Mitigating the Risk of Autonomous Weapon Misuse by Insurgent Groups
Abstract
1. Introduction
2. Background
2.1. How AI Transforms How Weapons Work
2.2. The Relevance of NSAGs
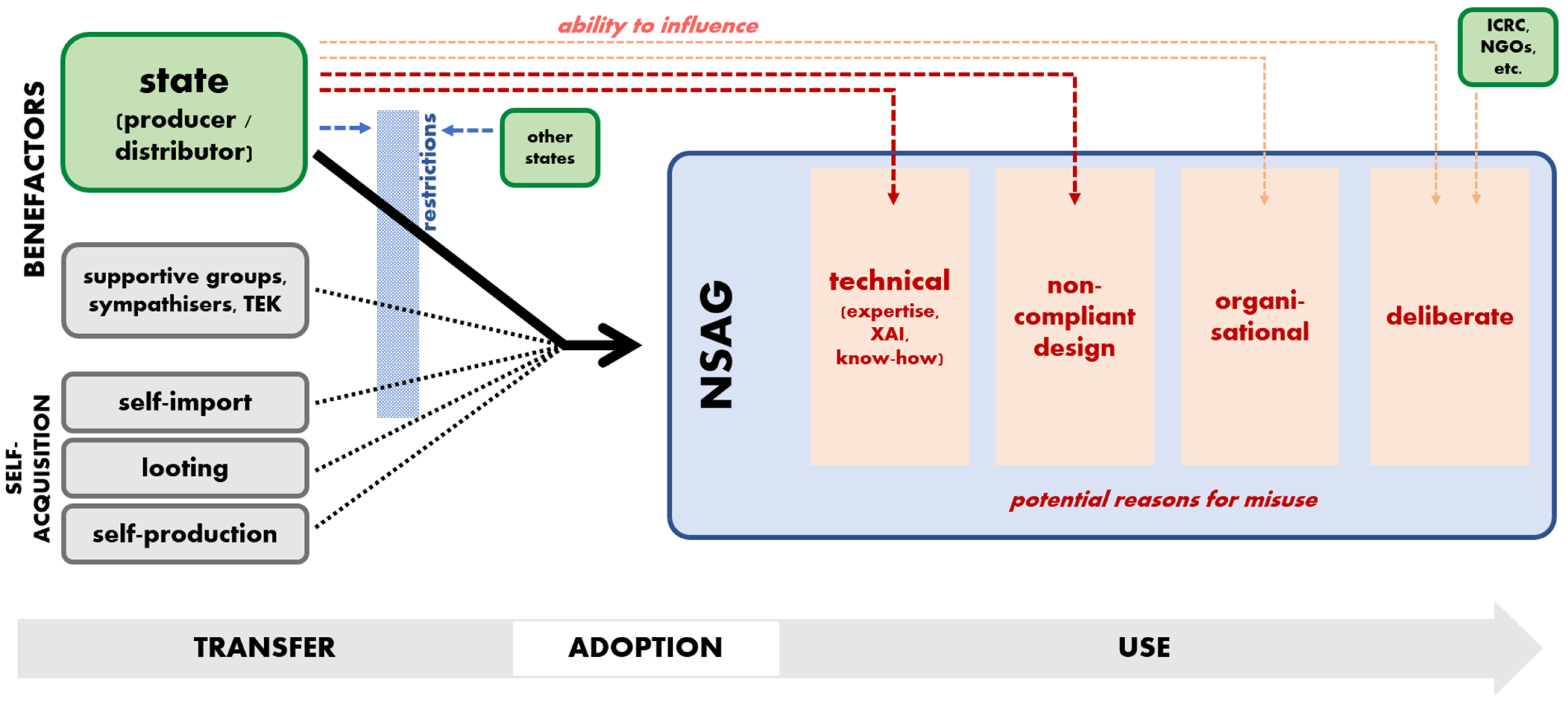
3. Acquisition Sources and Routes
3.1. Routes and Benefactors
3.2. Visibility and Movement
- Smart munitions and sensor-fused weapons (weapons that, after launch, search for a target signature and engage it) such as the BAE Bonus (BAE Systems 2020);
- Loitering systems (independent platforms which hover above a target area and search for a particular signature), such as the Harpy (Markoff 2014);
- Active protection and counter rocket, artillery and mortar systems, such as the Aegis and Goalkeeper (Scharre and Horowitz 2015);
- Anti-personnel perimeter defence, such as the South Korean SGR-A1 and South African Super aEgis II (Global Security 2017).
4. Reasons for Violations While in Use
4.1. Deliberate Misuse
4.2. Violation-Conducive Circumstances in the NSAG
4.3. Hand-Me-Down LOAC Non-compliant Weapons
4.4. Technical Reasons for Reckless Misuse
5. Focalising Responses
- AI reliability metrics (see, e.g., (Afonja 2017; Sharma 2019));
- The fact that AI are ‘narrow’ and can easily fail if deployed in environments for which they were not designed or tested (Yampolskiy 2020);
- That such failures are unintuitive; and
- The fact that systems may be opaque (thus potentially necessitating training in how to use XAI solutions) (Kwik and Van Engers 2021).
6. Closing Recommendations
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Additional Protocol I. 1977. Protocol Additional to the Geneva Conventions of 12 August 1949, and Relating to the Protection of Victims of International Armed Conflicts (adopted 8 June 1977, entered into force 7 December 1978) 1125 UNTS 3. Available online: https://www.ohchr.org/en/instruments-mechanisms/instruments/protocol-additional-geneva-conventions-12-august-1949-and (accessed on 27 November 2022).
- Additional Protocol II. 1977. Protocol Additional to the Geneva Conventions of 12 August 1949, and Relating to the Protection of Victims of Non-International Armed Conflicts. Geneva: GGE LAWS. [Google Scholar]
- Afonja, Tejumade. 2017. Accuracy Paradox. Available online: https://towardsdatascience.com/accuracy-paradox-897a69e2dd9b (accessed on 15 October 2021).
- Ahronheim, Anna. 2019. India to Buy 15 Harop Suicide Drones from Israel. Available online: https://www.jpost.com/israel-news/india-to-buy-15-harop-suicide-drones-from-israel-578947 (accessed on 21 July 2021).
- Arasli, Jahangir. 2011. States vs. Non-State Actors: Asymmetric Conflict of the 21st Century and Challenges to Military Transformation. Dubai: INEGMA. Available online: http://inegma.com/Admin/Content/File-81020131379.pdf (accessed on 10 October 2022).
- Arms Trade Treaty. 2013. Arms Trade Treaty (adopted 2 April 2013, entered into force 24 December 2014, New York) UNTS 3013. Available online: https://www.un.org/disarmament/convarms/arms-trade-treaty-2/ (accessed on 22 December 2022).
- Arya, Vijay, Rachel K. E. Bellamy, Pin-Yu Chen, Amit Dhurandhar, Michael Hind, Samuel C. Hoffman, Stephanie Houde, Q. Vera Liao, Ronny Luss, Aleksandra Mojsilović, and et al. 2019. September One Explanation Does Not Fit All: A Toolkit and Taxonomy of AI Explainability Techniques. arXiv arXiv:1909.03012. [Google Scholar]
- Atadjanov, Rustam B. 2011. Ensuring Compliance of Non-State Actors with Rules of International Humanitarian Law on the Use of Weapons in NIAC: A Way to Follow. Asia-Pacific Yearbook of International Humanitarian Law 4: 140–82. [Google Scholar]
- BAE Systems. 2020. Bofors 155 mm BONUS Munition. Available online: https://www.baesystems.com/en-us/product/155-bonus (accessed on 25 June 2020).
- Bakke, Kristin M. 2013. Copying and learning from outsiders? Assessing diffusion from transnational insurgents in the Chechen wars. In Transnational Dynamics of Civil War. Edited by Jeffrey T. Checkel. Cambridge: Cambridge University Press, pp. 31–62. [Google Scholar]
- Barredo Arrieta, Alejandro, Natalia Díaz-Rodríguez, Javier Del Ser, Adrien Bennetot, Siham Tabik, Alberto Barbado, Salvador Garcia, Sergio Gil-Lopez, Daniel Molina, Richard Benjamins, and et al. 2020. Explainable Artificial Intelligence (XAI): Concepts, taxonomies, opportunities and challenges toward responsible AI. Information Fusion 58: 82–115. [Google Scholar]
- Bartels, Rogier. 2018. When Do Terrorist Organisations Qualify as “Parties to an Armed Conflict” Under International Humanitarian Law? Revue de droit militaire et de droit de la guerre 56: 451–88. [Google Scholar] [CrossRef]
- Bassiouni, M. Cherif. 2008. The New Wars and the Crisis of Compliance with the Law of Anned Conflict by Non-State Actors. Journal of Criminal Law & Criminology 98: 711. [Google Scholar]
- Bellal, Annyssa. 2016. Welcome on Board: Improving Respect for International Humanitarian Law Through the Engagement of Armed Non-State Actors. In Yearbook of International Humanitarian Law 2016—Volume 19. Edited by T. D. Gill. The Hague: T.M.C. Asser Press. [Google Scholar]
- Blake, Duncan, and Joseph S. Imburgia. 2010. Bloodless weapons? The need to conduct legal reviews of certain weapons and the implications of defining them as ‘weapons’. Air Force Law Review 66: 157–204. [Google Scholar]
- Blanton, Shannon Lindsey. 1999. Instruments of Security or Tools of Repression? Arms Imports and Human Rights Conditions in Developing Countries. Journal of Peace Research 36: 233–44. [Google Scholar] [CrossRef]
- Boddens Hosang, J. F. R. 2021. Control Through ROE in Military Operations: Autonomous Weapons and Cyber Operations as Reasons to Change the Classic ROE Concept? In Military Operations and the Notion of Control under International Law. Edited by Rogier Bartels, Jeroen C. van den Boogaard, Paul A. L. Ducheine, Eric Pouw and Joop Voetelink. Berlin: Springer, pp. 393–420. [Google Scholar]
- Boothby, William H. 2016. Weapons and the Law of Armed Conflict, 2nd ed. Oxford: Oxford University Press. [Google Scholar]
- Boulanin, Vincent. 2016. Mapping the Development of Autonomy in Weapon Systems: A Primer on Autonomy. Stockholm: Stockholm International Peace Research Institute. [Google Scholar]
- Boulanin, Vincent, Netta Goussac, Laura Bruun, and Luke Richards. 2020. Responsible Military Use of Artificial Intelligence: Can the European Union Lead the Way in Developing Best Practice? Stockholm: SIPRI. [Google Scholar]
- Brownlee, Jason. 2020. Difference between Algorithm and Model in Machine Learning. Available online: https://machinelearningmastery.com/difference-between-algorithm-and-model-in-machine-learning/ (accessed on 7 November 2020).
- Buhaug, Halvard, Scott Gates, and Päivi Lujala. 2009. Geography, Rebel Capability, and the Duration of Civil Conflict. Journal of Conflict Resolution 53: 544–69. [Google Scholar] [CrossRef]
- Byman, Daniel, Peter Chalk, Bruce Hoffman, William Rosenau, and David Brannan. 2001. Trends in Outside Support for Insurgent Movements. Santa Monica: RAND Corporation. [Google Scholar]
- Capie, David. 2004. Armed Groups, Weapons Availability and Misuse: An Overview of the Issues and Options for Action, Background Paper for a Meeting Organized by the Centre for Humanitarian Dialogue, in Advance of the Sixth Meeting of the Human Security Network. Available online: https://gsdrc.org/document-library/armed-groups-weapons-availability-and-misuse-an-overview-of-these-and-options-for-action/ (accessed on 25 May 2004).
- Cederman, Lars-Erik, Kristian Skrede Gleditsch, and Halvard Buhaug. 2013. Inequality, Grievances, and Civil War. Cambridge: Cambridge University Press. [Google Scholar]
- Chairman of the US Joint Chiefs of Staff. 2012. Instruction—No Strike Policy and Collateral Damage Estimation. Washington, DC: The Joint Staff. [Google Scholar]
- Clapham, Andrew, Stuart Casey-Maslen, Gilles Giacca, and Sarah Parker. 2016. The Arms Trade Treaty: A Commentary. Oxford: Oxford University Press. [Google Scholar]
- Cragin, Kim, Peter Chalk, Sara A. Daly, and Brian A. Jackson. 2007. Sharing the Dragon’s Teeth. Terrorist Groups and the Exchange of New Technologies. Santa Monica: Rand Corporation. [Google Scholar]
- Cummings, M. L. 2018. Artificial intelligence and the future of warfare. In Artificial Intelligence and International Affairs: Disruption Anticipated. Edited by M. L. Cummings, Heather M. Roff, Kenneth Cukier, Jacob Parakilas and Hannah Bryce. London: Chatham House, pp. 7–18. [Google Scholar]
- Curtis E. Lemay Center. 2019. Air Force Doctrine Publication 3-60—Targeting. Montgomery: Curtis E. Lemay Center. [Google Scholar]
- Dailymail. 2017. Vladimir Putin Warns Whoever Cracks Artificial Intelligence will ’Rule the World’. Available online: www.dailymail.co.uk/sciencetech/article-4844322/Putin-Leader-artificial-intelligence-rule-world.html (accessed on 13 May 2020.).
- Daoust, Isabelle, Robin Coupland, and Rikke Ishoey. 2002. New wars, new weapons?: The obligation of States to assess the legality of means and methods of warfare. International Review of the Red Cross 84: 345–62. [Google Scholar] [CrossRef]
- Davison, Neil. 2017. A Legal Pperspective: Autonomous Weapon Systems under International Humanitarian Law. UNODA Occasional Papers No. 30. Available online: https://www.icrc.org/en/document/autonomous-weapon-systems-under-international-humanitarian-law (accessed on 27 November 2022).
- Defense Innovation Board. 2019. AI Principles: Recommendations on the Ethical Use of Artificial Intelligence by the Department of Defense Defense Innovation Board. Washington, DC: Department of Defense. [Google Scholar]
- Defense Science Board. 2012. The Role Of Autonomy in DoD Systems. Washington, DC: Department of Defense. [Google Scholar]
- Dharia, Saumil P. 2019. Dangerous Weapons: Arms Transfer, Interstate Conflict, and Dependence. Ph.D. thesis, University of Missouri-Columbia, Columbia, MO, USA. [Google Scholar]
- DoD Defense Science Board. 2016. Report of the Defense Science Board Summer Study on Autonomy. Washington, DC: Secretary of Defense for Acquisition, Technology and Logistics. [Google Scholar]
- Dunlap, Charles J. 2016. No Good Options against ISIS Barbarism? Human Shields in 21st Century Conflicts. AJIL Unbound 110: 311–16. [Google Scholar] [CrossRef]
- Duquet, Nils. 2009. Arms Acquisition Patterns and the Dynamics of Armed Conflict: Lessons from the Niger Delta. International Studies Perspectives 10: 169–85. [Google Scholar] [CrossRef]
- Durhin, Nathalie. 2016. Protecting civilians in urban areas: A military perspective on the application of international humanitarian law. International Review of the Red Cross 98: 177–200. [Google Scholar] [CrossRef]
- Eklund, Amanda Musco. 2020. Meaningful Human Control of Autonomous Weapon Systems: Definitions and Key Elements in the Light of International Humanitarian Law and International Human Rights Law. Stockholm: Totalförsvarets Forskningsinstitut. [Google Scholar]
- Erlanger, Steven, and Richard A. Oppel, Jr. 2006. A Disciplined Hezbollah Surprises Israel with Its Training, Tactics and Weapons. Available online: https://www.nytimes.com/2006/08/07/world/middleeast/07hezbollah.html (accessed on 8 October 2020).
- European Council. 2008. Council Common Position 2008/944/CFSP of 8 December 2008 Defining Common Rules Governing Control of Exports of Military Technology and Equipment. Official Journal of the European Union. OJ L 335. pp. 99–103. Available online: https://eur-lex.europa.eu/LexUriServ/LexUriServ.do?uri=OJ:L:2008:335:0099:0103:en:PDF (accessed on 10 October 2022).
- European Parliament. 2014. European Parliament Resolution of 27 February 2014 on the Use of Armed Drones. Available online: https://www.asil.org/blogs/european-parliament-passes-resolution-use-armed-drones-february-25-2014 (accessed on 10 October 2022).
- European Parliament. 2018. Resolution of 12 September 2018 on Autonomous Weapon Systems. Available online: https://op.europa.eu/en/publication-detail/-/publication/b1d51a34-256c-11ea-af81-01aa75ed71a1/language-en (accessed on 11 March 2020).
- European Parliament. 2020. Decision of 18 June 2020 on Setting Up a Special Committee on Artificial Intelligence in a Digital Age, and Defining Its Responsibilities, Numerical Strength and Term of Office. Available online: https://www.medialaws.eu/decision-on-setting-up-a-special-committee-on-artificial-intelligence-in-a-digital-age-and-defining-its-responsibilities-numerical-strength-and-term-of-office/ (accessed on 10 October 2022).
- Fleming, Nic. 2009. Campaign Asks for International Treaty to Limit War Robots. Available online: https://www.newscientist.com/article/dn17887-campaign-asks-for-international-treaty-to-limit-war-robots/ (accessed on 10 October 2022).
- Fornasier, Mateus De Oliveira. 2021. The Regulation of the Use of Artificial Intelligence (AI) in Warfare: Between International Humanitarian Law (IHL) and Meaningful Human Control. Revista Jurídica da Presidência 23: 67. [Google Scholar] [CrossRef]
- Fry, James D. 2006. Contextualized Legal Reviews for the Methods and Means of Warfare: Cave Combat and International Humanitarian Law. Columbia Journal of Transnational Law 44: 453–519. [Google Scholar]
- Gao, Charlotte. 2017. China Vows to Become an Artificial Intelligence World Leader. Available online: https://thediplomat.com/2017/07/china-vows-to-become-an-artificial-intelligence-world-leader/ (accessed on 25 October 2020).
- Garcia, Denise. 2014. ICRAC Statement on Technical Issues to the 2014 UN CCW Expert Meeting, International Committee for Robot Arms Control; ICRAC. Available online: https://www.icrac.net/icrac-statement-on-technical-issues-to-the-2014-un-ccw-expert-meeting (accessed on 30 May 2020).
- Geneva Convention IV. 1949. Geneva Convention Relative to the Protection of Civilian Persons in Time of War (adopted 12 August 1949, entered into force 21 October 1950) 75 UNTS 287. Available online: https://www.ohchr.org/en/instruments-mechanisms/instruments/geneva-convention-relative-protection-civilian-persons-time-war (accessed on 22 December 2022).
- Gettinger, Dan, and Holland Michel Arthur. 2017. Loitering Munitions: In Focus. New York: Center for the Study of the Drone at Bard College. [Google Scholar]
- Gleditsch, Kristian Skrede, and Idean Salehyan. 2006. Refugees and the Spread of Civil War. International Organization 60: 335–66. [Google Scholar]
- Global Security. 2017. Samsung Techwin SGR-A1 Sentry Guard Robot. Available online: https://www.globalsecurity.org/military/world/rok/sgr-a1.htm (accessed on 14 May 2017).
- Grauer, Ryan, and Dominic Tierney. 2018. The Arsenal of Insurrection: Explaining Rising Support for Rebels. Security Studies 27: 263–95. [Google Scholar] [CrossRef]
- GGE LAWS. 2019. Draft Report of the 2019 Session of the Group of Governmental Experts on Emerging Technologies in the Area of Lethal Autonomous Weapons System. Geneva: GGE LAWS. [Google Scholar]
- Hamberg, Stephan. 2013. Transnational advocacy networks, rebel groups, and demobilization of child soldiers in Sudan. In Transnational Dynamics of Civil War. Edited by Jeffrey T. Checkel. Cambridge: Cambridge University Press, pp. 149–72. [Google Scholar]
- Harbom, Lotta, and Peter Wallensteen. 2005. Armed Conflict and its International Dimensions, 1946–2004. Journal of Peace Research 42: 623–37. [Google Scholar] [CrossRef]
- Haugh, Brian A., David A. Sparrow, and David M. Tate. 2018. The Status of Test, Evaluation, Verification, and Validation (TEV&V) of Autonomous Systems. Alexandria: Institute for Defense Analyses. [Google Scholar]
- Hazen, Jennifer M. 2013. What Rebels Want: Resources and Supply Networks in Wartime. New York: Cornell University Press. [Google Scholar]
- Heffes, Ezequiel. 2013. The Responsibility of Armed Opposition Groups for Violations of International Humanitarian Law: Challenging the State-Centric System of International Law. Journal of International Humanitarian Legal Studies 4: 81–107. [Google Scholar] [CrossRef]
- Heyns, Christof. 2013. Report of the Special Rapporteur on Extrajudicial, Summary or Arbitrary Executions. Rome: United Nations. [Google Scholar]
- Holland Michel, Arthur. 2020. The Black Box, Unlocked: Predictability and Understandability in Military AI. Geneva: UNIDIR. [Google Scholar]
- Holtom, Paul, Mark Bromley, and Verena Simmel. 2012. Measuring International Arms Transfers. Solna: SIPRI. Available online: https://www.sipri.org/sites/default/files/files/FS/SIPRIFS1212.pdf (accessed on 10 October 2022).
- Horizon 2020 Commission Expert Group. 2020. Ethics of Connected and Automated Vehicles: Recommendations on Road Safety, Privacy, Fairness, Explainability and Responsibility. Luxembourg: Publication Office of the European Union. [Google Scholar]
- Human Rights Watch. 2012. Losing Humanity: The Case against Killer Robots. New York: Human Rights Watch. Available online: https://www.hrw.org/report/2012/11/19/losing-humanity/case-against-killer-robots (accessed on 10 October 2022).
- Human Rights Watch. 2020. Killer Robots: Growing Support for a Ban. Available online: https://www.hrw.org/news/2020/08/10/killer-robots-growing-support-ban (accessed on 15 February 2022).
- Independent High-Level Expert Group on Artificial Intelligence. 2019. A Definition of AI: Main Capabilities and Disciplines. Brussels: European Commission. [Google Scholar]
- ICRC. 1999. Arms Availability and the Situation of Civilians in Armed Conflict. Geneva: ICRC. [Google Scholar]
- ICRC. 2006. A Guide to the Legal Review of New Weapons, Means and Methods of Warfare: Measures to Implement Article 36 of Additional Protocol I of 1977. Geneva: ICRC. [Google Scholar]
- ICRC. 2013. Autonomous Weapons: States Must Address Major Humanitarian, Ethical Challenges. Versoix: ICRC. [Google Scholar]
- ICRC. 2014. What Is International Humanitarian Law?—Advisory Service on International Humanitarian Law. Versoix: ICRC. [Google Scholar]
- ICRC. 2016. Background paper prepared by the International Committee of the Red Cross. In Autonomous Weapon Systems: Implications of Increasing Autonomy in the Critical Functions of Weapons. Versoix: ICRC, pp. 69–85. [Google Scholar]
- ICRC. 2018a. Ethics and Autonomous Weapon Systems: An Ethical Basis for Human Control? Versoix: ICRC. [Google Scholar]
- ICRC. 2018b. The Roots of Restraint in War. Versoix: ICRC. [Google Scholar]
- International Court of Justice. 1986. Case Concerning Military and Paramilitary Activities In and Against Nicaragua (Nicaragua v. United States of America). Available online: https://iilj.org/wp-content/uploads/2016/08/Case-Concerning-Military-and-Paramilitary-Activities-In-and-Against-Nicaragua-Nicaragua-v.-United-States.pdf (accessed on 10 October 2022).
- ICTY. 1995. Prosecutor v Tadić, Decision on the Defence Motion for Interlocutory Appeal on Jurisdiction, 2 October 1995. Available online: https://www.icty.org/x/cases/tadic/acdec/en/51002.htm (accessed on 10 October 2022).
- International Law Commission. 2001. Draft Articles on Responsibility of States for Internationally Wrongful Acts. Available online: https://www.cambridge.org/core/books/abs/world-bank-group-the-imf-and-human-rights/draft-articles-on-the-responsibility-of-states-for-internationally-wrongful-acts-2001-excerpts/4431269ADCFB24B9536621F413991D4C (accessed on 27 November 2022).
- Israel Defence Force. 2019. Hezbollah’s Precision Guided Missile Project. Available online: https://www.idf.il/en/mini-sites/hezbollah/hezbollah-s-precision-guided-missile-project/ (accessed on 10 October 2022).
- Jackson, Thomas. 2011. From under Their Noses: Rebel Groups’ Arms Acquisition and the Importance of Leakages from State Stockpiles. International Studies Perspectives 11: 131–47. [Google Scholar] [CrossRef]
- Jamnejad, Maziar, and Michael Wood. 2009. The Principle of Non-intervention. Leiden Journal of International Law 22: 345–81. [Google Scholar] [CrossRef]
- Jensen, Eric Talbot. 2020. The (Erroneous) Requirement for Human Judgment (and Error) in the Law of Armed Conflict. SSRN Electronic Journal 96: 26–57. [Google Scholar] [CrossRef]
- Jevglevskaja, Natalia. 2018. Weapons Review Obligation under Customary International Law. International Law Studies 94: 186. [Google Scholar]
- Kalyvas, Stathis, and Laia Balcells. 2010. International System and Technologies of Rebellion: How the End of the Cold War Shaped Internal Conflict. American Political Science Review 104: 415–29. [Google Scholar] [CrossRef]
- Kleffner, Jann K. 2007. From ‘Belligerents’ to ‘Fighters’ and Civilians Directly Participating in Hostilities—On The Principle of Distinction in Non-International Armed Conflicts One Hundred Years After the Second Hague Peace Conference. Netherlands International Law Review 54: 315. [Google Scholar] [CrossRef]
- Kwik, Jonathan, and Tom Van Engers. 2021. Algorithmic fog of war: When lack of transparency violates the law of armed conflict. Journal of Future Robot Life 2: 43–66. [Google Scholar] [CrossRef]
- Lawand, Kathleen. 2006. Reviewing the legality of new weapons, means and methods of warfare. International Review of the Red Cross 88: 925–30. [Google Scholar] [CrossRef][Green Version]
- Levine, Paul, Somnath Sen, and Ron Smith. 1994. A model of the international arms market. Defence and Peace Economics 5: 1–18. [Google Scholar] [CrossRef]
- Lewis, John. 2015. The Case for Regulating Fully Autonomous Weapons. Yale Law Journal 124: 1309–25. [Google Scholar]
- Li, Qiang, and Dan Xie. 2019. Legal Regulation of AI Weapons under International Humanitarian Law: A Chinese Perspective. Available online: https://blogs.icrc.org/law-and-policy/2019/05/02/ai-weapon-ihl-legal-regulation-chinese-perspective/ (accessed on 26 May 2021).
- Longobardo, Marco. 2019. Training and Education of Armed Forces in the Age of High-Tech Hostilities. In Use and Misuse of New Technologies. Edited by Elena Carpanelli and Nicole Lazzerini. Cham: Springer International Publishing, pp. 73–91. [Google Scholar]
- Markoff, John. 2014. Fearing Bombs That Can Pick Whom to Kill. Available online: https://www.nytimes.com/2014/11/12/science/weapons-directed-by-robots-not-humans-raise-ethical-questions.html (accessed on 9 June 2021).
- Marks, Joshua. 2007. Border in Name Only: Arms Trafficking and Armed Groups at the DRC–Sudan Border. Geneva: Small Arms Survey. [Google Scholar]
- Marsh, Nicholas. 2007. Conflict Specific Capital: The Role of Weapons Acquisition in Civil War. International Studies Perspectives 8: 54–72. [Google Scholar] [CrossRef]
- Marsh, Nicholas. 2019. Preventing Diversion: A Challenge for Arms Trade Treaty States Parties. History of Global Arms Transfer 8: 55–66. [Google Scholar]
- McAllister, Amanda. 2018. Stranger than science fiction: The rise of A.I. interrogation in the dawn of autonomous robots and the need for an additional protocol to the U.N. convention against torture. Minnesota Law Review 101: 2527–73. [Google Scholar]
- Meier, Michael W. 2019. Lethal Autonomous Weapons Systems. In Complex Battlespaces. Edited by Winston S. Williams and Christopher M. Ford. Oxford: Oxford University Press, pp. 289–316. [Google Scholar]
- Ministère des Armées France. 2019. L’intelligence Artificielle au Service de la Défense. Paris: Ministère des Armées. [Google Scholar]
- Molnar, Cristoph. 2019. Interpretable Machine Learning: A Guide for Making Black Box Models Explainable. Victoria: Lean Publishing. Available online: https://christophm.github.io/interpretable-ml-book/ (accessed on 21 February 2019).
- Moore, Matthew. 2012. Selling to Both Sides: The Effects of Major Conventional Weapons Transfers on Civil War Severity and Duration. International Interactions 38: 325–47. [Google Scholar] [CrossRef]
- North Atlantic Treaty Organisation. 2016. Allied Joint Doctrine for Joint Targeting. Available online: https://www.gov.uk/government/publications/allied-joint-doctrine-for-joint-targeting-ajp-39a (accessed on 10 October 2022).
- Pamp, Oliver, Lukas Rudolph, Paul W. Thurner, Andreas Mehltretter, and Simon Primus. 2018. The build-up of coercive capacities. Journal of Peace Research 55: 430–44. [Google Scholar] [CrossRef]
- Parks, W. Hays. 2005. Conventional Weapons and Weapons Reviews. Yearbook of International Humanitarian Law 8: 55–142. [Google Scholar] [CrossRef]
- Pejić, Jelena. 2011. The Protective Scope of Common Article 3: More than Meets the Eye. International Review of the Red Cross 881: 189. [Google Scholar] [CrossRef]
- Peters, Ralph. 1994. The New Warrior Class. US Army War College Quarterly: Parameters 24: 29. [Google Scholar] [CrossRef]
- Prigg, Mark. 2016. UN to Debate ’Killer Robot’ Ban next Year as Experts Warn Time Is Running out to Stop AI Weapons. Available online: https://www.dailymail.co.uk/sciencetech/article-4042146/UN-debate-killer-robot-ban-year-experts-warn-time-running-stop-AI-weapons.html (accessed on 6 July 2017).
- Reynolds, Jefferson D. 2005. Collateral Damage on the 21st Century Battlefield: Enemy Exploitation of the Law of Armed Conflict, and the Struggle for a Moral High Ground. Air Force Law Review 56: 1–108. [Google Scholar]
- Ribeiro, Marco Tulio, Sameer Singh, and Carlos Guestrin. 2016. Why Should I Trust You?: Explaining the Predictions of Any Classifier. Paper presented at the 22nd ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, San Francisco, CA, USA, August 13–17; pp. 1135–1144. [Google Scholar]
- Righetti, Ludovic. 2016. Emerging technology and future autonomous weapons. In Autonomous Weapon Systems: Implications of Increasing Autonomy in the Critical Functions of Weapons. Versoix: ICRC, pp. 36–39. [Google Scholar]
- Roff, Heather. 2016. Sensor-fused munitions, missiles and loitering munitions. In Implications of Increasing Autonomy in the Critical Functions of Weapons. Versoix: ICRC, pp. 33–35. [Google Scholar]
- Roscini, Marco. 2014. Cyber Operations and the Use of Force in International Law. Oxford: Oxford University Press. [Google Scholar]
- Roy, Anna. 2018. National Strategy for Artificial Intelligence #AIFORALL. New Delhi: National Institution for Transforming India Aayog. [Google Scholar]
- Russell, Stuart J., and Peter Norvig. 2010. Artificial Intelligence: A Modern Approach, 3rd ed. New Jersey: Pearson. [Google Scholar]
- Ruys, T. 2014. Of Arms, Funding and “Non-lethal Assistance”–Issues Surrounding Third-State Intervention in the Syrian Civil War. Chinese Journal of International Law 13: 13–53. [Google Scholar] [CrossRef][Green Version]
- Safi, Michael. 2019. Are Drone Swarms the Future of Aerial Warfare? Available online: https://www.militaryaerospace.com/commercial-aerospace/article/14230840/drone-swarms-aerial-warfare (accessed on 1 October 2021).
- Samek, Wojciech, and Klaus-Robert Müller. 2019. Towards Explainable Artificial Intelligence. In Explainable AI: Interpreting, Explaining and Visualizing Deep Learning. Edited by Wojciech Samek, Grégoire Montavon, Andrea Vedaldi, Lars Kai Hansen and Klaus-Robert Müller. Cham: Springer Nature Switzerland, pp. 5–22. [Google Scholar]
- Sandoz, Yves, Christophe Swinarski, and Bruno Zimmerman. 1987. Commentary on the Additional Protocols of 8 June 1977 to the Geneva Conventions of 12 August 1949. Geneva: Martinus Nijhoff. [Google Scholar]
- Santoni de Sio, Filippo, and Jeroen van den Hoven. 2018. Meaningful Human Control over Autonomous Systems: A Philosophical Account. Frontiers in Robotics and AI 5. [Google Scholar] [CrossRef]
- Sartor, Giovanni, and Andrea Omicini. 2016. The autonomy of technological systems and responsibilities for their use. In Autonomous Weapons Systems: Law, Ethics, Policy. Edited by Nehal Bhuta, Susanne Beck, Robin Geis, Hin-yan Liu and Claus KREß. Cambridge: Cambridge University Press, pp. 39–74. [Google Scholar]
- Sassòli, Marco. 2008. Engaging Non-State Actors: The New Frontier for International Humanitarian Law. In Exploring Criteria & Conditions for Engaging Armed Non-State Actors to Respect Humanitarian Law and Human Rights Law. Geneva: UNIDIR, pp. 8–12. [Google Scholar]
- Sassòli, Marco. 2022. How will international humanitarian law develop in the future? International Review of the Red Cross 104: 2052–76. [Google Scholar] [CrossRef]
- Saul, Ben. 2017. Enhancing Civilian Protection by Engaging Non-State Armed Groups under International Humanitarian Law. Journal of Conflict and Security Law 22: 39–66. [Google Scholar] [CrossRef]
- Scharre, Paul, and Michael C. Horowitz. 2015. An Introduction to Autonomy in Weapon Systems. Washington, DC: Center for a New American Security. [Google Scholar]
- Scharre, Paul D. 2011. Why unmanned. Joint Force Quarterly 61: 92. [Google Scholar]
- Scharre, Paul D. 2018. Army of None: Autonomous Weapons and the Future of War. New York: Ww Norton & Co. [Google Scholar]
- Scherer, Matthew U. 2016. Regulating Artificial Intelligence Systems: Risks, Challenges, Competencies, and Strategies. Harvard Journal of Law & Technology 29: 353–400. [Google Scholar]
- Schmitt, Michael N., ed. 2017. Tallinn Manual 2.0 on the International Law Applicable to Cyber Warfare. Cambridge: Cambridge University Press. [Google Scholar]
- Schmitt, Michael N., and Jeffrey S. Thurnher. 2013. “Out of the Loop”: Autonomous Weapon Systems and the Law of Armed Conflict. Harvard Law School National Security Journal 4: 231–81. [Google Scholar]
- Schuller, Alan. 2017. At the Crossroads of Control: The Intersection of Artificial Intelligence in Autonomous Weapon Systems with International Humanitarian Law. Harvard National Security Journal 8: 379. [Google Scholar]
- Sharma, Prateek. 2019. Decoding the Confusion Matrix. Available online: https://keytodatascience.com/confusion-matrix/ (accessed on 15 October 2021).
- SIPRI. 1994. SIPRI Yearbook 1994. Oxford: Oxford University Press. [Google Scholar]
- SIPRI. 2002. SIPRI Yearbook 2002: Armaments, Disarmament and International Security. Oxford: Oxford University Press. [Google Scholar]
- SIPRI. 2017. Literature review for the Policy and Operations Evaluations Department of the Dutch Ministry of Foreign Affairs, Final Report. Solna: SIPRI. [Google Scholar]
- SIPRI. 2020. SIPRI Arms Transfers Database—Methodology. Solna: SIPRI. [Google Scholar]
- Sivakumaran, Sandesh. 2006. Binding Armed Opposition Groups. International and Comparative Law Quarterly 55: 369–94. [Google Scholar] [CrossRef]
- Smith, Ron P., and Ali Tasiran. 2005. The Demand for Arms Imports. Journal of Peace Research 42: 167–81. [Google Scholar] [CrossRef]
- Special Court for Sierra Leone. 2004. Prosecutor v. Sam Hinga Norman (Decision on Preliminary Motion Based on Lack of Jurisdiction). Available online: https://sierralii.gov.sl/sl/judgment/special-court-sierra-leone/2004/18 (accessed on 10 October 2022).
- Stewart, Darren. 2017. Protecting Civilians during Urban Warfare. Challenges from Recent Conflict and Future Prospects. Available online: https://www.icrc.org/en/what-we-do/war-in-cities (accessed on 10 October 2022).
- Stop Autonomous Weapons. 2017. Slaughterbots. Available online: https://www.youtube.com/watch?v=9CO6M2HsoIA (accessed on 2 June 2021).
- Stürchler, Nikolas, and Michael Siegrist. 2017. A “Compliance-Based” Approach to Autonomous Weapon Systems. Available online: https://www.ejiltalk.org/a-compliance-based-approach-to-autonomous-weapon-systems/ (accessed on 7 June 2021).
- Thorne, John G. 2020. Warriors and War Algorithms: Leveraging Artificial Intelligence to Enable Ethical Targeting. Newport: Naval War College. [Google Scholar]
- Thurner, Paul W., Christian S. Schmid, Skyler J. Cranmer, and Göran Kauermann. 2019. Network Interdependencies and the Evolution of the International Arms Trade. Journal of Conflict Resolution 63: 1736–64. [Google Scholar] [CrossRef]
- Thurnher, Jeffrey S. 2014. Examining Autonomous Weapon Systems from a Law of Armed Conflict Perspective. In New Technologies and the Law of Armed Conflict. Edited by Hitoshi Nasu and Robert McLaughlin. The Hague: T.M.C. Asser Press, pp. 213–28. [Google Scholar]
- Thurnher, Jeffry S. 2018. Feasible Precautions in Attack and Autonomous Weapons. In Dehumanization of Warfare: Legal Implications of New Weapon Technologies. Edited by Wolff Heintschel von Heinegg, Robert Frau and Tassilo Singer. New York: Springer International Publishing AG, pp. 99–117. [Google Scholar]
- Trusilo, Daniel, and Thomas Burri. 2021. Ethical Artificial Intelligence: An Approach to Evaluating Disembodied Autonomous Systems. In Autonomous Cyber Capabilities under International Law. Edited by Rain Liivoja and Ann Väljataga. Tallinn: NATO CCDCOE Publications, pp. 51–66. [Google Scholar]
- UK Ministry of Defence. 2011. The UK Approach to Unmanned Aircraft Systems. London: United Kingdom Ministry of Defence. [Google Scholar]
- UK Mission Geneva. 2019. Statement at Meeting of Group of Governmental Experts on Emerging Technologies in the Area of Lethal Autonomous Weapons Systems, 25–29 March 2019. Geneva: GGE LAWS. [Google Scholar]
- UN Security Council. 2010. Report of the Secretary-General on the Protection of Civilians in Armed Conflict. Available online: https://reliefweb.int/report/world/report-secretary-general-protection-civilians-armed-conflict-s2022381-enarruzh (accessed on 10 October 2022).
- United Kingdom. 2020. Expert Paper: The Human Role in Autonomous Warfare, Group of Governmental Experts on Emerging Technologies in the Area of Lethal Autonomous Weapons System Geneva, 21–25 September 2020 and 2–6 November 2020, Agenda Item 5. Available online: https://geneva.usmission.gov/2020/09/30/group-of-governmental-experts-on-lethal-autonomous-weapons-systems-laws-agenda-item-5b/ (accessed on 10 October 2022).
- United Nations. 1997. Report of the Panel of Governmental Experts on Small Arms. Available online: https://www.un-ilibrary.org/content/books/9789210584913c001 (accessed on 10 October 2022).
- United Nations. 1999. Small Arms: Report of the Secretary-General. Available online: https://www.un.org/disarmament/convarms/salw/small-arms-related-reports-of-the-secretary-general/ (accessed on 10 October 2022).
- United States Air Force. 2009. Unmanned Aircraft Systems Flight Plan. Available online: https://ntrl.ntis.gov/NTRL/dashboard/searchResults/titleDetail/ADA505168.xhtml (accessed on 10 October 2022).
- U.S. Air Force Office of the Chief Scientist. 2015. Autonomous Horizons: System Autonomy in the Air Force— A Path to the Future, Volume I: Human-Autonomy Teaming. Available online: https://www.af.mil/Portals/1/documents/SECAF/AutonomousHorizons.pdf (accessed on 10 October 2022).
- Van Creveld, Martin. 1999. The Rise and Decline of the State. Cambridge: Cambridge University Press. [Google Scholar]
- Vignard, Kersten. 2014. The Weaponization of Increasingly Autonomous Technologies: Considering How Meaningful Human Control Might Move Discussion Forward. Geneva: UNIDIR. [Google Scholar]
- Waszink, Camilla. 2011. Protection of Civilians under International Humanitarian Law: Trends and Challenges. Oslo: Norwegian Peacebuilding Resource Centre. [Google Scholar]
- Weaver, Oliver. 2021. Inheritance of loss: The weapons left behind for the Taliban in Afghanistan. Available online: https://aoav.org.uk/2021/inheritance-of-loss-the-weapons-left-behind-for-the-taliban-in-afghanistan/ (accessed on 21 December 2022).
- Wezeman, Pieter D. 2002. Conflicts and Transfers of Small Arms. Stockholm: SIPRI. [Google Scholar]
- Wittes, Benjamin. 2012. Does Human Rights Watch Prefer Disproportionate and Indiscriminate Humans to Discriminating and Proportionate Robots? Available online: https://www.lawfareblog.com/does-human-rights-watch-prefer-disproportionate-and-indiscriminate-humans-discriminating-and (accessed on 24 June 2021).
- Wood, Elisabeth Jean. 2008. The Social Processes of Civil War: The Wartime Transformation of Social Networks. Annual Review of Political Science 11: 539–61. [Google Scholar] [CrossRef]
- Yampolskiy, Roman V. 2020. AI Will Fail, Like Everything Else, Eventually. Mind Matters. Available online: https://mindmatters.ai/2020/07/ai-will-fail-like-everything-else-eventually/ (accessed on 31 October 2022).
| 1 | These are variably referred to in discussions as ‘lethal autonomous robots’, ‘fully autonomous weapons’, and ‘killer robots’. |
| 2 | For summaries of the overall debate and the constituent points of contention, see (Cummings 2018; Eklund 2020; Lewis 2015; Santoni de Sio and van den Hoven 2018). |
| 3 | See Section 2.2. |
| 4 | This does not take away from the fact that some international armed conflicts can also be particularly violation-dense, as observed during the Yugoslav wars and the 2022 Russo-Ukrainian war. However, existing literature on AWS plentifully addresses this type of conflict. |
| 5 | See Section 3.2. |
| 6 | While the conception of the specific technology being addressed varies significantly by source, one popular definition by the ICRC (Davison 2017) is formulated as follows: “Any weapon system with autonomy in its critical functions—that is, a weapon system that can select (search for, detect, identify, track or select) and attack (use force against, neutralize, damage or destroy) targets without human intervention”. For the lack of consensus on a definition in the international debate, see (Boulanin 2016). |
| 7 | This does not a priori exclude groups labelled as ’terrorist organisations’—strictly speaking a political designation—as long as they are parties to the conflict. For a more complete discussion on when terrorist groups qualify as parties under LOAC, see (Bartels 2018). |
| 8 | In addition, some are of the opinion that this argument cannot be resolved as it involves speculating how AI will develop in the future, which is not productive. See (Schuller 2017; UK Mission Geneva 2019; Wittes 2012). |
| 9 | For a graphical representation of the development of internal versus international armed conflicts, see (Harbom and Wallensteen 2005). |
| 10 | See Section 4. |
| 11 | See Section 3. |
| 12 | See www.sipri.org/databases/armstransfers, accessed on 10 October 2022. |
| 13 | The cited study uses this term in the colloquial sense, i.e., referring to groups or persons migrating for fear of harm (instead of in a legal sense, which carries legal consequences for the persons in question). |
| 14 | See Section 3.2. |
| 15 | The experience of the catastrophic US retreat from Afghanistan and the subsequent looting of US weapons by the Taliban (Weaver 2021), however, shows that ’stronger governments’ are not necessarily exempt from this scenario. |
| 16 | Most internal conflicts feature a government which has much higher arms sophistication compared to the NSAGs, as it had a weapons monopoly before the conflict outbreak (Pamp et al. 2018). In some situations, however, the government may be as weak as the NSAG. These conflicts are termed ‘symmetric nonconventional’ by (Kalyvas and Balcells 2010). Even in this case, however, the NSAG has an interest in overcoming the stalemate by obtaining and using stronger weapons, such as AWS. |
| 17 | Depending on the system in question, however, this can also take other forms. (McAllister 2018), for instance, discusses a hypothetical ’AI interrogator’ which, in NSAG hands, can also be misused in contravention to the prohibition on torture. |
| 18 | (Additional Protocol II 1977) only encourages (instead of obliges) States to “grant the broadest possible amnesty to persons who have participated in the armed conflict”. See also (Kleffner 2007). |
| 19 | This is purely a logistical remark; it does not mean that NSAGs are excused from using blatantly illegal weapons merely because they claim not to have the technical or legal expertise to evaluate them upon obtention. LOAC principles governing weapon use apply equally to States as to NSAGs. See (Sivakumaran 2006; Special Court for Sierra Leone 2004). |
| 20 | See and compare: (ICRC 2006; Jevglevskaja 2018). |
| 21 | If taking into consideration extra-LOAC norms, this risk can be reduced through arms control or disarmament regimes. We discuss this as a potential solution in Section 6. |
| 22 | Collateral damage is usually calculated with the help of collateral damage estimation (CDE) software, which also requires technical expertise. See, e.g., (Chairman of the US Joint Chiefs of Staff 2012). |
| 23 | Indeed, this is often the reason cited for why NSAGs prefer small arms in the first place. See (Jackson 2011). |
| 24 | Note that by itself, this treaty would not be sufficient to mitigate all risks identified in Section 4 because the obligation in Art. 6 only triggers if there is ‘knowledge’ that it will be misused. In many situations we discussed, particularly related to technical reasons, there is no certainty that such misuse will occur. |
| 25 | COTS software and subsystems are already part of many military systems today, indicating a trend in that direction. See (Cummings 2018; DoD Defense Science Board 2016; Scherer 2016). |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2022 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kwik, J. Mitigating the Risk of Autonomous Weapon Misuse by Insurgent Groups. Laws 2023, 12, 5. https://doi.org/10.3390/laws12010005
Kwik J. Mitigating the Risk of Autonomous Weapon Misuse by Insurgent Groups. Laws. 2023; 12(1):5. https://doi.org/10.3390/laws12010005
Chicago/Turabian StyleKwik, Jonathan. 2023. "Mitigating the Risk of Autonomous Weapon Misuse by Insurgent Groups" Laws 12, no. 1: 5. https://doi.org/10.3390/laws12010005
APA StyleKwik, J. (2023). Mitigating the Risk of Autonomous Weapon Misuse by Insurgent Groups. Laws, 12(1), 5. https://doi.org/10.3390/laws12010005





