Abstract
The r-rounds Even–Mansour block cipher is a generalization of the well known Even–Mansour block cipher to r iterations. Attacks on this construction were described by Nikolić et al. and Dinur et al. for . These attacks are only marginally better than brute force but are based on an interesting observation (due to Nikolić et al.): for a “typical” permutation P, the distribution of is not uniform. This naturally raises the following question. Let us call permutations for which the distribution of is uniformly “balanced” — is there a sufficiently large family of balanced permutations, and what is the security of the resulting Even–Mansour block cipher? We show how to generate families of balanced permutations from the Luby–Rackoff construction and use them to define a -bit block cipher from the 2-round Even–Mansour scheme. We prove that this cipher is indistinguishable from a random permutation of , for any adversary who has oracle access to the public permutations and to an encryption/decryption oracle, as long as the number of queries is . As a practical example, we discuss the properties and the performance of a 256-bit block cipher that is based on our construction, and uses the Advanced Encryption Standard (AES), with a fixed key, as the public permutation.
1. Introduction
The r-round Even–Mansour (EM) block cipher, suggested by Bogdanov et al. [1], encrypts an n-bit plaintext m by
where are secret keys and are publicly known permutations, which are selected uniformly and independently at random, from the set of permutations of . The confidentiality of the EM cipher is achieved even though the permutations are made public. For , Equation (1) reduces to the classical Even–Mansour construction [2].
As a practical example, Bogdanov et al. defined the 128-bit block cipher AES2, which is an instantiation of the 2-round EM cipher where the two public permutations are AES with two publicly known “arbitrary” keys (they chose the binary digits of the constant π). The complexity of the best (meet-in-the-middle) attack they showed uses cipher revaluations. Consequently, they conjectured that AES2 offers 128-bit security.
Understanding the security of the EM cipher has been a topic of extended research. First, Even and Mansour [2] proved, for , that an adversary needs to make oracle queries before he can decrypt a new message with high success probability. Daemen [3] showed that this bound is tight, by demonstrating a chosen-plaintext key-recovery attack after evaluations of and the encryption oracle. Bogdanov et al. [1] showed, for the r-round EM cipher, , that an adversary who sees only chosen plaintext-ciphertext pairs cannot distinguish the encryption oracle from a random permutation of . This result has been recently improved by Chen and Steinberger [4], superseding intermediate progress made by Steinberger [5] and by Lampe, Patarin and Seurin [6]. They showed that for every r, an adversary needs chosen plaintext-ciphertext pairs before he can distinguish the r-round EM cipher from a random permutation of . This bound is tight, by Bogdanov et al.’s [1] distinguishing attack after queries.
Nikolić et al. [7] demonstrated a chosen-plaintext key-recovery attack on the single key variant () of the 2-round EM cipher. Subsequently, Dinur et al. [8] produced additional key-recovery attacks on various other EM variants. All the attacks in [7,8] are only slightly better than a brute force approach. For example, the attack ([8]) on the single key variant of the 2-round EM cipher has time complexity , and the attack ([8]) on AES2 (with three different keys) has complexity of (still better than Bogdanov et al. [1], thus enough to invalidate their that AES2 has security).
The above attacks are based on the astute observation, made in [7], that for a “typical” permutation P of , the distribution of over uniformly chosen is not uniform. Currently, this observation yields only weak attacks, but the unveiled asymmetry may have the potential to lead to stronger results.
This motivates the following question. Call a permutation P of “balanced” if the distribution of , over uniformly chosen , is uniform. Can we construct a block cipher based on balanced permutations? We point out that, a priori, it is not even clear that there exists a family of such permutations, that is large enough to support a block cipher construction.
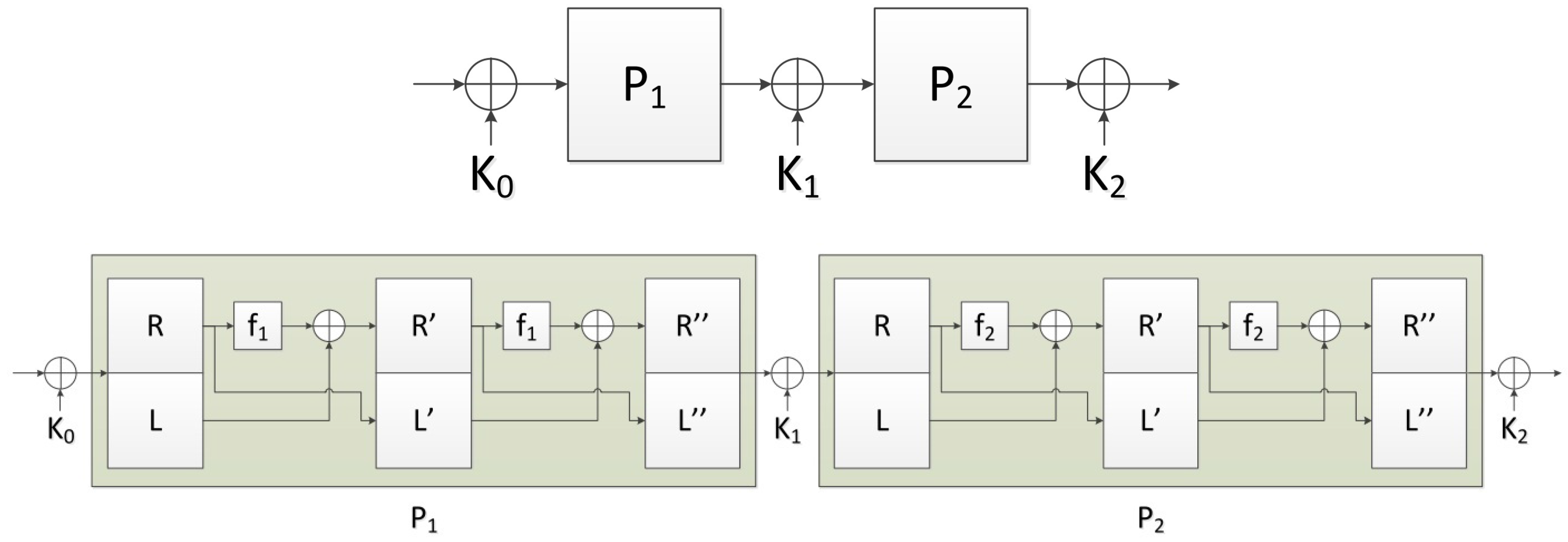
In this work, we show how to generate a large family of balanced permutations of , by observing that a 2-round Luby–Rackoff construction with any two identical permutations of , always yields a balanced permutation (of ). We use these permutations in an EM setup (illustrated in Figure 2, top panel), to construct a block cipher with block size of bits. Note that in this EM setup, the permutations are not chosen uniformly at random from the set of all permutations of . They are selected from a particular subset of the permutations of , and defined via a random choice of two permutations of , as the paper describes.
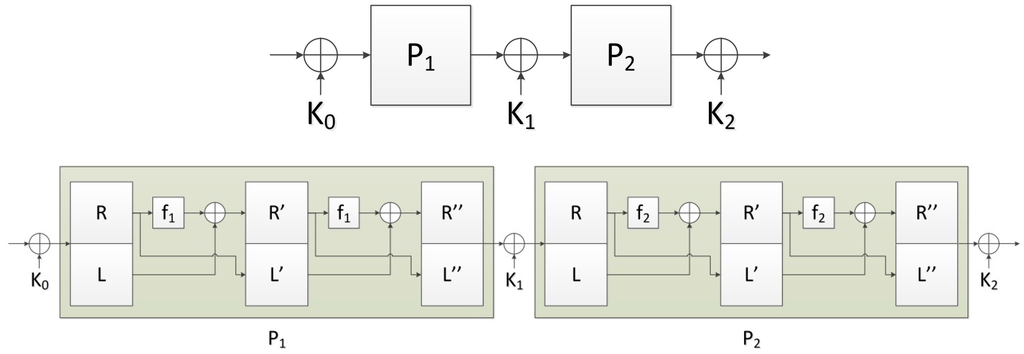
Figure 2.
The 2-round balanced permutation EM (BPEM) cipher operates on blocks of size bits. The permutations and are balanced permutations of , defined as 2-round Luby–Rackoff permutations. and are two (public) permutations of . Each of is a -bit secret key. See explanation in the text.
For the security of the resulting bits block cipher, we would ideally like to maintain the security of the EM cipher (on blocks of bits ). This would be guaranteed if we replaced the random permutation in the EM cipher, with an indifferentiable block cipher (as defined in [9]). However, the balanced permutations we use in the EM construction are 2-round Luby–Rackoff permutations, and it was shown in [10] that even the 5-round Luby–Rackoff construction does not satisfy indifferentiability. Therefore, it is reasonable to expect weaker security properties in our cipher. Indeed, we demonstrate a distinguishing (not a key recovery) attack that uses queries. On the other hand, we prove that a smaller number of chosen plaintext-ciphertext queries is not enough to distinguish the block cipher from a random permutation of .
We comment that the combination of EM and Luby–Rackoff constructions have already been used and analyzed. Gentry and Ramzan [11] showed that the internal permutation of the Even–Mansour construction for -bits block size can be securely replaced by a 4-round Luby–Rackoff scheme with public round functions. They proved that the resulting construction is secure up to queries. Lampe and Seurin [12] discuss r-round Luby–Rackoff constructions where the round functions are of the form , is a public random function, and is a (secret) round key. For an even number of rounds, this can be seen as a -round EM construction, where the permutations are 2-round Luby–Rackoff permutations. They show that this construction is secure up to queries, where for non-adaptive chosen-plaintext adversaries, and for adaptive chosen-plaintext and ciphertext adversaries. These works bare some similarities to ours, but the new feature in our construction is the emergence of balanced permutations.
The paper is organized as follows. In Section 2, we discuss balanced permutations and balanced permutations EM ciphers. Section 3 provides general background for the security analysis given in Section 4. In Section 5, we demonstrate the distinguishing attack. A practical use of our construction is a 256-bit block cipher is based on AES. Section 6 defines this cipher and discusses its performance characteristics. We conclude with a discussion in Section 7.
2. Balanced Permutations and Balanced Permutation EM Ciphers
2.1. Balanced Permutations
Definition 1 (Balanced permutation).
Let σ be a permutation of . Define the function by , for every . We say that σ is a balanced permutation if is also a permutation (such permutations are also called “orthomorphism” in the mathematical literature).
Example 1.
Let be a matrix such that both A and are invertible. Define by . Then, is a balanced permutation of . One such matrix is defined by for , and for all other .
Example 2.
Let a be an element of such that . Identify with , so that field addition corresponds to bitwise Exclusive Or (XOR). The field’s multiplication is denoted by ×. The function is a balanced permutation of . Note that this example is actually a special case of the previous one.
The balanced permutations provided by the above examples are a small family of permutations, and, moreover, are all linear. We now give a recipe for generating a large family of balanced permutations, by employing the Feistel construction that turns any function to a permutation of .
Let us use the following notation. For a string , denote the string of its first n bits by , and the string of its last n bits by . Denote the concatenation of two strings (in this order) by . We have the following identities:
Definition 2 (Luby–Rackoff permutations).
Let be a function. Let be the Luby–Rackoff (a.k.a Feistel) permutation
For every and r functions , we define the r-round Luby–Rackoff permutation to be the composition
Since we use here extensively the special case , we denote it by .
The following proposition shows that when f is, itself, a permutation, then is a balanced permutation.
Proposition 1.
Let f be a permutation of . Then, the 2-round Luby–Rackoff permutation, , is a balanced permutation of .
Proof.
Denote . Observe first that
Therefore,
Assume that such that , i.e.,
Then, and . Since (by assumption) f is one-to-one, and , it follows that .
We established that implies which concludes the proof. ☐
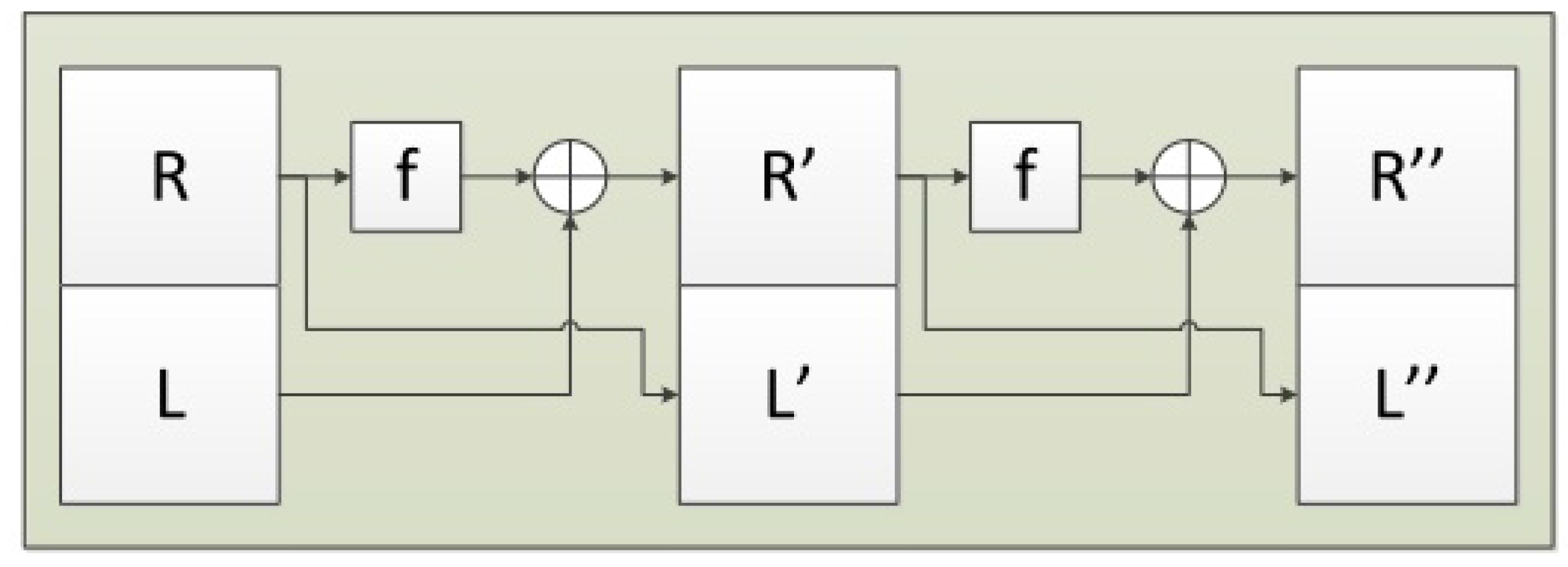
Figure 1 shows an illustration of 2-round Luby–Rackoff (balanced) permutation.
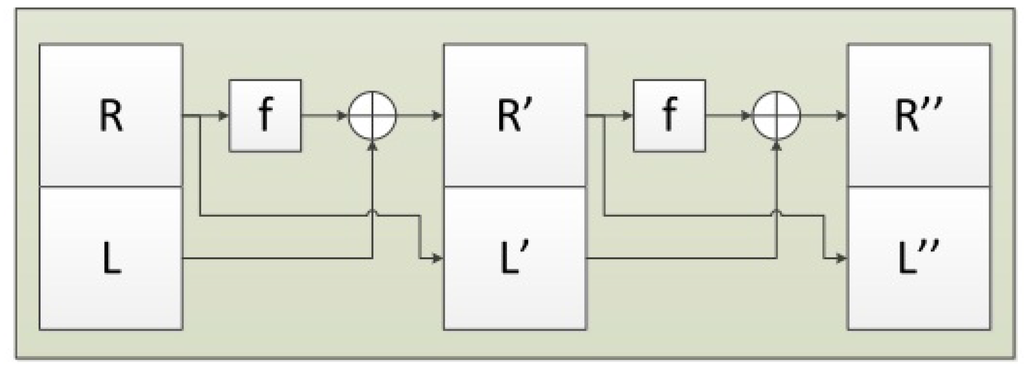
Figure 1.
The figure shows a function from to , based on two Feistel rounds with a function . For any function f, this construction is a permutation of , denoted . We call it a “2-round Luby–Rackoff permutation”. Proposition 1 shows that if f itself is a permutation of , then is a balanced permutation of .
2.2. Balanced Permutation EM Ciphers
Definition 3 (r-round balanced permutations EM ciphers (BPEM)).
Let and be integers. Let be strings in . Let be r permutations of . Their associated 2-round Luby–Rackoff (balanced) permutations (of ) are , respectively. The r-round balanced permutations EM (BPEM) block cipher is defined as
(where is defined by Equation (1)). It encrypts -bit blocks with an r-round EM cipher with the keys , where the r permutations (of ) are set to be , respectively.
The use of the r-round BPEM cipher for encryption (and decryption) starts with an initialization step, where the permutations are selected uniformly and independently, at random from the set of permutations of . After they are selected, they can be made public. Subsequently, per session/message, the secret keys are selected uniformly and independently, at random, from . Figure 2 illustrates a 2-round BPEM cipher , which is the focus of this paper.
Remark 1.
The r-round EM cipher is not necessarily secure with any choice of balanced permutations as . For example, it can be easily broken when using the linear balanced permutations shown in Examples 1 and 2.
Remark 2.
In our construction, the permutations are not random permutations. Therefore, the security analysis of the “classical” EM does not apply, and the resulting cipher (BPEM) may not be secure. Indeed, it is easy to see that the 1-round BPEM does not provide confidentiality. For any plaintexts , we have, by Equation (3),
Therefore, by Equations (4), (1) and (3),
It follows that if, e.g., then
which means that the ciphertexts leak out information on . This also implies that the r-round BPEM cipher must be used with to have any hope for achieving security.
Remark 3.
By construction, () is immune against any attack that tries to leverage the non-uniformity of (including [7,8])). Obviously, this does not guarantee it is secure (as indicated in Remark 1).
In Section 4, we prove that the 2-round BPEM cipher is indistinguishable from a random permutation.
2.3. Equivalent Representation of BPEM in Terms of LR
In this section, we show that 2-round BPEM can be viewed as a “keyed” Luby–Rackoff cipher (i.e., each function used in the Luby–Rackoff construction is selected from a family of functions indexed by a key). In fact, the r-round BPEM has a similar representation for every r.
Notation 1.
Given a function and a key we denote by , namely
Lemma 1.
Let and let be two permutations of . Then,
where
Proof.
In particular
and then
Therefore, by Equations (4) and (1),
☐
3. Security Preliminaries and Definitions
Let A be an oracle adversary which interacts with one or more oracles. Suppose that and are two oracles (or a tuple of oracles) with the same domain and range spaces. We define the distinguishing advantage of A distinguishing and as
The maximum advantage over all adversaries with complexity θ (which includes query, time complexities etc.) is denoted by . When we consider computationally unbounded adversaries (which is done in this paper), the time and memory parameters are not present and so we only consider query complexities. In the case of a single oracle, θ is the number of queries, and in the case of a tuple of oracles, θ would be of the form where denotes the number of queries to the oracle. While we define security advantages of , we usually choose to be an ideal candidate, such as the random permutation Π or a random function. The Pseudo Random Permutation advantage (PRP-advantage) of A against a keyed construction is . The maximum PRP-advantage with query complexity θ is denoted as .
In this paper, we always assume that queries to an oracle are allowed in both directions, i.e., to as well. We denote
The Symmetric Pseudo Random Permutation advantage ( SPRP-advantage) of a keyed construction (where the adversary has access to both the encryption and its decryption ) is defined by
When a construction is based on one or more ideal permutations or random permutations and a key K, we define SPRP-advantage of a distinguisher A, in the presence of ideal candidates, as where Π is sampled independently of . We denote the maximum advantage by which we call SPRP-advantage in the ideal model. The complexity parameters of the above advantages depend on the number of oracles, and will be explicitly declared in specific instances.
We state two simple observations on the distinguishing advantages for oracles (we skip the proofs of these observations, as these are straightforward).
Observation 1.
If , and are three independent oracles, then
Observation 2.
If is an oracle construction, then (by using standard reduction)
where r is the number of queries to , needed to simulate one query to the construction .
Note that in the Observation 2, we do not need to assume any kind of independence of the oracles. Analogous observations, up to obvious changes, hold for the case where are tuples of oracles.
3.1. Coefficient-H Technique
Patarin’s coefficient-H technique [13] (see also [14]) is a tool for showing an upper bound for the distinguishing advantage. Here is the basic result of the technique.
Theorem 1
(Patarin [13]). Let and be two oracle algorithms with domain D and range R. Suppose there exist a set and such that the following conditions hold:
- For all , …, ,(the above probabilities are called interpolation probabilities).
- For all A making at most q queries to , where , and denote the query and response of A to .
Then,
The above result can be applied for more than one oracle. In such cases, we split the parameter q into where denotes the maximum number of queries to the oracle. Moreover, if we have an oracle and its inverse , then the interpolation probability for both and can be simply expressed through the interpolation probability of only. For example, if an adversary makes a query y to and obtains the response x, we can write . Therefore, under the conditions of Theorem 1, we also have .
3.2. Known Related Results
3.2.1. The Security of Even–Mansour Cipher
It is known that the Even–Mansour cipher is SPRP secure in the ideal model, in the following sense: . The same is true for the single key variant . In Section 4, we provide (using Patarin’s coefficient-H technique) a simple proof of this result (Lemma 2) and a more general result (Lemma 3).
3.2.2. The Security of Luby–Rackoff Encryption
The 3-round Luby–Rackoff construction is PRP secure and the 4-round Luby–Rackoff construction is SPRP secure, when the underlying functions are PRPs (or Pseudo Random Functions). We use the following quantified version of the SPRP security of the 4-round case.
Theorem 2
(Piret [15]). Let be four independent random permutations of , and let Π be a random permutation of . Then, is SPRP secure in the following sense:
The above bound is tight (see [16]). In the proof of Theorem 7, we use the following, more general, result.
Theorem 3
(Nandi [17]). Let , and let be a sequence of numbers from such that . Let be t independent random permutations of , and let Π be a random permutation of . Then, is SPRP secure in the following sense:
4. Security Analysis of Our Construction
4.1. Security Analysis of Tuples of Single Key 1-Round EM Cipher
Notation 2.
Let . We use to indicate the existence of a collision, i.e., that for some . Otherwise, we write , and say that the tuple is block-wise distinct. Given a function and a tuple , we define
For positive integers , denote
Observation 3.
For every , and a uniform random permutation Π on ,
More generally, let be independent uniform random permutations over then, for every block-wise distinct tuples , we have
Now we show that for a random permutation Π of and a uniformly chosen K, the permutation (single keyed 1-round EM, see Notation 1) is SPRP secure in the ideal model.
Lemma 2.
Let Π and be independent random permutations of . Then
Proof.
We use Patarin’s coefficient H-technique. We take the set of bad views to be the empty set. We need to show that for every tuples , ,
where . With no loss of generality, we may assume that each of the tuples is block-wise distinct. Then, by Equation (6),
We say that a key is “good” if and for all , . In other words, for a good key, all the inputs (outputs) of Π (in the computation) are block-wise distinct. Thus, for any given good key K,
By a simple counting argument, the number of good keys is at least , i.e., the probability that a randomly chosen key is good, is at least , where . Therefore, we have
and the result follows by Theorem 1. ☐
Now, we extend Lemma 2 to a tuple of single key 1-round EM encryptions, where some keys and permutations can be repeated.
Lemma 3.
Let be independent random permutations of and be chosen uniformly and independently from . We write to denote . Let and be a sequence of elements from and , respectively, such that ’s are distinct. Then, for any (specifying the maximum number of queries for each permutation), we have
where and for every .
We note that Lemma 3 is a slightly more general case of [18], which considers Even–Mansour with multiple keys that are independently and uniformly drawn from the key space.
Proof.
The proof is similar to the proof of Lemma 2. Let , , , , be block-wise distinct tuples. From Equation (6), we have that
We say that a tuple of keys is “bad” if one of the following holds:
- There are , , such that , , and .
- There are , , such that .
- There are , , such that , , and .
- There are , , such that .
Note that there are at most cases in the first and in the third items, and at most cases in the second and fourth items.
If a key tuple is not bad, we say that it is a “good” key tuple. As in the proof of Lemma 2, for a good key tuple all the inputs (outputs) of each permutation are distinct. Thus, given a good tuple of keys , it is easy to see that
It now remains to bound the probability that a random key tuple is bad. This can happen with one of the cases listed in items 1-4 where each case has probability to occur. Hence, the probability that a random key tuple is bad, is at most , and the probability that a random key tuple is good is therefore at least . The result follows by Theorem 1. ☐
4.2. Main Theorems
Theorem 4.
Consider the BPEM cipher where the (secret) keys are selected uniformly and independently at random. Let be the maximum number of queries to the encryption/decryption oracle, and let be the maximum numbers of queries to the public permutations and , respectively. Then,
Proof.
By Lemma 1, we know that our BPEM construction is same as
where are defined via Equation (5) by . The matrix in Equation (5) is lower triangular with non-zero diagonal, and hence non-singular. Thus, the “new” keys are also distributed uniformly and independently. As are independent of all the “ingredients” of , it suffices to prove our result without the keys and .
Let be random permutations of and let Π be a random permutation of ; all are independent of each other and independent of ). Denote and . By Observation 2 and Lemma 3, we have
Note that each query to the oracle construction translates to four queries—one to each permutation , . Finally, by applying the triangle inequality, Observation 1 and Theorem 2, the SPRP-advantage in the ideal model is
☐
The same argument can be used to show a similar bound for the single permutation 2-round BPEM cipher.
Theorem 5.
Consider the single permutation BPEM cipher where the (secret) keys are selected uniformly and independently at random. Let be the maximum number of queries to the encryption/decryption oracle, and let q be the maximum number of queries to the public permutation f. Then,
Remark 4.
The difference in the bounds we received in Theorems 4 and 5 are due only to the difference in the value of σ in the application of Lemma 3.
We also comment that the same bounds hold in the single key variants. By Equation (5), we have
where
For both constructions, the “new” keys are no longer independent, so we need to generalize Lemma 3 as stated below.
Lemma 4.
Let be independent random permutations of and be chosen uniformly and independently from . We write to denote . Let be a sequence of elements from . Let M be a binary matrix of size , with no zero rows, satisfying the following condition: for every such that , the and rows of M are distinct. Let , for every .
Then, for any (specifying the maximum number of queries) we have
where and σ is as defined in Lemma 3.
We skip the proof of this lemma as it is similar to that of Lemma 3. Similarly to the proof of Theorem 4 (while using Lemma 4 instead of Lemma 3), we can obtain the following bound.
Theorem 6.
Consider the single key BPEM cipher where the (secret) key K is selected uniformly at random. Let be the maximum number of queries to the encryption/decryption oracle, and let be the maximum numbers of queries to the public permutations and , respectively. Then,
Finally, similarly to the proof of Theorem 5 (while using Lemma 4 instead of Lemma 3, and using Theorem 3 instead of Theorem 2), we obtain the following bound.
Theorem 7.
Consider the single key single permutation BPEM cipher where the (secret) key K is selected uniformly at random. Let be the maximum number of queries to the encryption/decryption oracle, and let q be the maximum number of queries to the public permutation f. Then,
5. A Distinguishing Attack on BPEM
In this section, we describe a distinguishing attack on BPEM that uses queries. This is the same attack as the one described in ([16], Section 3.2) for the 4-round Luby–Rackoff with internal permutations, not at all surprising, since we showed (in Section 2.3) that BPEM can be viewed as a 4-round Luby–Rackoff with internal (keyed) permutations. Nevertheless, for the sake of completeness, we describe and analyze the attack in this BPEM terminology. We will use the following technical lemma.
Lemma 5.
If such that
then .
Proof.
Denote
Similarly,
Therefore, we get from Equation (7) that , hence, since is injective, . Therefore, using Equation (3) again,
hence
Since is injective, we get that
hence . ☐
Proposition 2.
Consider the BPEM cipher with arbitrary (secret) keys . Let be the maximum number of queries to the encryption oracle. Then,
Remark 5.
Note that Proposition 2 implies that the adversary advantage becomes non-negligible for .
Proof.
Fix an n-bit string ρ and distinct n-bit strings . We query the encryption oracle for the plaintexts , and let be the corresponding ciphertexts. We now search for collisions between the n-bit strings . By Lemma 5, there will be no collision if the oracle encrypts using . By contrast, if the oracle encrypts by applying a randomly chosen permutation of , then the probability that there is no collision is at most
☐
6. A Practical Construction of a 256-Bit Cipher
In this section, we demonstrate a practical construction of a 256-bit block cipher based on the 2-round BPEM cipher, where the underlying permutation is AES.
Definition 4 (: a 256-bit block cipher).
Let and be two 128-bit keys and let be three 256-bit secret keys (assume are selected uniformly and independently at random). Let the permutations and be the AES encryption using and as the AES key, respectively.
The 256-bit block cipher is defined as the associated instantiation of the 2-round BPEM cipher .
Usage of :
- and are determined during the setup phase, and can be made public (e.g., sent from the sender to the receiver as an IV).
- are selected per encryption session.
The single key EM256AES is the special case where a single value and a single value are selected uniformly and independently at random, and the EM256AES cipher uses and .
Hereafter, we use the single key EM256AES. To establish security properties for , we make the standard assumption about AES with a secret key that is selected (uniformly at random): an adversary has negligible advantage in distinguishing AES from a random permutation of even after seeing a (very) large number of plaintext-ciphertext pairs (i.e., the assumption is that AES satisfies its design goals ([19], Section 4). This assumption is certainly reasonable if the number of blocks that are encrypted with the same keys is limited to be much smaller than (note that AES can also be argued to be secure in a known-key setting, although this property is not part of the design goals of AES [20,21]). Therefore, in our context, we can consider assigning the randomly selected key ℓ at setup time, as an approximation for a random selection of the permutations and (which are identical). Under this assumption, we can rely on the result of Theorem 7 for the security of .
Efficiency
An encryption session between two parties requires exchanging a 256-bit secret key and transmitting a 128-bit IV (). One key (and IV) can be used for N blocks as long as we keep . Computing one (256-bit) ciphertext involves four AES computations (with the as the AES key) plus a few much cheaper XOR operations. Let us assume that the encryption is executed on a platform that has the capability of computing AES at some level of performance. If the encryption (decryption) is done in a serial mode, we can estimate the encryption rate to be roughly half the rate of AES (serial) computation on that platform (4 AES operations per one 256-bit block). Similarly, if the encryption is done in a parallelized mode, we can estimate the throughput to be roughly half the throughput of AES.
Performance
To test the actual performance of , and validate our predictions, we coded an optimized implementation of . Its performance is reported here. The performance was measured on an Intel® CoreTM i7-4700MQ (microarchitecture Codename Haswell) where the enhancements (Intel® Turbo Boost Technology, Intel® Hyper-Threading Technology, and Enhanced Intel Speedstep® Technology) were disabled. The code used the AES instructions (AES-NI) that are available on such modern processors. On this platform, we point out the following baseline: the performance of AES (128-bit key) in a parallelized mode (CTR) is C/B, and in a serial mode (CBC encryption) it is cycles per byte (C/B hereafter). The measured performance of our implementation was C/B for the parallel mode, and C/B for the serial mode. The measured performance clearly matches the predictions. It is also interesting to compare the performance of to another 256-bit cipher. To this end, we prepared an implementation of Rijndael256 cipher [22] (we point out that although AES is based on the Rijndael block cipher, the AES standardizes only a 128 block size, while the Rijndael definitions support both 128-bit and 256-bit blocks). For details on how to code Rijndael256 with AES-NI, see [23]). Rijndael256 (in ECB mode) turned out to be much slower than , performing at C/B.
7. Conclusions
In this work, we showed how to construct a large family of balanced permutations, and analyzed the resulting new variation, BPEM, of the EM cipher.
The resulting -bit block cipher is obtained by using a permutation of as a primitive. The computational cost of encrypting (decrypting) one -bit block is four evaluations of a permutation of (plus a relatively small overhead). Note that this makes BPEM readily useful in practice, for example to define a 256-bit cipher, because “good” permutations of are available. We demonstrated the specific cipher , which is based on AES, and showed that its throughput is (only) half the throughput of AES (and times faster than Rijndael256).
A variation on the way by which BPEM can be used, would make it a tweakable -bit block cipher. Here, the public IV (=ℓ) can be associated with each encrypted block as an identifier, to be viewed as the tweak. The implementation would switch this tweak for each block. To randomize the keys for the (public) permutations, an additional encryption (using some secret key) is necessary.
The expression of the advantage in Theorem 4 behaves linearly with the number of queries to the public permutations, and quadratically with the number of queries to the encryption/decryption oracle. This reflects the intuition that the essential limitations on the number of adversary queries should be on the encryption/decryption invocations, while weaker (or perhaps no) limitations should be imposed on the number of queries to the public permutations. It also suggests the following protocol, where the secret keys are changed more frequently than the random permutations. Choose the public permutations for a period of, say, blocks, divided into sessions of blocks. Change the secret keys every session. This way, the relevant information on the block cipher, from a specific choice of keys, is limited to a session, while the adversary can accumulate relevant information from replies to the public permutations across sessions. Therefore, is limited to , while is limited to . Theorem 4 guarantees that this usage is secure.
Acknowledgments
This research was supported by the PQCRYPTO project, which was partially funded by the European Commission Horizon 2020 research Programme, grant #645622, and by the Bar Ilan University Center for Research in Applied Cryptography and Cyber Security in conjunction with the Israel National Cyber Bureau in the Prime Minister’s Office.
Author Contributions
All the authors contributed equally to this work.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Bogdanov, A.; Knudsen, L.R.; Leander, G.; Standaert, F.; Steinberger, J.P.; Tischhauser, E. Key-alternating ciphers in a provable setting: Encryption using a small number of public permutations (extended abstract). In Advances in Cryptology—EUROCRYPT 2012; Lecture Notes in Computer Science; Springer: Heidelberg, Germany, 2012; Volume 7237, pp. 45–62. [Google Scholar]
- Even, S.; Mansour, Y. A construction of a cipher from a single pseudorandom permutation. J. Cryptol. 1997, 10, 151–161. [Google Scholar] [CrossRef]
- Daemen, J. Limitations of the Even–Mansour construction. In Advances in Cryptology—ASIACRYPT 1991; Lecture Notes in Computer Science; Springer: Berlin, Germany, 1991; Volume 739, pp. 495–498. [Google Scholar]
- Chen, S.; Steinberger, J. Tight security bounds for key-alternating ciphers. In Advances in Cryptology—EUROCRYPT 2014; Lecture Notes in Computer Science; Springer: Heidelberg, Germany, 2014; Volume 8441, pp. 327–350. [Google Scholar]
- Steinberger, J.P. Improved Security Bounds for Key-Alternating Ciphers via Hellinger Distance. Available online: http://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.348.6401&rep=rep1&type=pdf (accessed on 15 January 2016).
- Lampe, R.; Patarin, J.; Seurin, Y. An Asymptotically Tight Security Analysis of the Iterated Even–Mansour Cipher. In Advances in Cryptology—ASIACRYPT 2012; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2012; Volume 7658, pp. 278–295. [Google Scholar]
- Nikolić, I.; Wang, L.; Wu, S. Cryptanalysis of Round-Reduced LED. In Fast Software Encryption—FSE 2013; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2013; Volume 8424, pp. 112–129. [Google Scholar]
- Dinur, I.; Dunkelman, O.; Keller, N.; Shamir, A. Key Recovery Attacks on 3-round Even–Mansour, 8-step LED-128, and full AES2. In Advances in Cryptology—ASIACRYPT 2013; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2013; Volume 8269, pp. 337–356. [Google Scholar]
- Maurer, U.; Renner, R.; Holenstein, C. Indifferentiability, impossibility results on reductions, and applications to the random oracle methodology. In Theory of Cryptography; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2004; Volume 2951, pp. 21–39. [Google Scholar]
- Coron, J.-S.; Patarin, J.; Seurin, Y. The random oracle model and the ideal cipher model are equivalent. In Advances in Cryptology—CRYPTO 2008; Lecture Notes in Computer Science; Springer: Berlin, Germany; 2008; Volume 5157, pp. 1–20. [Google Scholar]
- Gentry, C.; Ramzan, Z. Eliminating random permutation oracles in the Even–Mansour ciphe. In Advances in Cryptology—ASIACRYPT 2004; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2004; Volume 3329, pp. 32–47. [Google Scholar]
- Lampe, R.; Seurin, Y. Security Analysis of Key-Alternating Feistel Ciphers. In Fast Software Encryption—FSE 2014; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2014; Volume 8540, pp. 243–264. [Google Scholar]
- Patarin, J. Étude Des générateurs de Permutations Pseudo-aléatoires basés Sur le Schéma du D.E.S. Ph.D. Thesis, National Institute for Research in Computer Science and Control (INRIA), Rocquencourt, France, 1991. [Google Scholar]
- Patarin, J. Luby–Rackoff: 7 rounds are enough for 2n(1 − ε) security. In Advances in Cryptology—CRYPTO 2003; Lecture Notes in Computer Science; Springer: Berlin, Germnay, 2003; Volume 2729, pp. 513–529. [Google Scholar]
- Piret, G. Luby–Rackoff revisited: On the use of permutations as inner functions of a Feistel scheme. Des. Codes Cryptogr. 2006, 39, 233–245. [Google Scholar] [CrossRef]
- Treger, J.; Patarin, J. Generic attacks on Feistel networks with internal permutations. In Progress in Cryptology—AFRICACRYPT 2009; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2009; Volume 5580, pp. 41–59. [Google Scholar]
- Nandi, M. The characterization of Luby–Rackoff and its optimum single-key variants. In Progress in Cryptology—INDOCRYPT 2010; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2010; Volume 6498, pp. 82–97. [Google Scholar]
- Mouha, N.; Luykx, A. Multi-Key Security: The Even–Mansour Construction Revisited, In Advances in Cryptology—CRYPTO 2015; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2015; Volume 9251, pp. 209–223. [Google Scholar]
- Announcing Request for Candidate Algorithm Nominations for the Advanced Encryption Standard (AES). Available online: http://csrc.nist.gov/CryptoToolkit/aes/pre-round1/aes_9709.htm (accessed on 15 January 2016).
- Knudsen, L.; Rijmen, V. Known-Key Distinguishers for Some Block Ciphers. In Advances in Cryptology—ASIACRYPT 2007; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2007; Volume 4833, pp. 315–324. [Google Scholar]
- Gilbert, H.; Peyrin, T. Super-Sbox Cryptanalysis: Improved Attacks for AES-Like Permutations. In Fast Software Encryption—FSE 2010; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2010; Volume 6147, pp. 365–383. [Google Scholar]
- Daemen, J.; Rijmen, V. AES Proposal: Rijndael (National Institute of Standards and Technology). Available online: http://csrc.nist.gov/archive/aes/rijndael/Rijndael-ammended.pdf (accessed on 15 January 2016).
- Gueron, S. Intel Advanced Encryption Standard (AES) Instructions Set (Rev 3.01). Available online: http://software.intel.com/sites/default/files/article/165683/aes-wp-2012-09-22-v01.pdf (accessed on 15 January 2016).
© 2016 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons by Attribution (CC-BY) license ( http://creativecommons.org/licenses/by/4.0/.