Integrating Machine Learning and Business Intelligence into Supply Chain Risk Management for a Comprehensive Cybersecurity Framework: A Systematic Literature Review
Abstract
1. Introduction
1.1. Cybersecurity and Digitalization in Modern Supply Chains
1.2. Knowledge Gaps
1.3. Objectives and Contributions of This Systematic Review
1.4. Business Intelligence: A Comprehensive Definition
2. Systematic Review Methodology
2.1. Research Questions
- What are potential risks or dangers to supply chain systems in today’s digital environment?
- What specific types of machine learning-based threat detection methods are applied to detect and classify various cyber threats in supply chains?
- How can decision support tools use Business Intelligence Analytics to convert threat detection results into tactical cybersecurity actions or strategic decisions?
- Can machine learning (ML) and business intelligence (BI) be combined into one cybersecurity system rather than developed independently for identifying impending threats?
- What are the benefits and drawbacks regarding predictive accuracy and model interpretability in an ML/BI system?
- What is currently missing from the body of research as it relates to using ML and BI to mitigate supply chain cybersecurity risk? Specifically, how does one strike a balance between developing autonomous capabilities and retaining human oversight?
2.2. Search Strategy
2.3. Inclusion and Exclusion Criteria
2.4. Screening and Selection Process
- Identification: Search results were exported to a reference manager (Zotero), and duplicates were deleted.
- Screening: The study titles and abstracts were screened for relevance.
- Eligibility: The full texts of the articles were reviewed based on the inclusion criteria.
- Inclusion: The final articles were included in the systematic review for analysis.
2.5. Quality Assessment
- Methodological rigor: This dimension assesses the rigor and appropriateness of the research design, using a scale of 1–5.
- Theoretical foundation: This dimension evaluates the rigor of the theoretical framing used for the research using a scale of 1–5.
- Data quality: This dimension evaluates the validity and reliability of the data used in the study using a scale of 1–5.
- Analytical approach: This dimension evaluates the rigor and appropriateness of the analysis used in the study using a scale of 1–5.
- Practical implications: This dimension assesses the applicability and relevance of the findings to practice, using a scale of 1–5.
- Overall Quality: This dimension summarizes the study’s contribution to the scientific body of knowledge using a scale from 1 to 5.
- 5 points: All 10 CASP Questionnaire items received a response of “yes”.
- 4 points: 8–9 of the CASP Questionnaire items received a response of “yes”.
- 3 points: 6–7 of the CASP Questionnaire items received a response of “yes”.
- 2 points: 4–5 of the CASP Questionnaire items received a response of “yes”.
- 1 point: Less than 4 of the CASP Questionnaire items received a response of “yes”.
2.6. Data Extraction and Synthesis
2.7. Justification of Sample Size
3. Systematic Review Results
3.1. Descriptive Analysis
3.1.1. Study Distribution by Year of Publication, Journal, and Country
3.1.2. Distribution of Studies by Method
3.2. Thematic Categorization
3.2.1. Theoretical Walkthrough: Ransomware Threat Scenario
3.2.2. Classification of Machine Learning and Business Intelligence Techniques
3.2.3. Classification of Supply Chain Cybersecurity Threats
3.3. Industry Standard Alignment
3.4. Methodological Quality Assessment
3.5. Publication Trends
4. Discussion
4.1. Key Themes and Trends
4.1.1. A Focus on Ransomware and Phishing Attacks
4.1.2. Prominent Use of Supervised Machine Learning Models
4.1.3. Fragmented Use of Business Intelligence Tools
4.1.4. Infrequent Application of Hybrid Frameworks
4.1.5. Threat-Specific Analytical Approaches
4.2. Identified Research Gaps
4.2.1. Methodological Gaps
4.2.2. Technological Gaps
4.2.3. Contextual Gaps
4.2.4. Theoretical Gaps
4.3. Implications for Research and Practice
4.3.1. For Researchers
4.3.2. For Practitioners
4.3.3. For Policymakers
4.3.4. Key Recommendations
4.4. Ethical and Legal Considerations
4.4.1. Algorithmic Bias and Fairness
4.4.2. Data Privacy and Sovereignty
4.4.3. Accountability and Transparency
4.4.4. Human Oversight and Autonomy
4.4.5. Regulatory Compliance
4.5. Theoretical Tensions in ML-BI Integration
4.5.1. Trade-Off Between Model Performance (Prediction Accuracy) and Model Interpretability
4.5.2. Trade-Off Between Automated Decision-Making and Human Oversight
4.5.3. Trade-Off Between Standardization and Customization
4.5.4. Trade-Off Between Proactive Threat Detection and Reactive Incident Response
5. Proposed Conceptual Framework
5.1. Data Collection and Management Layer
5.2. Machine Learning Predictive Layer
5.3. Business Intelligence Analytical Layer
5.4. Response and Governance Layer
5.5. Framework Application Example: Ransomware Threat Scenario
5.6. Alignment with Industry Standards
5.6.1. NIST Cybersecurity Framework (CSF)
- Identify Function: The Data Collection Layer (Layer 1) collects and normalizes security data from the entire supply chain to enable the organization to identify assets, vulnerabilities, and threats.
- Detect Function: The ML Predictive Layer (Layer 2) provides primary support for the Detect Function, using machine learning to determine if there are any anomalous patterns that could be indicative of cyber threats; real-time anomaly detection capabilities will enable early threat identification.
- Respond Function: The BI Analytical Layer (Layer 3) and Response and Governance Layer (Layer 4) provide a decision-maker with contextual business information and automated response recommendations to support the Respond Function, enabling rapid decisions and coordinated response actions.
- Recover Function: The recovery planning and execution capability included within the Response and Governance Layer (Layer 4) supports the Recover Function through documented procedures and compliance tracking.
5.6.2. ISO 27001 Information Security Management
5.6.3. Distinction and Unique Contribution
- Explicit discussion of integrating machine learning and business intelligence technologies, which is not explicitly addressed in either NIST or ISO 27001.
- A practical, technology-based approach to implement Supply Chain Cybersecurity.
- Illustration of how predictive analytics (machine learning), and analytical decision support (business intelligence) can be formally combined to improve threat detection and response.
- Addresses the specific issues related to supply chain cybersecurity, such as multi-organizational coordination and third-party risk management.
- Therefore, the ML-BI framework represents a supplemental framework to operationalize the broad principles of NIST and ISO 27001 with the specific application of machine learning and business intelligence technologies within supply chain environments.
6. Conclusions
7. Limitations and Future Research Directions
7.1. Limitations
7.2. Future Research Directions
Supplementary Materials
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Appendix A. Complete List of Reviewed Studies
| Line Number | Ref. No. | Author(s) | Year | Title | Venue/Journal |
| 1 | [35] | Wang, G., Gunasekaran, A., Ngai, E. W. T., & Papadopoulos, T. | 2016 | Big data analytics in logistics and supply chain management: Certain investigations for research and applications | International Journal of Production Economics |
| 2 | [16] | Larson, D., & Chang, V. | 2016 | A review and future direction of agile, business intelligence, analytics and data science | International Journal of Information Management |
| 3 | [36] | Lamba, K., & Singh, S. P. | 2016 | Big data analytics in supply chain management: Some conceptual frameworks | International Journal of Systems, Control and Communications |
| 4 | [38] | Dorri, A., Kanhere, S. S., Jurdak, R., & Gauravaram, P. [38] | 2017 | Blockchain for IoT security and privacy: The case study of a smart home | IEEE PerCom Workshops |
| 5 | [39] | Kshetri, N. | 2017 | Blockchain’s roles in strengthening cybersecurity and protecting privacy | Telecommunications Policy |
| 6 | [33] | Ang, L.-M., Seng, K. P., Zungeru, A. M., & Ijemaru, G. K. | 2017 | Big sensor data systems for smart cities | IEEE Internet of Things Journal |
| 7 | [34] | Kourtit, K., Nijkamp, P., & Steenbruggen, J. | 2017 | The significance of digital data systems for smart city policy | Socio-Economic Planning Sciences |
| 8 | [22] | Barbosa-Póvoa, A. P., da Silva, C., & Carvalho, A. | 2018 | Opportunities and challenges in sustainable supply chain: An operations research perspective | European Journal of Operational Research |
| 9 | [40] | Sangeetha, M. | 2018 | Smart supply chain management using internet of things | International Journal of Systems, Control and Communications |
| 10 | [41] | Nguyen, T., Zhou, L., et al. | 2018 | Big data analytics in supply chain management: A state-of-the-art literature review | Computers & Operations Research |
| 11 | [42] | Kshetri, N. | 2018 | Blockchain’s roles in meeting key supply chain management objectives | International Journal of Information Management |
| 12 | [37] | Ivanov, D., Dolgui, A., Das, A., & Sokolov, B. | 2019 | Digital supply chain twins: Managing the ripple effect, resilience, and disruption risks by data-driven optimization, simulation, and visibility | Handbook of Ripple Effects in the Supply Chain |
| 13 | [43] | Radanliev, P., et al. | 2018 | Future developments in cyber risk assessment for the internet of things | Computers in Industry |
| 14 | [44] | Roopak, M., Tian, G. Y., & Chambers, J. | 2019 | Deep learning models for cyber security in IoT networks | IEEE Annual Computing and Communication Workshop and Conference |
| 15 | [17] | Carleo, G., et al. | 2019 | Machine learning and the physical sciences | Reviews of Modern Physics |
| 16 | [45] | Tissir, S., El Fezazi, S., & Cherrafi, A. | 2020 | Industry 4.0 impact on lean manufacturing | IEEE International Colloquium on Information Science and Technology |
| 17 | [11] | Ghadge, A., Er Kara, M., Moradlou, H., & Goswami, M. | 2020 | The impact of Industry 4.0 implementation on supply chains | Journal of Manufacturing Technology Management |
| 18 | [46] | Hassija, V., et al. | 2020 | A survey on supply chain security: Application areas, security threats, and solution architectures | Journal of Network and Computer Applications |
| 19 | [1] | Aljohani, A. | 2023 | Predictive analytics and machine learning for real-time supply chain risk mitigation and agility | Sustainability |
| 20 | [4] | Bharadiya, J. P. | 2023 | The role of machine learning in transforming business intelligence | International Journal of Computer Science and Technology |
| 21 | [6] | Cannas, V. G., et al. | 2023 | Artificial intelligence in supply chain and operations management: A systematic literature review | International Journal of Production Research |
| 22 | [8] | Cheung, K. F., Bell, M. G. H., & Bhattacharjya, J. | 2021 | Cybersecurity in logistics and supply chain management: An overview and future research directions | Transportation Research Part E: Logistics and Transportation Review |
| 23 | [12] | Chowdhury, R. H. | 2024 | Harnessing machine learning in business analytics for enhanced decision-making | World Journal of Advanced Research and Reviews |
| 24 | [15] | Creazza, A., et al. | 2022 | Who cares? Supply chain managers’ perceptions regarding cyber supply chain risk management in the digital transformation era | Supply Chain Management: An International Journal |
| 25 | [18] | Culot, G., Podrecca, M., & Nassimbeni, G. | 2024 | Artificial intelligence in supply chain management: A systematic literature review and future research agenda | International Journal of Production Economics |
| 26 | [2] | Ghadge, A., Weiß, M., Caldwell, N. D., & Wilding, R. | 2023 | Cybersecurity risk management in supply chains: A systematic literature review | Supply Chain Management: An International Journal |
| 27 | [19] | Guo, Y. | 2023 | A review of machine learning-based zero-day attack detection | Computer Communications |
| 28 | [29] | Hammi, B., Zeadally, S., & Nebhen, J. | 2023 | Security threats, countermeasures, and challenges of digital supply chains | ACM Computing Surveys |
| 29 | [9] | Kshetri, N. | 2022 | Economics of supply chain cyberattacks | IT Professional |
| 30 | [30] | Pandey, S., Singh, R. K., Gunasekaran, A., & Kaushik, A. | 2020 | Cyber security risks in globalized supply chains: Conceptual framework and empirical evidence | International Journal of Production Research |
| 31 | [31] | Quintero-Bonilla, S., & Martín del Rey, A. | 2020 | A new proposal on the advanced persistent threat: A survey | Applied Sciences |
| 32 | [14] | Gurtu, A., & Johny, J. | 2021 | Supply chain risk management: Literature review | Risks |
| 33 | [14] | Kashef, R., et al. | 2023 | Bridging the bubbles: Connecting academia and industry in cybersecurity research | IEEE Security & Privacy |
| 34 | [32] | Sobb, T., Turnbull, B., & Moustafa, N. | 2020 | Supply chain 4.0: A systematic literature review of cyber attacks, computer security, and risk management | Computers & Industrial Engineering |
| 35 | [10] | Rani, S., Kataria, A., & Chauhan, M. | 2022 | Cyber security techniques, architectures, and design | Holistic Approach to Quantum Cryptography in Cyber Security |
References
- Aljohani, A. Predictive analytics and machine learning for real-time supply chain risk mitigation and agility. Sustainability 2023, 15, 15088. [Google Scholar] [CrossRef]
- Ghadge, A.; Weiß, M.; Caldwell, N.D.; Wilding, R. Cybersecurity risk management in supply chains: A systematic review. Int. J. Prod. Econ. 2023, 265, 109015. [Google Scholar]
- Bazeley, P.; Jackson, K. (Eds.) Qualitative Data Analysis with NVivo, 2nd ed.; SAGE Publications: Thousand Oaks, CA, USA, 2013. [Google Scholar]
- Bharadiya, J.P. The role of machine learning in transforming business intelligence. Int. J. Comput. Artif. Intell. 2023, 4, 16–24. [Google Scholar] [CrossRef]
- Schoenherr, T.; Swink, M. Revisiting the arcs of integration: Cross-validations and extensions. J. Oper. Manag. 2012, 30, 99–115. [Google Scholar] [CrossRef]
- Cannas, V.G.; Ciano, M.P.; Saltalamacchia, M.; Secchi, R. Artificial intelligence in supply chain and operations management: Multiple case study research. Int. J. Prod. Res. 2023, 62, 3333–3360. [Google Scholar] [CrossRef]
- Cappelli, D.M.; Moore, A.P.; Trzeciak, R.F. The CERT Guide to Insider Threats: How to Prevent, Detect, and Respond to Information Technology Crimes (Theft, Sabotage, Fraud); Addison-Wesley Professional: Boston, MA, USA, 2012. [Google Scholar]
- Cheung, K.F.; Bell, M.G.H.; Bhattacharjya, J. Cybersecurity in logistics and supply chain management: An overview and future research directions. Transp. Res. Part E Logist. Transp. Rev. 2021, 146, 102217. [Google Scholar] [CrossRef]
- Kshetri, N. Economics of supply chain cyberattacks. IT Prof. 2022, 24, 96–100. [Google Scholar] [CrossRef]
- Rani, S.; Kataria, A.; Chauhan, M. Cyber security techniques, architectures, and design. In Holistic Approach to Quantum Cryptography in Cyber Security, 1st ed.; CRC Press: Boca Raton, FL, USA, 2022; pp. 41–66. [Google Scholar]
- Ghadge, A.; Er, M.; Moradlou, H.; Goswami, M. The impact of Industry 4.0 implementation on supply chains. J. Manuf. Technol. Manag. 2020, 31, 669–686. [Google Scholar] [CrossRef]
- Chowdhury, R.H. Harnessing machine learning in business analytics for enhanced decision-making. World J. Adv. Eng. Technol. Sci. 2024, 12, 674–683. [Google Scholar] [CrossRef]
- Kashef, R.; Freunek, M.; Schwartzentruber, J.; Samavi, R.; Bulgurcu, B.; Khan, A.; Santos, M. Bridging the bubbles: Connecting academia and industry in cybersecurity research. In 2023 IEEE Secure Development Conference (SecDev); IEEE: Piscataway, NJ, USA, 2023; pp. 207–213. [Google Scholar]
- Gurtu, A.; Johny, J. Supply chain risk management: Literature review. Risks 2021, 9, 16. [Google Scholar] [CrossRef]
- Creazza, A.; Colicchia, C.; Spiezia, S.; Dallari, F. Who cares? Supply chain managers’ perceptions regarding cyber supply chain risk management in the digital transformation era. Supply Chain. Manag. Int. J. 2022, 27, 30–53. [Google Scholar] [CrossRef]
- Larson, D.; Chang, V. A review and future direction of agile, business intelligence, analytics and data science. Int. J. Inf. Manag. 2016, 36, 700–710. [Google Scholar] [CrossRef]
- Carleo, G.; Cirac, I.; Cranmer, K.; Daudet, L.; Schuld, M.; Tishby, N.; Vogt-Maranto, L.; Zdeborová, L. Machine learning and the physical sciences. Rev. Mod. Phys. 2019, 91, 045002. [Google Scholar] [CrossRef]
- Culot, G.; Podrecca, M.; Nassimbeni, G. Artificial intelligence in supply chain management: A systematic literature review of empirical studies and research directions. Comput. Ind. 2024, 162, 104132. [Google Scholar] [CrossRef]
- Guo, Y. A review of machine learning-based zero-day attack detection: Challenges and future directions. Comput. Commun. 2023, 198, 175–185. [Google Scholar] [CrossRef]
- Yeoh, W.; Popovič, A. Extending the understanding of critical success factors for implementing business intelligence systems. J. Assoc. Inf. Sci. Technol. 2016, 67, 134–147. [Google Scholar] [CrossRef]
- Page, M.J.; McKenzie, J.E.; Bossuyt, P.M.; Boutron, I.; Hoffmann, T.C.; Mulrow, C.D.; Shamseer, L.; Tetzlaff, J.M.; Akl, E.A.; Brennan, S.E.; et al. The PRISMA 2020 statement: An updated guideline for reporting systematic reviews. Syst. Rev. 2021, 10, 89. [Google Scholar] [CrossRef]
- Barbosa-Póvoa, A.P.; da Silva, C.; Carvalho, A. Opportunities and challenges in sustainable supply chain: An operations research perspective. Eur. J. Oper. Res. 2018, 268, 399–431. [Google Scholar] [CrossRef]
- Gusenbauer, M.; Haddaway, N.R. Which academic search systems are suitable for systematic reviews or meta-analyses? Evaluating retrieval quality of Google Scholar, PubMed, and 26 other resources. Res. Synth. Methods 2020, 11, 181–217. [Google Scholar] [CrossRef]
- Higgins, J.P.T.; Green, S. (Eds.) Cochrane Handbook for Systematic Reviews of Interventions (Version 5.1.0); The Cochrane Collaboration: London, UK, 2011. [Google Scholar]
- Toorajipour, R.; Sohrabpour, V.; Nazarpour, A.; Oghazi, P.; Fischl, M. Applications of artificial intelligence in supply chain management: A systematic literature review. J. Bus. Res. 2021, 122, 502–517. [Google Scholar] [CrossRef]
- National Institute of Standards and Technology. Framework for Improving Critical Infrastructure Cybersecurity, Ver. 1.0; NIST: Gaithersburg, MD, USA, 2014.
- ISO 27001; Information Technology, Security Techniques, Information Security Management Systems, Requirements. International Organization for Standardization ISO: Geneve, Switzerland, 2005.
- Vinayakumar, R.; Soman, K.P.; Velan, K.S.; Ganorkar, S. Evaluating shallow and deep networks for ransomware detection and classification. In 2017 International Conference on Advances in Computing, Communications and Informatics (ICACCI); IEEE: Piscataway, NJ, USA, 2017; pp. 1609–1618. [Google Scholar]
- Hammi, B.; Zeadally, S.; Nebhen, J. Security threats, countermeasures, and challenges of digital supply chains. ACM Comput. Surv. 2023, 55, 1–40. [Google Scholar] [CrossRef]
- Pandey, S.; Singh, R.K.; Gunasekaran, A.; Kaushik, A. Cyber security risks in globalized supply chains: A conceptual framework. J. Glob. Oper. Strateg. Sourc. 2020, 13, 103–128. [Google Scholar] [CrossRef]
- Quintero-Bonilla, S.; Martín del Rey, A. A new proposal on the advanced persistent threat: A survey. Appl. Sci. 2020, 10, 3874. [Google Scholar] [CrossRef]
- Sobb, T.; Turnbull, B.; Moustafa, N. Supply Chain 4.0: A survey of cyber security challenges, solutions and future directions. Electronics 2020, 9, 1864. [Google Scholar] [CrossRef]
- Ang, L.-M.; Seng, K.P.; Zungeru, A.M.; Ijemaru, G.K. Big sensor data systems for smart cities. IEEE Internet Things J. 2017, 4, 2246–2257. [Google Scholar] [CrossRef]
- Kourtit, K.; Nijkamp, P.; Steenbruggen, J. The significance of digital data systems for smart city policy. Socio-Econ. Plan. Sci. 2017, 58, 30–40. [Google Scholar] [CrossRef]
- Wang, G.; Gunasekaran, A.; Ngai, E.W.T.; Papadopoulos, T. Big data analytics in logistics and supply chain management: Certain investigations for research and applications. Int. J. Prod. Econ. 2016, 176, 98–110. [Google Scholar] [CrossRef]
- Lamba, K.; Singh, S.P. Big data analytics in supply chain management: Some conceptual frameworks. Int. J. Syst. Control. Commun. 2017, 28, 877–890. [Google Scholar] [CrossRef]
- Ivanov, D.; Dolgui, A.; Das, A.; Sokolov, B. Digital supply chain twins: Managing the ripple effect, resilience, and disruption risks by data-driven optimization, simulation, and visibility. In Handbook of Ripple Effects in the Supply Chain; Ivanov, D., Dolgui, A., Sokolov, B., Eds.; Springer: Cham, Switzerland, 2019; pp. 309–332. [Google Scholar]
- Dorri, A.; Kanhere, S.S.; Jurdak, R.; Gauravaram, P. Blockchain for IoT security and privacy: The case study of a smart home. In Proceedings of the 2017 IEEE International Conference on Pervasive Computing and Communications Workshops (PerCom Workshops), Kona, HI, USA, 13 March 2017; pp. 618–623. [Google Scholar]
- Kshetri, N. Blockchain’s roles in strengthening cybersecurity and protecting privacy. Telecommun. Policy 2017, 41, 1027–1038. [Google Scholar] [CrossRef]
- Sangeetha, M. Smart supply chain management using internet of things. Int. J. Syst. Control. Commun. 2018, 9, 172–184. [Google Scholar] [CrossRef]
- Nguyen, T.; Li, Z.H.; Spiegler, V.; Ieromonachou, P.; Lin, Y. Big data analytics in supply chain management: A state-of-the-art literature review. Comput. Oper. Res. 2018, 98, 254–264. [Google Scholar] [CrossRef]
- Kshetri, N. 1 Blockchain’s roles in meeting key supply chain management objectives. Int. J. Inf. Manag. 2018, 39, 80–89. [Google Scholar] [CrossRef]
- Radanliev, P.; De Roure, D.C.; Nicolescu, R.; Huth, M.; Montalvo, R.M.; Cannady, S.; Burnap, P. Future developments in cyber risk assessment for the internet of things. Comput. Ind. 2018, 102, 14–22. [Google Scholar] [CrossRef]
- Roopak, M.; Tian, G.Y.; Chambers, J. Deep learning models for cyber security in IoT networks. In Proceedings of the 2019 IEEE 9th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 7 January 2019; pp. 0452–0457. [Google Scholar]
- Tissir, S.; El Fezazi, S.; Cherrafi, A. Industry 4.0 impact on lean manufacturing: Literature review. In Proceedings of the 2020 IEEE 13th International Colloquium of Logistics and Supply Chain Management (LOGISTIQUA), Fez, Morocco, 2 December 2020; pp. 1–5. [Google Scholar]
- Hassija, V.; Chamola, V.; Gupta, V.; Jain, S.; Guizani, N. A Survey on Supply Chain Security: Application Areas, Security Threats, and Solution Architectures. IEEE Internet Things J. 2020, 8, 6222–6246. [Google Scholar] [CrossRef]





| Publication Year | Number of Studies | Percentage |
|---|---|---|
| 2016–2017 | 7 | 20% |
| 2018–2019 | 8 | 22.9% |
| 2020–2021 | 9 | 25.7% |
| 2022–2023 | 7 | 20% |
| 2024–2025 | 4 | 11.4% |
| Total | 35 | 100% |
| Methodology | Number of Studies | Percentage |
|---|---|---|
| Theoretical Reviews | 12 | 34.3% |
| Empirical Studies | 10 | 28.6% |
| Case Studies | 8 | 22.9% |
| Mixed method | 5 | 14.3% |
| Total | 35 | 100% |
| ML/BI Technique | Number of Studies | Percentage | Key Applications |
|---|---|---|---|
| ML Technique | |||
| Neural Networks | 10 | 28.70% | Anomaly detection, threat prediction |
| Supervised Learning Algorithms | 6 | 17.10% | Threat classification, attack detection |
| Unsupervised Learning Algorithms | 4 | 11.40% | Pattern recognition, clustering threats |
| BI Technique | |||
| Predictive Analytics | 9 | 25.70% | Risk forecasting, vulnerability assessment |
| Big Data Analytics | 4 | 11.40% | Real-time monitoring, trend analysis |
| Business Intelligence Dashboards | 2 | 5.70% | Visualization, decision support |
| Total | 35 | 100% |
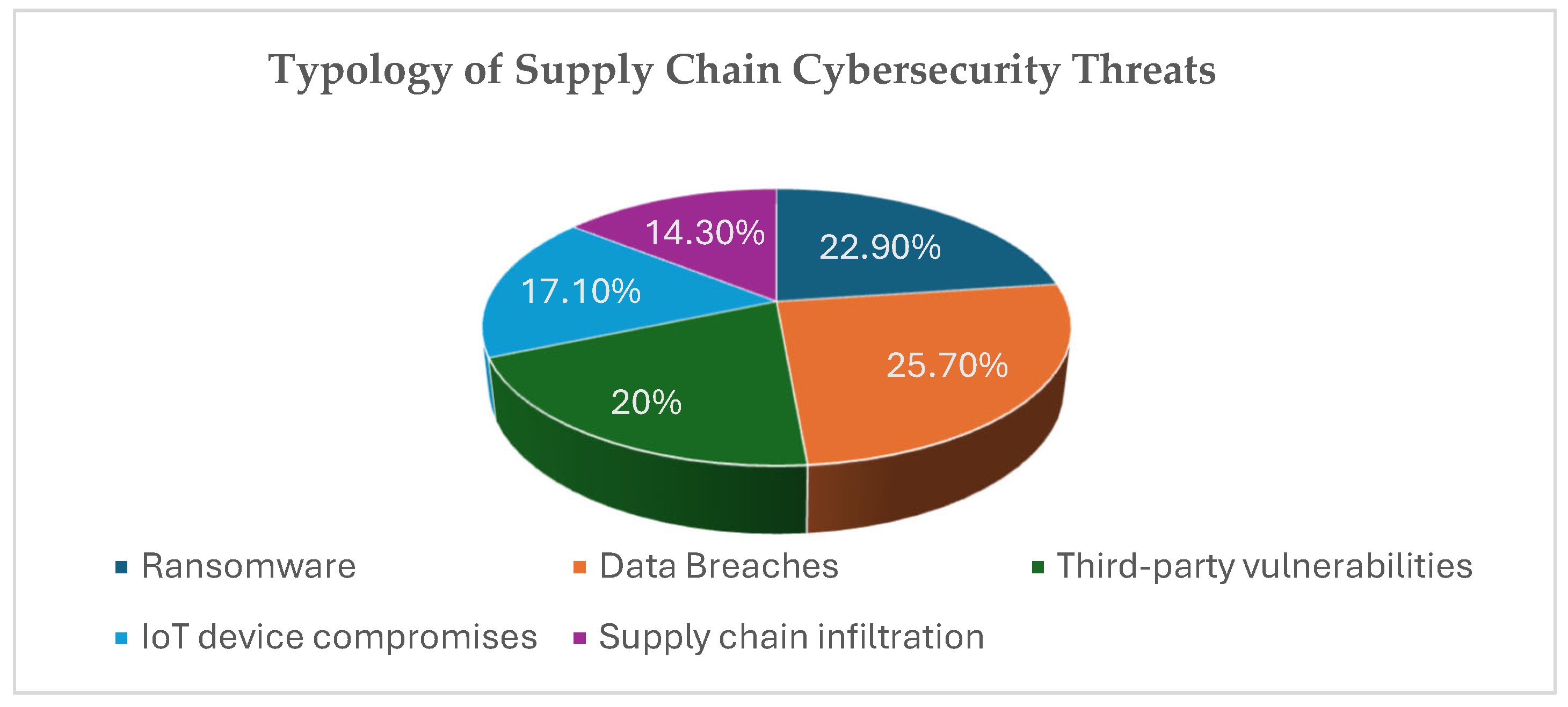
| Cybersecurity Risk Type | Number of Studies | Percentage | Key Characteristics |
|---|---|---|---|
| Data Breaches | 9 | 25.7% | Unauthorized access, data theft |
| Ransomware | 8 | 22.9% | System lockdown, extortion |
| Third-party vulnerabilities | 7 | 20% | Vendor security gaps, trust exploitation |
| IoT device compromises | 6 | 17.1% | Connected device weaknesses, botnet recruitment |
| Supply chain infiltration | 5 | 14.3% | Long-term persistence, stealthy operations |
| Total | 35 | 100% |
| Quality Dimension | Average Score (1–5) | Standard Deviation | Interpretation |
|---|---|---|---|
| Methodological rigor | 3.8 | 0.7 | Strong |
| Theoretical foundation | 3.5 | 0.9 | Moderate to strong |
| Data quality | 3.2 | 1.1 | Moderate |
| Analytical approach | 3.7 | 0.8 | Strong |
| Practical implications | 3.4 | 1.0 | Moderate to strong |
| Overall Quality | 3.5 | 0.9 | Moderate to strong |
| Period | No. Studies | Percentage | Primary Focus | ML-BI Integration | Line Number (Appendix A) |
|---|---|---|---|---|---|
| 2016–2017 | 7 | 20.0% | Foundational ML/BI applications in SCM | Low | 1–7 |
| 2018–2019 | 8 | 22.9% | Big Data Analytics emergence, IoT security | Moderate | 8–15 |
| 2020–2021 | 9 | 25.7% | COVID-19 cybersecurity challenges, threat detection | High | 16–24 |
| 2022–2023 | 7 | 20.0% | ML-BI integration frameworks, risk assessment | High | 25–31 |
| 2024–2025 | 4 | 11.4% | Applied frameworks, real-time analytics | Very High | 32–35 |
| Framework Layers | Primary Functions | Key Output |
| Data Collection & Management (Layer 1) | Capture security events across supply chain systems | Structured security data and event logs |
| Machine Learning Predictive (Layer 2) | Detect anomalies and identify threats | Threat alerts and risk scores |
| Business Intelligence Analytical (Layer 3) | Assess threat severity and organizational impact | Risk assessments and impact analyses |
| Response & Governance (Layer 4) | Support strategic cybersecurity decision | Cybersecurity decisions and action plans |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Aljaafreh, R.; Al-Doghman, F.; Hussain, F.; Khan, F.; Aljaafreh, A. Integrating Machine Learning and Business Intelligence into Supply Chain Risk Management for a Comprehensive Cybersecurity Framework: A Systematic Literature Review. Technologies 2026, 14, 194. https://doi.org/10.3390/technologies14040194
Aljaafreh R, Al-Doghman F, Hussain F, Khan F, Aljaafreh A. Integrating Machine Learning and Business Intelligence into Supply Chain Risk Management for a Comprehensive Cybersecurity Framework: A Systematic Literature Review. Technologies. 2026; 14(4):194. https://doi.org/10.3390/technologies14040194
Chicago/Turabian StyleAljaafreh, Rasha, Firas Al-Doghman, Farookh Hussain, Fazlullah Khan, and Ali Aljaafreh. 2026. "Integrating Machine Learning and Business Intelligence into Supply Chain Risk Management for a Comprehensive Cybersecurity Framework: A Systematic Literature Review" Technologies 14, no. 4: 194. https://doi.org/10.3390/technologies14040194
APA StyleAljaafreh, R., Al-Doghman, F., Hussain, F., Khan, F., & Aljaafreh, A. (2026). Integrating Machine Learning and Business Intelligence into Supply Chain Risk Management for a Comprehensive Cybersecurity Framework: A Systematic Literature Review. Technologies, 14(4), 194. https://doi.org/10.3390/technologies14040194






