Risk-Based Access Control Model: A Systematic Literature Review
Abstract
1. Introduction
- Reviewing recent studies of risk-based access control models by providing a summary of the contributions of each study.
- Identifying and analyzing various risk factors used in recent risk-based access control models.
- Determining and investigating different risk estimation techniques utilized in recent risk-based access control models.
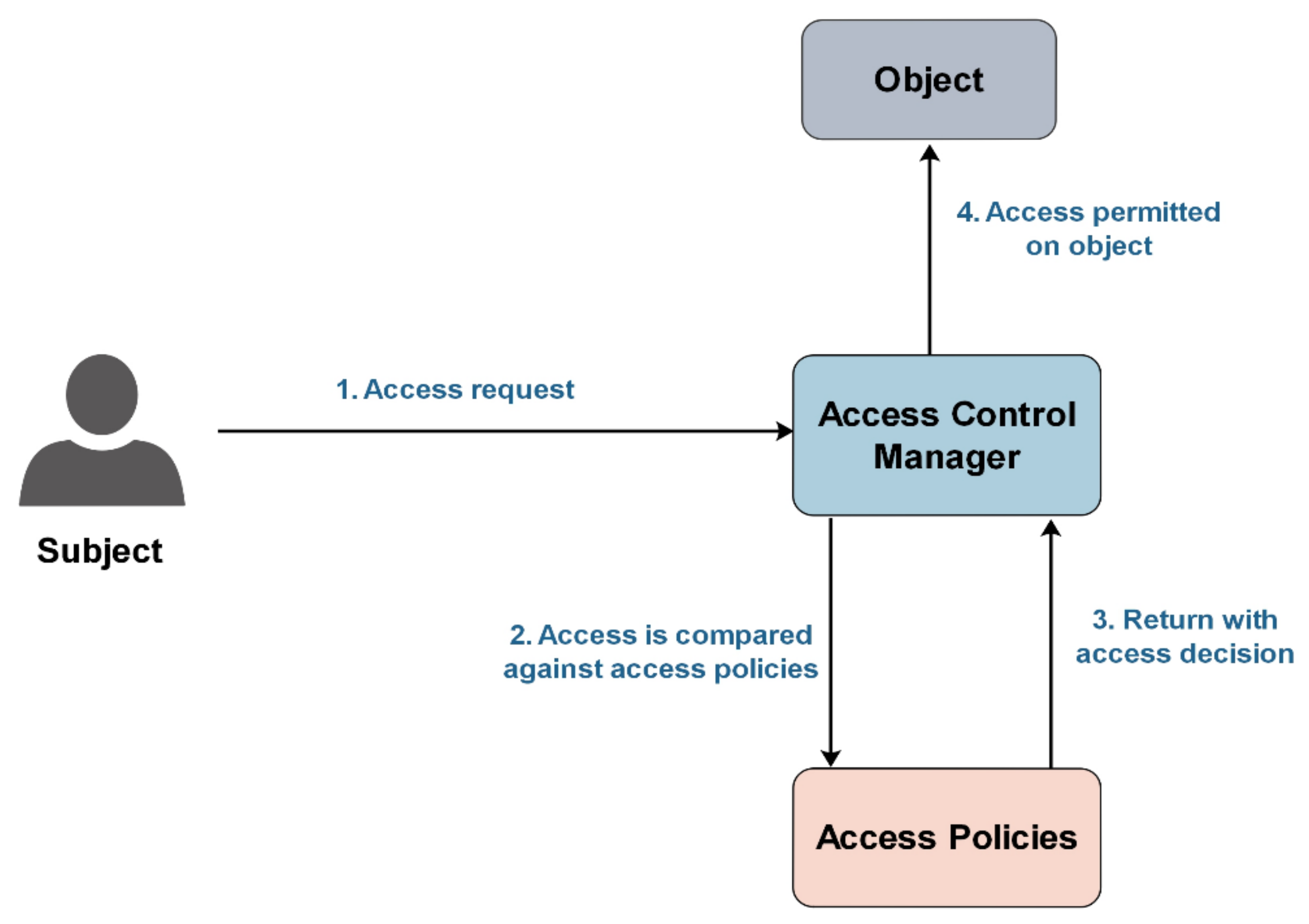
2. An Overview of Access Control
- Subjects: represents various entities that can be user, agents, or processes that make an access request to access system resources (objects).
- Objects: describes system resources encompassing data or information that needed to be accessed by subjects/users.
- Actions: represents various types of actions or activities that subjects can perform on a particular object such as read, write, execute, etc.
- Privileges: These are the permissions that are granted to subjects to be able to carry out a particular action on a particular object.
- Access policies: These are a group of rules or procedures that specify the criteria needed to determine the access decision whether granting or denying access for each access request.
2.1. Traditional Access Control Models
2.2. Dynamic Access Control Models
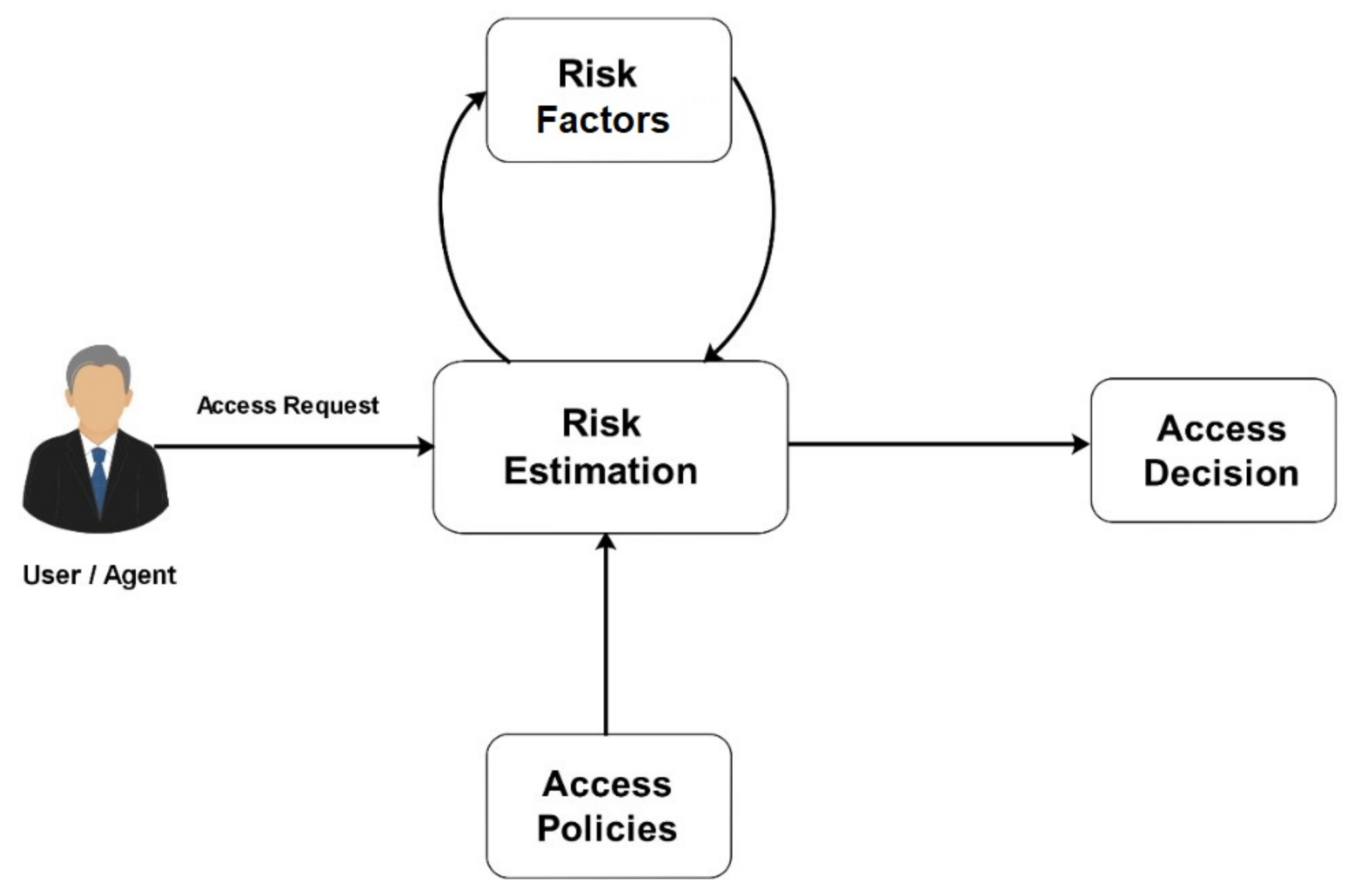
3. Risk-Based Access Control Model
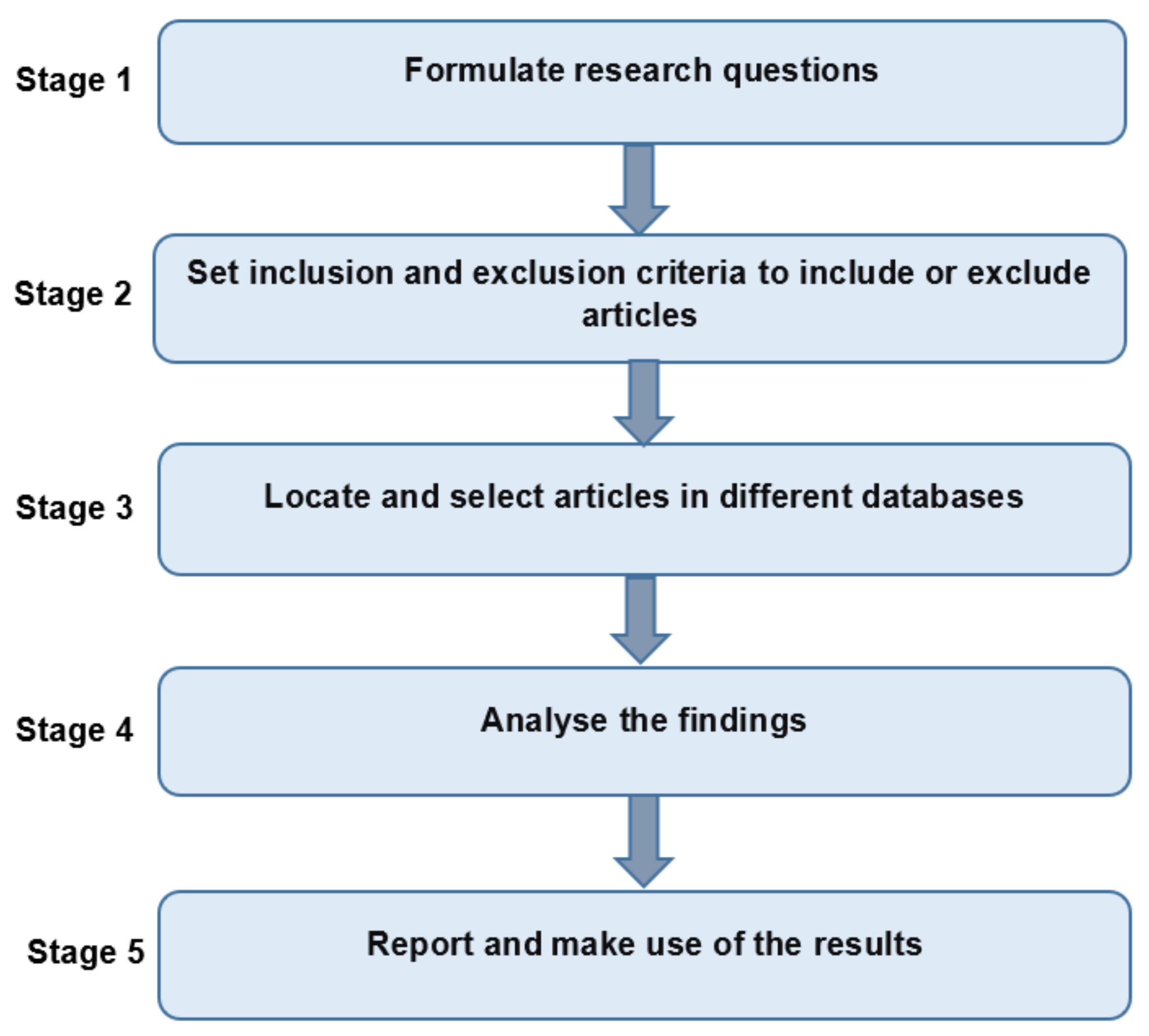
4. Methodology
4.1. Research Questions
- RQ1: What are recent and peer-reviewed literature regarding risk-based access control models?
- RQ2: What are the risk factors used to build risk-based access control models?
- RQ3: What are risk estimation techniques employed in risk-based access control models?
4.2. Inclusion and Exclusion Criteria
- Scientific and peer-reviewed articles
- Topic is mainly risk-based access control model
- Relevant to research questions
- Articles written in English
- Published any time (year of publication is open and is not limited to a specific period)
- Articles concerning risk estimation techniques that are not in the context of risk-based access control models
- Articles concerning risk factors that are not in the context of risk-based access control models
- Unpublished articles, non-peer-reviewed articles, and editorial articles
- Articles that are not fully available
- Non-English articles
- Duplicates of already included articles
4.3. Data Sources
- IEEE Xplore
- PubMed
- Elsevier ScienceDirect
- Google Scholar
- ACM Digital Library
- SpringerLink.
- Risk-Based Access Control
- Risk Estimation
- Risk estimation Technique
- Risk Factors
- Security Risk.
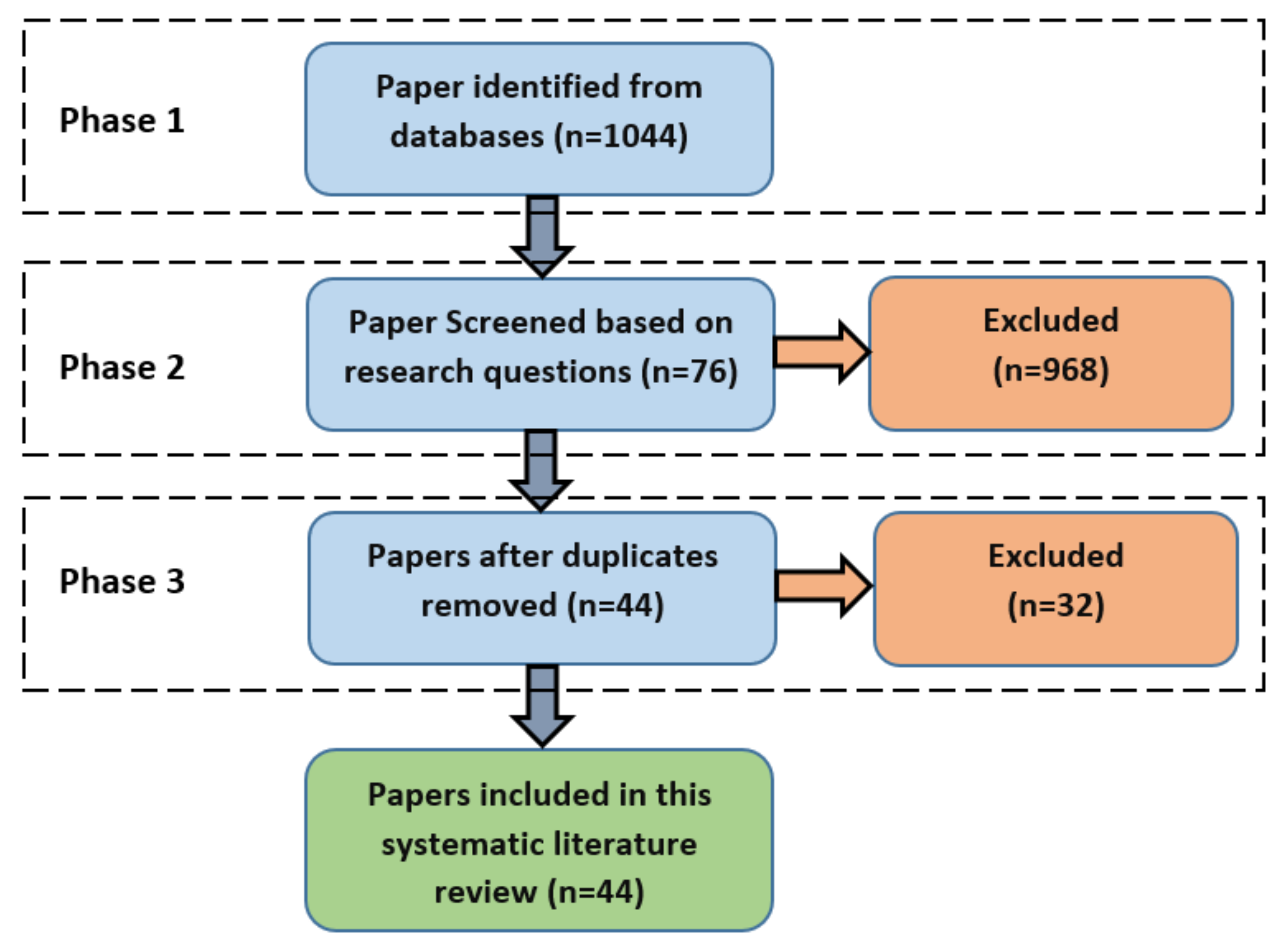
4.4. Selection of Relevant Articles
- Phase 1: The results of the search and collected publications were filtered depending on the inclusion and exclusion criteria that were discussed in Section 4.2. The search conducted was not bounded by a specific range of years to be able to collect all relevant publications regarding risk-based access control models.
- Phase 2: The publications collected from various online digital libraries were assessed depending on the relevance of the publication to the topic and research questions by examining only the title and abstract.
- Phase 3: The main purpose of this phase was to remove the duplicates of the collected publications from six different online digital libraries.
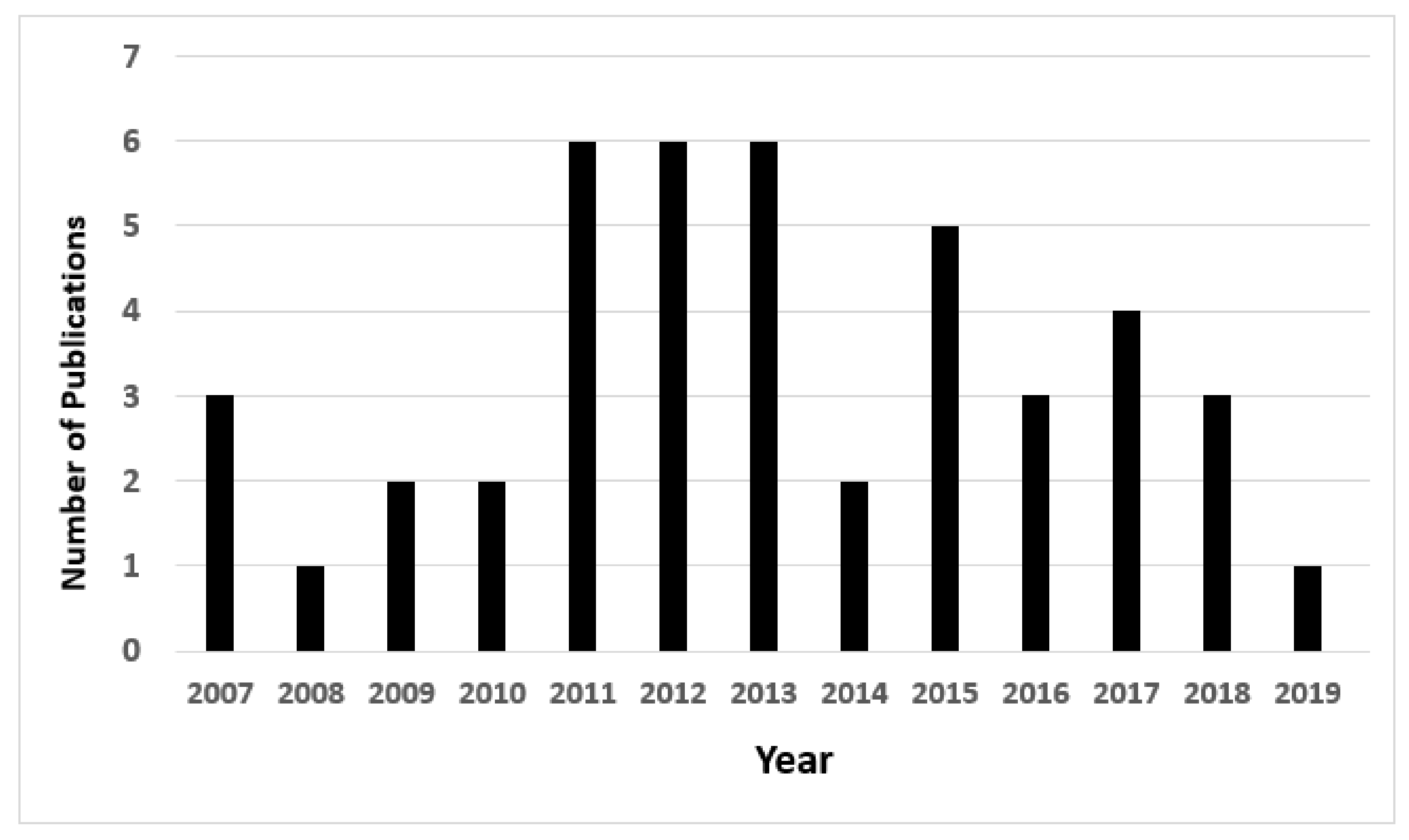
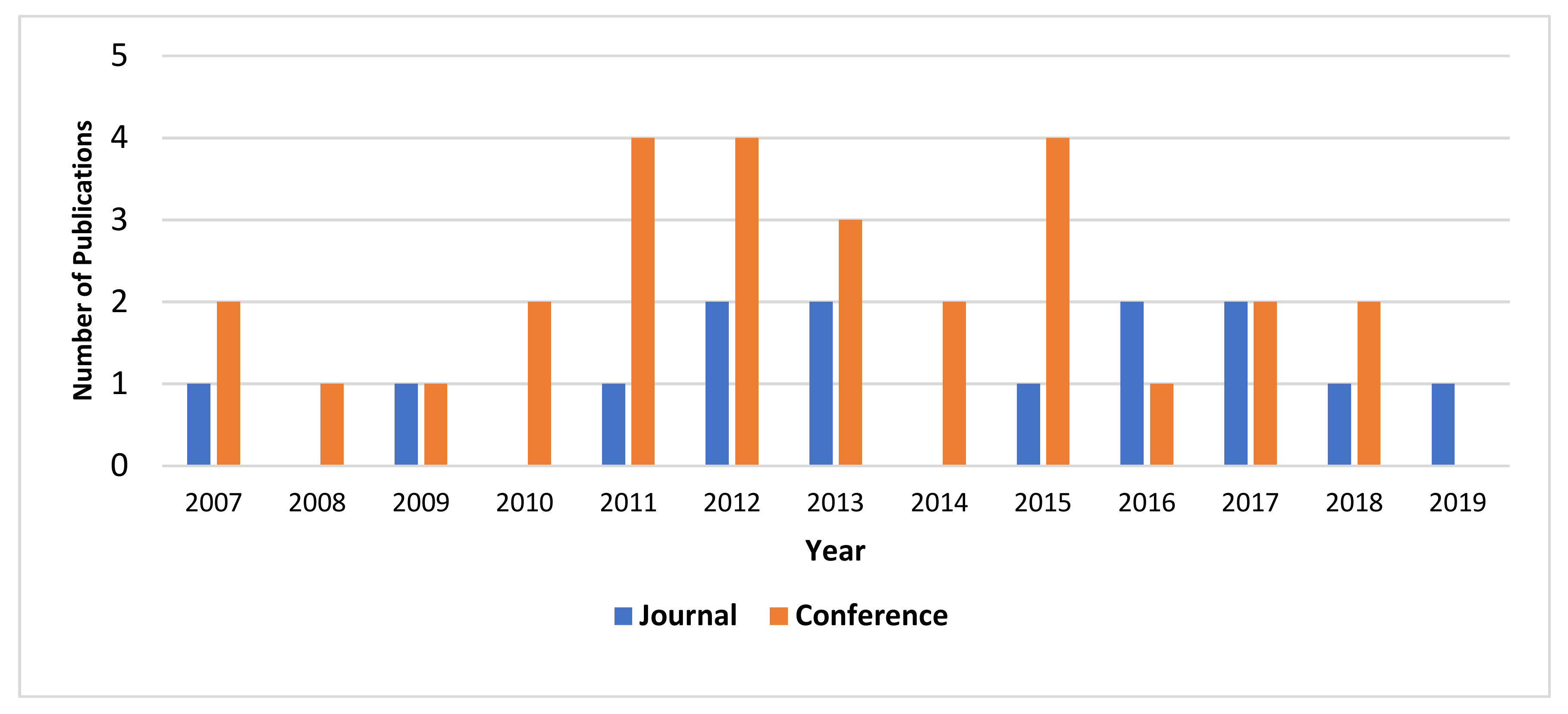
5. Analysis of Results
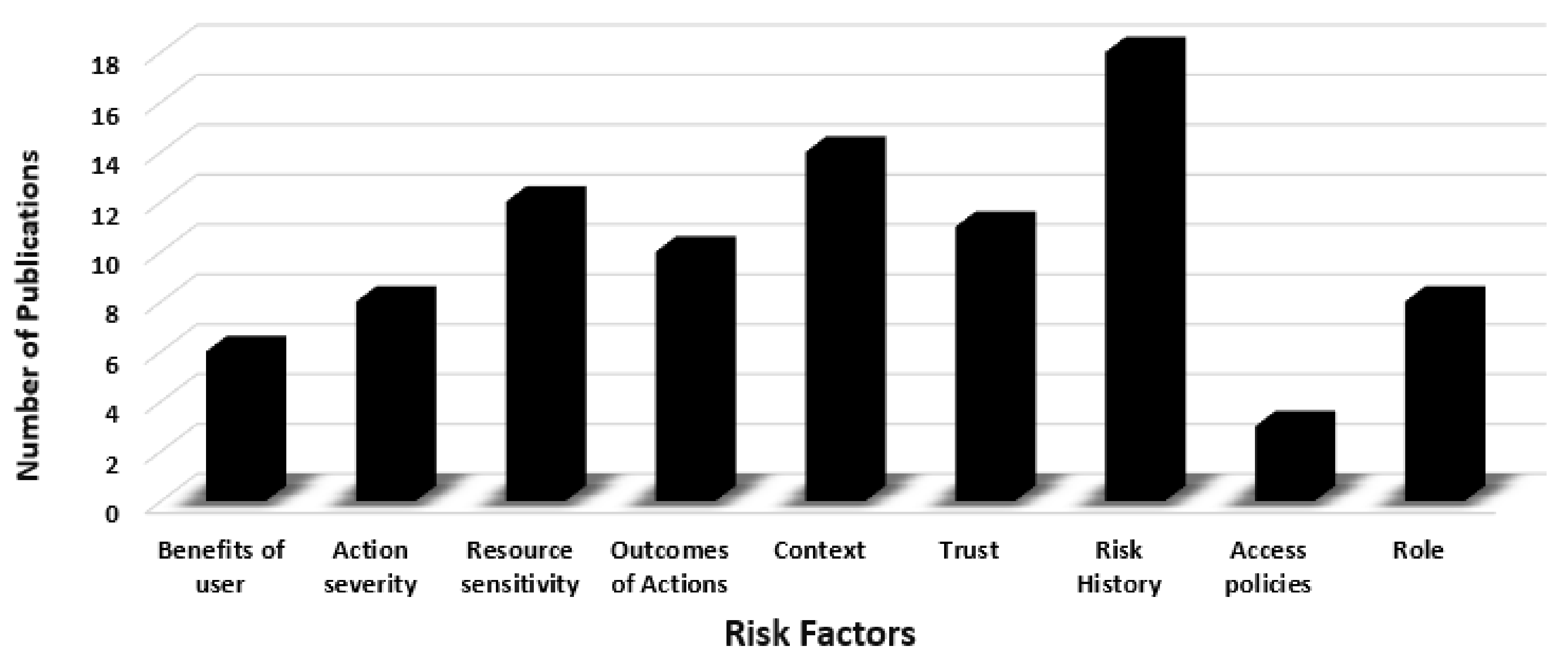
6. Discussion
- Subject Clearance (Role): It represents the subject security level acquired from the system administrator. The most popular clearances in the military are Top Secret, Secret, Confidential, and no clearance. Different access permissions are granted according to the subject role in the organization. Each role is associated with certain permissions [58]. The higher the clearance granted, the lower the associated risk value.
- Resource Sensitivity: It describes the sensitivity level of resources the user wants to access. Different sensitivity levels have different risk values. The higher the resource sensitivity, the higher the risk value if the access is granted to this resource [24].
- Action Severity: It characterizes the cost of a particular action on a particular resource in terms of confidentiality, integrity, and availability. So, different actions have different consequences and so have different risk values.
- Risk History: It represents user previous risk values on a certain resource. It can be used to detect the future behavior of the user toward a certain resource.
- Trust: It is similar to the risk history. It represents the subject/user trust toward a certain resource. Trust is classified into two categories: identity and behavioral trust. Identity trust is concerned with validating the authenticity of an object and focuses on objective credentials. While behavioral trust works with the entity’s trustworthiness, which depends on certain contexts [59]. In risk-based access control models, only behavioral trust is used.
- Benefits of User: It describes any sort of advantages/privileges the user will get when the access is granted. It also represents what will be the damage that will happen for the user if the access was denied [4].
- Outcomes of Actions: The access control system has inputs, consisting of the action and list of consequence outcomes of the action. Each outcome may occur in some specific contexts, consisting of principle context, environment context, and resource context. The outcome of actions estimates the risk of each of these contexts [20].
- Context: It signifies the real-time and environmental information that can be collected while making the access request. Contexts features are utilized to specify the security risk value related to each access request. Location and time are the most popular contexts [41].
- Access Policies: They are primarily utilized by the access control manager (risk estimation module in the risk-based access control model) to specify access decisions. These policies are designed by the resource owner or security system administrator to classify terms and situations of granting or denying access to a particular resource. In the risk-based control model, the estimated risk value resulted from the risk estimation module is compared against risk policies to decide whether granting or denying access [41].
7. Conclusions
Funding
Conflicts of Interest
References
- Dos Santos, D.R.; Westphall, C.M.; Westphall, C.B. A dynamic risk-based access control architecture for cloud computing. In Proceedings of the IEEE/IFIP NOMS 2014—IEEE/IFIP Network Operation and Managment Symposioum, Krakow, Poland, 5–9 May 2014; pp. 1–9. [Google Scholar]
- Liu, J.K.; Au, M.H.; Huang, X.; Lu, R.; Li, J. Fine-Grained Two-Factor Access Control for Web-Based Cloud Computing Services. IEEE Trans. Inf. Forensics Secur. 2016, 11, 484–497. [Google Scholar] [CrossRef]
- Suhendra, V. A Survey on Access Control Deployment. In Communications in Computer and Information Science; Kim, T., Adeli, H., Fang, W., Villalba, J.G., Arnett, K.P., Khan, M.K., Eds.; Springer: Berlin/Heidelberg, Germany, 2011; Volume 259, pp. 11–20. [Google Scholar]
- Chen, P.; Pankaj, C.; Karger, P.A.; Wagner, G.M.; Schuett, A. Fuzzy Multi—Level Security: An Experiment on Quantified Risk—Adaptive Access Control. In Proceedings of the 2007 IEEE Symposium on Security and Privacy (SP’07), Ouckland, CA, USA, 20–23 May 2007; pp. 222–227. [Google Scholar]
- Shaikh, R.A.; Adi, K.; Logrippo, L. Dynamic risk-based decision methods for access control systems. Comput. Secur. 2012, 31, 447–464. [Google Scholar] [CrossRef]
- Khambhammettu, H.; Boulares, S.; Adi, K.; Logrippo, L. A framework for risk assessment in access control systems. Comput. Secur. 2013, 39, 86–103. [Google Scholar] [CrossRef]
- Hulsebosch, R.J.; Bargh, M.S.; Lenzini, G.; Ebben, P.W.G.; Iacob, S.M. Context Sensitive Adaptive Authentication; Springer: Berlin/Heidelberg, Germany, 2007. [Google Scholar]
- Houlis, P. The History and Future of Access Control Credentials 2018. Available online: https://www.ifsecglobal.com/global/history-future-access-control-credentials/ (accessed on 9 March 2019).
- Atlam, H.F.; Alassafi, M.O.; Alenezi, A.; Walters, R.J.; Wills, G.B. XACML for Building Access Control Policies in Internet of Things. In Proceedings of the 3rd International Conference on Internet of Things, Big Data and Security (IoTBDS 2018), Madeira, Portugal, 19–21 May 2018. [Google Scholar]
- Metoui, N. Privacy-Aware Risk-Based Access Control Systems. Ph.D. Thesis, University of Trento, Trento, Italy, May 2018. [Google Scholar]
- Bugiel, S.; Heuser, S.; Sadeghi, A.-R. Flexible and fine-grained mandatory access control on Android for diverse security and privacy policies. In Proceedings of the 22nd USENIX Security Symposium, Washington, DC, USA, 14–16 August 2013; pp. 131–146. [Google Scholar]
- Hulsebosch, R.J.; Salden, A.H.; Bargh, M.S.; Ebben, P.W.G.; Reitsma, J. Context sensitive access control. In Proceedings of the Tenth ACM Symposium on Access Control Models and Technologies, Stockholm, Sweden, 1–3 June 2005; pp. 111–119. [Google Scholar]
- Bijon, K.Z.; Krishnan, R.; Sandhu, R. A framework for risk-aware role based access control. In Proceedings of the IEEE Conference on Communications and Network Security, National Harbor, MD, USA, 14–16 October 2013; pp. 462–469. [Google Scholar]
- Kumar, A.; Karnik, N.M.; Chafle, G. Context sensitivity in role-based access control. Oper. Syst. Rev. 2002, 36, 53–66. [Google Scholar] [CrossRef]
- Wang, Q.; Jin, H. Quantified risk-adaptive access control for patient privacy protection in health information systems. In Proceedings of the 6th ACM Symposium on Information, Computer and Communications Security—ASIACCS ’11, Hong Kong, China, 22–24 March 2011; pp. 406–410. [Google Scholar]
- Brooks, T.; Caicedo, C.; Park, J.S. Security Vulnerability Analysis in Virtualized Computing Environments. Int. J. Intell. Comput. Res. 2012, 3, 263–277. [Google Scholar] [CrossRef]
- Li, Y.; Sun, H.; Chen, Z.; Ren, J.; Luo, H. Using Trust and Risk in Access Control for Grid Environment. In Proceedings of the Security Technology, Hainan Island, China, 13–15 December 2008; pp. 13–16. [Google Scholar]
- Elky, S. An Introduction to Information System Risk Management; Sans Institute: Bethesda, MD, USA, 2006. [Google Scholar]
- Atlam, H.F.; Walters, R.J.; Wills, G.B. Fog computing and the internet of things: A review. Big Data Cogn. Comput. 2018, 2, 1–18. [Google Scholar]
- Diep, N.N.; Hung, L.X.; Zhung, Y.; Lee, S.; Lee, Y.; Lee, H. Enforcing Access Control Using Risk Assessment. In Proceedings of the Fourth European Conference on Universal Multiservice Networks, Toulouse, France, 14–16 February 2007; pp. 419–424. [Google Scholar]
- Kitchenham, B.; Charters, S. Guidelines for Performing Systematic Literature Reviews in Software Engineering; University of Durham: Durham, UK, 2007. [Google Scholar]
- Ricardo, D.; Marinho, R.; Schmitt, G.R.; Westphall, C.M.; Westphall, C.B. A Framework and Risk Assessment Approaches for Risk-based Access Control in the Cloud. J. Netw. Comput. Appl. 2016, 74, 1–27. [Google Scholar]
- Choi, D.; Kim, D.; Park, S. A Framework for Context Sensitive Risk-Based Access Control in Medical Information Systems. Comput. Math. Methods Med. 2015, 2015, 265132. [Google Scholar] [CrossRef] [PubMed]
- Li, J.; Bai, Y.; Zaman, N. A fuzzy modeling approach for risk-based access control in eHealth cloud. In Proceedings of the 12th IEEE International Conference on Trust, Security and Privacy in Computing and Communications, Melbourne, Australia, 16–18 July 2013; pp. 17–23. [Google Scholar]
- Arias-Cabarcos, P.; Rez-Mendoza, F.A.; Marín-López, A.; Díaz-Sánchez, D.; Sánchez-Guerrero, R. A metric-based approach to assess risk for ‘On cloud’ federated identity management. J. Netw. Syst. Manag. 2012, 20, 513–533. [Google Scholar] [CrossRef]
- Baracaldo, N.; Joshi, J. An adaptive risk management and access control framework to mitigate insider threats. Comput. Secur. 2013, 39, 237–254. [Google Scholar] [CrossRef]
- Kandala, S.; Sandhu, R.; Bhamidipati, V. An Attribute Based Framework for Risk-Adaptive Access Control Models. In Proceedings of the Sixth International Conference on Availability, Reliability and Security, Vienna, Austria, 22–26 August 2011; pp. 236–241. [Google Scholar]
- Lee, S.; Lee, Y.W.; Diep, N.N.; Lee, S.; Lee, Y.; Lee, H. Contextual Risk-based access control. Secur. Manag. 2007, 2007, 406–412. [Google Scholar]
- Atlam, H.F.; Wills, G.B. An efficient security risk estimation technique for Risk-based access control model for IoT. Internet Things 2019, 6, 1–20. [Google Scholar] [CrossRef]
- Diaz-Lopez, D.; Dolera-Tormo, G.; Gomez-Marmol, F.; Martinez-Perez, G. Dynamic counter-measures for risk-based access control systems: An evolutive approach. Futur. Gener. Comput. Syst. 2016, 55, 321–335. [Google Scholar] [CrossRef]
- Namitha, S.; Gopalan, S.; Sanjay, H.N.; Chandrashekaran, K. Risk Based Access Control In Cloud Computing. In Proceedings of the International Conference on Green Computing and Internet of Things (ICGCloT), Delhi, India, 8–10 October 2015; pp. 1502–1505. [Google Scholar]
- McGraw, R. Risk-Adaptable Access Control (RAdAC); National Security Agency: Fort Meade, MD, USA, 2009.
- Molloy, I.; Dickens, L.; Morisset, C.; Cheng, P.; Lobo, J.; Russo, A. IBM Research Report Risk-Based Access Control Decisions under Uncertainty; IBM: Armonk, NY, USA, 2011; Volume 25121. [Google Scholar]
- Ni, Q.; Bertino, E.; Lobo, J. Risk-based access control systems built on fuzzy inferences. In Proceedings of the 5th ACM Symposium on Information, Computer and Communications Security, Beijing, China, 13 April 2010; pp. 250–260. [Google Scholar]
- Abie, H.; Balasingham, I. Risk-Based Adaptive Security for Smart IoT in eHealth. In Proceedings of the 7th International Conference on Body Area Networks, Oslo, Norway, 24–26 September 2012; pp. 269–275. [Google Scholar]
- Shaikh, R.A.; Adi, K.; Logrippo, L.; Mankovski, S. Risk-based decision method for access control systems. In Proceedings of the PST 2011: 9th International Conference on Privacy, Security and Trust, Montreal, QC, Canada, 19–21 July 2011; pp. 189–192. [Google Scholar]
- Ricardo dos Santos, D.; Westphall, C.M.; Westphall, C.B. Risk-based Dynamic Access Control for a Highly Scalable Cloud Federation. In Proceedings of the Seventh International Conference on Emerging Security Information, Systems and Technologies (SECUREWARE 2013), Barcelona, Spain, 25–31 August 2013; pp. 8–13. [Google Scholar]
- Molloy, I.; Dickens, L.; Lobo, J.; Morisset, C.; Russo, A. Risk-Based Security Decisions Under Uncertainty Categories and Subject Descriptors. Data Appl. Secur. Priv. 2012, 157–168. [Google Scholar] [CrossRef]
- Rajbhandari, L.; Snekkenes, E.A. Using game theory to analyze risk to privacy: An initial insight. In Privacy and Identity Management for Life; Springer: Berlin/Heidelberg, Germany, 2011; pp. 41–51. [Google Scholar]
- Sharma, M.; Bai, Y.; Chung, S.; Dai, L. Using risk in access control for cloud-assisted ehealth. In Proceedings of the 2012 IEEE 14th International Conference on High Performance Computing and Communication & 2012 IEEE 9th International Conference on Embedded Software and Systems, Liverpool, UK, 25–27 June 2012; pp. 1047–1052. [Google Scholar]
- Atlam, H.F.; Alenezi, A.; Walters, R.J.; Wills, G.B.; Daniel, J. Developing an adaptive Risk-based access control model for the Internet of Things. In Proceedings of the 2017 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Exeter, UK, 21–23 June 2017; pp. 655–661. [Google Scholar]
- Atlam, H.F.; Alenezi, A.; Hussein, R.K.; Wills, G.B. Validation of an Adaptive Risk-based Access Control Model for the Internet of Things. Int. J. Comput. Netw. Inf. Secur. 2018, 10, 26–35. [Google Scholar] [CrossRef]
- Atlam, H.F.; Alenezi, A.; Walters, R.J.; Wills, G.B. An overview of risk estimation techniques in risk-based access control for the internet of things. In Proceedings of the 2nd International Conference on Internet of Things, Big Data and Security, Porto, Portugal, 24–26 April 2017. [Google Scholar]
- Molloy, I.; Cheng, P.C.; Rohatgi, P. Trading in risk: Using markets to improve access control. In Proceedings of the New Security Paradigms Workshop, Oxford, UK, 8–11 September 2009; pp. 107–125. [Google Scholar]
- Babu, B.M.; Bhanu, M.S. Prevention of Insider Attacks by Integrating Behavior Analysis with Risk based Access Control Model to Protect Cloud. Procedia Comput. Sci. 2015, 54, 157–166. [Google Scholar] [CrossRef]
- Clark, J.A.; Tapiador, J.E.; McDermid, J.; Cheng, P.-C.; Agrawal, D.; Ivanic, N.; Slogget, D. Risk based access control with uncertain and time-dependent sensitivity. In Proceedings of the 2010 International Conference on Security and Cryptography (SECRYPT), Athens, Greece, 26–28 July 2010. [Google Scholar]
- Helil, N.; Kim, M.; Han, S. Trust and risk based access control and access control constraints. KSII Trans. Internet Inf. Syst. 2011, 5, 2254–2271. [Google Scholar] [CrossRef]
- Badar, N.; Vaidya, J.; Atluri, V.; Shafiq, B. Risk based access control using classification. In Automated Security Management; Springer International Publishing: Cham, Switzerland, 2013; pp. 79–95. [Google Scholar]
- Metoui, N.; Bezzi, M.; Armando, A. Trust and risk-based access control for privacy preserving threat detection systems. In Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer Science+Business Media: Berlin, Germany, 2016; Volume 10018 LNCS, pp. 285–304. [Google Scholar]
- Chun, S.A.; Atluri, V. Risk-Based Access Control for Personal Data Services. In Algorithms, Architectures and Information Systems Security; World Scientific: Sinagapore, 2008; pp. 263–283. [Google Scholar]
- Rahmati, A.; Fernandes, E.; Eykholt, K.; Prakash, A. Tyche: A risk-based permission model for smart homes. In Proceedings of the 2018 IEEE Cybersecurity Development Conference, SecDev 2018, Cambridge, MA, USA, 30 September–2 October 2018; pp. 29–36. [Google Scholar]
- Metoui, N.; Bezzi, M.; Armando, A. Risk-based privacy-aware access control for threat detection systems. In Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer Science+Business Media: Berlin, Germany, 2017; Volume 10720 LNCS, pp. 1–30. [Google Scholar]
- Burnett, C.; Chen, L.; Edwards, P.; Norman, T.J. TRAAC: Trust and risk aware access control. In Proceedings of the 2014 Twelfth Annual International Conference on Privacy, Security and Trust, Toronto, ON, Canada, 23–24 July 2014; pp. 371–378. [Google Scholar]
- Dankar, F.K.; Badji, R. A risk-based framework for biomedical data sharing. J. Biomed. Inform. 2017, 66, 231–240. [Google Scholar] [CrossRef]
- Abomhara, M.; Koien, G.; Oleschchuk, V.; Hamid, M. Towards Risk-aware Access Control Framework for Healthcare Information Sharing. In Proceedings of the 4th International Conference on Information Systems Security and Privacy, Funchal, Madeira, Portugal, 22–24 January 2018; pp. 312–321. [Google Scholar]
- Armando, A.; Bezzi, M.; Di Cerbo, F.; Metoui, N. Balancing trust and risk in access control. In Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer Science+Business Media: Berlin, Germany, 2015; Volume 9415, pp. 660–676. [Google Scholar]
- Chen, L.; Crampton, J. Risk-aware role-based access control. In Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer Science+Business Media: Berlin, Germany, 2012; Volume 7170 LNCS, pp. 140–156. [Google Scholar]
- Atlam, H.F.; Walters, R.J.; Wills, G.B.; Daniel, J. Fuzzy Logic with Expert Judgment to Implement an Adaptive Risk-Based Access Control Model for IoT. Mob. Netw. Appl. 2019, 1–13. [Google Scholar] [CrossRef]
- Luo, J.; Ni, X.; Yong, J. A trust degree based access control in grid environments. Inf. Sci. N. Y. 2009, 179, 2618–2628. [Google Scholar] [CrossRef]
- Habib, K.; Leister, W. Context-Aware Authentication for the Internet of Things. In Proceedings of the Eleventh International Conference on Autonomic and Autonomous Systems Fined, Rome, Italy, 24–29 May 2015; pp. 134–139. [Google Scholar]
| Item | Traditional Access Control | Dynamic Access Control |
|---|---|---|
| Features | It uses predetermined and static policies to determine the access decision. | It uses access policies and contextual features that are collected at the time of making the access request to determine the access decision. |
| Grant Decision | The access is granted only if it matches one of the rules in the access policy. | The access is granted based on the context and the policy. The decision can be overridden based on the context. |
| Deny Decision | The access is denied only if it does not match any rule in the access policy. | The access is denied based on the context and the policy. The change in the context can lead to changing the decision immediately. |
| Example | ACL, DAC, MAC, and RBAC are the common and popular approaches or examples of traditional access control. | Risk-based access control, trust-based access control, and combination of risk with trust are common examples of dynamic access control. |
| Advantages |
|
|
| Weaknesses |
|
|
| Applications | The applications that do not have access to real-time features/attributes such as the operating system. | Various dynamic and distributed systems need dynamic access control to provide more flexibility including IoT and cloud applications, etc. |
| Database | Phase 1 | Phase 2 | Phase 3 |
|---|---|---|---|
| IEEE Xplore | 16 | 9 | 4 |
| PubMed | 52 | 10 | 5 |
| Google Scholar | 886 | 37 | 28 |
| SpringerLink | 48 | 7 | 2 |
| Elsevier ScienceDirect | 22 | 8 | 3 |
| ACM Digital Library | 20 | 5 | 2 |
| Total | 1044 | 76 | 44 |
| Publication ID | Citation | Publication Type | Year of Publication |
|---|---|---|---|
| 1 | Ricardo et al. [22] | Journal | 2016 |
| 2 | Chen et al. [4] | Conference | 2007 |
| 3 | Diep et al. [20] | Conference | 2007 |
| 4 | Dos Santos et al. [1] | Conference | 2014 |
| 5 | Choi et al. [23] | Journal | 2015 |
| 6 | Khambhammettu et al. [6] | Journal | 2013 |
| 7 | Li et al. [24] | Conference | 2013 |
| 8 | Arias-Cabarcos et al. [25] | Journal | 2012 |
| 9 | Baracaldo and Joshi [26] | Journal | 2013 |
| 10 | Kandala et al. [27] | Conference | 2011 |
| 11 | Lee et al. [28] | Journal | 2007 |
| 12 | Atlam and Wills [29] | Journal | 2019 |
| 13 | Diaz-Lopez et al. [30] | Journal | 2016 |
| 14 | Shaikh et al. [5] | Journal | 2012 |
| 15 | Wang and Jin [15] | Conference | 2011 |
| 16 | Namitha et al. [31] | Conference | 2015 |
| 17 | McGraw et al. [32] | Journal | 2009 |
| 18 | Molloy et al. [33] | Conference | 2011 |
| 19 | Ni et al. [34] | Conference | 2010 |
| 20 | Abie and Balasingham [35] | Conference | 2012 |
| 21 | Shaikh et al. [36] | Conference | 2011 |
| 22 | Dos Santos et al. [37] | Conference | 2013 |
| 23 | Molloy et al. [38] | Conference | 2012 |
| 24 | Rajbhandari and Snekkenes [39] | Book Chapter | 2011 |
| 25 | Sharma et al. [40] | Conference | 2012 |
| 26 | Atlam et al. [41] | Conference | 2017 |
| 27 | Atlam et al. [42] | Journal | 2018 |
| 28 | Atlam et al. [43] | Conference | 2017 |
| 29 | Molloy et al. [44] | Conference | 2009 |
| 30 | Babu and Bhanu [45] | Conference | 2015 |
| 31 | Clark et al. [46] | Conference | 2010 |
| 32 | Helil et al. [47] | Journal | 2011 |
| 33 | Badar et al. [48] | Book Chapter | 2013 |
| 34 | Bijon et al. [13] | Conference | 2013 |
| 35 | Metoui et al. [49] | Conference | 2016 |
| 36 | Atlam et al. [9] | Conference | 2018 |
| 37 | Chun and Atluri [50] | Book Chapter | 2008 |
| 38 | Rahmati et al. [51] | Conference | 2018 |
| 39 | Metoui et al. [52] | Journal | 2017 |
| 40 | Burnett et al. [53] | Conference | 2014 |
| 41 | Dankar et al. [54] | Journal | 2017 |
| 42 | Abomhara et al. [55] | Journal | 2015 |
| 43 | Armando et al. [56] | Conference | 2015 |
| 44 | Chen and Crampton [57] | Conference | 2012 |
| Citation | Summary of the Contributions of Each Publication |
|---|---|
| Chen et al. [4] | This paper presented a risk-based model that is based on the Multi-Level Security (MLS) approach. The paper utilized the risk value resulted from the difference between object and subject security level as a risk factor. Then, the fuzzy logic system was applied to represent the risk as a binary value, where 0 allows the access and 1 denies the access. |
| Diep et al. [20] | This paper presented the main elements needed to build a dynamic and flexible risk-based access control model by collecting environmental information, assess it, and make the access decision using a risk assessment. |
| Ni et al. [34] | This paper used the same elements of the risk-based model proposed by Diep et al. [20] but with the use of the fuzzy logic system to estimates the risk value associated with the access request. They indicated that the fuzzy logic system is an efficient method for evaluating the security risks of access control operations. The major difference between both publications was the risk estimation technique adopted to assess the security risk of each access request. |
| Lee et al. [28] | This paper provided a risk-based model by utilizing the risk assessment. The authors collected environmental and contextual information and assessed it based on outcomes of actions in term of CIA (Confidentiality, Integrity, and Availability). In addition, the MultiFactor Evaluation Process (MFEP) technique was utilized with the risk assessment to estimate the security risk value related to each access request to decide the access decision. |
| Chun and Atluri [50] | This paper proposed a risk-based model that employs the concept of “access first and verify later”; hence, the required information/data can be accessed immediately without delaying access. The paper also utilized semantics to build situation role hierarchies, which are used to assess the security risk to provide access decisions. |
| McGraw et al. [32] | This paper proposed a Risk-Adaptable Access Control (RAdAC) model, which is based on estimating the security risk and operational needs to grant or deny access. This model was implemented to first estimate the risk associated with the access request then compares the estimated risk with the access control policy. After that, the system verifies the operational needs, if the associated operational needs and the policy are met; then, the access is granted. |
| Kandala et al. [27] | This paper utilized the Risk-Adaptable Access Control (RAdAC) model developed by McGraw et al. [32] to identify different risk components with the operational needs using the Attribute-Based Access Control (ABAC) model. This paper integrated the ABAC model with the risk-based model to use other user attributes as risk factors. |
| Molloy et al. [44] | This paper reviewed open problems in risk-based access control systems and proposed using market approaches to identify the risk allocation and tolerance for each organization. The paper utilized the simulation to show the advantages of risk-based access control that promote security and information sharing. |
| Clark et al. [46] | This paper presented a risk-based access control model and how it can overcome issues with uncertainty and time-varying security specifications. The paper utilized resource sensitivity as a probability distribution, security labels, and clearance level to estimate the risk using the fuzzy logic system in various real-world situations. |
| Helil et al. [47] | This paper introduced a trust and risk-based access control model by combining trust and risk as risk factors to enhance data protection and information accessibility. Each user’s trustworthiness and their related risk values were employed to decide the access decision. |
| Molloy et al. [33] | This paper presented a new learning and risk-based architecture for distributed policy enforcement under uncertainty. The paper utilized learned classifiers of access control decisions to improve the accuracy of the access decision. |
| Rajbhandari and Snekkenes [39] | This paper introduced a risk-based model that utilizes user’s benefits rather than subjective probability as a risk factor to decide the access decision. The authors demonstrated that game theory can be used as a risk estimation approach to assess security risks. |
| Shaikh et al. [36] and Shaikh et al. [5] | The paper [36] proposed a dynamic risk-based decision method. This method used the user past behavior with the risk history to estimates the security risk value associated with each access request. Besides, it gave reward and penalty points for subjects/users after completing a transaction based on the estimated risk value associated with the transaction. The work presented in [36] was extended in [5] to involve the process of implementing the risk estimation process to identify good and bad users based on their past behavior. |
| Wang and Jin [15] | This paper proposed a quantified risk-based model. The risk value is estimated based on the purpose of access to different data sensitivity levels. The risk estimation process was performed by employing the concept of Shannon entropy from information theory. A prototype using medical history records was utilized to illustrate the efficiency of their suggested model. |
| Abie and Balasingham [35] | This paper implemented the concept of security risks to identify access decisions by proposing a risk-based adaptive security framework that employs the game theory as the risk estimation method to asses risk loses and their future benefits by collecting contextual information in the healthcare environment. |
| Arias-Cabarcos et al. [25] | This paper utilized the risk-based access control model in the federated identity management process in cloud computing. It utilized the security risk to provide the access decision and diminish weaknesses and risks when access decisions about collaboration are made. The paper also proposed a hierarchical risk aggregation system for cloud federation. |
| Chen and Crampton [57] | This paper incorporated the security risk with RBAC to build a risk-aware role-based access control model. In addition, the paper discussed the issues in the proposed risk-aware model and its implementation procedures. |
| Molloy et al. [38] | This paper utilized the risk-based access control model to make access decisions by utilizing the benefits of access as a risk factor. The paper also proposed an improved model that uses learned classifiers to provide efficient and accurate access decisions. |
| Sharma et al. [40] | This paper presented a task-based access control model that estimates the risk value based on the action to be performed by the requester. The risk estimation process evaluates the risk using outcomes of actions to make the access decision. |
| Baracaldo and Joshi [26] | This paper proposed a framework that extends the RBAC model to incorporate trust with risk to provide the access decision. The authors argued that their framework can be adjusted to different changes in users’ behavior by using a threshold value that is defined using a risk assessment process. |
| Badar et al. [48] | This paper proposed utilizing classification to assess the risk value related to each access request. The paper presented two approaches; the first approach presented an access control matrix to evaluate the risk of granting access depending on user-permission assignments. The second approach specified the best contextual role that provides the lowest risk and allows maximum accessibility by integrating security risk with RBAC. |
| Bijon et al. [13] | This paper proposed a framework that combines the RBAC with the security risk to specify access decisions. The paper introduced the concept of RBAC-based risk-awareness and also provided a formal description of an adaptive risk-aware RBAC model. |
| Dos Santos et al. [37] | This paper presented a dynamic risk-based model to achieve a highly scalable system in a cloud federation. In addition, the paper introduced a prototype implementation for the proposed model to show the effectiveness of their suggested model. |
| Khambhammettu et al. [6] | This paper presented a framework depending on subject trustworthiness, object sensitivity, and the difference between them using a risk assessment. However, this framework requires a system administrator with broad experience to provide a sensible metric for each input before conducting the risk assessment process. |
| Li et al. [24] | This paper utilized the fuzzy logic system to estimate the risk associated with access to healthcare information. Three risk factors involving action severity, data sensitivity, and risk history were utilized. In addition, a fuzzy risk metric is assigned to each risk factor to decide whether granting or denying access. |
| Burnett et al. [53] | This paper proposed a trust and risk-aware access control model that provides policy coverage and dynamic access decisions. The paper defined a zone policy model that allows the data owner to have total control over his/her own data. Trust is used to define the verification of whether the requester respected the obligations that are assigned to him/her or not. The paper also utilized a probabilistic computational trust model, called subjective logic, to formulate their trust assessment. The risk estimation was done using a classic method of defining expected loss in term of unwanted disclosure. |
| Babu and Bhanu [45] | This paper proposed building a trust and risk-based access control model to provide access decisions in cloud computing. The paper introduced a privilege management procedure that combines the security risk with trust to create an efficient and scalable access control system. |
| Choi et al. [23] | This paper presented a framework for a context-sensitive risk-based model for medical information systems. This framework categorized information to calculate the risk value and apply the risk through treatment-based permission profiling and specifications. This framework provided the access decision based on the severity of the context and treatment. |
| Namitha et al. [31] | This paper implemented a risk-based access control model based on user features including years of experience, designation, defect level, location index, time index, and probationary period and estimate the risk value using a mathematical function. |
| Armando et al. [56] | This paper proposed a framework that integrates the risk with trust to provide access decisions. The access decision is determined by comparing the risk value with the trust, in which the access is granted if the trust value is higher than the risk value. The paper also presented mitigation strategies to increase the trust level and reduce the risk. |
| Diaz-Lopez et al. [30] | This paper presented a risk-based access control model that adopted dynamic countermeasures to adjust to various changes in the risk value of system resources. The paper utilized genetic algorithms to build the most suitable set of countermeasures for a specific situation. |
| Dos Santos et al. [1] and Dos Santos et al. [22] | The paper [1] proposed a risk-based access control model that uses the idea of quantifying risk and aggregating them to decide access decisions. The risk value is mainly evaluated based on predetermined risk policies that are created either by the system security administrator or the resource owner. Further, a prototype of this model is created using risk metrics provided in the work of Sharma et al. [40]. This work was extended in [22] to develop an ontology-based method to estimate the risk value depending on the context and adjusting values of risk metrics and using predetermined access policies to make the access decision. |
| Metoui et al. [49] and Metoui et al. [52] | The paper [49] proposed a risk-aware framework that combines the privacy risk with the user trust to identify threats related to each access request. The access decision is determined by comparing the privacy-risk with the user trust in which if the user trust is higher than the privacy risk, the access will be granted. Otherwise, access will be denied. This work was extended in [52] to implement the risk estimation process based on privacy risk and user trust. In addition, several access scenarios were presented to show the effectiveness of their proposed risk estimation approach. The paper [52] also introduced adaptive adjustment strategies to increase the trust level and reduce privacy risk. |
| Atlam et al. [41], Atlam et al. [42] and Atlam and Wills [29] | The paper proposed [41] a dynamic and adaptive risk-based access control model by using user context, resource sensitivity, action severity, and risk history to compute the security risk value related to each access request. The paper also proposed using a smart contract to track user behavior during access sessions to detect and prevent malicious actions. This work was extended in [42] to show the validation of the proposed risk-based model using 20 security experts. In addition, the paper [42] discussed some of the risk estimation techniques and proposed the fuzzy logic system as the most appropriate approach for the IoT context where there are no available datasets. This work was extended in [29] to propose the fuzzy logic system with expert judgement as the risk estimation method to implement their proposed risk-based model. The paper showed a detailed description of using the fuzzy logic system to estimate the security risk value associated with each access request, showing the access control scenarios of the network router. |
| Atlam et al. [9] | The paper introduced eXtensible Access Control Markup Language (XACML) as the suitable language for implementing access control policies for the IoT system. In addition, the paper adopted XACML to build the access policies for the risk-based access control model. |
| Atlam et al. [43] | This paper provided an overview of risk estimation techniques in risk-based access control for the IoT. The paper discussed the benefits and drawbacks of various quantitative risk estimation techniques that are required to implement a risk-based access control model. |
| Dankar et al. [54] | This paper proposed a conceptual risk-aware model, which utilizes real-time and contextual information in the surrounding environment to make the access decision. The paper also implemented some mitigation measures to enforce the access decision in case of having a high-risk value in the access request. |
| Rahmati et al. [51] | This paper introduced a risk-based access control model to build a system called Tyche, which is a system that controls the risk in physical devices. Tyche presents the concept of risk-based access decisions in which it classifies various applications into several risk groups. Then, each risk group has a set of permissions based on the risk value. |
| Citation | Benefits of User | Action Severity | Resource Sensitivity | Outcomes of ACTIONS | Context | Trust | Risk History | Access Policies | Role |
|---|---|---|---|---|---|---|---|---|---|
| Ricardo et al. [22] | - | ✓ | ✓ | - | - | - | - | - | - |
| Chen et al. [4] | ✓ | - | - | - | - | - | - | - | - |
| Diep et al. [20] | ✓ | ||||||||
| Dos Santos et al. [1] | - | - | - | - | - | - | ✓ | - | - |
| Choi et al. [23] | - | - | - | - | ✓ | - | - | - | - |
| Khambhammettu et al. [6] | - | - | ✓ | - | - | ✓ | - | - | - |
| Li et al. [24] | - | ✓ | ✓ | - | - | - | ✓ | - | - |
| Baracaldo and Joshi [26] | - | - | - | - | - | ✓ | - | - | ✓ |
| Kandala et al. [27] | - | - | - | ✓ | ✓ | - | ✓ | ✓ | - |
| Lee et al. [28] | - | - | - | - | ✓ | - | - | - | - |
| Atlam and Wills [29] | - | ✓ | ✓ | - | ✓ | - | ✓ | - | - |
| Diaz-Lopez et al. [30] | - | - | - | - | - | - | ✓ | - | - |
| Shaikh et al. [5] | - | - | - | - | - | ✓ | ✓ | - | - |
| Wang & Jin [15] | - | - | - | ✓ | - | - | - | - | - |
| Namitha et al. [31] | - | - | - | - | ✓ | - | - | - | ✓ |
| McGraw et al. [32] | ✓ | - | - | ✓ | ✓ | - | - | ✓ | - |
| Molloy et al. [33] | - | - | - | ✓ | - | - | - | - | - |
| Ni et al. [34] | - | - | ✓ | - | - | - | - | - | - |
| Abie and Balasingham [35] | - | - | - | - | ✓ | - | - | - | - |
| Shaikh et al. [36] | - | - | ✓ | ✓ | - | ✓ | ✓ | - | ✓ |
| Dos Santos et al. [37] | - | - | - | - | - | - | - | ✓ | - |
| Molloy et al. [38] | - | - | - | ✓ | - | - | - | - | - |
| Rajbhandari and Snekkenes [39] | ✓ | - | - | - | - | - | - | - | - |
| Sharma et al. [40] | ✓ | ✓ | ✓ | - | - | - | - | - | - |
| Atlam et al. [41] | - | ✓ | ✓ | - | ✓ | - | ✓ | - | - |
| Atlam et al. [42] | - | ✓ | ✓ | - | ✓ | - | ✓ | - | - |
| Molloy et al. [44] | - | - | - | ✓ | - | - | ✓ | - | - |
| Babu and Bhanu [45] | - | - | - | - | - | ✓ | - | - | ✓ |
| Clark et al. [46] | - | - | - | ✓ | - | - | - | - | ✓ |
| Helil et al. [47] | - | - | - | - | - | ✓ | ✓ | - | - |
| Badar et al. [48] | - | - | - | - | - | - | - | - | ✓ |
| Bijon et al. [13] | ✓ | - | - | - | ✓ | - | ✓ | - | ✓ |
| Metoui et al. [49] | - | - | - | - | - | ✓ | ✓ | - | - |
| Atlam et al. [9] | - | ✓ | ✓ | - | ✓ | - | ✓ | - | - |
| Chun and Atluri [50] | - | - | - | - | ✓ | - | - | - | - |
| Metoui et al. [52] | - | - | - | - | - | ✓ | ✓ | - | - |
| Burnett et al. [53] | - | - | ✓ | ✓ | - | ✓ | - | - | - |
| Dankar et al. [54] | - | - | ✓ | - | ✓ | - | ✓ | - | - |
| Abomhara et al. [55] | - | ✓ | - | - | ✓ | - | ✓ | - | - |
| Armando et al. [56] | - | - | - | - | - | ✓ | ✓ | - | - |
| Chen and Crampton [57] | ✓ | - | - | - | - | ✓ | - | - | ✓ |
| Citation | Fuzzy Logic | Machine Learning | Game Theory | Risk Assessment | Mathematical Equation | Not Discussed |
|---|---|---|---|---|---|---|
| Chen et al. [4] | ✓ | - | - | - | - | - |
| Diep et al. [20] | - | - | - | ✓ | - | - |
| Lee et al. [28] | - | - | - | ✓ | - | - |
| Chun and Atluri [50] | - | - | - | - | - | ✓ |
| McGraw et al. [32] | - | - | - | - | - | ✓ |
| Molloy et al. [44] | - | - | - | - | ✓ | - |
| Clark et al. [46] | - | - | - | - | - | ✓ |
| Ni et al. [34] | ✓ | - | - | - | - | - |
| Helil et al. [47] | - | - | - | - | ✓ | - |
| Kandala et al. [27] | - | - | - | - | - | ✓ |
| Molloy et al. [33] | - | ✓ | - | - | - | - |
| Rajbhandari and Snekkenes [39] | - | - | ✓ | - | - | - |
| Shaikh et al. [36] | - | - | - | - | ✓ | - |
| Wang and Jin [15] | - | - | - | - | - | ✓ |
| Abie and Balasingham [35] | - | - | ✓ | - | - | - |
| Arias-Cabarcos et al. [25] | ✓ | - | - | - | - | - |
| Chen and Crampton [57] | - | - | - | - | - | ✓ |
| Molloy et al. [38] | - | ✓ | - | - | - | - |
| Shaikh et al. [5] | - | - | - | - | - | ✓ |
| Sharma et al. [40] | - | - | - | - | ✓ | - |
| Baracaldo and Joshi [26] | - | - | - | ✓ | - | - |
| Badar et al. [48] | - | - | - | - | - | ✓ |
| Bijon et al. [13] | - | - | - | - | ✓ | - |
| Dos Santos et al. [37] | - | - | - | - | - | ✓ |
| Khambhammettu et al. [6] | - | - | - | ✓ | - | - |
| Li et al. [24] | ✓ | - | - | - | - | - |
| Burnett et al. [53] | - | - | - | - | ✓ | - |
| Dos Santos et al. [1] | - | - | - | - | - | ✓ |
| Babu and Bhanu [45] | - | - | - | ✓ | - | - |
| Choi et al. [23] | - | - | - | ✓ | - | - |
| Namitha et al. [31] | - | - | - | - | ✓ | - |
| Armando et al. [56] | - | - | - | - | - | ✓ |
| Diaz-Lopez et al. [30] | - | - | - | - | - | ✓ |
| Dos Santos et al. [22] | - | - | - | - | - | ✓ |
| Metoui et al. [49] | - | - | - | - | - | ✓ |
| Atlam et al. [41] | - | - | - | - | - | ✓ |
| Atlam et al. [43] | ✓ | - | ✓ | ✓ | - | - |
| Dankar et al. [54] | - | - | - | - | ✓ | - |
| Metoui et al. [52] | - | - | - | - | - | ✓ |
| Atlam et al. [9] | - | - | - | - | - | ✓ |
| Atlam et al. [42] | ✓ | - | - | - | - | - |
| Rahmati et al. [51] | - | - | - | - | - | ✓ |
| Atlam and Wills [29] | ✓ | - | - | - | - | - |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Atlam, H.F.; Azad, M.A.; Alassafi, M.O.; Alshdadi, A.A.; Alenezi, A. Risk-Based Access Control Model: A Systematic Literature Review. Future Internet 2020, 12, 103. https://doi.org/10.3390/fi12060103
Atlam HF, Azad MA, Alassafi MO, Alshdadi AA, Alenezi A. Risk-Based Access Control Model: A Systematic Literature Review. Future Internet. 2020; 12(6):103. https://doi.org/10.3390/fi12060103
Chicago/Turabian StyleAtlam, Hany F., Muhammad Ajmal Azad, Madini O. Alassafi, Abdulrahman A. Alshdadi, and Ahmed Alenezi. 2020. "Risk-Based Access Control Model: A Systematic Literature Review" Future Internet 12, no. 6: 103. https://doi.org/10.3390/fi12060103
APA StyleAtlam, H. F., Azad, M. A., Alassafi, M. O., Alshdadi, A. A., & Alenezi, A. (2020). Risk-Based Access Control Model: A Systematic Literature Review. Future Internet, 12(6), 103. https://doi.org/10.3390/fi12060103








