1. Introduction
The existing world demands fast and secure communication. The bandwidth is increasing every day due to third generation, fourth generation and fifth generation technologies. Digital contents can be easily accessed through any geographical remote area because of the ideology of a global village. By advancing the technologies, smart and simple to access information from any remote station creates a massive insecurity of digital information. The security of digital multimedia is one of the vital problems of the information sciences. The widespread broadcasting and distribution of digital information over the internet, especially social media like Facebook and Twitter, have made it important to protect our most important information from theft, illegal copying, handling and sharing. The advancement of digital media technology and other multimedia related technology has made it possible to perform some standard procedures in order to improve the security of our digital images/audio/videos from being utilized criminally over the web.
There are a number of information security techniques that have been designed whose algorithms are based on cryptography, which is one of the most important branch of cryptology that is used to make an encryption scheme to secure information. Classical encryption techniques usually utilize either substitution or permutation to develop a cryptosystem; for instance, mono-alphabetical and polyalphabetic ciphers. The use of only substitution or permutation while developing any encryption scheme is susceptible to different cryptographic attacks. Consequently, the cryptosystems are getting weaker every day due to the advancement of technologies and computational powers of machines. In 1949, Claude Shannon gave the idea of confusion and diffusion, which completely changed the security mechanisms of the digital world. The information theory added a new pillar in information security. After the theory of Claude Shannon, the idea of confusion and diffusion was extensively used, which means substitution and permutation were utilized at a time in modern block ciphers [
1,
2]. According to Shannon, confusion specifies the connections between the cipher text and the key as much as complex whereas diffusion corresponds to the redundancy in the statistical data of the plaintext used in the statistical data of the cipher text. This master idea fundamentally changed the ideology of modern block and steam ciphers. The ideas of confusion and diffusion were utilized in a number of modern block ciphers namely international data encryption standard (IDEA), data encryption standard (DES), and advanced encryption standard (AES).
Thereafter, different new techniques were designed which use chaos theory, wavelets transform, discrete transforms, optics, DNA sequences and quantum spinning and rotations [
3,
4,
5,
6,
7,
8,
9,
10,
11,
12,
13,
14,
15,
16,
17,
18,
19,
20,
21,
22,
23,
24,
25,
26,
27,
28,
29,
30,
31,
32,
33,
34]. In recent times, chaos theory has been used in an extensive way for the development of image encryption mechanisms [
35,
36]. The three fundamental characteristics of chaos that have made it possible to use it in the development of encryption algorithms are sensitive to the initial condition, topological mixing, and dense periodic orbits. These three properties were closely related to cryptography. Due to the cryptographically robust characteristics of chaos, we have utilized the Lorenz chaotic system while designing our novel image encryption technique.
So far, different types of mathematical structures were utilized namely Group, Ring, Galois field and Galois ring for the construction of a substitution box (S-box), which is one of the most important nonlinear components of any modern block ciphers. The thrust of new mathematical structures for the development of encryption techniques is one of the most important areas of research in information security [
8,
11,
12,
15]. An algebraic structure equipped with a closed and left invertive binary operation is called a left almost semigroup (abbreviated as LA-semigroup). This notion was made known by Kazim and Naseeruddin in the early 1970s [
37]. Mushtaq and Yusuf discussed some important properties in [
38]. Such groupoids are also called right modular groupoids or left invertive groupoids or incorrectly as Abel Grassmann’s groupoid [
39,
40,
41]. By successive applications of the left invertive law in an arbitrary LA-semigroup, it can be seen that the medial identity
naturally holds in an LA-semigroup. It is important to mention here that every LA-semigroup is always medial but its converse is not true. It is a non-associative and non-commutative structure midway between a groupoid and commutative semigroup.
In order to define the associative powers of elements in an LA-semigroup the identity
(ss)s = s(ss) was introduced in Reference [
42]. An LA-semigroup with this additional property is called a locally associative LA-semigroup. Some important decompositions of locally associative LA-semigroups were also investigated in References [
42,
43]. Consider a locally associative LA-semigroup defined by the
Table 1.
Where , substantiates that a locally associative LA-semigroup not need to have associative powers necessarily.
The LA-semigroups, after the evolved from the study of a diverse generalization of groups and semigroups. It has become a separate branch within itself with a considerable number of research results. The reason for its procession is its natural existence in almost all mathematical contexts in which groups and semigroups have been developed.
The study of LA-semigroups has wide applications in the locally associative LA-semigroups, abelian groups, the theory of fuzzy LA-semigroups, ternary semihypergroups,
-semihypergroups, neutrosophic LA-semigroups, soft sets and the theory of non-commutative groupoids [
42,
43,
44,
45,
46,
47,
48,
49]. Here, we propose a new scheme for the encryption of images based on an inverse LA-semigroup and a modified nonlinear chaotic map, which has better confusion and diffusion characteristics that are necessary for a modern substitution-permutation network.
This article comprises of five sections. In
Section 2, we introduce fundamentals of a novel structure inverse LA-semigroups. In
Section 3, we propose an algorithm for the encryption of images. The efficiency and safety measures for the suggested algorithm are examined in
Section 4. The numerical measures are also discussed in
Section 4 to examine the response of suggested scheme against differential attacks. Finally, give conclusions in the
Section 5.
2. Preliminaries
This section is primarily related to some standard definitions, which will be quite useful in subsequent sections.
Definition 1. An LA-semigroup is a pairwhereis a non-empty set;satisfiesfor all. One can easily observe that the medial identitynaturally holds in the LA-semigroups. It is important to mention here that every LA-semigroup is always medial but its converse is not true.
Definition 2. An LA-semigroupsatisfying the left permutable lawis called LA**-semigroup. An LA-semigroup with left identity is always LA**-semigroup and LA**-semigroup naturally satisfies the paramedial identity.
We provide counter examples of three groupoids of order
in
Table 2, where (i) is a medial groupoid but not an LA-semigroup, (ii) is a left permutable groupoid, which is also paramedial but not an LA-semigroup, (iii) is a left permutable groupoid with left identity but not an LA-semigroup (see
Table 2).
Definition 3. An LA-semigroup ( equiped with left identity , that is, for all is LA-monoid. One can notice that left permutable law and paramedial law always hold in an LA-monoid . We also investigate a paramedial groupoid with a left identity is LA**-semigroup. An element for which there exist an element such that , then is called left inverse of . Right inverse for an element in an LA-monoid can also be defined analogously. It is easy to observe that if is the left inverse for an element , that is, . Then . Then . Showing that left and right inverses are unique in an LA-monoid. An LA-monoid, in which each element has its left inverse element is known as LA-group.
Definition 4. An LA-semigroupsatisfying the weak associative lawis called LA*-semigroup. The identitiesare equivalent in an LA-semigroup.
Definition 5. LA-group is an LA-monoid in which each element has a unique left multiplicative inverse. LA-monoids are special cases of LA-semigroups whereas LA-groups are special cases of LA-monoid.
Definition 6. An LA-semigroupis unipotent iffor all. We define a transformationbyfor all.
Proposition 1. An LA-semigroupis unipotent if and only if, where.
Lemma 1. Every unipotent left cancellative LA-semigroup is paramedial.
Let ( and be any two LA-semigroups of the same order. A mapping is a homomorphism if it preserves the multiplication, that is, and an anti-homomorphism if it reverts the multiplication that is, . If such mapping is bijective, then it is known as isomorphism and anti-isomorphism respectively. If such a bijection exists, then the groupoids are isomorphic and anti-isomorphic respectively.
For instance, if two LA-semigroups have isomorphic tables, they have the same structural properties. So we say that an isomorphism is an action between two multiplication tables. If we are provided with a permutation
of the elements of
, we transform the table by permuting the rows according to
, then each column, and permuting the values at the end. An anti-isomorphism is an action followed by transposing the resulting table of an isomorphism. The outcome of applying the permutation
is given in
Table 3 (ii).
Table 3 (i) and
Table 3 (ii) are isomorphic. If
has
elements then atmost multiplication tables isomorphic to given LA-semigroup.
Theorem 1. Letbe an LA-semigroup satisfying paramedical law. Then, one has
- (i)
is an anti-endomorphism.
- (ii)
is sub LA-semigroup of.
- (iii)
is a congruence relation.
Definition 7. An LA-semigroup, in which for everythere exists a uniquefor whichandis called an inverse LA-semigroup. This notion was made known by Mushtaq and Iqbal in Reference [9]. They proved some interesting facts and a famous Wagner Preston theorem on the representation of inverse LA-semigroups [9]. An inverse LA*-semigroup and inverse LA**-semigroup are defined analogously. Some interesting results are that every LA-group is an inverse LA-semigroup more precisely an inverse LA**-semigroup but the converse is not true [10]. Presentation of a semigroup is a set of generators and relations which completely depicts a particular semigroup of a finite or an infinite semigroup. Ruskuc worked on semigroup presentations in his PhD thesis [11]. Here, we find thatrepresents an inverse LA**-semigroup of order 256 generated by. Here, by an S-box of order, we mean a latin square of sizewhose entries are selected from a set ofdifferent symbols in such a way that there is no repetition in any row and column of the table. 3. Proposed Digital Image Encryption Algorithm
The present section deals with the encryption procedure.
3.1. Image Encryption
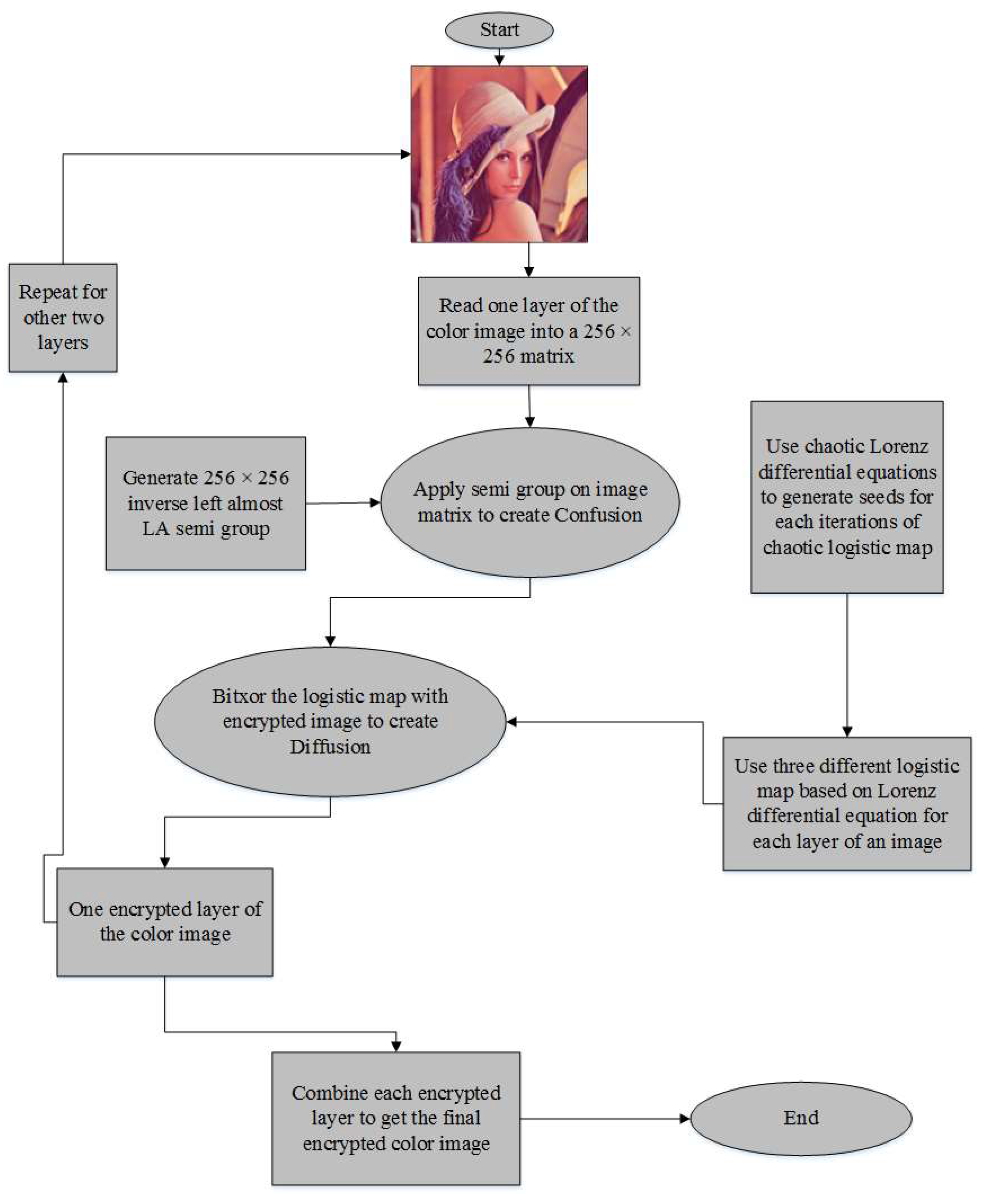
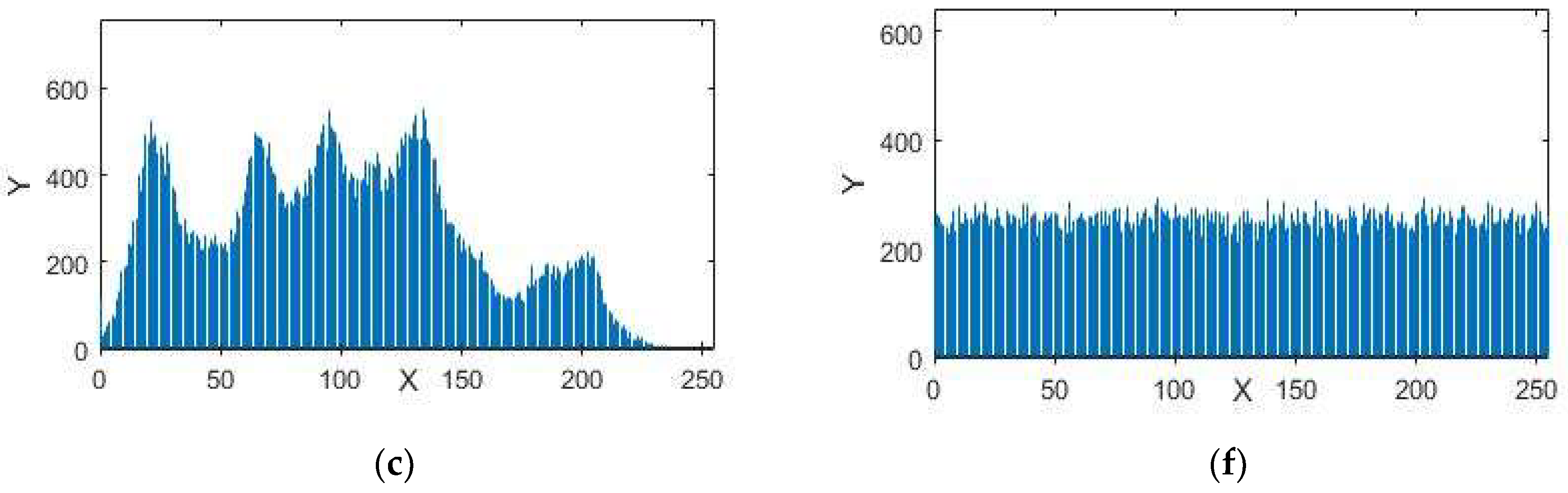
Designed image encryption techniques comprise of confusion and diffusion. As illustrated in
Figure 1, the encryption method is based on the steps given below:
Step 1: Take a standard digital color image of size
Step 2: Read the inverse left almost LA-semigroup of order m
Step 3: Apply a substitution transformation by using the LA-semigroup as listed in Step 2, which adds confusion to the proposed algorithm.
Step 4: Generate chaotic sequences using Lorenz chaotic differential equations with a logistic map (seed values for each iteration comes from the Lorenz chaotic differential equation utilized three chaotic logistic maps used seeds from x, y and z directions solutions of Lorenz chaotic differential equations).
Step 5: Apply a bitwise addition under modulo 2, of confused image produced in Step 3 with the chaotic sequences generated in Step 4 for each layer of the digital image that uses x component values for the red layer, y component values from the green layer and z component values of the logistic map for the blue layer of a given image.
Step 6: Apply all of the above steps on each layer of the digital image.
Step 7: Display the encrypted image.
3.2. Image Decryption
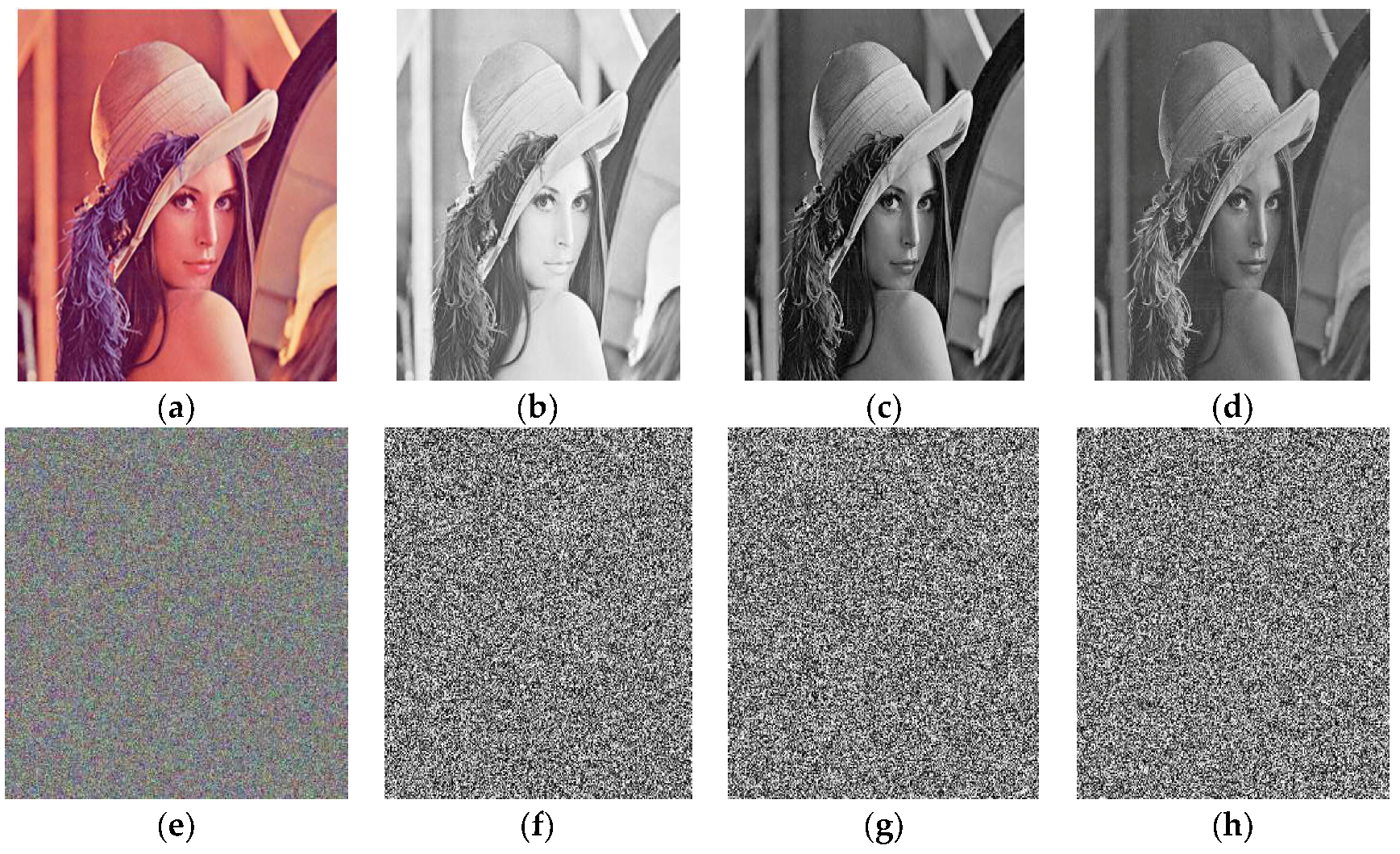
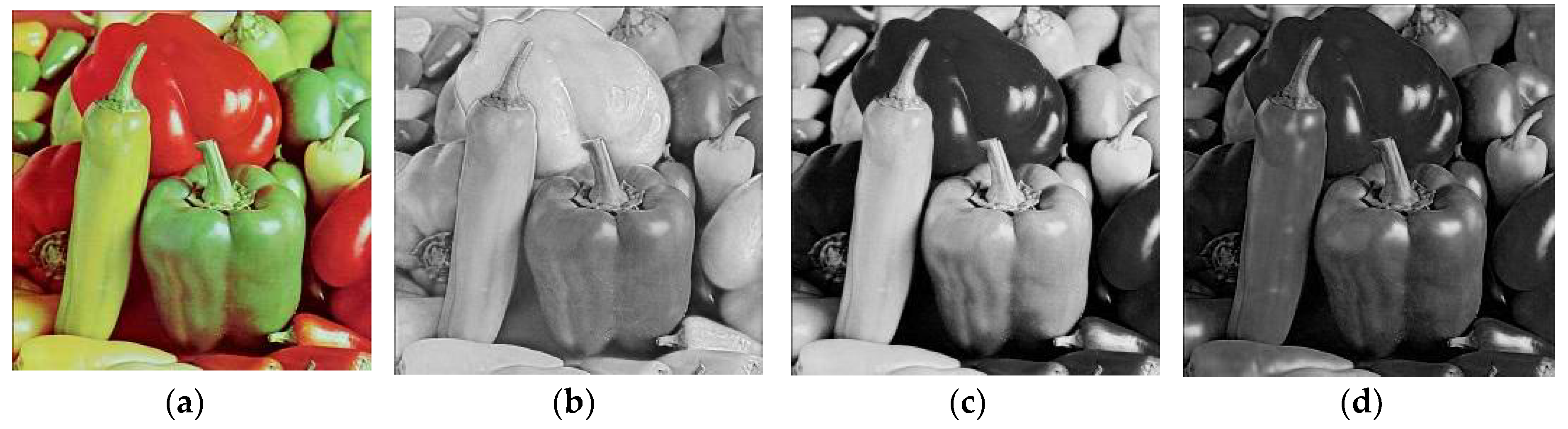
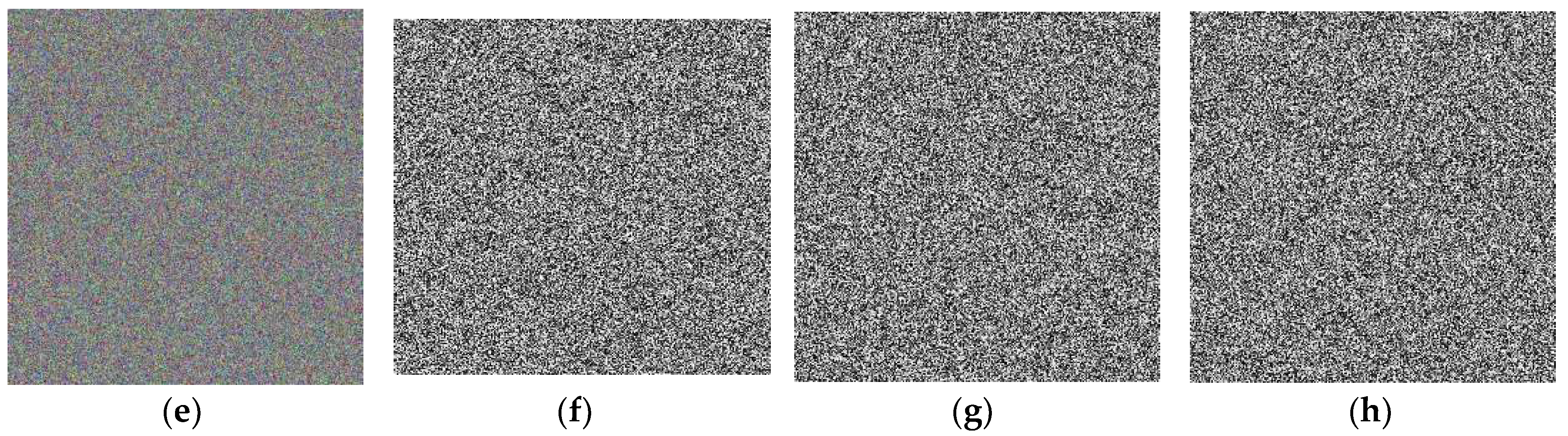
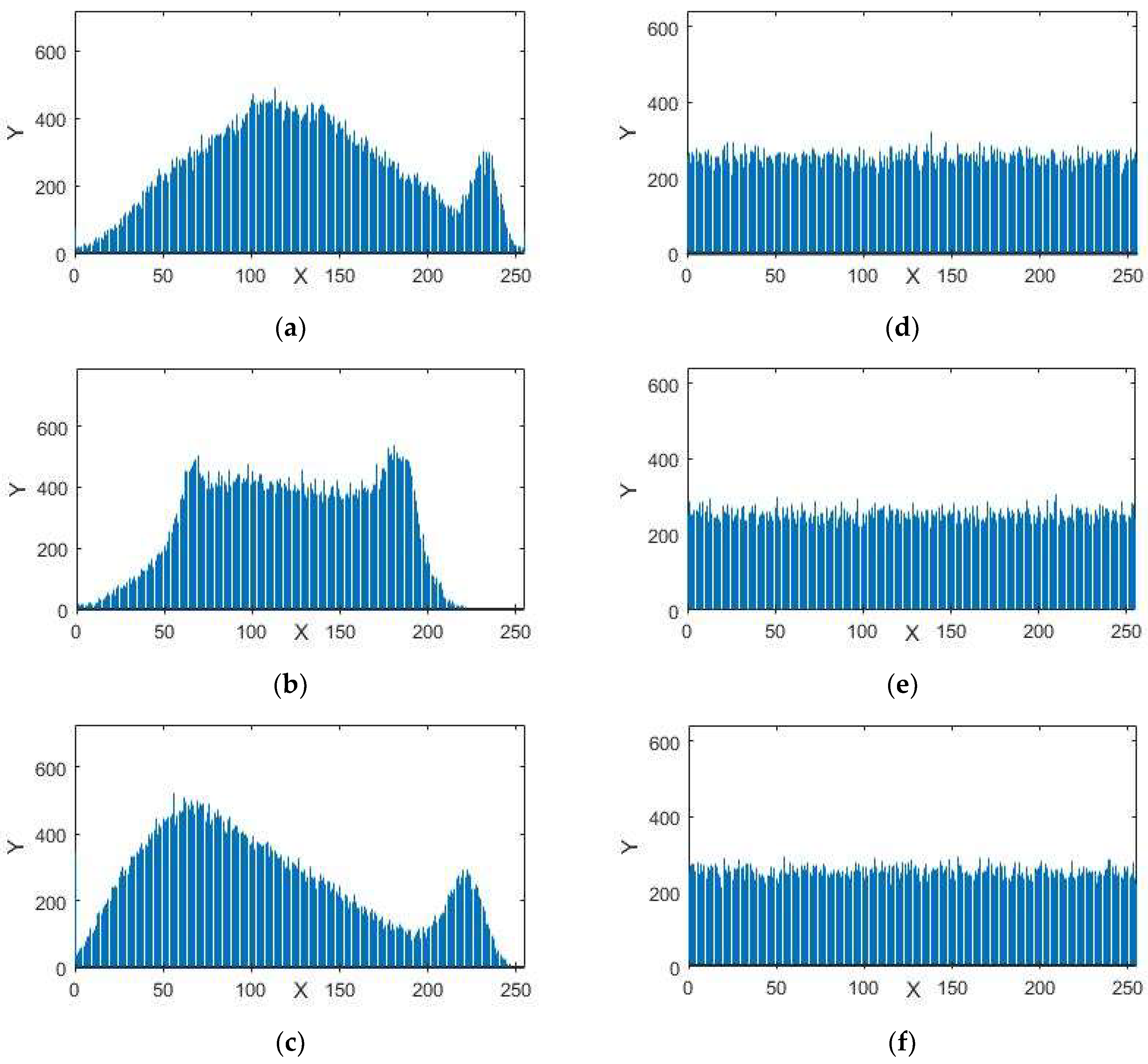
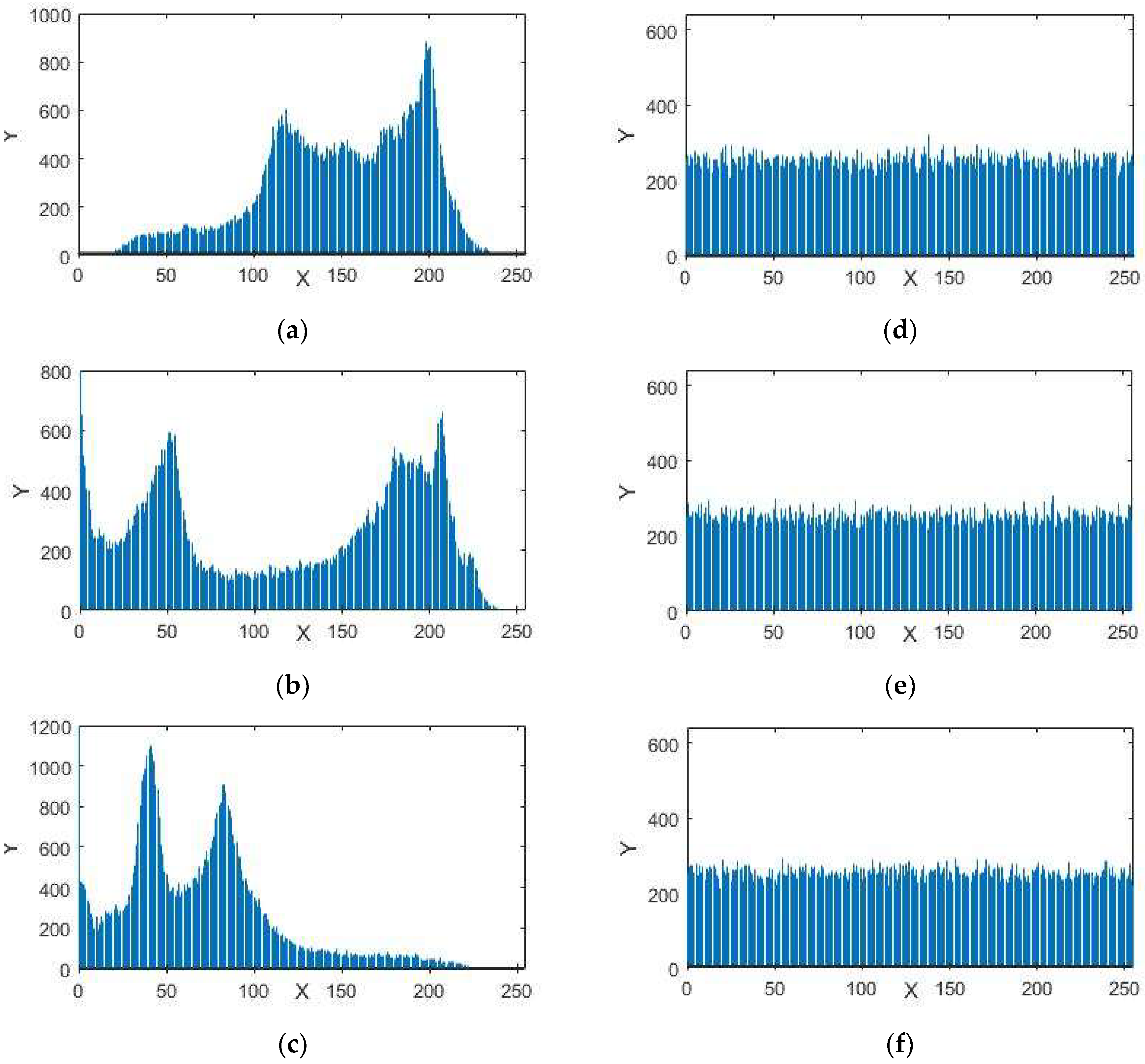
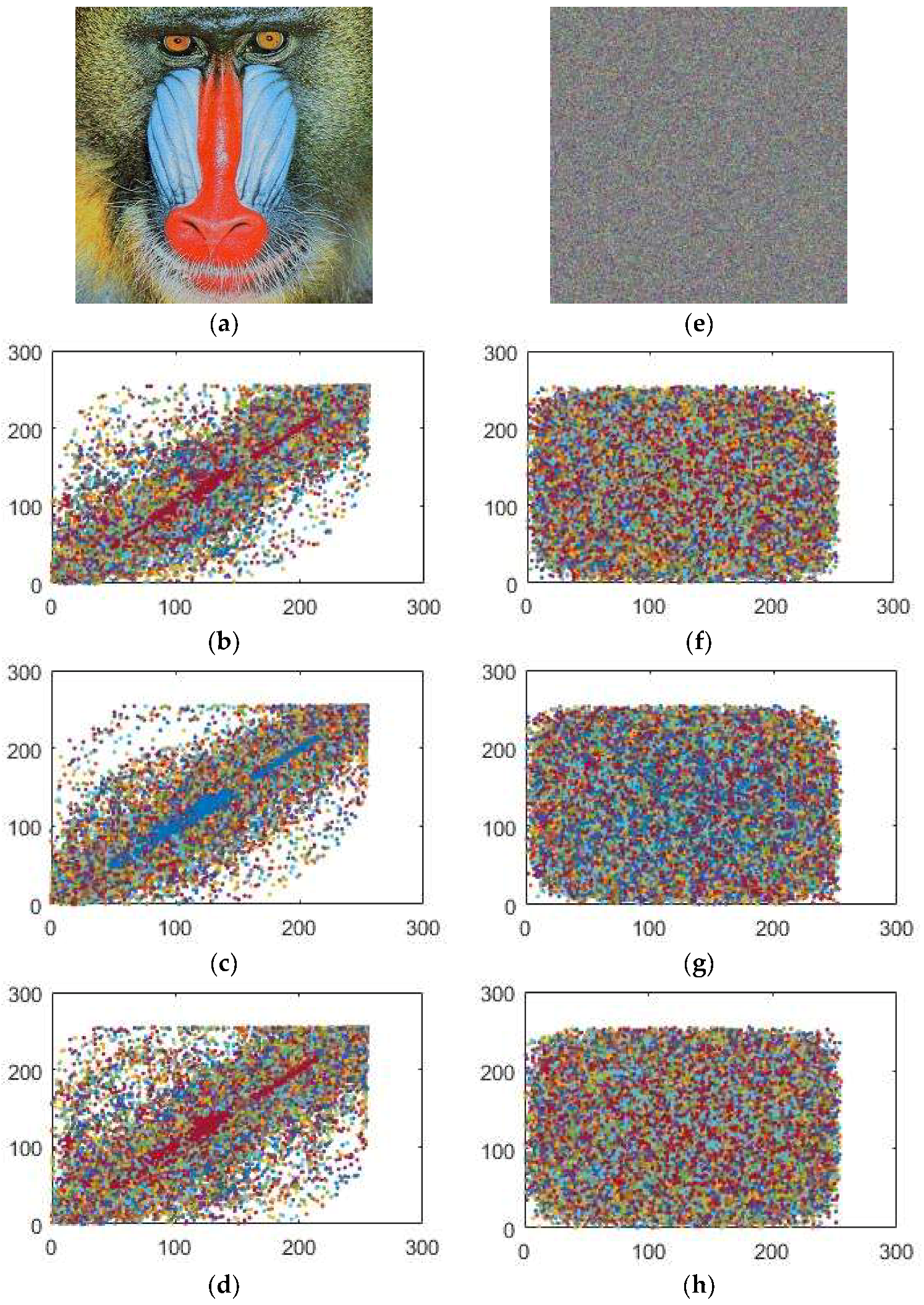
This method is used as a reverse process of our encryption procedure. The encrypted images through our proposed algorithm can be seen in
Figure 2,
Figure 3 and
Figure 4 respectively.