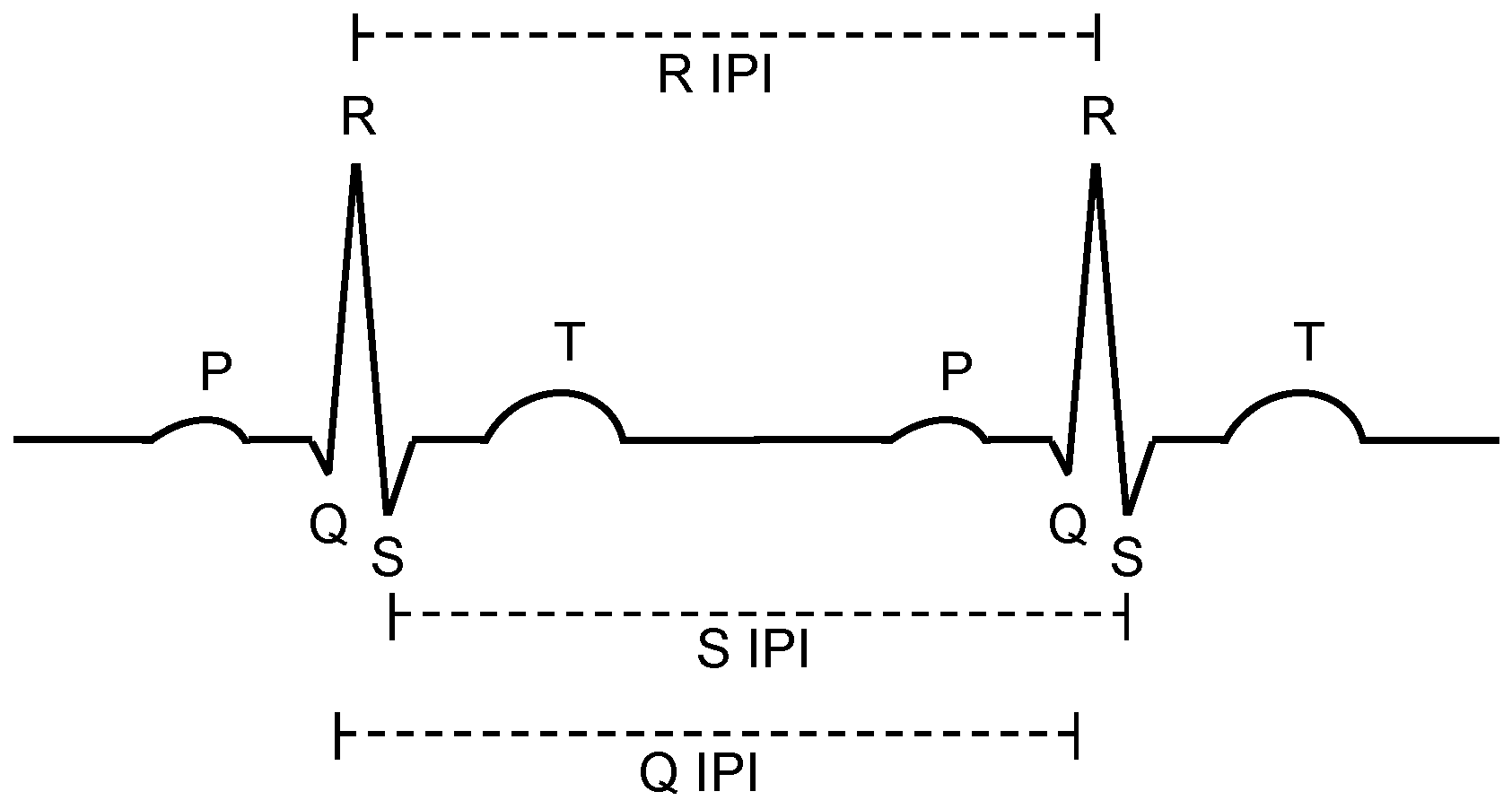
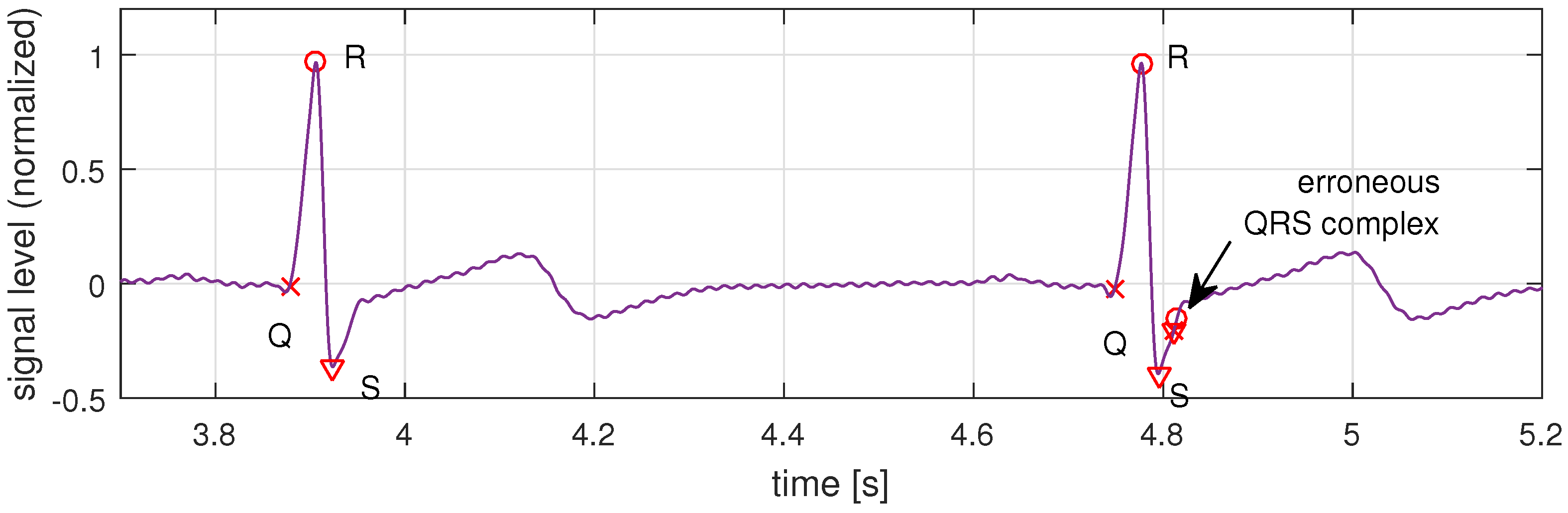
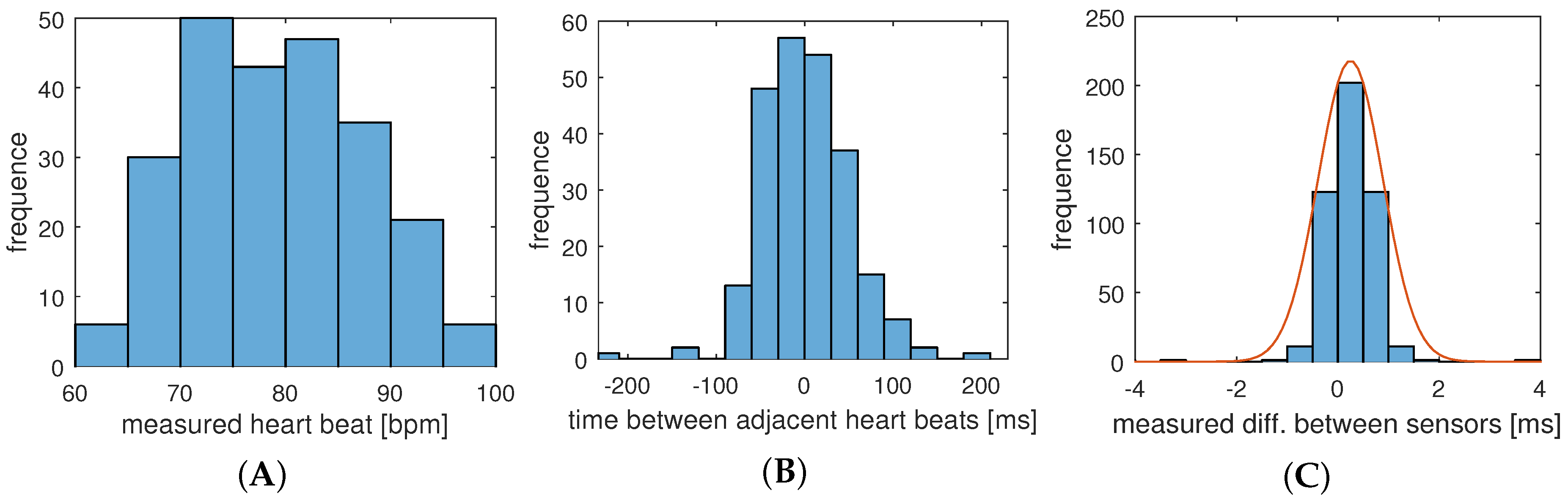
In this section, we apply the results and measurements we gained for the system, presented in the previous section, to engineer and evaluate a secure and robust biometric authentication protocol. The major challenge is that different sensor nodes measure similar but not exactly the same values, so that a margin of error has to be accepted. In the authentication protocol, we exploit the fact, that the natural distribution of IPIs (see
Figure 11B) is larger than the measured uncertainty of our system (
Figure 11C). The hypothesis is that we can decide whether deviations for a set of sampling points from different sensors is caused by technical uncertainties or by a node that is not attached to the same body. Furthermore, our investigations address the question of how the number of samples and their resolution affect the quality and reliability of the authentication process.
7.2. Parameters of the Authentication Protocol
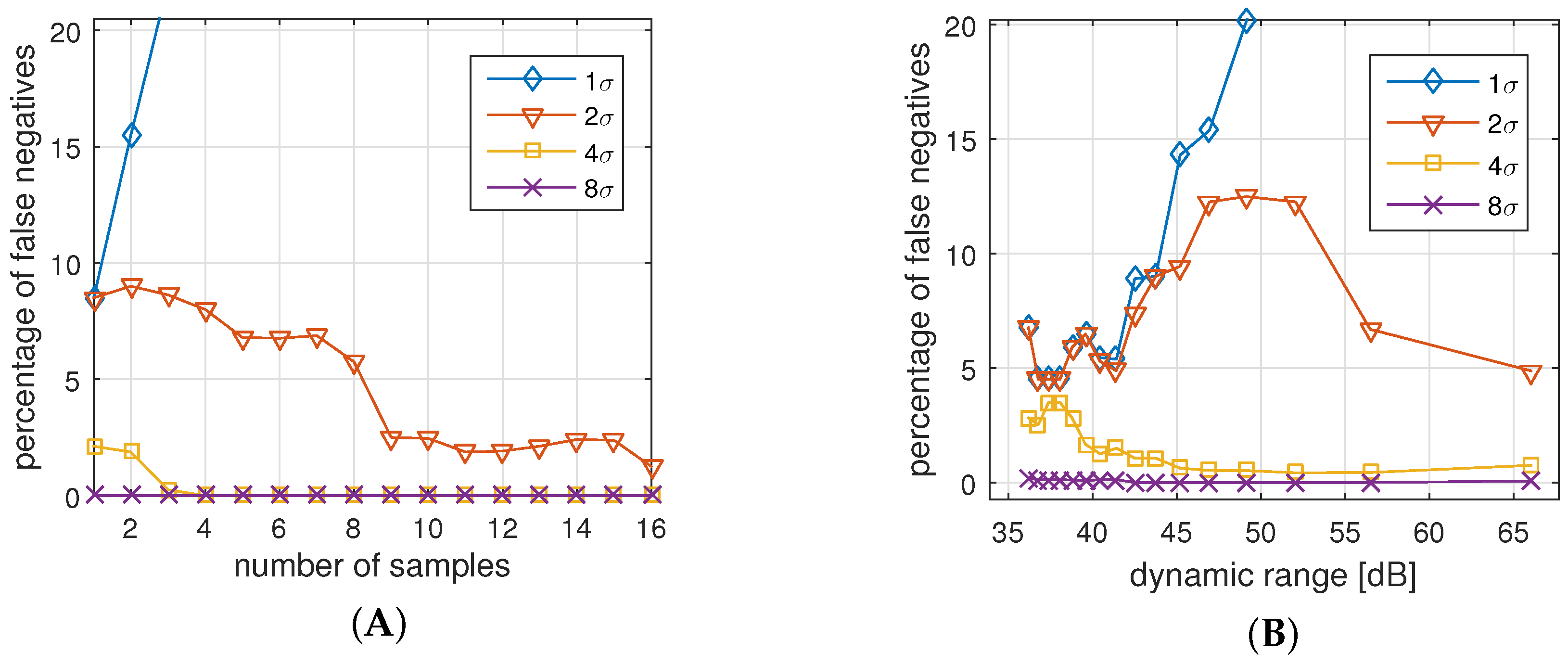
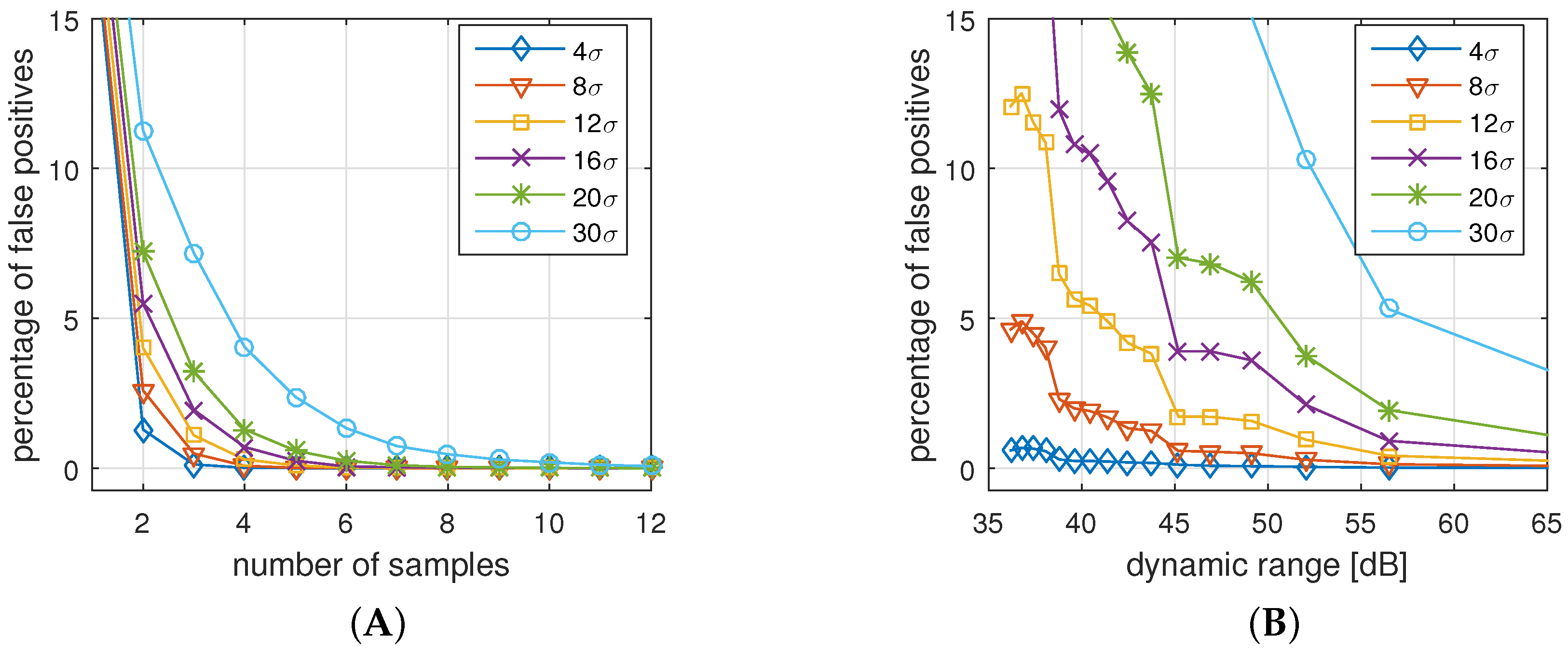
Since participated sensor nodes might sense or process different IPI values, the comparison function over the two IPI arrays of equal size has to accept a degree of uncertainty in the data values. Thereby, it is the goal to minimize the number of false positive authentications (FPA) and false negative authentications (FNA).
False negative authentications (NFA) is the percentage of legitimate authentication attempts that are rejected due to a high level of measurement or processing errors.
False positive authentications (NPA) is the percentage of non-legitimate authentication attempts that are accepted by a node due to a high tolerance for measurement or processing errors.
The comparison function compares the statistical properties of the two IPI vectors. The function and its acceptance properties and its footprint can be tailored by three parameters:
Dynamic range (r) measured in dB, expresses the resolution of the sampled IPI values.
r is based on the distance Δ between two adjacent IPI values in ms. Since the underlying physical phenomenon is in a range of
ms, we can compute the required number of bits per value by
, and the dynamic range is
.
Table 4 shows example values for Δ,
b, and
r. We assume that a lower dynamic range will reduce the number of false positives but increases the number of false negatives.
It should be noted that changing the resolution also changes the statistical properties of the reference model. For instance the results in
Figure 11 was taken with a resolution of
ms and resulted in a standard deviation of
, while a resolution of 2 ms results in
.
Number of samples (s) defines the number of IPI data points we use for one authentication process. The number of samples influences the time for taking measurements, as well as the message size.
Table 5 shows the message sizes for a range of configurations. From a quality perspective, we can expect that more samples compensate for outlier data points, and increase confidence in the positive or negative decision.
Allowed deviation (d) measured in number of standard deviations (
σ), determines how much deviation is acceptable to distinguish legitimate measurements from data not originating from the same body. Therefore,
d can be considered as similarity factor that decides whether a node is trusted or not. The value of
σ is based on the actual measurements (see
Figure 11) and the underlying dynamic range. Using the error factor
, while
σ is the standard deviation of the expected measurement error (see
Figure 11C), and
is the error distribution of the difference between
and
:
we define the comparison function as:
It can be assumed that a larger d reduces the number of false negatives but increases the number of false positives.
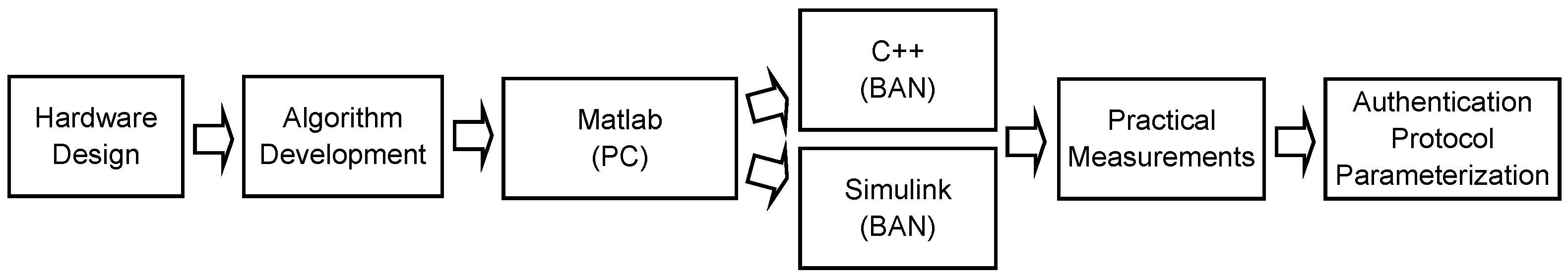
The number samples (
s) and the dynamic range (
r) have a minor effect on the total computation time of the protocol. The protocol requires two hashing operations (of the nonce and the samples), and the computation of one standard deviation (of the differences between the measurements of the two peers). Depending on
s and
r, the total time for these operations varies between 130
s and 160
s when we apply MD5 as hash function, and between 250
s and 290
s when SHA256 is applied. These figures are negligible compared to the signal processing efforts reported in
Section 6.3, and, therefore, do not affect the search for preferable parameter combinations.
7.4. Parameter Selection and Sensitivity Analysis
Based on the practical and analytical experimental results, the parameters of the comparison function ≈ can be set, so that the FPA and FNA rates are reduced, and the required resources (packet size) and authentication time (number of required samples) are considered. As a result, for our analysis of the data gathered with the presented BAN setup, we decided on a sample size of eight, with 8-bit sample encoding (48 dB) and an allowed deviation of . In our experiments, this setup led to 0% false positives and 0% false negatives. In fact, for the given setting, the allowed deviation d could be freely selected between 2 and 14 to obtain the same positive result.
To investigate the sensitivity of the parameter selection, in cases where the nodes process the data with a higher timing uncertainty than in our experiment, we ran tests with an increased noise level. Specifically, we studied the sensitivity of the accepted deviation
d in environments with higher uncertainty. Possible reasons for higher deviations are less precise sensors and signal processing, timing-uncertainties in the embedded system, but also older or less healthy persons [
18]. We were interested in the required thresholds of
d to limit the FNR to 1%, and to limit the FPR to the levels of 1% and 5%.
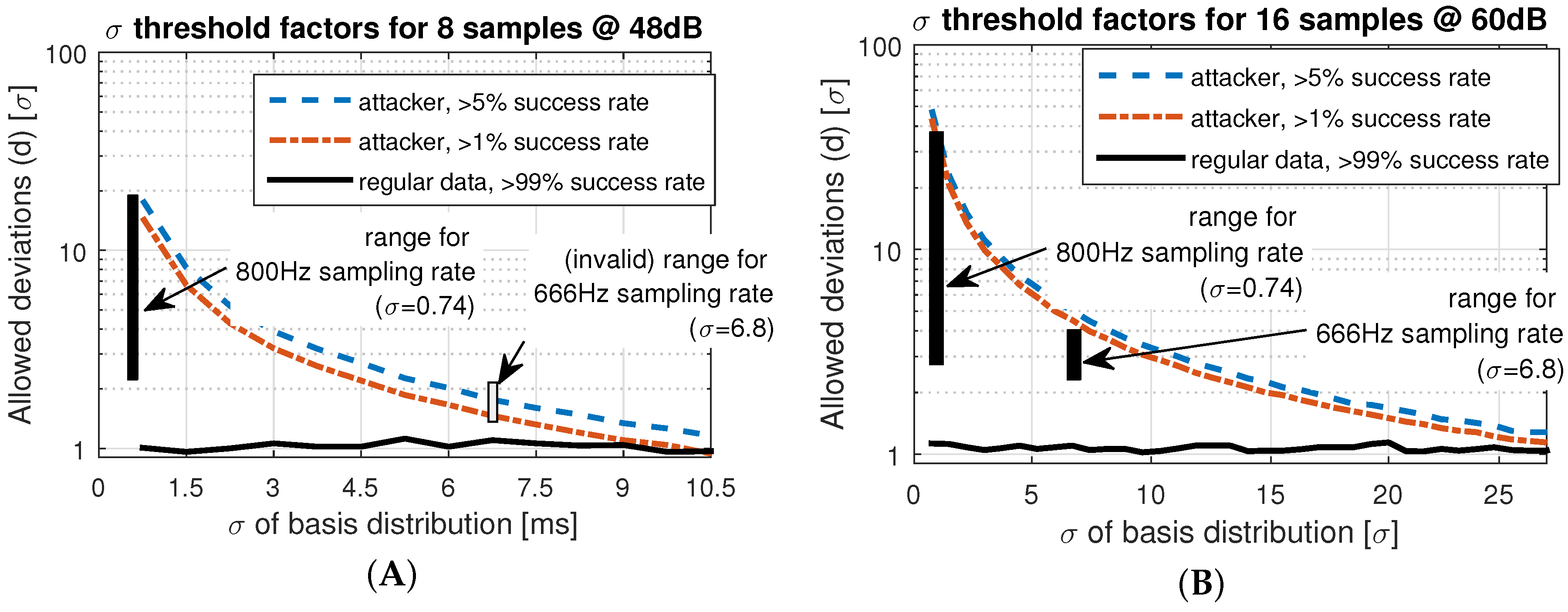
The results are shown in
Figure 15.
Figure 15A shows the thresholds for our selected settings (eight samples, 48 dB). We see that the acceptable threshold for the FNR stays between
and
and is not affected by increased variation of the underlying measurements. The reason is that
σ is a factor in the acceptance Equation (
3), and, therefore, an increased noise level in the underlying distribution increases the acceptance deviation as well.
However,
Figure 15A,B show that the thresholds for FPR decrease with an increased deviation in the reference error distribution. That effect is plausible, because if a high level of noise has to be tolerated, it is more challenging to differentiate between deviations due to attacks and natural noise.
Our default settings of the protocol, shown in
Figure 15A, can tolerate measurement uncertainty up to
ms, if we require 1
σ between the FPA and FNA thresholds. Higher noise levels would increase the FPAs, since attacks cannot be clearly distinguished from legitimate authentication attempts.
Larger uncertainty than
ms requires an adaptation of the system parameters.
Figure 15B shows the thresholds for 16 samples and 60 dB (11 bit) dynamic range. The plot shows that, in this case, a 20 times higher basis deviation still provides sufficient space to differentiate between authentic and forged attempts. However, the cost for this improved confidence is the extended sample time (16 instead of 8 heart beats) and the larger packet sizes (160 instead of 64 byte).
To validate the simulation results, we applied practical measurements gathered with different sampling rates. The effective ranges for a 99% confidence of FPA and FNA are highlighted as the rectangles in
Figure 15A,B. We only show the 800 Hz and 666 Hz sampling rates, because higher rates were not distinguishable from 800 Hz. Lower rates such as 500 Hz result in a standard deviation of
ms, which is impractical. The measurements show that the practical FNA threshold is about
higher than estimated in the simulations, while the FPA threshold corresponds to the simulations. As a result, shown in
Figure 15A, the data gathered at 666 Hz cannot be successfully distinguished, because with
, the practical threshold to prevent attacks is lower than the threshold to identify legitimate attempts. With the extended setting (
Figure 15B), we still have a valid range for
d between 2.5
σ and 4
σ. The results show that protocol parameters with a preferable quality-to-resource trade-off can be found if the uncertainty of the implemented system are known.