Attacks and Defenses for Single-Stage Residue Number System PRNGs
Abstract
:1. Introduction
2. Materials and Methods
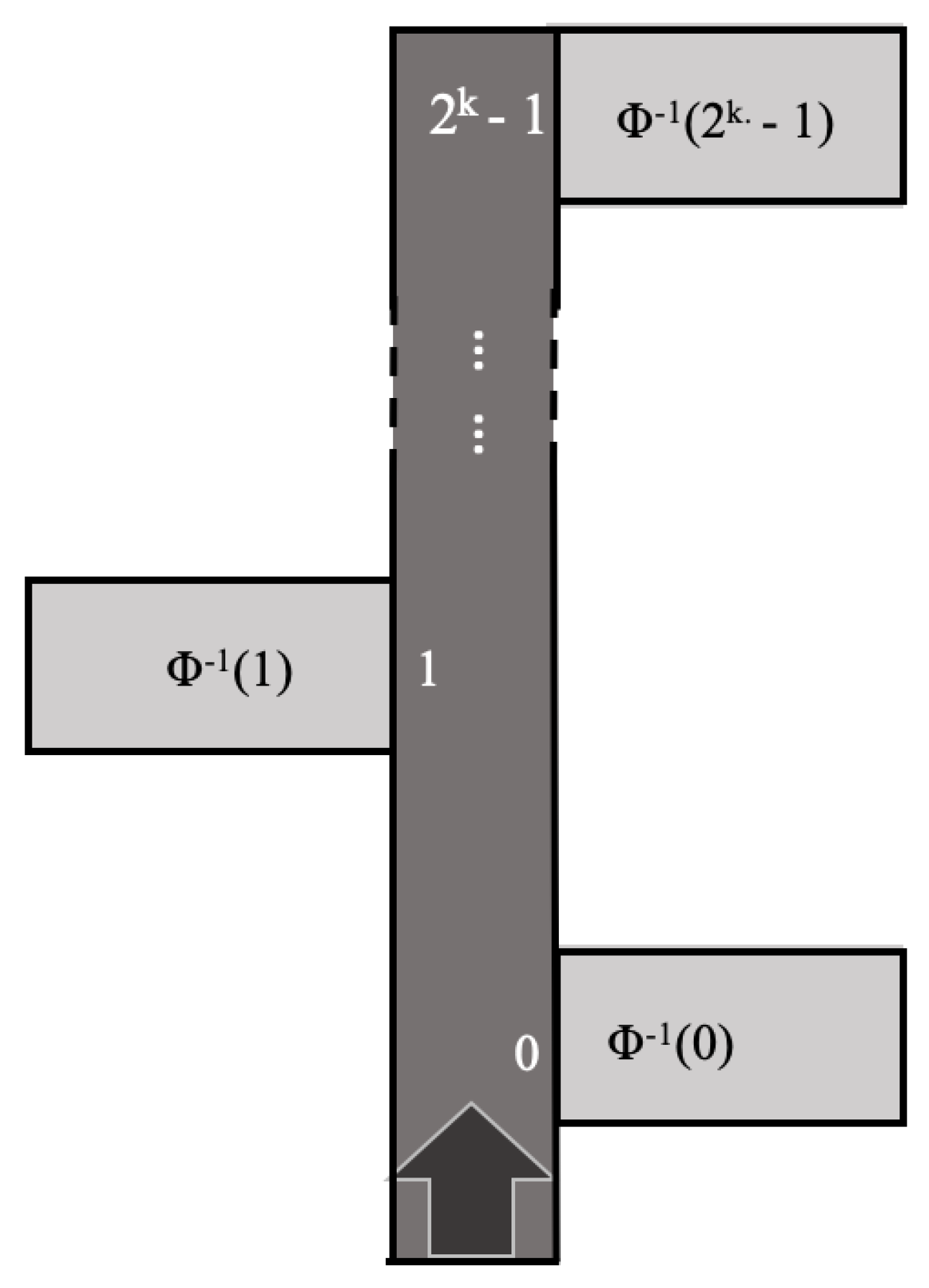
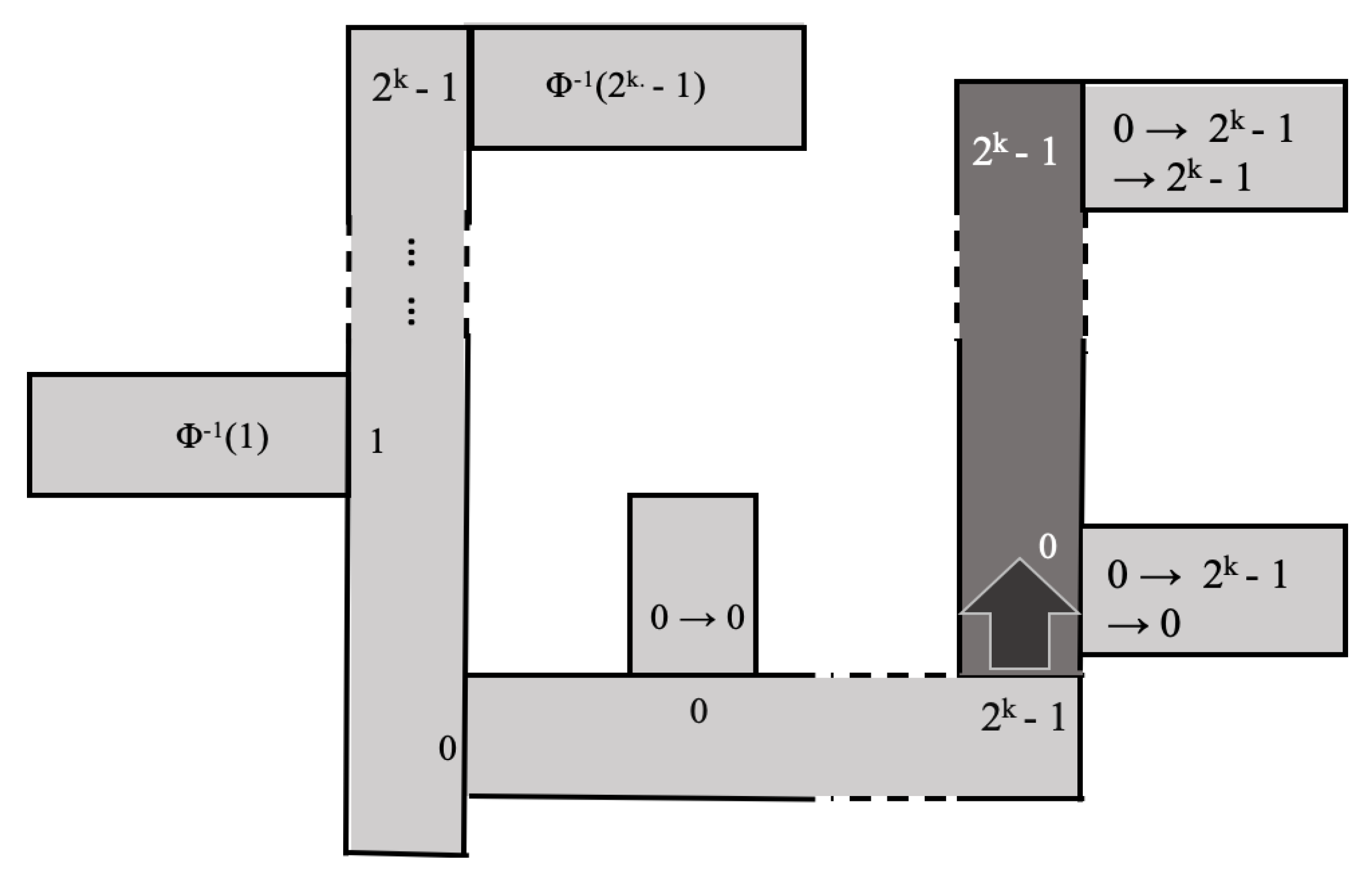
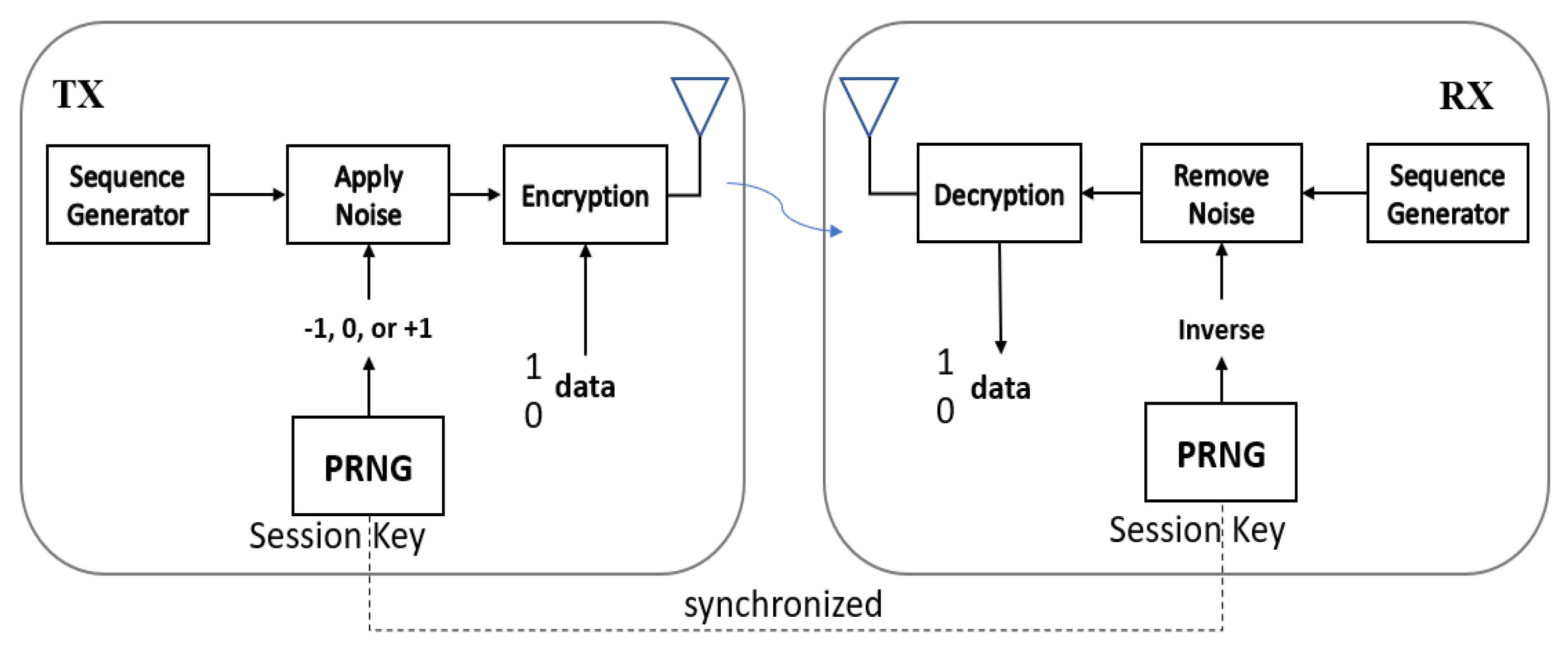
2.1. System Description
2.2. Assumptions and Goals
2.3. Mathematical Tools
Measures of Randomness
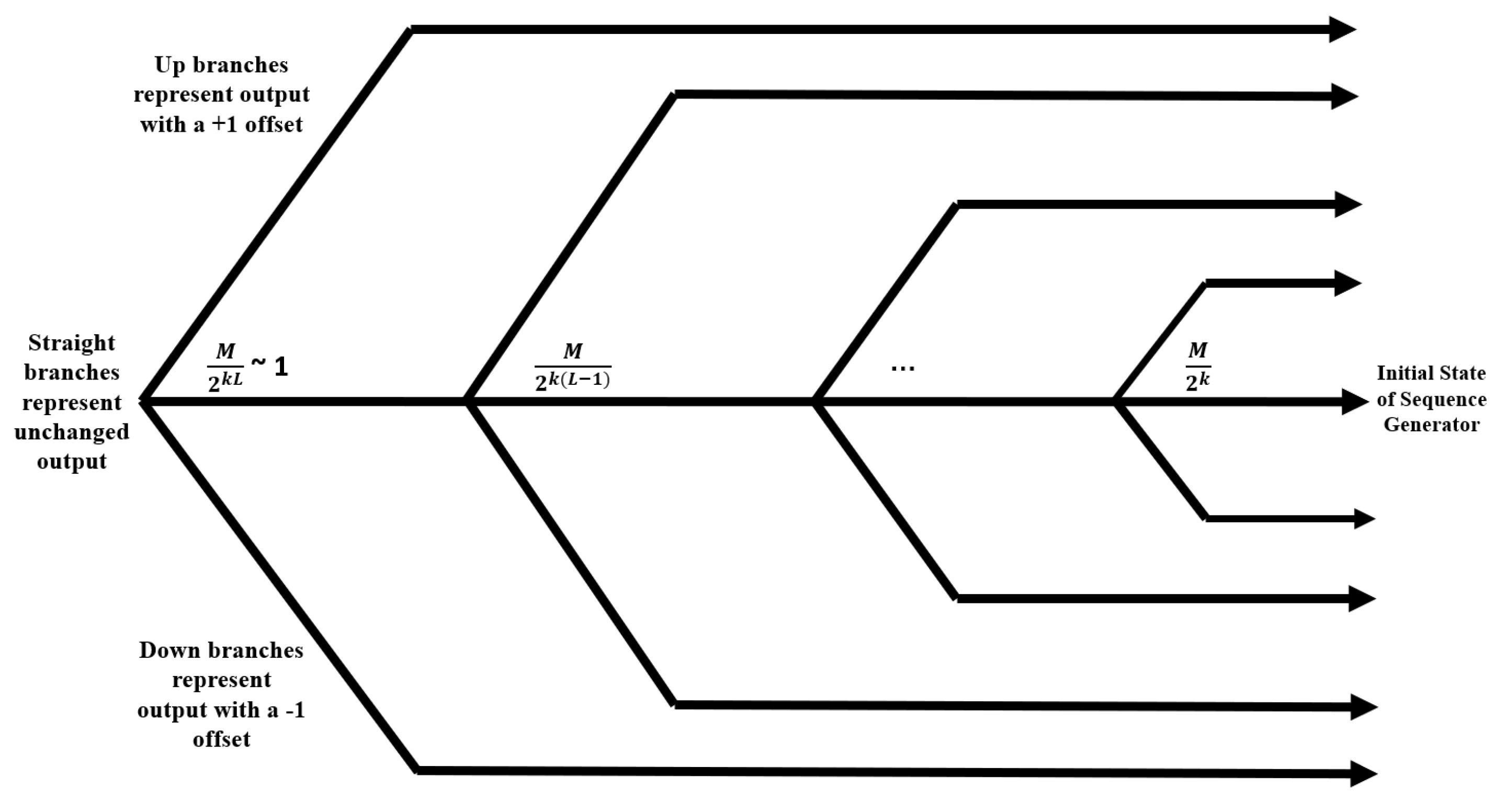
2.4. RNS-Based PRNG Attacks
3. Results
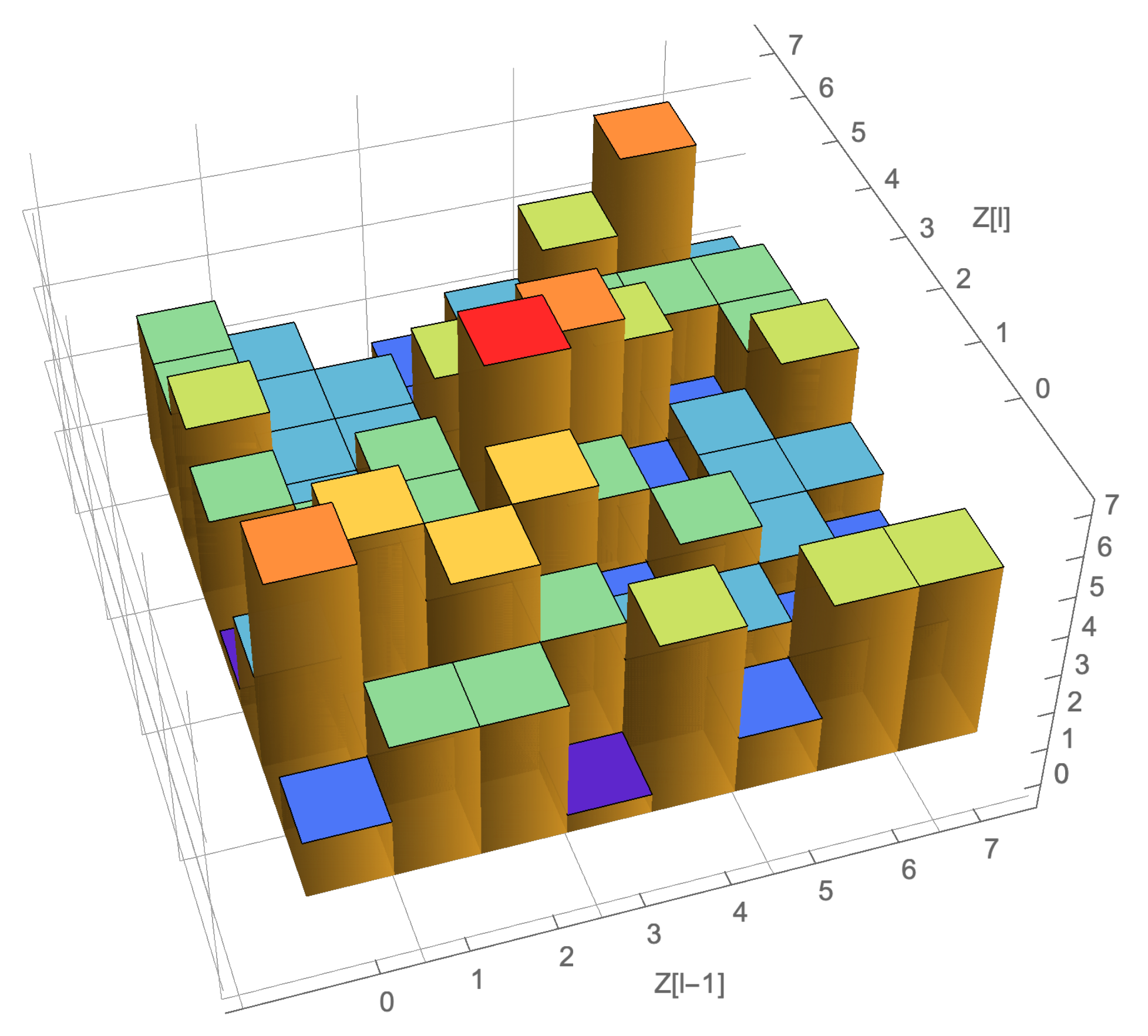
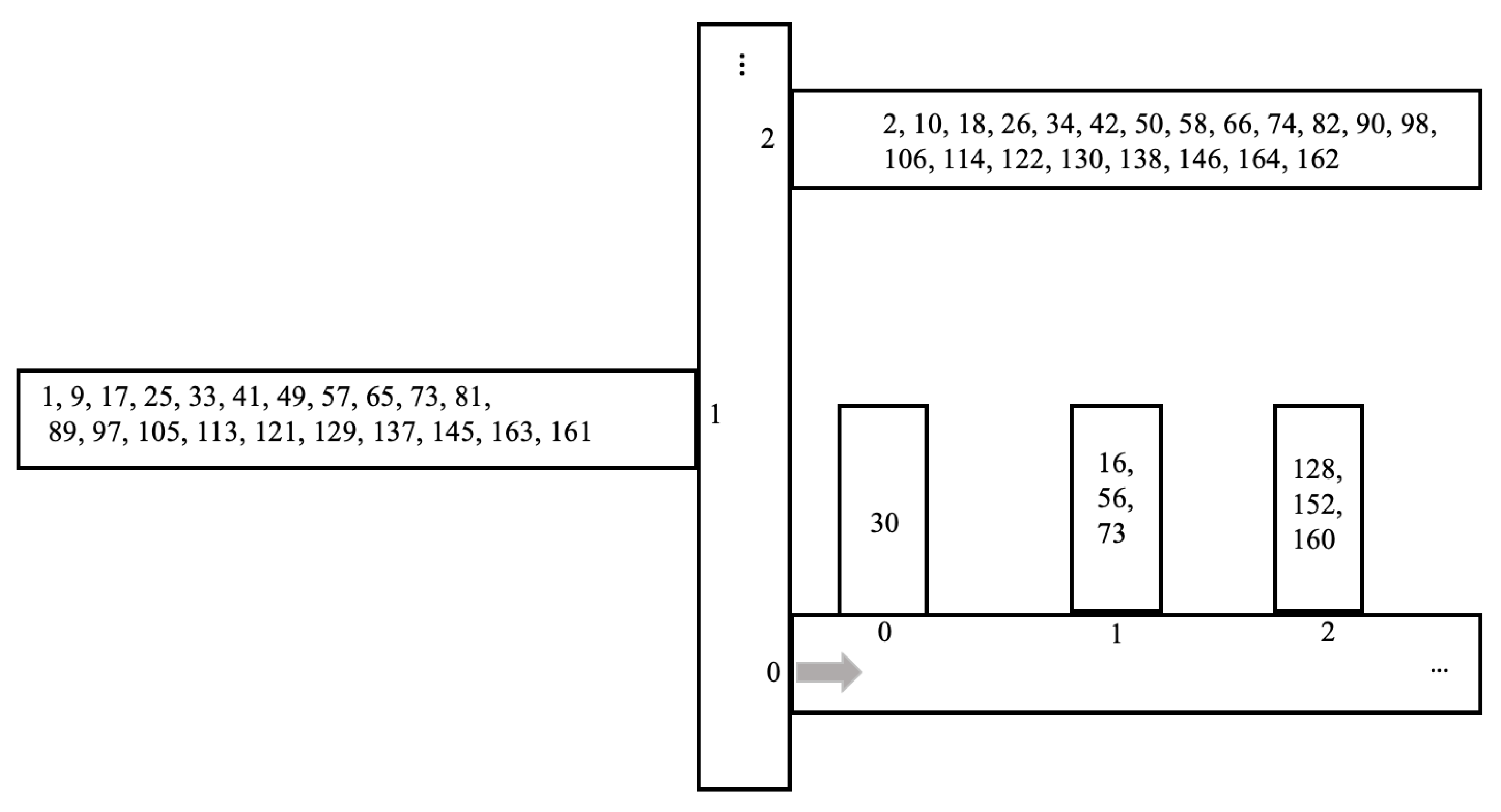
3.1. Toy Example
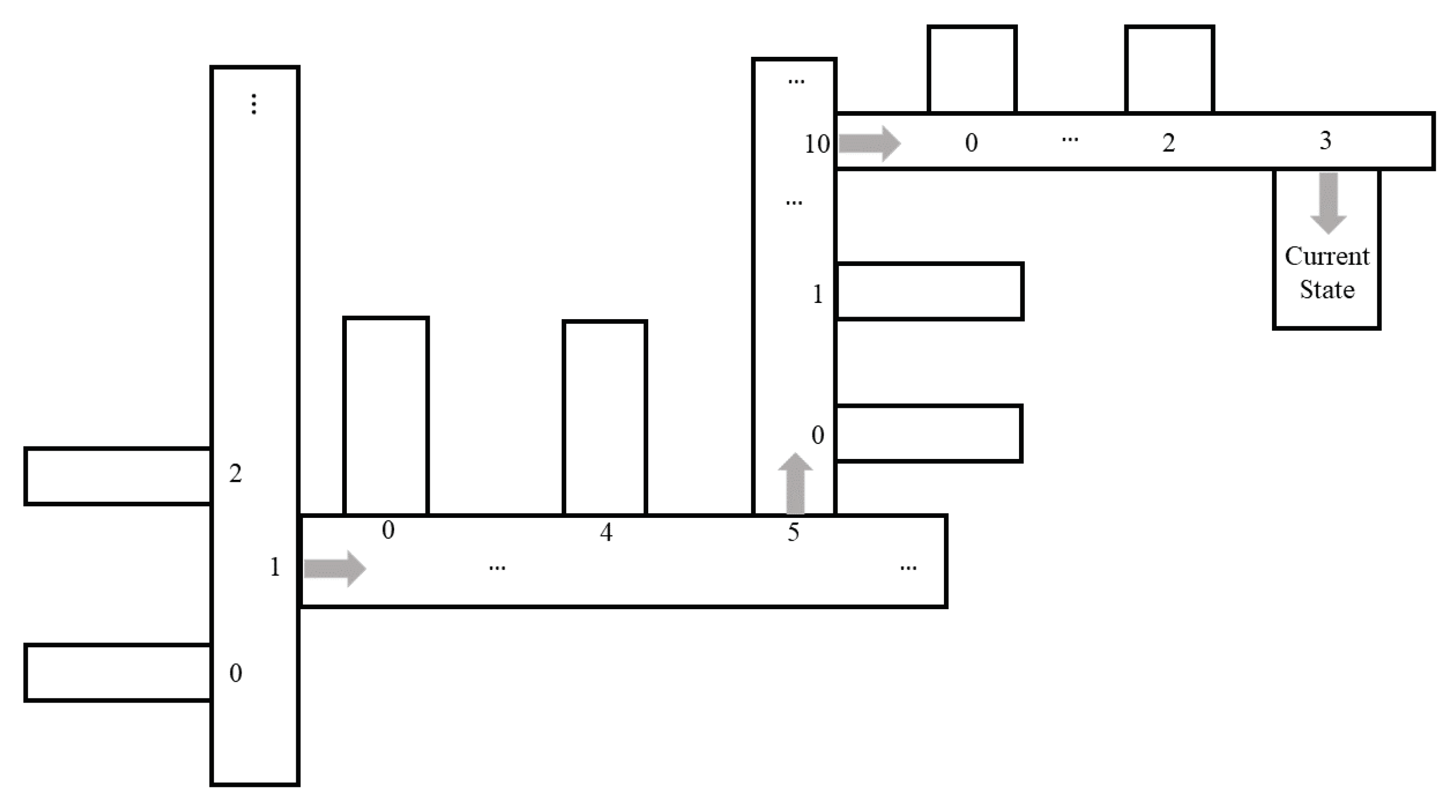
3.1.1. Toy Example: Implementing the Attack
3.1.2. Analysis of Toy Example Attack
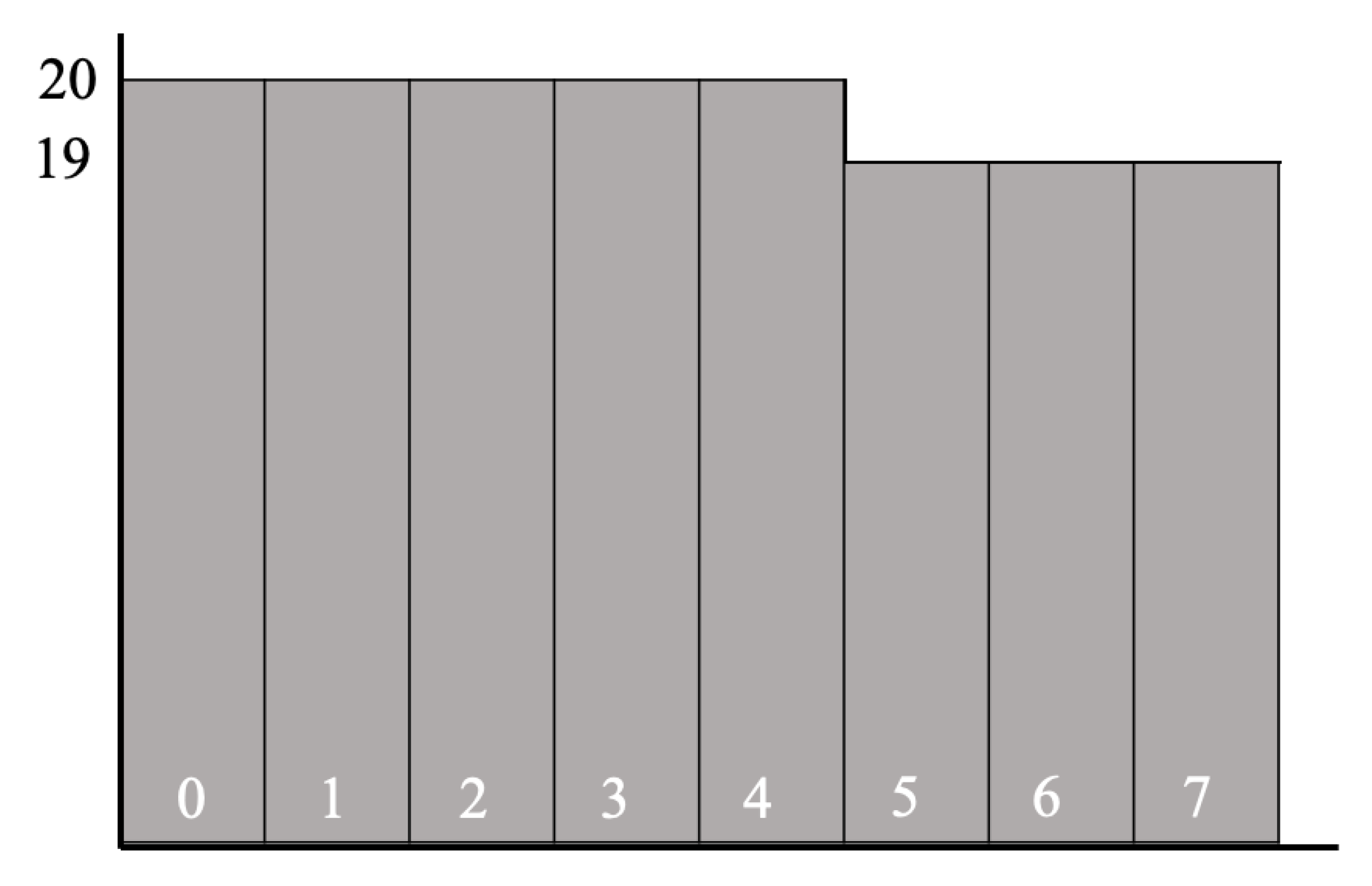
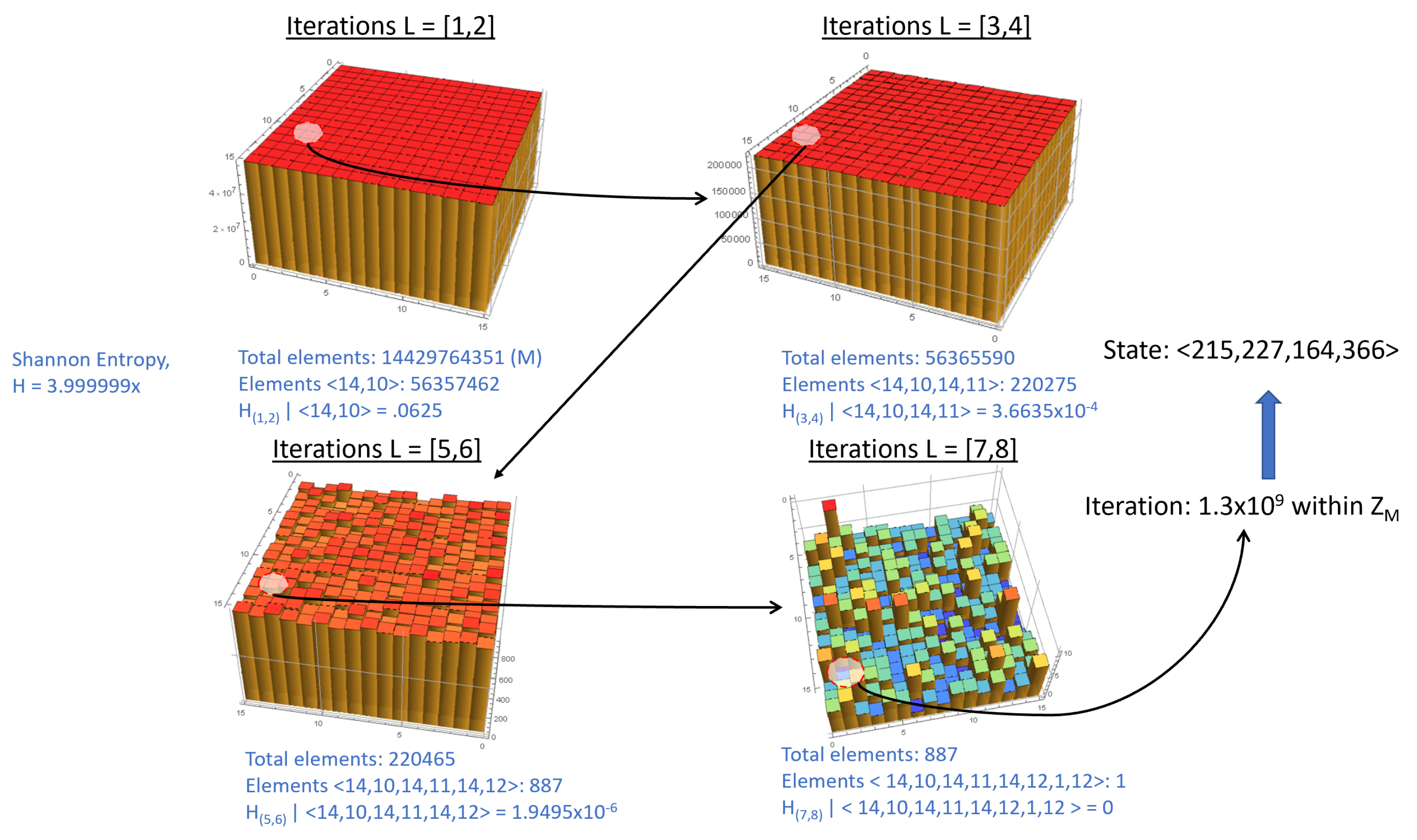
3.2. Implementing PRNG on IOT-Caliber Example
3.3. Extending to Even Larger Examples
3.4. RNS-Based PRNG Defenses and Perturbations
3.4.1. Noise
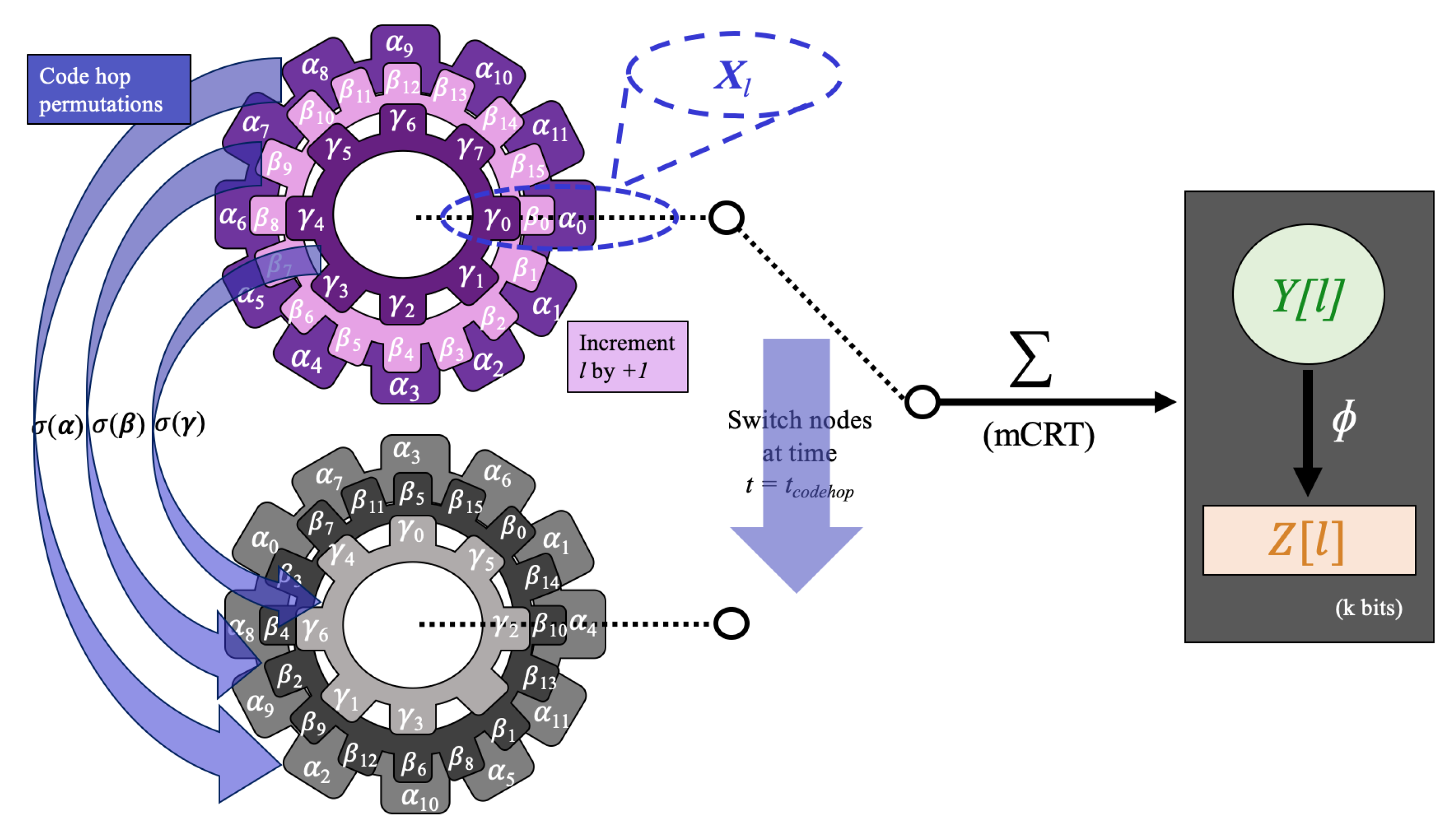
3.4.2. Code Hopping
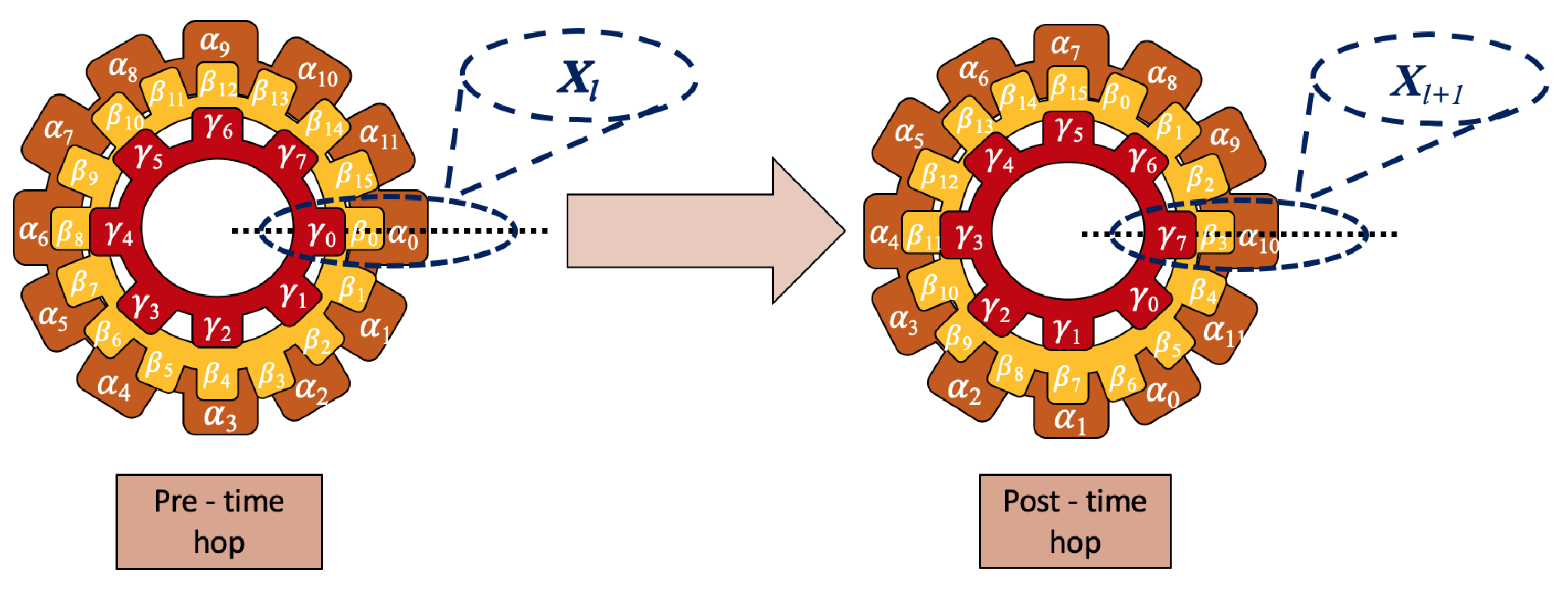
3.4.3. Time Hopping
3.5. Modified RNS Attack to Account for Noise
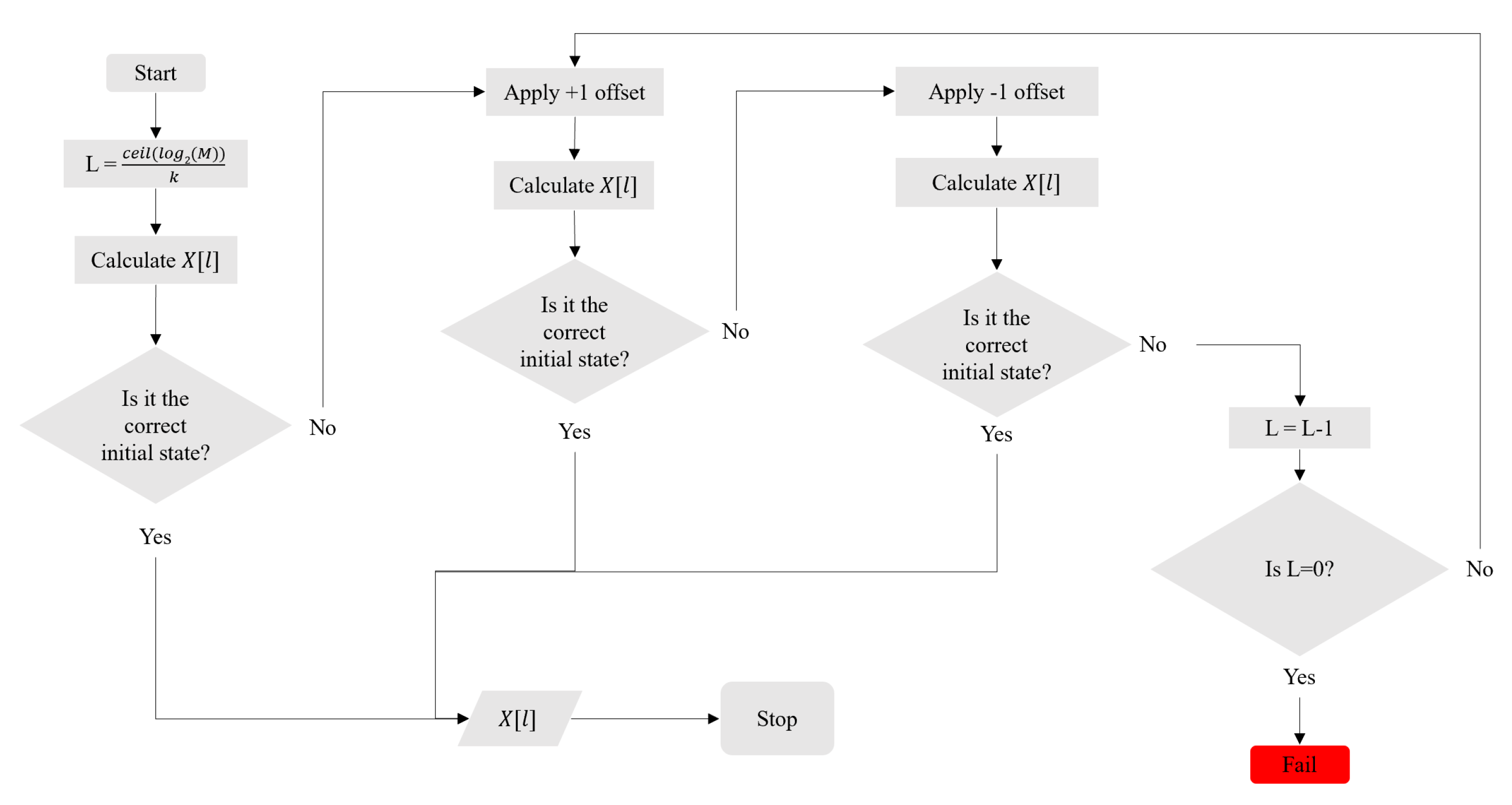
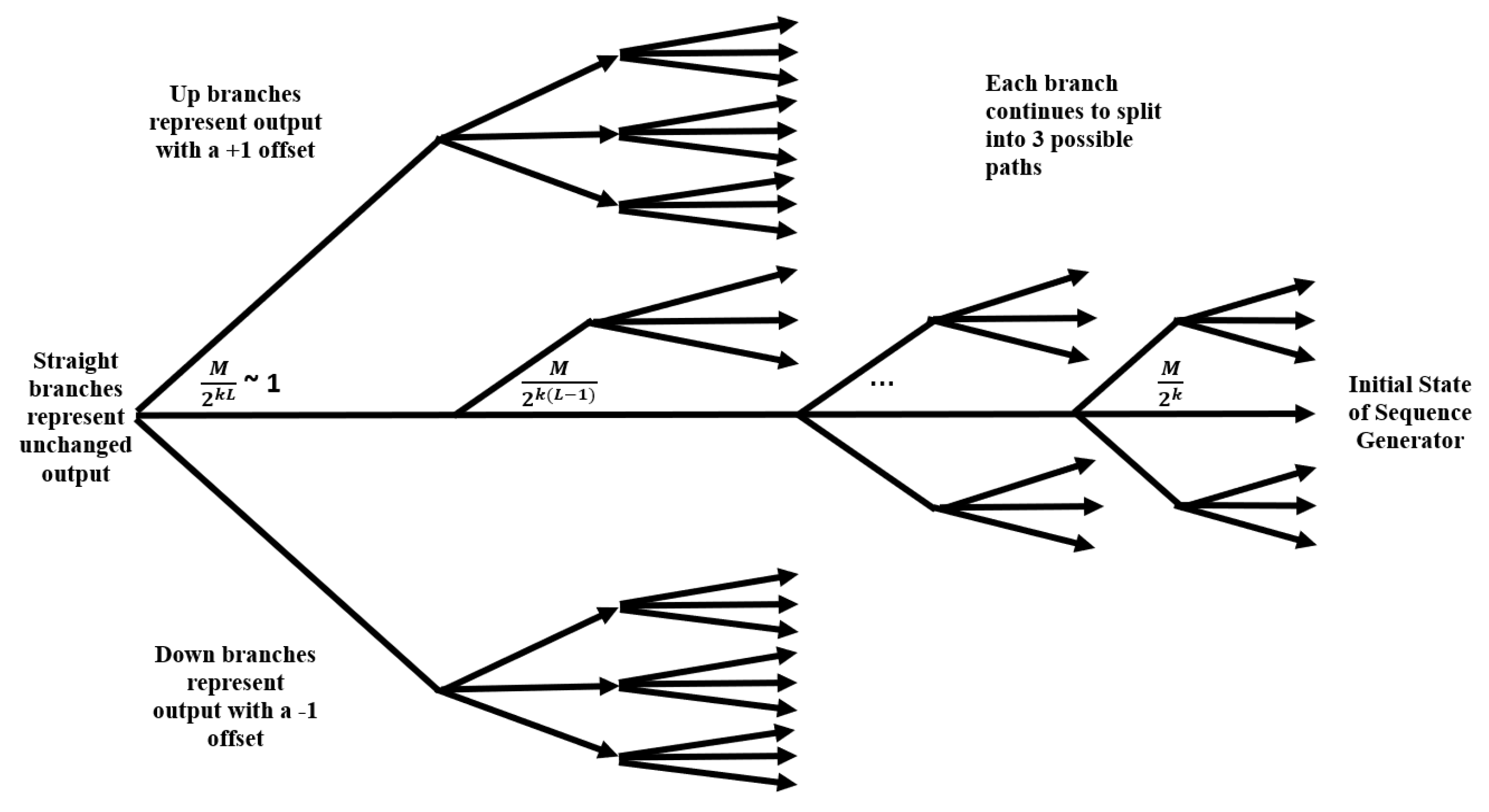
| Algorithm 1: Modified RNS Attack for a Single Error |
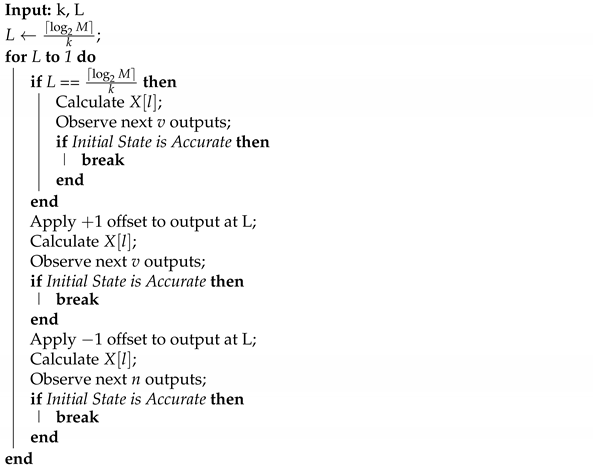 |
3.6. Analysis of RNS-Based PRNG Defenses
4. Conclusions and Future Work
Author Contributions
Funding
Institutional Review Board Statement
Acknowledgments
Conflicts of Interest
References
- Smid, M.E.; Branstad, D.K. Data Encryption Standard: Past and future. Proc. IEEE 1988, 76, 550–559. [Google Scholar] [CrossRef] [Green Version]
- distributed.net. DES Code Cracked in Record Time. Available online: http://www.distributed.net/images/7/7e/19990120_-_PR-_nmfusion.pdf (accessed on 4 February 2021).
- NIST CNSS Policy No. 15, Fact Sheet No. 1. National Policy on the Use of the Advanced Encryption Standard (AES) to Protect National Security Systems and National Security Information. June 2003. Available online: https://csrc.nist.gov/csrc/media/projects/cryptographic-module-validation-program/documents/cnss15fs.pdf (accessed on 13 May 2021).
- NIST. Report on the Development of the Advanced Encryption Standard (AES). J. Res. Natl. Inst. Stand. Technol. 2001, 106, 511–577. [Google Scholar] [CrossRef]
- Bogdanov, A. Improved Side-Channel Collision Attacks on AES; Springer: Berlin/Heidelberg, Germany, 2007; pp. 84–95. [Google Scholar]
- Bogdanov, A.; Khovratovich, D.; Rechberger, C. Biclique Cryptanalysis of the Full AES. In Advances in Cryptology—ASIACRYPT 2011; Lee, D.H., Wang, X., Eds.; Springer: Berlin/Heidelberg, Germany, 2011; pp. 344–371. [Google Scholar]
- Dworkin, M.J.; Barker, E.B.; Nechvatal, J.R.; Foti, J.; Bassham, L.E.; Roback, E.; Dray, J.F. Announcing the Advanced Encryption Standard (AES). NIST Publication Series Report. 2001. Available online: https://www.nist.gov/publications/advanced-encryption-standard-aes (accessed on 15 June 2021).
- Kulkarni, A.; Sathe, S. Healthcare Applications of the Internet of Things: A Review. Int. J. Comput. Sci. Inf. Technol. 2014, 5, 6229–6232. [Google Scholar]
- Chen, D.; Liu, Z.; Wang, L.; Dou, M.; Chen, J.; Li, H. Natural Disaster Monitoring with Wireless Sensor Networks: A Case Study of Data-intensive Applications upon Low-Cost Scalable Systems. Mobile Netw. Appl. 2013, 18, 651–663. [Google Scholar] [CrossRef]
- Rolfes, C.; Poschmann, A.; Leander, G.; Paar, C. Ultra-Lightweight Implementations for Smart Devices—Security for 1000 Gate Equivalents. In Smart Card Research and Advanced Applications; Grimaud, G., Standaert, F.X., Eds.; Springer: Berlin/Heidelberg, Germany, 2008; pp. 89–103. [Google Scholar]
- Patel, S.T.; Mistry, N.H. A survey: Lightweight cryptography in WSN. In Proceedings of the 2015 International Conference on Communication Networks (ICCN), Gwalior, India, 19–21 November 2015; pp. 11–15. [Google Scholar] [CrossRef]
- Easttom, C. A Study of Cryptographic Backdoors in Cryptographic Primitives. In Proceedings of the Iranian Conference on Electrical Engineering (ICEE), Mashhad, Iran, 8–10 May 2018; pp. 1664–1669. [Google Scholar] [CrossRef]
- Barker, E.B.; Kelsey, J.M. Recommendation for Random Number Generation Using Deterministic Random Bit Generators (Revised); US Department of Commerce, Technology Administration, National Institute of Standards and Technology, Computer Security Division, Information Technology Laboratory: Gaithersburg, MD, USA, 2012.
- Landau, S. Highlights from Making Sense of Snowden, Part II: What’s Significant in the NSA Revelations. IEEE Secur. Priv. 2014, 12, 62–64. [Google Scholar] [CrossRef]
- Schneier, B.; Fredrikson, M.; Kohno, T.; Ristenpart, T. Surreptitiously Weakening Cryptographic Systems. IACR Cryptol. ePrint Arch. 2015, 2015, 97. [Google Scholar]
- Amin, M.; Afzal, M. On the Vulnerability of EC DRBG. In Proceedings of the 2015 12th International Bhurban Conference on Applied Sciences and Technology (IBCAST), Islamabad, Pakistan, 13–17 January 2015; pp. 318–322. [Google Scholar] [CrossRef]
- Albertini, A.; Aumasson, J.P.; Eichlseder, M.; Mendel, F.; Schläffer, M. Malicious Hashing: Eve’s Variant of SHA-1. In Proceedings of the Selected Areas in Cryptography—SAC 2014, Montreal, QC, Canada, 14–15 August 2014; Joux, A., Youssef, A., Eds.; Lecture Notes in Computer Science. Springer: Cham, Switzerland, 2014; Volume 2. [Google Scholar]
- Bannier, A.; Filiol, E. Mathematical backdoors in symmetric encryption systems—Proposal for a backdoored AES-like block cipher. arXiv 2017, arXiv:1702.06475. [Google Scholar]
- McKay, K.; Bassham, L.; Turan, M.S.; Mouha, N. NISTIR 8114: Report on Lightweight Cryptography. 2017. Available online: https://nvlpubs.nist.gov/nistpubs/ir/2017/NIST.IR.8114.pdf (accessed on 25 April 2021).
- Park, J.; Na, J.; Kim, M. A Practical Approach for Enhancing Security of EPC global RFID Gen2 Tag. In Proceedings of the IEEE Future Generation Communication and Networking (FGCN 2007), Jeju, Korea, 6–8 December 2007; Volume 1, pp. 436–441. [Google Scholar] [CrossRef]
- ISO, ISO/IEC 18000-63:2015. Information Technology—Radio Frequency Identification for Item Management—Part 63: Parameters for Air Interface Communications at 860 MHz to 960 MHz Type C. 2015; Available online: https://www.iso.org/standard/63675.html (accessed on 25 April 2021).
- Bucci, M.; Germani, L.; Luzzi, R.; Trifiletti, A.; Varanonuovo, M. A high-speed oscillator-based truly random number source for cryptographic applications on a smart card IC. IEEE Trans. Comput. 2003, 52, 403–409. [Google Scholar] [CrossRef]
- Şarkışla, M.A.; Ergün, S. An Area Efficient True Random Number Generator Based on Modified Ring Oscillators. In Proceedings of the 2018 IEEE Asia Pacific Conference on Circuits and Systems (APCCAS), Chengdu, China, 26–30 October 2018; pp. 274–278. [Google Scholar]
- Stipčević, M. Quantum random number generators and their applications in cryptography. In Advanced Photon Counting Techniques VI; International Society for Optics and Photonics: Bellingham, WA, USA, 2012; Volume 8375, pp. 1474–1479. Available online: https://spie.org/Publications/Proceedings/Paper/10.1117/12.919920?SSO=1 (accessed on 15 June 2021).
- Gong, L.; Zhang, J.; Liu, H.; Sang, L.; Wang, Y. True Random Number Generators Using Electrical Noise. IEEE Access 2019, 7, 125796–125805. [Google Scholar] [CrossRef]
- Holman, W.T.; Connelly, J.A.; Dowlatabadi, A.B. An integrated analog/digital random noise source. IEEE Trans. Circuits Syst. I Fundam. Theory Appl. 1997, 44, 521–528. [Google Scholar] [CrossRef]
- Li, D.; Lu, Z.; Zhou, X.; Liu, Z. PUFKEY: A High-Security and High-Throughput Hardware True Random Number Generator for Sensor Networks. Sensors 2015, 15, 26251–26266. [Google Scholar] [CrossRef] [Green Version]
- Sathyanarayana, S.V.; Lavanya, R. Group Diffie Hellman key exchange algorithm based secure group communication. In Proceedings of the 3rd International Conference on Applied and Theoretical Computing and Communication Technology, Tumkur, Karnataka, India, 21–23 December 2017; pp. 281–289. [Google Scholar]
- Cagigal, N.P.; Bracho, S. Algorithmic determination of linear-feedback in a shift register for pseudorandom binary sequence generation. IEEE Proc. G Electron. Circuits Syst. 1986, 133, 191–194. [Google Scholar] [CrossRef]
- Dey, S. SD-C1BBR: SD-count-1-byte-bit randomization: A new advanced cryptographic randomization technique. In Proceedings of the IEEE World Congress on Information and Communication Technologies, Las Vegas, NV, USA, 27–29 April 2012; pp. 236–241. [Google Scholar]
- Shin, S.-H.; Yoo, K.-Y. An Improved PRNG Based on the Hybrid between One- and Two- Dimensional Cellular Automata. In Proceedings of the 2009 Sixth International Conference on Information Technology: New Generations, Chennai, India, 3–5 April 2018. [Google Scholar] [CrossRef] [Green Version]
- Saha, S.; Karsh, R.K.; Amrohi, M. Encryption and decryption of images using secure linear feedback shift registers. In Proceedings of the IEEE 2018 International Conference on Communication and Signal Processing (ICCSP), Kansas City, MO, USA, 20–24 May 2018; pp. 295–298. [Google Scholar]
- Jumaa, N. Digital Image Encryption using AES and Random Number Generator. Iraqi J. Electr. Electron. Eng. 2018, 14. [Google Scholar] [CrossRef]
- Hobincu, R.; Datcu, O. A novel chaos based prng targeting secret communication. In Proceedings of the 2018 International Conference on Communications (COMM), Bucharest, Romania, 14–16 June 2018; pp. 459–462. [Google Scholar]
- Kwan, P. Interface Specification IS-GPS-200. 2019. Available online: https://navcen.uscg.gov/pdf/gps/IS_GPS_200K_Mar19.pdf (accessed on 15 June 2021).
- Aguirre, J.V.; Álvarez, R.; Tortosa, L.; Zamora, A. Fast pseudorandom generator based on packed matrices. In Proceedings of the 6th WSEAS International Conference on Information Security and Privacy, Tenerife, Spain, 14–16 December 2007. [Google Scholar]
- Michaels, A.J.; Meadows, M.; Ernst, J. PRNG sequence combination techniques via galois extension fields. In Proceedings of the MILCOM 2017—2017 IEEE Military Communications Conference (MILCOM), Baltimore, MD, USA, 23–25 October 2017; pp. 841–845. [Google Scholar]
- Manjula, G.; Mohan, H.S. Improved dynamic S-box generation using hash function for AES and its performance analysis. In Proceedings of the IEEE 2018 Second International Conference on Green Computing and Internet of Things (ICGCIoT), Karnataka, India, 16–18 August 2018; pp. 109–115. [Google Scholar]
- Tsoi, K.H.; Leung, K.H.; Leong, P.H.W. Compact FPGA-based true and pseudo random number generators. In Proceedings of the 11th Annual IEEE Symposium on Field-Programmable Custom Computing Machines, Napa, CA, USA, 9–11 April 2003; pp. 51–61. [Google Scholar]
- Salmon, J.K.; Moraes, M.A.; Dror, R.O.; Shaw, D.E. Parallel random numbers: As easy as 1, 2, 3. In Proceedings of the 2011 International Conference for High Performance Computing, Networking, Storage and Analysis, New York, NY, USA, 12–18 November 2011; pp. 1–12. [Google Scholar]
- Kaur, A.; Verma, H.K.; Singh, R.K. 3D—Playfair cipher using LFSR based unique random number generator. In Proceedings of the Sixth International Conference on Contemporary Computing (IC3), Noida, India, 8–10 August 2013; pp. 18–23. [Google Scholar]
- Jessa, M. Data transmission with adjustable security exploiting chaos-based pseudorandom number generators. In Proceedings of the IEEE International Symposium on Circuits and Systems, Phoenix-Scottsdale, AZ, USA, 26–29 May 2002; Volume 3, p. III. [Google Scholar]
- Paul, B.; Trivedi, G.; Jan, P.; Němec, Z. Efficient PRNG Design and Implementation for Various High Throughput Cryptographic and Low Power Security Applications. In Proceedings of the 29th International Conference Radioelektronika, Pardubice, Czech Republic, 16–18 April 2019; pp. 1–6. [Google Scholar]
- Gonzalez-Diaz, V.R.; Pareschi, F.; Setti, G.; Maloberti, F. A Pseudorandom Number Generator Based on Time-Variant Recursion of Accumulators. IEEE Trans. Circuits Syst. II Express Briefs 2011, 58, 580–584. [Google Scholar] [CrossRef]
- Visan, D.A.; Lita, I.; Jurian, M.; Gherghe, M. Pseudorandom sequence generator for spread spectrum communications. In Proceedings of the 2018 10th International Conference on Electronics, Computers and Artificial Intelligence (ECAI), Iasi, Romania, 28–30 June 2018; pp. 1–4. [Google Scholar]
- Gutiérrez-Cárdenas, J.M. Secret key steganography with message obfuscation by pseudo-random number generators. In Proceedings of the 2014 IEEE 38th International Computer Software and Applications Conference Workshops, Vasteras, Sweden, 21–25 July 2014; pp. 164–168. [Google Scholar]
- Chernyshev, M.; Valli, C.; Johnstone, M. Revisiting Urban War Nibbling: Mobile Passive Discovery of Classic Bluetooth Devices Using Ubertooth One. IEEE Trans. Inf. Forensics Secur. 2017, 12, 1625–1636. [Google Scholar] [CrossRef]
- Buchovecká, S.; Hlaváč, J. Frequency injection attack on a random number generator. In Proceedings of the IEEE 16th International Symposium on Design and Diagnostics of Electronic Circuits & Systems, Karlovy Vary, Czech Republic, 8–10 April 2013; pp. 128–130. [Google Scholar]
- Ferrenberg, A.; Landau, D.P.; Wong, Y.J. Monte Carlo Simulations: Hidden Errors from ‘‘Good’’ Random Number Generators. Phys. Rev. Lett. 1992, 69, 3382–3384. [Google Scholar] [CrossRef] [PubMed]
- Lüscher, M. A Portable High-Quality Random Number Generator for Lattice Field Theory Simulations. Comput. Phys. Commun. 1994, 71, 100–110. [Google Scholar] [CrossRef] [Green Version]
- Rukhin, A.; Soto, J.; Nechvatal, J.; Smid, M.; Barker, E. A Statistical Test Suite for Random and Pseudorandom Number Generators for Cryptographic Applications. 2000. Available online: http://repository.root-me.org/Cryptographie/EN%20-%20NIST%20statistical%20test%20suite%20for%20random%20and%20pseudorandom%20number%20generators.pdf (accessed on 15 June 2021).
- Marsaglia, G. DIEHARD: A Battery of Tests of Randomness. 1995. Available online: https://ci.nii.ac.jp/naid/10026040317/#cit (accessed on 15 June 2021).
- Nighswander, T.; Ledvina, B.; Diamond, J.; Brumley, R.; Brumley, D. GPS software attacks. In Proceedings of the 2012 ACM Conference on Computer and Communications Security, Raleigh, NC, USA, 16–18 October 2012. [Google Scholar]
- Adrian, D.; Bhargavan, K.; Durumeric, Z.; Gaudry, P.; Green, M.; Halderman, J.A.; Heninger, N.; Springall, D.; Thomé, E.; Valenta, L.; et al. Imperfect Forward Secrecy: How Diffie-Hellman Fails in Practice. In Proceedings of the 22nd ACM SIGSAC Conference on Computer and Communications Security (CCS ’15), Denver, CO, USA, 12–16 October 2015; pp. 5–17. [Google Scholar]
- Chouhan, N.; Saini, H.K.; Jain, S.C. A novel technique to modify the SHOR’S algorithm—Scaling the encryption scheme. In Proceedings of the Second International Conference on Electrical, Computer and Communication Technologies (ICECCT), Coimbatore, India, 20–22 February 2019; pp. 1–4. [Google Scholar]
- Imamura, K.; Yoshida, W. A simple derivation of the Berlekamp-Massey algorithm and some applications. IEEE Trans. Inf. Theory 1987, 33, 146–150. [Google Scholar] [CrossRef]
- Feng, G.; Tzeng, K.K. A generalization of the Berlekamp-Massey algorithm for multisequence shift-register synthesis with applications to decoding cyclic codes. IEEE Trans. Inf. Theory 1991, 37, 1274–1287. [Google Scholar] [CrossRef]
- McGinthy, J.M.; Michaels, A.J. Semi-coherent transmission security for low power IoT devices. In Proceedings of the 2018 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Halifax, NS, Canada, 30 July–3 August 2018; pp. 170–177. [Google Scholar]
- Jessa, M.; Walentynowicz, M. Statistical properties of number sequences generated by 1D chaotic maps considered as a potential source of pseudorandom number sequences. In Proceedings of the 8th IEEE International Conference on Electronics, Circuits and Systems, Malta, 2–5 September 2001; Volume 1, pp. 449–455. [Google Scholar]
- Inayah, K.; Sukmono, B.E.; Purwoko, R.; Indarjani, S. Insertion attack effects on standard PRNGs ANSI X9.17 and ANSI X9.31 based on statistical distance tests and entropy difference tests. In Proceedings of the International Conference on Computer, Control, Informatics and Its Applications (IC3INA), Jakarta, Indoneisia, 19–20 November 2013; pp. 219–224. [Google Scholar]
- Bhowal, S.; Dutta, S.; Mitra, S. An efficient reduced set brute force attack technique for a particular steganographic tool using Vername algorithm. In Proceedings of the 2017 Fourth International Conference on Image Information Processing (ICIIP), Shimla, India, 21–23 May 2017; pp. 1–4. [Google Scholar]
- Khiabani, Y.S.; Wei, S.; Yuan, J.; Wang, J. Enhancement of Secrecy of Block Ciphered Systems by Deliberate Noise. IEEE Trans. Inf. Forensics Secur. 2012, 7, 1604–1613. [Google Scholar] [CrossRef] [Green Version]
- Willett, M. Deliberate noise in a modern cryptographic system (Corresp.). IEEE Trans. Inf. Theory 1980, 26, 102–104. [Google Scholar] [CrossRef]
- Vilela, J.P.; Bloch, M.; Barros, J.; Mclaughlin, S.W. Wireless Secrecy Regions With Friendly Jamming. IEEE Trans. Inf. Forensics Secur. 2011, 6, 256–266. [Google Scholar] [CrossRef]
- Anand, S.A.; Saxena, N. Vibreaker: Securing vibrational pairing with deliberate acoustic noise. In Proceedings of the 9th ACM Conference on Security & Privacy in Wireless and Mobile Networks—WiSec 16, Darmstadt, Germany, 18–20 July 2016. [Google Scholar] [CrossRef]
- Michaels, A.J. A maximal entropy digital chaotic circuit. In Proceedings of the IEEE International Symposium of Circuits and Systems (ISCAS), Rio de Janeiro, Brazil, 15–18 May 2011; pp. 717–720. [Google Scholar]
- Michaels, A. Improved RNS-based PRNGs. In Proceedings of the 13th International Conference on Availability, Reliability and Security (ARES 2018), Hamburg, Germany, 27–30 August 2018. [Google Scholar]
- Ho, S.W. On the relation between the Shannon entropy and the von Neumann entropy. Master’s Thesis, The Chinese University of Hong Kong, Hong Kong, China, 2004; pp. 1–116. [Google Scholar]
- Zhang, F.; Ai, Y.; Liu, F. Typical Fault Mode Determination for Rotor Test Rig Based on Correlation Dimension and Kolmogorov Entropy. In Proceedings of the Sixth International Conference on Fuzzy Systems and Knowledge Discovery, Tianjin, China, 14–16 August 2009; pp. 484–488. [Google Scholar]
- Michaels, A.J.; Lau, C. Quantization Effects in Digital Chaotic Communication Systems. In Proceedings of the 2013 IEEE Military Communications Conference (MILCOM), San Diego, CA, USA, 18–20 November 2013; pp. 1564–1569. [Google Scholar]
- Fisher, R.A.; Yates, F. Statistical Tables for Biological, Agricultural and Medical Research, 3rd ed.; Oliver & Boyd: London, UK, 1938; pp. 26–27. [Google Scholar]
- Sattolo, S. An algorithm to generate a random cyclic permutation. Inf. Process. Lett. 1986, 22, 315–317. [Google Scholar] [CrossRef]




| Label | Description |
|---|---|
| mCRT | |
| Surjective mapping |
| l | CRT Output | |||
|---|---|---|---|---|
| 0 | 145 | 85 | 5 | |
| 1 | 141 | 3 | 3 | |
| 2 | 23 | 59 | 3 | |
| ⋮ | ⋮ | ⋮ | ⋮ | ⋮ |
| 163 | 27 | 141 | 5 | |
| 164 | 74 | 32 | 0 |
| n | |||||
|---|---|---|---|---|---|
| 3 | 11 | 132 | 1216 | 0.1 | ≈20.2 |
| 4 | 479 | 25,893 | ≈ | ||
| 16 | 1021 | 242,038 | ≈ | ||
| 24 | 2003 | 126,229 | ≈ |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Vennos, A.; George, K.; Michaels, A. Attacks and Defenses for Single-Stage Residue Number System PRNGs. IoT 2021, 2, 375-400. https://doi.org/10.3390/iot2030020
Vennos A, George K, Michaels A. Attacks and Defenses for Single-Stage Residue Number System PRNGs. IoT. 2021; 2(3):375-400. https://doi.org/10.3390/iot2030020
Chicago/Turabian StyleVennos, Amy, Kiernan George, and Alan Michaels. 2021. "Attacks and Defenses for Single-Stage Residue Number System PRNGs" IoT 2, no. 3: 375-400. https://doi.org/10.3390/iot2030020
APA StyleVennos, A., George, K., & Michaels, A. (2021). Attacks and Defenses for Single-Stage Residue Number System PRNGs. IoT, 2(3), 375-400. https://doi.org/10.3390/iot2030020








