A Robust Security Architecture for SDN-Based 5G Networks
Abstract
:1. Introduction
- In this paper, we propose a security architecture for SDN-based 5G networks. To the best of our knowledge, there is no other work in this field.
- We detail the security problems of SDN-based 5G network in the communication plane. We propose a low-cost security authentication scheme for these problems.
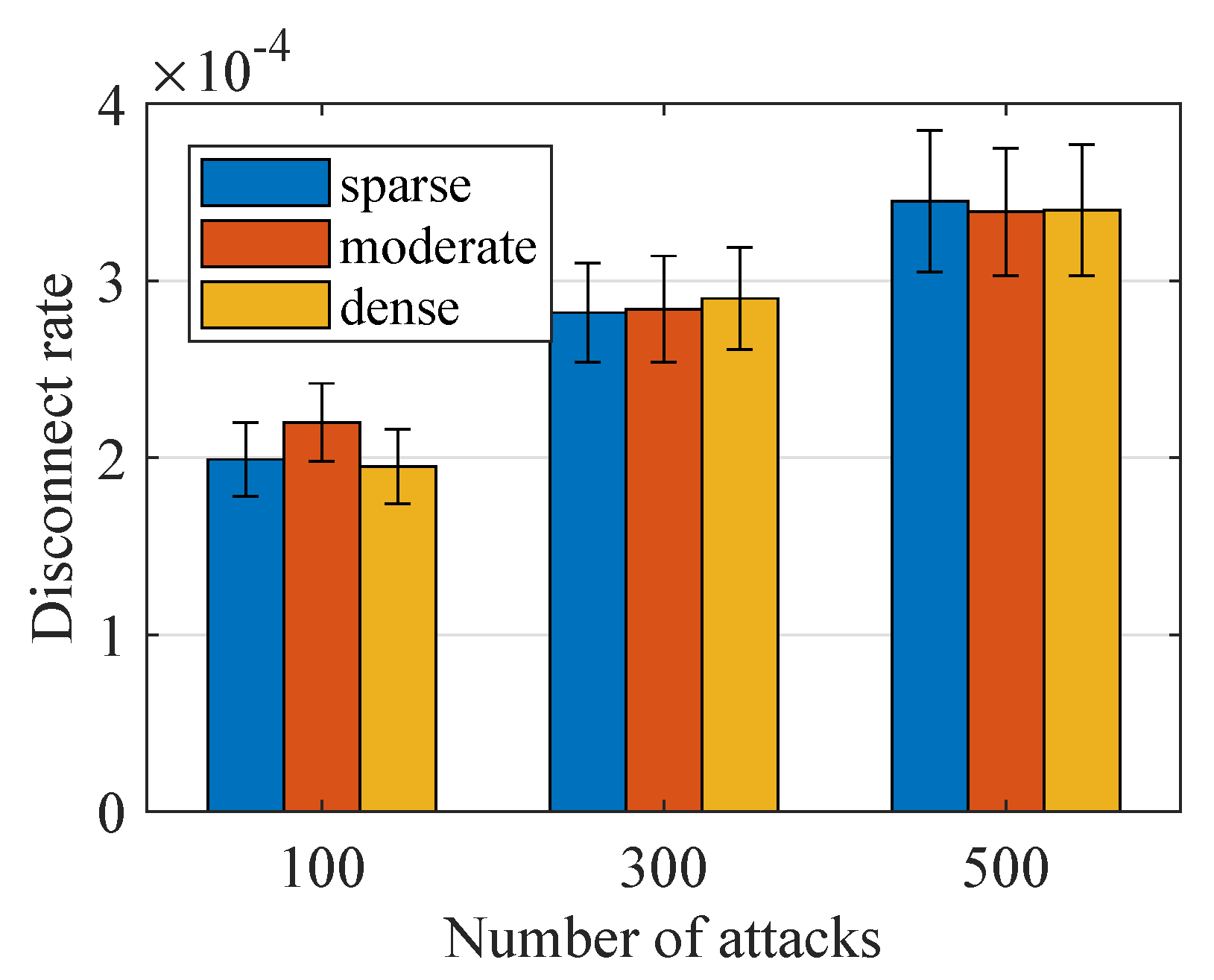
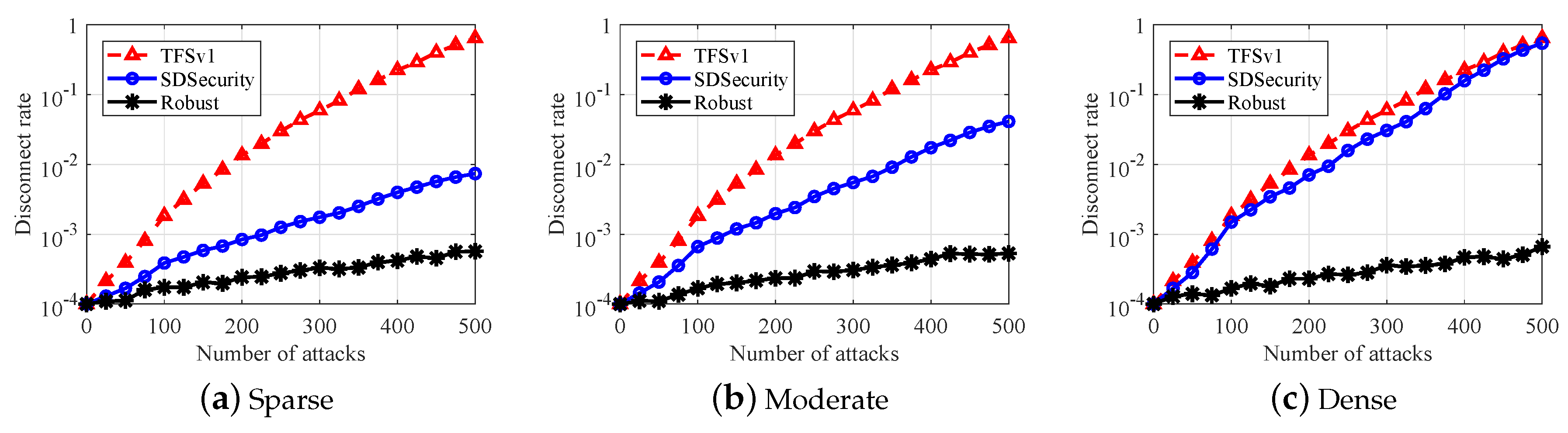
- We detail how our scheme raises the security of a current SDN based 5G network. In addition, we compare our work with the state of the art. The simulation results show that our work is robust while it has a low disconnect rate of 0.01%, whose rate is about 80% in the state of the art when the number of attacks is 50,000.
2. Background
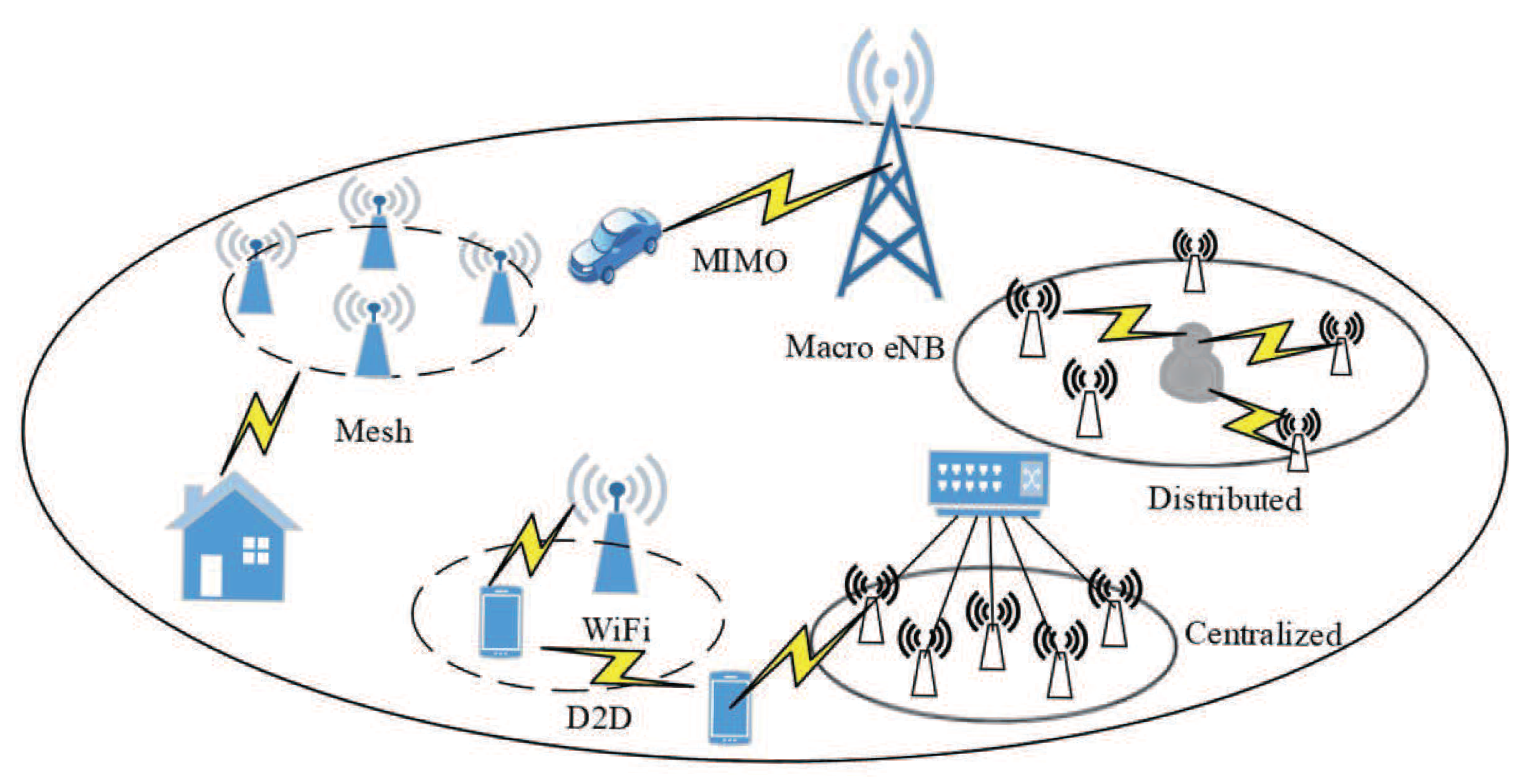
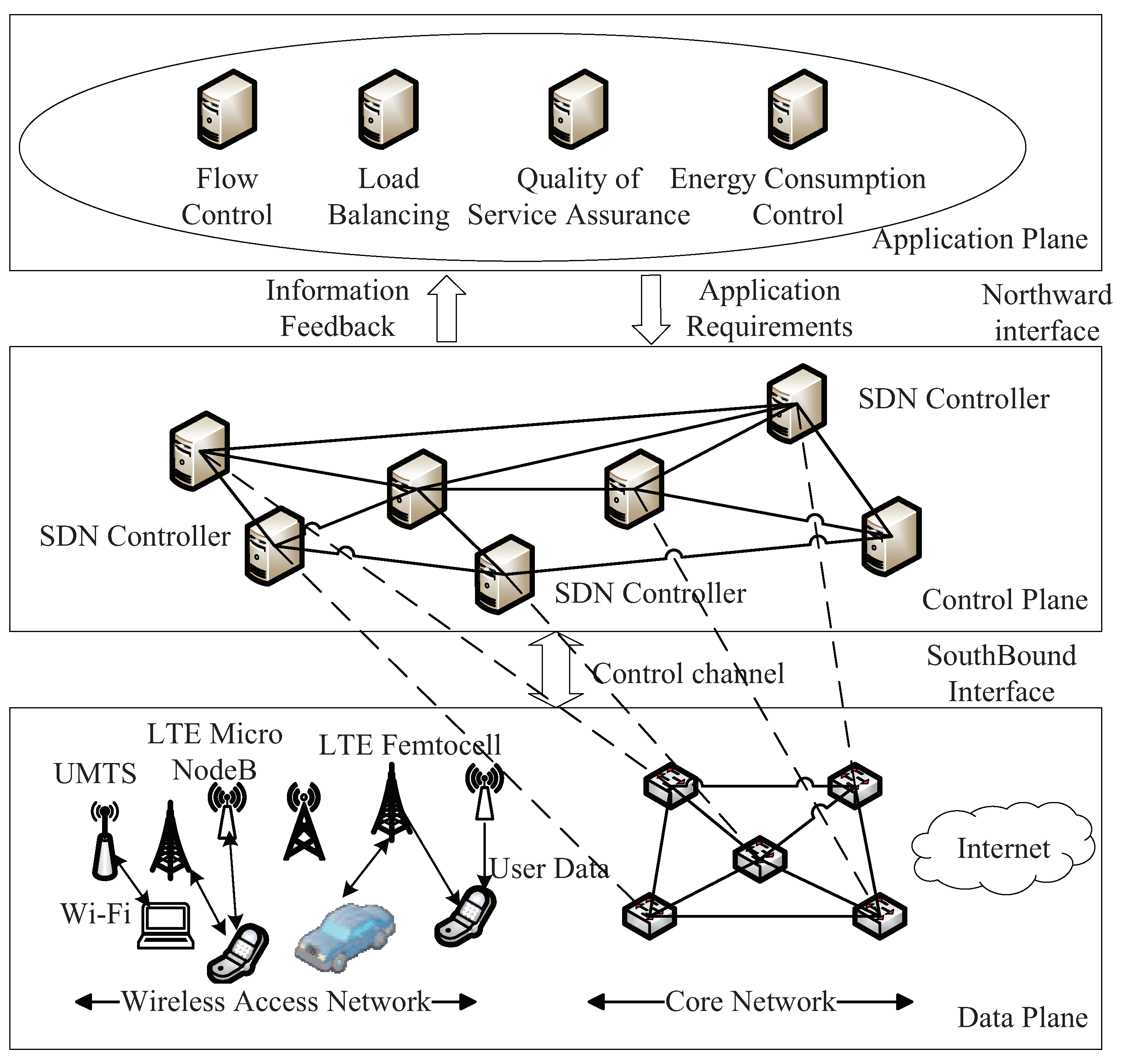
2.1. SDN Based 5G Network Architecture
2.2. Security Problems in SDN-Based 5G Networks
- The absence of trust and weak authentication between the applications and the controller, which may lead to a spoofing attack by spoofing northbound API messages.
- Inappropriate authorization may cause inappropriate or malicious access on the application.
- The absence of encryption of the traffic between the controller and switches leads to eavesdropping and spoofed southbound communications.
- The absence of trust and weak authentication at this level may lead to Man-In-The-Middle and spoofing attacks, which makes it easier for the attacker to eavesdrop on flows to see what flows are in use and what traffic is being permitted across the network.
- Inappropriate authorization that may cause unauthorized access. In fact, if a user requests a service that triggers the controller to create a route and cause packets to traverse that route, it must be ensured that the user is authorized to do so and that the environment can account for that activity.
- Southbound communication affected by attacks on flow rules mainly in In-band deployments
2.3. Related Work
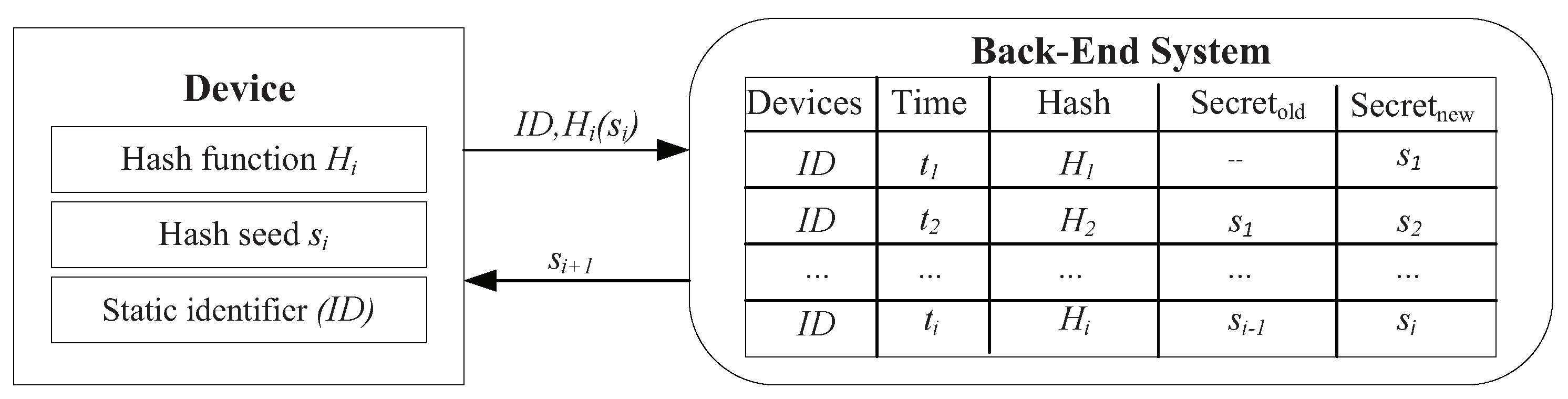
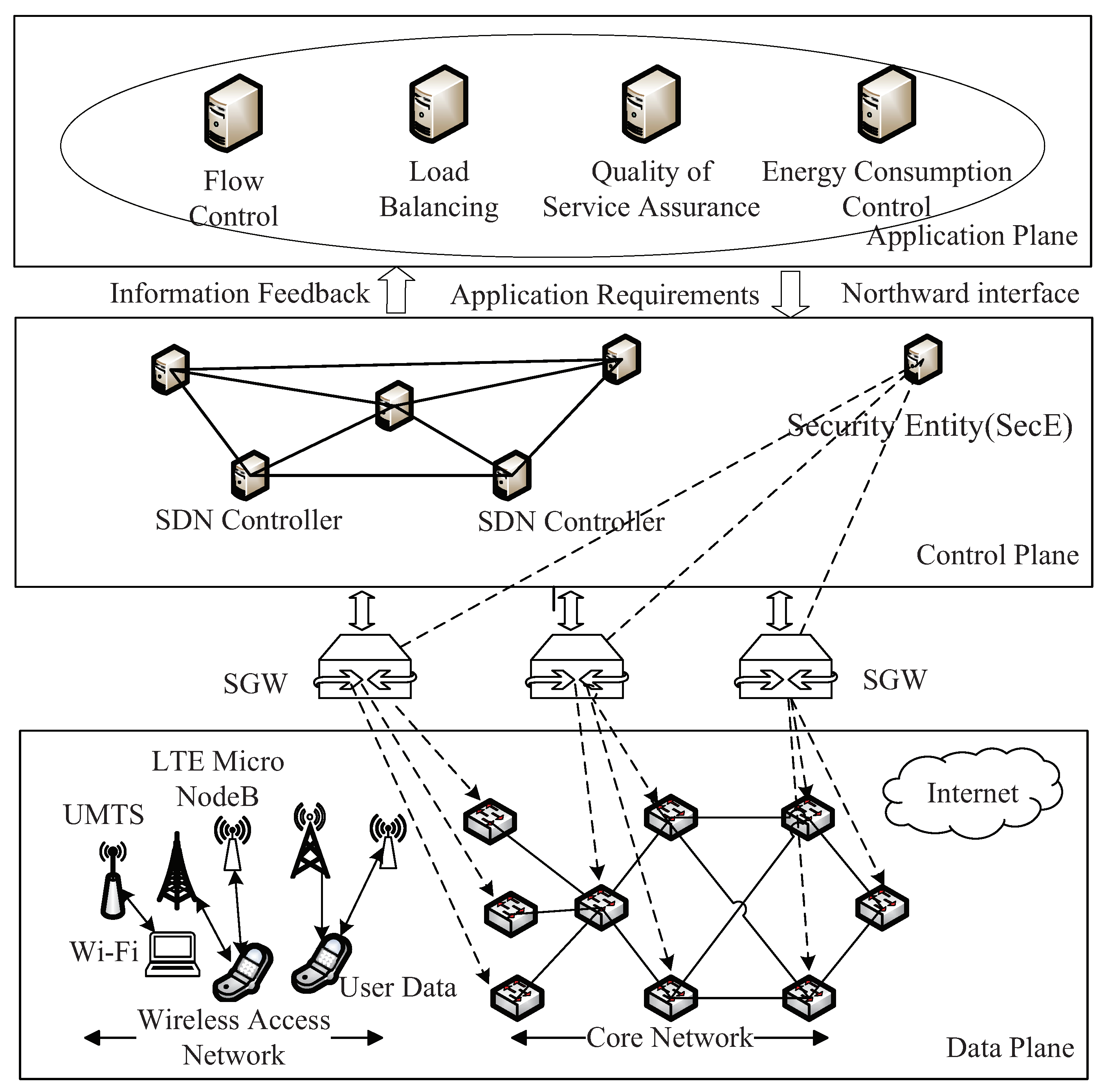
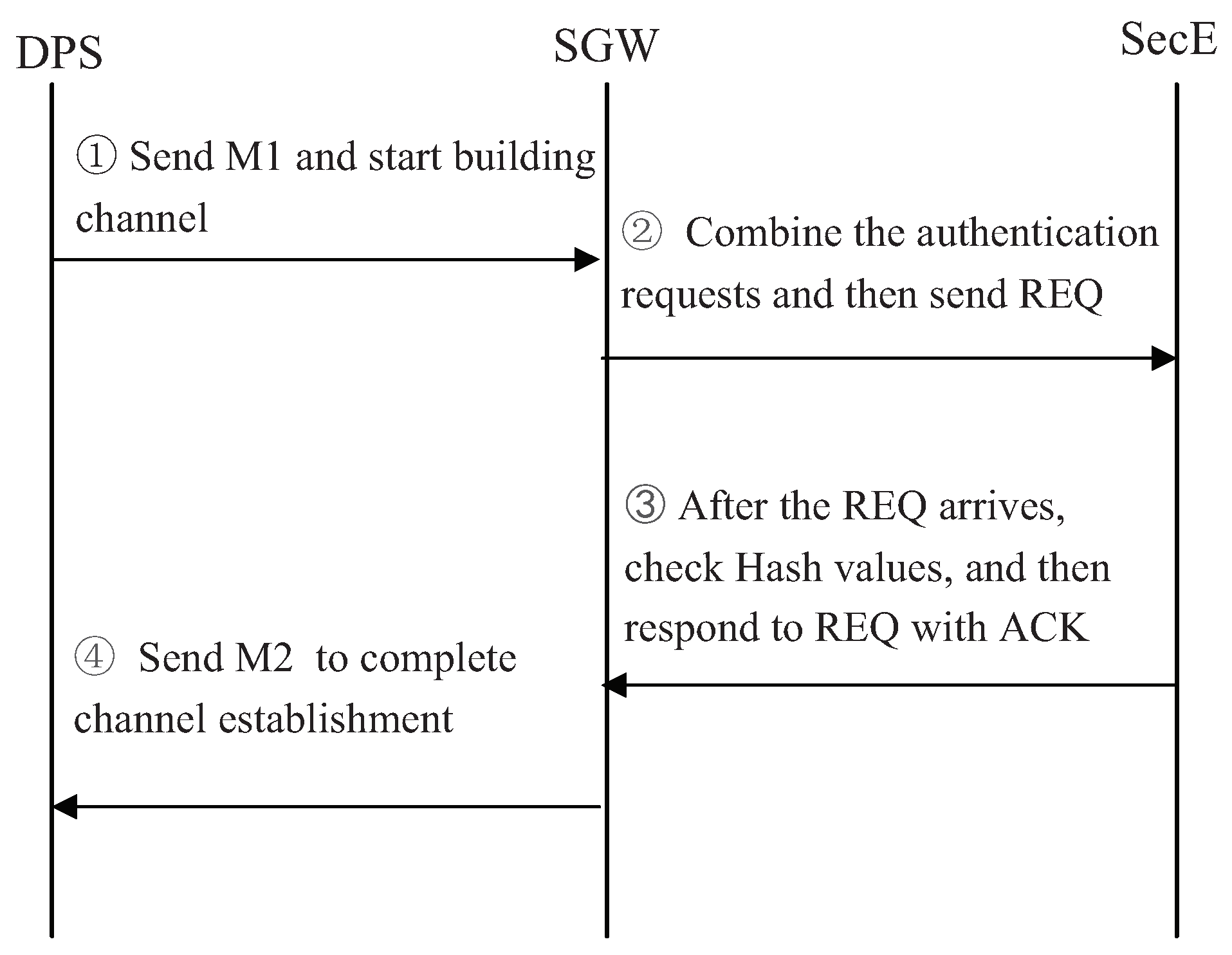
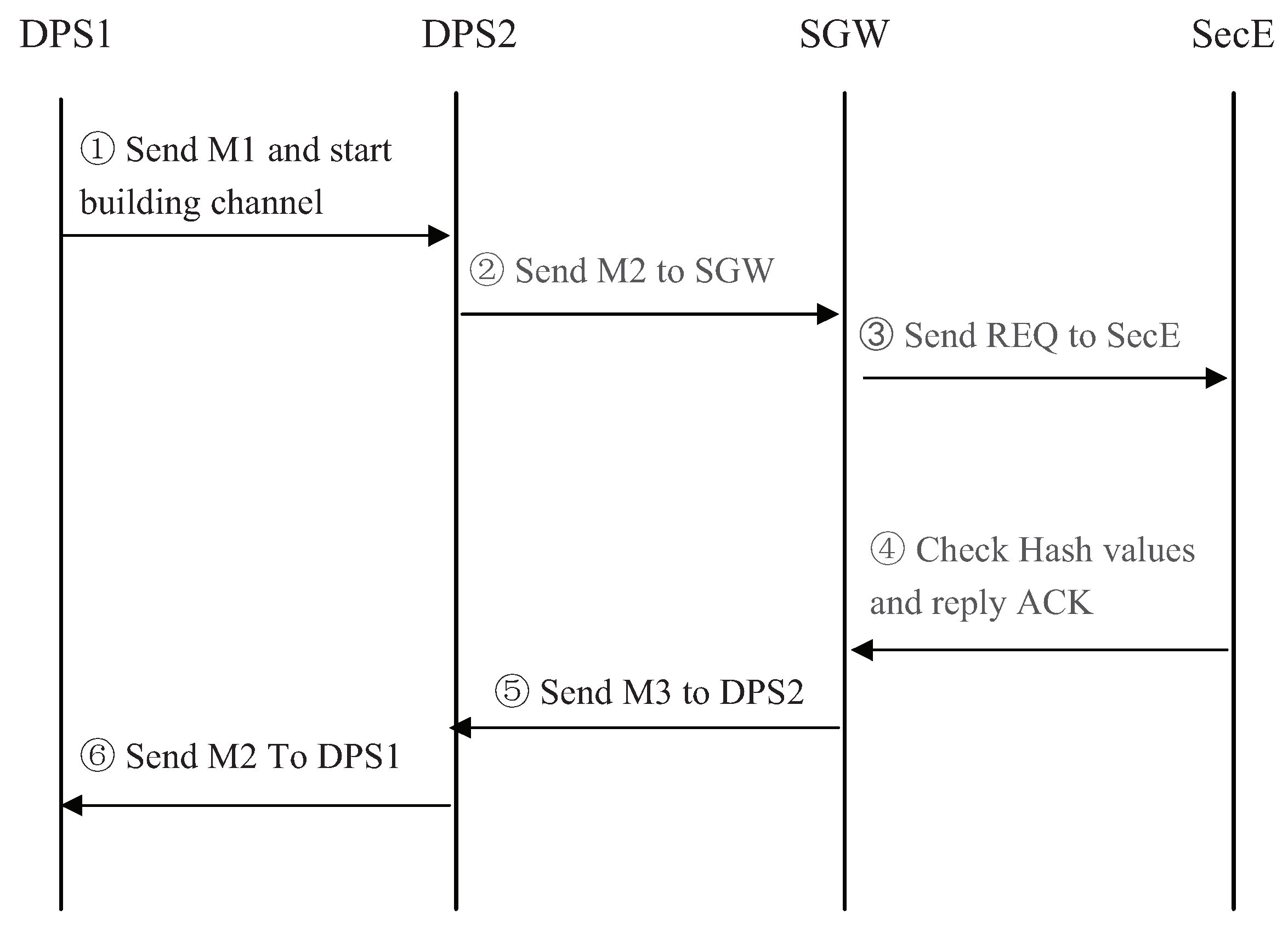
3. Robust Security Architecture of SDN-Based 5G Networks
3.1. Basic Idea
3.2. Security Architecture
4. Security Analysis
4.1. IP Spoofing
4.2. MITM Attack
4.3. Replay Attack
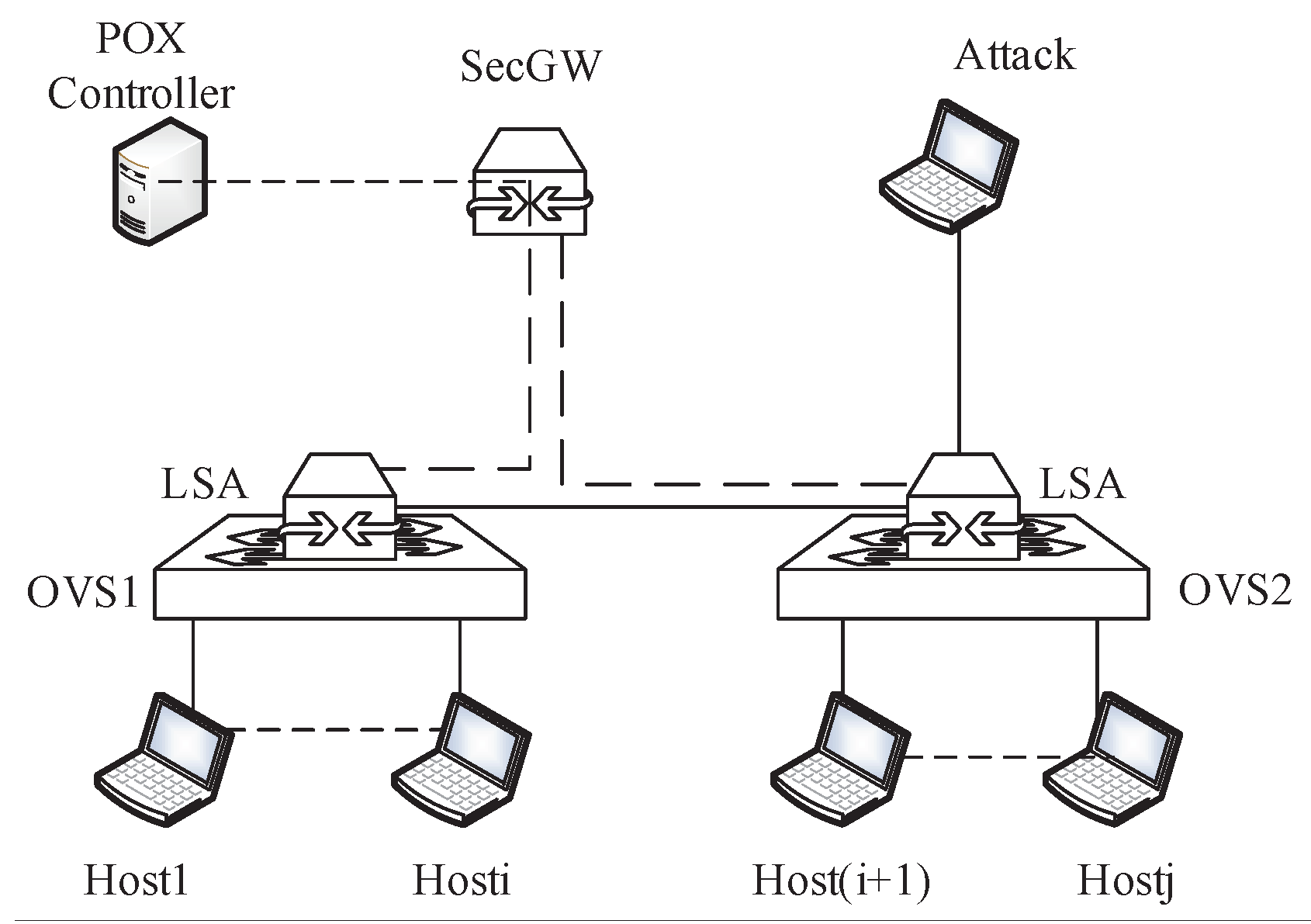
5. Performance Evaluation
5.1. Simulation Set up
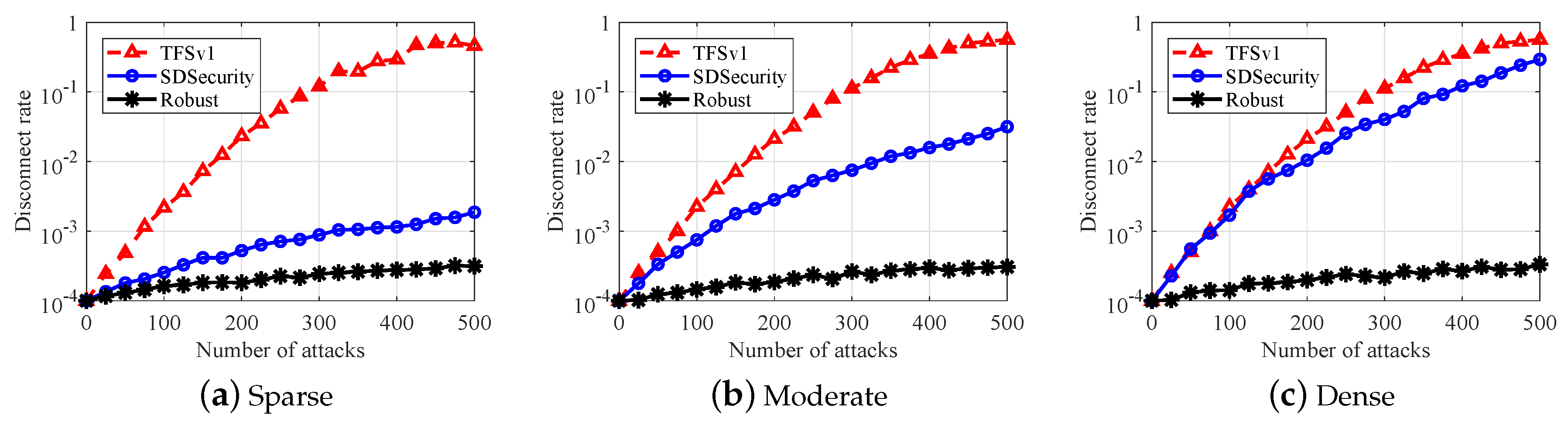
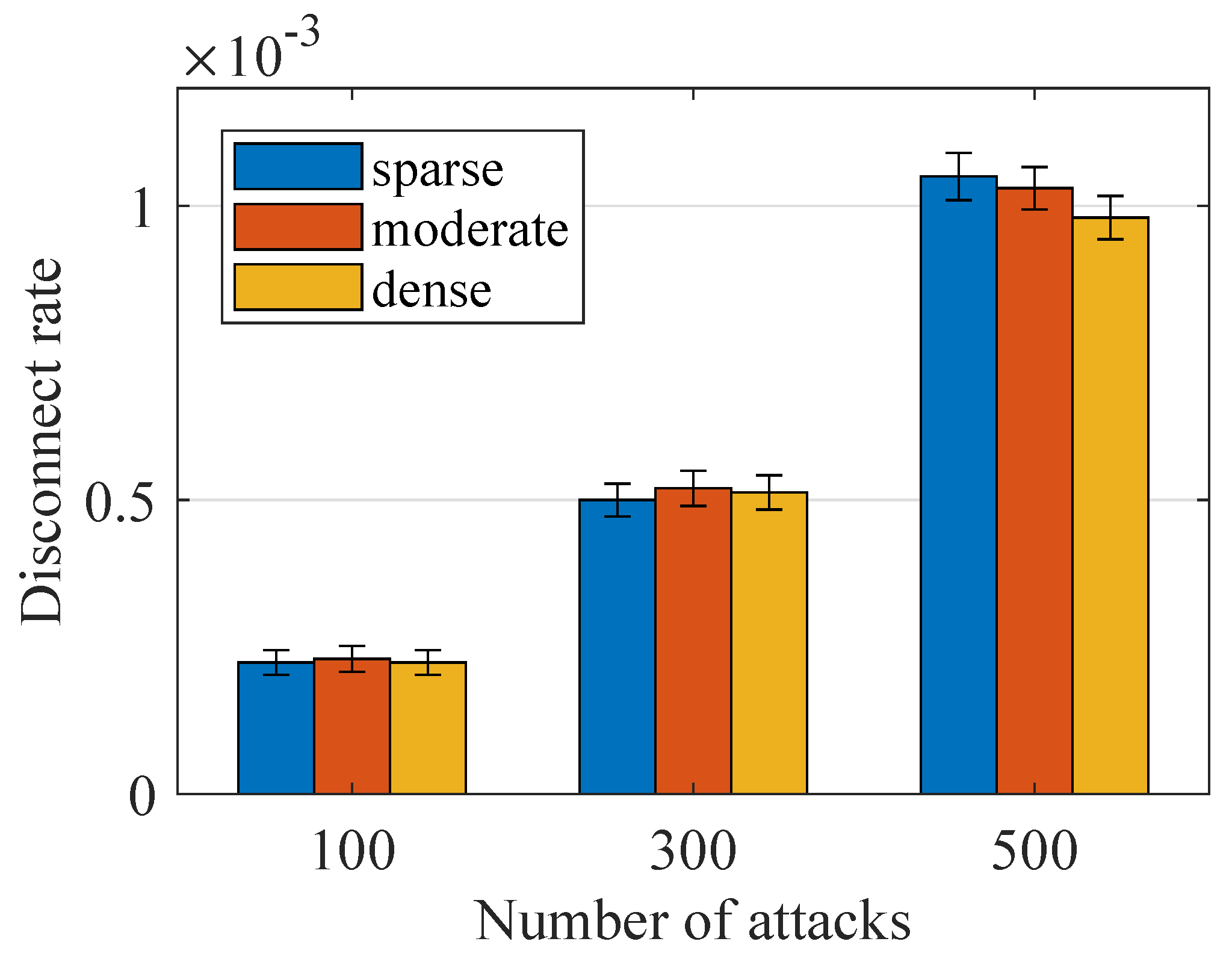
5.2. IP Spoofing
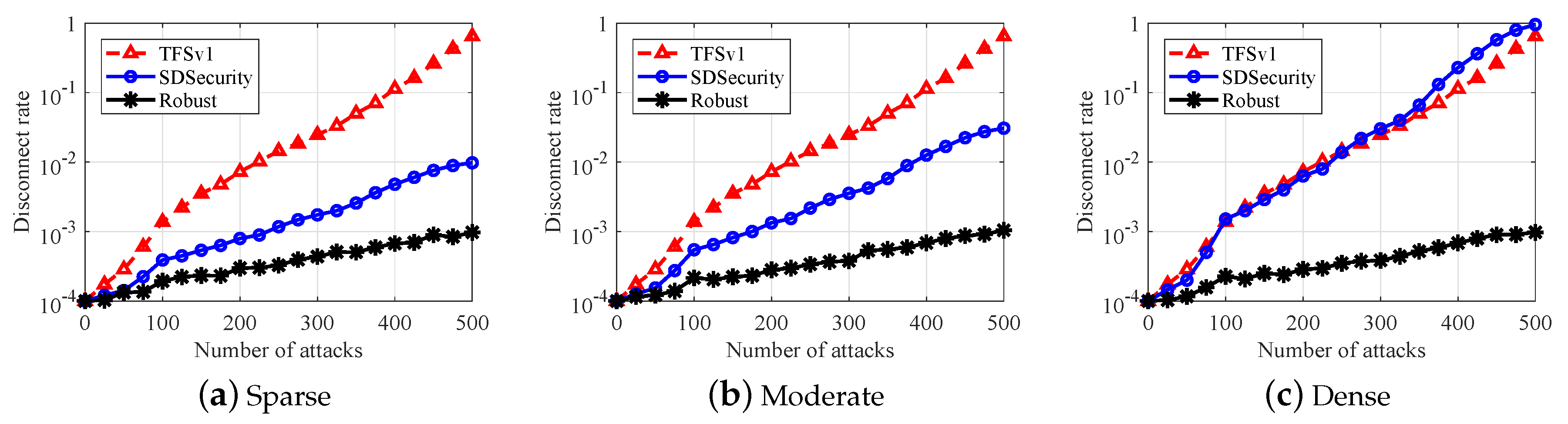
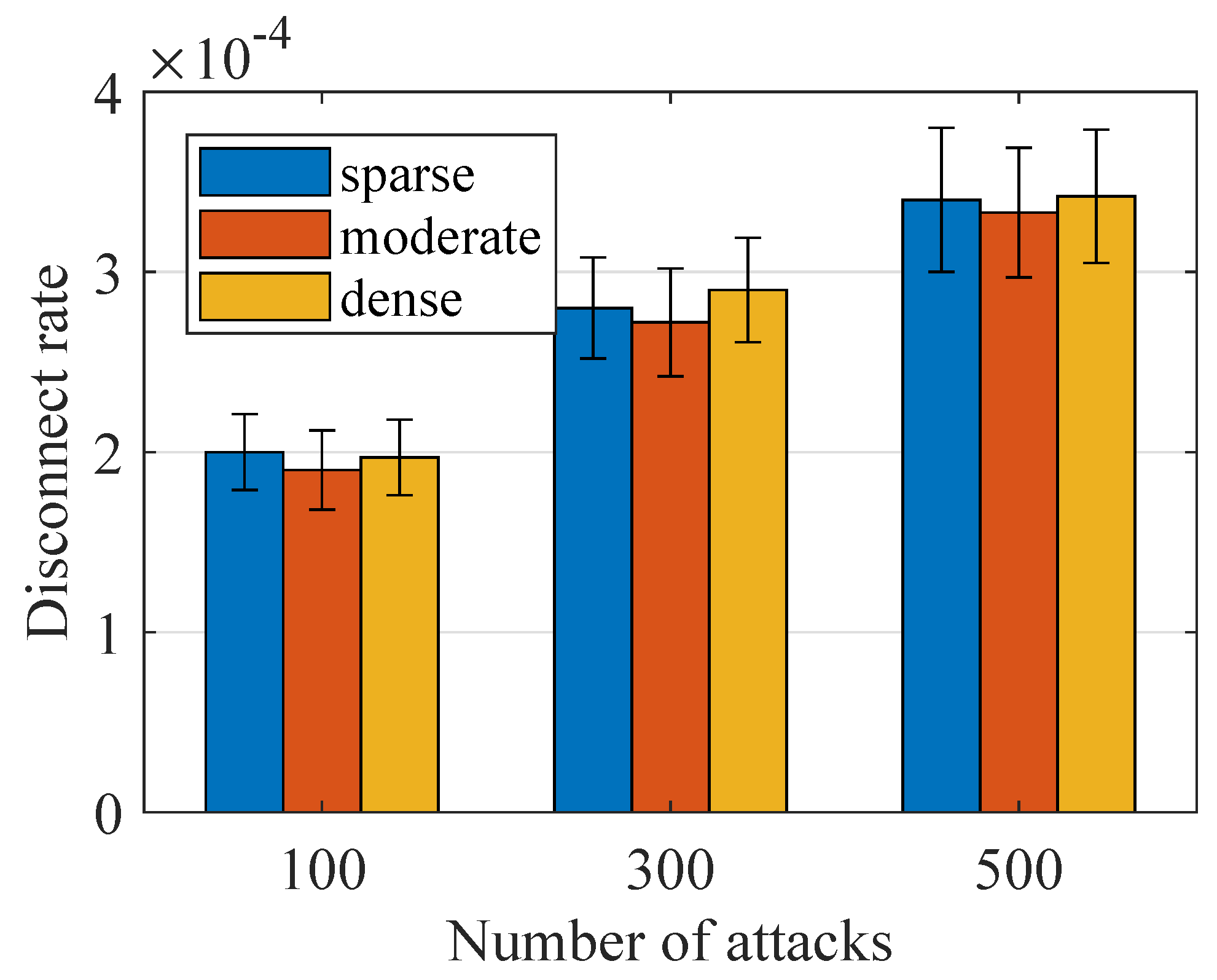
5.3. MITM Attack
5.4. Replay Attack
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Fan, K.; Gong, Y.; Liang, C.; Li, H.; Yang, Y. Lightweight and ultralightweight RFID mutual authentication protocol with cache in the reader for IoT in 5G. Secur. Commun. Netw. 2016, 9, 3095–3104. [Google Scholar] [CrossRef]
- Zhang, Z.; Chai, X.; Long, K.; Vasilakos, A.V.; Hanzo, L. Full duplex techniques for 5G networks: Self-interference cancellation, protocol design, and relay selection. IEEE Commun. Mag. 2015, 53, 128–137. [Google Scholar] [CrossRef]
- Ravindran, R.; Chakraborti, A.; Amin, S.O.; Azgin, A.; Wang, G. 5G-ICN: Delivering ICN services over 5G using network slicing. IEEE Commun. Mag. 2017, 55, 101–107. [Google Scholar] [CrossRef]
- Benzekki, K.; El Fergougui, A.; Elbelrhiti Elalaoui, A. Software-defined networking (SDN): A survey. Secur. Commun. Netw. 2016, 9, 5803–5833. [Google Scholar] [CrossRef]
- Casado, M.; Foster, N.; Guha, A. Abstractions for software-defined networks. Commun. ACM 2014, 57, 86–95. [Google Scholar] [CrossRef]
- Felix, A.; Borges, N.; Wu, H.P.; Hanlon, M.; Birk, M.; Tschersich, A. Multi-layer SDN on a commercial network control platform for packet optical networks. In Proceedings of the Optical Fiber Communication Conference, San Francisco, CA, USA, 9–13 March 2014. [Google Scholar]
- Kuklinski, S.; Chemouil, P. Network management challenges in software-defined networks. IEICE Trans. Commun. 2014, 97, 2–9. [Google Scholar] [CrossRef]
- Giotis, K.; Argyropoulos, C.; Androulidakis, G.; Kalogeras, D.; Maglaris, V. Combining OpenFlow and sFlow for an effective and scalable anomaly detection and mitigation mechanism on SDN environments. Comput. Netw. 2014, 62, 122–136. [Google Scholar] [CrossRef]
- Braga, R.; Mota, E.; Passito, A. Lightweight DDoS flooding attack detection using NOX/OpenFlow. In Proceedings of the IEEE Local Computer Networks (LCN), Denver, CO, USA, 11–14 October 2010; pp. 408–415. [Google Scholar]
- Feamster, N. Outsourcing home network security. In Proceedings of the ACM SIGCOMM Workshop on Home Networks, New Delhi, India, 30 August–3 September 2010; pp. 37–42. [Google Scholar]
- Jin, R.; Wang, B. Malware detection for mobile devices using software-defined networking. In Proceedings of the 2013 Second GENI Research and Educational Experiment Workshop, Salt Lake City, UT, USA, 20–22 March 2013; pp. 81–88. [Google Scholar]
- Jafarian, J.H.; Al-Shaer, E.; Duan, Q. Openflow random host mutation: Transparent moving target defense using software defined networking. In Proceedings of the First Workshop on Hot Topics in Software Defined Networks, Helsinki, Finland, 13 August 2012; pp. 127–132. [Google Scholar]
- Kampanakis, P.; Perros, H.; Beyene, T. SDN-based solutions for Moving Target Defense network protection. In Proceedings of the IEEE World of Wireless, Mobile and Multimedia Networks (WoWMoM), Boston, MA, USA, 14–17 June 2014; pp. 1–6. [Google Scholar]
- Sherwood, R.; Gibb, G.; Yap, K.K.; Appenzeller, G.; Casado, M.; McKeown, N.; Parulkar, G. Flowvisor: A network virtualization layer. OpenFlow Switch Consortium Tech. Rep 2009, 1, 132. [Google Scholar]
- Al-Shaer, E.; Al-Haj, S. FlowChecker: Configuration analysis and verification of federated OpenFlow infrastructures. In Proceedings of the 3rd ACM Workshop on Assurable and Usable Security Configuration, Chicago, IL, USA, 4 October 2010; pp. 37–44. [Google Scholar]
- Canini, M.; Venzano, D.; Peresini, P.; Kostic, D.; Rexford, J. A NICE way to test OpenFlow applications. In Proceedings of the 9th USENIX Conference on Networked Systems Design and Implementation, San Jose, CA, USA, 25–27 April 2012. [Google Scholar]
- Bernardo, D.V.; Chua, B.B. Introduction and analysis of SDN and NFV security architecture (SN-SECA). In Proceedings of the Advanced Information Networking and Applications (AINA), Gwangju, Korea, 25–27 March 2015; pp. 796–801. [Google Scholar]
- Feghali, A.; Kilany, R.; Chamoun, M. SDN security problems and solutions analysis. In Proceedings of the IEEE International Conference on Protocol Engineering (ICPE) and International Conference on New Technologies of Distributed Systems (NTDS), Paris, France, 22–24 July 2015; pp. 1–5. [Google Scholar]
- Alsmadi, I.; Xu, D. Security of Software Defined Networks: Asurvey. Comput. Secur. 2015, 53, 79–108. [Google Scholar] [CrossRef]
- Shin, S.W.; Gu, G. Cloudwatcher: Network security monitoring using openflow in dynamic cloud networks. In Proceedings of the 2012 IEEE International Conference on Network Protocols (ICNP), Austin, TX, USA, 30 October–2 November 2012; pp. 1–6. [Google Scholar]
- Hong, S.; Xu, L.; Wang, H.; Gu, G. Poisoning Network Visibility in Software-Defined Networks: New Attacks and Countermeasures. In Proceedings of the Network and Distributed System Security Symposium, San Diego, CA, USA, 8–11 February 2015. [Google Scholar]
- Dhawan, M.; Poddar, R.; Mahajan, K.S.; Mann, V. SPHINX: Detecting Security Attacks in Software-Defined Networks. In Proceedings of the Network and Distributed System Security Symposium, San Diego, CA, USA, 8–11 February 2015. [Google Scholar]
- Wang, K.; Qi, Y.; Yang, B.; Xue, Y.; Li, J. LiveSec: Towards Effective Security Management in Large-Scale Production Networks. In Proceedings of the 2012 32nd International Conference on Distributed Computing Systems Workshops, Macau, China, 18–21 June 2012; pp. 451–460. [Google Scholar]
- Kempf, J.; Bellagamba, E.; Kern, A.; Jocha, D.; Takács, A.; Sköldström, P. Scalable fault management for OpenFlow. In Proceedings of the IEEE Communications (ICC), Ottawa, ON, Canada, 10–15 June 2012; pp. 6606–6610. [Google Scholar]
- Darabseh, A.; Alayyoub, M.; Jararweh, Y.; Benkhelifa, E.; Vouk, M.A.; Rindos, A. SDSecurity: A Software Defined Security experimental framework. In Proceedings of the 2015 IEEE International Conference on Communication Workshop (ICCW), London, UK, 8–12 June 2015. [Google Scholar]
| Channel Types | IP Spoofing | MITM Attack | Replay Attack |
|---|---|---|---|
| Control channel | √ | √ | √ |
| Data channel | √ | √ | √ |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Yao, J.; Han, Z.; Sohail, M.; Wang, L. A Robust Security Architecture for SDN-Based 5G Networks. Future Internet 2019, 11, 85. https://doi.org/10.3390/fi11040085
Yao J, Han Z, Sohail M, Wang L. A Robust Security Architecture for SDN-Based 5G Networks. Future Internet. 2019; 11(4):85. https://doi.org/10.3390/fi11040085
Chicago/Turabian StyleYao, Jiaying, Zhigeng Han, Muhammad Sohail, and Liangmin Wang. 2019. "A Robust Security Architecture for SDN-Based 5G Networks" Future Internet 11, no. 4: 85. https://doi.org/10.3390/fi11040085
APA StyleYao, J., Han, Z., Sohail, M., & Wang, L. (2019). A Robust Security Architecture for SDN-Based 5G Networks. Future Internet, 11(4), 85. https://doi.org/10.3390/fi11040085






