A Survey of Patterns for Web Services Security and Reliability Standards
Abstract
:1. Introduction
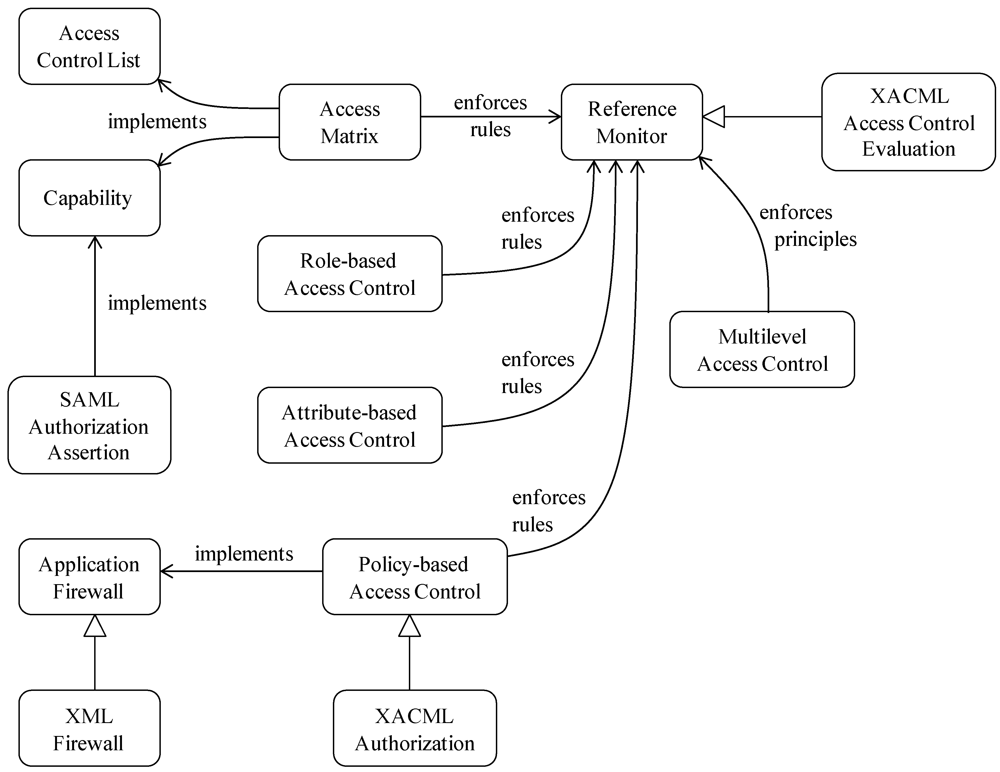
2. Fundamental Patterns for Access Control
- The Multilevel model organizes the data using security levels. This model is usually implemented as a mandatory model where its entities are labeled indicating their levels. There are separate models for confidentiality and integrity and accesses are decided by enforcing two principles or generic rules. This model is able to reach a high degree of security, although it can be too rigid for some applications. Usually, it is not possible to structure the variety of entities involved in complex applications into strictly hierarchical structures. However, they can be useful for structuring the architecture of systems.
- The Access Matrix describes access by subjects (actors, entities) to protected objects in specific ways (access types) [10]. It is more flexible than the multilevel model and it can be made even more flexible and precise using predicates and other extensions. However, it is intrinsically a discretionary model in which users own the data objects and may grant access to other subjects. It is not clear who owns the medical or financial information and the discretionary property reduces security because it may not be possible to decide who will acquire a specific right. This model is usually implemented using Access Control Lists (lists of the subjects that can access a given object) or Capabilities (tickets that allow a process to access some objects), described in two patterns:
- ○ Access Control List [12]: controls access to objects by indicating which subjects can access an object and in what way. There is usually an ACL associated with each object.
- ○ Capability [12]: controls access to objects by providing a credential or ticket to be given to a subject for accessing an object in a specific way.
- Role-Based Access Control (RBAC), collects users into roles based on their tasks or functions and assigns rights to each role. Some of these models have their roles structured as hierarchies, which may simplify administration.
- Attribute-Based Access Control (ABAC). This model controls access based on properties of subjects or objects. It is used in environments where some or all subjects may not be pre-registered and where the effect of the context is important to decide access.
- ○ Policy-Based Access Control [12]: models how to decide if a subject is authorized to access an object according to policies defined in a policy repository.
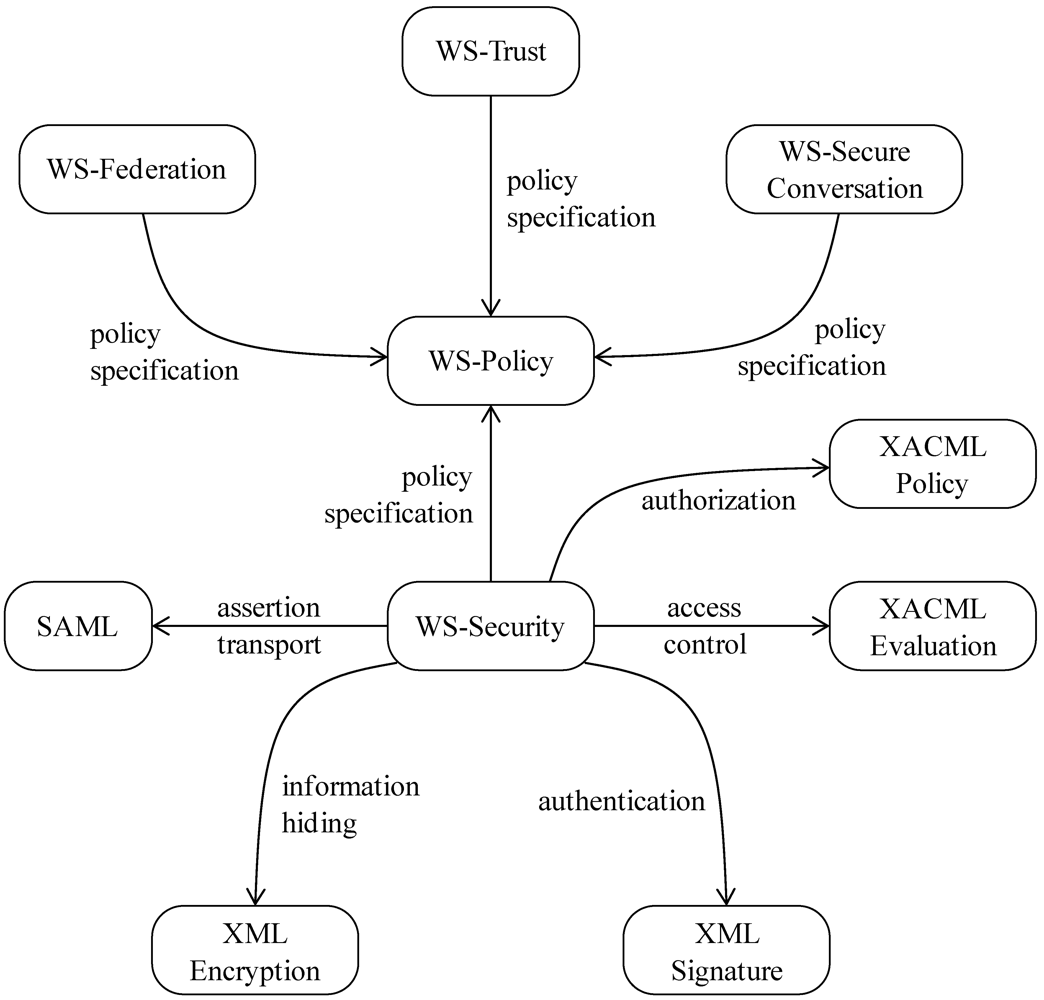
3. Access Control and Policies for Web Services
4. Cryptography for Web Services
5. Patterns for Identity [25]]

6. Wireless Web Services
7. Patterns for Web Services Reliability
8. Misuse Patterns
9. A Complete Pattern: WS-Trust
9.1. Intent
9.2. Example
9.3. Context
9.4. Problem
- Knowledge: In human relationships, we are concerned with first knowing a person before we trust her. That attitude applies also to web services. We need to have a structure that encapsulates some knowledge about the unit we intend to trust.
- Policy consideration: The web service policy contains all the required assertions and conditions that should be met to use that web service. The trust structure should consider this policy for verification purposes.
- Confidentiality and Integrity: Policies may include sensitive information. Malicious consumers may acquire sensitive information, fingerprint the service and infer service vulnerabilities. This implies that the policy itself should be protected.
- Message integrity: The data to be transferred between the partners through messages may be private data that need to be protected. Attackers may try to modify or replace these messages.
- Time Validity: For protection purposes, any interactions or means of communications (including the trust relationships) between the web services should have a time limit, that determines for how long the trust relationship is valid.
9.5. Solution
9.5.1. Structure
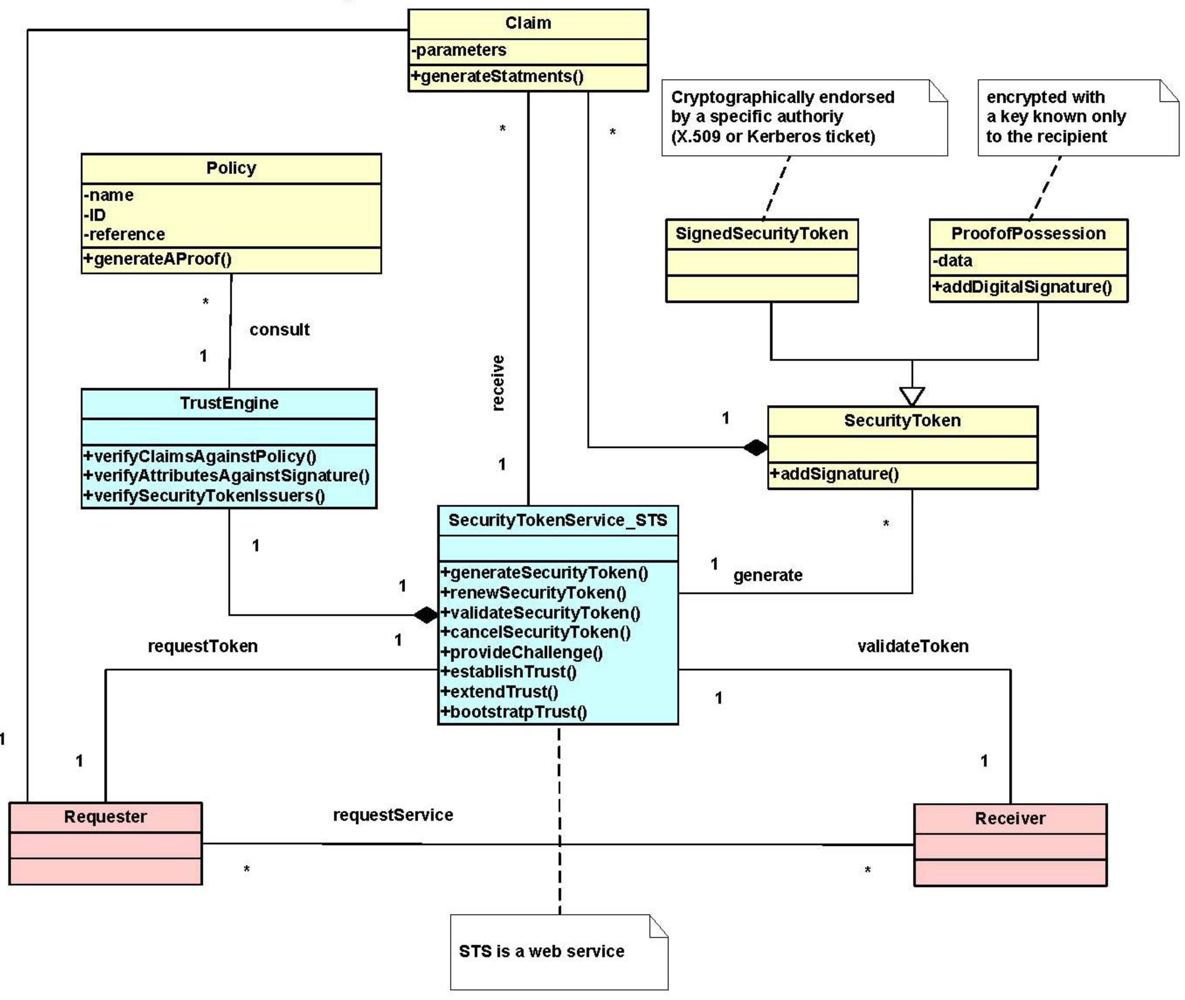
9.5.2. Dynamics
- Summary: STS creates a security token using the claims provided by the requester.
- Actors: A Requester
- Precondition: The STS has the required policy to verify the requester claims and the requester provides parameters in form of claims and RequestType signed by a signature.
- Description:
- The requester requests a security token by sending the required claims and RequestType signed by a Signature to the STS. The signature verifies that the request is legitimate.
- The STS contacts the Trust Engine to check the requester’s claims.
- The Trust Engine contacts the web service’s policy to verify the claims including attributes and security token issuers of the requester.
- Once approved, the STS creates a security token containing the requested claims.
- The STS sends back its SecurityTokenResponse with a security token issued for the requester.
- Postcondition: The requester has a security token that can be used to access resources in a trusted unit.
- Summary: A STS allows the use of resources by establishing trust by verifying proofOfClaims sent by the requester.
- Actors: A Requester
- Precondition: The Trust Engine has the required policy to verify the requester’ security token.
- Description:
- The requester asks for a service access by providing the required security token.
- The receiver sends the security token to the STS for verification.
- The STS use its Trust engine to verify the security token claims.
- Once approved, the STS notifies the receiver that the security token is valid and verified.
- The receiver gives the requester a token that implies the right to use the service.
- Postcondition: The requester has a security token that can be used to access services in a Receiver web service.


9.6. Implementation
- To communicate trust, a service requires proof, such as a signature to prove knowledge of a security token or set of security tokens. A service itself can generate tokens or it can rely on a separate STS to issue a security token with its own trust statement.
- Although the messages exchanged between the involved entities are protected by WS-Security; still three issues related to security tokens are possible: security token format incompatibility, security token trust, and namespace differences. The WS-Trust pattern addresses these issues by defining a request/response protocol (in which the client sends RequestSecurityToken and receives RequestSecurityTokenResponse) and introducing a Security Token Service (STS) which is another web service.
- Based on the credential provided by the requester, there are different aspects of requesting a security token (RST), each of which has a unique format that the requester should follow:
- ○ The issuance process: formed as RequestSecurityToken (RequestType, Claims). This is our use case Create a security token in the Dynamics section.
- ○ The renewal process: formed as RequestSecurityToken (RequestType, RenewTarget).
- ○ The cancel process: formed RequestSecurityToken (RequestType, CancelTarget). By the way, the cancelled token is no longer valid for authentication and authorization.
- ○ The validate process: formed as RequestSecurityToken (RequestType, ValidateTarget).
9.7. Example Resolved
9.8. Known Uses
- DataPower’s XS40 XML Security Gateway [33] is a device for securing web services that provides web services access control, message filtering and field-level encryption. It centralizes policy enforcement, supporting standards such as WS-Security, WS-Trust, WS-Policy and XACML.
- SecureSpan™ XML Firewall [34] enforces WS* and WS-I standards to centralize security and access requirements in policies that can be run as a shared service in front of applications.
- Vordel Security Token Service [35] is used to issue security tokens and to convert security tokens from one format to another. The security tokens created by an STS are bound to the messages travelling between web services..
- PingTrust, a standalone WS-Trust Security Token Server [36] creates and validates security tokens that are bound into SOAP messages according to the Web Services Security (WSS) standard.
9.9. Consequences
- Security. By extending the WS-Security mechanisms, we can handle security issues such as security tokens (the possibility of a token substitution attack), and signing (where all private elements should be included in the scope of the signature and where this signature must include a timestamp).
- Trust. With this solution, we have the choice of implementing the WS-Policy framework to support trust partners by expressing and exchanging their statements of trust. The description of this expected behavior within the security space can also be expressed as a trust policy.
- Confidentiality. We can achieve confidentiality of users’ information. Since Policy providers now can use mechanisms provided by other web services specifications such as WS-Security [ibm09b] to secure access to the policy, XML Digital Signature [24] to authenticate sensitive information, and WS-Metadata Exchange [37].
- All the security tokens exchanged between the involved parties are signed and stamped with unique keys that are known only to the recipients.
- Time validity. We can specify time constraints in the parameters of a security token issued by STS. This constraint will specify for how long that security token is valid. Upon expiring, the security token’s holder may renew or cancel it.
- The efficiency of WS-Trust may suffer from the repeated round-trips for multiple token requests. We need to make an effort to reduce the number of messages exchanged.
- The WS-Trust standard is a lengthy document and several details were left to avoid making the pattern too complex. The interested reader can find more details in the WS-Trust Standard web page [17].
9.10. Related Patterns
- The Trust Analysis Pattern, [38]. The objective of this pattern is to provide a conceptual model that embodies the abstract aspects of trust to make it applicable to different domains and applications.
- The Credential Pattern [39]. This pattern addresses the problem of exchanging data between trust boundaries and how to resolve the problem of authenticating and authorizing a principal’s identity over different systems.
- The Circle of Trust pattern allows the formation of trust relationships among service providers in order for their subjects to access an integrated and more secure environment [25]. The WS-Trust pattern could be used to establish trust between providers.
10. Related Work
11. Conclusions
Acknowledgements
References
- Gamma, E.; Helm, R.; Johnson, R.; Vlissides, J. Design Patterns: Elements of Reusable Object-Oriented Software; Addison-Wesley: Reading, MA, USA, 1994. [Google Scholar]
- Schumacher, M.; Fernandez, E.B.; Hybertson, D.; Buschmann, F.; Sommerlad, P. Security Patterns: Integrating Security and Systems Engineering; Wiley: Hoboken, NJ, USA, 2006. [Google Scholar]
- Fernandez, E.B. Security Patterns in Practice: Building Secure Architectures Using Software Patterns; John Wiley & Sons: Hoboken, NJ, USA, 2012. [Google Scholar]
- Fernandez, E.B.; Larrondo-Petrie, M.M.; Sorgente, T.; VanHilst, M. A Methodology to Develop Secure Systems Using Patterns. In Integrating Security and Software Engineering: Advances and Future Vision; Mouratidis, H., Giorgini, P., Eds.; IGI Gloga: Hershey, PA, USA, 2006; pp. 107–126. [Google Scholar]
- Delessy, N.; Fernandez, E.B. A Pattern-driven Security Process for SOA Applications. In Proceedings of the 3rd International Conference on Availability, Reliability, and Security (ARES 2008), Barcelona, Spain, 4–7 March 2008; pp. 416–421.
- Fernandez, E.B.; Delessy, N. Using Patterns to Understand and Compare Web Services Security Products and Standards. In Proceedings of the International Conference on Web Applications and Services (ICIW’06), Guadeloupe, French Caribbean, 23–25 February 2006.
- Fernandez, E.B.; Hashizume, K.; Buckley, I.; Larrondo-Petrie, M.M.; VanHilst, M. Web Services Security: Standards and Products. In Web Services Security Development and Architecture: Theoretical and Practical Issues; IGI Global Group: Hershey, PA, USA, 2009; pp. 152–177. [Google Scholar]
- Buschmann, F.; Meunier, R.; Rohnert, H.; Sommerlad, P.; Stal, M. Pattern- Oriented Software Architecture; Wiley: Hoboken, NJ, USA, 1996. [Google Scholar]
- Fernandez, E.; Pan, R. A pattern Language for Security Models. In Proceedings of the 8th Conference on Pattern Language of Programs (PLoP2001), Monticello, IL, USA, 11–15 September 2001.
- De Capitani di Vimercati, S.; Samarati, P.; Jajodia, S. Policies, Models, and Languages for Access Control. In Proceedings of the (Databases in Networked Information Systems)DNIS 2005, Aizu-Wakamatsu, Japan, 28–30 March 2005; pp. 225–237.
- De Capitani di Vimercati, S.D.; Paraboschi, S.; Samarati, P. Access control: Principles and solutions. Softw Pract. Exp. 2002, 33, 397–421. [Google Scholar]
- Delessy, N.; Fernandez, E.B.; Larrondo-Petrie, M.M.; Wu, J. Patterns for Access Control in Distributed Systems. In Proceedings of the 14th Pattern Languages of Programs Conference (PLoP2007), Monticello, IL, USA, 5–8 September 2007.
- Priebe, T.; Fernandez, E.B.; Mehlau, J.I.; Pernul, G. A Pattern System for Access Control. In Research Directions in Data and Applications Security XVIII; Farkas, C., Samarati, P., Eds.; Springer: Berlin, Germany, 2004. [Google Scholar]
- Delessy-Gassant, N.; Fernandez, E.B.; Rajput, S.; Larrondo-Petrie, M.M. Patterns for Application Firewalls. In Proceedings of the Pattern Languages of Programs Conference (PLoP) 2004, Monticello, IL, USA, 8–12 September 2004.
- Delessy, N.; Fernandez, E.B. Patterns for the eXtensible Access Control Markup Language. In Proceedings of the 12th Pattern Languages of Programs Conference (PLoP2005), Monticello, IL, USA, 7–10 September 2005.
- Ajaj, O.; Fernandez, E.B. A Pattern for the WS-Policy Standard. In Proceedings of the 8th Latin American Conference on Pattern Languages of Programs (SugarLoafPLoP 2010), Salvador, Bahia, Brazil, 23–26 September 2010.
- OASIS, WS-Trust 1.4. Available online: http://docs.oasis-open.org/ws-sx/ws-trust/v1.4/cd/ws-trust-1.4-spec-cd-01.pdf (accessed on 18 April 2012).
- Fernandez, E.B.; Delessy, N.A; Larrondo-Petrie, M.M. Patterns for Web Services Security. In Proceedings of the 21st International Conference on Object-Oriented Programming, Systems, Languages, and Applications, Portland, OR, USA, 22–26 October 2006.
- Lockhart, H.; Andersen, S.; Bohren, J.; Sverdlov, Y.; Hondo, M.; Maruyama, H.; Nadalin, A.; Nagaratnam, N.; Boubez, T.; Morrison, K.S.; et al. Web Services Federation Language (WS-Federation) Version 1.1. Available online: http://download.boulder.ibm.com/ibmdl/pub/software/dw/specs/ws-fed/WS-Federation-V1-1B.pdf?S_TACT=105AGX04&S_CMP=LP (accessed on April 18, 2012).
- OASIS, WS-SecureConversation 1.3. Available online: http://docs.oasis-open.org/ws-sx/ws-secureconversation/200512/ws-secureconversation-1.3-os.html (accessed on April 18, 2012).
- Hashizume, K.; Fernandez, E.B. A Pattern for WS-Security. In First IEEE Int. Workshop on Security Eng.Environments, Shanghai, China, 17–19 December 2009.
- Hashizume, K.; Fernandez, E.B. Symmetric Encryption and XML Encryption Patterns. In Proceedings of the 16th Conference on Pattern Languages of Programs (PLoP 2009), Chicago, IL, USA, 28–30 August 2009.
- Hashizume, K.; Fernandez, E.B.; Huang, S. Digital Signature with Hashing and XML Signature patterns. In Proceedings of the 14th European Conference on Pattern Languages of Programs (EuroPLoP 2009), Bavaria, Germany, 8–12 July 2009.
- XML Signature Syntax and Processing. Available online: http://www.w3.org/TR/xmldsig-core (accessed on April 18, 2012).
- Delessy, N.; Fernandez, E.B.; Larrondo-Petrie, M.M. A Pattern Language for Identity Management. In Proceedings of the 2nd IEEE International Multiconference on Computing in the Global Information Technology (ICCGI 2007), Guadeloupe, French Caribbean, 4–9 March 2007.
- Delessy, N.; Fernandez, E.B. Adapting Web Services Security Standards for Mobile and Wireless Environments. Lect. Notes Comput. Sci. 2007, 4537/2007, 624–633. [Google Scholar]
- W3C, Web Services Policy 1.5—Framework. Available online: http://www.w3.org/TR/ws-policy/ (accessed on 15 December 2011).
- OASIS, W-S SecurityPolicy 1.2. 2007. Available online: http://docs.oasis-open.org/ws-sx/ws-securitypolicy/v1.2/ws-securitypolicy.pdf (accessed on April 18, 2012).
- Buckley, I.; Fernandez, E.B.; Rossi, G.; Sadjadi, M. Web Services Reliability Patterns. In Proceedings of the 21st International Conference on Software Engineering and Knowledge Engineering (SEKE’2009), Boston, MA, USA, 1–3 July 2009.
- Fernandez, E.B.; Pelaez, J.C.; Larrondo-Petrie, M.M. Attack patterns: A new forensic and design tool. IFIP Int. Fed. Inf. Process. 2007, 242/2007, 345–357. [Google Scholar]
- Muñoz-Arteaga, J.; Fernandez, E.B.; Caudel, H. Misuse Pattern: Spoofing Web Services. In Proceedings of the Asian Pattern Languages of Programs Conference, 2011, Toyko, Japan, 5–7 October 2011.
- Box, D. Available online: http://msdn.microsoft.com/en-us/library/aa479664.aspx (accessed on 15 December 2009).
- IBM Corporation. WebSphere DataPower XML Security Gateway XS40. Available online: http://www-01.ibm.com/software/integration/datapower/xs40/ (accessed on 25 November 2009).
- The SecureSpan XML Firewall. Available online: http://www.layer7tech.com/main/products/xml-firewall.html (accessed on 9 December 2009).
- Vordel STS. Available online: http://www.vordel.com/solutions/security_token_services.html (accessed on 15 December 2009).
- PingTrust, a standalone Security Token Server. Available online: http://www.pingidentity.com/about-us/news-press.cfm?customel_datapageid_1173=1404 (accessed on 15 December 2009).
- Web Services Metadata Exchange. Available online: http://www.w3.org/TR/ws-gloss/ (accessed on 15 December 2009).
- Fayad, M.E.; Hamza, H. The Trust Analysis Pattern. Proceedings of the Fourth Latin American Conference on Pattern Languages of Programming (SugarLoafPLoP 2004), Porto Das Dunas, Brazil, 10–13, August 2004; Available online: http://sugarloafplop2004.ufc.br/acceptedPapers/ww/WW_1.pdf (accessed on 15 December 2009).
- Morrison, P.; Fernandez, E.B. The credentials pattern. Proceedings of the 2006 conference on Pattern languages of programs (PLoP 2006), Portland, OR, USA, 21–23 October 2006; Available online: http://portal.acm.org/citation.cfm?id=1415472.1415483 (accessed on 15 December 2009).
- Zirpins, C.; Lamersdorf, W.; Baier, T. Flexible Coordination of Service Interaction Patterns. In Proceedings of the Second International Conference on Service-Oriented Computing (ICSOC’04), New York, NY, USA, 15–18 November 2004.
- Benatallah, B.; Dumas, M.; Fauvet, M.-C.; Rabhi, F.A.; Sheng, Q.Z. Overview of some patterns for architecting and managing composite web services. ACM SIGecom Exch. 2002, 3, 9–16. [Google Scholar]
- Tatsubori, M.; Imamura, T.; Nakamura, Y. Best-Practice Patterns and Tool Support for Configuring Secure Web Services Messaging. In Proceedings of the IEEE International Conference on Web Services (ICWS’04), San Diego, CA, USA, 6–9 June 2004.
- Imamura, T.; Tatsubori, M. Patterns for Securing Web Services Messaging. In Proceedings of the OOPSLA Workshop on Web Services and Service Oriented Architecture Best Practice and Patterns, Anaheim, CA, USA, 26–31 November 2003.
- Grushka, N.; Jensen, M.; LoIacono, L. A Design Pattern for Event-Based Processing of Security-enriched SOAP Messages. In Proceedings of the International Conference on Availability, Reliability, and Security (ARES 2010), Krakow, Poland, 15–18 February 2010.
- Erl, T. SOA Design Patterns; Prentice Hall: Upper Saddle River, NJ, USA, 2009. [Google Scholar]
- Web Service Security Patterns—Community Technical Preview. 2010. Available online: http://msdn.microsoft.com/en-us/library/ff648183.aspx (accessed on 12 April 2012).
- Steel, C.; Nagappan, R.; Lai, R. Core Security Patterns: Best Strategies for J2EE, Web Services, and Identity Management; Prentice Hall: Upper Saddle River, NJ, USA, 2005. [Google Scholar]
© 2012 by the authors; licensee MDPI, Basel, Switzerland. This article is an open-access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/3.0/).
Share and Cite
Fernandez, E.B.; Ajaj, O.; Buckley, I.; Delessy-Gassant, N.; Hashizume, K.; Larrondo-Petrie, M.M. A Survey of Patterns for Web Services Security and Reliability Standards. Future Internet 2012, 4, 430-450. https://doi.org/10.3390/fi4020430
Fernandez EB, Ajaj O, Buckley I, Delessy-Gassant N, Hashizume K, Larrondo-Petrie MM. A Survey of Patterns for Web Services Security and Reliability Standards. Future Internet. 2012; 4(2):430-450. https://doi.org/10.3390/fi4020430
Chicago/Turabian StyleFernandez, Eduardo B., Ola Ajaj, Ingrid Buckley, Nelly Delessy-Gassant, Keiko Hashizume, and Maria M. Larrondo-Petrie. 2012. "A Survey of Patterns for Web Services Security and Reliability Standards" Future Internet 4, no. 2: 430-450. https://doi.org/10.3390/fi4020430
APA StyleFernandez, E. B., Ajaj, O., Buckley, I., Delessy-Gassant, N., Hashizume, K., & Larrondo-Petrie, M. M. (2012). A Survey of Patterns for Web Services Security and Reliability Standards. Future Internet, 4(2), 430-450. https://doi.org/10.3390/fi4020430



