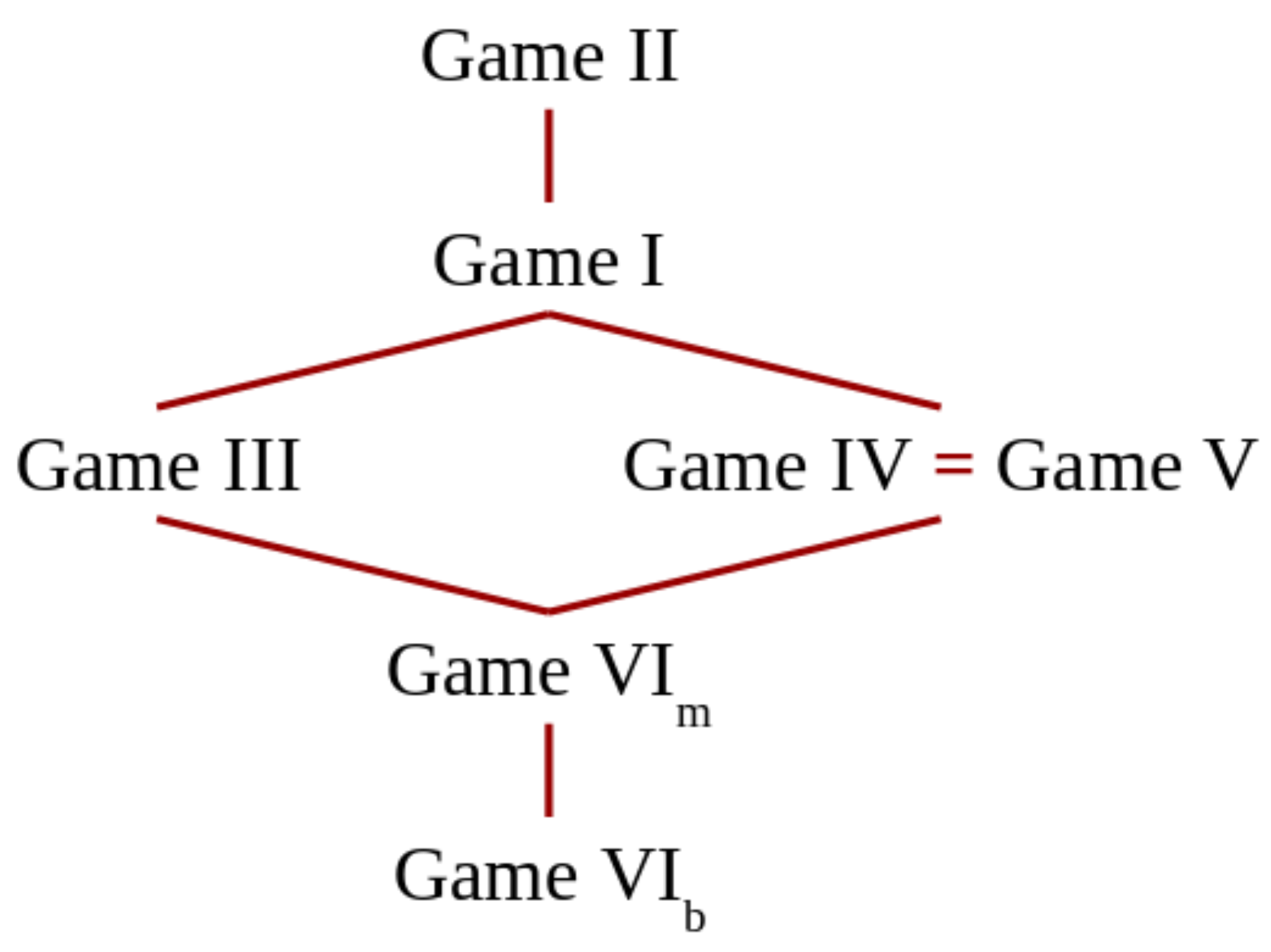
This strategy is part of an equilibrium and guarantees that for any choice of the attacker, the posterior Bayes vulnerability is at most (so the multiplicative leakage is bounded by , an intermediate value between the minimum of about and the maximum of about ).
The running time, on the other hand, of this new password-checker is the same as that of the original one. Under the assumption that either the password or the low-input is uniformly distributed, each check fails with probability , giving a total expected time of . Hence, this technique substantially decreases the program’s information leakage, without affecting at all its expected running time.
7.2. On Optimal Strategies for the Defender
Interestingly, in the 3-bit password case study from the previous section, the defender’s optimal strategy consists of uniformly sampling among all available versions of the checker. A uniform distribution seems to be an adequate candidate for the defender, but is it always the best choice for any prior and any number of bits?
We first answer this question in the case of a uniform prior
for arbitrary
n-bit passwords, which already turns out to be challenging. Under this prior, and exploiting a crucial symmetry of the password checker (see the proof of Theorem 7), we can show that all strategies for the adversary are in fact equivalent, namely:
For the defender, on the other hand, the situation is far from trivial: although all pure strategies d are still equivalent, does in general depend on . By exploiting another symmetry of the password checker together with the symmetry of , we can show that a uniform strategy is indeed optimal for the defender, as stated in the following result.
Theorem 7. Consider the password checker program of Algorithm 1 for n-bit passwords, where the attacker controls the low input to the checker and the defender controls the order in which the bits are checked. If the prior on possible passwords is uniform and the payoff is given by the posterior Bayes-vulnerability: , then the strategy where is uniform and is arbitrary is an equilibrium strategy.
Perhaps surprisingly, however, Theorem 7 does not generalize to non-uniform priors (or to different vulnerability metrics). More precisely, when the prior on passwords is not uniform, the defender may benefit from assigning different probabilities to different versions of the password checker. This subtlety arises from the fact that the defender’s goal is not to maximize the attacker’s uncertainty about the selected password checker itself (i.e., the defender’s action), but it is rather to maximize the attacker’s uncertainty about the secret value. The following examples illustrate this (perhaps counter-intuitive) fact.
Consider again a 3-bit password scenario, similar to that of the previous section. Assume that the attacker knows only that the first bit of the password is surely zero, so that the prior on secrets is:
The payoff table for this case is presented in
Table 7, and a corresponding equilibrium defender’s best strategy, computed using techniques from [
6], is:
Note that this equilibrium means that the defender never has to check the bits in the order (2, 1, 3) or in the order (3, 1, 2). The game’s payoff (i.e., posterior Bayes vulnerability) in this case is , which is smaller than the payoff of that would ensue in case the defender’s strategy were uniform. This means that, from the point of view of the defender, uniformly randomizing is not optimal.
Now, assume that the attacker knows that some passwords are more likely than others, even if all are possible, as reflected in the prior:
The payoff table for this case is presented in
Table 8, and a corresponding equilibrium defender’s best strategy can be computed to be:
Note that this equilibrium means that every version of the checker may be selected by the defender, but the probability distribution is not uniform. The game’s payoff (i.e., posterior Bayes vulnerability) in this case is , which is again smaller than the payoff of that would ensue in case the defender’s strategy were uniform.