1. Introduction
The rapid advancement of quantum computing has precipitated an urgent need for cryptographic primitives that remain secure against quantum-capable adversaries [
1,
2]. Traditional public-key cryptosystems, which derive their security from the hardness of integer factorization or the discrete logarithm problem in finite fields and elliptic curves, are rendered vulnerable by Shor’s algorithm [
3]. This existential threat has catalyzed global standardization efforts, notably by NIST and ETSI, to identify and vet post-quantum cryptographic (PQC) schemes [
4,
5]. The current PQC landscape is dominated by several families [
6], including lattice-based constructions (e.g., Kyber [
7,
8] and Dilithium [
9,
10]), hash-based signatures (e.g., SPHINCS+ [
11]), code-based encryption (e.g., Classic McEliece [
12,
13]), and multivariate cryptography [
14,
15].
Beyond these established families, there is growing interest in exploring algebraic constructions that deliberately depart from well-studied abelian settings and from assumptions that are already deeply integrated into the current standardization pipeline. Such exploratory approaches do not aim to replace mature PQC candidates, but rather to investigate alternative mathematical structures whose associated computational problems fall outside the scope of known classical and quantum algorithmic techniques. In this sense, post-quantum cryptography also encompasses the systematic study of non-standard hardness assumptions and algebraic phenomena that may give rise to future cryptographic primitives.
This work advances an alternative paradigm grounded in the linear algebra of finite fields. Expanding upon the foundational matrix-based framework introduced in [
16], we delve deeper into the structural properties of the core mathematical objects involved and repurpose them as building blocks for a challenge–response authentication mechanism rather than for a traditional key exchange scheme. Our constructions operate within the algebra of
matrices over finite fields
, and rely on classical hardness assumptions involving noncommutative matrix problems, including the difficulty of factorizing structured matrix products and solving conjugacy-type equations in matrix groups [
17,
18].
The contribution of this work should be understood as an algebraic heuristic that is intentionally positioned outside the canon of reduction-based PQC schemes. We do not claim a formal post-quantum security reduction, nor do we assert resistance against all conceivable quantum adversaries. Instead, we focus on a class of noncommutative and non-diagonalizable matrix constructions whose induced computational problems do not appear to admit known reductions to abelian hidden subgroup problems or to other structures efficiently solvable by Shor-type quantum algorithms. From this perspective, the proposed framework is investigated as a potential post-quantum-oriented construction, motivated by structural considerations rather than by established complexity-theoretic guarantees.
Throughout the paper, our security discussion is explicitly carried out in the classical adversarial model; a full post-quantum analysis is beyond the scope of the present work.
A central tenet of our approach is the deliberate construction and utilization of non-diagonalizable matrices as fundamental building blocks. By ensuring that the relevant matrix products lack a full basis of eigenvectors, we prevent a straightforward reduction of exponentiation to a set of simpler, independent scalar discrete logarithm problems within the field, a common pitfall in naive matrix-based schemes. In particular, we focus on upper triangular Toeplitz matrices with a single Jordan block and exploit the structured way in which their powers depend on a small set of parameters and on the exponent.
The primary contributions of this article are twofold. First, we present a systematic and verifiable method for generating invertible non-diagonalizable matrices suitable for cryptographic applications. This is achieved through the controlled product of a diagonal matrix and a specifically structured upper triangular matrix, guaranteeing a defective eigenvalue structure that resists diagonalization. Second, we conduct a detailed structural analysis of matrix exponentiation for upper triangular Toeplitz matrices. We derive closed-form expressions for their powers and introduce the concept of autopotency—a collection of deterministic algebraic relationships between the entries of a matrix and the entries of its powers. These relationships can be efficiently verified by legitimate users in possession of certain secret parameters, but give rise to nonlinear multivariate systems of equations for any adversary attempting to deduce the base matrix or exponent from a public power, which we treat as a classical hardness assumption in our heuristic security discussion.
Building on these algebraic ingredients, we then design and analyze a noncommutative challenge–response protocol based on cyclic products of secret matrices and their powers. A prover holds a family of secret factors whose ordered products form a cycle of mutually conjugate matrices; the corresponding powered products are made public. In an authentication round, the verifier issues a challenge that selects one of these conjugacy relations, and the prover must reveal the appropriate secret factor so that the resulting conjugation equation is satisfied. We formalize the underlying factor recovery and conjugacy problems, state an explicit algebraic conjecture capturing their presumed hardness, and discuss how these problems differ from standard abelian discrete logarithm settings.
While challenge–response authentication is a classical paradigm, the novelty of the present work lies in its instantiation through structured non-diagonalizable matrix products, cyclic conjugacy relations, and autopotent algebraic constraints. The resulting protocol illustrates how these ingredients can be combined to define authentication tasks in noncommutative settings that are algebraically distinct from conventional discrete-logarithm-based constructions.
The remainder of this article is organized as follows.
Section 2 reviews the algebraic background and notation used throughout the paper, including matrix groups over finite fields and the Toeplitz structures that underlie our constructions.
Section 3 introduces the core noncommutative challenge–response authentication protocol, specifying the key generation procedure, the public data, and the interactive verification mechanism.
Section 4 develops a systematic methodology for constructing invertible non-diagonalizable matrices, illustrated with a concrete example.
Section 5 presents the theoretical foundations of autopotency in upper triangular Toeplitz matrices, deriving closed-form expressions for matrix powers and formulating the associated parameter recovery problems.
Section 6 discusses practical parameter considerations, including recommended ranges for the matrix dimension and field size, as well as storage and implementation aspects.
Section 7 reports our experimental evaluation, including preliminary performance measurements and computational complexity estimates for representative parameter sets. Finally,
Section 8 summarizes the main contributions, and outlines directions for future research and implementation.
2. Algebraic Preliminaries
This section delineates the core protocol studied in this work. Rather than deriving a shared secret key as in a classical Diffie–Hellman-type construction, we now use the matrix framework as the basis for a noncommutative challenge–response authentication mechanism. The analysis incorporates the specific constructions of non-diagonalizable matrices detailed in
Section 4 and the structural properties of their powers developed in
Section 5. All cryptographic operations take place in the algebra of
matrices over the finite field
, with
denoting the corresponding matrix space. The prime
p is assumed to be cryptographically large (e.g.,
), so that the associated search spaces are beyond the reach of exhaustive methods. The fundamental security of the protocol is predicated on classical hardness assumptions involving structured matrix factorization and conjugacy problems within this noncommutative setting [
17,
18]. These assumptions are investigated here as part of a structurally motivated research direction, aimed at identifying algebraic configurations whose induced problems fall outside the scope of standard abelian reductions.
The protocol’s resilience stems from the deliberate choice of secret matrices in a noncommutative matrix group. Concretely, a prover (Bob) samples a family of secret matrices
from a structured set
of invertible, non-diagonalizable matrices constructed as in
Section 4. From this family, he forms a cyclic sequence of ordered products
where indices are taken modulo
n, so that
is obtained from
by a cyclic rotation of the factors. By construction, each
is invertible and non-diagonalizable, and the family
consists of mutually conjugate elements:
for a suitable rotation permutation
of
determined by the cyclic ordering of the factors.
To obfuscate the underlying factors while preserving this conjugacy structure, Bob selects a secret exponent
and publishes the powered products
Since conjugacy is stable under integer powers, the family
satisfies
while the individual factors
remain hidden. In the protocol, these relations are used as the basis for an interactive test of knowledge: a verifier challenges the prover to exhibit a factor
consistent with a specific conjugacy relation among the public powered products.
2.1. Underlying Hardness Assumptions and Conjugacy Perspective
The public information in our framework consists of a family of powered products built from secret matrices as described above. At a high level, these matrices are related by conjugation via the unknown factors , and the challenge–response mechanism exploits precisely these conjugacy relations.
In this setting, we formulate the following problems.
Both problems can be viewed as structured instances of the classical Conjugacy Search Problem (CSP) in non-abelian groups: given elements with , the problem consists in recovering a conjugator u. In our case, the role of g and h is played by powered products such as and , and the potential conjugators are drawn from the closed family generated by the secret matrices .
In contrast to generic instances of CSP in matrix groups, the problems considered here are tightly constrained by the cyclic construction of the products, the fixed exponentiation layer, and the enforced non-diagonalizable Toeplitz structure of the matrices involved. These restrictions induce coupled algebraic relations that are not present in unconstrained conjugacy settings and play a central role in the intended hardness of PPIP and FRP.
We emphasize that neither PPIP nor FRP is intended as a unique recovery problem. The existence of multiple algebraic solutions arising from centralizers or commuting elements does not undermine the security interpretation of the protocol, since authentication relies solely on the ability to verify a conjugacy relation, rather than on reconstructing a canonical secret representation. This non-uniqueness is not a flaw of the formulation, but a direct consequence of the underlying non-abelian and structured setting. In the context of the proposed challenge–response protocol, the role of PPIP and FRP is to capture the difficulty of producing responses that are consistent with the cyclic conjugacy relations induced by the secret family, rather than to identify a unique secret representation. While alternative matrices may satisfy isolated conjugacy relations, such solutions do not, in general, enable an adversary to respond correctly to arbitrary challenges across multiple protocol executions without access to the full structured family.
The PPIP focuses on the existence of a non-trivial conjugator linking two powered products, whereas FRP aims at recovering an explicit set of factors consistent with the published products. In both cases, the powered exponent x and the deliberately engineered non-diagonalizable structure are intended to move the instance away from settings where conjugacy can be efficiently decided.
2.2. Scope, Efficiency, and Intended Use
The primary objective of the present work is not to propose a drop-in replacement for established authentication standards, nor to compete directly with optimized post-quantum authentication schemes. Instead, the contribution is conceptual and structural: it introduces a new class of algebraic authentication problems arising from the conjugacy and factorization properties of non-diagonalizable matrix products. From a practical standpoint, the protocol is best suited for settings in which authentication is performed infrequently, or where one-time or bounded-use credentials are acceptable. Typical examples include bootstrapping phases, device provisioning, or experimental authentication mechanisms in constrained algebraic environments. The intentional revelation of individual secret factors during authentication makes the scheme inappropriate for indefinite reuse without refresh mechanisms, a limitation that is explicitly acknowledged. Regarding efficiency, the dominant computational costs arise from matrix multiplication and exponentiation in . For the illustrative dimensions considered in this work (), these operations are computationally feasible, while larger values of k quickly incur cubic-time overhead. Consequently, the intended hardness of the construction is not derived from large matrix dimensions, but from the combination of a large underlying field , the secret exponent x, and the structured nonlinearity induced by Toeplitz and autopotent constraints. No implementation or performance benchmarks are claimed in this work. A detailed evaluation of concrete parameter choices, optimization strategies, and implementation trade-offs is left as future work. The present manuscript should therefore be understood as a foundational exploration of algebraic authentication mechanisms in noncommutative settings, rather than as a fully engineered cryptographic primitive.
At a conceptual level, the bounded-use interpretation of the proposed protocol shares a high-level similarity with classical one-time or limited-use authentication mechanisms, such as one-time-password (OTP) schemes [
19,
20], in which security is achieved by consuming secret materials over time. However, the similarity is purely operational rather than structural: in contrast to hash-based or symmetric constructions, the present framework is entirely algebraic and relies on noncommutative conjugacy relations between structured matrix products, as explored in other noncommutative cryptographic contexts [
21]. The objective of this work is therefore not to replicate or optimize existing OTP-style mechanisms, but to explore a distinct algebraic design space in which bounded-use authentication emerges naturally from the intentional revelation of structured factors.
2.3. Global Consistency Verification of the Powered Product Family
In the interactive challenge–response mechanism defined earlier, each round reveals a single secret matrix
and allows the verifier to check a local conjugacy condition of the form
or the corresponding rotated variant. Such checks ensure correctness for the challenged index, but they do not, by themselves, prevent an adversary from responding with ad hoc conjugators that satisfy each individual round without belonging to a globally consistent family
.
To address this, we consider a stronger post-challenge step—a
global consistency verification. After all challenge rounds conclude, the prover discloses the complete tuple
and the verifier reconstructs the cyclic products
with indices taken modulo
n. Correctness requires that for every
i,
This post hoc verification enforces two global algebraic constraints:
- 1.
Consistency of the factor family. The prover must now exhibit matrices whose cyclic products generate all published powered matrices. This eliminates strategies where the prover produces unrelated conjugators for individual rounds without forming a coherent solution.
- 2.
Uniqueness of the exponent. Because every public value
is derived using the same exponent, the equalities in (
7) force a single-value exponent
x that is globally compatible with the entire family.
Together, these checks ensure that the prover possesses a concrete solution to the algebraic system
Solving this system corresponds precisely to the Factor Recovery Problem (FRP) and the Powered Product Identification Problem (PPIP), now coupled with the nonlinear autopotency constraints introduced in
Section 5.
We emphasize that global consistency verification is appropriate when the tuple is an ephemeral secret associated with a single authentication session. Revealing these values is compatible with one-time authentication, initialization, or registration phases, but not with reusable long-term secrets. This design choice reflects a deliberate trade-off between algebraic transparency and bounded reuse, enabling lightweight authentication mechanisms without reliance on long-lived secret material.
2.4. Remarks on MDLP, Conjugacy, and Quantum Algorithms
For completeness, we distinguish two different algebraic problem settings that arise in our framework.
First, whenever a public matrix
is raised to a secret exponent
y and we are only given
, the associated problem lives in the finite cyclic subgroup
where
. Via the isomorphism
, this
Matrix Discrete Logarithm Problem (MDLP) reduces to a standard discrete logarithm in a finite abelian group. Classically, no polynomial-time algorithm is known, but from the quantum perspective, Shor’s algorithm solves this type of problem in polynomial-time in
. Thus, any component of the scheme that relies solely on MDLP is not post-quantum-secure.
Second, and more specific to our proposal, the challenge–response mechanism and the powered products
give rise to the PPIP and FRP problems in (
5) and (
6), as well as to the Autopotent Parameter Recovery Problem (APRP) discussed in
Section 5. These tasks are naturally phrased as instances of the Conjugacy Search Problem and as structured multivariate systems over
, rather than as abelian hidden subgroup problems.
In particular, the presence of exponentiation and autopotent constraints prevents a direct reduction of PPIP or FRP to linear intertwiner equations of the form with known coefficients. Instead, the unknown conjugators and matrix parameters appear nonlinearly and are coupled across multiple powered products, precluding straightforward linearization techniques commonly used in matrix conjugacy problems.
The Autopotent Parameter Recovery Problem (APRP) induces systems of coupled multivariate polynomial equations over , whose variables correspond to the structured parameters defining the secret matrices (e.g., Toeplitz coefficients and diagonal entries), together with constraints arising from autopotency relations among matrix powers. While we do not claim a formal reduction of APRP to standard Multivariate Quadratic (MQ) problems, the resulting systems share several characteristic features with MQ-type instances encountered in algebraic cryptanalysis: a growing number of variables as the matrix dimension k increases, nonlinear coupling between parameters, and polynomial degrees that grow with the depth of the power expansions. In particular, even for modest values of k, the autopotent constraints generate polynomial relations whose degrees exceed the purely quadratic case, yielding dense and structured systems. As k increases, both the number of unknown parameters and the algebraic degree of the resulting system increase, which is expected to adversely affect the performance of generic algebraic attacks such as Gröbner basis or XL-type methods. Although no formal complexity bounds are claimed, solving such systems is heuristically expected to require computational resources beyond currently known polynomial-time methods, especially when combined with a large underlying field . We emphasize that this discussion is intended to clarify the structural nature of APRP and its distinction from abelian discrete-logarithm-type problems, rather than to assert provable hardness. The security assumptions adopted in this work are therefore heuristic and structural in nature.
This distinction is central to the post-quantum-oriented motivation of the present work: while no formal quantum hardness reduction is claimed, the absence of an apparent embedding into abelian hidden subgroup formulations motivates the investigation of these problems as non-standard candidates for post-quantum cryptanalysis.
At present, we are not aware of any classical or quantum algorithms that solve PPIP, FRP, or APRP in polynomial-time for the non-diagonalizable Toeplitz constructions considered here, nor of any reduction that casts them into the abelian hidden subgroup framework underlying Shor’s algorithm. This motivates the following working hypothesis.
Conjecture 1 (Heuristic hardness of the non-diagonalizable conjugacy framework). For suitable choices of p, k, and the family of non-diagonalizable matrices, solving PPIP, FRP, or APRP on generic instances derived from our key generation and challenge procedures requires super-polynomial-time, even for adversaries equipped with a quantum computer.
Our formal security analysis in this paper remains classical: we do not claim a proven post-quantum reduction. Nevertheless, the conjugacy-based structure and the lack of a known reduction to abelian hidden subgroup problems suggest that the framework may be a promising candidate for further post-quantum cryptanalytic investigation.
3. Challenge–Response Authentication Protocol
The proposed authentication mechanism follows a standard challenge–response paradigm and involves two parties: a prover (Bob) and a verifier (Alice). A single authentication execution proceeds as follows.
- Step 1:
Setup (Prover). Bob samples a secret family of matrices
from the structured set
defined in
Section 4, and selects a secret exponent
x. He computes the cyclic products
and publishes the powered products
.
- Step 2:
Challenge (Verifier). Alice selects an index uniformly at random (or according to a prescribed distribution) and sends i to Bob.
- Step 3:
Response (Prover). Upon receiving the challenge index i, Bob reveals the corresponding secret matrix .
- Step 4:
Verification (Verifier). Alice verifies Bob’s response by checking the conjugacy relation
where
denotes the cyclic index shift induced by the product construction. If the verification succeeds and
satisfies the required structural constraints, Alice accepts; otherwise, she rejects.
For clarity, we now provide a more detailed description of each phase of the protocol as illustrated schematically in
Figure 1.
Bob generates his long-term secret as follows: we emphasize that this secret may be instantiated per session or refreshed after a bounded number of authentication rounds, depending on the intended deployment model.
When Alice wishes to authenticate Bob, she proceeds as follows:
She retrieves Bob’s public data .
She selects a challenge index at random (or according to a prescribed distribution) and sends i to Bob.
Upon receiving the challenge index i, Bob responds by
An external adversary observing the protocol transcript therefore gains access to the challenged index i and the corresponding matrix , but not to the remaining factors nor to the exponent x.
Alice verifies Bob’s response by checking the conjugacy relation
where
is the rotation mapping induced by the cyclic ordering of the products.
More explicitly, the permutation is defined as the cyclic shift for and , corresponding to the ordering of the cyclic products used to define .
If (
8) holds and
satisfies the required structural constraints (e.g., belonging to the Toeplitz family), Alice accepts the authentication; otherwise, she rejects. In an implementation, the index 1 in (
8) may be replaced by any fixed reference product, as long as the mapping
is well-defined.
3.1. Correctness and Security Discussion
The following security discussion assumes a standard challenge–response setting, in which an adversary may observe previous protocol executions and attempt to impersonate the legitimate prover, but does not initially know the secret family nor the exponent x.
Correctness follows directly from the construction: since
, raising both sides to the power
x yields (
4), and hence the verification Equation (
8) holds for honest Bob.
From a security perspective, an adversary attempting to impersonate Bob faces two basic strategies:
- 1.
Online guessing: Without prior computation, the adversary can attempt to respond to a challenge index
i by outputting a random matrix
and hoping that (
8) happens to hold. Under mild assumptions on the distribution of the public products, the success probability of such an attempt in a single authentication round is upper bounded by
, where
n denotes the number of secret factors. By repeating the protocol for
r-independent rounds, the impersonation success probability is bounded by
.
An adversary who observes multiple authentication sessions and accumulates valid transcript pairs does not gain an advantage beyond the number of unrevealed secret factors. Once a factor has been disclosed, it is treated as consumed and is not assumed to remain secure for future sessions. Consequently, the above impersonation bound applies with respect to the remaining unrevealed factors, and transcript accumulation does not invalidate the stated success probability estimates.
- 2.
Offline algebraic attack: The adversary may try to solve an instance of PPIP or FRP, using the public data to compute either a valid conjugator or a set of factors in that satisfy the same cyclic relations. In our instantiation, this task reduces to solving multivariate polynomial systems that encode the Toeplitz and autopotent structure of the underlying matrices and their powers. We assume that no polynomial-time classical algorithms are known to solve such systems for our parameter ranges, beyond generic exponential-time algebraic techniques.
We emphasize that the proposed authentication mechanism is not formulated as a reusable long-term authenticator. The protocol description does not assume indefinite reuse of the same secret family across arbitrarily many sessions. In particular, the intentional revelation of individual matrices during authentication is compatible with one-time or bounded-use authentication scenarios. If the same secret family were to be reused across many sessions, repeated revelations of could indeed lead to cumulative information leakage. Such long-term reuse scenarios, and the countermeasures they would require, are outside the scope of the present work. In particular, once a factor has been revealed during authentication, the corresponding index i should be treated as consumed in subsequent sessions unless the secret family is refreshed.
After at most n successful authentication sessions, all secret factors may have been revealed. At this point, the original secret family provides no further security and must be refreshed. The protocol is therefore inherently bounded-use, with the parameter n directly determining the maximum number of supported authentication sessions.
The protocol is therefore best interpreted as a structurally grounded challenge–response mechanism, whose security relies on explicit algebraic assumptions rather than on standard reduction-based proofs. It does not claim provable security under a standard reduction, nor does it directly compete with established post-quantum authentication mechanisms. Its main contribution is to illustrate how structured non-diagonalizable matrices and their power expansions can be used to define algebraic authentication tasks in noncommutative settings.
3.2. Worked Example (Toy Parameters)
To make the protocol fully explicit and self-contained, we provide a worked example with small parameters. All computations below are performed in with modular arithmetic on matrix entries. For this toy example, we focus on the conjugacy verification equation; structural-membership checks (e.g., Toeplitz-parameter validation) are omitted for brevity.
We choose , , , and a secret exponent . The cyclic permutation is defined by , that is, , , and .
Let Bob’s secret family be
, where
Each
is invertible (e.g.,
,
, and
in
). The matrices are noncommutative (for instance,
), and are chosen from the structured non-diagonalizable family described in
Section 4.
For
, the cyclic products are defined as
,
, and
. A direct computation in
yields
Bob publishes the public key
. Since
, we write
, and obtain
Suppose Alice challenges Bob with index
. Bob reveals
. Alice verifies the relation
A direct computation in
yields
so Alice accepts. Analogously, one verifies that
and
.
This toy example is included solely to illustrate the mechanics of the protocol and the verification relation, and is not intended to suggest security for these small parameter choices.
3.3. Permutation-Coded Authenticated Message Space
The challenge–response protocol in
Section 3 allows a verifier (Alice) to check the validity of individual authenticators
by means of the conjugacy relation (
8). As a direct consequence, the same infrastructure can be used to transmit authenticated
messages by encoding information in the
order in which the authenticators are revealed. As in the base authentication protocol, this construction is intended for scenarios where the underlying authenticators are used in a bounded or one-time manner, such as initialization, bootstrapping, or session-bound authenticated exchanges.
Let
be the length of the secret family
held by Bob, and let
denote the symmetric group on
. We consider a finite message space
and a non-empty set of
admissible permutations
together with an injective encoding map
The pair is fixed in advance and known to both parties. Given a permutation , we write in one-line notation, so that is the index of the authenticator sent in position t.
If
and
is the identity, the message space has cardinality
so that each possible permutation of the authenticators corresponds to a distinct message. More generally, by choosing
as a proper subset of
(e.g., to impose additional structure, distance, or robustness constraints), one obtains a reduced but still large message space
.
Assume that the setup phase of
Section 3 has been completed: Bob holds the secret family
A and exponent
x; Alice knows the public powered products
and the rotation
induced by the cyclic construction of the products.
To send a message , Bob and Alice proceed as follows.
- 1.
Encoding (Bob). Bob computes the permutation
- 2.
Transmission (Bob → Alice). Over an order-preserving channel, Bob sends the sequence of authenticators
No challenge indices are issued by Alice in this variant; the entire permutation is chosen and initiated by Bob.
- 3.
Global verification (Alice). After receiving the full sequence, Alice performs the following checks:
- (a)
For each position
, she verifies that the conjugacy relation
holds and that
satisfies the required structural constraints (e.g., membership in the Toeplitz family).
- (b)
She reconstructs the permutation from the ordered list of valid indices and checks that .
If any of these checks fails, she rejects the transmission.
- 4.
Decoding (Alice). If all checks succeed, Alice computes
where
is the inverse of
on its image
. She accepts
m as an authenticated message from Bob.
For an honest prover Bob, the correctness of the original challenge–response verification (
8) implies that step 3(a) always succeeds for the true family
and the corresponding public products. Since
by construction, step 3(b) also succeeds, and Alice recovers the intended message
m in step 4.
From an adversarial standpoint, producing a new authenticated message amounts to generating a full sequence of matrices
that simultaneously (i) satisfies all conjugacy checks in step 3(a), and (ii) corresponds to a permutation
under the agreed encoding. This requires solving a non-trivial instance of the powered product and factor recovery problems (PPIP/FRPs) together with the structural constraints imposed on the family
A, and hence inherits the heuristic hardness assumptions discussed in
Section 2.
In summary, the challenge–response protocol gives rise, as a corollary, to a permutation-coded authenticated message channel with message space of size , which can be as large as when all permutations are admissible.
In this sense, message authentication and identity authentication are unified under the same noncommutative algebraic hardness assumptions.
4. Construction of Non-Diagonalizable Matrices in
The resilience of the proposed protocol against spectral decomposition and linearization attacks critically depends on the use of matrices whose structure resists simplification via diagonalization [
22]. A matrix
is considered
diagonalizable over the field if it is similar to a diagonal matrix
D, meaning there exists an invertible matrix
P such that
[
23]. This transformation is possible if and only if the algebraic multiplicity of each eigenvalue—the number of times it appears as a root of the characteristic polynomial—equals its geometric multiplicity—the dimension of its corresponding eigenspace,
.
Conversely, a matrix is non-diagonalizable (or defective) when at least one eigenvalue has a geometric multiplicity strictly less than its algebraic multiplicity. This defectiveness typically arises from the presence of non-trivial Jordan blocks in the Jordan canonical form of the matrix, which occur when the matrix lacks a full set of linearly independent eigenvectors. In the context of our algebraic framework, employing non-diagonalizable matrices in the construction of the secret factors and of the derived products is a deliberate countermeasure: it hinders an adversary from simplifying the underlying problems by transforming the public matrices into a diagonal form, which would otherwise decompose their action into a set of independent and potentially easier scalar problems within the multiplicative group of the field .
Throughout the manuscript, we denote by the structured family of invertible, non-diagonalizable matrices in that are constructed according to the method described in this section. Elements of are obtained as products of structured factors, including diagonal and upper triangular Toeplitz components, chosen so as to enforce non-diagonalizability and to satisfy the algebraic constraints required by the protocol. The family is therefore not an arbitrary subset of , but a restricted class of matrices whose parameters give rise to coupled algebraic relations under conjugation and exponentiation.
To systematically generate such matrices, we propose a constructive method that guarantees non-diagonalizability for a specified matrix size k. The core idea is to engineer the matrix products to have a controlled eigenvalue structure that inherently leads to a deficient eigenspace. We achieve this by defining one factor, , as a diagonal matrix with distinct, non-zero entries, ensuring it is itself diagonalizable and invertible. The other factor, , is constructed as an invertible upper triangular matrix, whose scalar parameters (denoted by t) are chosen independently of those of , and which is specifically designed to lack a single, common eigenvector basis with . The key insight is that the product will inherit a triangular structure from , but its eigenvector structure is disrupted by the distinct scaling imposed by , often resulting in a single, repeated eigenvalue with an insufficient number of associated eigenvectors.
The subsequent subsections detail this construction for the fundamental case of
, providing a clear blueprint for generating noncommutative, non-diagonalizable pairs
whose product
can be used as a building block for the secret factors
appearing in the cyclic products
of
Section 3. This method can be generalized to larger dimensions by working with block matrix extensions or by ensuring that a single Jordan block of maximal size governs the matrix structure.
4.1. Method Overview
The systematic construction of a non-diagonalizable matrix for cryptographic use requires carefully selecting the constituent matrices to engineer a specific spectral structure. For clarity and foundational understanding, we first present the construction for the minimal dimension , which captures the essential principles and can be generalized to higher dimensions.
Let
be an invertible diagonal matrix with distinct, non-zero entries. This choice ensures
is itself diagonalizable and contributes distinct scaling factors to the rows of
. For instance,
Let
be an invertible upper triangular matrix. This structure is pivotal as it constrains the eigenvectors of the resulting product. A general form is
The product
is then computed as
This product M is an upper triangular matrix. For M to be non-diagonalizable over , two conditions must be simultaneously satisfied:
- 1.
Repeated Eigenvalue: The eigenvalues of
M, which are its diagonal entries
and
, must be equal. This gives the condition
This ensures the characteristic polynomial has a single root of algebraic multiplicity 2.
- 2.
Deficient Eigenspace: The matrix must not have two linearly independent eigenvectors. For an upper triangular matrix with a repeated eigenvalue
; this occurs if and only if it is not a scalar multiple of the identity, i.e., the superdiagonal entry is non-zero:
Under this condition, the matrix has rank 1, implying its kernel (the eigenspace for ) is one-dimensional. Thus, the geometric multiplicity (1) is strictly less than the algebraic multiplicity (2), confirming non-diagonalizability.
To procedurally generate such a matrix M, one can
- 1.
Randomly select distinct non-zero values ;
- 2.
Randomly choose (ensuring is satisfied);
- 3.
Compute t from the repeated eigenvalue condition: .
This algorithm efficiently yields a non-diagonalizable matrix M suitable as a core factor in the families of secret matrices employed by the protocol.
4.2. Example
Consider the finite field . We follow the construction method to build a non-diagonalizable matrix.
Let the diagonal matrix be . We have , .
Choose and . This satisfies .
Compute
t to enforce a repeated eigenvalue:
Since
(as
), we have
Thus, .
The matrix
M has a single eigenvalue
with algebraic multiplicity 2. To find the geometric multiplicity, we examine the eigenspace
The rank of is 1 (since the second row is zero, but the first row is non-zero), confirming that the kernel is one-dimensional. Therefore, the geometric multiplicity is 1, which is less than the algebraic multiplicity of 2, proving that M is non-diagonalizable over .
Finally, note that
, as
which differs from
M. This noncommutativity is essential for the conjugacy relationships that underpin the challenge–response protocol, where products of such matrices appear as the secret factors and their cyclic combinations.
5. Autopotencies of Upper Triangular Toeplitz Matrices
A critical aspect of the proposed framework lies in the properties of matrix exponentiation. The public data in the protocol, as well as several internal verification steps, are fundamentally composed of matrices raised to secret powers, typically of the form , where M is a structured, non-diagonalizable matrix and n is a large, secret integer. The algebraic strength of the construction hinges on the apparent computational infeasibility of deriving these secret exponents or the constituent parameters of M from their exponentiated products, a challenge that naturally leads to parameter recovery and factor recovery problems.
To rigorously assess the resilience of these transformations against algebraic cryptanalysis, a deep understanding of the structural evolution of matrices under exponentiation is paramount. It is necessary to characterize the precise algebraic relationships that emerge between the entries of a matrix M and its power . Specifically, we seek to identify which structural invariants are preserved and what new deterministic patterns arise, as these could potentially be exploited by an adversary to simplify the underlying hard problems.
In this work, we impose a specific structure on the matrix factor
to facilitate this analysis while maintaining security; we model it as an
upper triangular Toeplitz matrix. A Toeplitz matrix is constant along its diagonals, and an upper triangular one has the following general form for size
:
This structure is particularly advantageous because it allows for the derivation of closed-form expressions for the entries of any power . These expressions reveal that the entries on the t-th superdiagonal of are not independent but are governed by a deterministic function of the base coefficients , the eigenvalue , and the exponent n.
We formalize these intrinsic dependencies through a concept we term autopotency. An autopotency identity is a precise algebraic relation that binds the entries of a matrix power to the original parameters of M and the exponent n. For a legitimate user in possession of the private parameters (the coefficients and the exponent n), these identities serve as efficient verification tools, enabling them to confirm the correctness of computed powers or protocol messages without re-performing the full exponentiation.
Conversely, for an adversary who only observes the public matrix , these same identities present a formidable barrier. The autopotency relations constitute a system of multivariate polynomial equations over the finite field . Isolating the secret parameters from this system is equivalent to solving a complex, nonlinear decomposition problem that appears intractable for large matrix dimensions and field sizes, thereby underpinning the security of the exponentiation process against parameter recovery attacks. The following subsections derive these autopotency identities explicitly for the general case and for small values of k.
In other words, the autopotency property serves a dual purpose:
- 1.
It provides structural predictability necessary for efficient verification and protocol checks by honest parties.
- 2.
It ensures cryptographic opacity, since isolating the private parameters from the observable entries of involves solving nonlinear systems over , which in general leads to multivariate polynomial systems with a structure similar to multivariate quadratic (MQ) problems, for which only generic exponential-time algebraic techniques (such as Gröbner bases or XL-type methods) are currently known.
The following subsections derive explicit expressions for these powers and the corresponding autopotency relations, beginning with the general case and illustrating particular instances for and .
5.1. General Form of the Matrix M
To harness the analytical advantages of the Toeplitz structure, we formally define the matrix
(or a relevant block thereof) as an upper triangular Toeplitz matrix
M of size
. This matrix can be elegantly decomposed using a basis of nilpotent matrices. Let
I be the
identity matrix, and let
N be the nilpotent shift matrix defined by
which satisfies the nilpotency condition
. The matrix
has 1’s on the
t-th superdiagonal and zeros elsewhere, for
.
Any upper triangular Toeplitz matrix
M can be expressed as a polynomial in
N:
where
. The scalar
ensures the matrix is invertible. In this formulation,
appears on the main diagonal, the coefficient
defines the first superdiagonal,
the second, and so forth. This representation is powerful because it reduces matrix multiplication and exponentiation to operations on the coefficients within the polynomial ring
, subject to the relation
.
5.2. Computing
The computation of
is central to the cryptographic operations. Leveraging the binomial theorem within the commutative algebra generated by
and the nilpotent matrix
, we obtain a finite expansion:
where the series terminates at
due to the nilpotency of
A. The entry on the
t-th superdiagonal of
, denoted
, is determined by the terms where the combined power of
N in
equals
t. This yields the explicit formula
The diagonal entries are simply
. This expression reveals that
is a polynomial in the base coefficients
and the exponent
n.
We can isolate the leading term of this polynomial, which is linear in
, by defining the
adjusted entry :
This definition allows us to establish the core
autopotency identity. Observing that
, a simple manipulation shows that for any
,
Raising both sides to the power
n confirms the identity
This identity is a powerful tool for a legitimate user who knows the private parameters
and
n. They can compute
directly and efficiently verify the consistency of a computed power
by checking if the identity holds.
For an adversary, however, exploiting this identity is computationally infeasible. While the public matrix
reveals
and the full
, the adjusted entry
is not directly observable; it is masked within the complete expression for
, which includes higher-order terms involving products of the coefficients
. For example, for the third superdiagonal (
), the full expression is
An adversary faces a system of such multivariate polynomial equations for the different superdiagonals. Isolating the secret parameters and n from this system is equivalent to solving a structured decomposition problem. Guessing the exponent n alone is infeasible due to the search space size of . Furthermore, even with a hypothesized n, extracting the coefficients requires solving a system of nonlinear equations over with a structure that resembles generic multivariate quadratic (MQ) problems. We refer to this task as the Autopotent Parameter Recovery Problem (APRP). Although we do not provide a reduction from APRP to any standard MQ-hardness assumption, we are not aware of polynomial-time classical algorithms that solve such systems in general, beyond generic exponential-time algebraic techniques (e.g., Gröbner bases or XL-type methods).
This analysis confirms that the autopotency property, while enabling efficient verification for legitimate users, simultaneously creates a cryptographic barrier that helps protect the secrecy of the exponent and the base matrix parameters against algebraic parameter recovery attacks.
5.3. Base Case:
The case
provides the most elementary yet insightful illustration of the autopotency principle. Consider the upper triangular Toeplitz matrix:
The nilpotency condition is
, which drastically simplifies the binomial expansion for
. The computation yields a closed form:
Here, the diagonal entry is
, and the first superdiagonal entry is
. In this simple case, the adjusted entry is identical to the observable superdiagonal,
, as there are no higher-order terms. The autopotency identity manifests clearly:
Raising both sides to the power n confirms that . For a legitimate user, this serves as a trivial yet perfect verification. For an adversary, the security in this case rests primarily on the hardness of recovering n from , given , and on the difficulty of determining without knowledge of n.
5.4. Case
The three-dimensional case,
, reveals the full interplay of terms that characterizes the general autopotency concept. The matrix is defined as
with the nilpotent shift matrix
N satisfying
. The power
requires expanding up to the second power of
:
Calculating
(since
and
), we obtain the full power:
Extracting the entries from this expansion gives
The adjusted entry for the second superdiagonal is defined as
, which represents the component of
that is linear in
. The autopotency identity for
is then verified as
This case provides a concrete illustration of the core cryptographic mechanism. A legitimate user who knows
, and
n can compute
and use the identity for verification. An adversary, however, faces the fundamental obstacle that the publicly observable value is
, not
. To isolate
, the adversary must somehow subtract the term
, which requires knowledge of the very secrets
n and
they are trying to determine. This creates a circular dependency and a nonlinear system of equations that underpins the security for larger matrix sizes and links APRP naturally to the broader factor recovery and powered product problems discussed in
Section 2.
From a cryptanalytic standpoint, the autopotency identities imply that any attacker who attempts to recover the secret parameters must simultaneously satisfy both the conjugacy constraints among the powered products (as in PPIP/FRP) and the multivariate polynomial relations induced by the Toeplitz structure (as in APRP). This coupling places the problem at the intersection of Conjugacy Search in non-abelian matrix groups and MQ-type algebraic cryptanalysis, for which no efficient classical or quantum algorithms are currently known in the general case.
6. Parameter Size and Storage Requirements
The methodology followed in this work is constructive and exploratory. We first design a controlled algebraic construction of invertible, non-diagonalizable matrices over finite fields, ensuring explicit structural properties that resist diagonalization-based simplifications. These constructions are then embedded into a cyclic challenge–response protocol whose correctness follows directly from conjugacy relations. Next, we abstract the adversarial task into well-defined algebraic problems (PPIP, FRP, and APRP) that capture the difficulty of recovering conjugators or structured parameters from powered matrix products. The hardness of these problems is discussed heuristically by analyzing their algebraic structure, the induced multivariate relations, and their separation from classical abelian discrete-logarithm settings. Finally, we complement the theoretical development with explicit worked examples and basic experimental measurements to demonstrate feasibility and internal consistency, without claiming concrete cryptographic security levels. The present section places these constructions into a practical context by discussing parameter selection, efficiency, and storage requirements.
In the present work, the matrix dimensions
and
are used as concrete construction parameters to illustrate the proposed algebraic framework and to enable explicit experimentation. In particular, the case
is intended primarily for pedagogical and illustrative purposes, as it allows closed-form expressions and compact examples, but it should not be regarded as a recommended choice for security-oriented deployments. From a practical standpoint,
represents a reasonable baseline that preserves computational feasibility while inducing a substantially richer algebraic structure. Increasing the matrix dimension
k enlarges the number of underlying parameters and the complexity of the resulting algebraic relations, which is expected to make generic algebraic recovery attacks more difficult. However, this increase also incurs a non-negligible efficiency cost, since matrix multiplication and exponentiation scale roughly as
, while storage and communication costs scale as
. For this reason, rather than relying on large matrix dimensions, the intended hardness of the construction is primarily supported by the use of a sufficiently large finite field
, together with a suitably chosen exponent
x, and by the structured nonlinearity induced by the Toeplitz and autopotent constraints. Indicative parameter choices reflecting these design considerations are summarized in
Table 1, which distinguishes between illustrative settings and practical bounded-use deployments.
The algebraic framework proposed in this work is designed to be flexible with respect to concrete parameter choices. Nevertheless, it is useful to outline the asymptotic size of the main objects involved in the challenge–response setting.
We work over a finite field with a cryptographically large prime p, and we consider matrices of size . The secret state held by a prover consists of
In the most direct representation, each matrix
is stored as
field elements, so the secret family requires
elements of
, plus one additional element for the exponent
x. When the construction of
Section 4 is used, the effective number of parameters per factor can be reduced (e.g., to the diagonal entries of
and the Toeplitz parameters of
), but for simplicity we can regard the storage cost as
bits.
The public information published by the prover in one authentication instance consists of the n powered products , each of which is a matrix over . This yields a transcript of size bits. If multiple authentication rounds are executed with fresh exponents or modified families of factors, the storage and transmission costs scale linearly in the number of rounds.
These order-of-magnitude estimates show that, for moderate values of k and values of n appropriate to the intended deployment model, the storage and communication requirements remain practical and are dominated by the bit-length of the underlying prime p. A detailed optimization of parameter choices and encoding strategies is left as future work, since the main focus of the present paper is the algebraic structure and the associated hardness assumptions.
When the authentication mechanism is deployed in a bounded-use or single-use factor setting, the parameter n primarily determines the available budget of factor revelations before secret renewal is required. In such scenarios, n is not constrained by algebraic considerations, but by storage and communication requirements. Consequently, while small values of n suffice for illustrative and experimental purposes, larger values (for example, n in the range –) may be adopted in practical deployments to support many authentication sessions, in a manner analogous to one-time-password pools.
7. Experimental Results
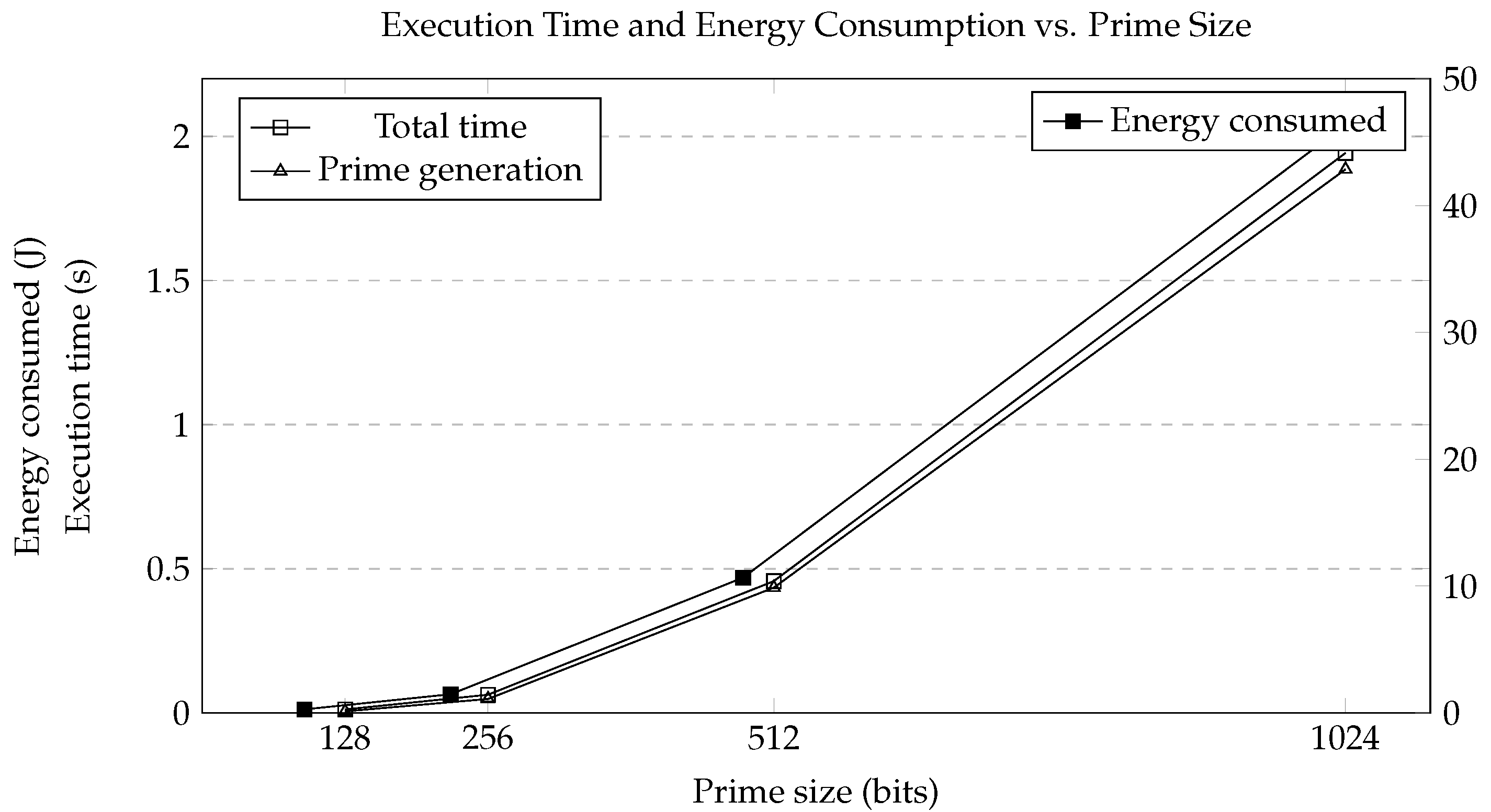
We carried out an experimental evaluation of the proposed non-diagonalizable matrix framework in order to quantify the practical cost of the core operations used in our challenge–response setting: generation of suitable matrix factors, construction of non-diagonalizable products, and exponentiation of these matrices over finite fields of different sizes. We emphasize that these experiments are intended to characterize the computational cost and practical feasibility of the underlying algebraic operations, rather than to establish concrete security levels or to validate the cryptographic hardness assumptions discussed elsewhere in the paper.
All experiments were executed on the Cocalc online environment, using a laptop with a 13th Gen Intel(R) Core(TM) i5-1335U (1.30 GHz) processor, 16.0 GB RAM, and a 64-bit operating system. Each test configuration was repeated 20 times, and both average values and statistical variations were recorded.
8. Conclusions
This work has introduced an algebraic framework for constructing challenge–response authentication mechanisms based on powers of non-diagonalizable matrices over finite fields. The core ingredients are (i) a controlled method for generating invertible, non-diagonalizable matrices via products of diagonal and upper triangular factors; (ii) the use of autopotent upper triangular Toeplitz matrices, whose structured power expansions induce nonlinear relations between matrix parameters and exponents; and (iii) a cyclic family of powered products that yields matrix instances of the classical Conjugacy Search Problem.
Within this framework, we formulated three heuristic hardness assumptions: the Powered Product Identification Problem (PPIP) and the Factor Recovery Problem (FRP), which capture the difficulty of recovering valid conjugators or individual factors from powered products; and the Autopotent Parameter Recovery Problem (APRP), modeled as a structured multivariate system over . The Toeplitz–triangular representation allowed us to derive closed-form expressions for matrix powers and to identify autopotency identities that legitimate users can exploit for efficient verification, while any adversary must satisfy coupled conjugacy constraints and multivariate polynomial relations. At present, we are not aware of classical or quantum algorithms that solve PPIP, FRP, or APRP in polynomial-time for the constructions considered here, nor of reductions that place them within the abelian hidden subgroup framework underlying Shor’s algorithm; this motivates the explicit conjecture stated in the paper, while keeping our security claims heuristic and explicitly confined to the classical setting. At the same time, the structural separation from abelian hidden subgroup formulations provides a natural motivation for further post-quantum-oriented cryptanalytic investigation.
Rather than asserting post-quantum security, the present work highlights algebraic features—such as non-diagonalizability, enforced conjugacy relations, and structured parameter coupling—that currently prevent a straightforward embedding of the proposed problems into known quantum algorithmic paradigms. This perspective is intended to motivate continued exploration of such noncommutative constructions in the context of post-quantum cryptography, without overstating the current state of knowledge.
The experimental evaluation for prime sizes between 128 and 1024 bits confirms the practical feasibility of the underlying matrix operations on general-purpose hardware, with execution time and energy consumption growing with the bit-length of the prime in line with the cost of arithmetic and matrix exponentiation over . For smaller parameter ranges, the performance remains within practical bounds. These observations support the practical implementability of the proposed algebraic constructions, without implying concrete cryptographic security levels.
Overall, the main contribution of this work is a structured algebraic toolkit—non-diagonalizable matrix constructions, Toeplitz autopotency, and cyclic powered products—and the demonstration of how these tools can be assembled into a concrete authentication mechanism. The framework is not proposed as a drop-in replacement for standardized primitives, but as a structurally grounded contribution to the broader investigation of matrix-based cryptography. Future work includes a more detailed cryptanalytic study of the proposed hardness assumptions, the design of protocol variants with richer challenge structures, and the investigation of implementations in other environments and languages, as well as potential applications to pseudorandom matrix transformations, coding-theoretic schemes, and network coding over finite fields. In this sense, the work aims to broaden the design space of algebraic cryptographic constructions by highlighting the role of non-diagonalizability and structured conjugacy as viable organizing principles in the post-quantum era.