Misbehavior Scenarios in Cognitive Radio Networks
Abstract
:1. Introduction
2. Spectrum Sharing Processes
2.1. Sensing and Monitoring
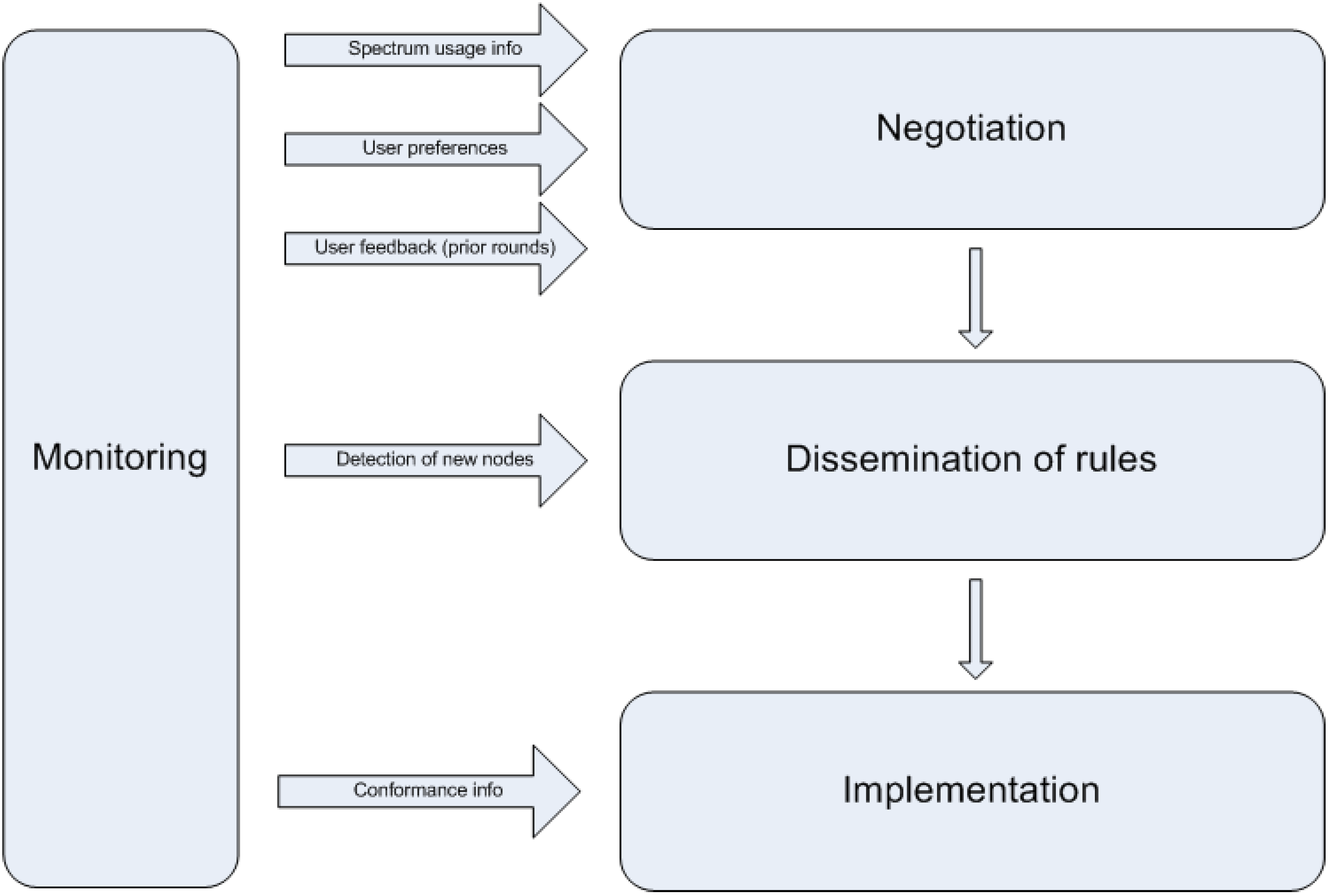
2.2. Negotiation
2.3. Distribution of Rules
2.4. Implementation
3. Attacker Profiles
- ▪
- Malicious nodes are nodes violating the rules on purpose, without even necessarily attempting to obtain direct (short-term) benefit. Their goal is to cause disturbance either to the underlying network as a whole, or to selected (victim) nodes.
- ▪
- Rational nodes are those whose aim is to increase their utility (gained by using the underlying network), mainly by using more spectrum resources (bands, or larger time frames, or codes etc.) than those assigned to them or agreed to by them (possibly implicitly). Rational nodes may attempt to determine unused resources and use them against explicit or implicit allocations, with no negative effect to others, or cheat, i.e., attempt to maximize their payoff by degrading the performance of others (which are cheated out of their allocated resources).
4. Security Threats
4.1. Sensing and Monitoring
- ▪
- Primary user masking: A (malicious) node may transmit signals able to mask the primary user’s ones towards misleading the spectrum sensing procedure. Thus, a legitimate node would not be able to detect the primary user’s transmissions and falsely assume it found a spectrum hole [24].
- ▪
- Primary user emulation (PUE) attacks: A node may transmit elaborately created signals which seem exactly the same as a primary user’s ones. A sensing node may be unable to distinguish the real from the fake signals and falsely mark a spectrum portion as occupied by a primary user and defer its transmission, thus leaving more spectrum for the attacker. Mechanisms to counter PUE attacks are presented in [17,29,30].
- ▪
- Non-standards-compliant sensing techniques: Standards as to how sensing should be implemented or requirements so that the desired sensing performance is achieved may be in place. Here we refer to cases when, either due to malice or selfishness, or even due to software or hardware failures, nodes do not follow the stipulated sensing behavior and we elaborate with some examples. First, nodes may use sensing intervals that are too long in order to allow for a timely reaction, e.g., to the appearance of a licensed user. Second, a node may not release a channel for sensing purposes in due time (given that sensing is to be performed at specified intervals, time during which secondary users need to remain “silent”). Other examples of misbehavior would be deliberately introducing de-synchronization between nodes, in order to blur the boundary between deliberate and accidental misuse or sensing with insufficient sensitivity. Finally, there is the case for tampering with spectrum sensor software and hardware to affect their normal and stable operation [31].
4.2. Negotiation
4.2.1. Negotiation Obstruction
4.2.2. Fake Spectrum Requests Injection
4.2.3. Spectrum Requests Falsification
4.2.4. Client Feedback Falsification
4.2.5. Spectrum Needs Over-reporting
4.2.6. False Claims of Continuous Changing Demands or Environmental Conditions
4.2.7. Auction Cheating
- ▪
- Bid Shielding [47]: An attacking node may announce an extremely high bid to a sharing mechanism with the view to discourage its competitors from making any more offers. Since each node maintains its own affordable upper bid limit, in such a case it would be obliged to retire early from the whole process. To make things worse, if a node has the right to retract its last bid, allowing the second biggest one to be accepted, a number of colluding nodes may exploit such a vulnerability to successfully mislead the underlying mechanism and gain access to the auctioned spectrum at a really low price.
- ▪
- Shilling: One or more attacking nodes may announce sequential bids to a sharing mechanism with aiming to increase the winning price of a special spectrum portion. In fact, these nodes may even have no intention to win the auction, but their sole objective would be to press nodes in real need of the available spectrum to offer more and more money.
- ▪
- Sniping: An attacking node may choose to announce a high (or higher than the current) bid, just before an auction closes. As a consequence, none of its opponents would have the time to respond with a higher one, losing automatically the chance to gain access to the spectrum. Since nodes could stop offering higher bids even before reaching the highest price they can afford (for example when they know that there has been no higher bid offered by their competitors until then), a legitimate node could fail to win the auction, even if it had not reached its price limit.
- ▪
- Bidding ring and loser collusion [48]: These types of attacks are closely related to those already described in Section 4.2.5.
- ▪
- Sub-leasing [48]: One or more cheating nodes may do their best to win an auction at the lowest possible price and, in turn, sublease the spectrum to others (and losers of the original auction may be included). The primary objective of such an attacker would be to earn extra profit at zero cost by gaining benefits which should be credited to the original spectrum auctioneer.
4.2.8. Fake Complaints Regarding the Received QoS
4.2.9. Identity Theft and the Use of Multiple Identities
4.3. Distribution of Sharing Rules
4.3.1. Rules Never Received Claim
4.3.2. Altered/Distorted Rules Received Claim
4.3.3. Unreachable Rules
- ▪
- Positive rules: This category contains rules defining the conditions under which a node is allowed to use the available resources.
- ▪
- Negative rules: These rules define the requirements to be satisfied to prevent a node from using the aforementioned resources.
4.3.4. Fake Rules Injection
4.3.5. Rules Altering
4.4. Implementation
4.4.1. Timeslots Usage Violation
4.4.2 Transmission Power Thresholds Violation
4.4.3 Channel Usage Violation
4.4.4. Control and Management Time Period Violations
4.4.5. Common Control Channel Jamming
4.4.6. Identity Theft/Multiple Identities
4.4.7. NEPA, CEPA and LORA Parasite Attacks
5. Conclusions
Acknowledgement
References
- Polyzos, G.C.; Jerman-Blažič, B.; Trossen, D.; Kennedy, D.; Hailes, S.; Mähönen, P.; Papadimitriou, D. The EIFFEL approach towards Visions for a Future Networked Society. In Proceedings of the ICT Mobile Summit Conference & Exhibition, Santander, Spain, June 2009.
- Hui, S.Y. Challenges in the Migration to 4G Mobile Systems. IEEE Commun. Mag. 2003, 41, 54–59. [Google Scholar]
- Frattasi, S.; Fathi, H.; Fitzek, F.H.P; Prasad, R. Defining 4G Technology from the User’s Perspective. IEEE Network 2006, 6, 35–41. [Google Scholar]
- ITU Internet Reports 2005: The Internet of Things. Available online: http://www.itu.int/osg/spu/publications/internetofthings/index.html/ (accessed on 9 July 2010).
- Botterman, M. Internet of Things: An early reality of the Future Internet; Workshop Report for European Commission, Information Society and Media Directorate General; Networked Enterprise & RFID Unit (D4): Prague, Czech Republic, 10 May 2009. [Google Scholar]
- Akan, O.B.; Karli, O.B; Ergul, O. Cognitive Radio Sensor Networks. IEEE Network 2009, 23, 34–40. [Google Scholar]
- Akyildiz, I.F.; Lee, W.Y; Vuran, M.C.; Mohanty, S. Next generation/dynamic spectrum access/cognitive radio wireless networks: A Survey. Comput. Netw. 2006, 50, 2127–2159. [Google Scholar]
- Akyildiz, I.F.; Lee, W.Y.; Vuran, M.C.; Mohanty, S. A Survey on Spectrum Management in Cognitive Radio Networks. IEEE Commun. Mag. 2008, 46, 40–48. [Google Scholar]
- McCoy, D.; Sicker, D.; Grunwald, D. A Mechanism for Detecting and Responding to Misbehaving Nodes in Wireless Networks. In Proceedings of the 4th Annual IEEE Conference on Sensor, Mesh and Ad Hoc Communications and Networks (SECON '07), San Diego, CA, USA, June 2007.
- Berlemann, L.; Hiertz, G.R.; Walke, B.; Mangold, S. Strategies for distributed QoS support in radio spectrum sharing. In Proceedings of the IEEE International Conference on Communications (ICC’05), Seoul, Korea, May 2005.
- Fattahi, A.R.; Fangwen, F.; van der Schaar, M.; Paganini, F. Mechanism-based resource allocation for multimedia transmission over spectrum agile wireless networks. IEEE J. Sel. Area. Commun. 2007, 25, 601–612. [Google Scholar]
- Ycek, T.; Arslan, H. A survey of spectrum sensing algorithms for cognitive radio applications. IEEE Commun. Surv. Tutorial. 2009, 11, 116–160. [Google Scholar]
- Zhang, R.; Liang, Y.C. Exploiting hidden power-feedback loops for cognitive radio. In Proceedings of IEEE DySPAN 2008, Chicago, IL, USA, October 2008.
- Zhao, G.; Li, Y.G.; Yang, C. Proactive detection of spectrum holes in cognitive radio. In Proceedings of the IEEE International Conference on Communications (ICC’09), Dresden, Germany, June 2009.
- Cabric, D; Mishra, S.M.; Brodersen, R.W. Implementation Issues in Spectrum Sensing. In Proceedings of the Asilomar Conference on Signal, Systems and Computers, Pacific Grove, CA, USA, November 2004.
- Isaksson, L.; Fiedler, M.; Rakus-Andersson, E. A Fuzzy Set Theory Based Method to Discover Transmissions in Wireless Personal Area Networks. In Proceedings of ICWMC'06, Bucuresti, Romania, July 2006.
- Chen, R; Park, J.-M.; Reed, J.H. Defense against primary user emulation attacks in cognitive radio networks. IEEE J. Sel. Area. Commun. 2008, 26, 25–37. [Google Scholar]
- Cao, L.; Zheng, H. Distributed Spectrum Allocation via Local Bargaining. In Proceedings of IEEE SECON’05, Santa Clara, CA, USA, September 2005.
- Peng, C.; Zheng, H.; Zhao, B.Y. Utilization and fairness in spectrum assignment for opportunistic spectrum access. Mobile Netw. Appl. 2006, 11, 555–576. [Google Scholar]
- Steenstrup, M. Opportunistic use of radio-frequency spectrum: a network perspective. In Proceedings of IEEE DySPAN 2005, Baltimore, MD, USA, November 2005.
- Neel, J.; Reed, J. Performance of distributed dynamic frequency selection schemes for interference reducing networks. In Proceedings of IEEE MILCOM 2006, Washington, DC, USA, October 2006.
- Nie, N.; Comaniciu, C. Adaptive channel allocation spectrum etiquette for cognitive radio networks. In Proceedings of IEEE DySPAN 2005, Baltimore, MD, USA, November 2005.
- Vamsi Krishna, T; Das, A. A survey on MAC protocols in OSA networks. Comput. Netw. 2009, 53, 1377–1394. [Google Scholar]
- Brown, T.X.; Sethi, A. Potential cognitive radio denial-of-service vulnerabilities and protection countermeasures: a multidimensional analysis and assessment. In Proceedings of the 2nd International Conference on Cognitive Radio Oriented Wireless Networks and Communications (CrownCom 2007), Orlando, FL, USA, 9 August 2007.
- Popescu, A; Erman, D.; Fiedler, M; Kouvatsos, D. A Multi-Dimensional CAN Approach to CRN Routing. In Proceedings of the 6th International Working Conference on Performance Modeling and Evaluation of Heterogeneous Networks (HET-NETs), Zakopane, Poland, 14–16 January 2010.
- Efstathiou, E. A Peer-to-Peer Approach to Sharing Wireless Local Area Networks. Ph.D. Thesis, Athens University of Economics and Business, Athens, Greece, June 2006. [Google Scholar]
- Buttyán, L.; Hubaux, J.P. Security and Cooperation in Wireless Networks; Cambridge University Press: Cambridge, UK, 2008. [Google Scholar]
- Arkoulis, S.; Kazatzopoulos, L.; Delakouridis, C.; Marias, G.F. Cognitive Spectrum and its Security Issues. In Proceedings of the 2nd IEEE International Conference on Next Generation Mobile Applications, Services, and Technologies (NGMAST), Cardiff, Wales, UK, September 2008.
- Chen, R.; Park, J. Ensuring Trustworthy Spectrum Sensing in Cognitive Radio Networks. In Proceedings of the 1st IEEE Workshop on Networking Technologies for Software Defined Radio Networks, Reston, VA, USA, September 2006.
- Chen, R; Park, J.-M.; Hou, Y.T.; Reed, J.H. Toward secure distributed spectrum sensing in cognitive radio networks. IEEE Commun. Mag. 2008, 46, 50–55. [Google Scholar]
- Xiao, S.; Park, J.; Ye, Y. Tamper Resistance for Software Defined Radio Software. In Proceedings of the 33rd Annual IEEE International Computer Software and Applications Conference, Seattle, Washington, DC, USA, July 2009.
- Frangoudis, P.A.; Zografos, D.I.; Polyzos, G.C. Secure Interference Reporting for Dense Wi-Fi Deployments. In Proceedings of the ACM CoNEXT '09 Student Workshop, Rome, Italy, December 2009.
- Jia, J.; Zhang, Q.; Shen, X. HC-MAC: A hardware-constrained cognitive MAC for efficient spectrum management. IEEE J. Sel. Area. Commun. 2008, 26, 106–117. [Google Scholar]
- So, J.; Vaidya, N. Channelization: multi-channel MAC for ad hoc networks: handling multi-channel hidden terminals using a single transceiver. In Proceedings of ACM MobiHoc, Florence, Italy, May 2004.
- Thoppian, M.; Venkatesan, S.; Prakash, R.; Chandrasekaran, R. MAC layer scheduling in multi-hop wireless networks. In Proceedings of IEEE WoWMoM 2006, Niagara-Falls, Buffalo, NY, USA, June 2006.
- Romero, J.-P.; Sallent, O.; Agusti, R.; Giupponi, L. A novel on-demand cognitive pilot channel enabling dynamic spectrum allocation. In Proceedings of IEEE DySPAN 2007, Dublin, Ireland, April 2007.
- Ma, L.; Han, X.; Shen, C.-C. Dynamic open spectrum sharing MAC protocol for wireless ad hoc networks. In Proceedings of IEEE DySPAN 2005, Baltimore, MD, USA, November 2005.
- Lazos, L.; Liu, S.; Krunz, M. Mitigating control-channel jamming attacks in multi-channel ad hoc networks. In Proceedings of the Second ACM Conference on Wireless Network Security (WiSec’09), Zurich, Switzerland, March 2009.
- Brown, T.X.; James, J.E.; Sethi, A. Jamming and sensing of encrypted wireless ad hoc networks. In Proceedings of the 7th ACM International Symposium on Mobile Ad Hoc Networking and Computing (MobiHoc), Florence, Italy, May 2006.
- Bian, K.; Park, J.M. MAC-layer misbehaviors in multi-hop cognitive radio networks. In Proceedings of the 2006 US-Korea Conference on Science, Technology, and Entrepreneurship (UKC2006), Teaneck, NJ, USA, August 2006.
- Ma, L.; Shen, C.-C.; Ryu, B. Single-radio adaptive channel algorithm for spectrum agile wireless ad hoc networks. In Proceedings of IEEE DySPAN 2007, Dublin, Ireland, April 2007.
- Brik, V.; Rozner, E.; Banarjee, S.; Bahl, P. DSAP: A protocol for coordinated spectrum access. In Proceedings of IEEE DySPAN 2005, Baltimore, MD, USA, November 2005.
- Kloeck, C.; Jaekel, H.; Jondral, F. K. Dynamic and local combined pricing, allocation and billing system with coginitive radios. In Proceedings of IEEE DySPAN 2005, Baltimore, MD, USA, November 2005.
- Cramton, P.; Shoham, Y.; Steinberg, R. Combinatorial Auctions; MIT Press: Cambridge, MA, USA, 2006. [Google Scholar]
- Krishna, V. Auction Theory; Academic Press: San Diego, CA, USA, 2002. [Google Scholar]
- Ji, Z.; Liu, K.J.R. Multi-stage pricing game for collusion resistant dynamic spectrum allocation. IEEE J. Sel. Area. Commun. 2008, 26, 182–191. [Google Scholar]
- Benyoucef, M.; Alj, H.; Levy, K.; Keller, R.K. A Rule-Driven Approach for Defining the Behaviour of Negotiating Software Agents. In Proceedings of the 4th International Workshop on Distributed Communities on the Web, Sydney, Australia, April 2002.
- Wu, Y.; Wang, B.; Liu, K.; Clancy, T. Collusion-resistant multi-winner spectrum auction for cognitive radio networks. In Proceedings of IEEE Globecom, New Orleans, LA, USA, December 2008.
- Cao, L.; Zheng, H. Distributed Rule-Regulated Spectrum Sharing. IEEE J. Sel. Area. Commun. 2008, 26, 130–145. [Google Scholar]
- Rondeau, T.; Rieser, C.; Le, B.; Bostian, C. Cognitive radios with genetic algorithms: Intelligent control of software defined radios. In Proceedings of the SDR Forum Conference, Phoenix, AZ, USA, November 2004.
- Atia, G.; Saligrama, V.; Sahai, A. Codes to unmask spectrum violators. In Proceedings of the Asilomar Conference on Signals, Systems and Computers, Pacific Grove, CA, USA, October 2008.
- Xu, W.; Kamat, P.; Trappe, W. TRIESTE: A Trusted Radio Infrastructure for Enforcing SpecTrum Etiquettes. In Proceedings of the 1st IEEE Workshop on Networking Technologies for Software Defined Radio Networks, Reston, VA, USA, September 2006.
- Stallings, W. Network Security Essentials: Applications and Standards, 3rd ed.; Prentice Hall: Upper Saddle River, NJ, USA; p. 432.
- Chapin, J.M.; Lehr, W.H. The path to market success for dynamic spectrum access technology. IEEE Commun. Mag. 2007, 45, 96–103. [Google Scholar]
- Cordeiro, C.; Challapali, K. C-MAC: A cognitive MAC protocol for multi-channel wireless networks. In Proceedings of IEEE DySPAN 2007, Dublin, Ireland, April 2007.
- IEEE 802.22 Working Group on Wireless Regional Area Networks. Available online: http://www.ieee802.org/22/ (accessed on 9 July 2010).
- Atia, G.; Sahai, A.; Saligrama, V. Spectrum enforcement and liability assignment in cognitive radio systems. In Proceedings of IEEE DySPAN 2008, Chicago, IL, USA, October 2008.
- Haykin, S. Cognitive radio: brain-empowered wireless communications. IEEE J. Sel. Area. Commun. 2005, 23, 201–220. [Google Scholar]
- Narayanan, L. Channel assignment and graph multicoloring. In Handbook of Wireless Networks and Mobile Computing; John Wiley and Sons, Inc.: New York, NY, USA, 2002; pp. 71–94. [Google Scholar]
- Mody, A.N.; Reddy, R.; Sherman, M.J.; Kiernan, T.; Shyy, D.J. Security and the Protocol Reference Model Enhancements in IEEE 802.22; IEEE Document No. 802.22-08-0083r04; IEEE Standards Association: Piscataway, NJ, USA, June 2008. [Google Scholar]
- Sahai, A.; Tandra, R.; Mishra, S.M.; Hoven, N. Fundamental design tradeoffs in cognitive radio systems. In Proceedings of the 1st International Workshop on Technology and Policy For Accessing Spectrum (TAPAS’06), Boston, MA, USA, August 2006.
- Naveed, A.; Kanhere, S. Security vulnerabilities in channel assignment of multi-radio multi-channel wireless mesh networks. In Proceedings of IEEE GLOBECOM 2006, San Francisco, CA, USA, November 2006.
- All these apply independently of the category of the control channel. Note that according to [23], there are three types of control channels: global, local, and the dynamically selected ones.
© 2010 by the authors; licensee MDPI, Basel, Switzerland. This article is an Open Access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/3.0/).
Share and Cite
Arkoulis, S.; Marias, G.F.; Frangoudis, P.A.; Oberender, J.; Popescu, A.; Fiedler, M.; Meer, H.d.; Polyzos, G.C. Misbehavior Scenarios in Cognitive Radio Networks. Future Internet 2010, 2, 212-237. https://doi.org/10.3390/fi2030212
Arkoulis S, Marias GF, Frangoudis PA, Oberender J, Popescu A, Fiedler M, Meer Hd, Polyzos GC. Misbehavior Scenarios in Cognitive Radio Networks. Future Internet. 2010; 2(3):212-237. https://doi.org/10.3390/fi2030212
Chicago/Turabian StyleArkoulis, Stamatios, Giannis F. Marias, Pantelis A. Frangoudis, Jens Oberender, Alexandru Popescu, Markus Fiedler, Hermann de Meer, and George C. Polyzos. 2010. "Misbehavior Scenarios in Cognitive Radio Networks" Future Internet 2, no. 3: 212-237. https://doi.org/10.3390/fi2030212
APA StyleArkoulis, S., Marias, G. F., Frangoudis, P. A., Oberender, J., Popescu, A., Fiedler, M., Meer, H. d., & Polyzos, G. C. (2010). Misbehavior Scenarios in Cognitive Radio Networks. Future Internet, 2(3), 212-237. https://doi.org/10.3390/fi2030212




